| File name: | secureclean-dongle-setup.exe |
| Full analysis: | https://app.any.run/tasks/94776d7b-acc6-4355-9a2a-4cb7c6d7e961 |
| Verdict: | Malicious activity |
| Analysis date: | February 02, 2022, 23:50:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | A6AAC9DF17D26684CE9AAADF404CC1C5 |
| SHA1: | 0F85922793654831622394E60CEDE32CC4986A0E |
| SHA256: | 522025FCA55B5301B1606B275F6E3CA142C1CF0ECB8CA98437F27D492E8CE71C |
| SSDEEP: | 196608:qpif/WNIeOygxjjezCSH+Eqsl/oFMVDE/NRQOjMDrA/ytGD8HQruJz+itg+H2fUO:czIeOygpeXdlgFMdmRdmrA/4QaJz+i+1 |
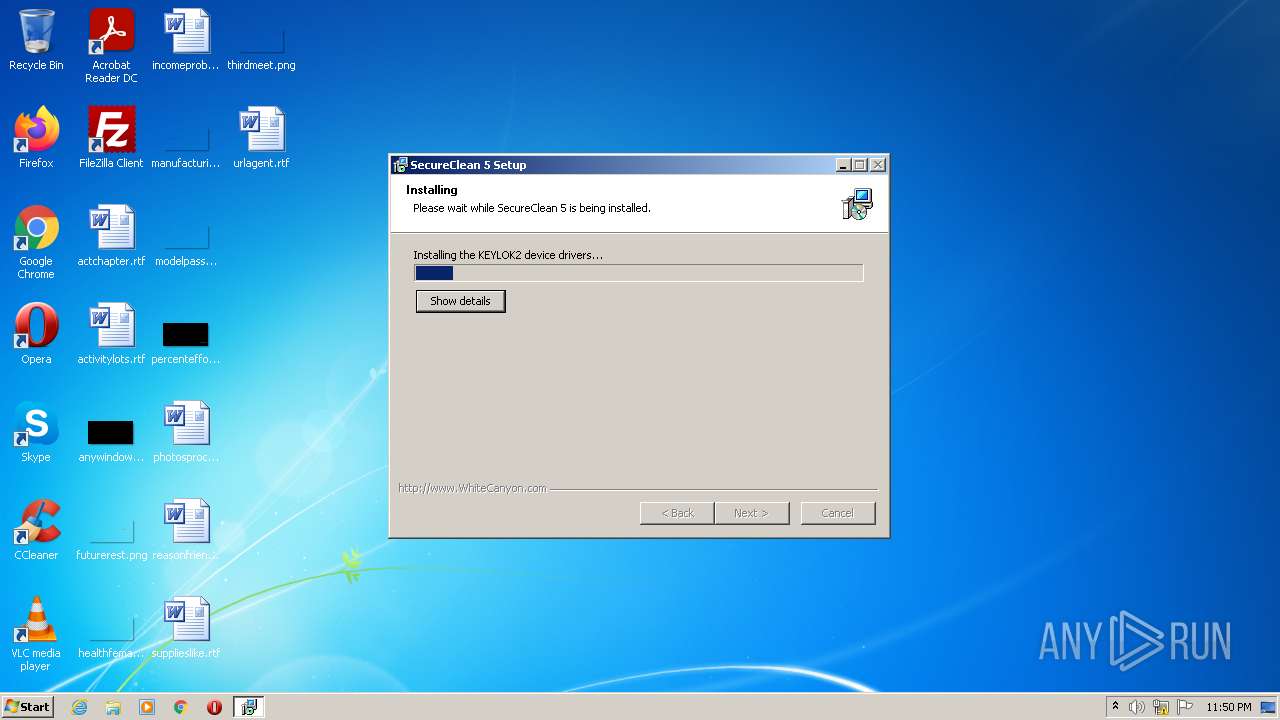
MALICIOUS
Loads dropped or rewritten executable
- secureclean-dongle-setup.exe (PID: 2056)
- SC5Service.exe (PID: 1872)
- SC5Service.exe (PID: 3992)
- SC5Service.exe (PID: 600)
- SecureClean.exe (PID: 3832)
- SecureClean.exe (PID: 3568)
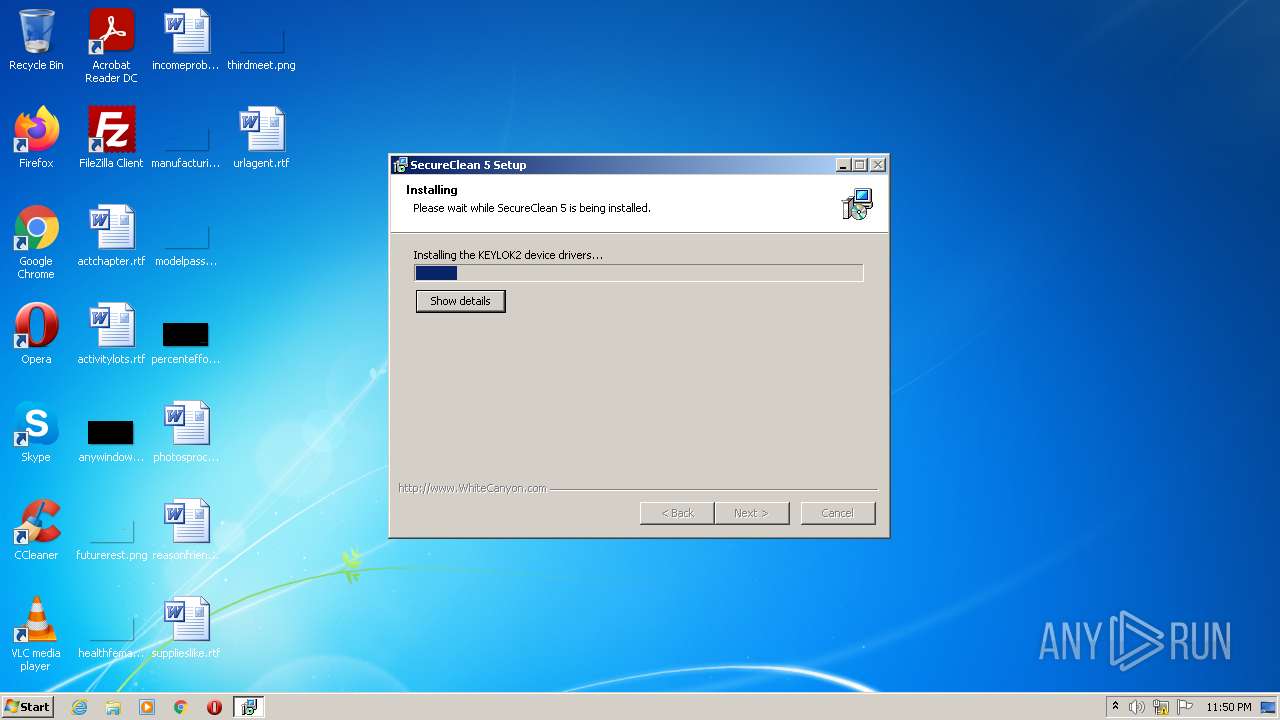
Drops executable file immediately after starts
- secureclean-dongle-setup.exe (PID: 2056)
- KeylokInstall.exe (PID: 1372)
- DPInst.exe (PID: 1252)
- DrvInst.exe (PID: 568)
Application was dropped or rewritten from another process
- KeylokInstall.exe (PID: 1372)
- DPInst.exe (PID: 1252)
- SC5Service.exe (PID: 1872)
- SC5Service.exe (PID: 3992)
- SC5Service.exe (PID: 600)
- SecureClean.exe (PID: 3832)
- SecureClean.exe (PID: 3568)
Changes the autorun value in the registry
- secureclean-dongle-setup.exe (PID: 2056)
Actions looks like stealing of personal data
- SC5Service.exe (PID: 600)
Steals credentials from Web Browsers
- SC5Service.exe (PID: 600)
SUSPICIOUS
Checks supported languages
- secureclean-dongle-setup.exe (PID: 2056)
- KeylokInstall.exe (PID: 1372)
- DPInst.exe (PID: 1252)
- DrvInst.exe (PID: 568)
- SC5Service.exe (PID: 1872)
- ns5B9F.tmp (PID: 3616)
- SC5Service.exe (PID: 3992)
- SecureClean.exe (PID: 3832)
- SecureClean.exe (PID: 3568)
- ns4F69.tmp (PID: 3568)
- SC5Service.exe (PID: 600)
Drops a file with a compile date too recent
- KeylokInstall.exe (PID: 1372)
Drops a file with too old compile date
- KeylokInstall.exe (PID: 1372)
- secureclean-dongle-setup.exe (PID: 2056)
- DPInst.exe (PID: 1252)
- DrvInst.exe (PID: 568)
Executable content was dropped or overwritten
- secureclean-dongle-setup.exe (PID: 2056)
- KeylokInstall.exe (PID: 1372)
- DPInst.exe (PID: 1252)
- DrvInst.exe (PID: 568)
Reads the computer name
- secureclean-dongle-setup.exe (PID: 2056)
- DPInst.exe (PID: 1252)
- KeylokInstall.exe (PID: 1372)
- DrvInst.exe (PID: 568)
- SC5Service.exe (PID: 1872)
- SC5Service.exe (PID: 3992)
- SC5Service.exe (PID: 600)
- SecureClean.exe (PID: 3832)
Creates files in the Windows directory
- DPInst.exe (PID: 1252)
- KeylokInstall.exe (PID: 1372)
- DrvInst.exe (PID: 568)
- SC5Service.exe (PID: 600)
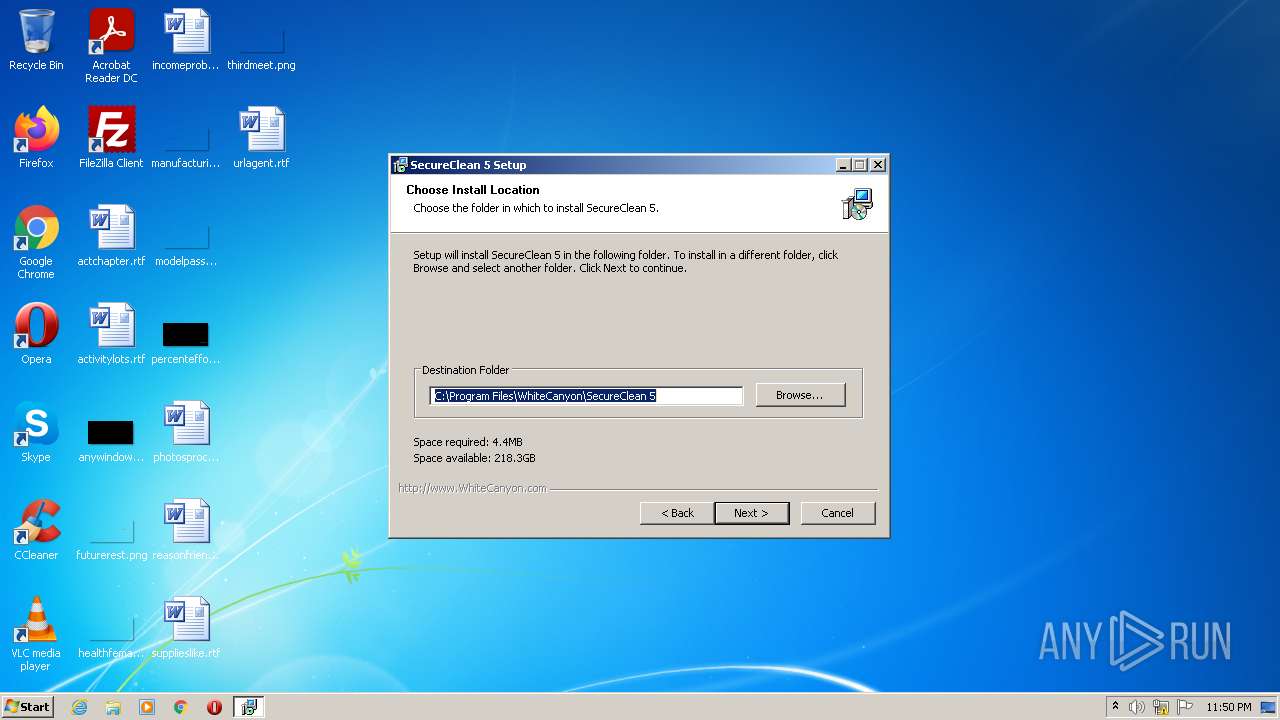
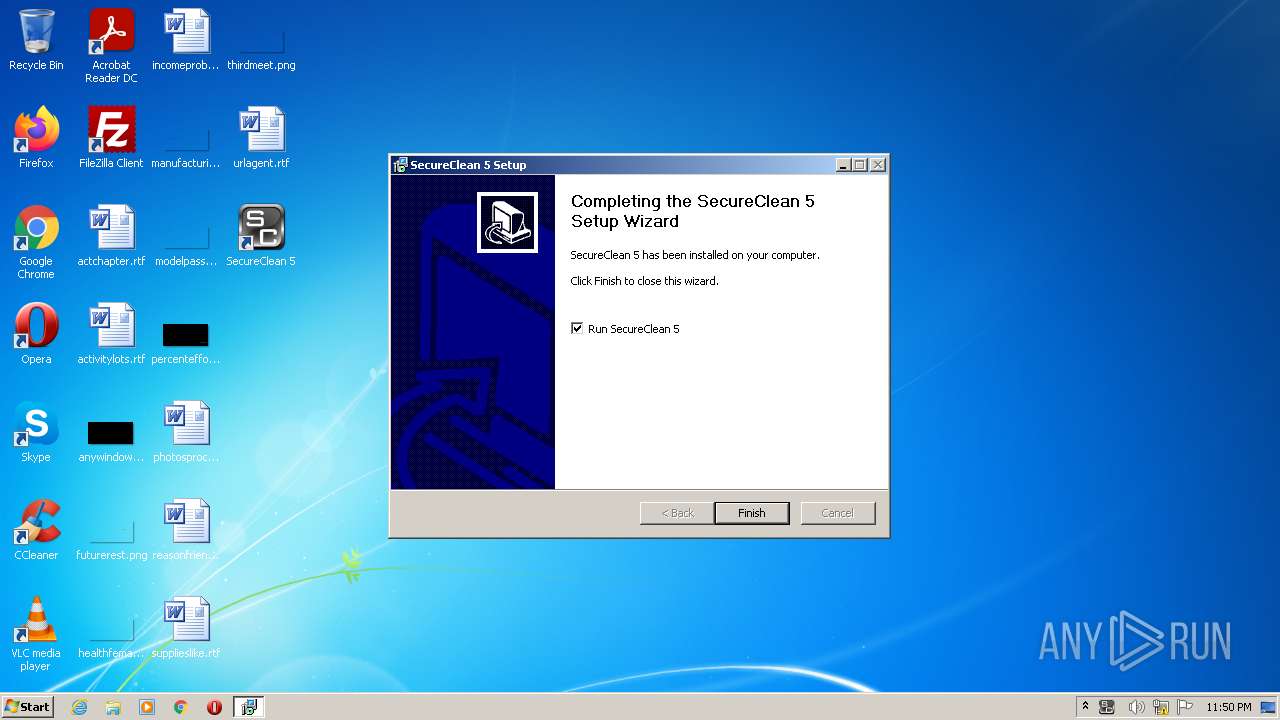
Creates a directory in Program Files
- secureclean-dongle-setup.exe (PID: 2056)
Drops a file that was compiled in debug mode
- KeylokInstall.exe (PID: 1372)
- DPInst.exe (PID: 1252)
- DrvInst.exe (PID: 568)
- secureclean-dongle-setup.exe (PID: 2056)
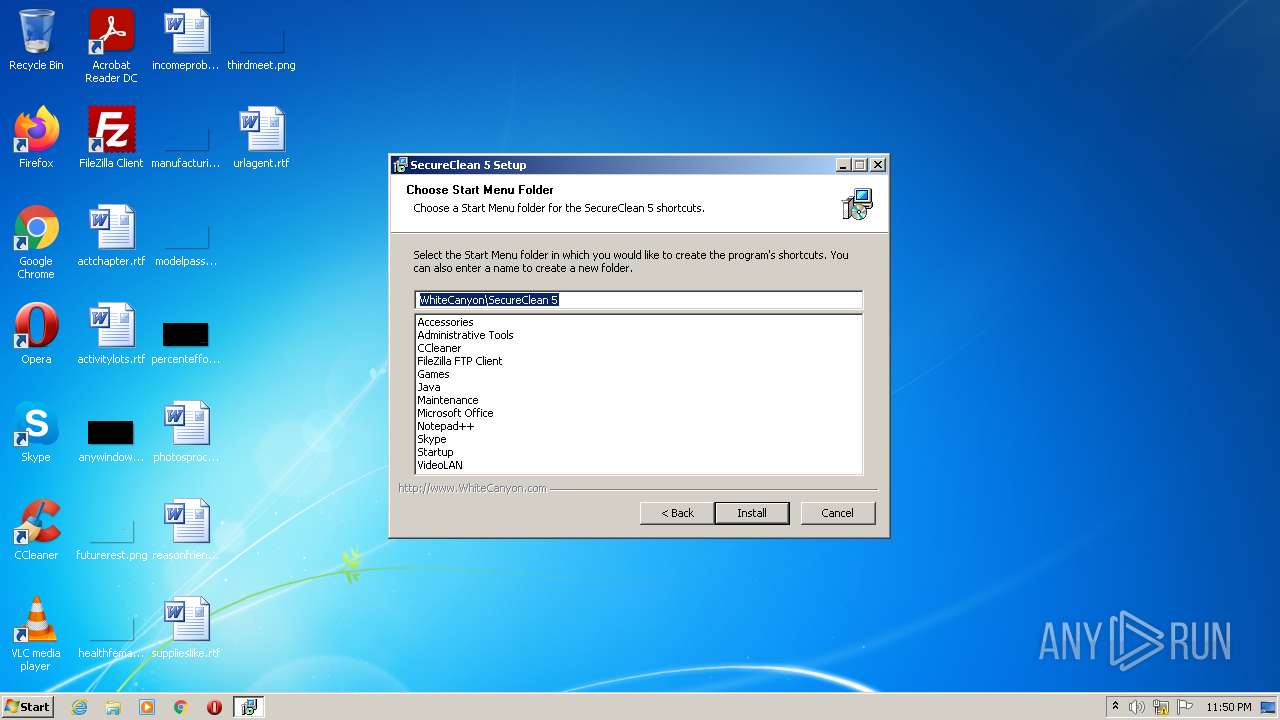
Creates a software uninstall entry
- KeylokInstall.exe (PID: 1372)
- secureclean-dongle-setup.exe (PID: 2056)
Executed via COM
- DrvInst.exe (PID: 568)
Removes files from Windows directory
- DrvInst.exe (PID: 568)
- SC5Service.exe (PID: 600)
Creates files in the driver directory
- DrvInst.exe (PID: 568)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 568)
Creates files in the program directory
- DPInst.exe (PID: 1252)
- secureclean-dongle-setup.exe (PID: 2056)
- SC5Service.exe (PID: 600)
Creates/Modifies COM task schedule object
- secureclean-dongle-setup.exe (PID: 2056)
Starts application with an unusual extension
- secureclean-dongle-setup.exe (PID: 2056)
Executed as Windows Service
- SC5Service.exe (PID: 600)
Reads CPU info
- SecureClean.exe (PID: 3832)
Reads the cookies of Mozilla Firefox
- SC5Service.exe (PID: 600)
Creates files in the user directory
- SC5Service.exe (PID: 600)
INFO
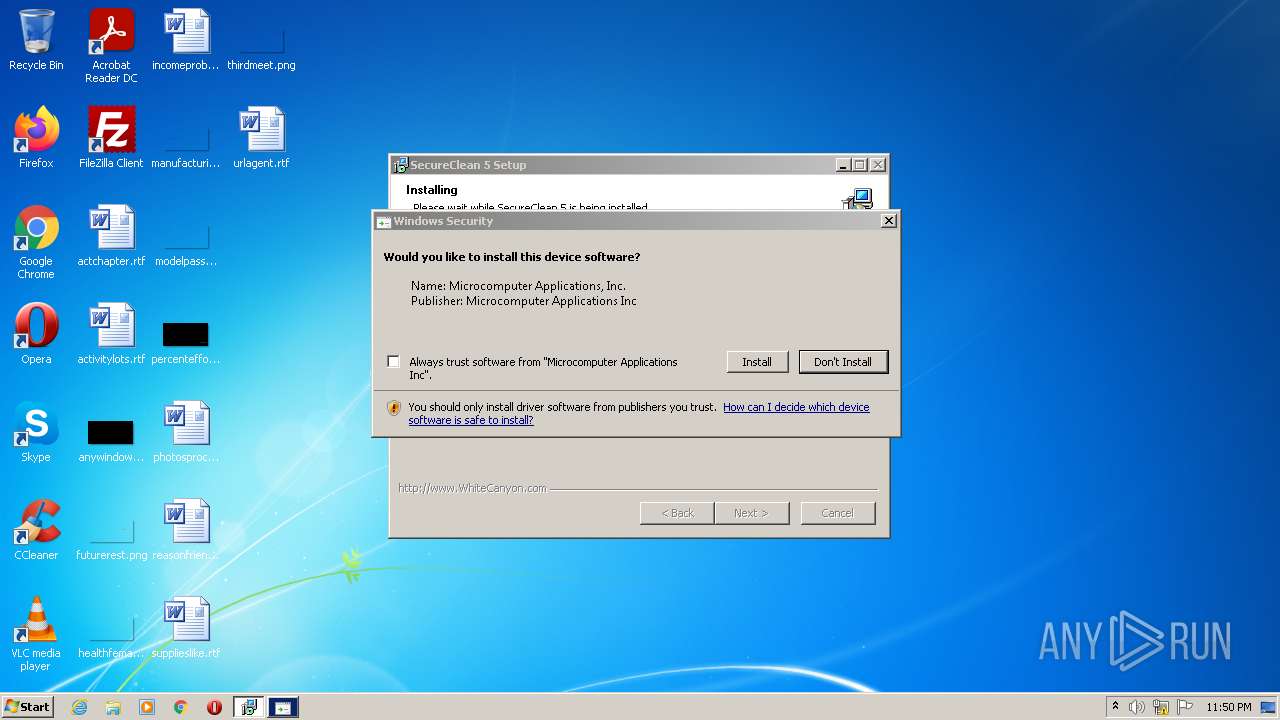
Checks Windows Trust Settings
- DrvInst.exe (PID: 568)
- rundll32.exe (PID: 2220)
- DPInst.exe (PID: 1252)
- SC5Service.exe (PID: 600)
Reads settings of System Certificates
- DrvInst.exe (PID: 568)
- DPInst.exe (PID: 1252)
- rundll32.exe (PID: 2220)
- SC5Service.exe (PID: 600)
Changes settings of System certificates
- DrvInst.exe (PID: 568)
Checks supported languages
- rundll32.exe (PID: 2220)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 568)
Reads the computer name
- rundll32.exe (PID: 2220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
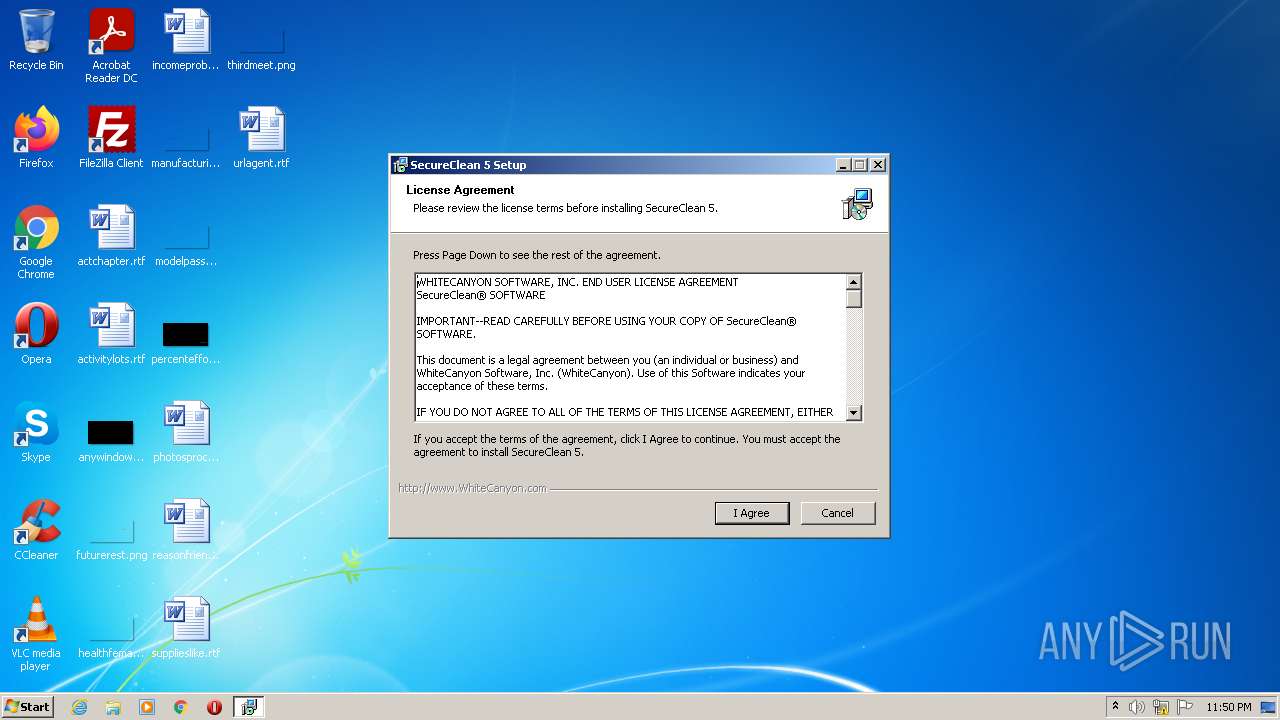
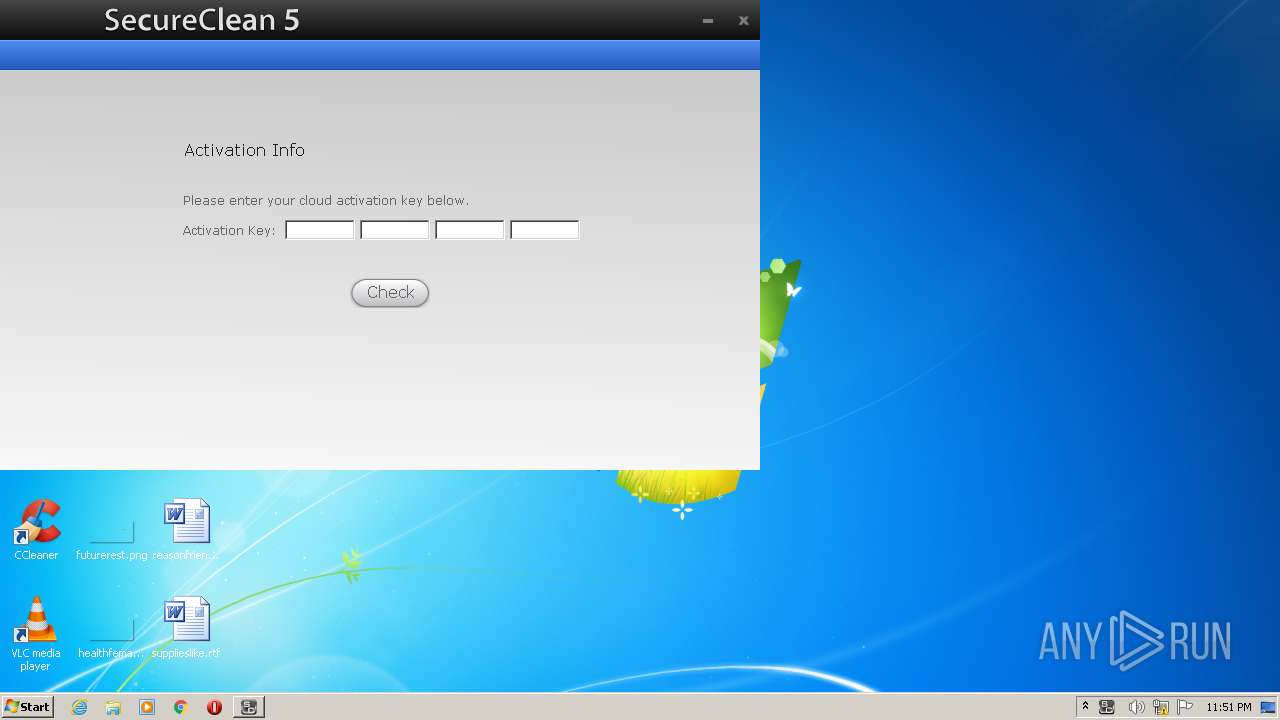
| ProductName: | SecureClean 5 |
|---|---|
| LegalTrademarks: | SecureClean 5 is a trademark of WhiteCanyon Software, Inc. |
| LegalCopyright: | © 2009-2014 WhiteCanyon Software, Inc. |
| FileVersion: | 5.6.0.0 |
| FileDescription: | SecureClean 5 Setup |
| CompanyName: | WhiteCanyon Software, Inc. |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 5.6.0.0 |
| FileVersionNumber: | 5.6.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x323c |
| UninitializedDataSize: | 1024 |
| InitializedDataSize: | 119808 |
| CodeSize: | 23552 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2009:12:05 23:50:46+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:46 |
| Detected languages: |
|
| CompanyName: | WhiteCanyon Software, Inc. |
| FileDescription: | SecureClean 5 Setup |
| FileVersion: | 5.6.0.0 |
| LegalCopyright: | © 2009-2014 WhiteCanyon Software, Inc. |
| LegalTrademarks: | SecureClean 5 is a trademark of WhiteCanyon Software, Inc. |
| ProductName: | SecureClean 5 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005A5A | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4177 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18163 |
.data | 0x00009000 | 0x0001AF98 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.70903 |
.ndata | 0x00024000 | 0x00014000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00038000 | 0x000021B8 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.4581 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21482 | 958 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 3.25755 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.64576 | 62 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.92787 | 238 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
52
Monitored processes
13
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 520 | "C:\Users\admin\AppData\Local\Temp\secureclean-dongle-setup.exe" | C:\Users\admin\AppData\Local\Temp\secureclean-dongle-setup.exe | — | Explorer.EXE | |||||||||||
User: admin Company: WhiteCanyon Software, Inc. Integrity Level: MEDIUM Description: SecureClean 5 Setup Exit code: 3221226540 Version: 5.6.0.0 Modules
| |||||||||||||||
| 568 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{163788da-a74f-7f3f-9256-75744fa73f7f}\usbkey.inf" "0" "63fcbf803" "000004D8" "WinSta0\Default" "000002C0" "208" "c:\users\admin\appdata\local\temp" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 3758096963 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 600 | "C:\Program Files\WhiteCanyon\SecureClean 5\SC5Service.exe" | C:\Program Files\WhiteCanyon\SecureClean 5\SC5Service.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 1252 | C:\Users\admin\AppData\Local\Temp\DPInst.exe /sw /se | C:\Users\admin\AppData\Local\Temp\DPInst.exe | KeylokInstall.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Driver Package Installer Exit code: 2147549184 Version: 2.1.1 Modules
| |||||||||||||||
| 1372 | C:\Users\admin\AppData\Local\Temp\KeylokInstall.exe /Q /B | C:\Users\admin\AppData\Local\Temp\KeylokInstall.exe | secureclean-dongle-setup.exe | ||||||||||||
User: admin Company: KEYLOK Integrity Level: HIGH Description: KEYLOK Security Key Install Application Exit code: 0 Version: 2014, 3, 2, 0 Modules
| |||||||||||||||
| 1872 | "SC5Service.exe" /install | C:\Program Files\WhiteCanyon\SecureClean 5\SC5Service.exe | — | ns4F69.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2056 | "C:\Users\admin\AppData\Local\Temp\secureclean-dongle-setup.exe" | C:\Users\admin\AppData\Local\Temp\secureclean-dongle-setup.exe | Explorer.EXE | ||||||||||||
User: admin Company: WhiteCanyon Software, Inc. Integrity Level: HIGH Description: SecureClean 5 Setup Exit code: 0 Version: 5.6.0.0 Modules
| |||||||||||||||
| 2220 | rundll32.exe C:\Windows\system32\pnpui.dll,InstallSecurityPromptRunDllW 20 Global\{4891cd65-ff0b-462d-1fe3-aa34e9a18542} Global\{4d7bb4db-12d5-7768-a113-eb6b07b05b2d} C:\Windows\System32\DriverStore\Temp\{7f1c2b1b-9f99-5044-498e-372bfae88d4c}\usbkey.inf C:\Windows\System32\DriverStore\Temp\{7f1c2b1b-9f99-5044-498e-372bfae88d4c}\usbkey.cat | C:\Windows\system32\rundll32.exe | — | DrvInst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3568 | "C:\Users\admin\AppData\Local\Temp\nsjF969.tmp\ns4F69.tmp" "SC5Service.exe" /install | C:\Users\admin\AppData\Local\Temp\nsjF969.tmp\ns4F69.tmp | — | secureclean-dongle-setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3568 | "C:\Program Files\WhiteCanyon\SecureClean 5\SecureClean.exe" | C:\Program Files\WhiteCanyon\SecureClean 5\SecureClean.exe | — | secureclean-dongle-setup.exe | |||||||||||
User: admin Integrity Level: HIGH Description: SecureClean Exit code: 0 Version: 1, 0, 0, 4 Modules
| |||||||||||||||
Total events
17 512
Read events
17 413
Write events
99
Delete events
0
Modification events
| (PID) Process: | (1372) KeylokInstall.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Keylok |
| Operation: | write | Name: | DisplayName |
Value: Keylok Driver | |||
| (PID) Process: | (1372) KeylokInstall.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Keylok |
| Operation: | write | Name: | UninstallString |
Value: C:\VSS\Development\SingleFileInstall\Release\install.exe | |||
| (PID) Process: | (1252) DPInst.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1252) DPInst.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.dev.log |
Value: 4096 | |||
| (PID) Process: | (568) DrvInst.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (568) DrvInst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\742C3192E607E424EB4549542BE1BBC53E6174E2 |
| Operation: | write | Name: | Blob |
Value: 04000000010000001000000010FC635DF6263E0DF325BE5F79CD676709000000010000002A000000302806082B0601050507030206082B0601050507030306082B0601050507030406082B060105050703010F0000000100000010000000D7C63BE0837DBABF881D4FBF5F986AD8030000000100000014000000742C3192E607E424EB4549542BE1BBC53E6174E27E0000000100000008000000000010C51E92D2017A000000010000000E000000300C060A2B0601040182375E01021D000000010000001000000027B3517667331CE2C1E74002B5FF2298140000000100000014000000E27F7BD877D5DF9E0A3F9EB4CB0E2EA9EFDB6977620000000100000020000000E7685634EFACF69ACE939A6B255B7B4FABEF42935B50A265ACB5CB6027E44E7053000000010000002400000030223020060A2B0601040182375E010130123010060A2B0601040182373C0101030200C00B000000010000004600000056006500720069005300690067006E00200043006C006100730073002000330020005000750062006C006900630020005000720069006D00610072007900200043004100000019000000010000001000000091161B894B117ECDC257628DB460CC0468000000010000000800000000003DB65BD9D5012000000001000000400200003082023C308201A5021070BAE41D10D92934B638CA7B03CCBABF300D06092A864886F70D0101020500305F310B300906035504061302555331173015060355040A130E566572695369676E2C20496E632E31373035060355040B132E436C6173732033205075626C6963205072696D6172792043657274696669636174696F6E20417574686F72697479301E170D3936303132393030303030305A170D3238303830313233353935395A305F310B300906035504061302555331173015060355040A130E566572695369676E2C20496E632E31373035060355040B132E436C6173732033205075626C6963205072696D6172792043657274696669636174696F6E20417574686F7269747930819F300D06092A864886F70D010101050003818D0030818902818100C95C599EF21B8A0114B410DF0440DBE357AF6A45408F840C0BD133D9D911CFEE02581F25F72AA84405AAEC031F787F9E93B99A00AA237DD6AC85A26345C77227CCF44CC67571D239EF4F42F075DF0A90C68E206F980FF8AC235F702936A4C986E7B19A20CB53A585E73DBE7D9AFE244533DC7615ED0FA271644C652E816845A70203010001300D06092A864886F70D010102050003818100BB4C122BCF2C26004F1413DDA6FBFC0A11848CF3281C67922F7CB6C5FADFF0E895BC1D8F6C2CA851CC73D8A4C053F04ED626C076015781925E21F1D1B1FFE7D02158CD6917E3441C9C194439895CDC9C000F568D0299EDA290454CE4BB10A43DF032030EF1CEF8E8C9518CE6629FE69FC07DB7729CC9363A6B9F4EA8FF640D64 | |||
| (PID) Process: | (568) DrvInst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\742C3192E607E424EB4549542BE1BBC53E6174E2 |
| Operation: | write | Name: | Blob |
Value: 5C00000001000000040000000004000068000000010000000800000000003DB65BD9D50119000000010000001000000091161B894B117ECDC257628DB460CC040B000000010000004600000056006500720069005300690067006E00200043006C006100730073002000330020005000750062006C006900630020005000720069006D00610072007900200043004100000053000000010000002400000030223020060A2B0601040182375E010130123010060A2B0601040182373C0101030200C0620000000100000020000000E7685634EFACF69ACE939A6B255B7B4FABEF42935B50A265ACB5CB6027E44E70140000000100000014000000E27F7BD877D5DF9E0A3F9EB4CB0E2EA9EFDB69771D000000010000001000000027B3517667331CE2C1E74002B5FF22987A000000010000000E000000300C060A2B0601040182375E01027E0000000100000008000000000010C51E92D201030000000100000014000000742C3192E607E424EB4549542BE1BBC53E6174E20F0000000100000010000000D7C63BE0837DBABF881D4FBF5F986AD809000000010000002A000000302806082B0601050507030206082B0601050507030306082B0601050507030406082B0601050507030104000000010000001000000010FC635DF6263E0DF325BE5F79CD67672000000001000000400200003082023C308201A5021070BAE41D10D92934B638CA7B03CCBABF300D06092A864886F70D0101020500305F310B300906035504061302555331173015060355040A130E566572695369676E2C20496E632E31373035060355040B132E436C6173732033205075626C6963205072696D6172792043657274696669636174696F6E20417574686F72697479301E170D3936303132393030303030305A170D3238303830313233353935395A305F310B300906035504061302555331173015060355040A130E566572695369676E2C20496E632E31373035060355040B132E436C6173732033205075626C6963205072696D6172792043657274696669636174696F6E20417574686F7269747930819F300D06092A864886F70D010101050003818D0030818902818100C95C599EF21B8A0114B410DF0440DBE357AF6A45408F840C0BD133D9D911CFEE02581F25F72AA84405AAEC031F787F9E93B99A00AA237DD6AC85A26345C77227CCF44CC67571D239EF4F42F075DF0A90C68E206F980FF8AC235F702936A4C986E7B19A20CB53A585E73DBE7D9AFE244533DC7615ED0FA271644C652E816845A70203010001300D06092A864886F70D010102050003818100BB4C122BCF2C26004F1413DDA6FBFC0A11848CF3281C67922F7CB6C5FADFF0E895BC1D8F6C2CA851CC73D8A4C053F04ED626C076015781925E21F1D1B1FFE7D02158CD6917E3441C9C194439895CDC9C000F568D0299EDA290454CE4BB10A43DF032030EF1CEF8E8C9518CE6629FE69FC07DB7729CC9363A6B9F4EA8FF640D64 | |||
| (PID) Process: | (2220) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2056) secureclean-dongle-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WhiteCanyon\SecureClean 5 |
| Operation: | write | Name: | Out |
Value: 4/8/2014 | |||
| (PID) Process: | (2056) secureclean-dongle-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WhiteCanyon\SecureClean 5 |
| Operation: | write | Name: | UIL |
Value: C:\Program Files\WhiteCanyon\SecureClean 5 | |||
Executable files
46
Suspicious files
11
Text files
21
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2056 | secureclean-dongle-setup.exe | C:\Users\admin\AppData\Local\Temp\nsjF969.tmp\System.dll | executable | |
MD5:C17103AE9072A06DA581DEC998343FC1 | SHA256:DC58D8AD81CACB0C1ED72E33BFF8F23EA40B5252B5BB55D393A0903E6819AE2F | |||
| 2056 | secureclean-dongle-setup.exe | C:\Users\admin\AppData\Local\Temp\KeylokInstall.exe | executable | |
MD5:— | SHA256:— | |||
| 2056 | secureclean-dongle-setup.exe | C:\Users\admin\AppData\Local\Temp\nsjF969.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 2056 | secureclean-dongle-setup.exe | C:\Users\admin\AppData\Local\Temp\nsjF969.tmp\StartMenu.dll | executable | |
MD5:A4173B381625F9F12AADB4E1CDAEFDB8 | SHA256:7755FF2707CA19344D489A5ACEC02D9E310425FA6E100D2F13025761676B875B | |||
| 1372 | KeylokInstall.exe | C:\Users\admin\AppData\Local\Temp\usbkey64.cat | cat | |
MD5:4681CA0C10A60A8F07388ED9BF9F1A85 | SHA256:B37FF139F605E2C2AC7C2F521D1B4CFCE13DA9310546FB6E10B274EE565B0EFB | |||
| 1372 | KeylokInstall.exe | C:\Users\admin\AppData\Local\Temp\PPMON.EXE | executable | |
MD5:098247A42EA5201B16E9D14813BA3DA5 | SHA256:5C5BD7391B7B4AD47EFB06BA8F135507A601449185D52803BBFA229FD5D5C421 | |||
| 1372 | KeylokInstall.exe | C:\Users\admin\AppData\Local\Temp\Usbkey64.inf | ini | |
MD5:D3BC13764DA48DA2EF4BFBDA2FEA4811 | SHA256:2BFFFA83D8B40624EF0C5F42164F94DEE3ABA0B5B7A890EB34020DBE17406E3E | |||
| 1372 | KeylokInstall.exe | C:\Users\admin\AppData\Local\Temp\PPMON.DLL | executable | |
MD5:8F521B95A478F863209C14CFAC78B0CB | SHA256:680E686A19F2B826BFB624392F312E2097AF4EAB91FC00B73993EF1105B8D0F5 | |||
| 1372 | KeylokInstall.exe | C:\Users\admin\AppData\Local\Temp\usbkey.inf | ini | |
MD5:051A9049D768359774BE260FBB188973 | SHA256:4AE9BB3DDA966D2B714729E15BBEAB01491245E1F09BFEE6C43B2EE61A207EB0 | |||
| 1372 | KeylokInstall.exe | C:\Users\admin\AppData\Local\Temp\USBKey64.sys | executable | |
MD5:5C0087AFE5C6C2103901074CA009FF79 | SHA256:8BFFE06E6619C880A8E5EC33FC6BE74785178B02D07F5594F4DC395F79CF4224 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
5
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
600 | SC5Service.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
600 | SC5Service.exe | GET | 301 | 172.66.43.13:80 | http://www.whitecanyon.com/SecureClean5/SecureClean5_dongle_version.dat | US | html | 155 b | whitelisted |
600 | SC5Service.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?2881c27d8c88ca34 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
600 | SC5Service.exe | 172.66.43.13:80 | www.whitecanyon.com | — | US | unknown |
600 | SC5Service.exe | 172.66.43.13:443 | www.whitecanyon.com | — | US | unknown |
600 | SC5Service.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
600 | SC5Service.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
600 | SC5Service.exe | 172.66.40.243:443 | www.whitecanyon.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.whitecanyon.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
download.whitecanyon.com |
| unknown |