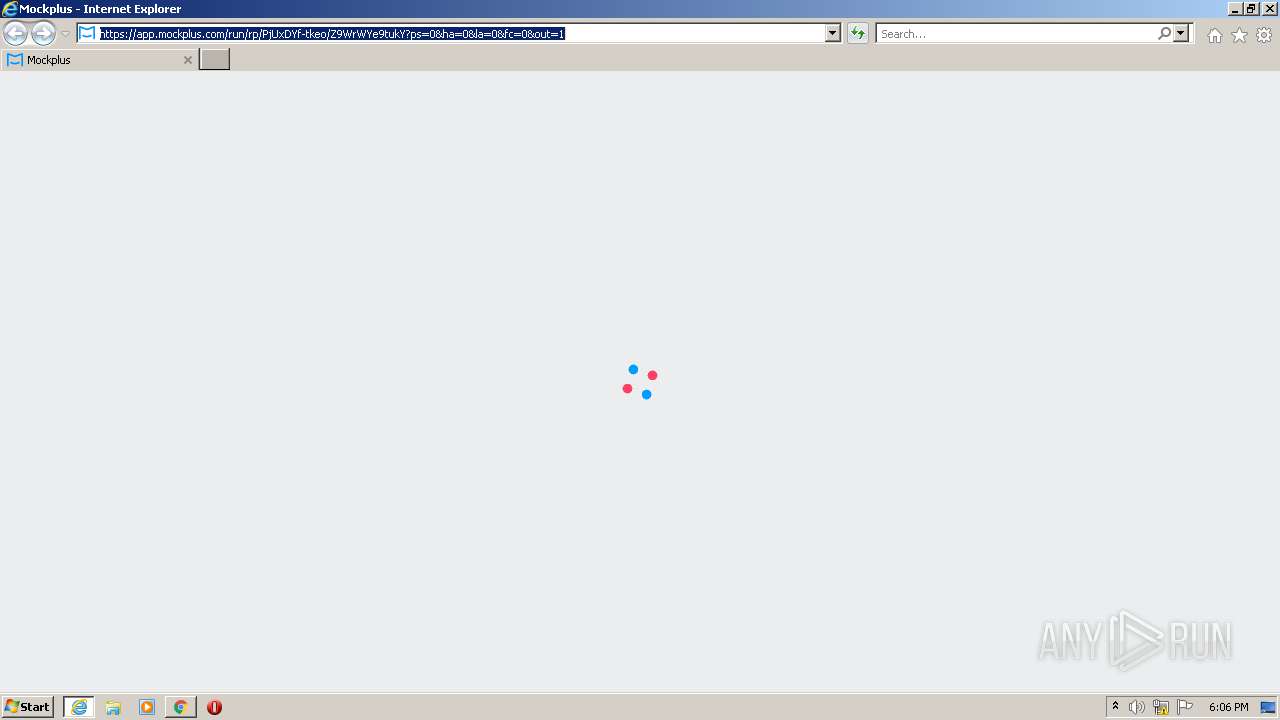
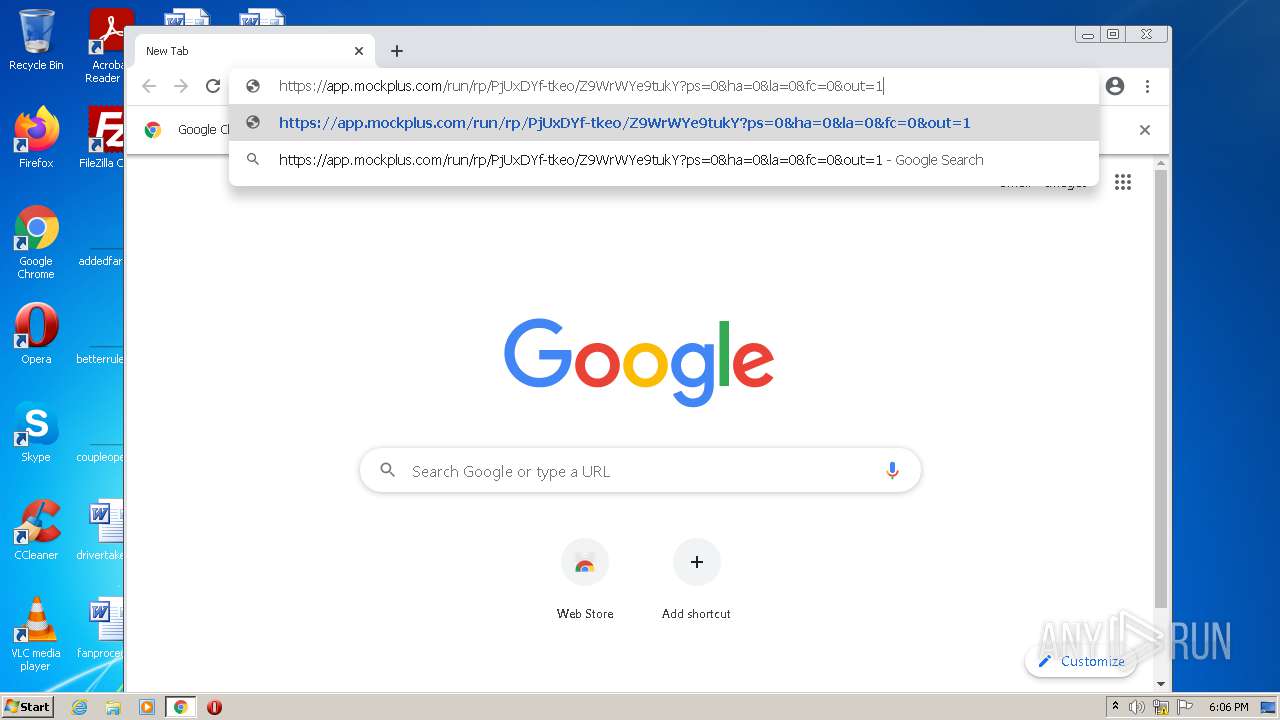
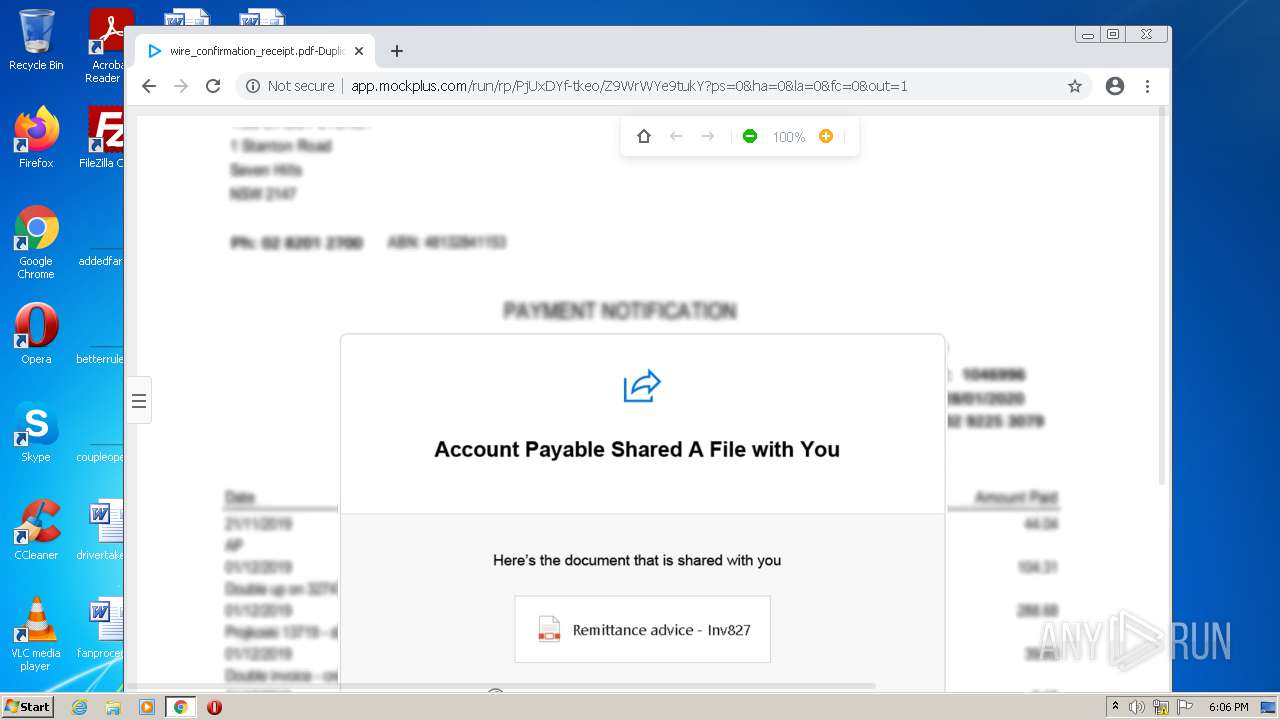
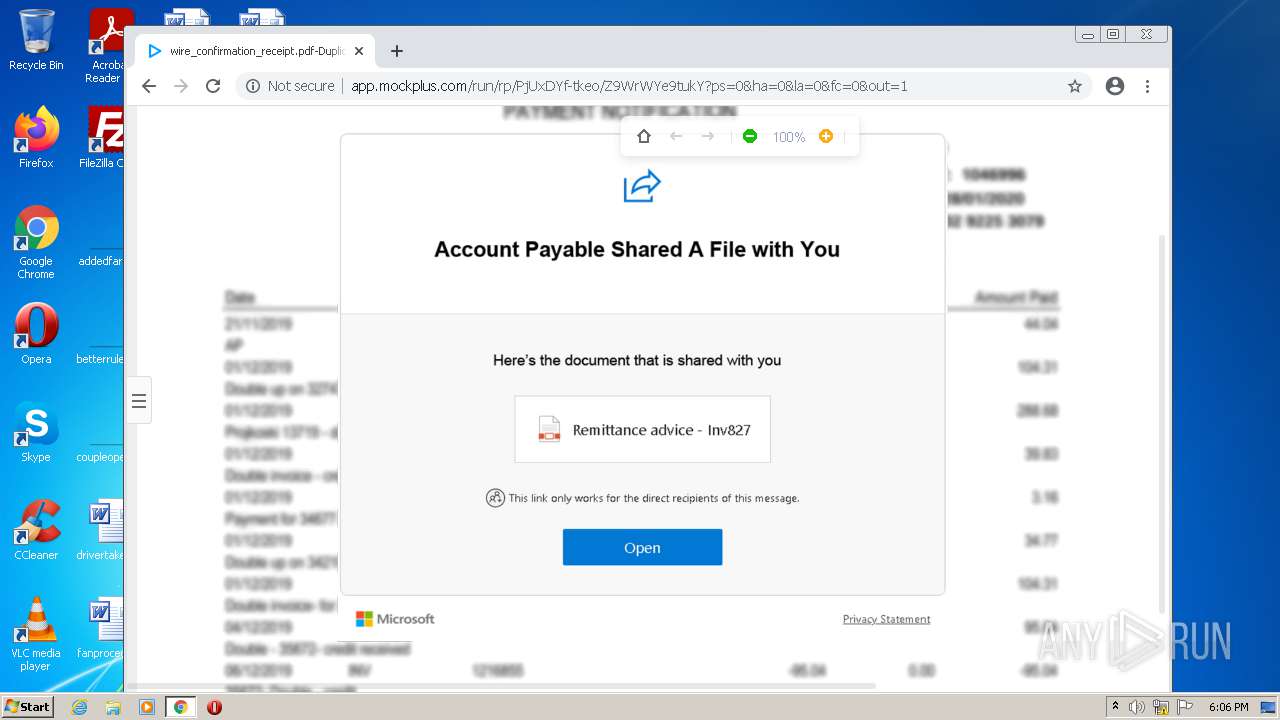
| URL: | https://app.mockplus.com/run/rp/PjUxDYf-tkeo/Z9WrWYe9tukY?ps=0&ha=0&la=0&fc=0&out=1 |
| Full analysis: | https://app.any.run/tasks/da5ba316-f325-4c6f-a5c6-87462db15f8c |
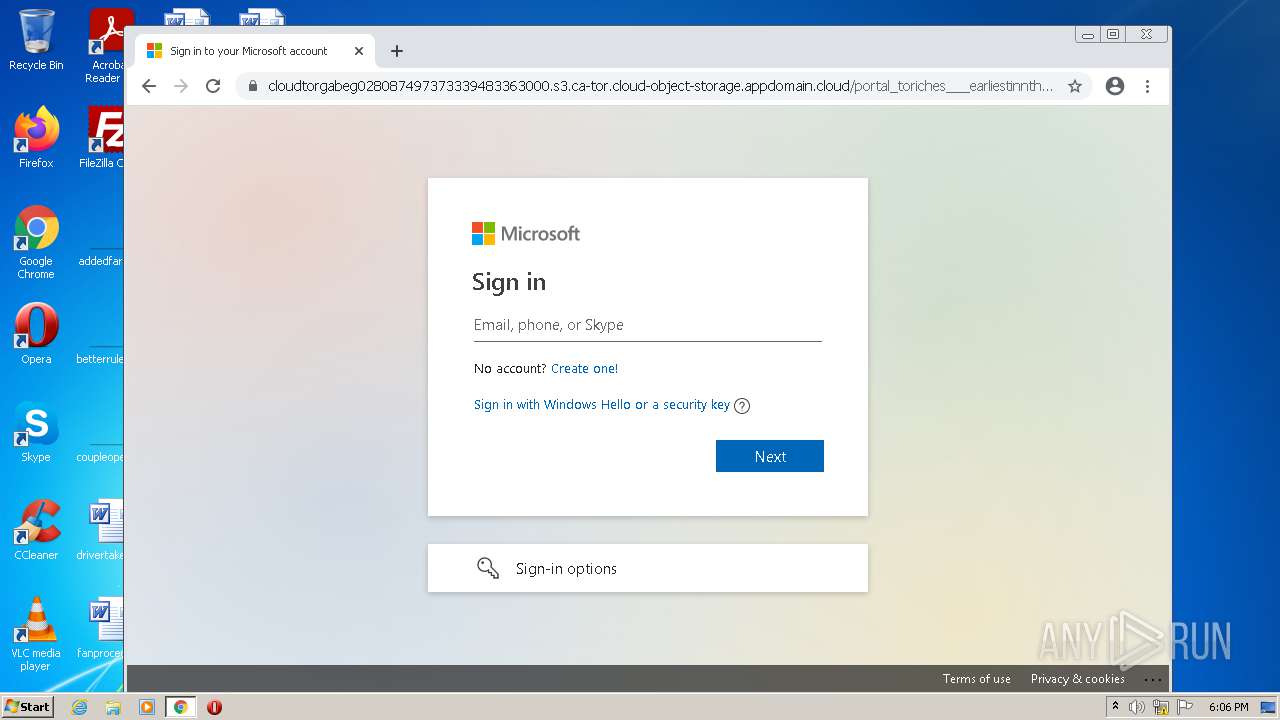
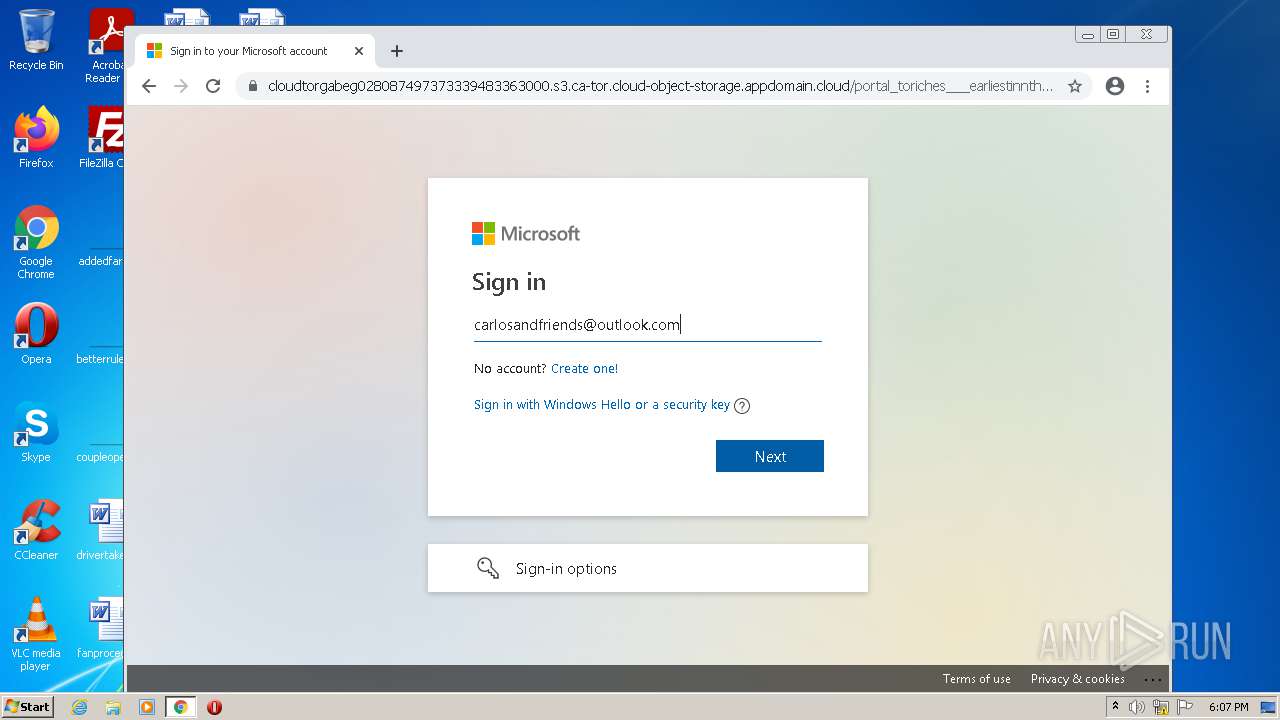
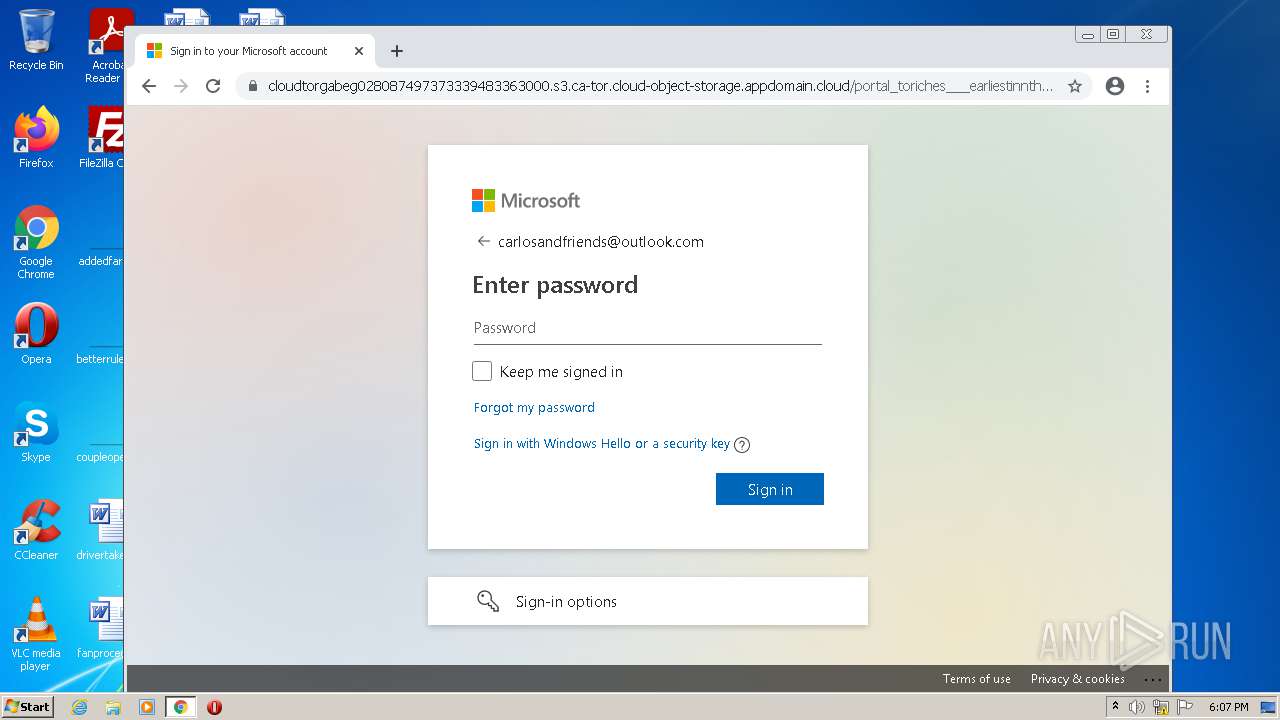
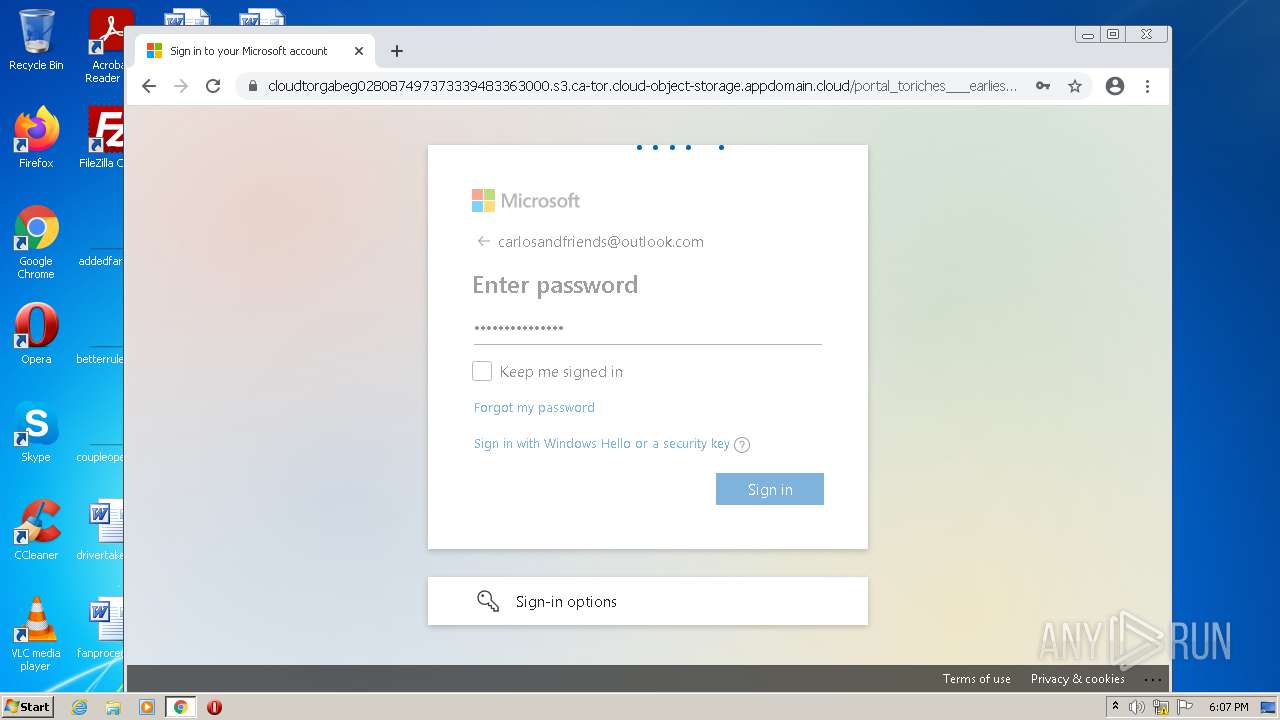
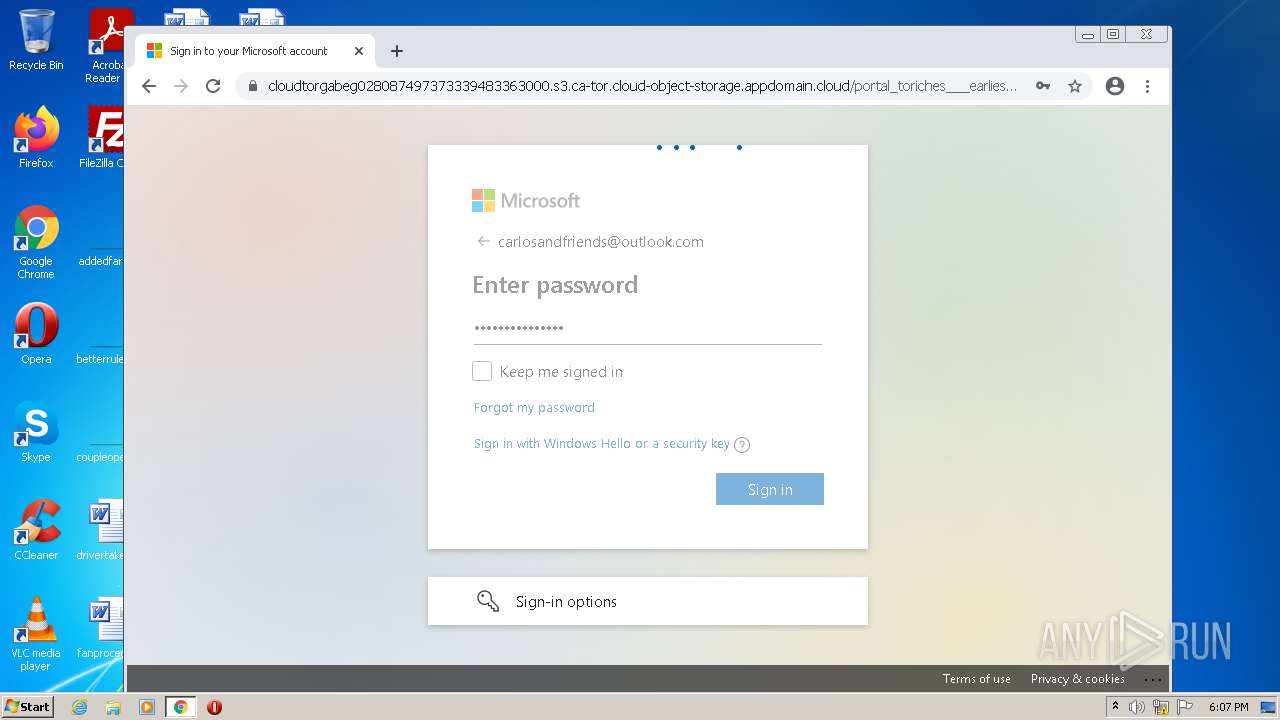
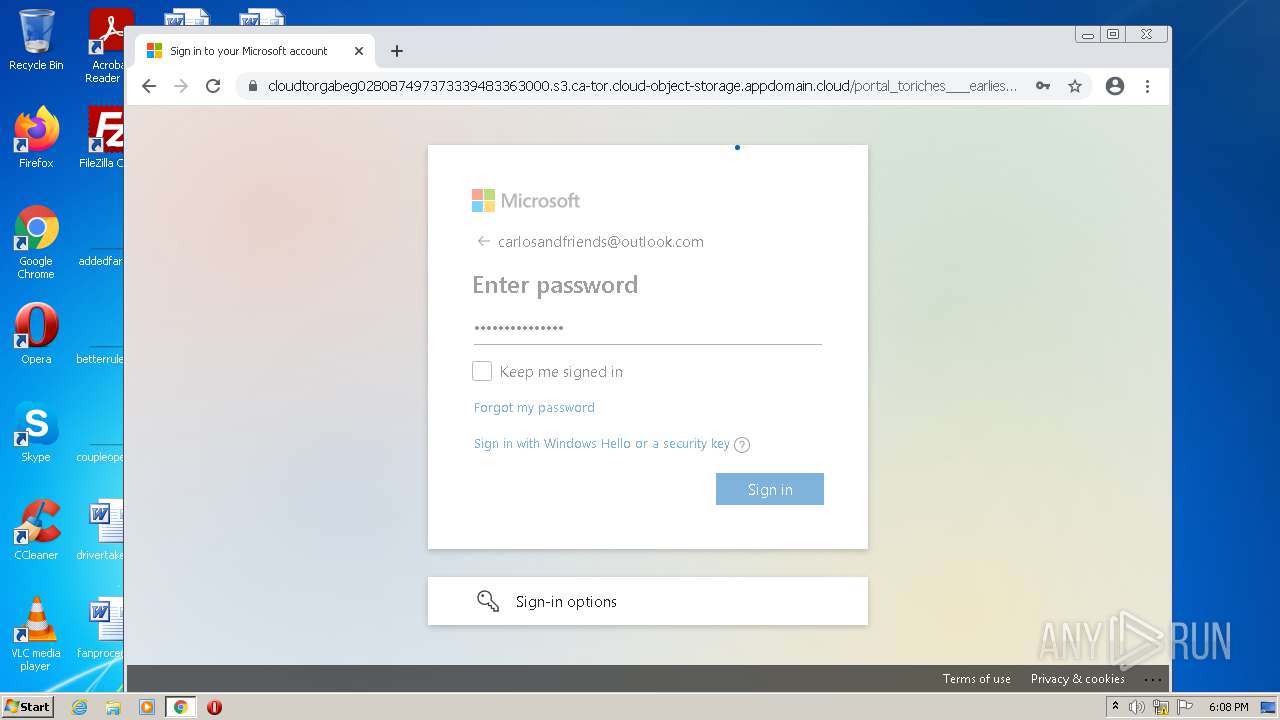
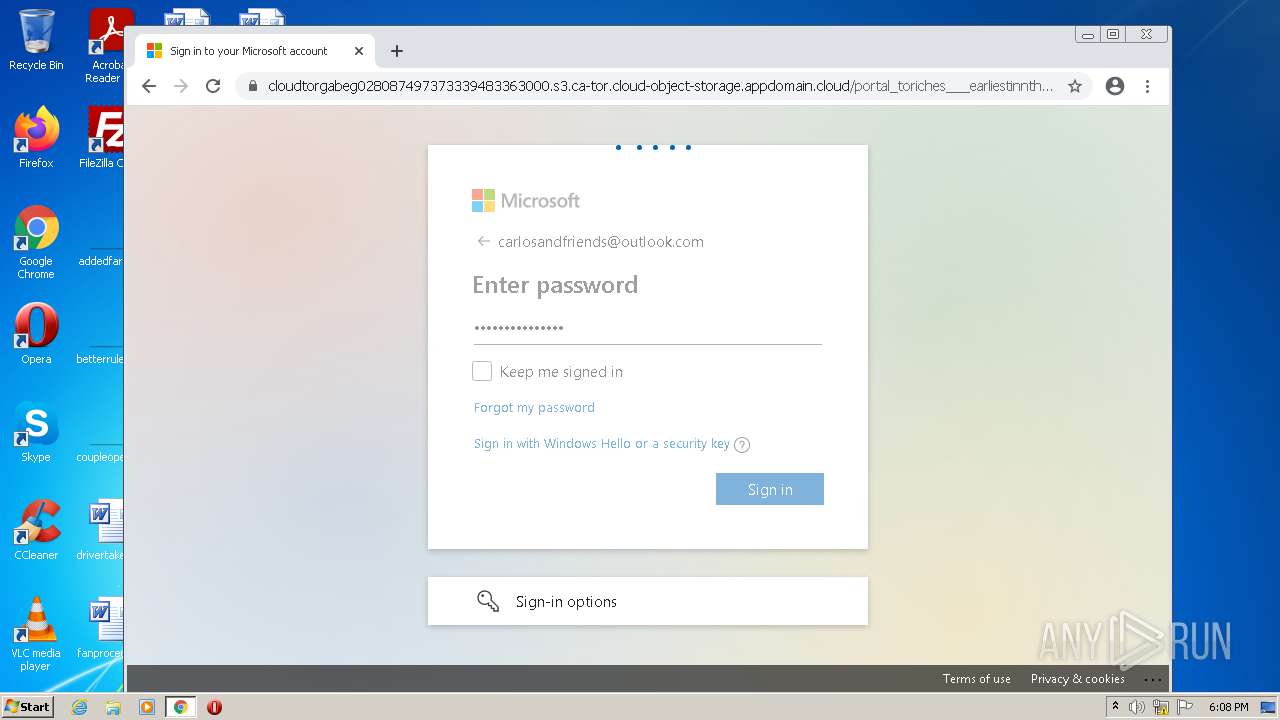
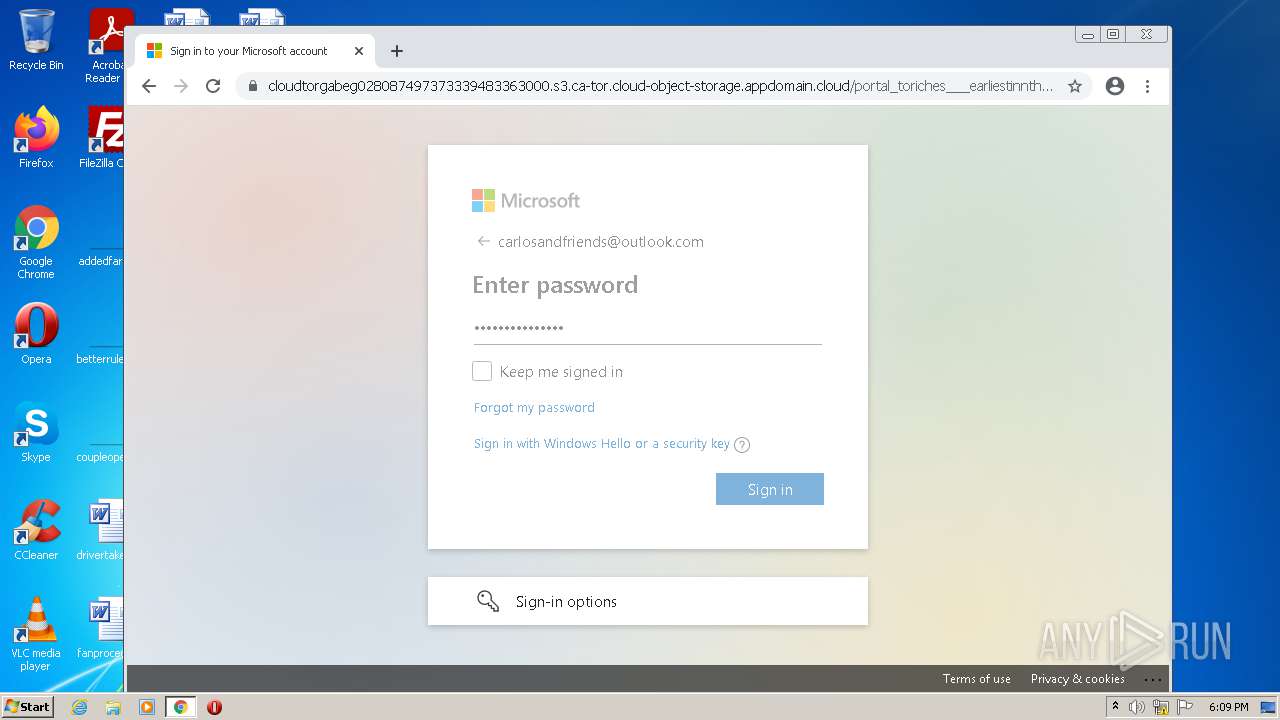
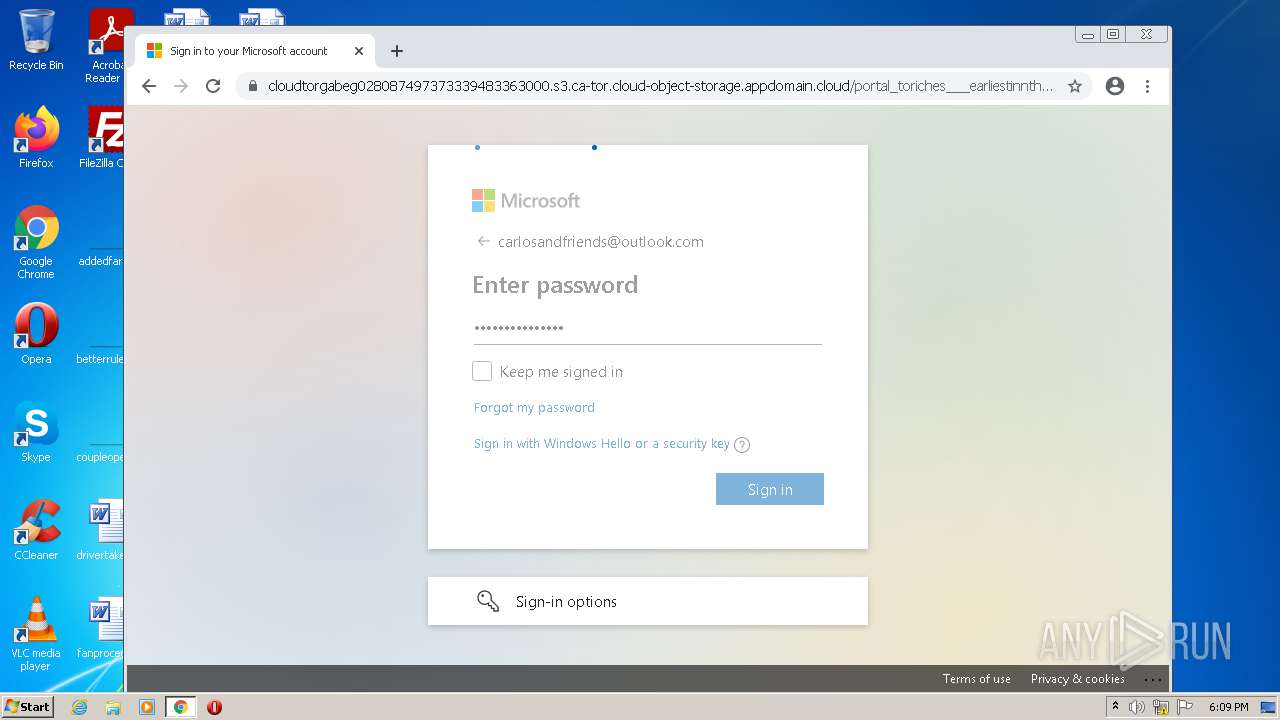
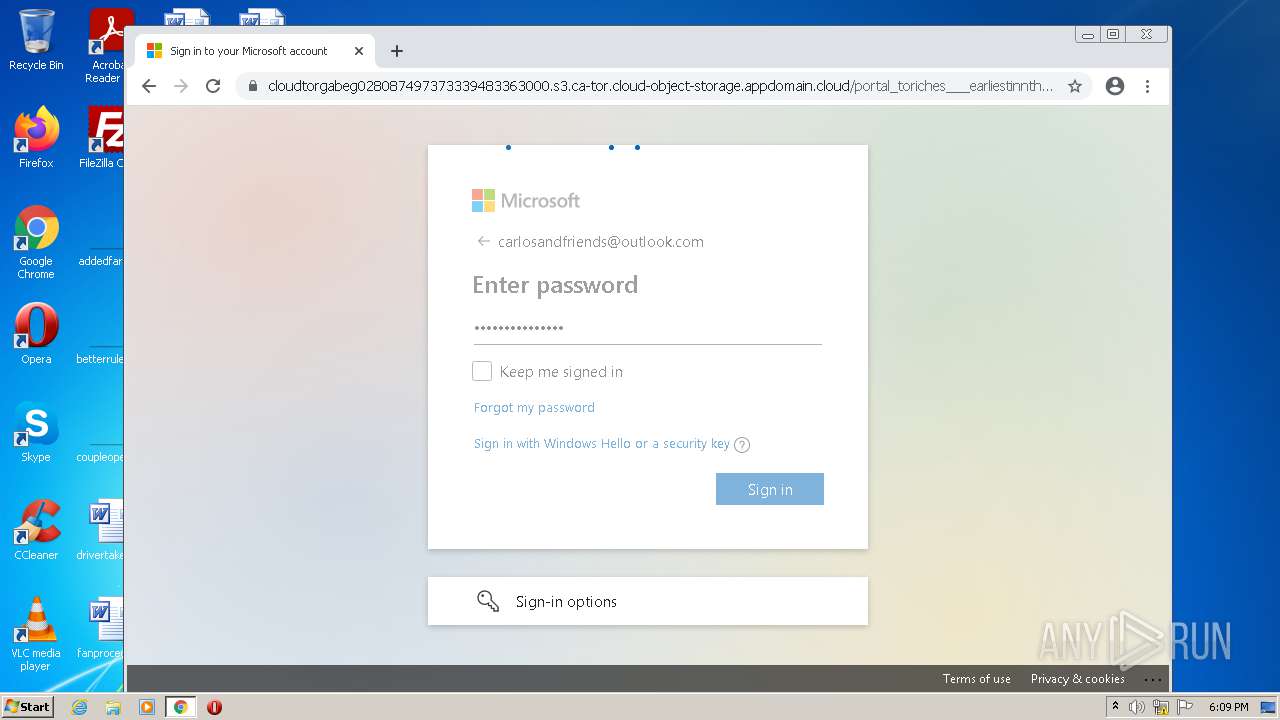
| Verdict: | Malicious activity |
| Analysis date: | June 24, 2021, 17:05:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 85F958C8DB6996C055575B3DB09789DF |
| SHA1: | B5052A3C41597AD986B20DD28031EF3685FFA5F7 |
| SHA256: | 51DB83B429FE706B20708E706F2D4FB9BA44F81BA788A0BA21B9F4A4F7E1C588 |
| SSDEEP: | 3:N8atV8A9VKFtDsvRXoab7pJFDKxUn:2atvgFx5WpJFDXn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2956)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2940)
INFO
Checks supported languages
- iexplore.exe (PID: 2956)
- iexplore.exe (PID: 2440)
- chrome.exe (PID: 2940)
- chrome.exe (PID: 3068)
- chrome.exe (PID: 1260)
- chrome.exe (PID: 3324)
- chrome.exe (PID: 2576)
- chrome.exe (PID: 1296)
- chrome.exe (PID: 3160)
- chrome.exe (PID: 2184)
- chrome.exe (PID: 2500)
- chrome.exe (PID: 1944)
- chrome.exe (PID: 3172)
- chrome.exe (PID: 1548)
- chrome.exe (PID: 1196)
- chrome.exe (PID: 1652)
- chrome.exe (PID: 1876)
- chrome.exe (PID: 2996)
- chrome.exe (PID: 908)
- chrome.exe (PID: 908)
- chrome.exe (PID: 3728)
- chrome.exe (PID: 3816)
- chrome.exe (PID: 3592)
- chrome.exe (PID: 2184)
- chrome.exe (PID: 324)
- chrome.exe (PID: 2276)
- chrome.exe (PID: 1764)
- chrome.exe (PID: 1952)
- chrome.exe (PID: 1040)
- chrome.exe (PID: 2180)
Reads the computer name
- iexplore.exe (PID: 2440)
- iexplore.exe (PID: 2956)
- chrome.exe (PID: 2940)
- chrome.exe (PID: 1260)
- chrome.exe (PID: 3324)
- chrome.exe (PID: 3172)
- chrome.exe (PID: 1196)
- chrome.exe (PID: 3592)
- chrome.exe (PID: 1040)
- chrome.exe (PID: 3728)
Application launched itself
- iexplore.exe (PID: 2440)
- chrome.exe (PID: 2940)
Changes internet zones settings
- iexplore.exe (PID: 2440)
Reads settings of System Certificates
- iexplore.exe (PID: 2956)
- iexplore.exe (PID: 2440)
- chrome.exe (PID: 1260)
Checks Windows Trust Settings
- iexplore.exe (PID: 2956)
- iexplore.exe (PID: 2440)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2440)
Reads internet explorer settings
- iexplore.exe (PID: 2956)
Changes settings of System certificates
- iexplore.exe (PID: 2440)
Manual execution by user
- chrome.exe (PID: 2940)
Reads the hosts file
- chrome.exe (PID: 2940)
- chrome.exe (PID: 1260)
Reads the date of Windows installation
- iexplore.exe (PID: 2440)
- chrome.exe (PID: 3728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
67
Monitored processes
30
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1060,15195128212543772408,585909558366628164,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2020 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1060,15195128212543772408,585909558366628164,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2020 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1060,15195128212543772408,585909558366628164,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1524 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1060,15195128212543772408,585909558366628164,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2024 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1060,15195128212543772408,585909558366628164,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3348 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1060,15195128212543772408,585909558366628164,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1324 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,15195128212543772408,585909558366628164,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1320 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1060,15195128212543772408,585909558366628164,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2816 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,15195128212543772408,585909558366628164,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3124 