| File name: | 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader |
| Full analysis: | https://app.any.run/tasks/4b7fcd1c-6b40-41e9-9b6e-f6fe99f90132 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 00:57:11 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 3EE898EE8CD395C91F15162E01142B60 |
| SHA1: | 8C7AC62C212418F917C8CA987D07143C7F388ADE |
| SHA256: | 52241C4C99C1C6198D818A731207EC5FC500EBB74E4FC4F240325ADFEBEEC935 |
| SSDEEP: | 98304:hilxFZ8VWHB9IWRUqo2rmf1zJ7EnQd2VZc5/:CG |
MALICIOUS
Connects to the CnC server
- 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe (PID: 5008)
SUSPICIOUS
Executable content was dropped or overwritten
- 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe (PID: 5008)
Process drops legitimate windows executable
- 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe (PID: 5008)
Reads security settings of Internet Explorer
- 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe (PID: 5008)
Contacting a server suspected of hosting an CnC
- 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe (PID: 5008)
There is functionality for taking screenshot (YARA)
- 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe (PID: 5008)
INFO
The sample compiled with english language support
- 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe (PID: 5008)
The sample compiled with korean language support
- 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe (PID: 5008)
Failed to create an executable file in Windows directory
- 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe (PID: 5008)
Reads the computer name
- 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe (PID: 5008)
Checks supported languages
- 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe (PID: 5008)
Checks proxy server information
- 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe (PID: 5008)
- slui.exe (PID: 5984)
Create files in a temporary directory
- 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe (PID: 5008)
UPX packer has been detected
- 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe (PID: 5008)
Reads the software policy settings
- slui.exe (PID: 5984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (16.3) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (14.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.4) |
| .exe | | | Win32 Executable (generic) (2.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2086:06:02 18:32:34+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 1199616 |
| InitializedDataSize: | 561664 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x101d14 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Korean |
| CharacterSet: | Unicode |
| CompanyName: | TODO: <회사 이름> |
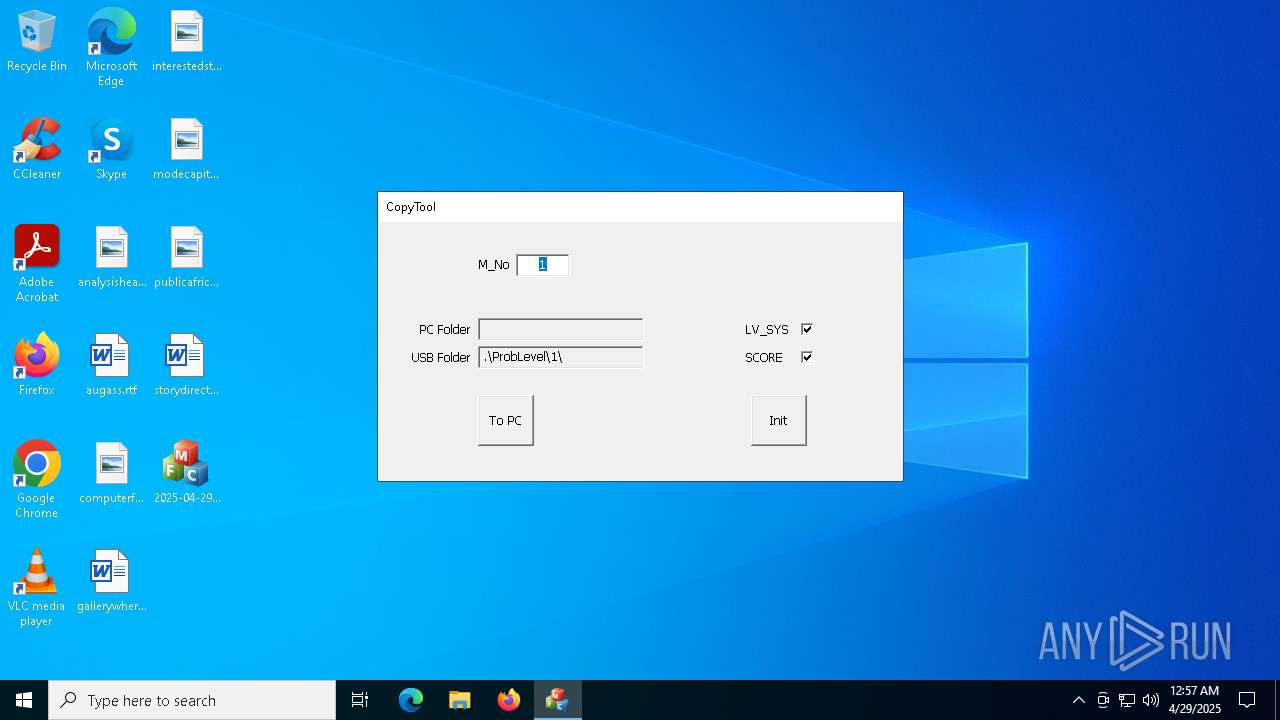
| FileDescription: | CopyTool |
| FileVersion: | 1.0.0.1 |
| InternalName: | CopyTool.exe |
| LegalCopyright: | TODO: (c) <회사 이름>. 모든 권리 보유. |
| OriginalFileName: | CopyTool.exe |
| ProductName: | TODO: <제품 이름> |
| ProductVersion: | 1.0.0.1 |
Total processes
129
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5008 | "C:\Users\admin\Desktop\2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe" | C:\Users\admin\Desktop\2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe | explorer.exe | ||||||||||||
User: admin Company: TODO: <회사 이름> Integrity Level: MEDIUM Description: CopyTool Version: 1.0.0.1 Modules
| |||||||||||||||
| 5984 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 786
Read events
3 783
Write events
3
Delete events
0
Modification events
| (PID) Process: | (5008) 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5008) 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5008) 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5008 | 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe | C:\Users\admin\AppData\Local\Temp\conres.dll | executable | |
MD5:7574CF2C64F35161AB1292E2F532AABF | SHA256:DE055A89DE246E629A8694BDE18AF2B1605E4B9B493C7E4AEF669DD67ACF5085 | |||
| 5008 | 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe | C:\Users\admin\AppData\Local\Temp\conres.dll.000 | text | |
MD5:1130C911BF5DB4B8F7CF9B6F4B457623 | SHA256:EBA08CC8182F379392A97F542B350EA0DBBE5E4009472F35AF20E3D857EAFDF1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
56
DNS requests
23
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1616 | RUXIMICS.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1616 | RUXIMICS.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5008 | 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe | GET | 403 | 45.33.18.44:80 | http://www.aieov.com/logo.gif | unknown | — | — | malicious |
5008 | 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe | GET | 403 | 45.33.18.44:80 | http://www.aieov.com/logo.gif | unknown | — | — | malicious |
— | — | GET | 200 | 52.149.20.212:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
5008 | 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe | GET | 403 | 45.33.18.44:80 | http://www.aieov.com/logo.gif | unknown | — | — | malicious |
5968 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
5968 | SIHClient.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1616 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1616 | RUXIMICS.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1616 | RUXIMICS.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
5isohu.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.aieov.com |
| malicious |
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5008 | 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |
5008 | 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |
5008 | 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |
5008 | 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |
5008 | 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |
5008 | 2025-04-29_3ee898ee8cd395c91f15162e01142b60_amadey_darkgate_elex_floxif_smoke-loader.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |