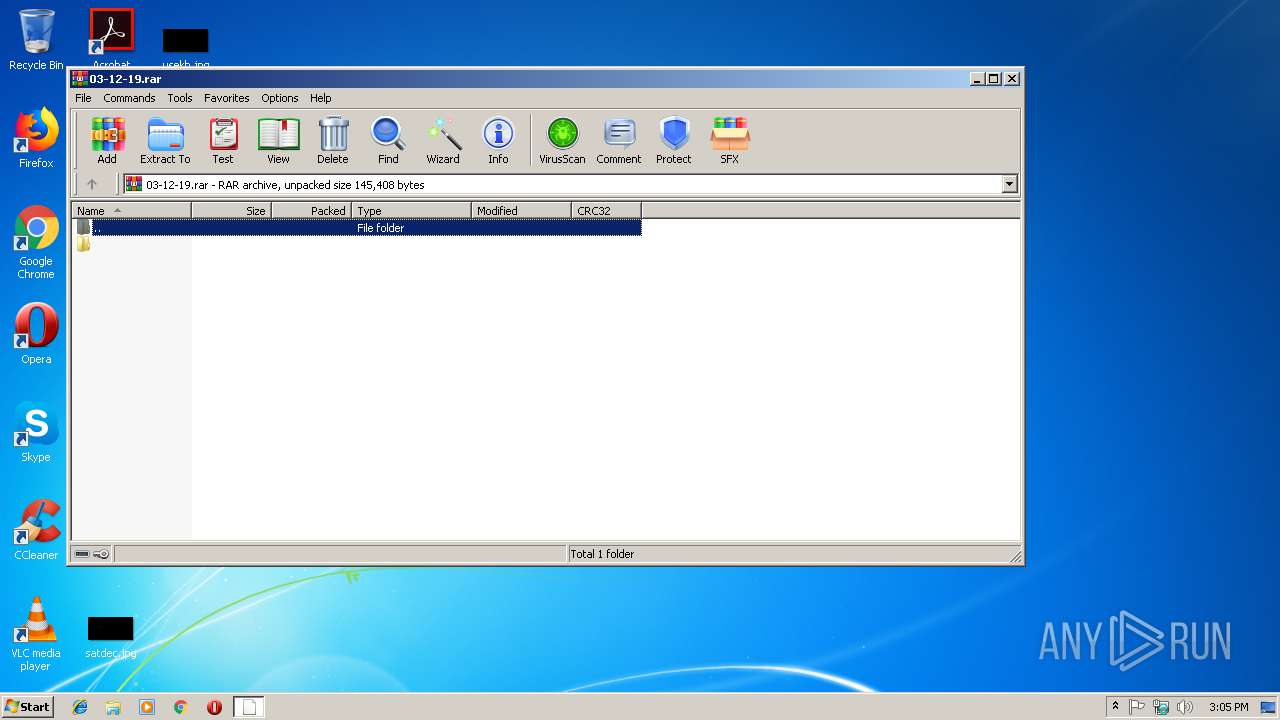
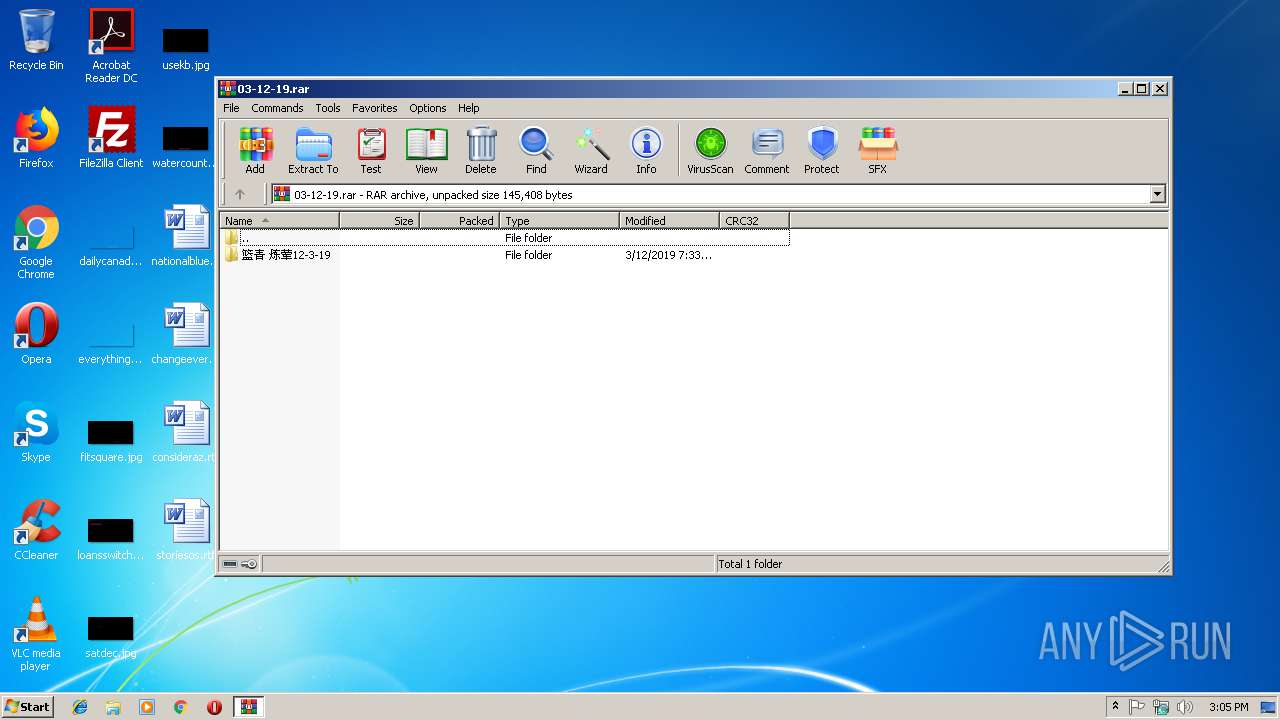
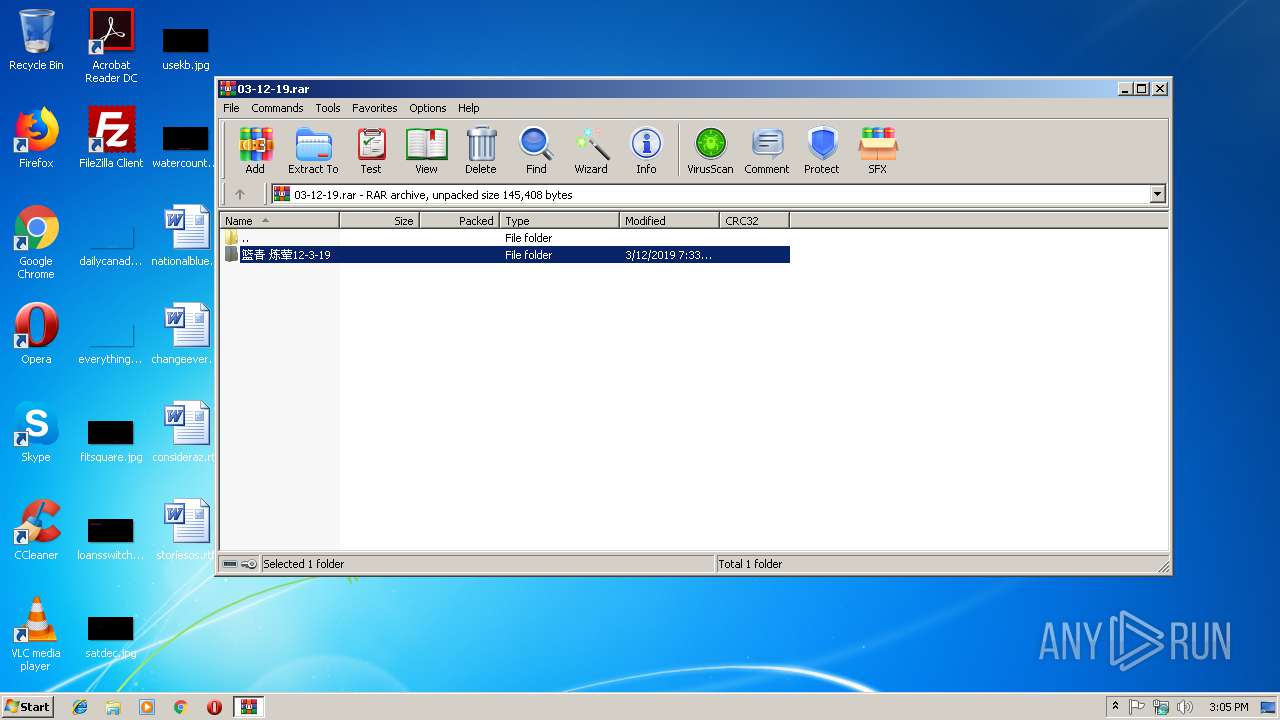
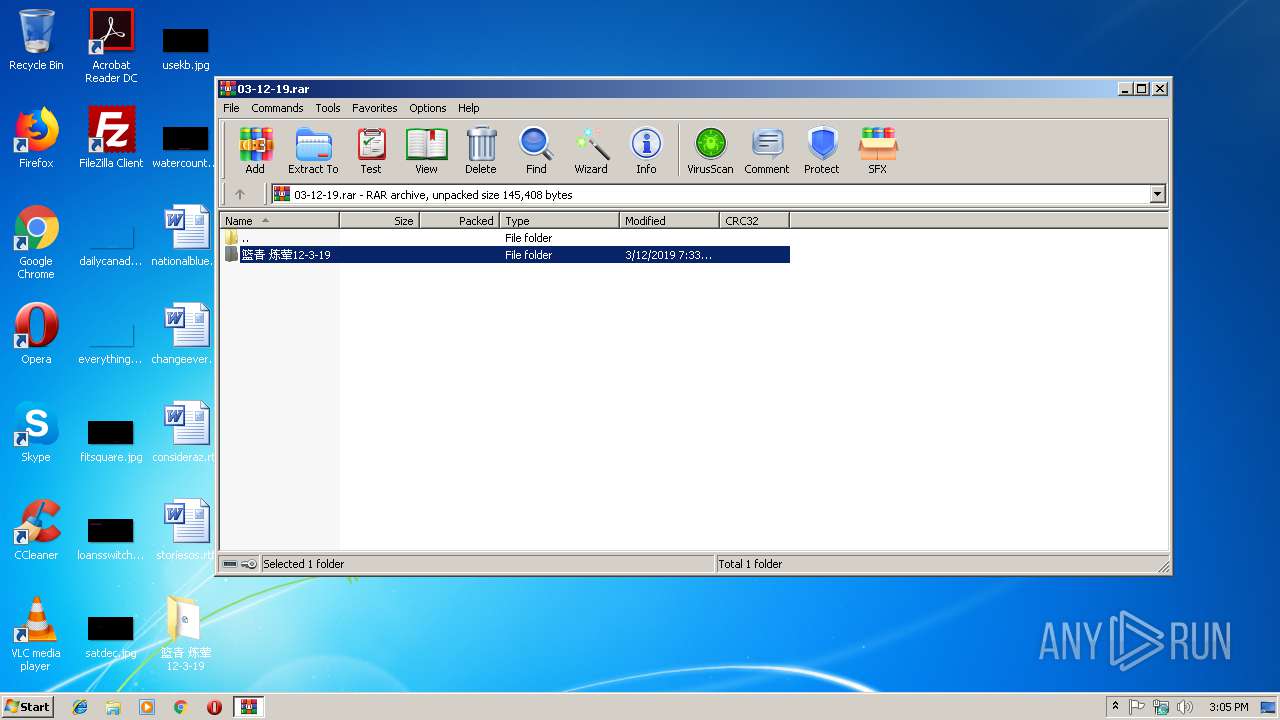
| File name: | 03-12-19.rar |
| Full analysis: | https://app.any.run/tasks/e6ba6483-0bbb-46ec-b467-0699bc9b6030 |
| Verdict: | Malicious activity |
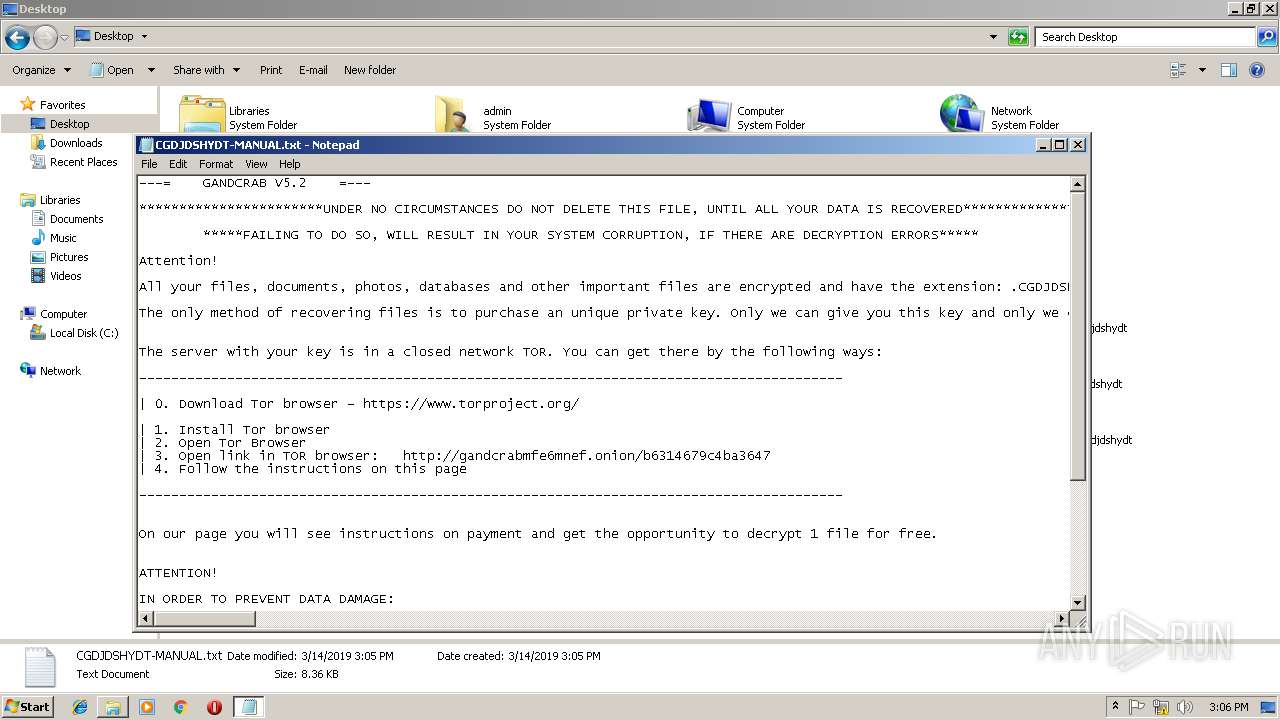
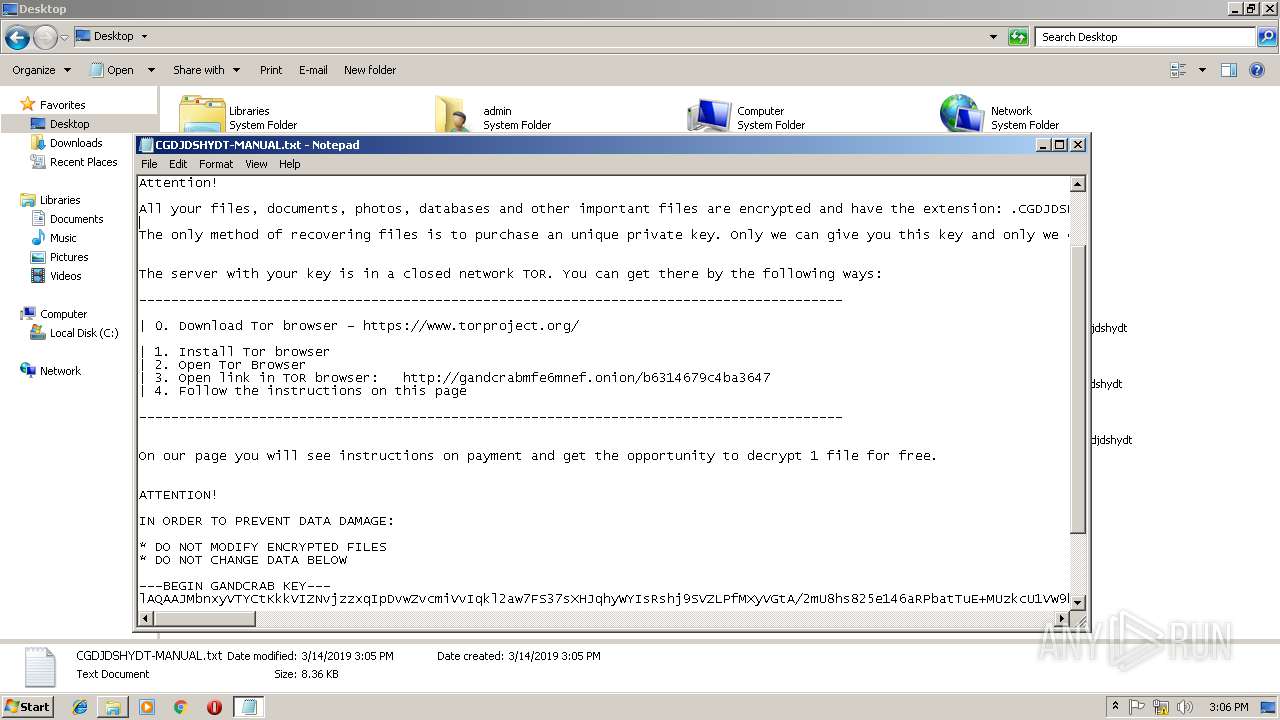
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | March 14, 2019, 15:04:36 |
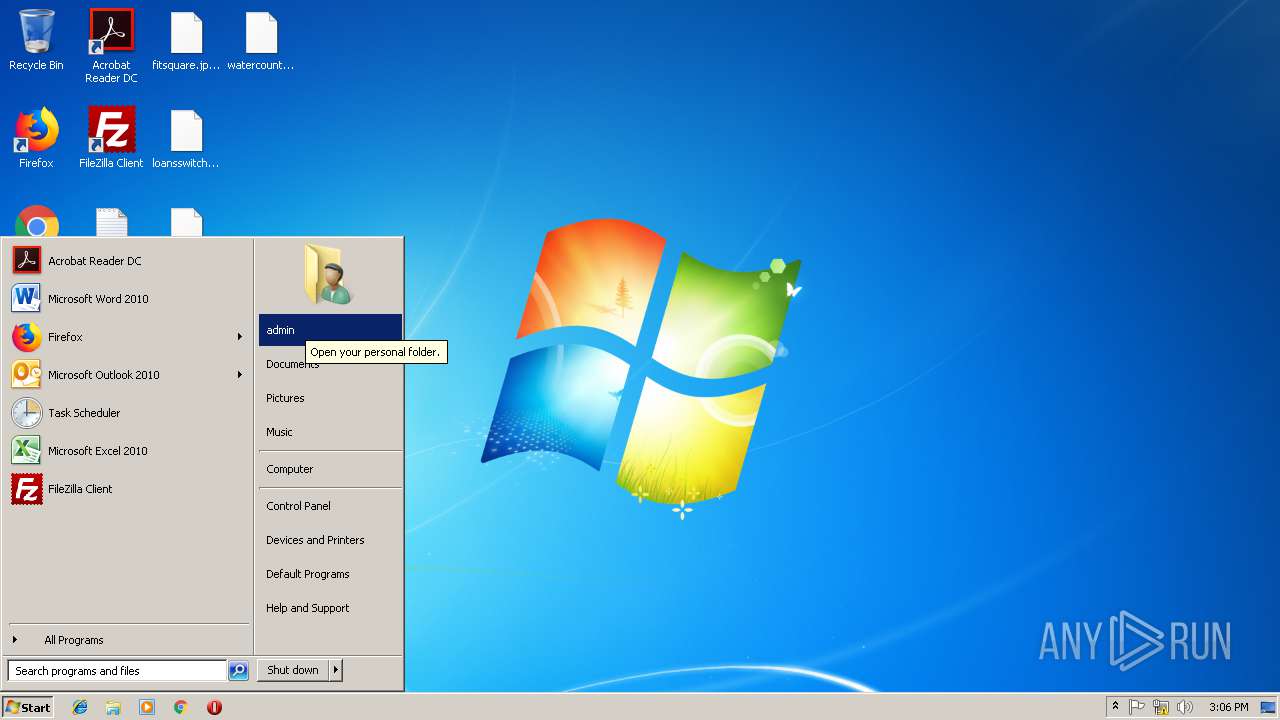
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 847BBEEF6647BC944AC9666BF6C5AF70 |
| SHA1: | 971626B71C4D8914A93B257DF39CB7B854F67BCC |
| SHA256: | 51D2565B1E10C5DD2CB77BE0F43A50EED62A7CBAAA8433D57E2C54C4B308EB48 |
| SSDEEP: | 1536:KnNlTjPDMNmmGjCf19lPjc93iw6Sr2AnI0dwifB/123pPgv/vhoQVoXOn3T3bQ5a:8PMnUCtPeZ7HdVB123ponhoQVoM3L80 |
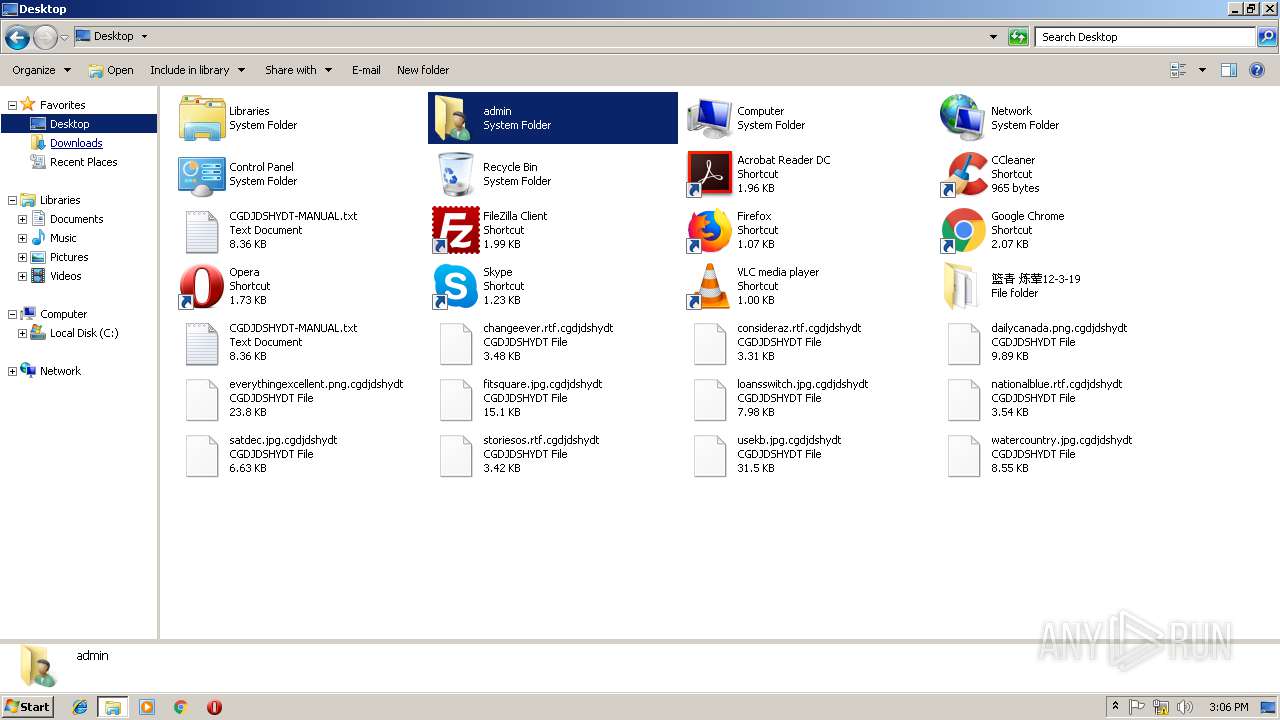
MALICIOUS
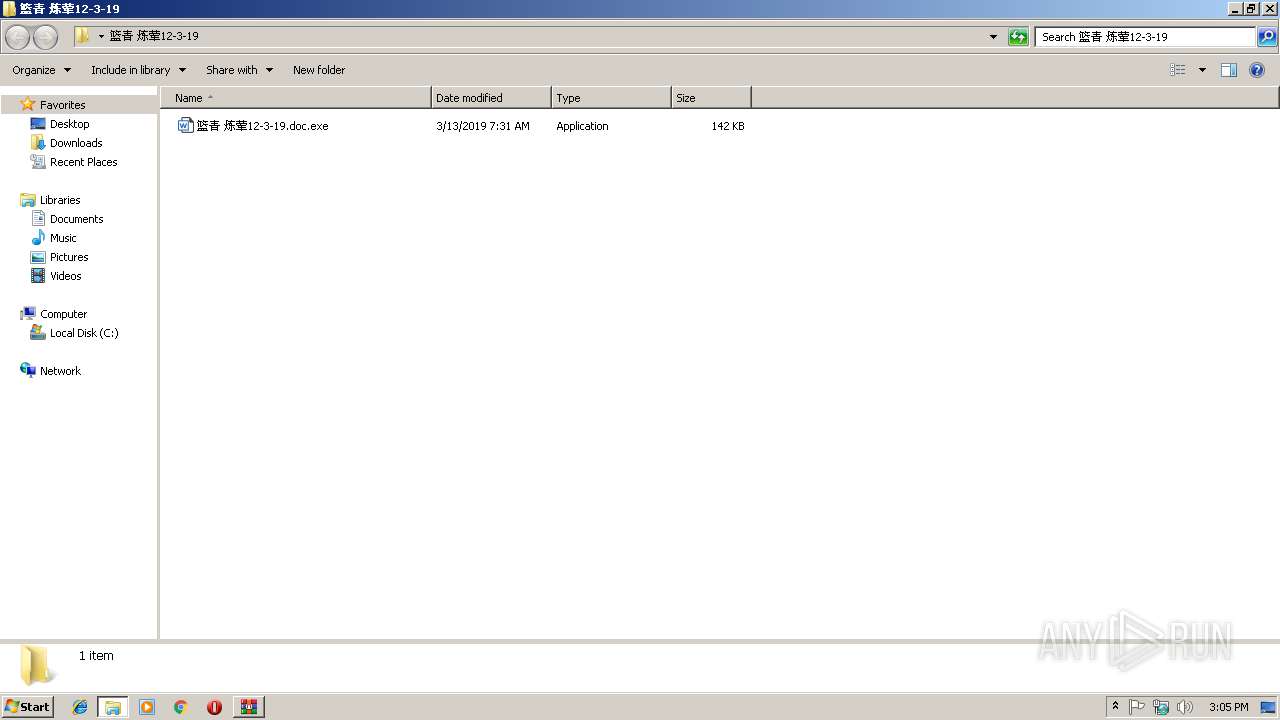
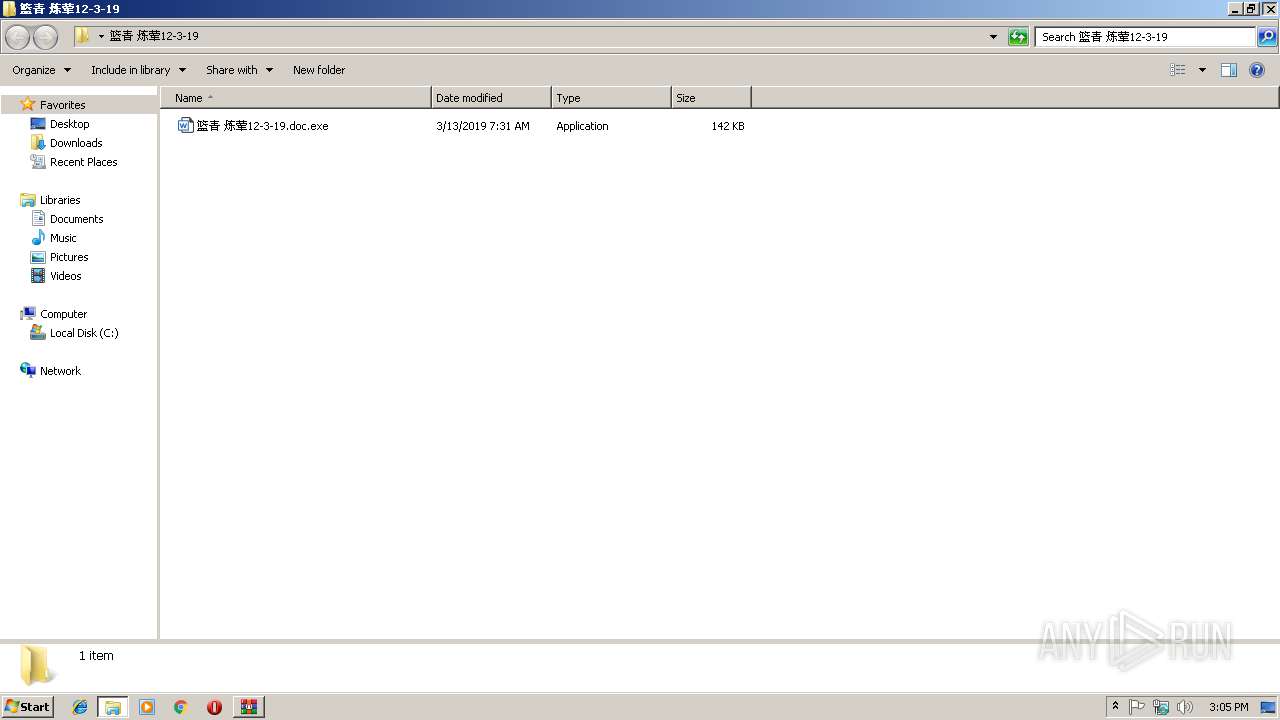
Application was dropped or rewritten from another process
- 篮青 炼荤12-3-19.doc.exe (PID: 2992)
Writes file to Word startup folder
- 篮青 炼荤12-3-19.doc.exe (PID: 2992)
Actions looks like stealing of personal data
- 篮青 炼荤12-3-19.doc.exe (PID: 2992)
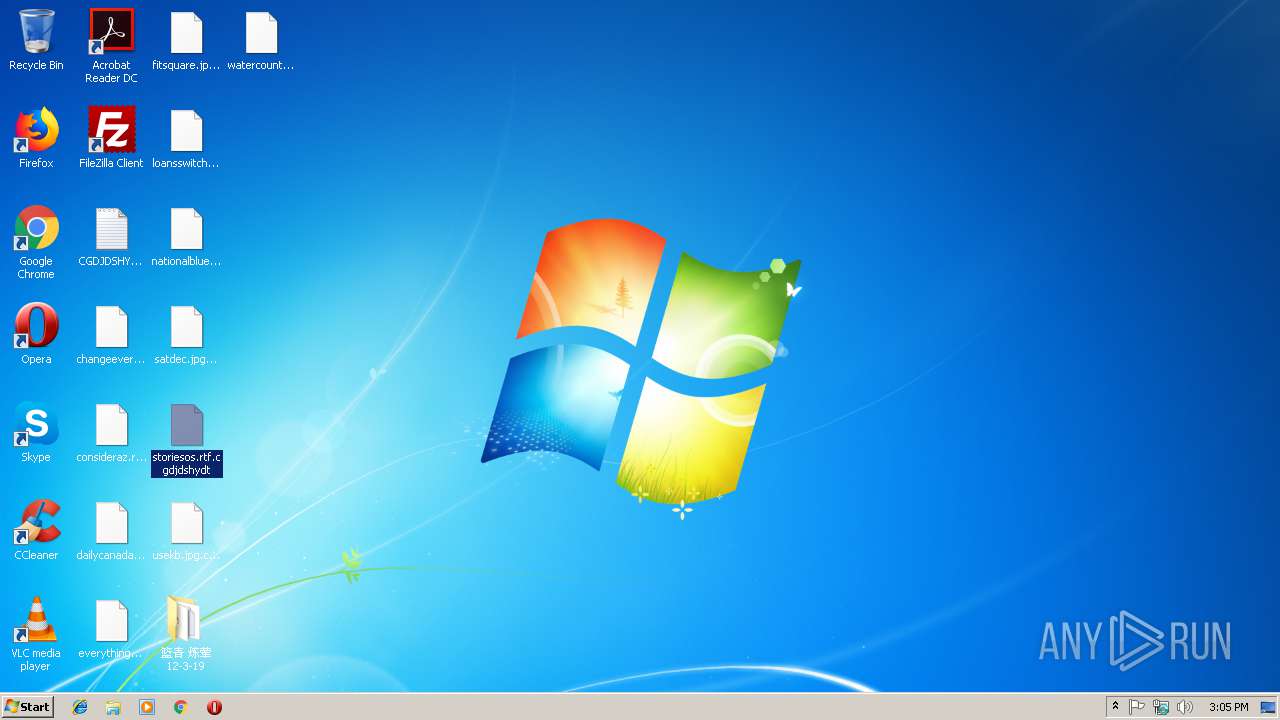
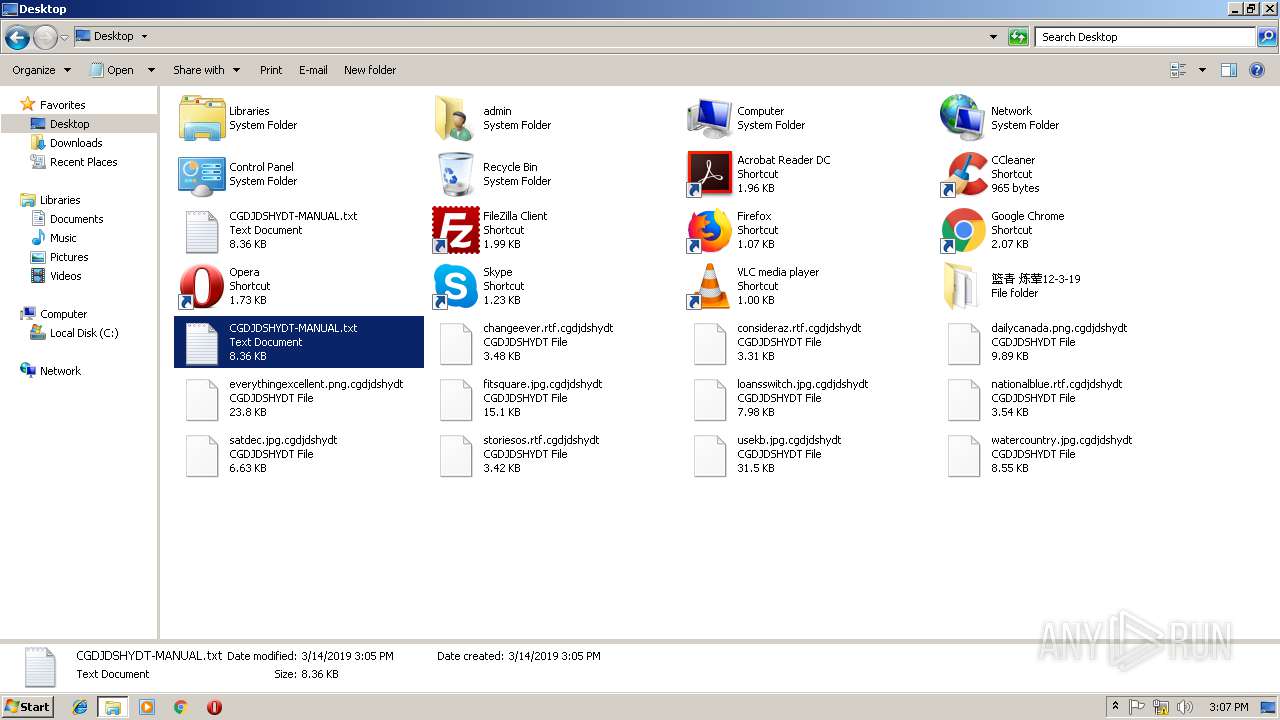
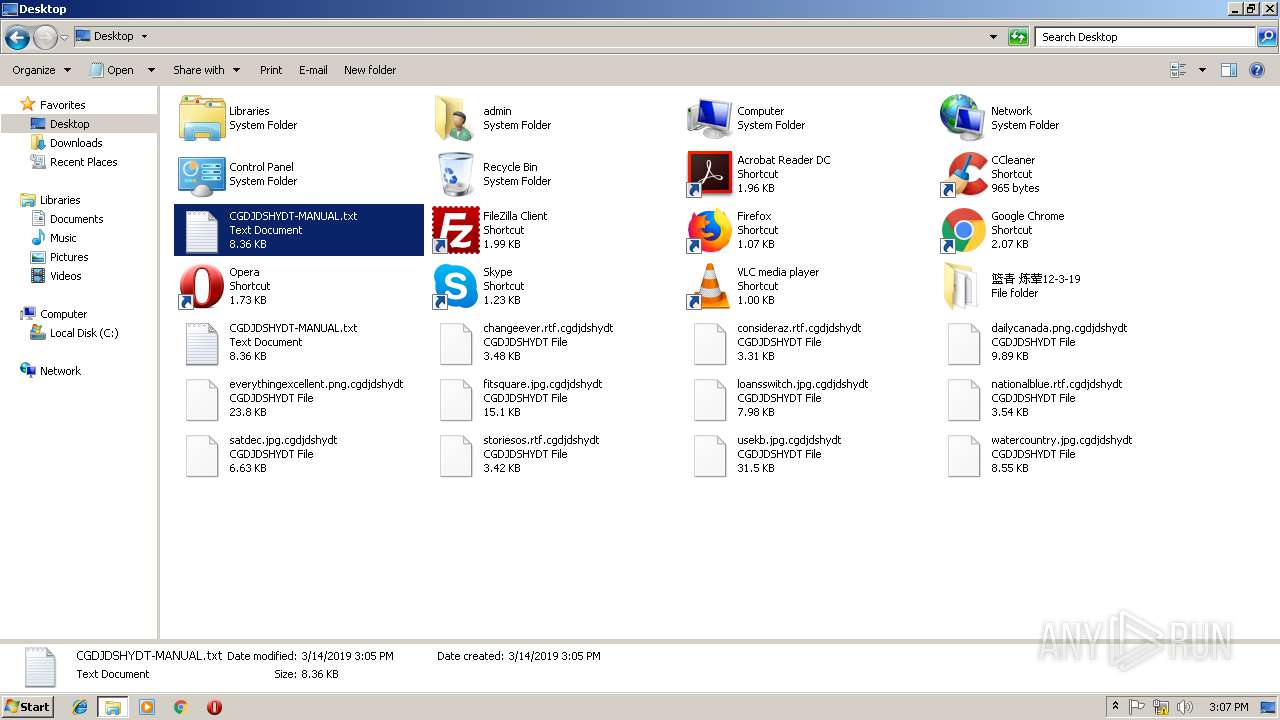
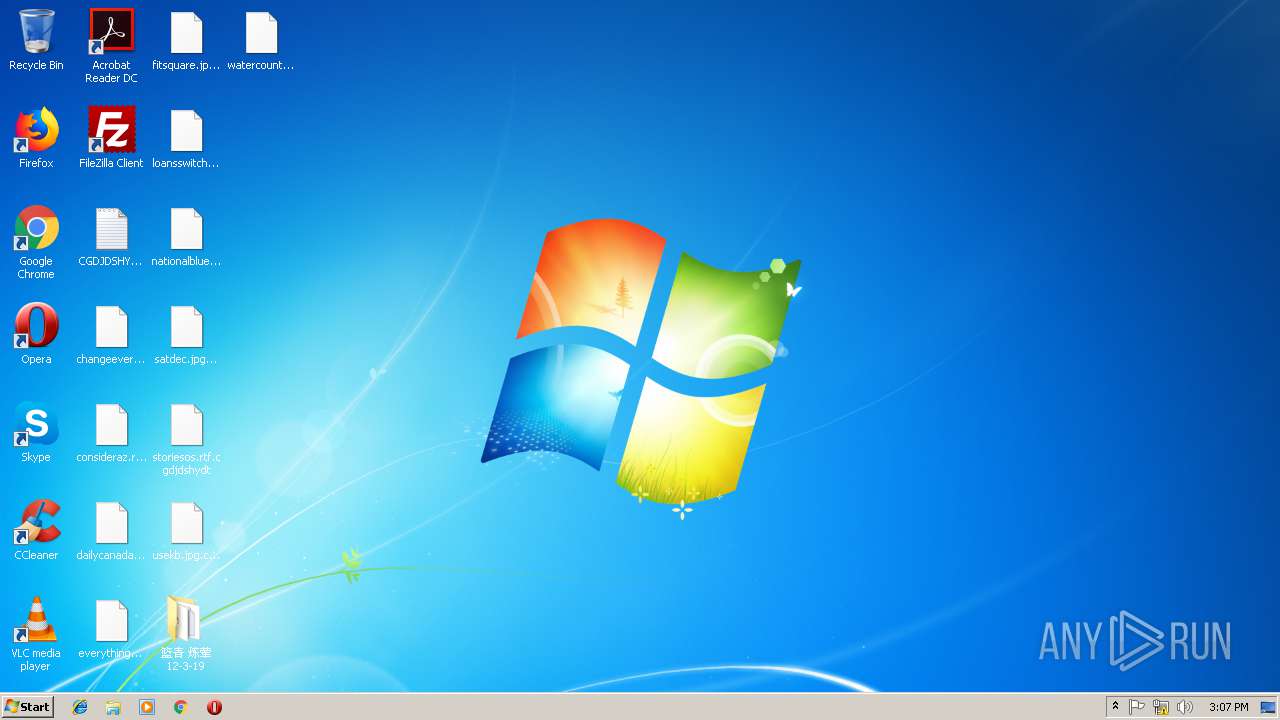
Renames files like Ransomware
- 篮青 炼荤12-3-19.doc.exe (PID: 2992)
Deletes shadow copies
- 篮青 炼荤12-3-19.doc.exe (PID: 2992)
Changes settings of System certificates
- 篮青 炼荤12-3-19.doc.exe (PID: 2992)
Connects to CnC server
- 篮青 炼荤12-3-19.doc.exe (PID: 2992)
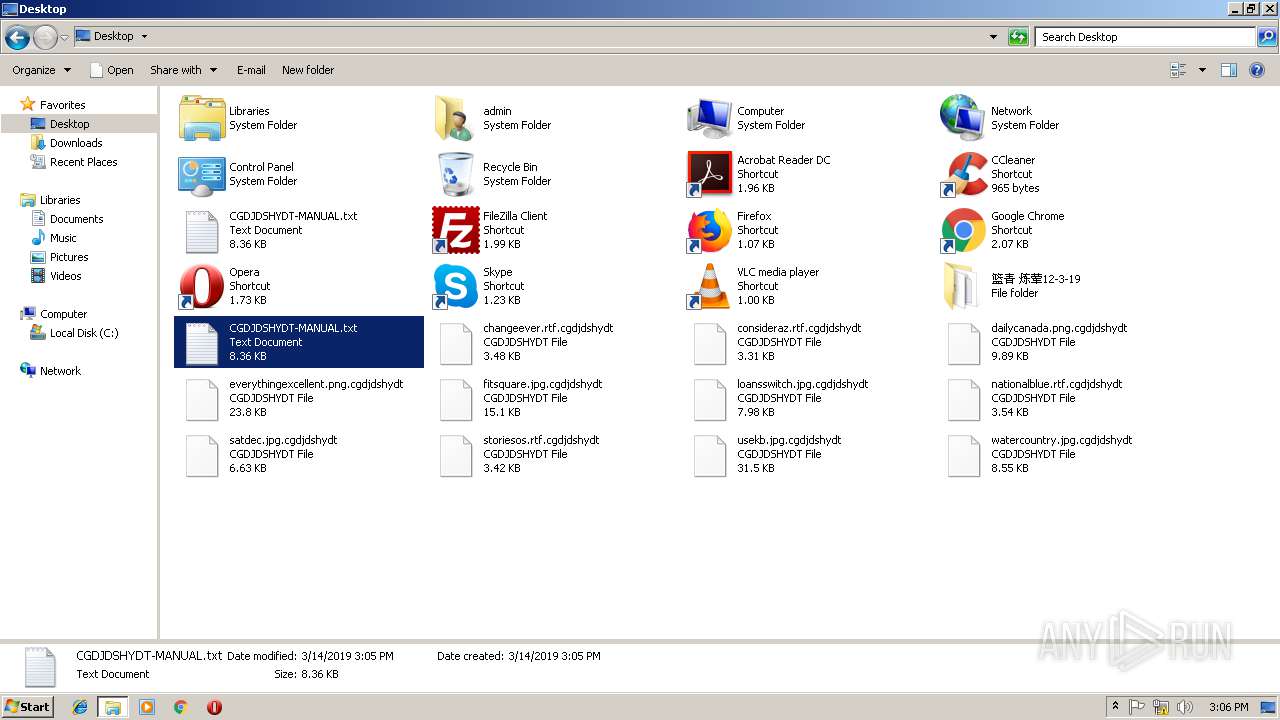
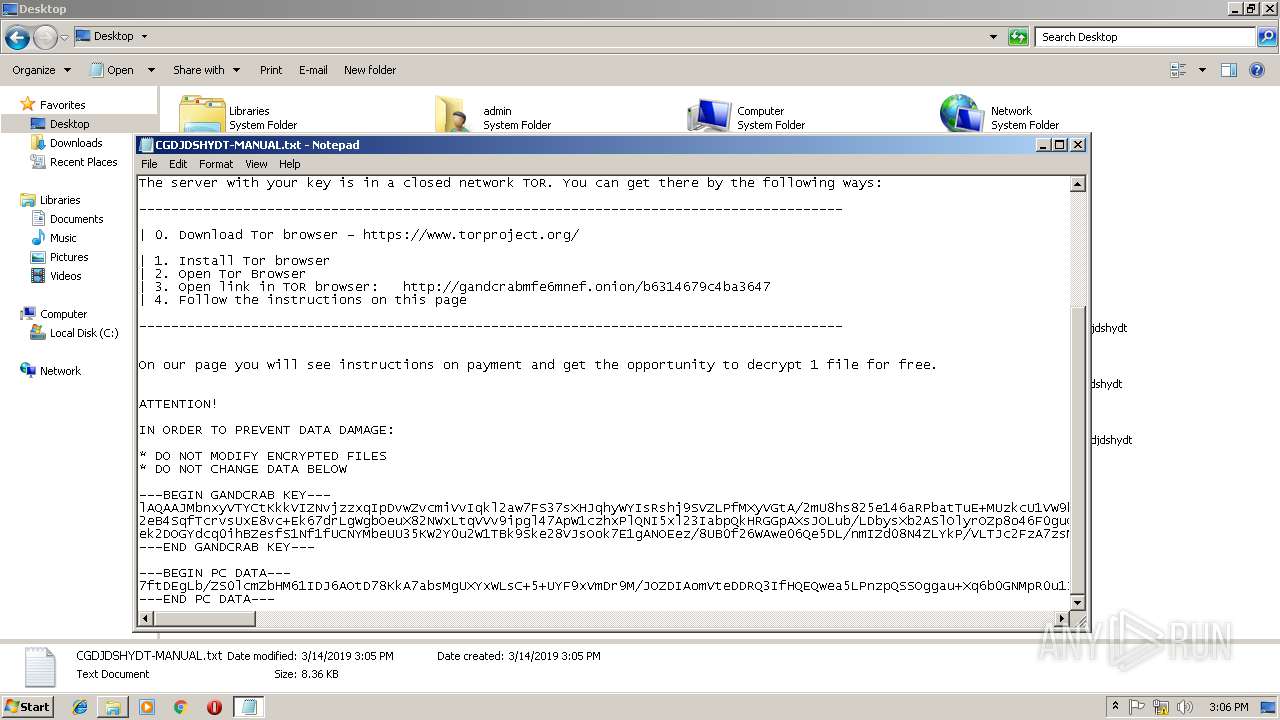
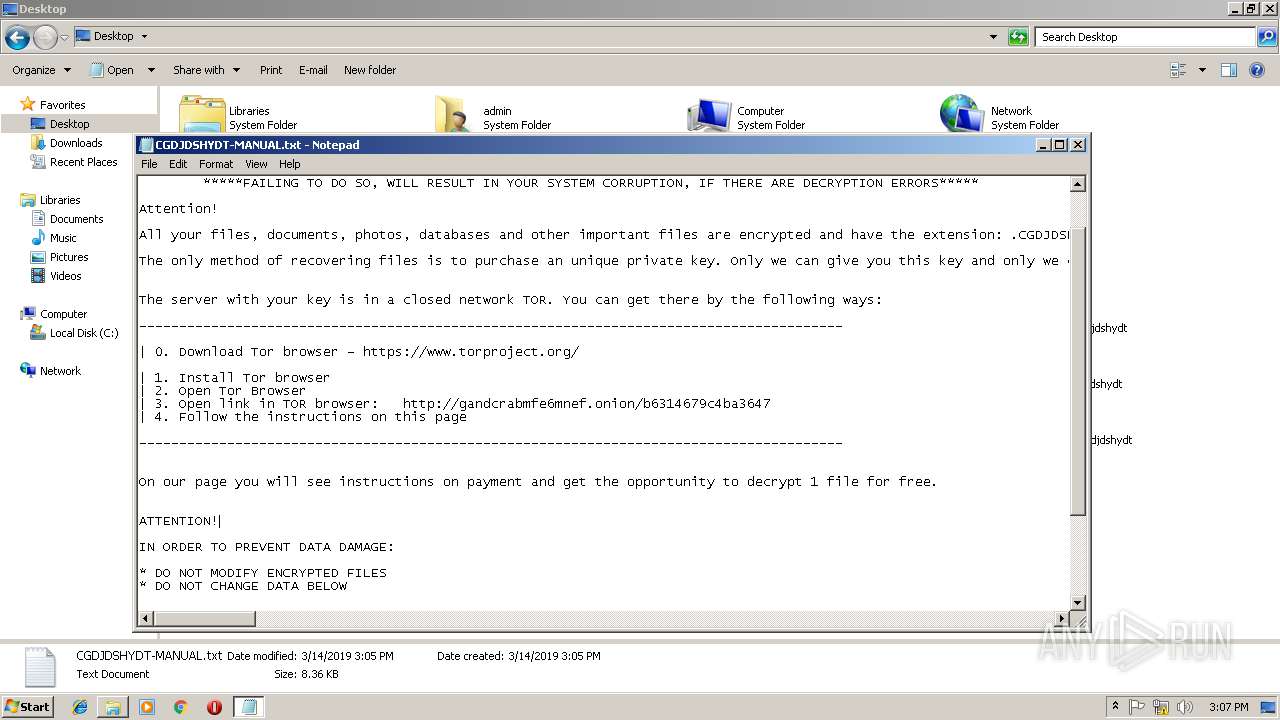
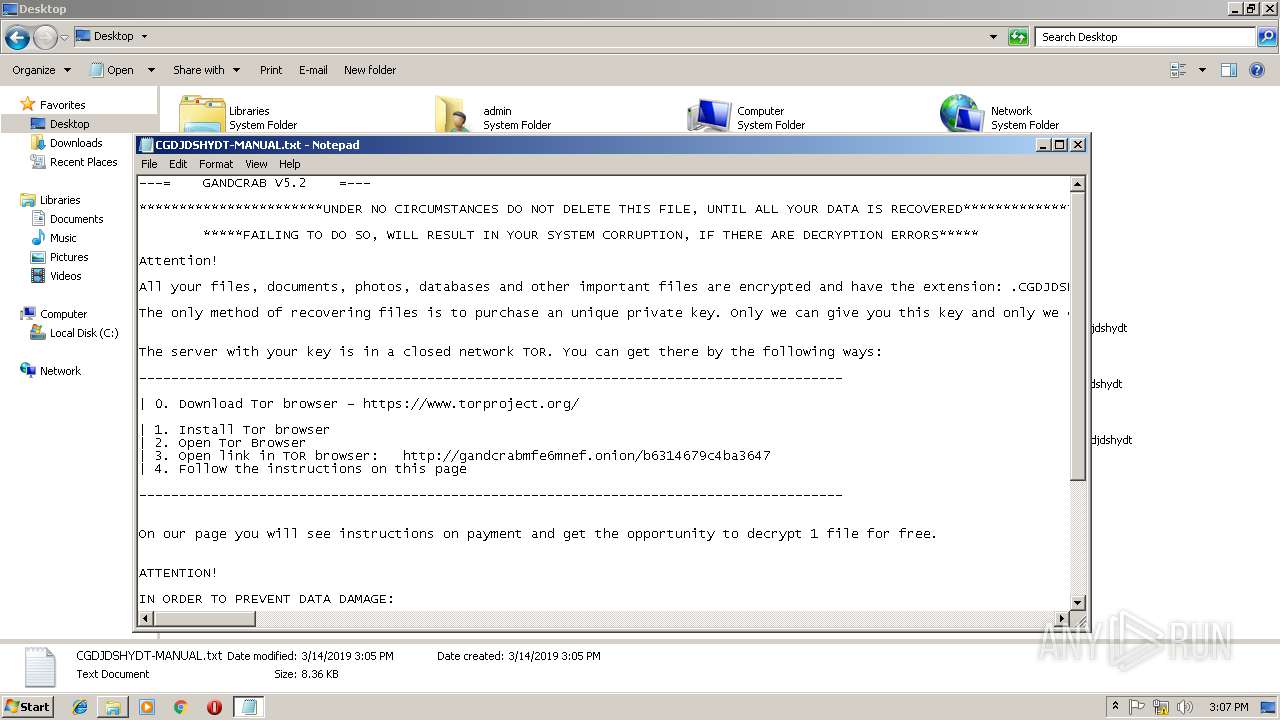
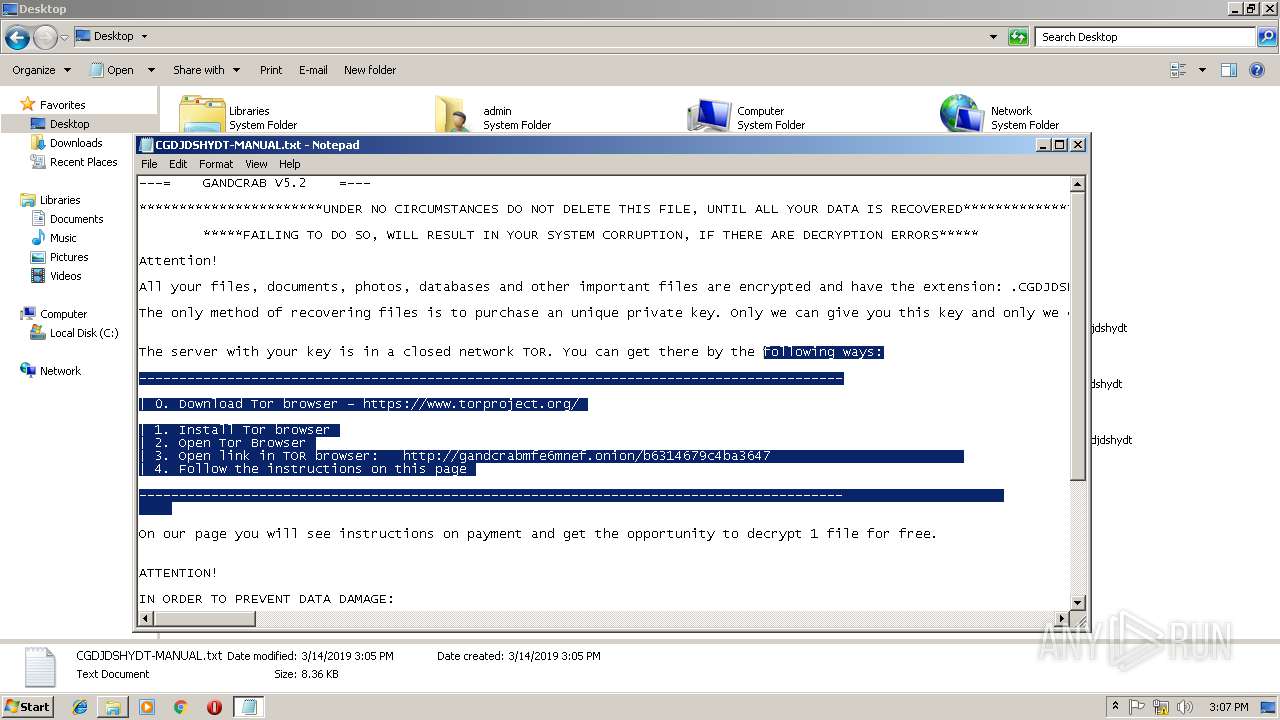
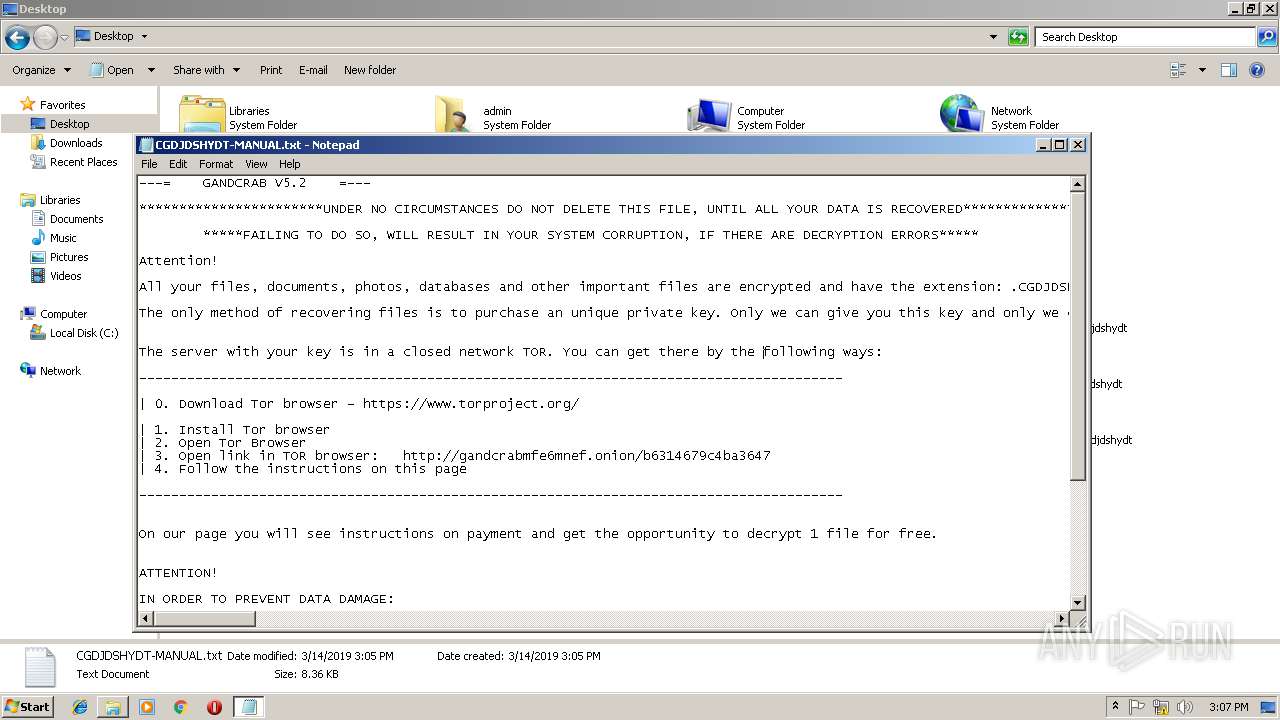
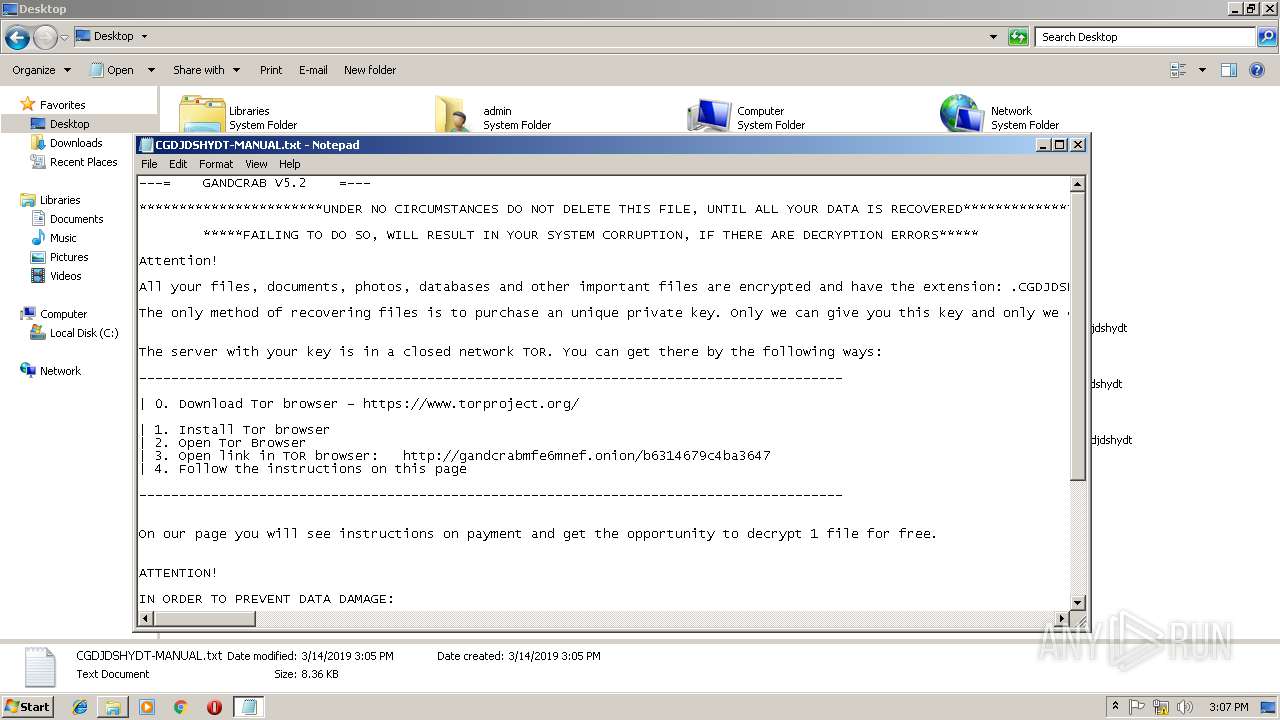
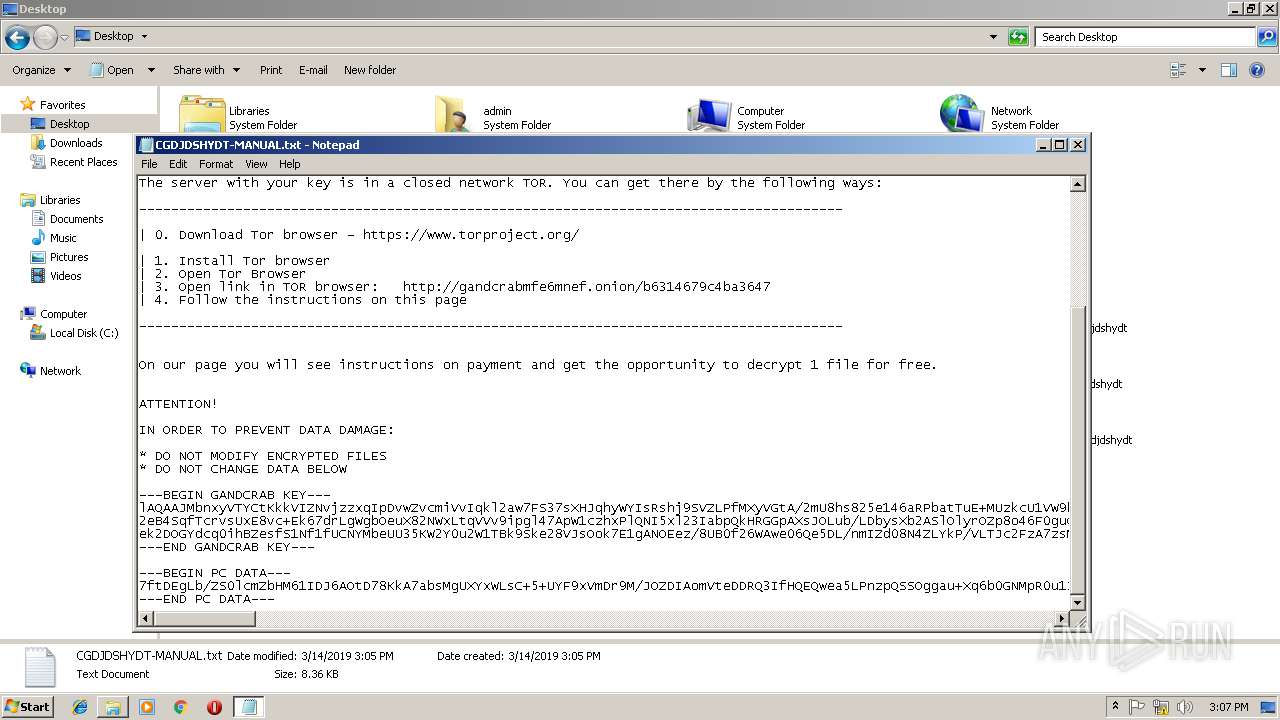
Dropped file may contain instructions of ransomware
- 篮青 炼荤12-3-19.doc.exe (PID: 2992)
GANDCRAB detected
- 篮青 炼荤12-3-19.doc.exe (PID: 2992)
SUSPICIOUS
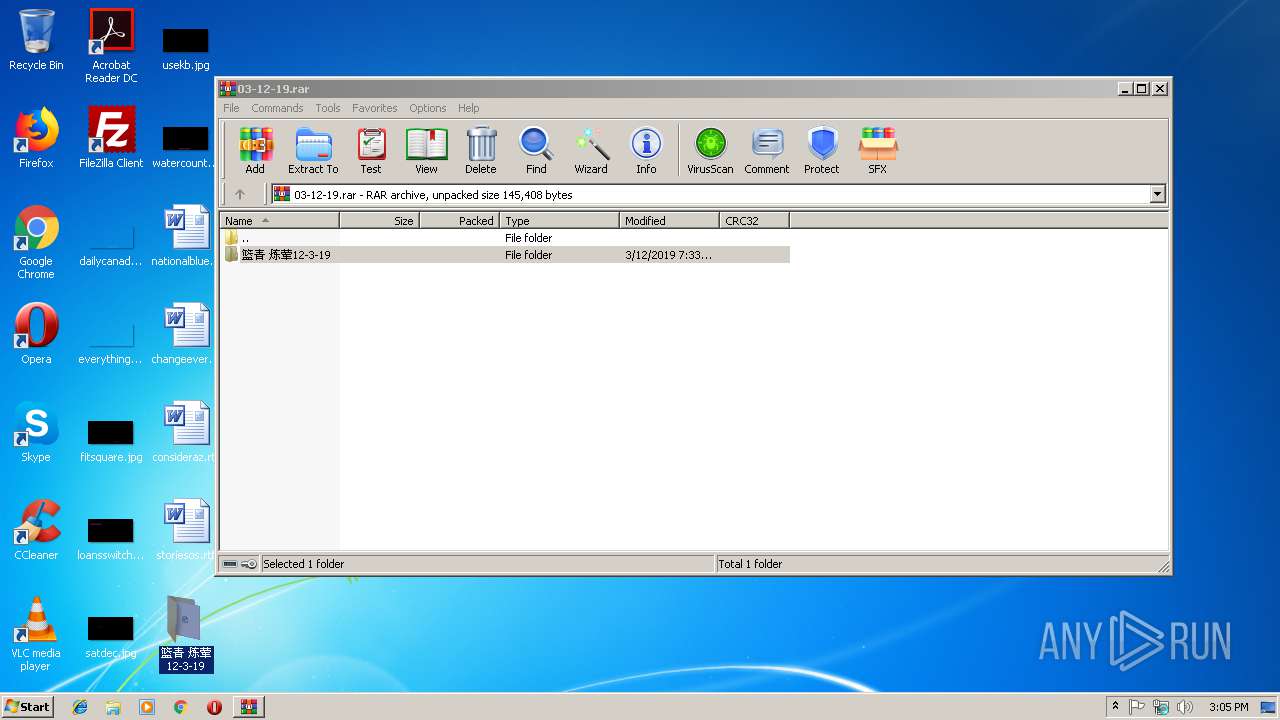
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2720)
Creates files in the program directory
- 篮青 炼荤12-3-19.doc.exe (PID: 2992)
Reads the cookies of Mozilla Firefox
- 篮青 炼荤12-3-19.doc.exe (PID: 2992)
Reads Internet Cache Settings
- 篮青 炼荤12-3-19.doc.exe (PID: 2992)
Adds / modifies Windows certificates
- 篮青 炼荤12-3-19.doc.exe (PID: 2992)
Creates files in the user directory
- 篮青 炼荤12-3-19.doc.exe (PID: 2992)
INFO
Dropped object may contain TOR URL's
- 篮青 炼荤12-3-19.doc.exe (PID: 2992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
42
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
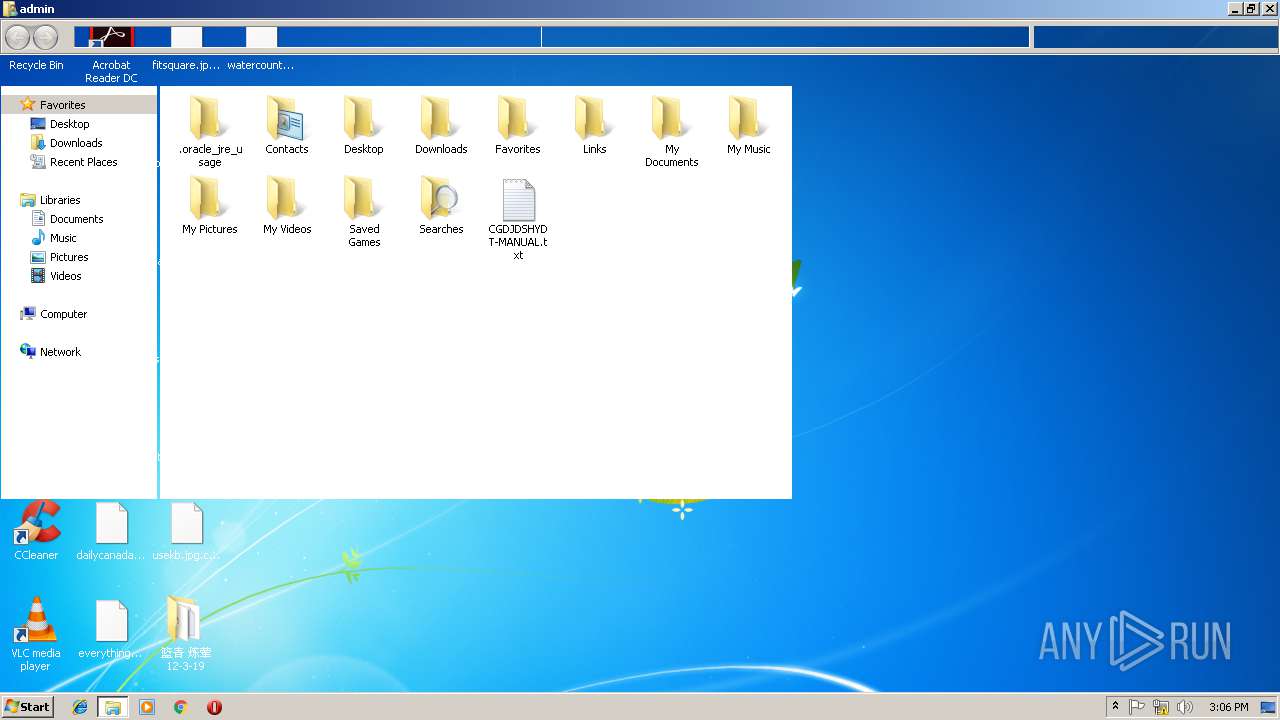
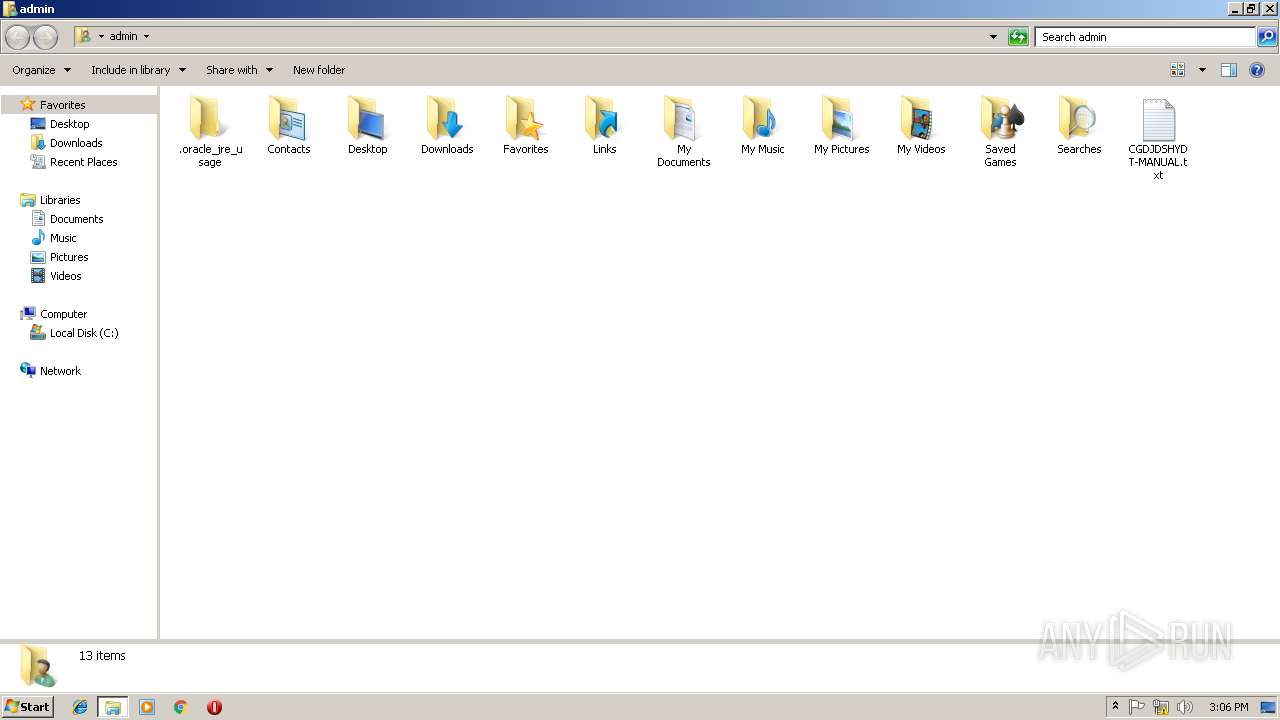
| 1712 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\CGDJDSHYDT-MANUAL.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
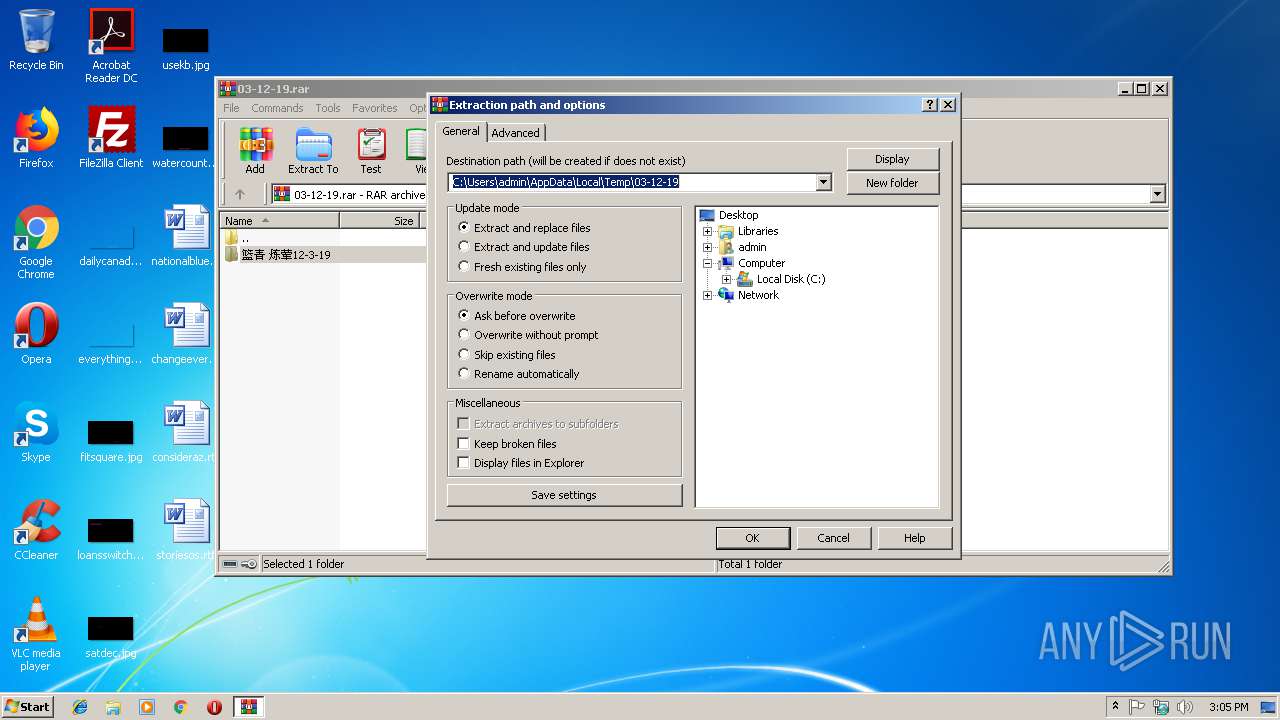
| 2720 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\03-12-19.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2932 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2984 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | 篮青 炼荤12-3-19.doc.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
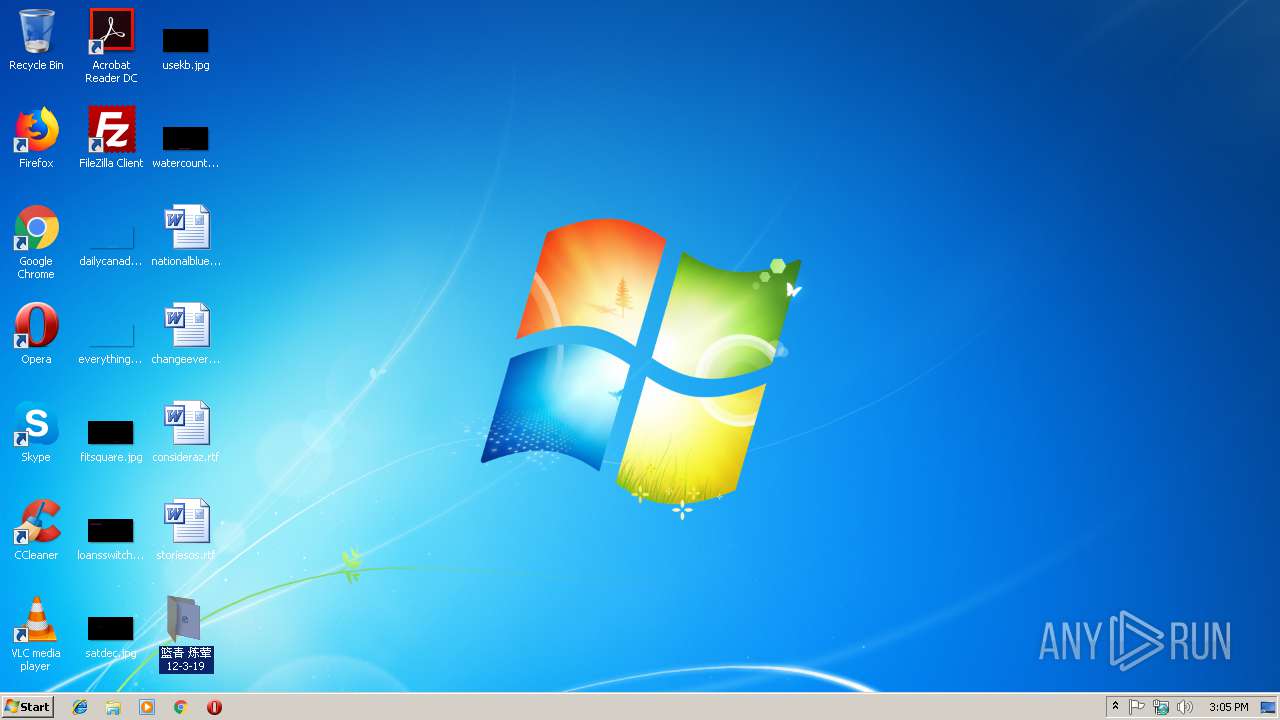
| 2992 | "C:\Users\admin\Desktop\篮青 炼荤12-3-19\篮青 炼荤12-3-19.doc.exe" | C:\Users\admin\Desktop\篮青 炼荤12-3-19\篮青 炼荤12-3-19.doc.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3284 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\Public\Desktop\CGDJDSHYDT-MANUAL.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
612
Read events
552
Write events
60
Delete events
0
Modification events
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\03-12-19.rar | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFD60000004C0000009604000041020000 | |||
Executable files
1
Suspicious files
425
Text files
322
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2992 | 篮青 炼荤12-3-19.doc.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi | — | |
MD5:— | SHA256:— | |||
| 2992 | 篮青 炼荤12-3-19.doc.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.cgdjdshydt | — | |
MD5:— | SHA256:— | |||
| 2992 | 篮青 炼荤12-3-19.doc.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 2992 | 篮青 炼荤12-3-19.doc.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{05ed3515-06b3-48f6-8cf2-bf24b1bf0727}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2992 | 篮青 炼荤12-3-19.doc.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{16d74681-6bc3-4c44-97f0-8b8dfefe2355}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2992 | 篮青 炼荤12-3-19.doc.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{38e8535f-27d0-4352-aa3a-ce4178930102}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2992 | 篮青 炼荤12-3-19.doc.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi.cgdjdshydt | binary | |
MD5:— | SHA256:— | |||
| 2992 | 篮青 炼荤12-3-19.doc.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{3cc0f82b-873a-4e59-b89f-689fbdf88af9}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2992 | 篮青 炼荤12-3-19.doc.exe | C:\Recovery\CGDJDSHYDT-MANUAL.txt | text | |
MD5:— | SHA256:— | |||
| 2992 | 篮青 炼荤12-3-19.doc.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{5c4beaff-a038-4df7-9b35-072a18f8e3d6}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2992 | 篮青 炼荤12-3-19.doc.exe | GET | 301 | 107.173.49.208:80 | http://www.kakaocorp.link/ | US | html | 162 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2992 | 篮青 炼荤12-3-19.doc.exe | 107.173.49.208:80 | www.kakaocorp.link | ColoCrossing | US | malicious |
2992 | 篮青 炼荤12-3-19.doc.exe | 107.173.49.208:443 | www.kakaocorp.link | ColoCrossing | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.kakaocorp.link |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2992 | 篮青 炼荤12-3-19.doc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklisted GandCrab Ransomware C2 Server |
2992 | 篮青 炼荤12-3-19.doc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklisted GandCrab Ransomware C2 Server |
2992 | 篮青 炼荤12-3-19.doc.exe | A Network Trojan was detected | MALWARE [PTsecurity] GandCrab v.5 SSL Connection |
2 ETPRO signatures available at the full report