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1060,15195128212543772408,585909558366628164,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=496 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
27 654
Read events
27 387
Write events
254
Delete events
13
Modification events
| (PID) Process: | (2440) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2440) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 717227552 | |||
| (PID) Process: | (2440) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30894363 | |||
| (PID) Process: | (2440) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2440) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30894363 | |||
| (PID) Process: | (2440) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2440) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2440) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2440) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2440) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
91
Text files
263
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2956 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\D8555708FC41988FA4ACA22DEF9E3BE4 | der | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\loading_v2[1].gif | image | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\Z9WrWYe9tukY[1].htm | html | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\index.de330887a269783e8ca5[1].js | text | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\lib.787ef8772194366ef349[1].css | text | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\D8555708FC41988FA4ACA22DEF9E3BE4 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
87
DNS requests
57
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1796 | svchost.exe | HEAD | 200 | 74.125.97.72:80 | http://r3---sn-aigzrnld.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ?cms_redirect=yes&mh=Pe&mip=85.203.34.106&mm=28&mn=sn-aigzrnld&ms=nvh&mt=1624467613&mv=m&mvi=3&pl=24&rmhost=r1---sn-aigzrnld.gvt1.com&shardbypass=yes&smhost=r1---sn-aigzrn7s.gvt1.com | US | — | — | whitelisted |
1796 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | — | — | whitelisted |
2956 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
2440 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2956 | iexplore.exe | GET | 200 | 47.246.43.209:80 | http://img02.mockplus.cn/rp/loading_v2.gif | US | image | 13.3 Kb | whitelisted |
2956 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
1796 | svchost.exe | GET | 206 | 74.125.97.72:80 | http://r3---sn-aigzrnld.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ?cms_redirect=yes&mh=Pe&mip=85.203.34.106&mm=28&mn=sn-aigzrnld&ms=nvh&mt=1624467613&mv=m&mvi=3&pl=24&rmhost=r1---sn-aigzrnld.gvt1.com&shardbypass=yes&smhost=r1---sn-aigzrn7s.gvt1.com | US | binary | 9.62 Kb | whitelisted |
1796 | svchost.exe | GET | 206 | 74.125.97.72:80 | http://r3---sn-aigzrnld.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ?cms_redirect=yes&mh=Pe&mip=85.203.34.106&mm=28&mn=sn-aigzrnld&ms=nvh&mt=1624467613&mv=m&mvi=3&pl=24&rmhost=r1---sn-aigzrnld.gvt1.com&shardbypass=yes&smhost=r1---sn-aigzrn7s.gvt1.com | US | binary | 5.76 Kb | whitelisted |
1260 | chrome.exe | GET | 302 | 142.250.186.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 556 b | whitelisted |
2956 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQDXYzUThA2P2Frh5y8%2BHv%2Fh | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2956 | iexplore.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
2956 | iexplore.exe | 47.246.43.209:80 | img02.mockplus.cn | — | US | malicious |
2956 | iexplore.exe | 47.246.43.224:443 | s3.pstatp.com | — | US | malicious |
2956 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2956 | iexplore.exe | 47.246.43.226:443 | s3.pstatp.com | — | US | malicious |
2440 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2956 | iexplore.exe | 2.16.186.33:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
2956 | iexplore.exe | 47.246.43.223:443 | s3.pstatp.com | — | US | malicious |
2956 | iexplore.exe | 13.248.176.215:443 | app.mockplus.com | — | US | unknown |
2440 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
app.mockplus.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
img02.mockplus.cn |
| whitelisted |
s3.pstatp.com |
| whitelisted |
s0.pstatp.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
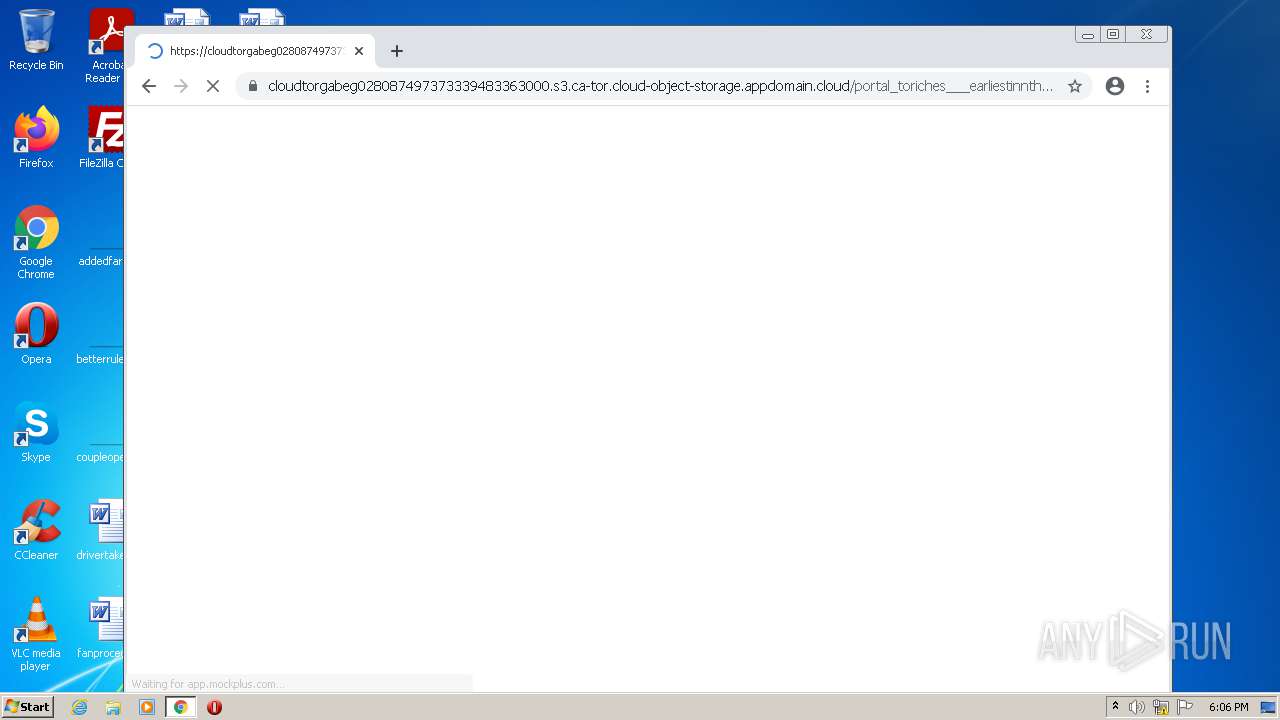
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |