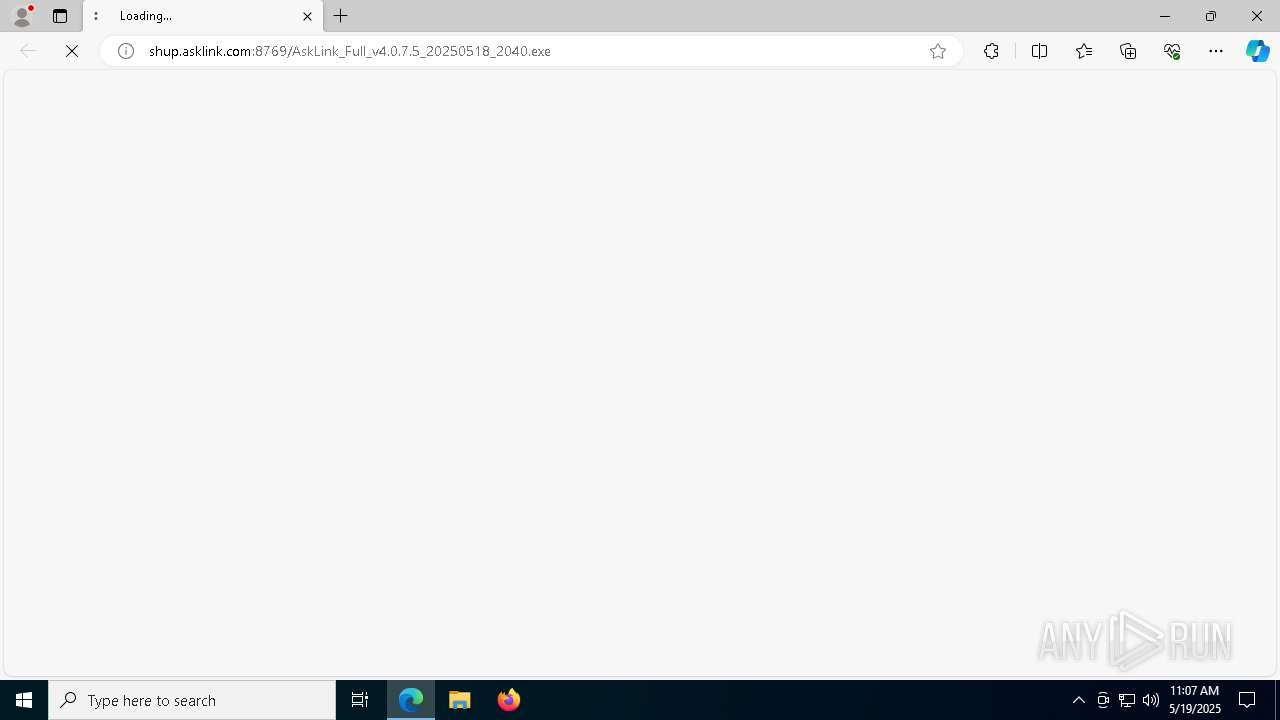
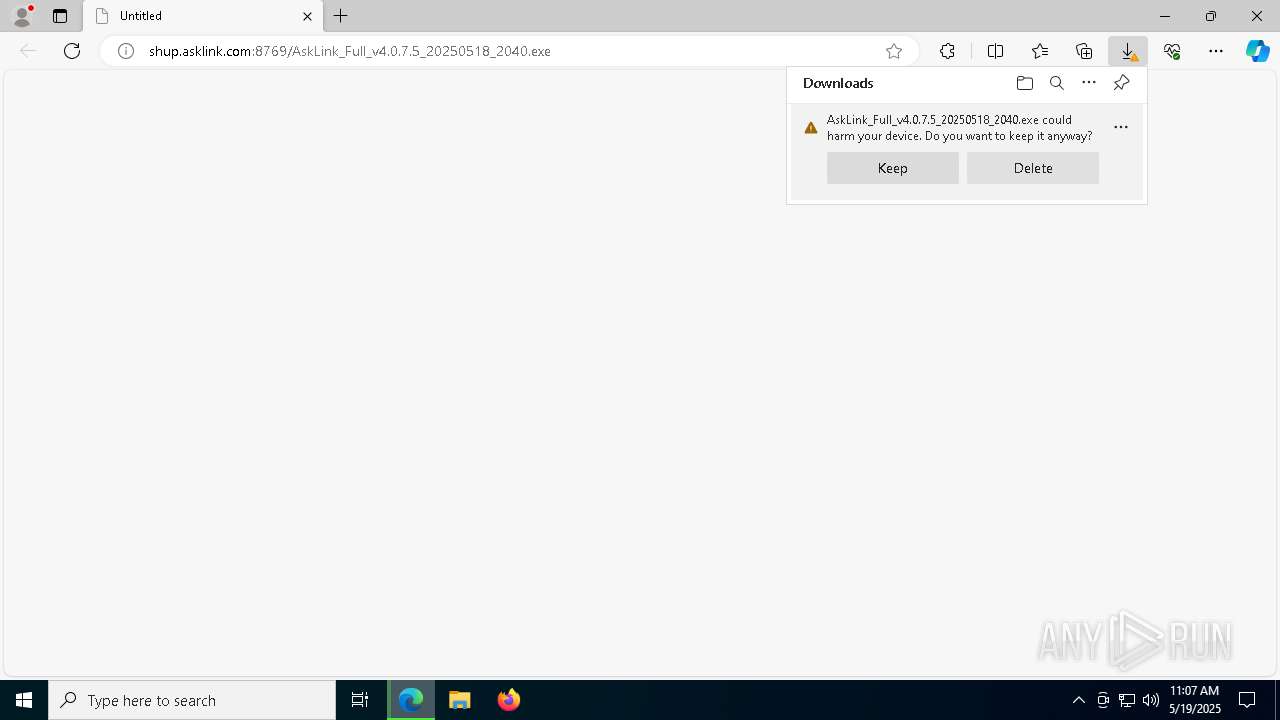
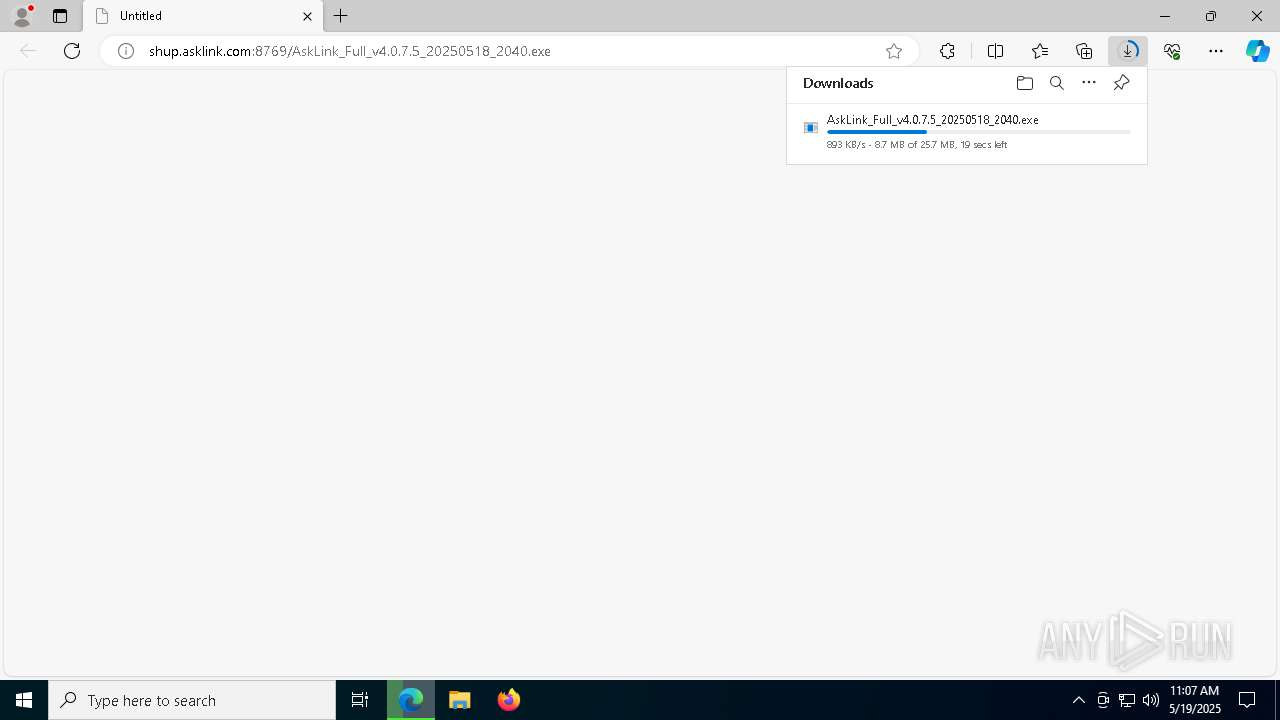
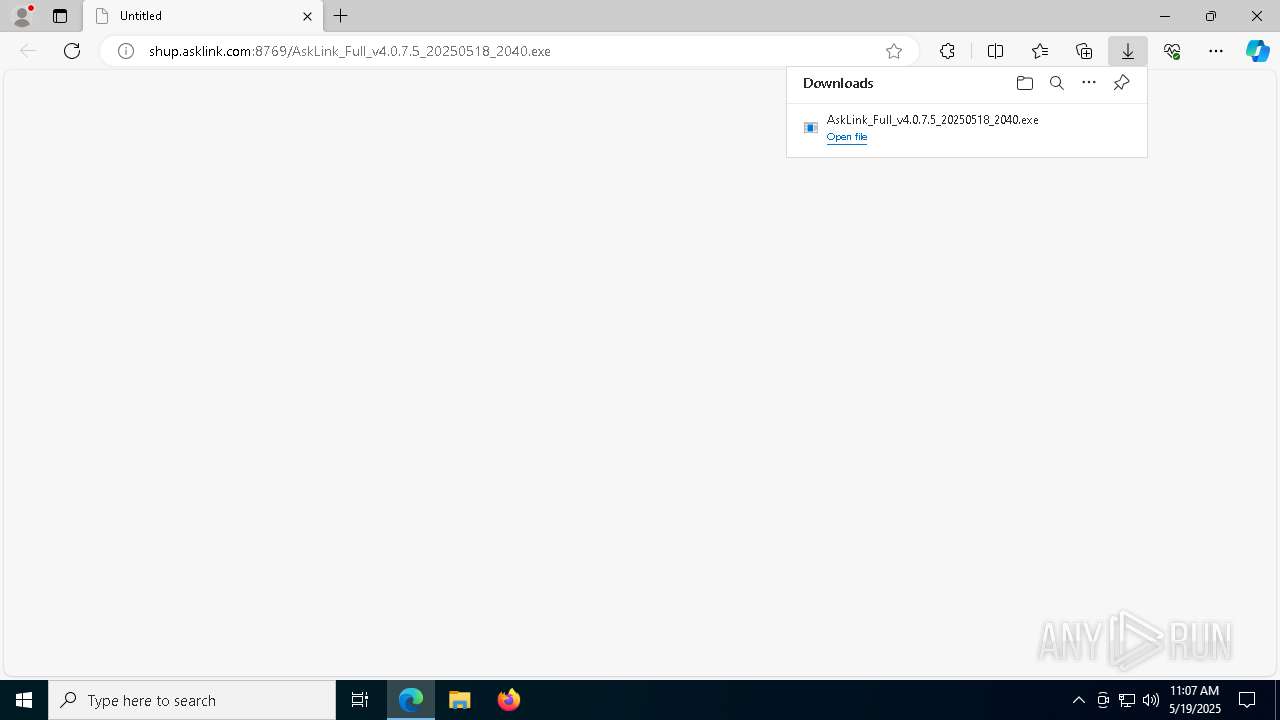
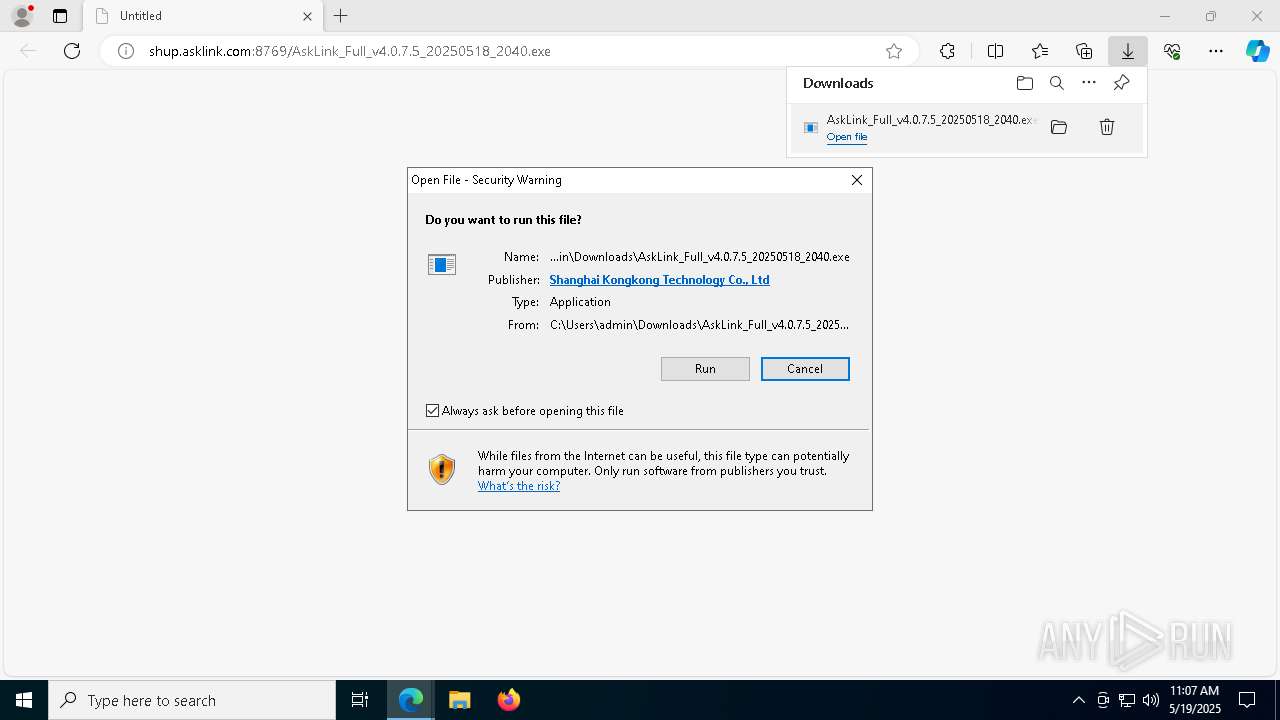
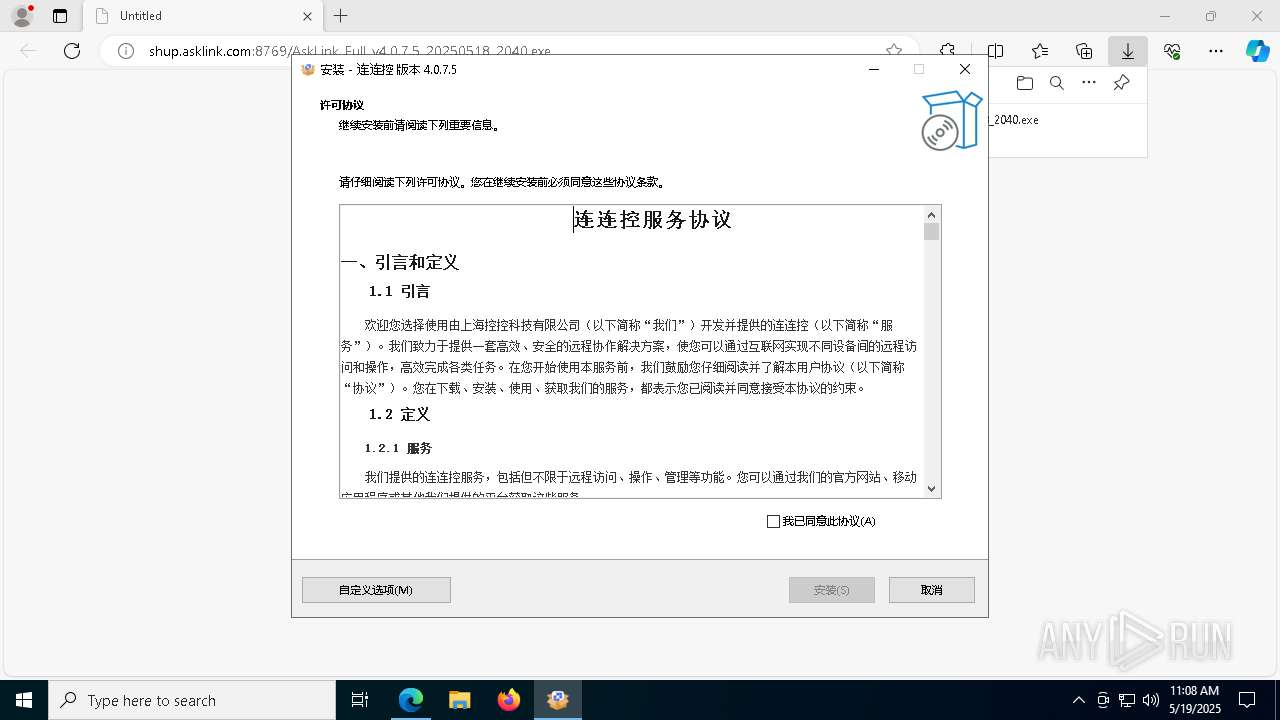
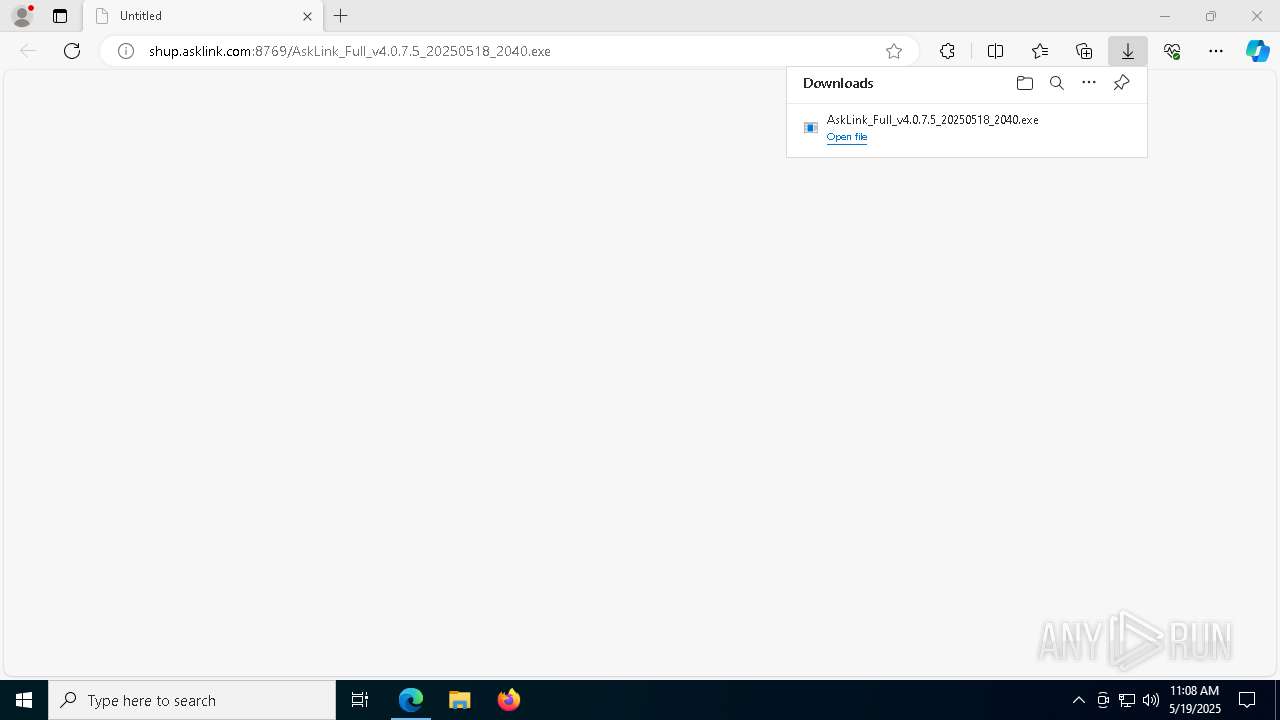
| URL: | http://shup.asklink.com:8769/AskLink_Full_v4.0.7.5_20250518_2040.exe |
| Full analysis: | https://app.any.run/tasks/e3c8afc5-a915-40ea-94ca-6e3af39124b6 |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2025, 11:07:03 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8D8A53D5DB1B0B15D5F24D3423735917 |
| SHA1: | 0741F67EE6055EFD651B9C19B5D5D218930E8A0B |
| SHA256: | 51D3ADA2DA3192D212B7F1AE4483F26A4B9A25C6746DFAC5D117072AF1F14334 |
| SSDEEP: | 3:N1KNNuEsgKfG3LOI3Jh4/EERWC:CmEBEYLJ3Jh4/EEAC |
MALICIOUS
No malicious indicators.SUSPICIOUS
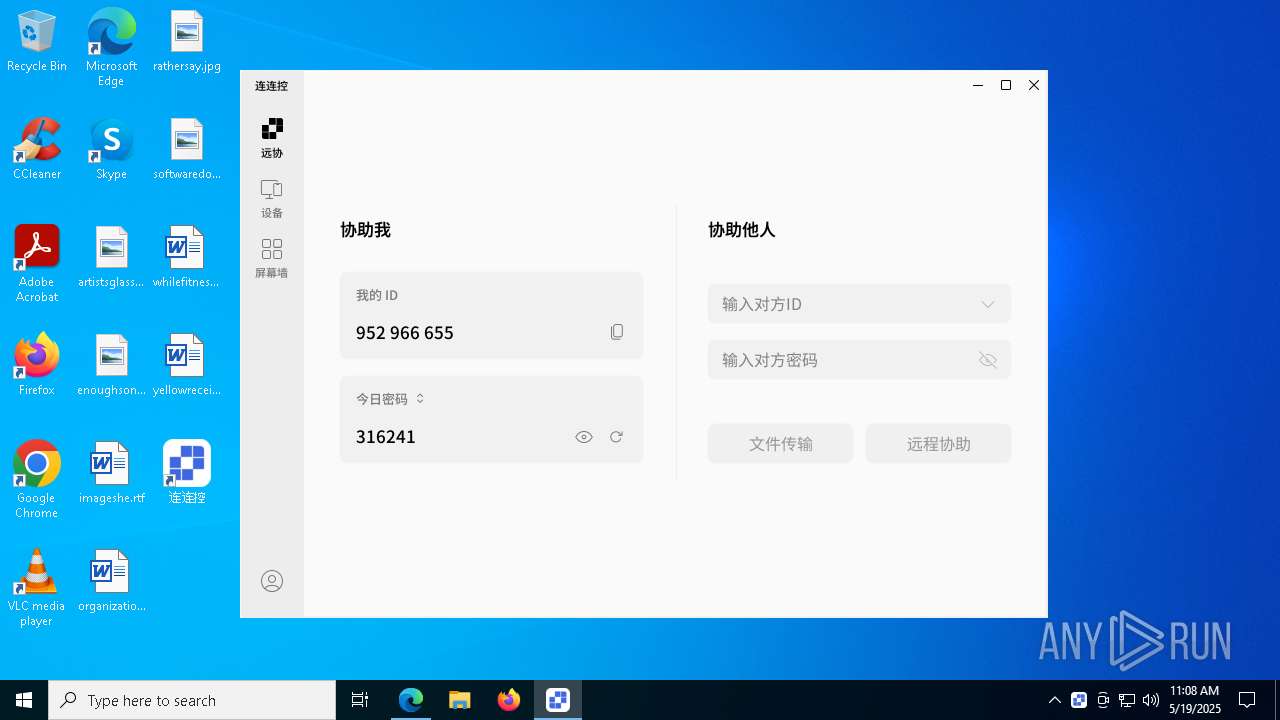
Potential Corporate Privacy Violation
- msedge.exe (PID: 7232)
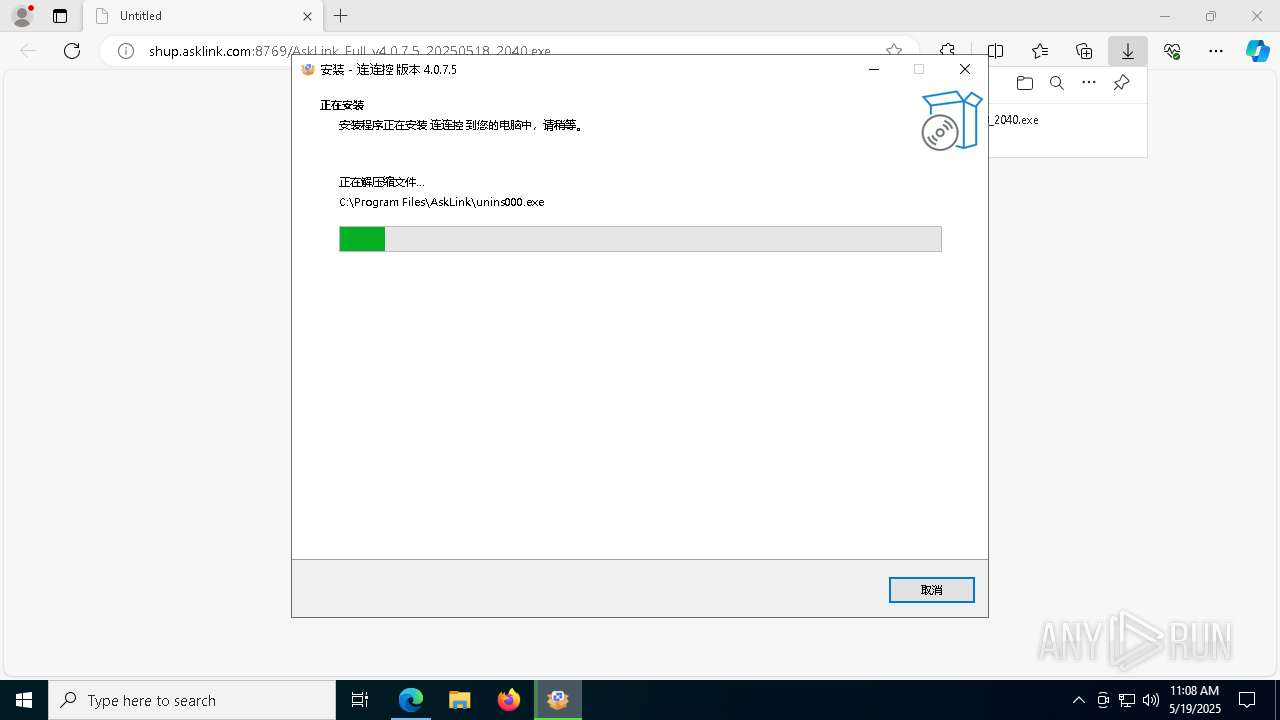
Executable content was dropped or overwritten
- AskLink_Full_v4.0.7.5_20250518_2040.exe (PID: 1676)
- AskLink_Full_v4.0.7.5_20250518_2040.exe (PID: 7000)
- AskLink_Full_v4.0.7.5_20250518_2040.tmp (PID: 4224)
- drvinst.exe (PID: 5508)
- devcon.exe (PID: 7020)
- devcon.exe (PID: 632)
- drvinst.exe (PID: 7784)
- devcon.exe (PID: 1132)
- drvinst.exe (PID: 6724)
- drvinst.exe (PID: 6416)
Reads the Windows owner or organization settings
- AskLink_Full_v4.0.7.5_20250518_2040.tmp (PID: 4224)
Starts CMD.EXE for commands execution
- AskLink_Full_v4.0.7.5_20250518_2040.tmp (PID: 4224)
- DriverTool.exe (PID: 5020)
- AskLink.exe (PID: 7760)
- AskLink.exe (PID: 8128)
Get information on the list of running processes
- AskLink_Full_v4.0.7.5_20250518_2040.tmp (PID: 4224)
- cmd.exe (PID: 1532)
- cmd.exe (PID: 2504)
- cmd.exe (PID: 7844)
- cmd.exe (PID: 7896)
Reads security settings of Internet Explorer
- AskLink_Full_v4.0.7.5_20250518_2040.tmp (PID: 4108)
- devcon.exe (PID: 7020)
- devcon.exe (PID: 632)
- devcon.exe (PID: 1132)
Drops a system driver (possible attempt to evade defenses)
- AskLink_Full_v4.0.7.5_20250518_2040.tmp (PID: 4224)
- devcon.exe (PID: 7020)
- drvinst.exe (PID: 5508)
- devcon.exe (PID: 1132)
- drvinst.exe (PID: 6724)
- drvinst.exe (PID: 6416)
Process drops legitimate windows executable
- AskLink_Full_v4.0.7.5_20250518_2040.tmp (PID: 4224)
- devcon.exe (PID: 1132)
- drvinst.exe (PID: 6724)
Creates files in the driver directory
- drvinst.exe (PID: 5508)
- drvinst.exe (PID: 7784)
- drvinst.exe (PID: 6724)
- drvinst.exe (PID: 6416)
Creates or modifies Windows services
- drvinst.exe (PID: 7580)
- drvinst.exe (PID: 7892)
- drvinst.exe (PID: 6416)
Executes as Windows Service
- WUDFHost.exe (PID: 8096)
- AskLink.exe (PID: 7760)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 924)
- cmd.exe (PID: 7632)
- cmd.exe (PID: 632)
- cmd.exe (PID: 1676)
- cmd.exe (PID: 7708)
- cmd.exe (PID: 4016)
Process uses IPCONFIG to discover network configuration
- cmd.exe (PID: 2064)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 8048)
Starts application with an unusual extension
- cmd.exe (PID: 2064)
Application launched itself
- AskLink.exe (PID: 7760)
INFO
Application launched itself
- msedge.exe (PID: 2432)
Executable content was dropped or overwritten
- msedge.exe (PID: 2432)
- msedge.exe (PID: 7232)
Connects to unusual port
- msedge.exe (PID: 7232)
Process checks computer location settings
- AskLink_Full_v4.0.7.5_20250518_2040.tmp (PID: 4108)
Checks supported languages
- AskLink_Full_v4.0.7.5_20250518_2040.exe (PID: 7000)
- AskLink_Full_v4.0.7.5_20250518_2040.exe (PID: 1676)
- AskLink_Full_v4.0.7.5_20250518_2040.tmp (PID: 4108)
- AskLink_Full_v4.0.7.5_20250518_2040.tmp (PID: 4224)
- DriverTool.exe (PID: 5020)
- devcon.exe (PID: 5512)
- devcon.exe (PID: 7020)
- drvinst.exe (PID: 5508)
- drvinst.exe (PID: 7580)
- devcon.exe (PID: 472)
- devcon.exe (PID: 632)
- drvinst.exe (PID: 7784)
- drvinst.exe (PID: 7892)
- devcon.exe (PID: 3024)
- devcon.exe (PID: 1132)
- drvinst.exe (PID: 6724)
- AskLinkLauncher.exe (PID: 2560)
- AskLinkLauncher.exe (PID: 496)
- drvinst.exe (PID: 6416)
Reads the computer name
- AskLink_Full_v4.0.7.5_20250518_2040.exe (PID: 7000)
- AskLink_Full_v4.0.7.5_20250518_2040.tmp (PID: 4108)
