| File name: | AdminService.exe |
| Full analysis: | https://app.any.run/tasks/9eed6a48-33f0-4c77-ac77-90b8cb6aee65 |
| Verdict: | Malicious activity |
| Analysis date: | March 13, 2025, 12:27:39 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 8 sections |
| MD5: | 546CCCC70E397A5273145ECE316E023F |
| SHA1: | 8313A2584586353B8CE7517DD58D1CDCF0BA0FFA |
| SHA256: | 52238BF0D56983CD5D8C36B4F3C7D6B72D259CC60F3FCD8AD081A8380C349B82 |
| SSDEEP: | 12288:ql0lOndZjJJh+VXsh5E+RGZA2XnRLxf4s:ql0lSZN+GGW2XnTf4s |
MALICIOUS
Executing a file with an untrusted certificate
- AdminService.exe (PID: 5088)
- AdminService.exe (PID: 2380)
SUSPICIOUS
Reads the date of Windows installation
- AdminService.exe (PID: 5088)
Application launched itself
- AdminService.exe (PID: 5088)
Reads security settings of Internet Explorer
- AdminService.exe (PID: 5088)
Reads the Internet Settings
- AdminService.exe (PID: 5088)
INFO
The sample compiled with english language support
- AdminService.exe (PID: 5088)
Reads the computer name
- AdminService.exe (PID: 2380)
- AdminService.exe (PID: 5088)
Checks supported languages
- AdminService.exe (PID: 2380)
- AdminService.exe (PID: 5088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2019:09:03 08:57:53+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14 |
| CodeSize: | 198656 |
| InitializedDataSize: | 174080 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x19c8c |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 10.0.10011.16384 |
| ProductVersionNumber: | 10.0.10011.16384 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Windows (R) Win 7 DDK provider |
| FileDescription: | Windows Setup API |
| FileVersion: | 10.0.10011.16384 |
| InternalName: | SETUPAPI.DLL |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | SETUPAPI.DLL |
| ProductName: | Windows (R) Win 7 DDK driver |
| ProductVersion: | 10.0.10011.16384 |
Total processes
103
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2320 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AdminService.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2380 | "C:\Users\admin\Desktop\AdminService.exe" uninstall | C:\Users\admin\Desktop\AdminService.exe | — | AdminService.exe | |||||||||||
User: admin Company: Windows (R) Win 7 DDK provider Integrity Level: MEDIUM Description: Windows Setup API Exit code: 0 Version: 10.0.10011.16384 Modules
| |||||||||||||||
| 4456 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AdminService.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
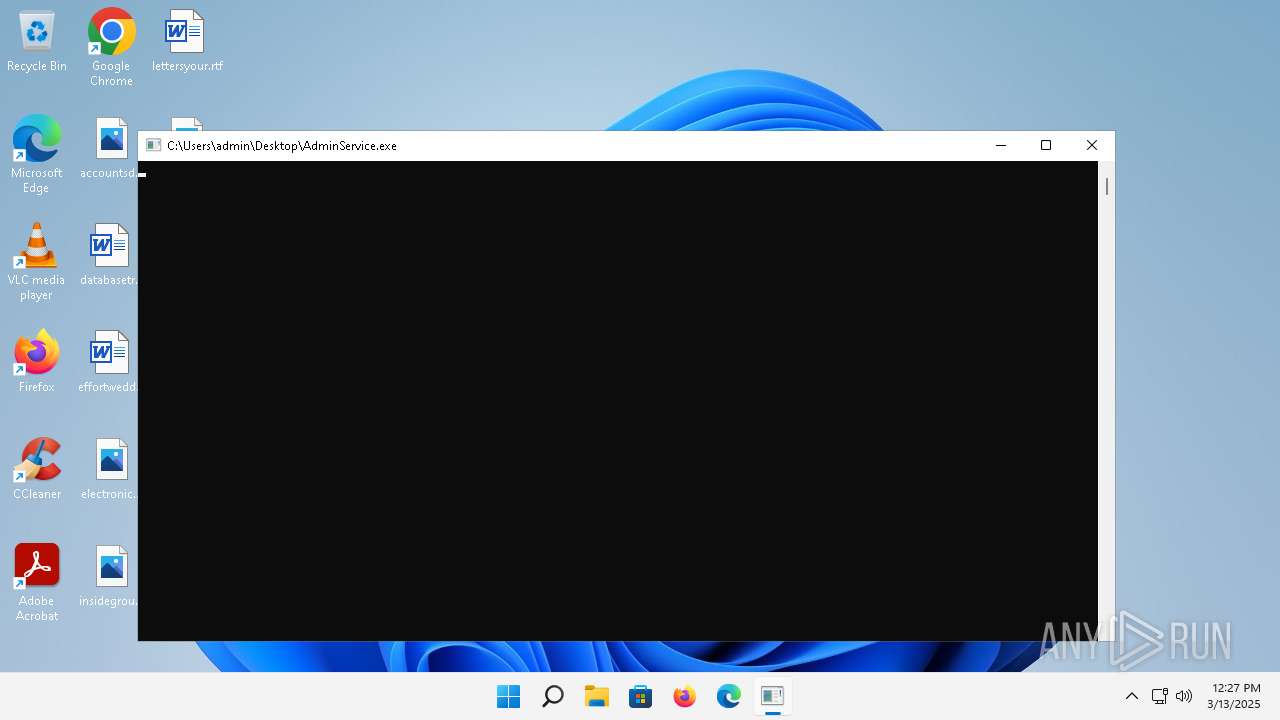
| 5088 | "C:\Users\admin\Desktop\AdminService.exe" | C:\Users\admin\Desktop\AdminService.exe | explorer.exe | ||||||||||||
User: admin Company: Windows (R) Win 7 DDK provider Integrity Level: MEDIUM Description: Windows Setup API Exit code: 1 Version: 10.0.10011.16384 Modules
| |||||||||||||||
Total events
309
Read events
301
Write events
8
Delete events
0
Modification events
| (PID) Process: | (5088) AdminService.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (5088) AdminService.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (5088) AdminService.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (5088) AdminService.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
15
DNS requests
9
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5340 | MoUsoCoreWorker.exe | GET | 200 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b8be39d89852d784 | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.32.238.224:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
3640 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e9f723a4a1e59b1b | unknown | — | — | whitelisted |
— | — | HEAD | 200 | 23.199.214.10:443 | https://fs.microsoft.com/fs/windows/config.json | unknown | — | — | unknown |
2768 | svchost.exe | GET | 200 | 23.50.131.216:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?5d698932ccffdd8a | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 23.50.131.216:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?9a78fd978e6e7371 | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 23.50.131.216:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?0cde1ba27ffa6121 | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.190.160.128:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
— | — | POST | 200 | 40.126.32.134:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
— | — | POST | 200 | 4.231.66.184:443 | https://checkappexec.microsoft.com/windows/shell/actions | unknown | binary | 182 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 23.32.238.224:80 | — | Akamai International B.V. | DE | whitelisted |
5340 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5340 | MoUsoCoreWorker.exe | 199.232.210.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
3640 | svchost.exe | 20.190.160.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3640 | svchost.exe | 199.232.210.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
3828 | smartscreen.exe | 20.82.9.214:443 | checkappexec.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2176 | svchost.exe | 23.60.203.209:443 | fs.microsoft.com | AKAMAI-AS | DE | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2768 | svchost.exe | 23.50.131.216:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | whitelisted |
2988 | OfficeClickToRun.exe | 52.182.143.214:443 | self.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
login.live.com |
| whitelisted |
checkappexec.microsoft.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
dns.msftncsi.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Microsoft Connection Test |
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
Process | Message |
|---|---|
AdminService.exe | DeleteAthService Enter ==>
|
AdminService.exe | DeleteAthService, The szFilename is: "C:\Users\admin\Desktop\AdminService.exe"
|
AdminService.exe | SetRegInfHwId, didn't find path
|
AdminService.exe | SetRegInfHwId Enter ==>
|