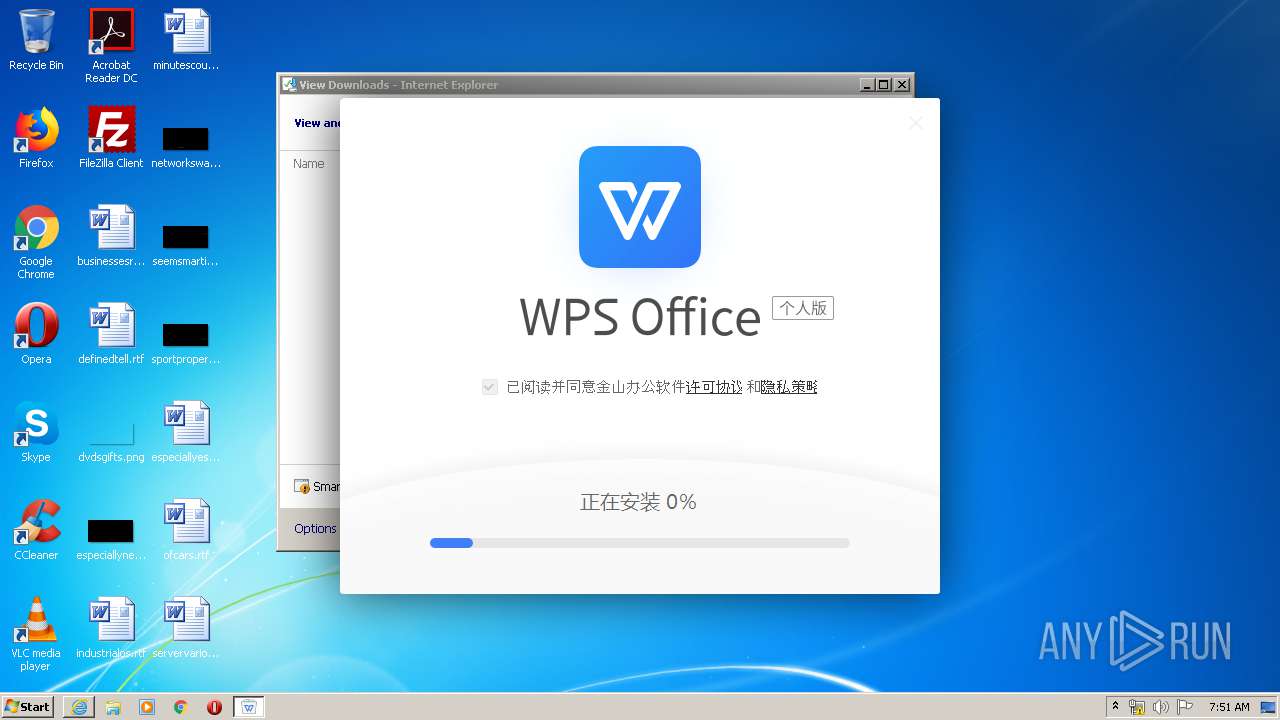
| URL: | http://dl.softmgr.qq.com/original/Office/W.P.S.9339.50.517.exe |
| Full analysis: | https://app.any.run/tasks/f0011864-e930-4018-9ec8-5951ea96b813 |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2020, 07:49:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9D7828F4C3F2897469222F21DFE473CA |
| SHA1: | E6287B694A29BC6BE194305B047B4654E2D6185C |
| SHA256: | 51EAF6EDAAB3E9802B83DDB46A12A631D4E11893767786CC98E87AC5DDC29956 |
| SSDEEP: | 3:N1KaJpNf0K6XeEDDDMj2S2:CaJpNb6Xewo2 |
MALICIOUS
Loads dropped or rewritten executable
- W.P.S.9339.50.517.exe (PID: 2588)
- wpscloudsvr.exe (PID: 2876)
- ksomisc.exe (PID: 3644)
- ksomisc.exe (PID: 3152)
- ksomisc.exe (PID: 3704)
- ksomisc.exe (PID: 3404)
- ksomisc.exe (PID: 3876)
- ksomisc.exe (PID: 3224)
- ksomisc.exe (PID: 3592)
- ksomisc.exe (PID: 580)
- ksomisc.exe (PID: 3252)
- ksomisc.exe (PID: 2056)
- regsvr32.exe (PID: 3312)
- ksomisc.exe (PID: 3332)
- ksomisc.exe (PID: 3760)
- ksomisc.exe (PID: 3344)
- ksomisc.exe (PID: 852)
- ksomisc.exe (PID: 3168)
- ksomisc.exe (PID: 2004)
- regsvr32.exe (PID: 2064)
- regsvr32.exe (PID: 3872)
- wpsupdate.exe (PID: 3580)
- wpscloudsvr.exe (PID: 3072)
- wpsupdate.exe (PID: 1296)
- wpscloudsvr.exe (PID: 180)
- ksomisc.exe (PID: 2712)
- regsvr32.exe (PID: 1016)
- svchost.exe (PID: 860)
- explorer.exe (PID: 372)
- regsvr32.exe (PID: 2600)
- regsvr32.exe (PID: 1692)
- ksomisc.exe (PID: 3740)
- ksomisc.exe (PID: 3796)
- ksomisc.exe (PID: 1412)
- regsvr32.exe (PID: 2764)
- ksomisc.exe (PID: 2388)
- wps.exe (PID: 4004)
- wps.exe (PID: 3316)
- wps.exe (PID: 3620)
- wps.exe (PID: 3832)
- ksomisc.exe (PID: 2988)
- ksomisc.exe (PID: 2312)
- wps.exe (PID: 3456)
- wps.exe (PID: 2944)
- photolaunch.exe (PID: 3552)
- ksomisc.exe (PID: 3764)
- ksolaunch.exe (PID: 3176)
- ksolaunch.exe (PID: 2472)
- ksolaunch.exe (PID: 3036)
- ksolaunch.exe (PID: 3924)
- wps.exe (PID: 3644)
- ksomisc.exe (PID: 2624)
- regsvr32.exe (PID: 2928)
- ksomisc.exe (PID: 2352)
- wps.exe (PID: 3140)
- wps.exe (PID: 2940)
- ksomisc.exe (PID: 3728)
- wps.exe (PID: 3840)
- regsvr32.exe (PID: 3148)
- promecefpluginhost.exe (PID: 4036)
- wps.exe (PID: 628)
- promecefpluginhost.exe (PID: 3664)
- wps.exe (PID: 2068)
- wps.exe (PID: 3020)
- wps.exe (PID: 3732)
- wps.exe (PID: 1732)
- wps.exe (PID: 1516)
Drops known malicious document
- W.P.S.9339.50.517.exe (PID: 2132)
Registers / Runs the DLL via REGSVR32.EXE
- ksomisc.exe (PID: 3876)
- ksomisc.exe (PID: 3168)
- W.P.S.9339.50.517.exe (PID: 2836)
- ksomisc.exe (PID: 2712)
- ksomisc.exe (PID: 2624)
- ksomisc.exe (PID: 3728)
Application was dropped or rewritten from another process
- wpscloudsvr.exe (PID: 2876)
- ksomisc.exe (PID: 3152)
- ksomisc.exe (PID: 3592)
- ksomisc.exe (PID: 3644)
- ksomisc.exe (PID: 3876)
- ksomisc.exe (PID: 3252)
- ksomisc.exe (PID: 3704)
- ksomisc.exe (PID: 852)
- ksomisc.exe (PID: 2056)
- ksomisc.exe (PID: 3332)
- ksomisc.exe (PID: 3344)
- ksomisc.exe (PID: 3760)
- ksomisc.exe (PID: 2004)
- ksomisc.exe (PID: 3168)
- ksomisc.exe (PID: 580)
- ksomisc.exe (PID: 3404)
- ksomisc.exe (PID: 3224)
- wpscloudsvr.exe (PID: 180)
- wpscloudsvr.exe (PID: 3072)
- ksomisc.exe (PID: 2712)
- ksomisc.exe (PID: 3740)
- ksomisc.exe (PID: 3796)
- ksomisc.exe (PID: 1412)
- ksomisc.exe (PID: 2388)
- wpscloudsvr.exe (PID: 3084)
- ksomisc.exe (PID: 2988)
- ksomisc.exe (PID: 2312)
- wps.exe (PID: 4004)
- wps.exe (PID: 3316)
- wps.exe (PID: 3832)
- ksolaunch.exe (PID: 3036)
- wps.exe (PID: 3620)
- wps.exe (PID: 3456)
- wps.exe (PID: 2944)
- photolaunch.exe (PID: 3552)
- ksomisc.exe (PID: 3764)
- ksolaunch.exe (PID: 3176)
- wpsupdate.exe (PID: 3580)
- ksolaunch.exe (PID: 3924)
- wps.exe (PID: 3644)
- ksomisc.exe (PID: 3728)
- wps.exe (PID: 3840)
- ksolaunch.exe (PID: 2472)
- wpsupdate.exe (PID: 1296)
- ksomisc.exe (PID: 2352)
- wps.exe (PID: 3140)
- oem_static.exe (PID: 2232)
- wps.exe (PID: 2940)
- ksomisc.exe (PID: 2624)
- promecefpluginhost.exe (PID: 4036)
- wps.exe (PID: 628)
- promecefpluginhost.exe (PID: 3664)
- wps.exe (PID: 3020)
- wps.exe (PID: 3732)
- wps.exe (PID: 1732)
- wps.exe (PID: 2068)
- wps.exe (PID: 1516)
Loads the Task Scheduler COM API
- wpsupdate.exe (PID: 1296)
- wps.exe (PID: 3620)
- wps.exe (PID: 3316)
SUSPICIOUS
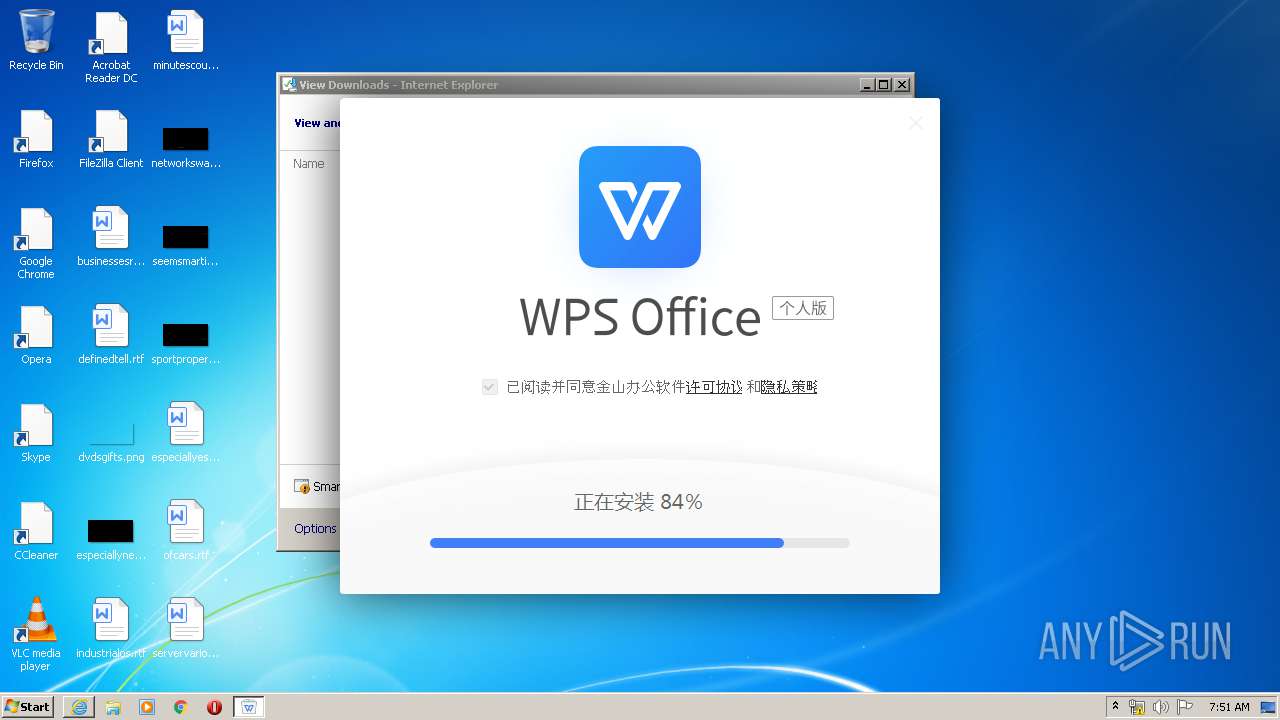
Executable content was dropped or overwritten
- W.P.S.9339.50.517.exe (PID: 2588)
- W.P.S.9339.50.517.exe (PID: 2132)
- wps.exe (PID: 3456)
- wps.exe (PID: 3140)
- wps.exe (PID: 2944)
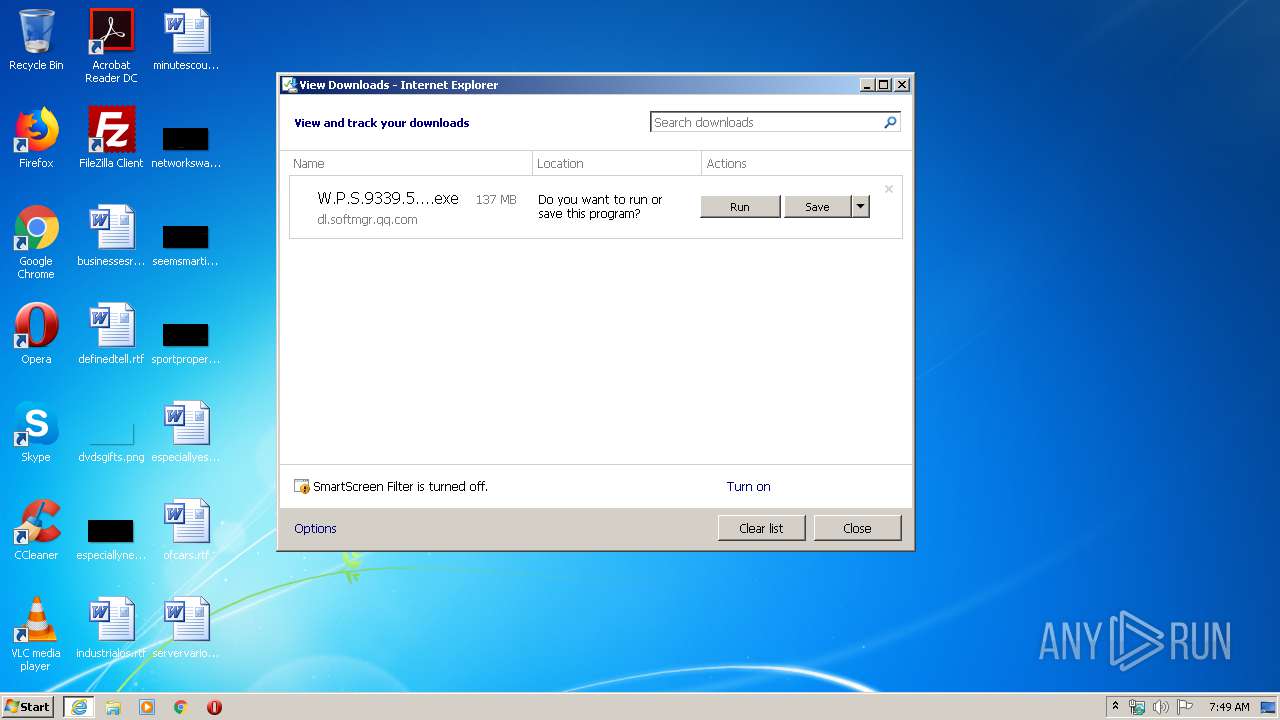
Starts Internet Explorer
- explorer.exe (PID: 372)
Creates files in the program directory
- W.P.S.9339.50.517.exe (PID: 2588)
- ksomisc.exe (PID: 580)
Creates files in the user directory
- W.P.S.9339.50.517.exe (PID: 2132)
- ksomisc.exe (PID: 3152)
- ksomisc.exe (PID: 3760)
- wpsupdate.exe (PID: 3580)
- regsvr32.exe (PID: 1016)
- ksomisc.exe (PID: 2312)
- wps.exe (PID: 2944)
- wps.exe (PID: 3140)
Creates a software uninstall entry
- W.P.S.9339.50.517.exe (PID: 2836)
Low-level read access rights to disk partition
- W.P.S.9339.50.517.exe (PID: 2132)
Modifies the open verb of a shell class
- ksomisc.exe (PID: 3876)
- ksomisc.exe (PID: 3224)
- ksomisc.exe (PID: 3704)
- ksomisc.exe (PID: 3404)
- ksomisc.exe (PID: 3252)
- W.P.S.9339.50.517.exe (PID: 2836)
- ksomisc.exe (PID: 3764)
Creates COM task schedule object
- ksomisc.exe (PID: 3876)
- regsvr32.exe (PID: 2064)
- regsvr32.exe (PID: 3872)
- regsvr32.exe (PID: 1016)
- regsvr32.exe (PID: 2600)
- regsvr32.exe (PID: 2764)
- regsvr32.exe (PID: 1692)
- regsvr32.exe (PID: 3148)
Reads Internet Cache Settings
- ksomisc.exe (PID: 3252)
- ksomisc.exe (PID: 3764)
- wps.exe (PID: 2944)
- wps.exe (PID: 3140)
Creates files in the Windows directory
- svchost.exe (PID: 860)
- cmd.exe (PID: 3592)
Application launched itself
- wps.exe (PID: 3316)
- wps.exe (PID: 2944)
Executed as Windows Service
- wpscloudsvr.exe (PID: 3084)
Starts CMD.EXE for commands execution
- wps.exe (PID: 3456)
Starts itself from another location
- wps.exe (PID: 3140)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3100)
- iexplore.exe (PID: 576)
Changes internet zones settings
- iexplore.exe (PID: 3100)
Creates files in the user directory
- iexplore.exe (PID: 3100)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3100)
Dropped object may contain Bitcoin addresses
- W.P.S.9339.50.517.exe (PID: 2132)
- wps.exe (PID: 3140)
- wps.exe (PID: 2944)
Manual execution by user
- W.P.S.9339.50.517.exe (PID: 2836)
Reads settings of System Certificates
- iexplore.exe (PID: 3100)
- wps.exe (PID: 3140)
Reads the hosts file
- wps.exe (PID: 3140)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3100)
Changes settings of System certificates
- iexplore.exe (PID: 3100)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
114
Monitored processes
75
Malicious processes
66
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | "C:\Users\admin\AppData\Local\Kingsoft\WPS Office\wpscloudsvr.exe" CheckService | C:\Users\admin\AppData\Local\Kingsoft\WPS Office\wpscloudsvr.exe | — | wpsupdate.exe | |||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS service program for service such as login and Cloud storage Exit code: 0 Version: 11,1,0,9339 Modules
| |||||||||||||||
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 576 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3100 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 580 | "C:\Users\admin\AppData\Local\Kingsoft\WPS Office\11.1.0.9339\office6\ksomisc.exe" -regmtfont | C:\Users\admin\AppData\Local\Kingsoft\WPS Office\11.1.0.9339\office6\ksomisc.exe | W.P.S.9339.50.517.exe | ||||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: HIGH Description: WPS Office Module Exit code: 0 Version: 11,1,0,9339 Modules
| |||||||||||||||
| 628 | "C:\Users\admin\AppData\Local\Kingsoft\WPSOFF~1\1110~1.933\office6\wps.exe" Run /AppUserModelID=Kingsoft.Office.cefhomepage -Entry=EntryPoint -EncodePathU8=QzpcVXNlcnNcYWRtaW5cQXBwRGF0YVxMb2NhbFxLaW5nc29mdFxXUFMgT2ZmaWNlXDExLjEuMC45MzM5XG9mZmljZTZcYWRkb25zXGtjZWZca2NlZnJlbmRlci5kbGw= -EncodePath QzpcVXNlcnNcYWRtaW5cQXBwRGF0YVxMb2NhbFxLaW5nc29mdFxXUFMgT2ZmaWNlXDExLjEuMC45MzM5XG9mZmljZTZcYWRkb25zXGtjZWZca2NlZnJlbmRlci5kbGw= -CefPluginPathU8=QzpcVXNlcnNcYWRtaW5cQXBwRGF0YVxMb2NhbFxLaW5nc29mdFxXUFMgT2ZmaWNlXDExLjEuMC45MzM5XG9mZmljZTZcYWRkb25zXGNlZg== -CefPluginPath=QzpcVXNlcnNcYWRtaW5cQXBwRGF0YVxMb2NhbFxLaW5nc29mdFxXUFMgT2ZmaWNlXDExLjEuMC45MzM5XG9mZmljZTZcYWRkb25zXGNlZg== -CefParentID=3140 "C:/Users/admin/AppData/Local/Kingsoft/WPS Office/11.1.0.9339/office6/promecefpluginhost.exe" --type=renderer --no-sandbox --js-flags=--expose-gc --service-pipe-token=8933209400162340913 --lang=zh-CN --no-zygote --log-file="C:\Users\admin\AppData\Local\Kingsoft\WPS Office\11.1.0.9339\office6\debug.log" --log-severity=disable --disable-extensions --disable-pdf-extension --enable-system-flash --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8933209400162340913 --renderer-client-id=3 --mojo-platform-channel-handle=2536 /prefetch:1 | C:\Users\admin\AppData\Local\Kingsoft\WPSOFF~1\1110~1.933\office6\wps.exe | — | wps.exe | |||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Office Exit code: 0 Version: 11,1,0,9339 Modules
| |||||||||||||||
| 852 | "C:\Users\admin\AppData\Local\Kingsoft\WPS Office\11.1.0.9339\office6\ksomisc.exe" -checkcompatiblemso | C:\Users\admin\AppData\Local\Kingsoft\WPS Office\11.1.0.9339\office6\ksomisc.exe | W.P.S.9339.50.517.exe | ||||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Office Module Exit code: 0 Version: 11,1,0,9339 Modules
| |||||||||||||||
| 860 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1016 | "C:\Windows\system32\regsvr32.exe" /s /n /i:user "C:\Users\admin\AppData\Local\Kingsoft\WPS Office\11.1.0.9339\office6\qingnse.dll" | C:\Windows\system32\regsvr32.exe | — | ksomisc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1296 | "C:\Users\admin\AppData\Local\Kingsoft\WPS Office\11.1.0.9339\wtoolex\wpsupdate.exe" -createtask | C:\Users\admin\AppData\Local\Kingsoft\WPS Office\11.1.0.9339\wtoolex\wpsupdate.exe | W.P.S.9339.50.517.exe | ||||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Office Expansion tool Exit code: 1 Version: 11,1,0,9339 Modules
| |||||||||||||||
| 1412 | "C:\Users\admin\AppData\Local\Kingsoft\WPS Office\11.1.0.9339\\office6\ksomisc.exe" -unassoepub | C:\Users\admin\AppData\Local\Kingsoft\WPS Office\11.1.0.9339\office6\ksomisc.exe | W.P.S.9339.50.517.exe | ||||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: HIGH Description: WPS Office Module Exit code: 0 Version: 11,1,0,9339 Modules
| |||||||||||||||
Total events
24 598
Read events
8 936
Write events
13 378
Delete events
2 284
Modification events
| (PID) Process: | (3100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 4255882062 | |||
| (PID) Process: | (3100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30802553 | |||
| (PID) Process: | (3100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
282
Suspicious files
371
Text files
2 510
Unknown types
275
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 576 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\W.P.S.9339.50.517[1].exe | — | |
MD5:— | SHA256:— | |||
| 3100 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab4B83.tmp | — | |
MD5:— | SHA256:— | |||
| 3100 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar4B84.tmp | — | |
MD5:— | SHA256:— | |||
| 3100 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver4BC4.tmp | — | |
MD5:— | SHA256:— | |||
| 3100 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\3Z6FHGM4.txt | — | |
MD5:— | SHA256:— | |||
| 3100 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\J7OWZ9AF.txt | — | |
MD5:— | SHA256:— | |||
| 576 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\W.P.S.9339.50.517.exe.7fkn8kj.partial | — | |
MD5:— | SHA256:— | |||
| 3100 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF4B4670A18B7C8024.TMP | — | |
MD5:— | SHA256:— | |||
| 3100 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\W.P.S.9339.50.517.exe.7fkn8kj.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 3100 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\W.P.S.9339.50.517.exe | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
10
DNS requests
9
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
576 | iexplore.exe | GET | — | 203.205.137.101:80 | http://dl.softmgr.qq.com/original/Office/W.P.S.9339.50.517.exe | CN | — | — | malicious |
3100 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3100 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3100 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
576 | iexplore.exe | 203.205.137.101:80 | dl.softmgr.qq.com | Tencent Building, Kejizhongyi Avenue | CN | malicious |
3100 | iexplore.exe | 204.79.197.200:443 | ieonline.microsoft.com | Microsoft Corporation | US | whitelisted |
3100 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3100 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dl.softmgr.qq.com |
| malicious |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
576 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3140 | wps.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3140 | wps.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3140 | wps.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3140 | wps.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3140 | wps.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3140 | wps.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3140 | wps.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3140 | wps.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3140 | wps.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
Process | Message |
|---|---|
W.P.S.9339.50.517.exe | [kscreen] isElide:0 switchRec:0 switchRecElide:1 |
W.P.S.9339.50.517.exe | [kscreen] now screensaver is |
W.P.S.9339.50.517.exe | unregister dll path:qingshellext.dll
|
W.P.S.9339.50.517.exe | unInstall qingshellex success!
|
W.P.S.9339.50.517.exe | unregister dll path:qingshellext.dll
|
ksomisc.exe | 2020/03/25 07:51:24 I ksomisc 00000c50:00000c18 [wWinMain][ksomisc begin] cmdline:-setlng zh_CN FL:T:\rc_v11_personal_20191216_branch\Coding\support\ksomisc\ksomisc.cpp(483)
|
ksomisc.exe | 2020/03/25 07:51:24 I ksomisc 00000e3c:000006cc [wWinMain][ksomisc begin] cmdline:-setservers FL:T:\rc_v11_personal_20191216_branch\Coding\support\ksomisc\ksomisc.cpp(483)
|
ksomisc.exe | 2020/03/25 07:51:24 I ksomisc 00000f24:000004cc [wWinMain][ksomisc begin] cmdline:-register FL:T:\rc_v11_personal_20191216_branch\Coding\support\ksomisc\ksomisc.cpp(483)
|
ksomisc.exe | 2020/03/25 07:51:38 E ksomisc 00000f24:000004cc [Run]RegisterModule(0, true) faild! FL:T:\rc_v11_personal_20191216_branch\Coding\support\ksomisc\ksomisc.cpp(78)
|
ksomisc.exe | 2020/03/25 07:51:38 I ksomisc 00000244:00000d50 [wWinMain][ksomisc begin] cmdline:-regmtfont FL:T:\rc_v11_personal_20191216_branch\Coding\support\ksomisc\ksomisc.cpp(483)
|