- AskLink_Full_v4.0.7.5_20250518_2040.tmp (PID: 4224)
- devcon.exe (PID: 7020)
- drvinst.exe (PID: 5508)
- drvinst.exe (PID: 7580)
- devcon.exe (PID: 632)
- drvinst.exe (PID: 7784)
- drvinst.exe (PID: 7892)
- devcon.exe (PID: 1132)
- drvinst.exe (PID: 6724)
- drvinst.exe (PID: 6416)
- AskLinkLauncher.exe (PID: 2560)
Create files in a temporary directory
- AskLink_Full_v4.0.7.5_20250518_2040.exe (PID: 1676)
- AskLink_Full_v4.0.7.5_20250518_2040.exe (PID: 7000)
- AskLink_Full_v4.0.7.5_20250518_2040.tmp (PID: 4224)
- devcon.exe (PID: 7020)
- devcon.exe (PID: 632)
- devcon.exe (PID: 1132)
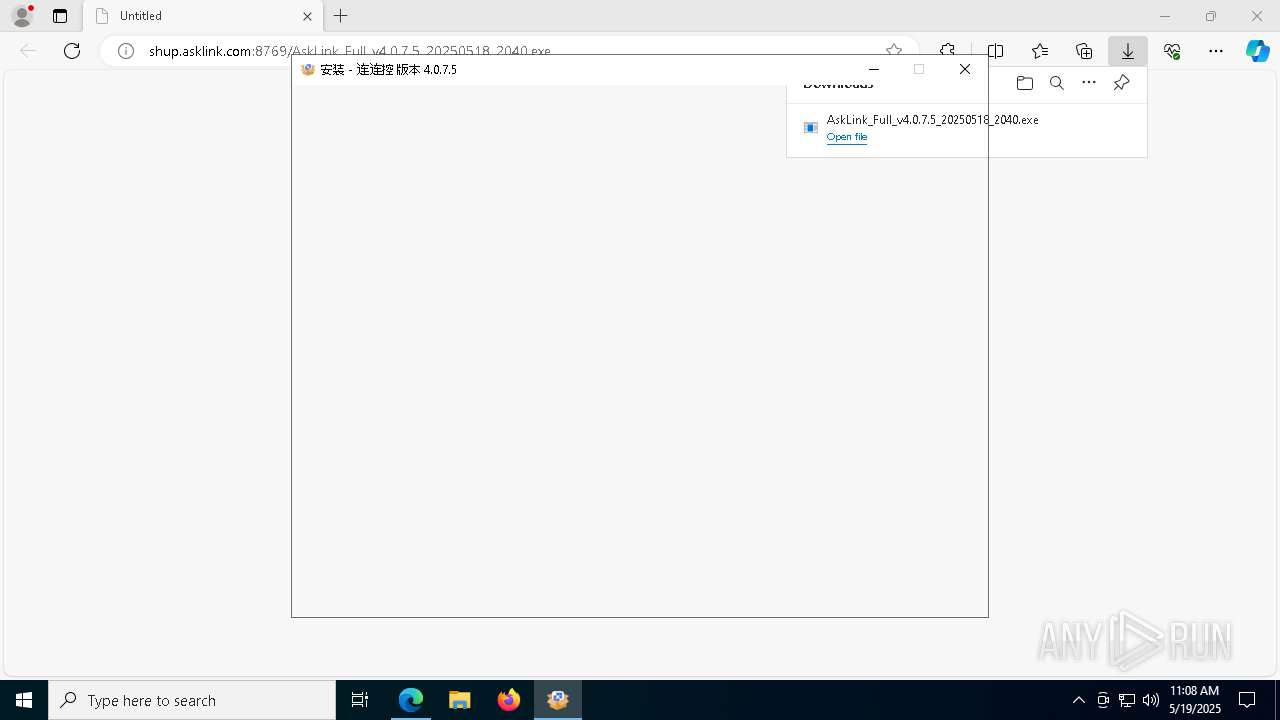
Detects InnoSetup installer (YARA)
- AskLink_Full_v4.0.7.5_20250518_2040.exe (PID: 1676)
- AskLink_Full_v4.0.7.5_20250518_2040.tmp (PID: 4108)
- AskLink_Full_v4.0.7.5_20250518_2040.exe (PID: 7000)
Compiled with Borland Delphi (YARA)
- AskLink_Full_v4.0.7.5_20250518_2040.exe (PID: 1676)
- AskLink_Full_v4.0.7.5_20250518_2040.tmp (PID: 4108)
- AskLink_Full_v4.0.7.5_20250518_2040.exe (PID: 7000)
Creates files in the program directory
- AskLink_Full_v4.0.7.5_20250518_2040.tmp (PID: 4224)
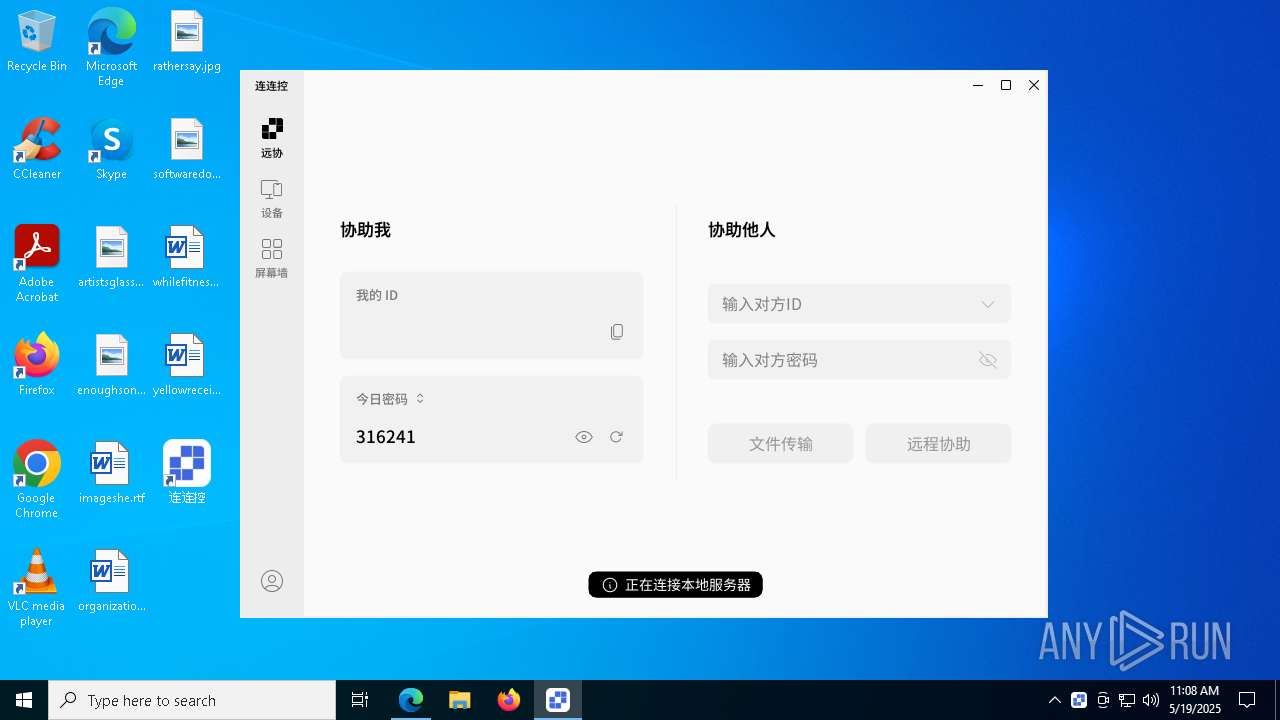
The sample compiled with chinese language support
- AskLink_Full_v4.0.7.5_20250518_2040.tmp (PID: 4224)
Creates a software uninstall entry
- AskLink_Full_v4.0.7.5_20250518_2040.tmp (PID: 4224)
Reads the software policy settings
- devcon.exe (PID: 7020)
- drvinst.exe (PID: 5508)
- devcon.exe (PID: 632)
- slui.exe (PID: 4944)
- drvinst.exe (PID: 7784)
- devcon.exe (PID: 1132)
- drvinst.exe (PID: 6724)
Reads the machine GUID from the registry
- devcon.exe (PID: 7020)
- drvinst.exe (PID: 5508)
- devcon.exe (PID: 632)
- drvinst.exe (PID: 7784)
- devcon.exe (PID: 1132)
- drvinst.exe (PID: 6724)
Changes the display of characters in the console
- cmd.exe (PID: 2064)
Reads Environment values
- AskLinkLauncher.exe (PID: 496)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
252
Monitored processes
112
Malicious processes
7
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | "C:\Program Files\AskLink\4.0.7.5\Driver\Ldd\devcon.exe" find "Root\AskLinkIddDriver" | C:\Program Files\AskLink\4.0.7.5\Driver\Ldd\devcon.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 6.1.7600.16385 (win7_wdk.100208-1538) Modules
| |||||||||||||||
| 496 | "C:\Program Files\AskLink\AskLinkLauncher.exe" --gpuup | C:\Program Files\AskLink\AskLinkLauncher.exe | — | AskLink_Full_v4.0.7.5_20250518_2040.tmp | |||||||||||
User: admin Company: Shanghai Kongkong Technology Co., Ltd. Integrity Level: HIGH Description: AskLink Launcher Exit code: 0 Version: 4.0.7.5 Modules
| |||||||||||||||
| 632 | "C:\Program Files\AskLink\4.0.7.5\Driver\Ldd\devcon.exe" install "C:\Program Files\AskLink\4.0.7.5\Driver\Ldd\AskLinkIddDriver.inf" "Root\AskLinkIddDriver" | C:\Program Files\AskLink\4.0.7.5\Driver\Ldd\devcon.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 6.1.7600.16385 (win7_wdk.100208-1538) Modules
| |||||||||||||||
| 632 | cmd.exe /c netsh advfirewall firewall add rule name="AskLink" dir=in action=allow program="C:\Program Files\AskLink\4.0.7.5\AskLink.exe" protocol=tcp enable=yes profile=private | C:\Windows\System32\cmd.exe | — | AskLink.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6088 --field-trial-handle=2052,i,1746688065326686856,18379764688702494256,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 660 | netsh advfirewall firewall add rule name="AskLink" dir=in action=allow program="C:\Program Files\AskLink\4.0.7.5\AskLink.exe" protocol=udp enable=yes profile=private | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 924 | cmd.exe /c netsh advfirewall firewall add rule name="AskLink" dir=in action=allow program="C:\Program Files\AskLink\4.0.7.5\AskLink.exe" protocol=udp enable=yes profile=domain | C:\Windows\System32\cmd.exe | — | AskLink.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 960 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7072 --field-trial-handle=2052,i,1746688065326686856,18379764688702494256,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 960 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
33 868
Read events
33 722
Write events
120
Delete events
26
Modification events
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F2D7926A11942F00 | |||
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 662CA16A11942F00 | |||
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393876 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7D08129E-73C2-4A40-ACFB-EB31E027C960} | |||
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393876 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {0DD076A6-5A55-468D-B844-28DF4AB232EC} | |||
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 6E97F06A11942F00 | |||
| (PID) Process: | (2432) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
77
Suspicious files
129
Text files
43
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bba1.TMP | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bbb1.TMP | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bbb1.TMP | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bba1.TMP | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bba1.TMP | — | |
MD5:— | SHA256:— | |||
| 2432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
63
DNS requests
52
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4728 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1747700435&P2=404&P3=2&P4=iZqQj3Prv%2faEAp9i83xFveDwBNzwok6kAJlFVc5WjLlmS2CHSELyeImBeuPaS6hCTe%2behINJEBgHCzVSMAY0Vw%3d%3d | unknown | — | — | whitelisted |
4728 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1747700435&P2=404&P3=2&P4=iZqQj3Prv%2faEAp9i83xFveDwBNzwok6kAJlFVc5WjLlmS2CHSELyeImBeuPaS6hCTe%2behINJEBgHCzVSMAY0Vw%3d%3d | unknown | — | — | whitelisted |
4728 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1747700435&P2=404&P3=2&P4=iZqQj3Prv%2faEAp9i83xFveDwBNzwok6kAJlFVc5WjLlmS2CHSELyeImBeuPaS6hCTe%2behINJEBgHCzVSMAY0Vw%3d%3d | unknown | — | — | whitelisted |
4728 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1747700435&P2=404&P3=2&P4=iZqQj3Prv%2faEAp9i83xFveDwBNzwok6kAJlFVc5WjLlmS2CHSELyeImBeuPaS6hCTe%2behINJEBgHCzVSMAY0Vw%3d%3d | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7232 | msedge.exe | GET | — | 117.143.60.202:8769 | http://shup.asklink.com:8769/AskLink_Full_v4.0.7.5_20250518_2040.exe | unknown | — | — | unknown |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2772 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2432 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7232 | msedge.exe | 13.107.43.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7232 | msedge.exe | 117.143.60.202:8769 | shup.asklink.com | Shanghai Mobile Communications Co.,Ltd. | CN | unknown |
7232 | msedge.exe | 13.107.9.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
shup.asklink.com |
| unknown |
_8769._https.shup.asklink.com |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7232 | msedge.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |