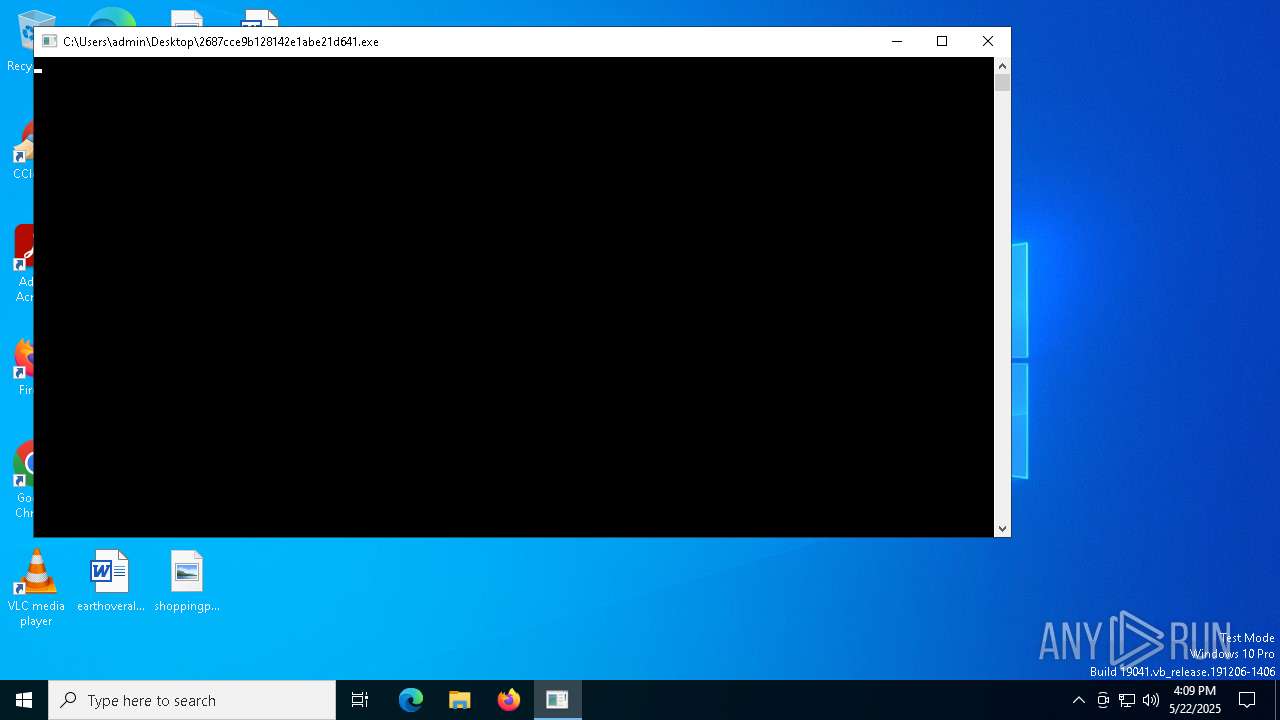
| File name: | 2687cce9b128142e1abe21d641.exe |
| Full analysis: | https://app.any.run/tasks/ba29758f-6f57-48a2-ba34-000d755409c3 |
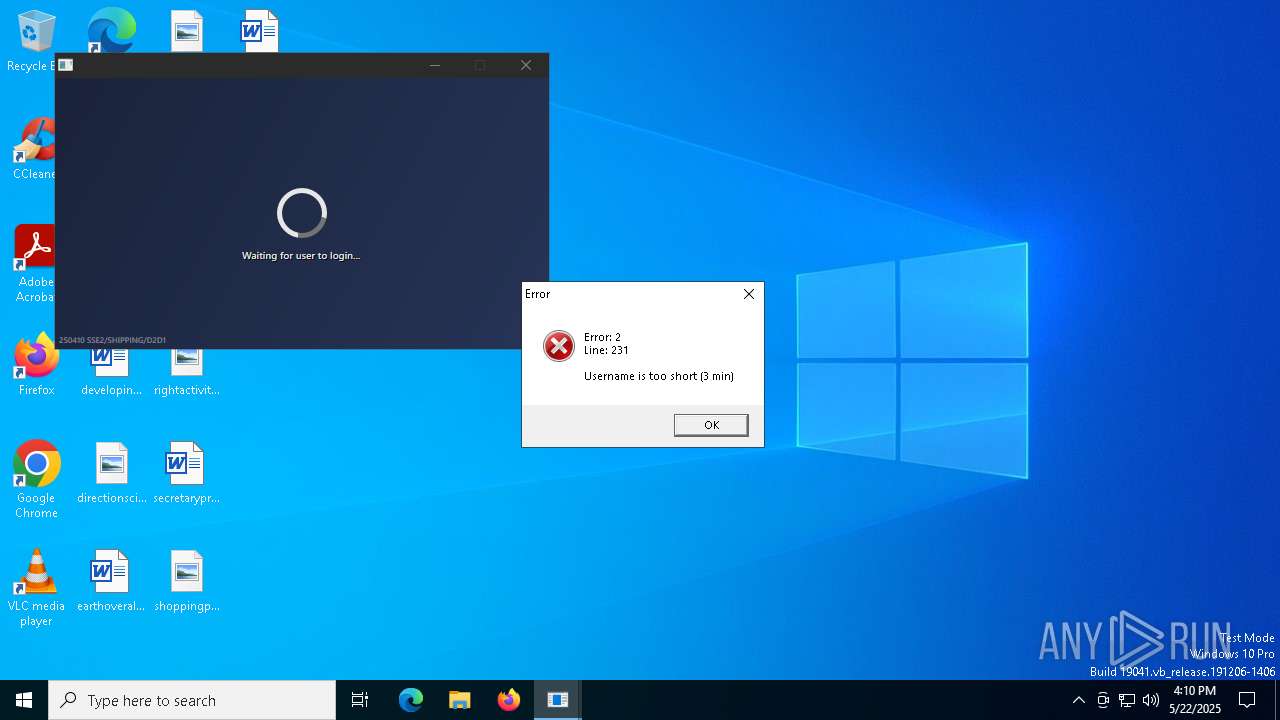
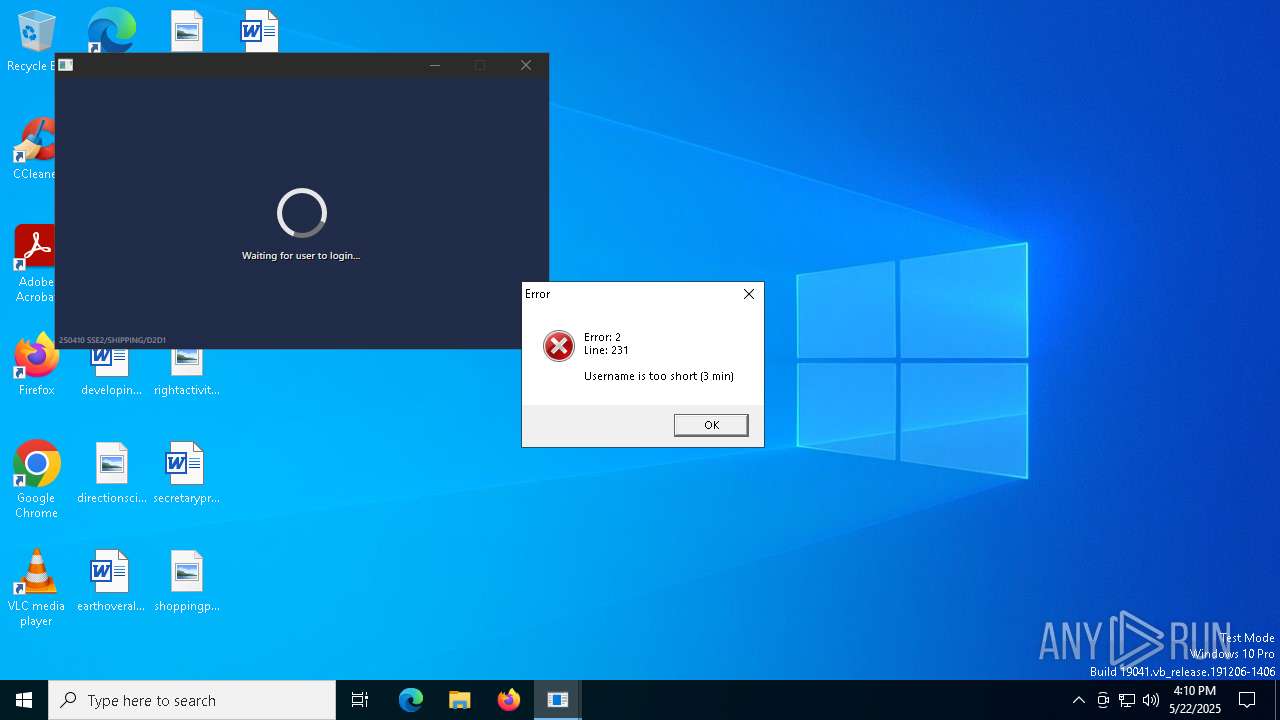
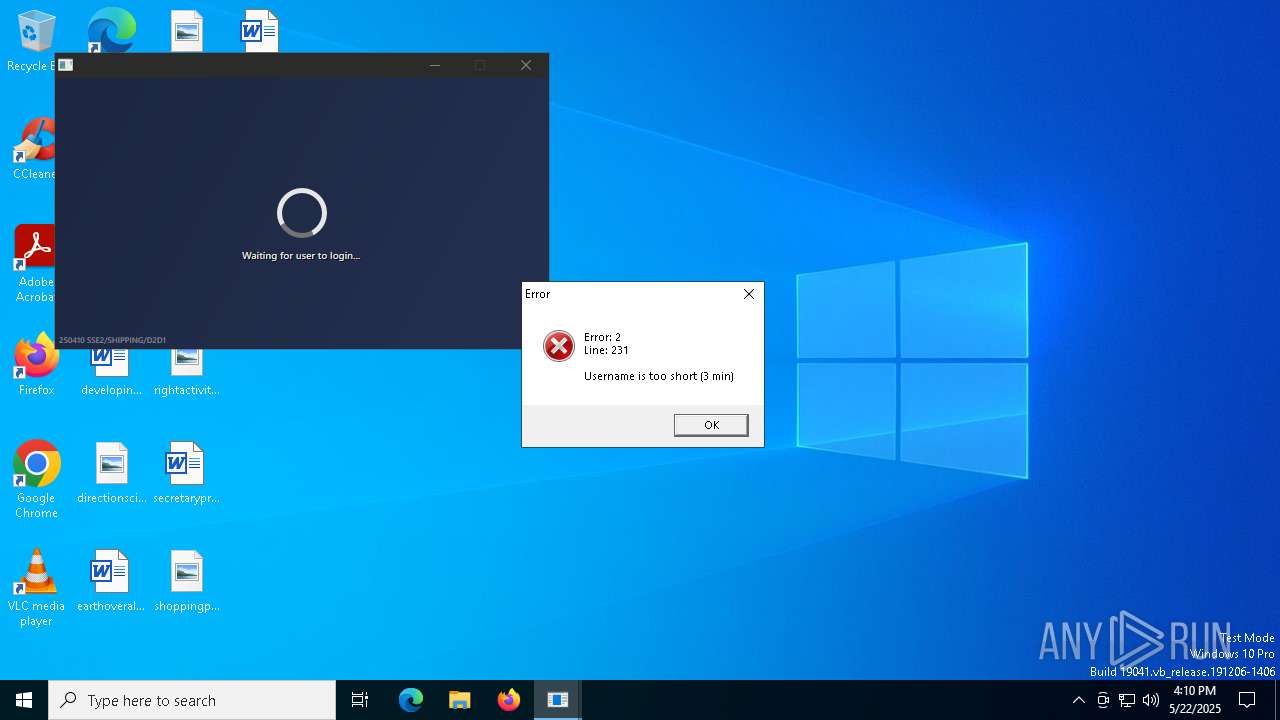
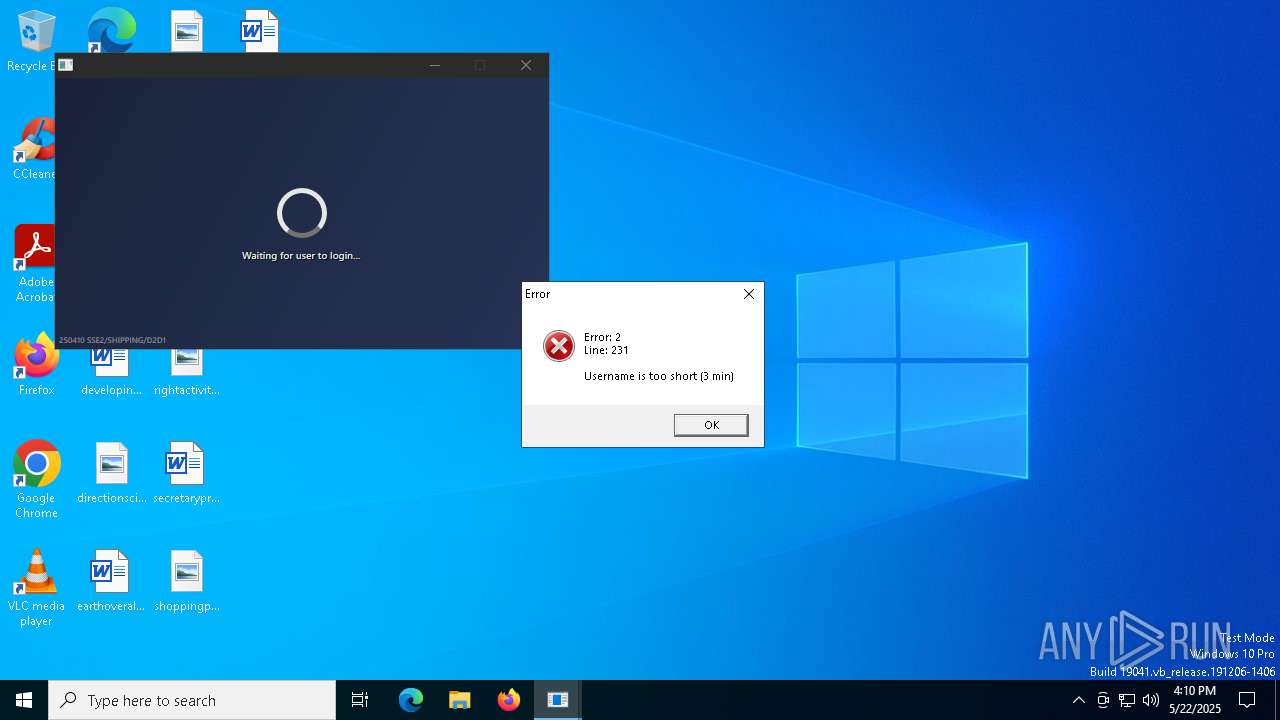
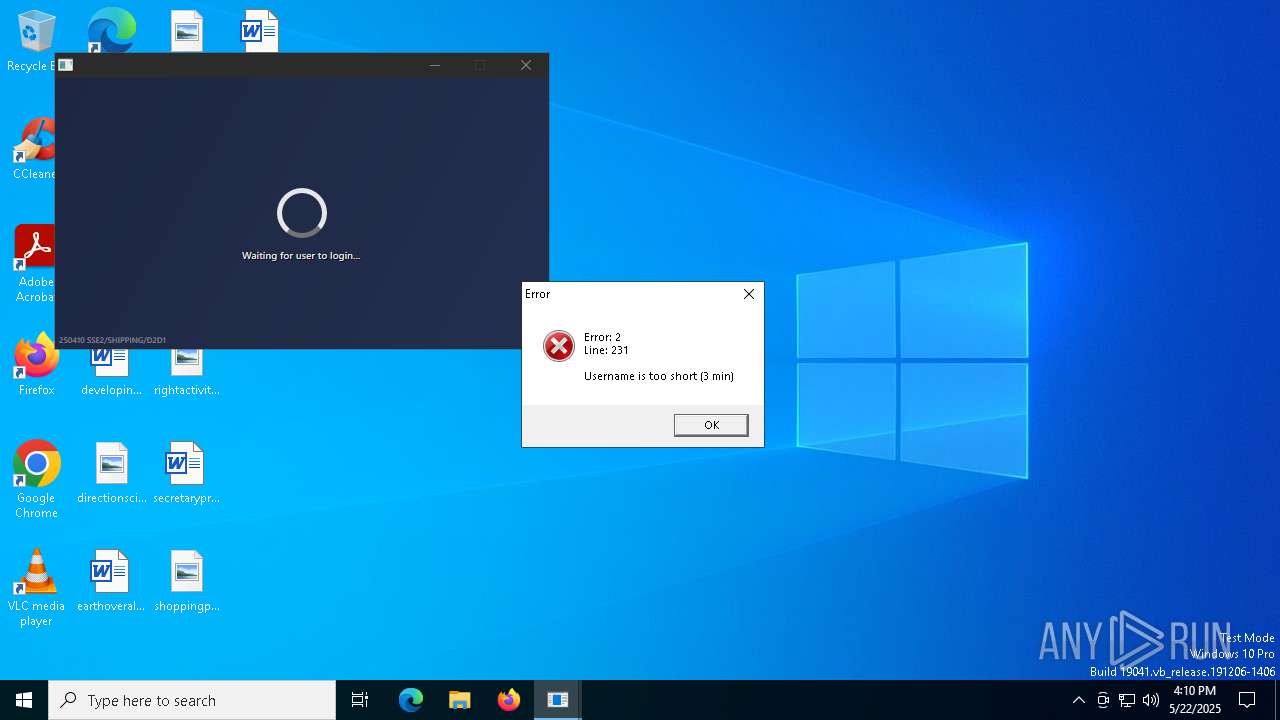
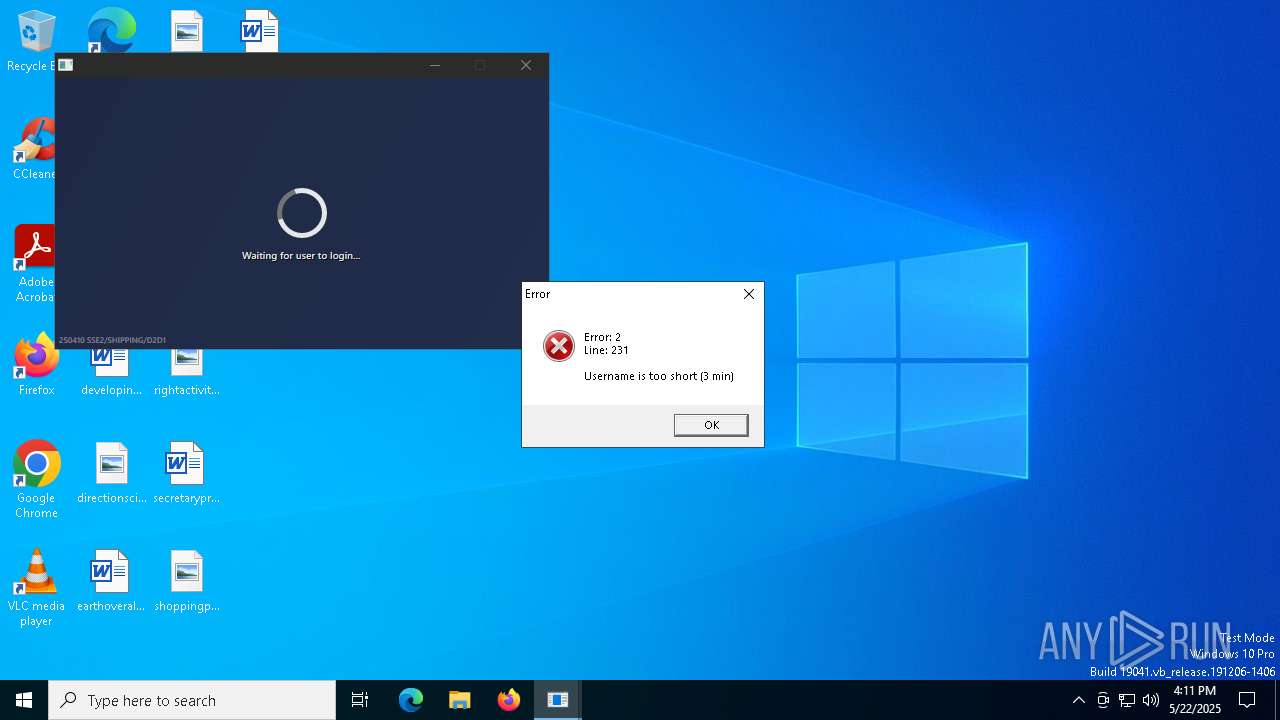
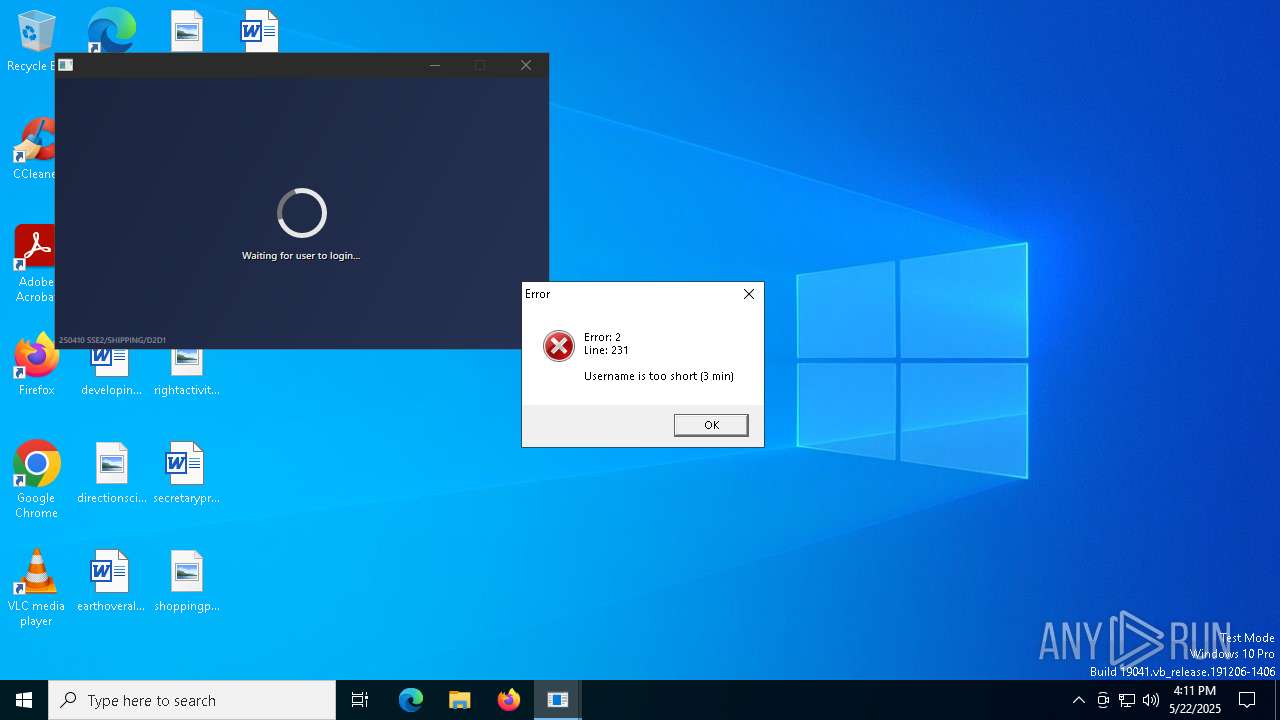
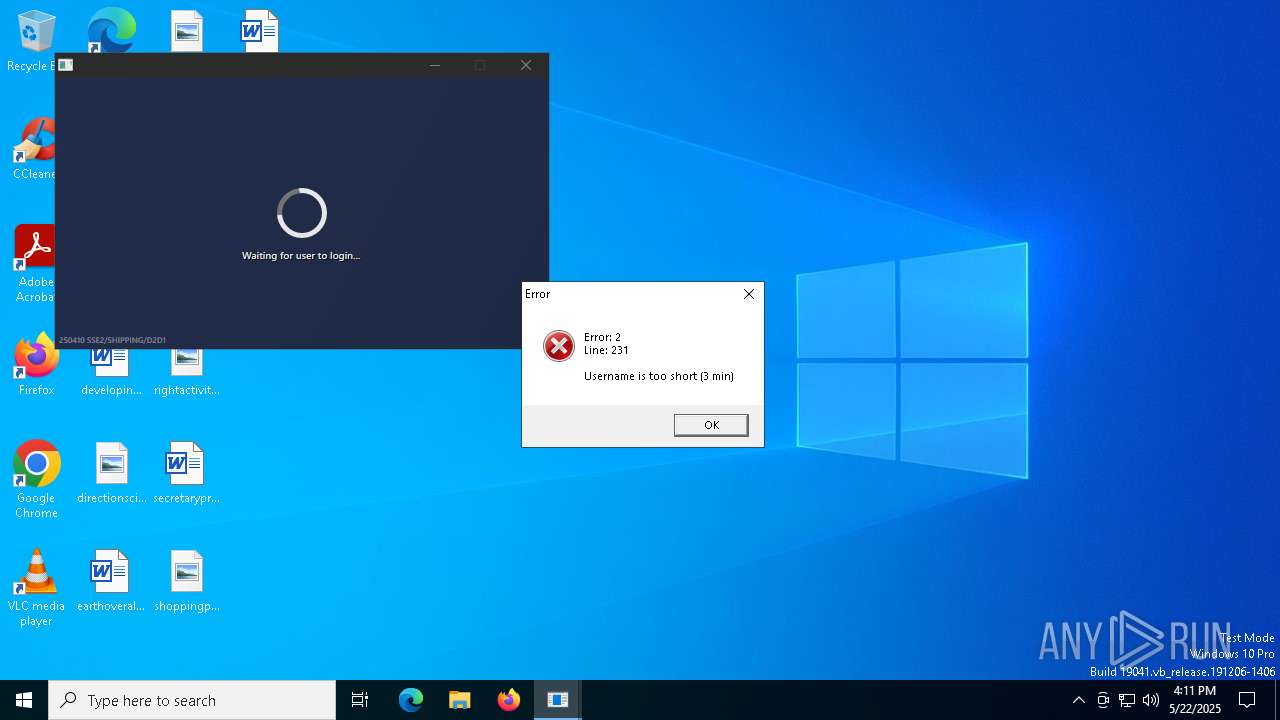
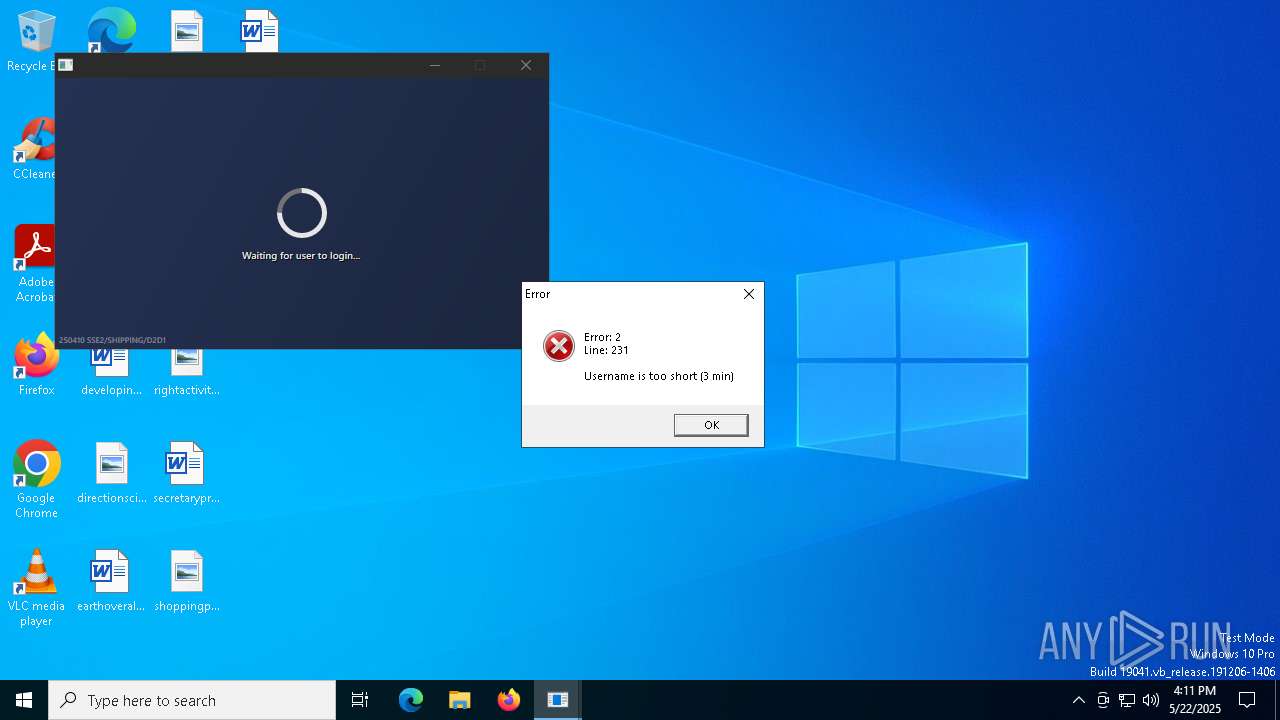
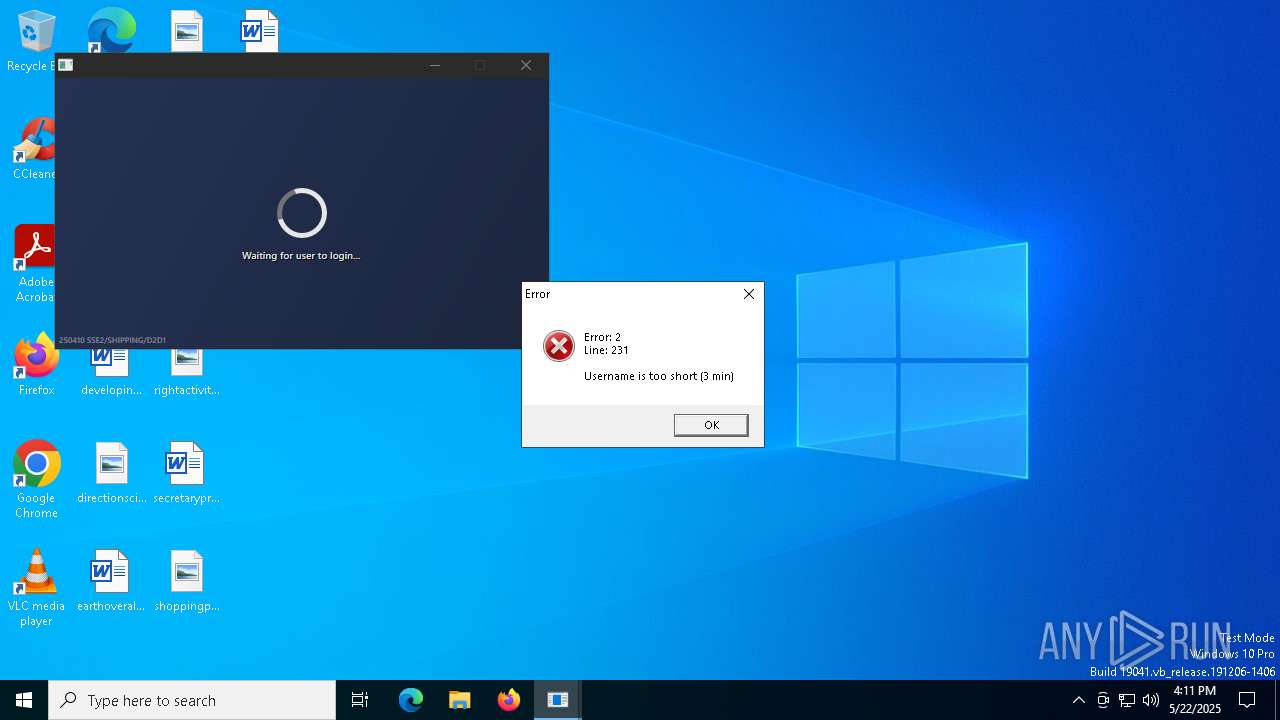
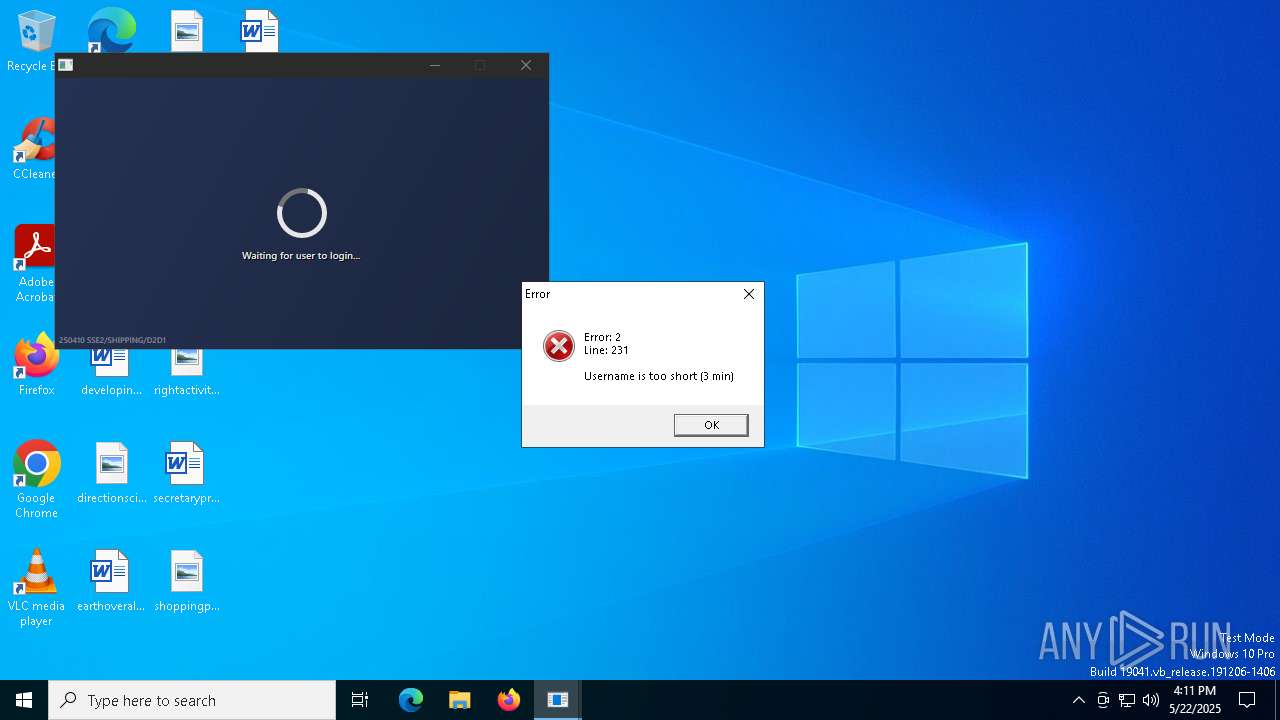
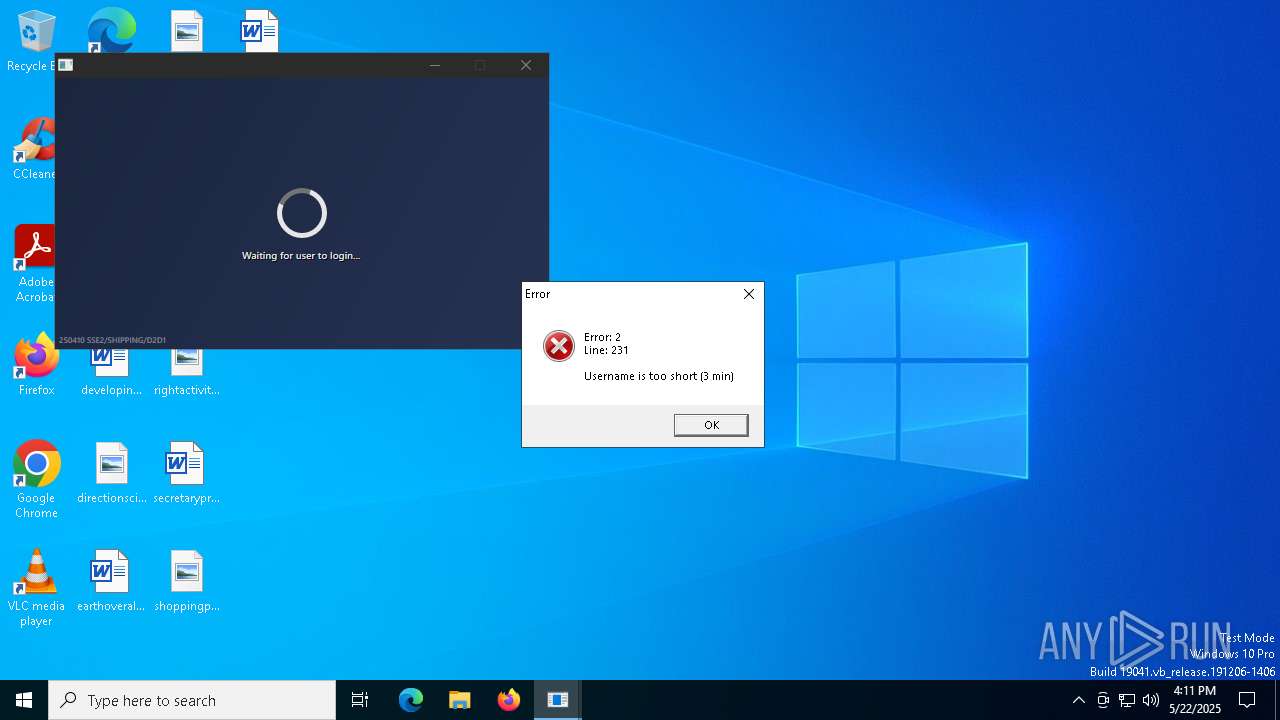
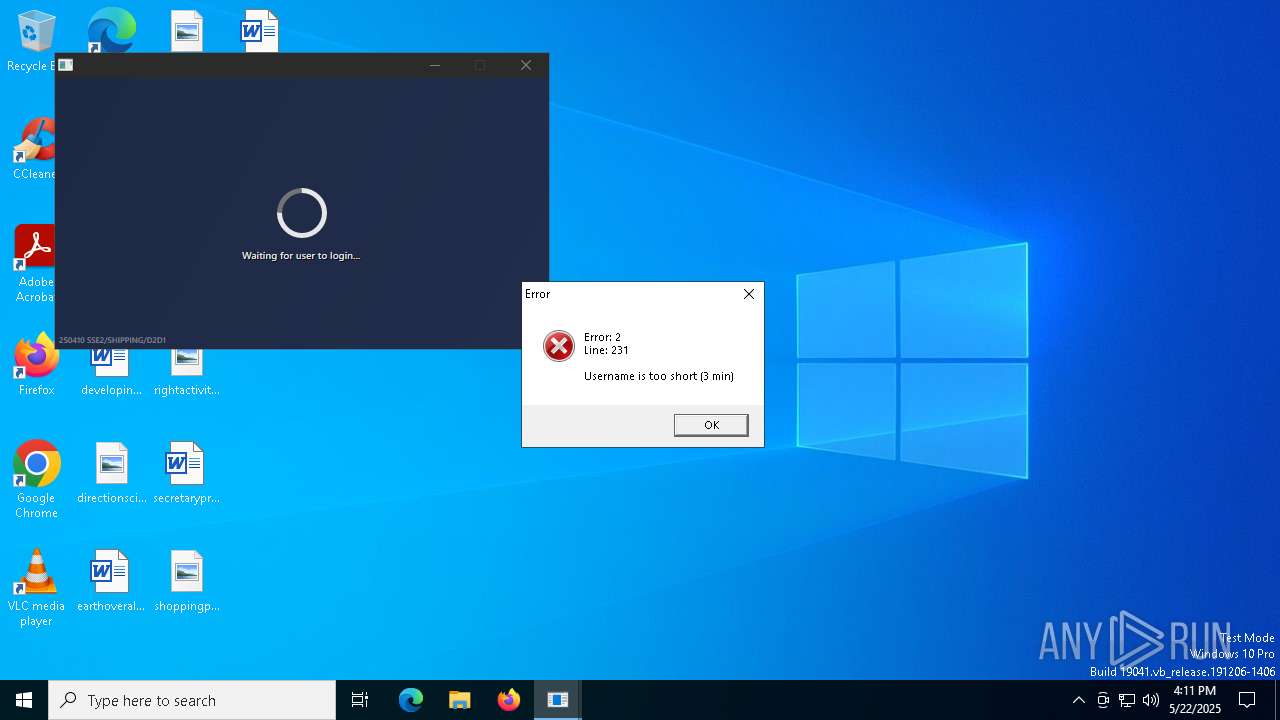
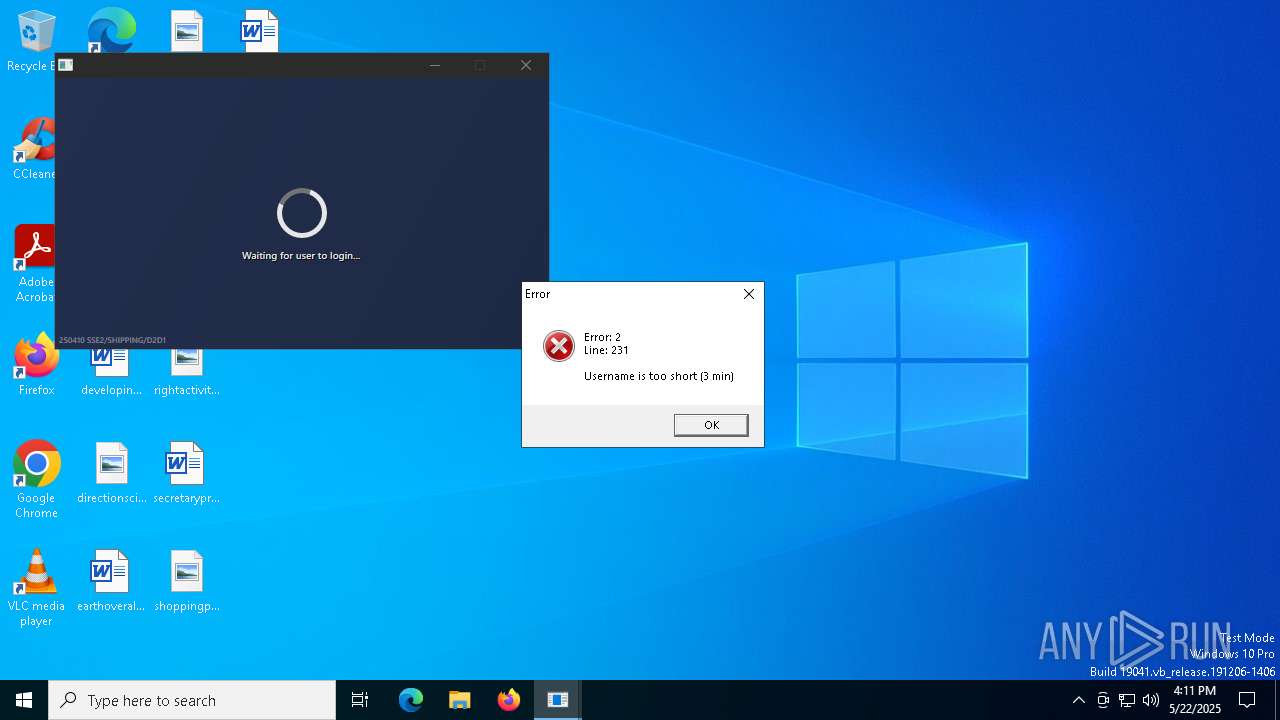
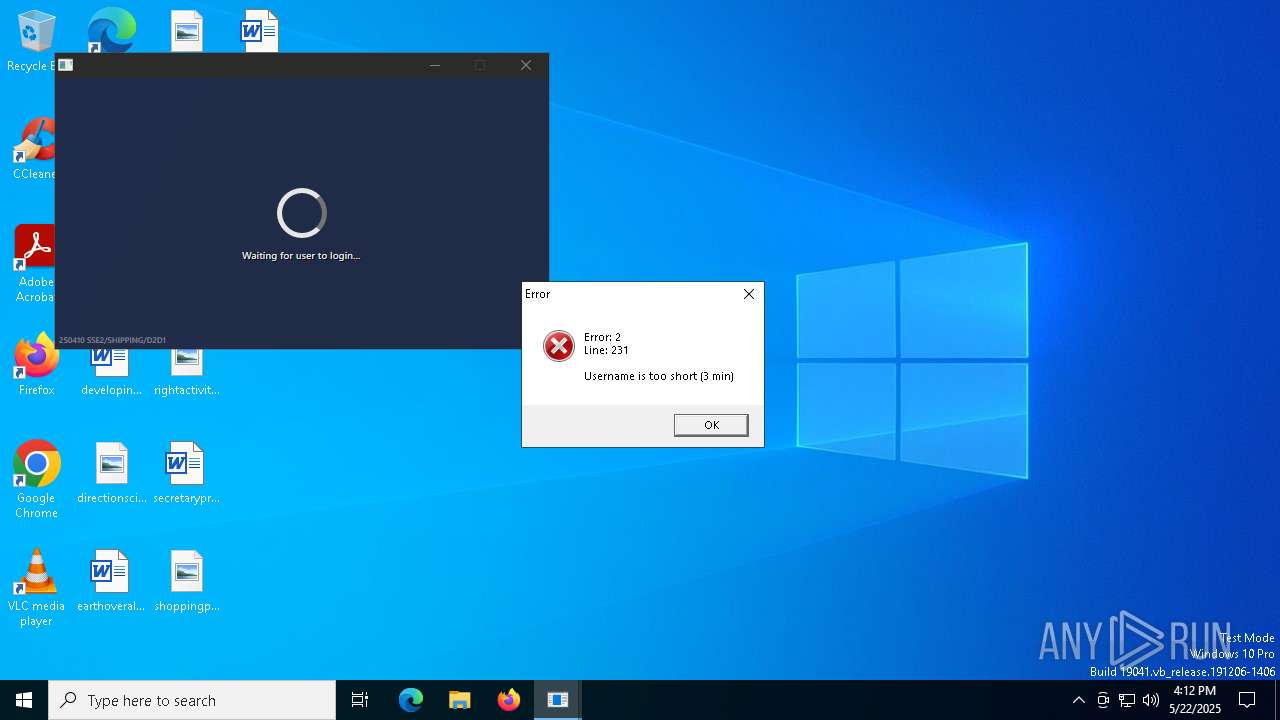
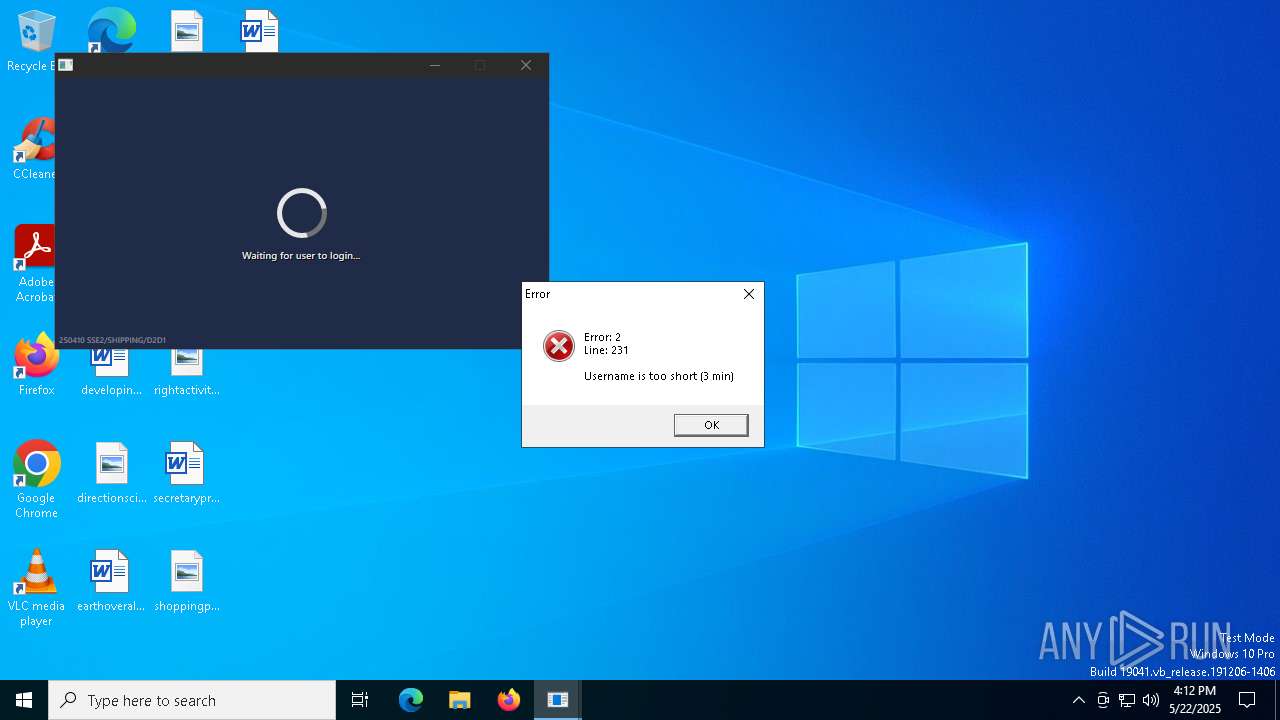
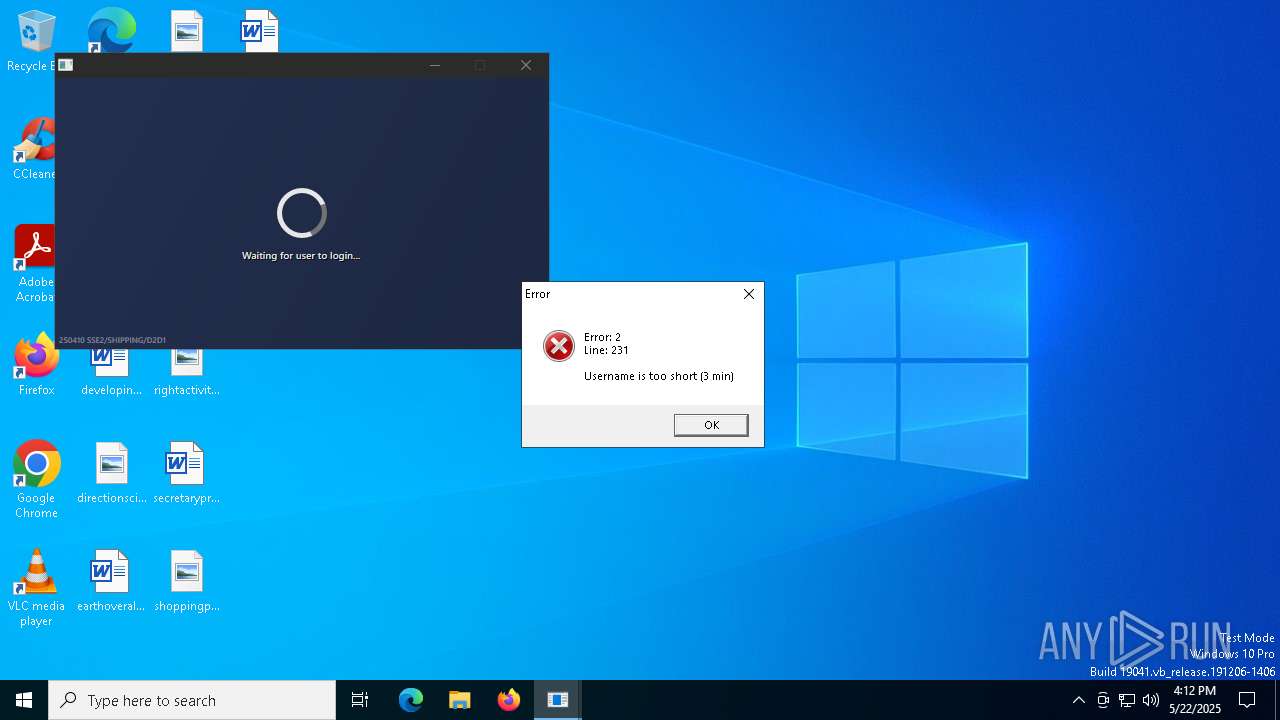
| Verdict: | Malicious activity |
| Analysis date: | May 22, 2025, 16:09:34 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64 (stripped to external PDB), for MS Windows, 19 sections |
| MD5: | 7FFB934110BD950E441697C1992A1884 |
| SHA1: | DDEE0813F4B07A7E063751D7EB6045284D395EF1 |
| SHA256: | 51A50926C9E0168FDF9D8413FF94963A8C793B968E9520D930FF2A0D0C7C5B5F |
| SSDEEP: | 98304:jL5YmIcOJC1sgBu4qUifYYitn8uOs5e6z9qwEm8NwVHlaW5sRoESNehiHiL3PRrw:DCYjpl2Af |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the BIOS version
- 2687cce9b128142e1abe21d641.exe (PID: 1312)
Reads security settings of Internet Explorer
- 2687cce9b128142e1abe21d641.exe (PID: 1312)
INFO
Process checks whether UAC notifications are on
- 2687cce9b128142e1abe21d641.exe (PID: 1312)
Checks proxy server information
- 2687cce9b128142e1abe21d641.exe (PID: 1312)
- slui.exe (PID: 4272)
Checks supported languages
- 2687cce9b128142e1abe21d641.exe (PID: 1312)
Reads the computer name
- 2687cce9b128142e1abe21d641.exe (PID: 1312)
Reads the software policy settings
- 2687cce9b128142e1abe21d641.exe (PID: 1312)
- slui.exe (PID: 4272)
Reads the machine GUID from the registry
- 2687cce9b128142e1abe21d641.exe (PID: 1312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (49.6) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.5) |
| .vxd | | | VXD Driver (0.7) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:04:10 13:04:07+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Large address aware, No debug |
| PEType: | PE32+ |
| LinkerVersion: | 2.44 |
| CodeSize: | 5767168 |
| InitializedDataSize: | 4956672 |
| UninitializedDataSize: | 7168 |
| EntryPoint: | 0xb5a058 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
Total processes
121
Monitored processes
4
Malicious processes
0
Suspicious processes
1
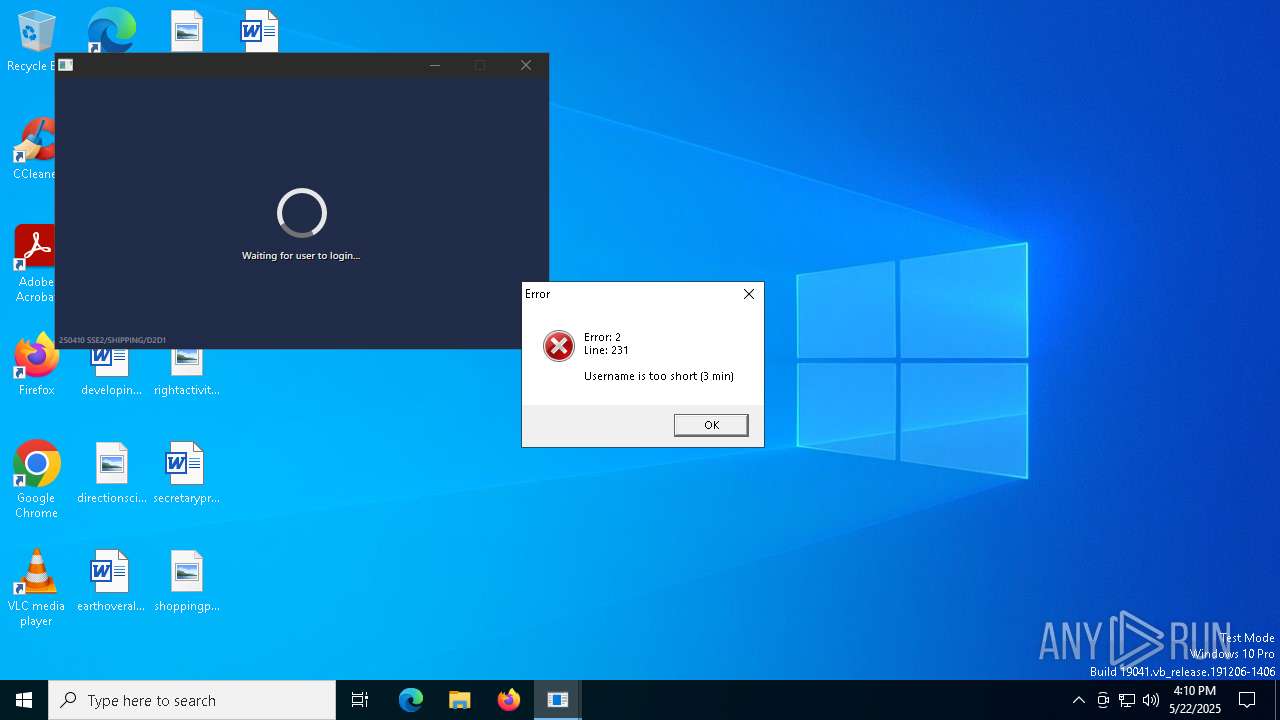
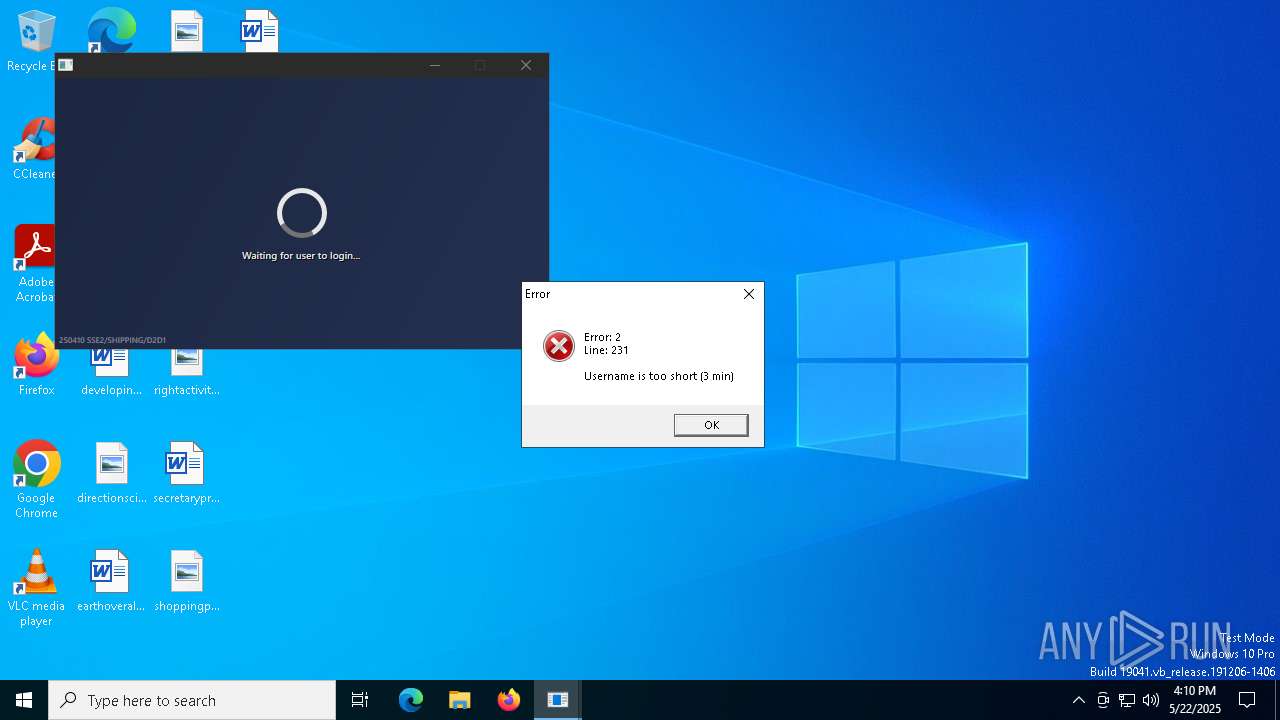
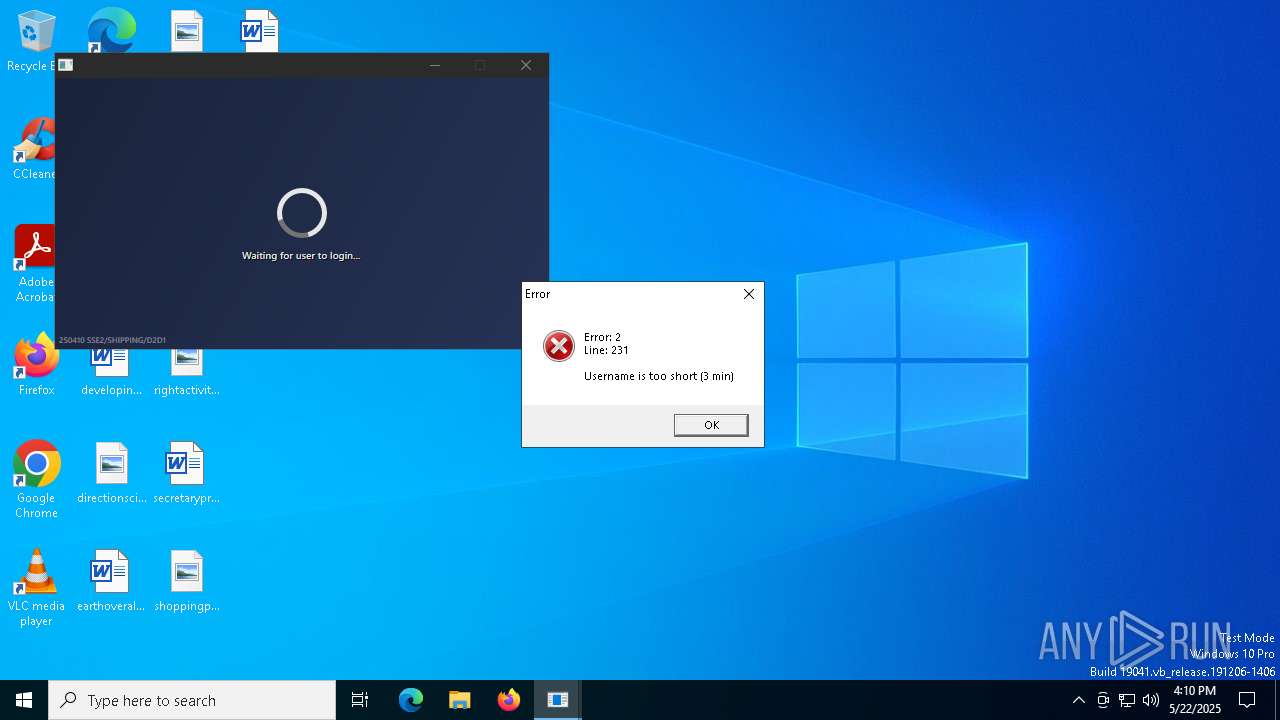
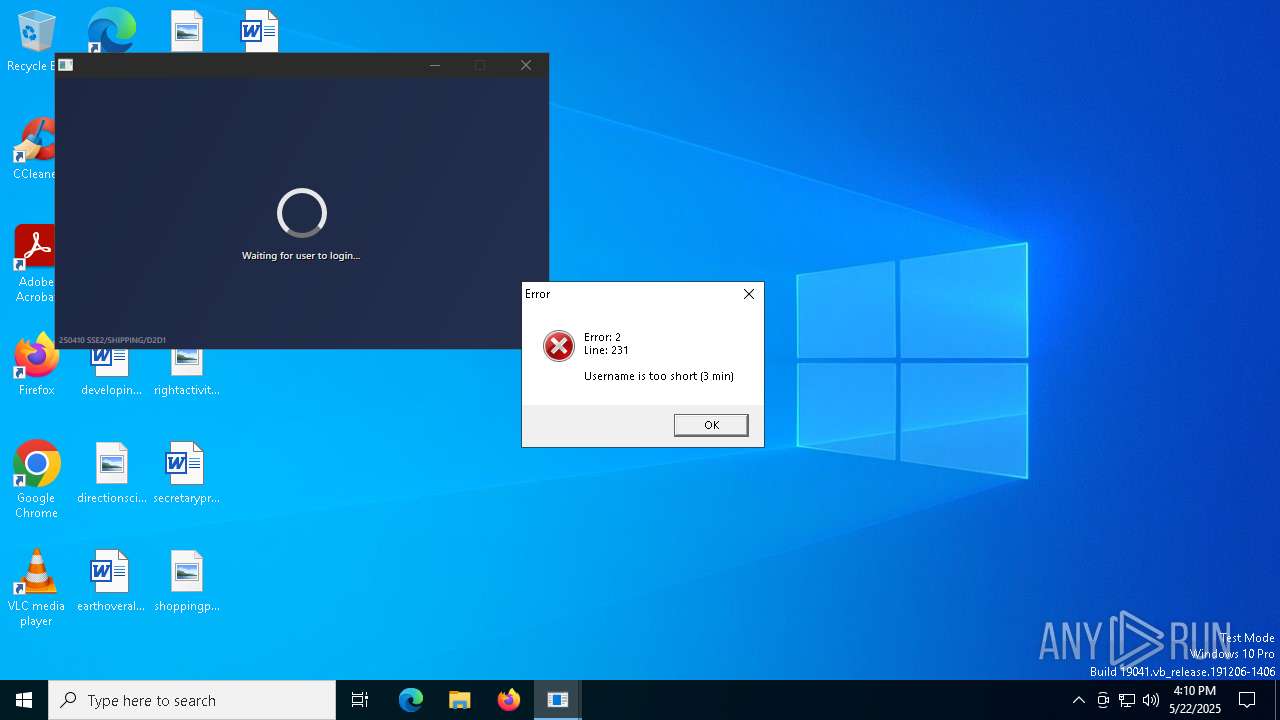
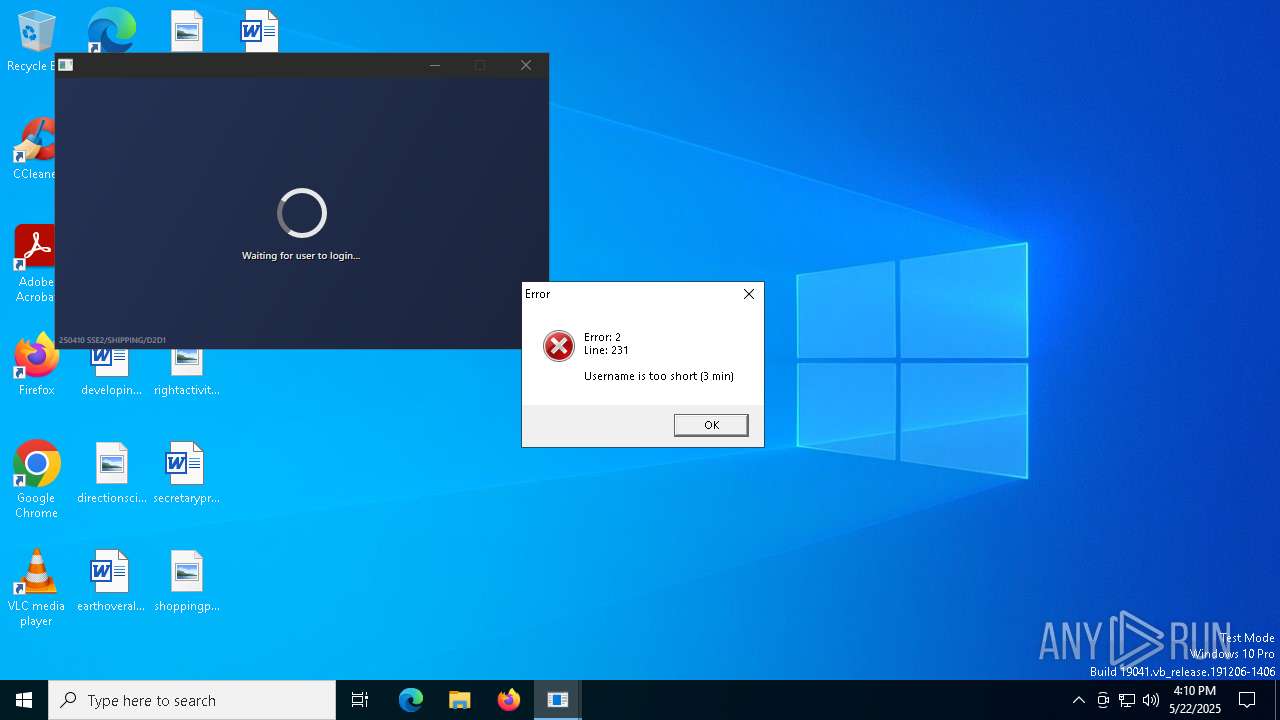
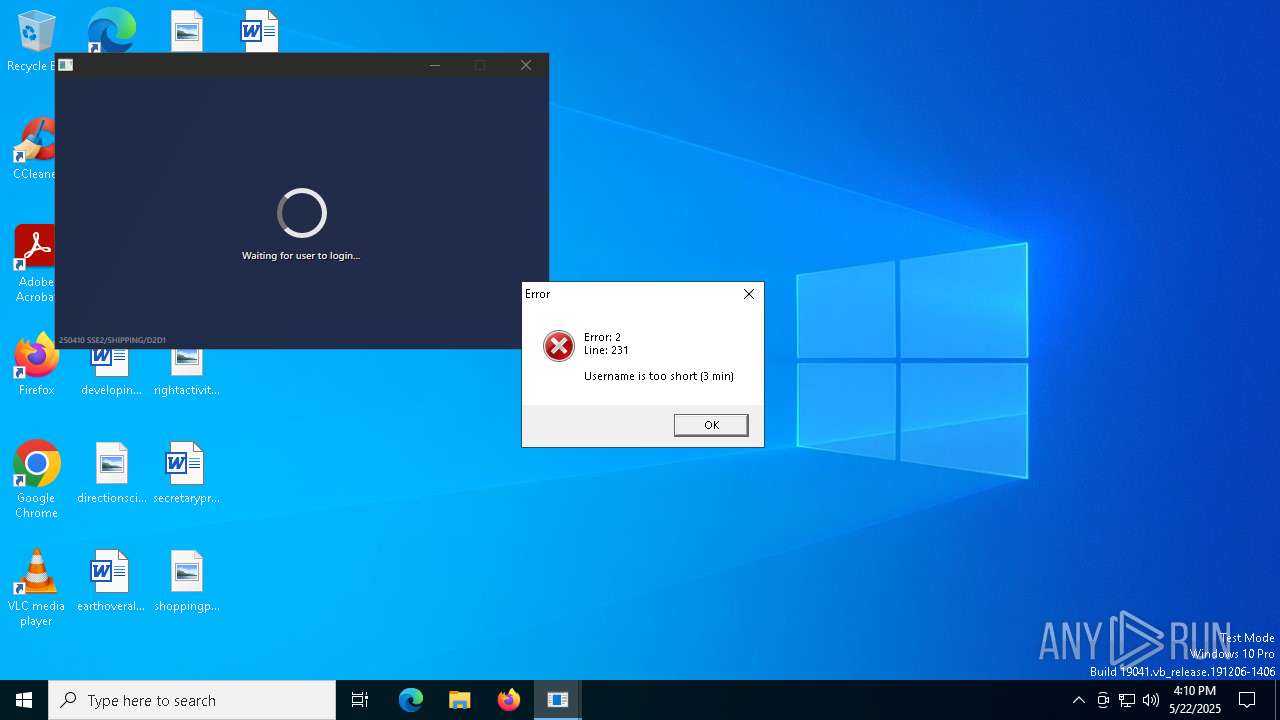
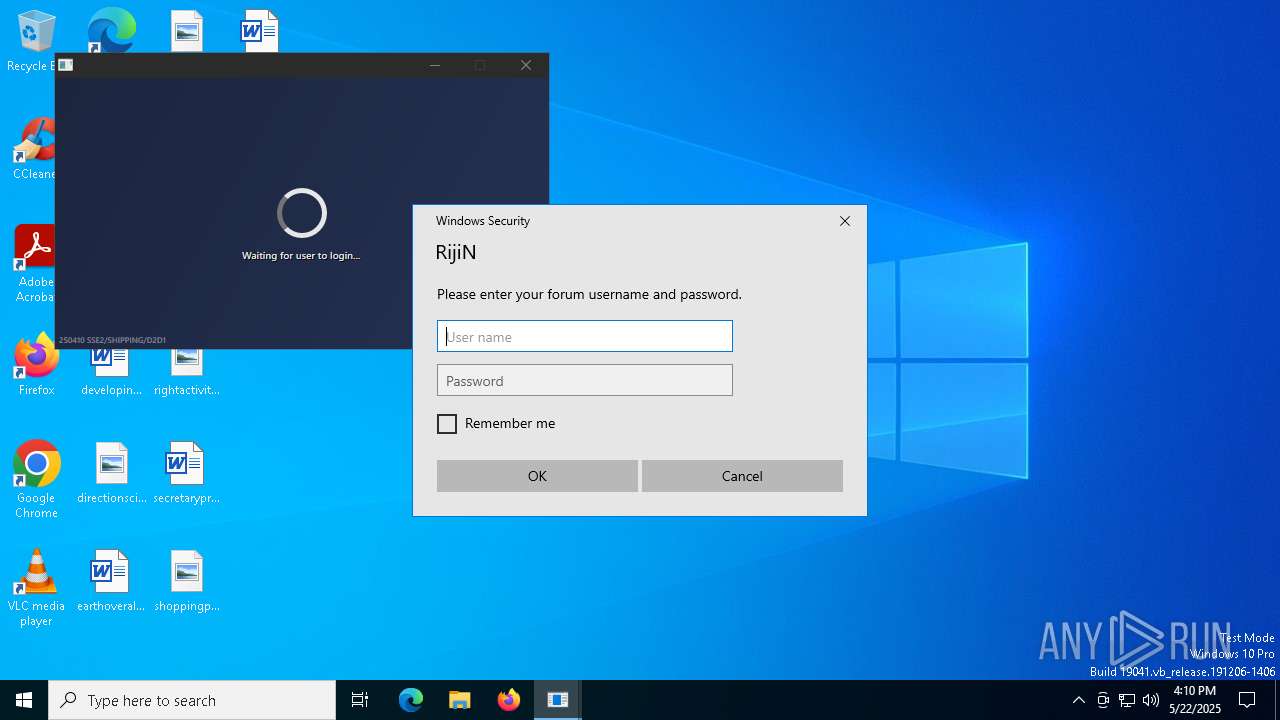
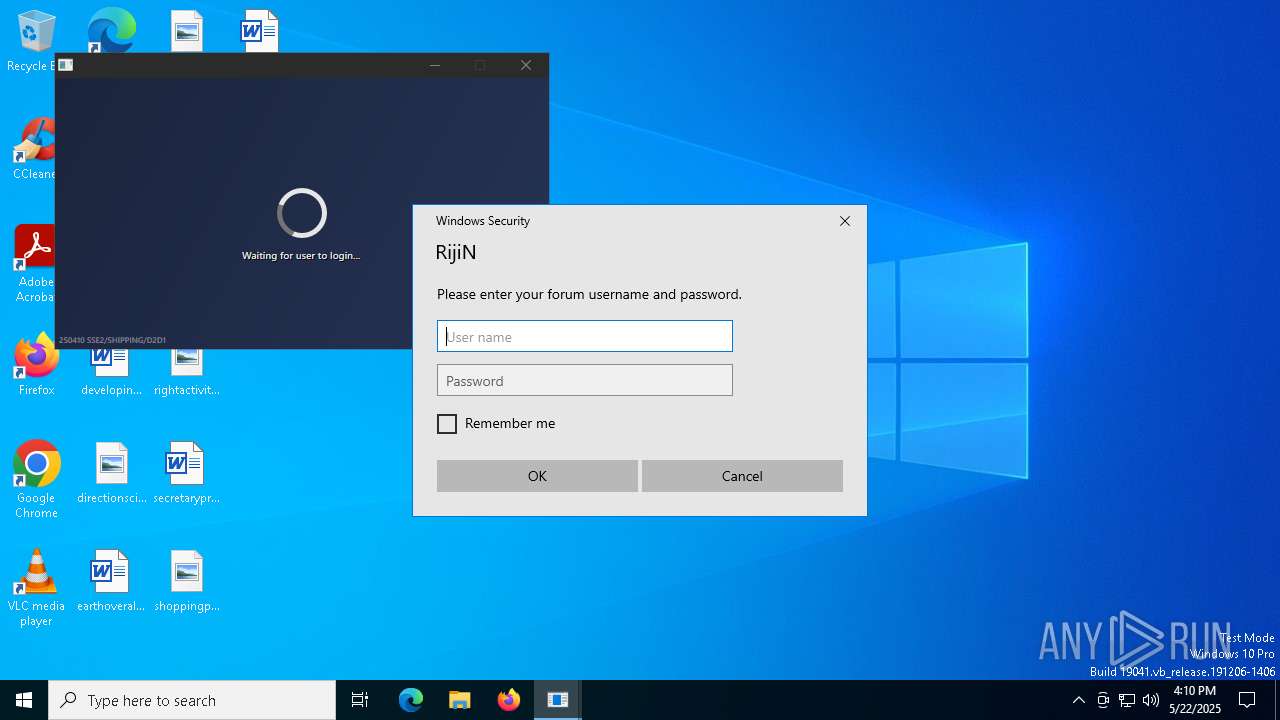
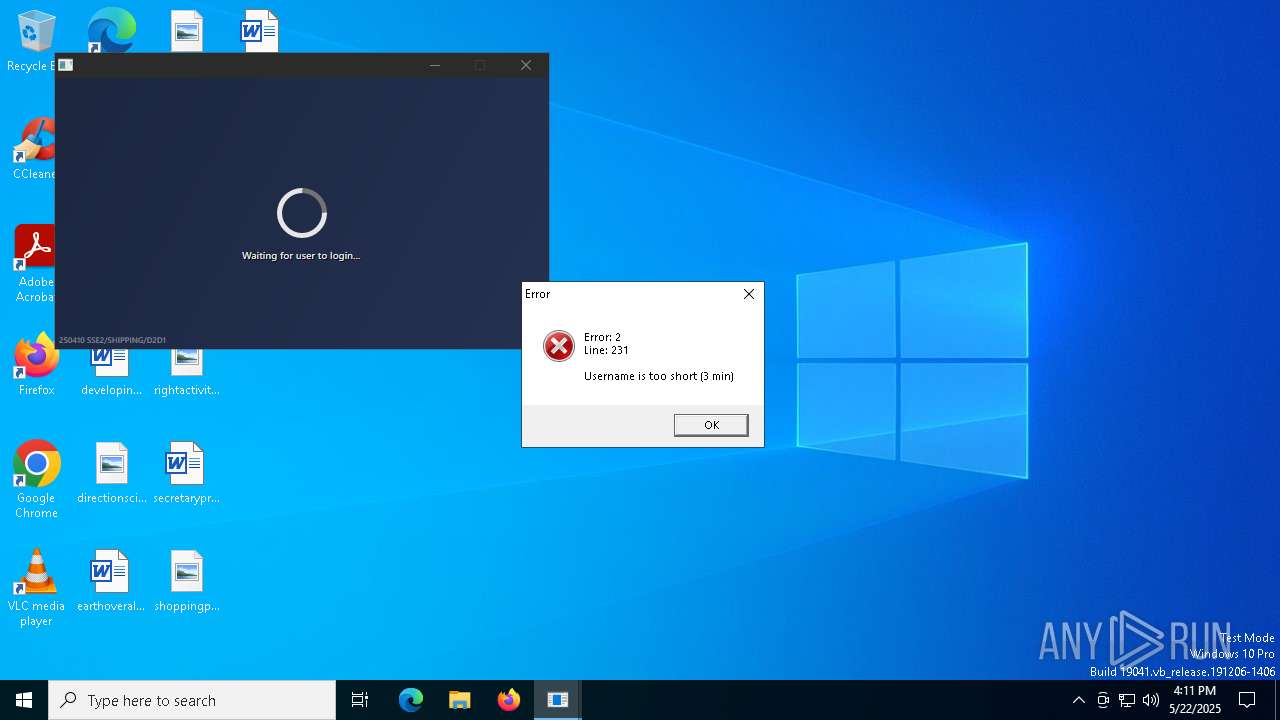
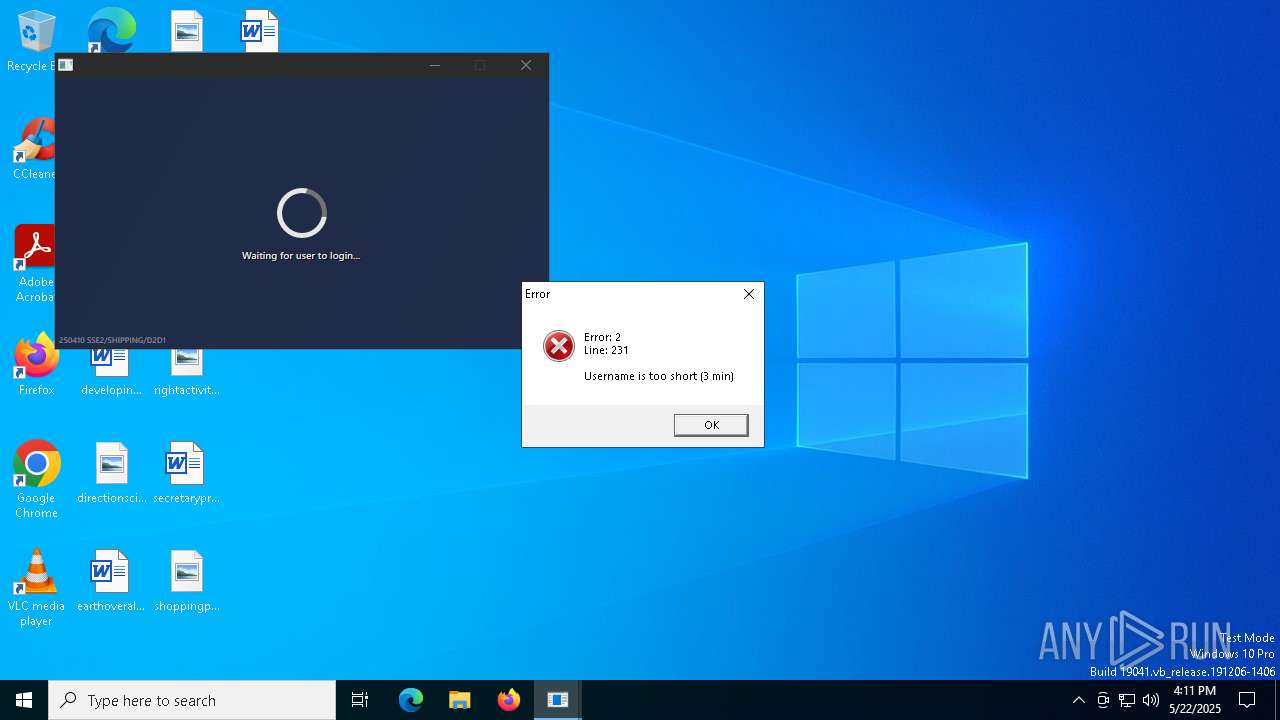
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1180 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 2687cce9b128142e1abe21d641.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1312 | "C:\Users\admin\Desktop\2687cce9b128142e1abe21d641.exe" | C:\Users\admin\Desktop\2687cce9b128142e1abe21d641.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 4272 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4776 | "C:\Users\admin\Desktop\2687cce9b128142e1abe21d641.exe" | C:\Users\admin\Desktop\2687cce9b128142e1abe21d641.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
11 180
Read events
11 095
Write events
85
Delete events
0
Modification events
| (PID) Process: | (1312) 2687cce9b128142e1abe21d641.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1312) 2687cce9b128142e1abe21d641.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1312) 2687cce9b128142e1abe21d641.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
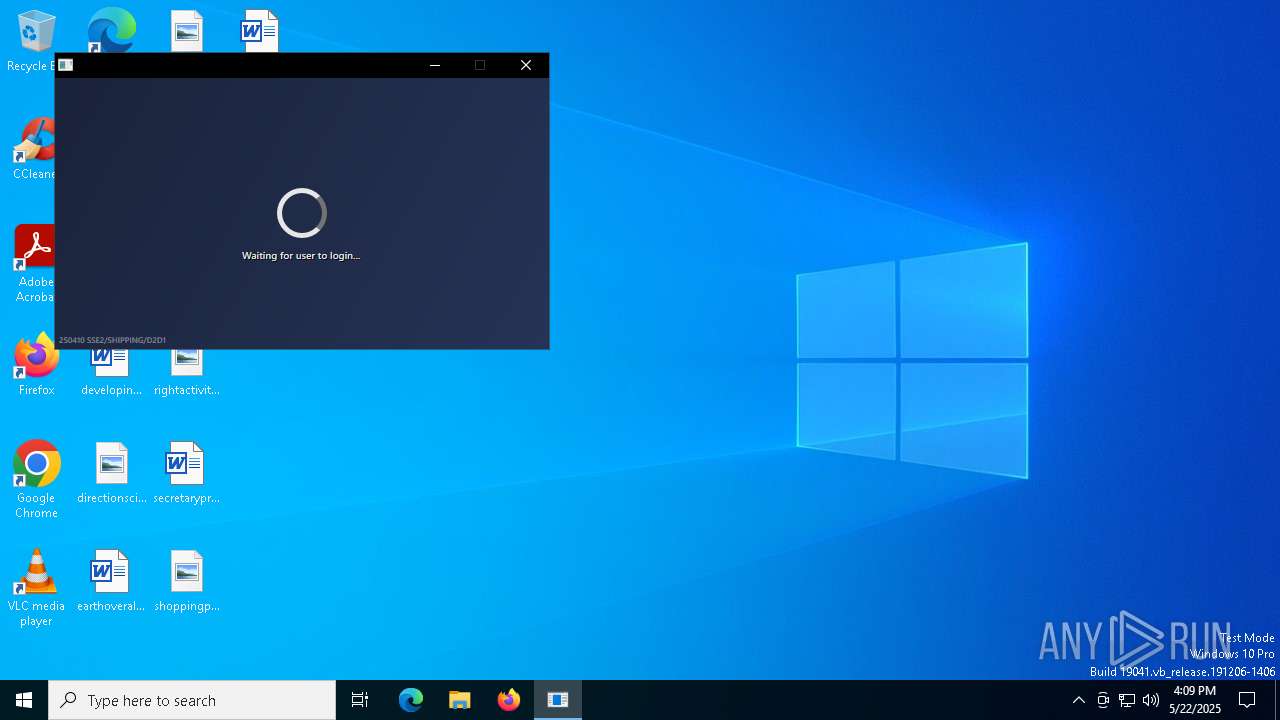
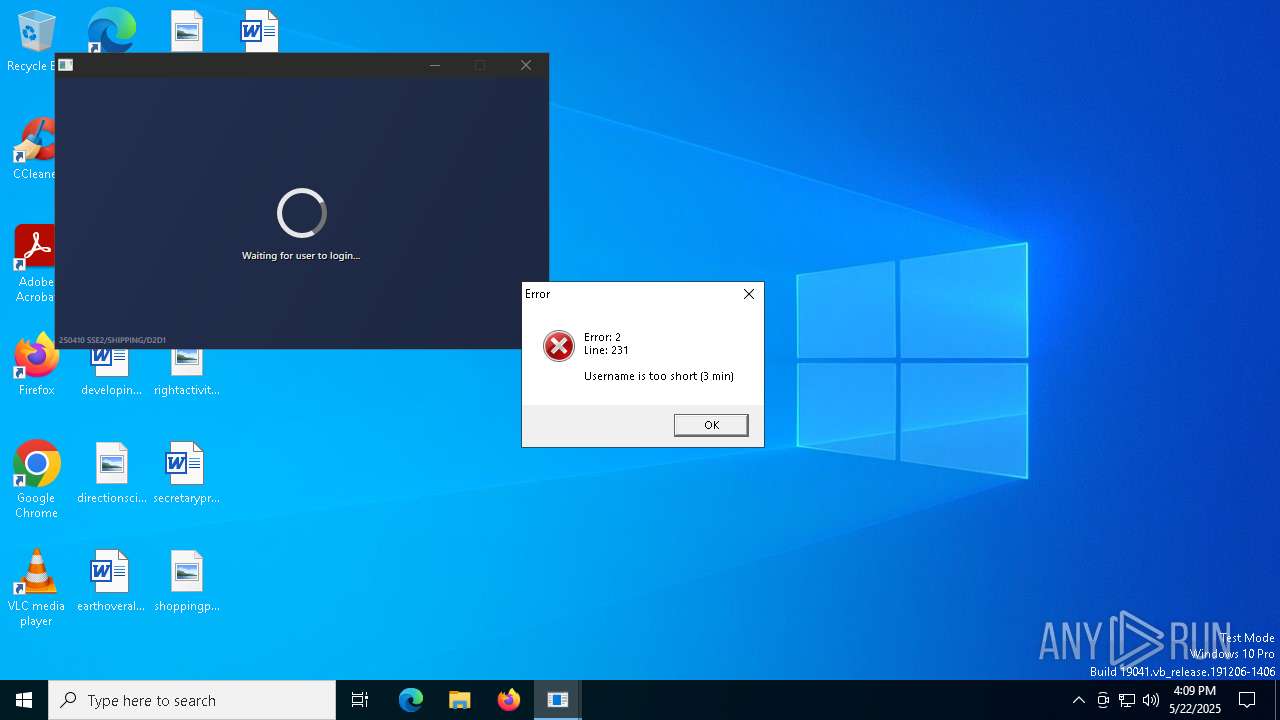
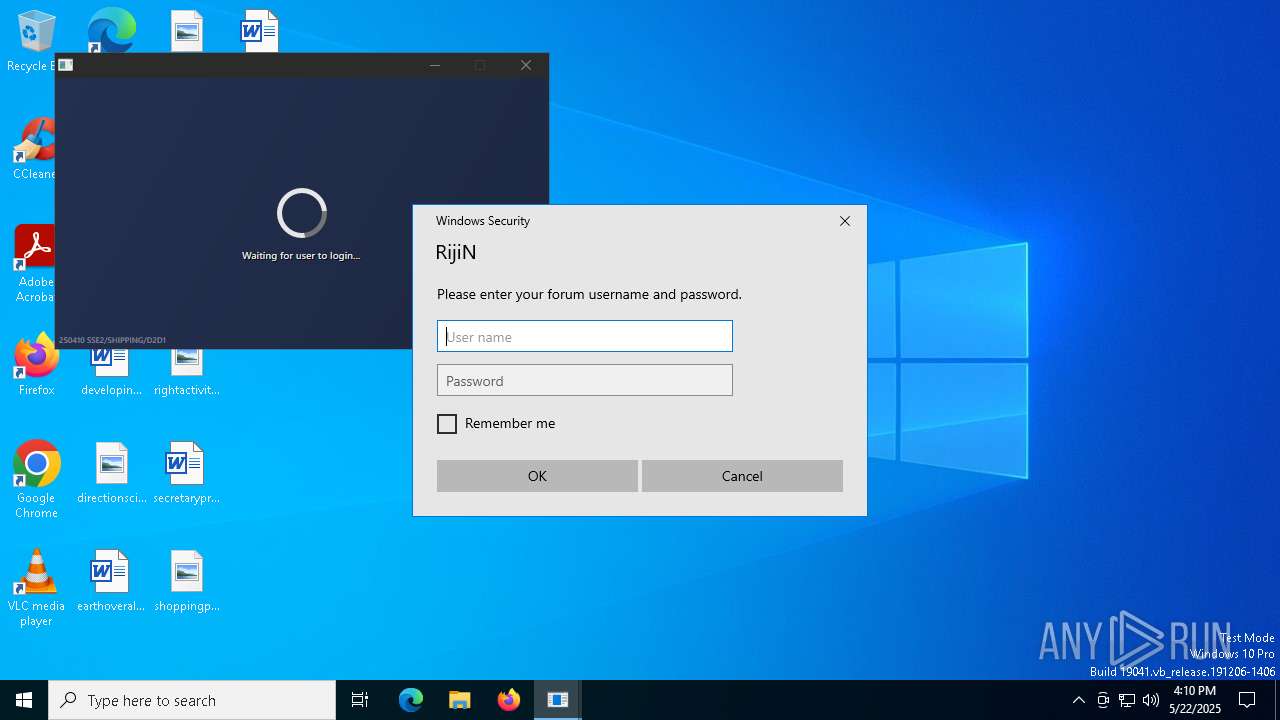
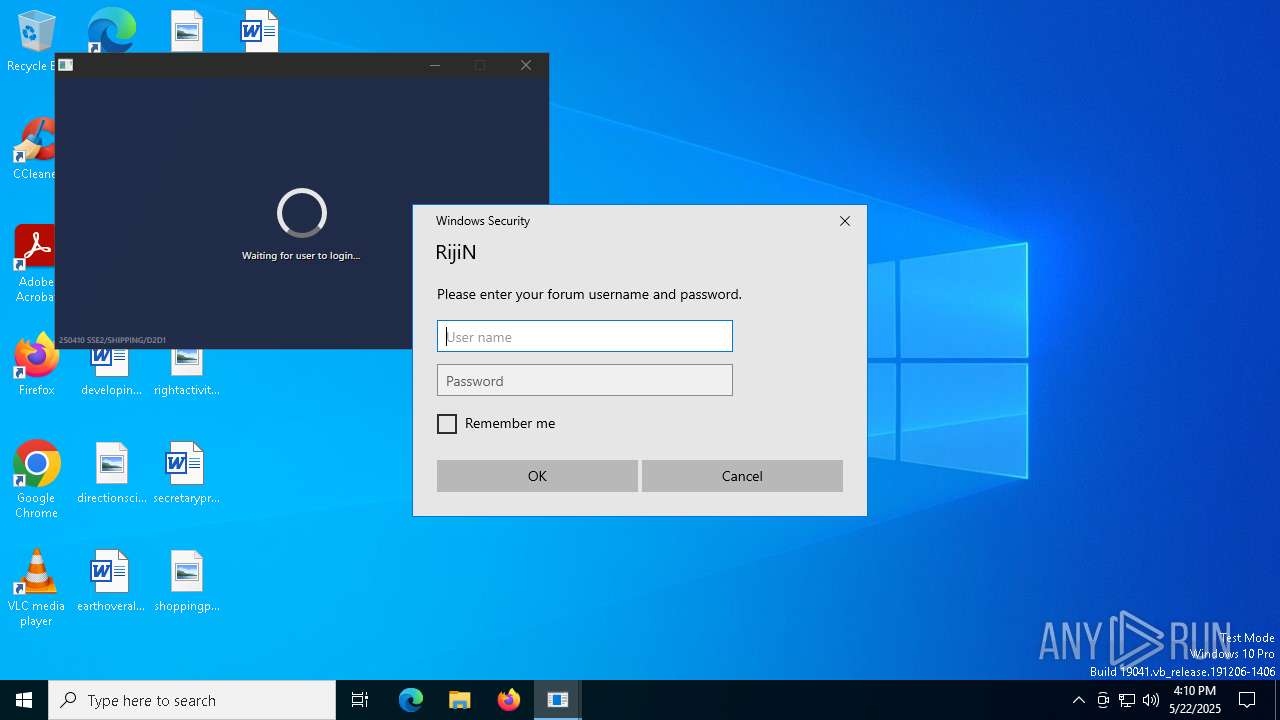
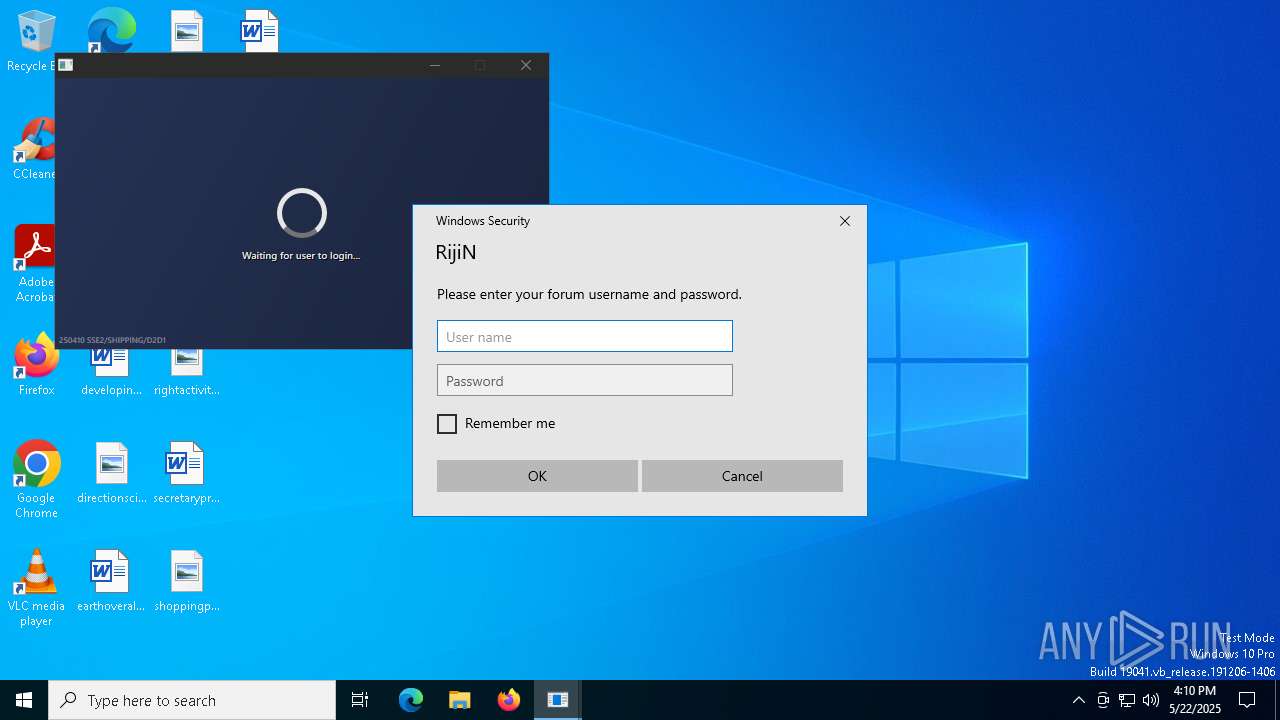
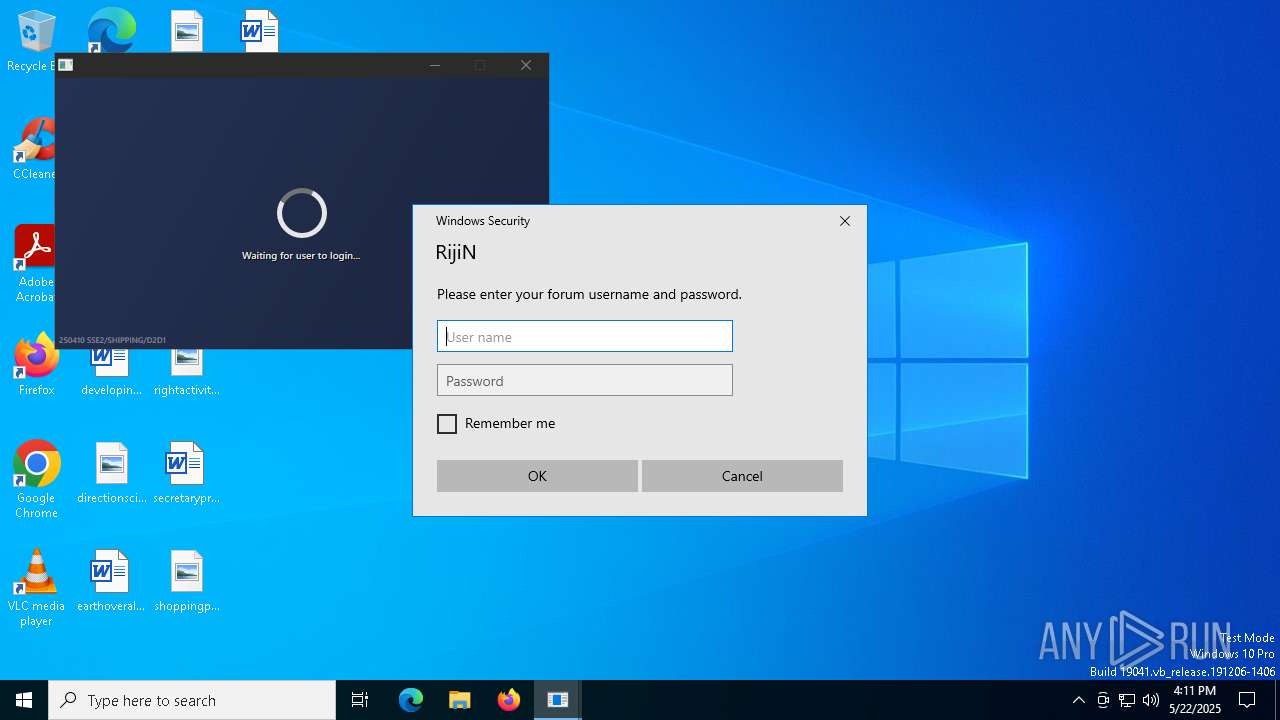
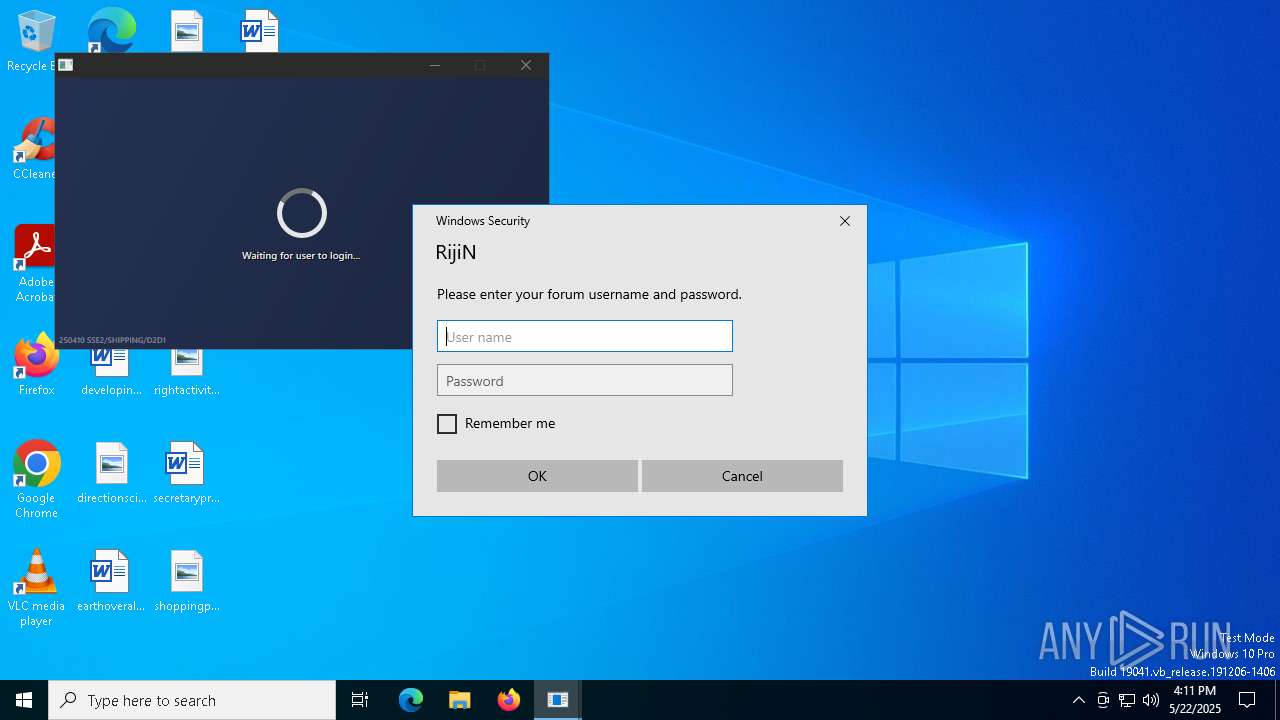
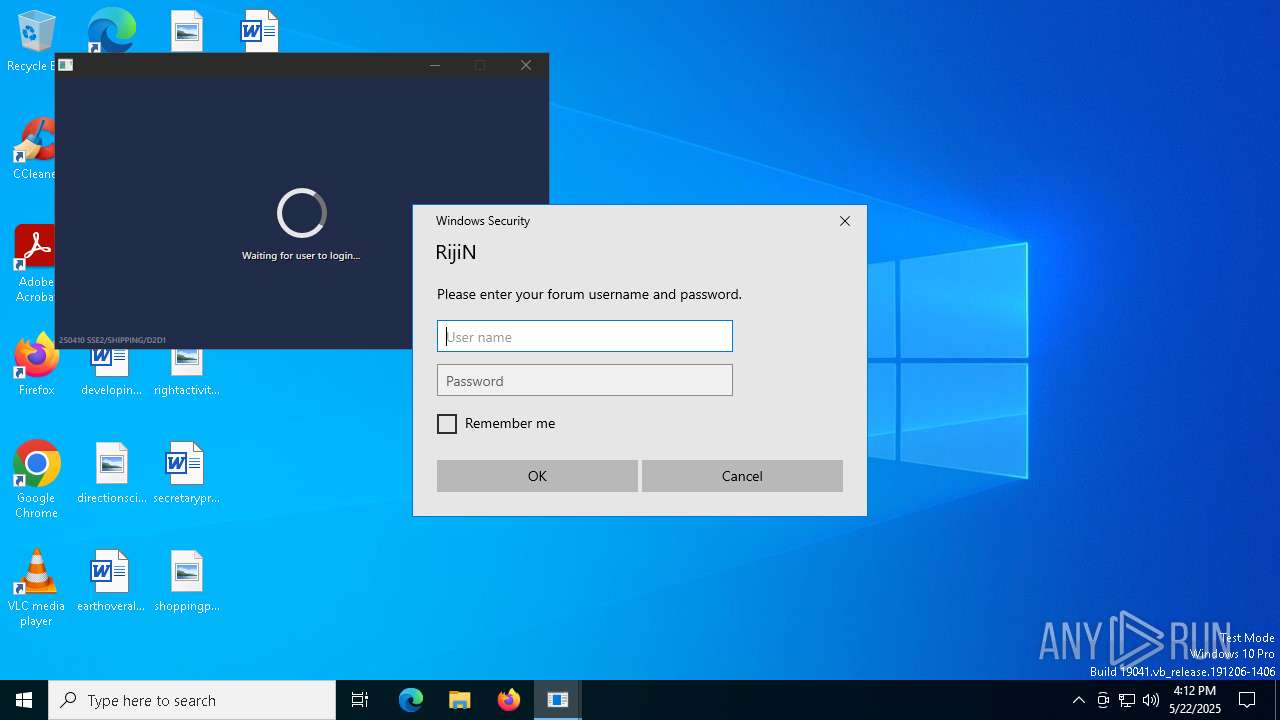
| (PID) Process: | (1312) 2687cce9b128142e1abe21d641.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Authentication\LogonUI\FaceLogon |
| Operation: | write | Name: | CredProvUncompletedInstances |
Value: 1 | |||
| (PID) Process: | (1312) 2687cce9b128142e1abe21d641.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Authentication\LogonUI\FaceLogon |
| Operation: | write | Name: | CredProvUncompletedInstances |
Value: 2 | |||
| (PID) Process: | (1312) 2687cce9b128142e1abe21d641.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Authentication\LogonUI\FaceLogon |
| Operation: | write | Name: | CredProvUncompletedInstances |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
20
DNS requests
7
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
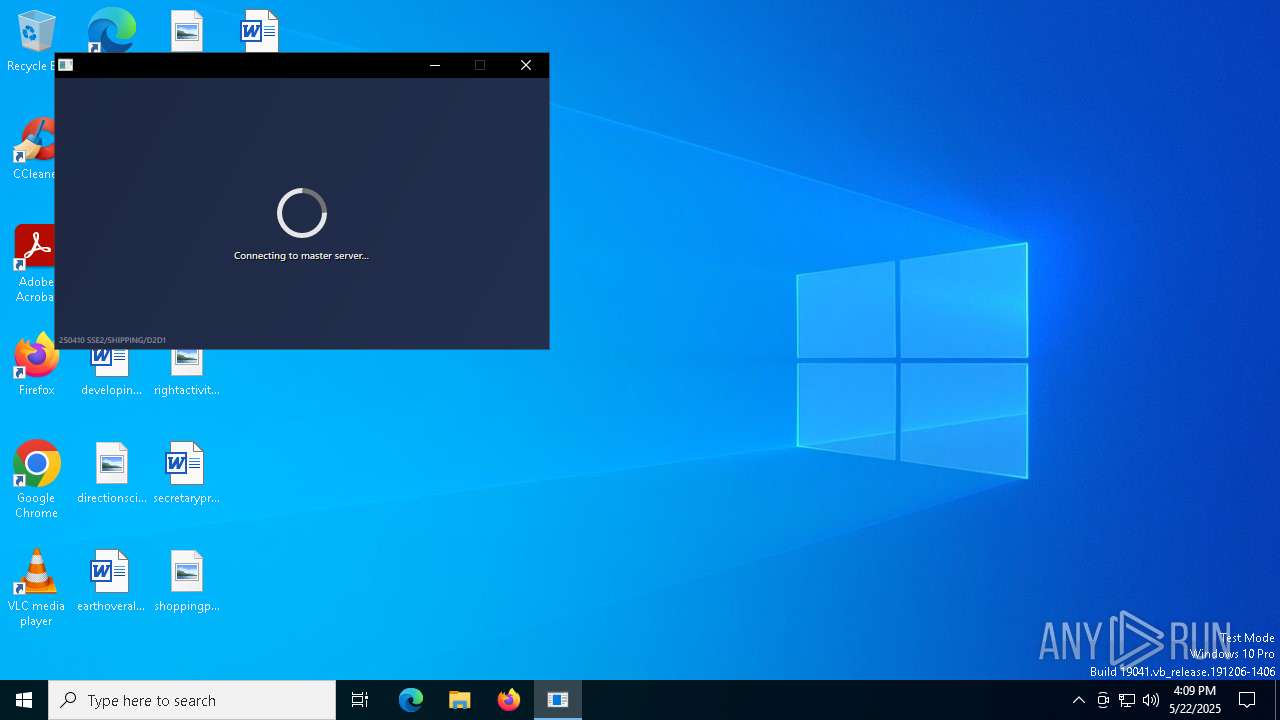
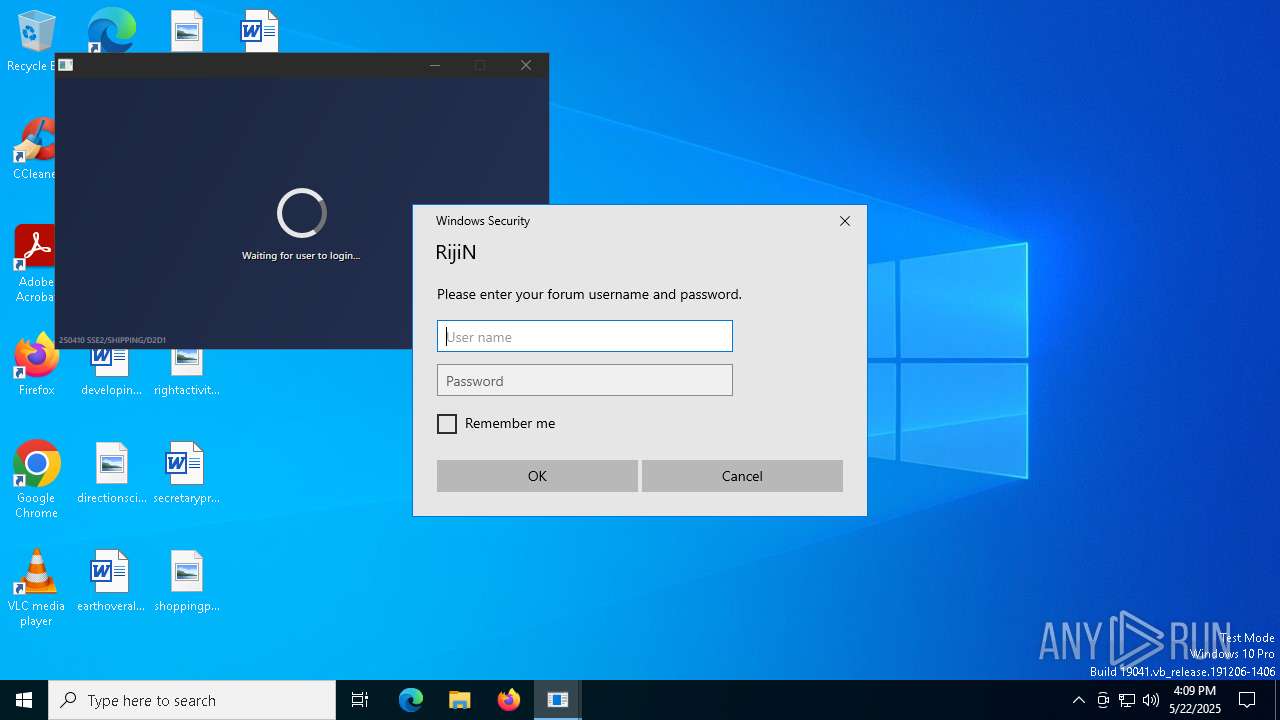
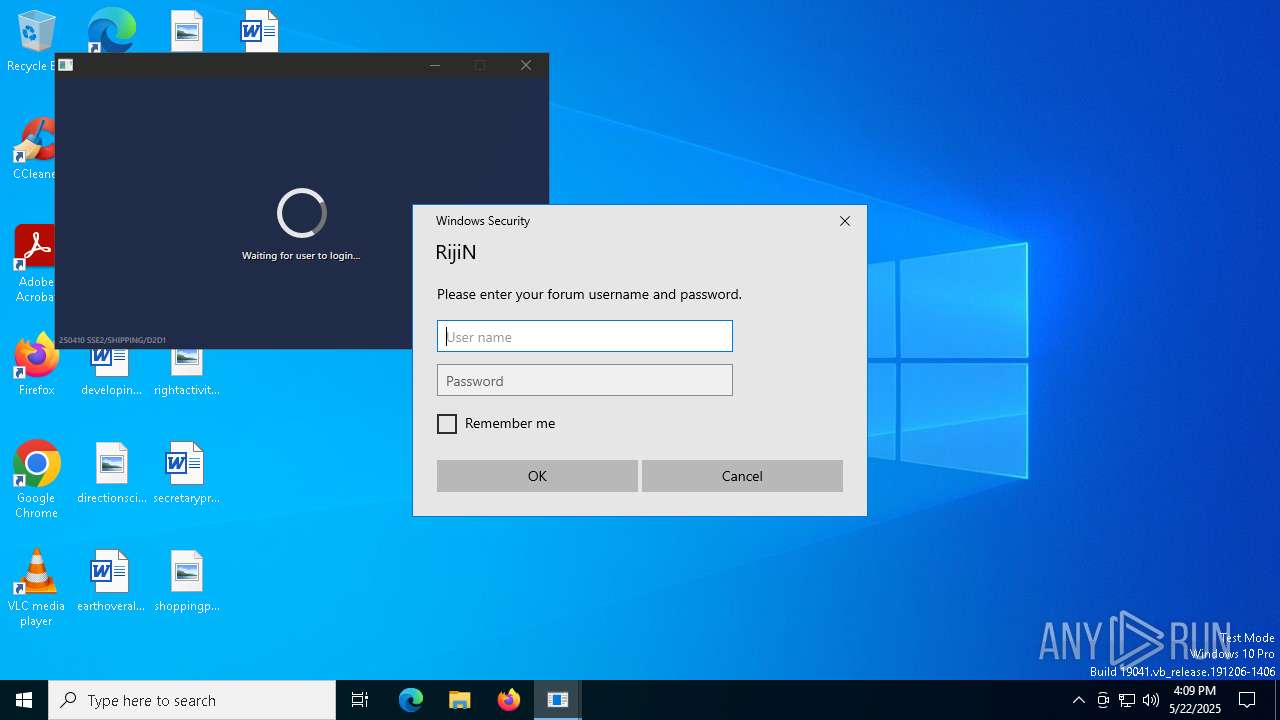
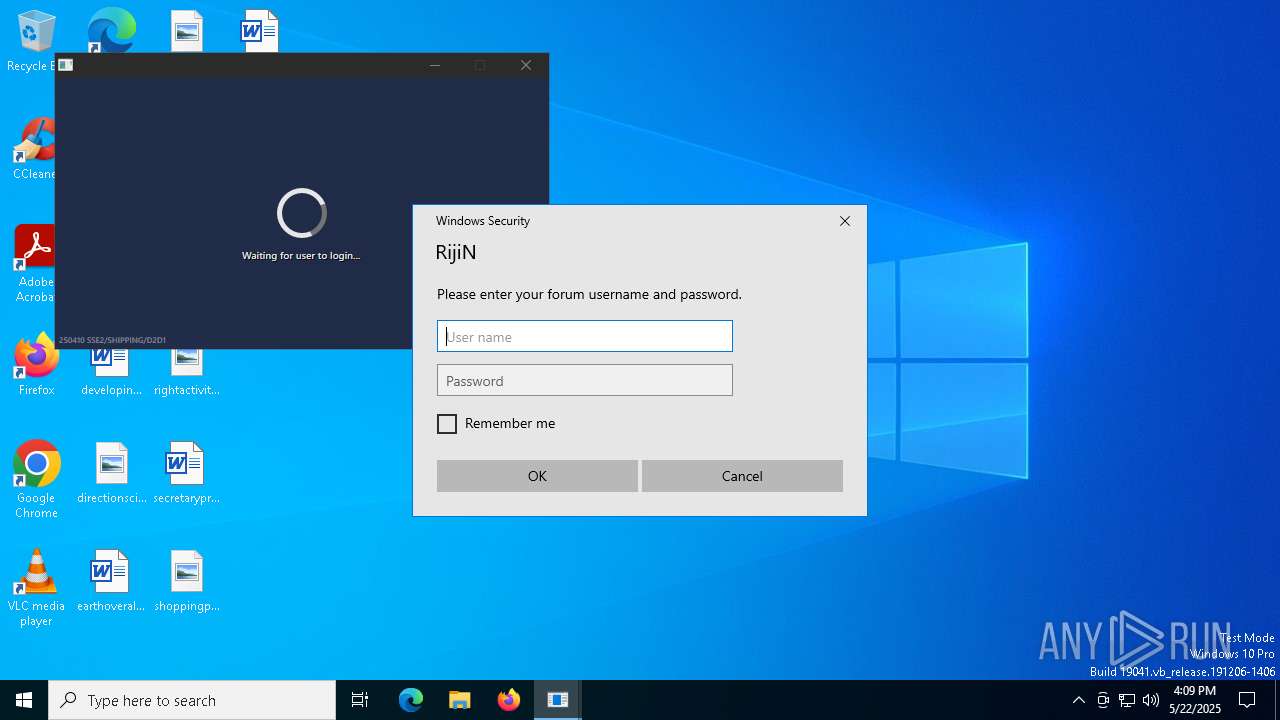
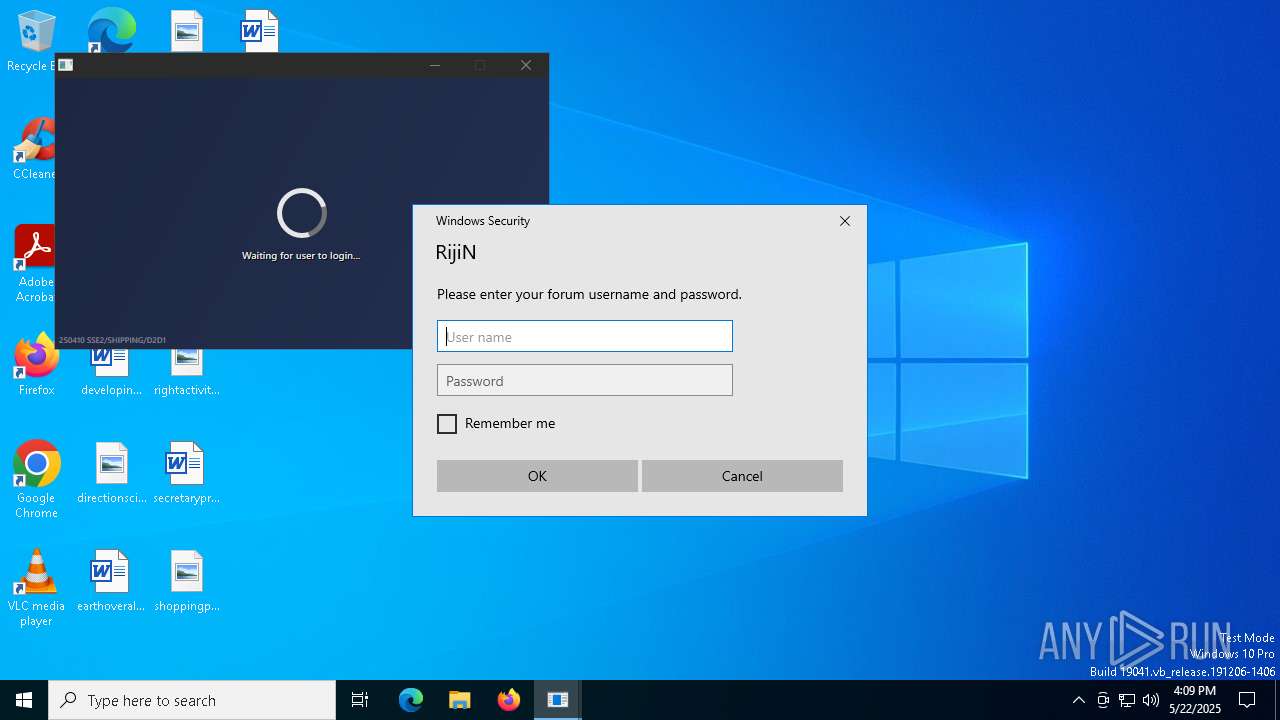
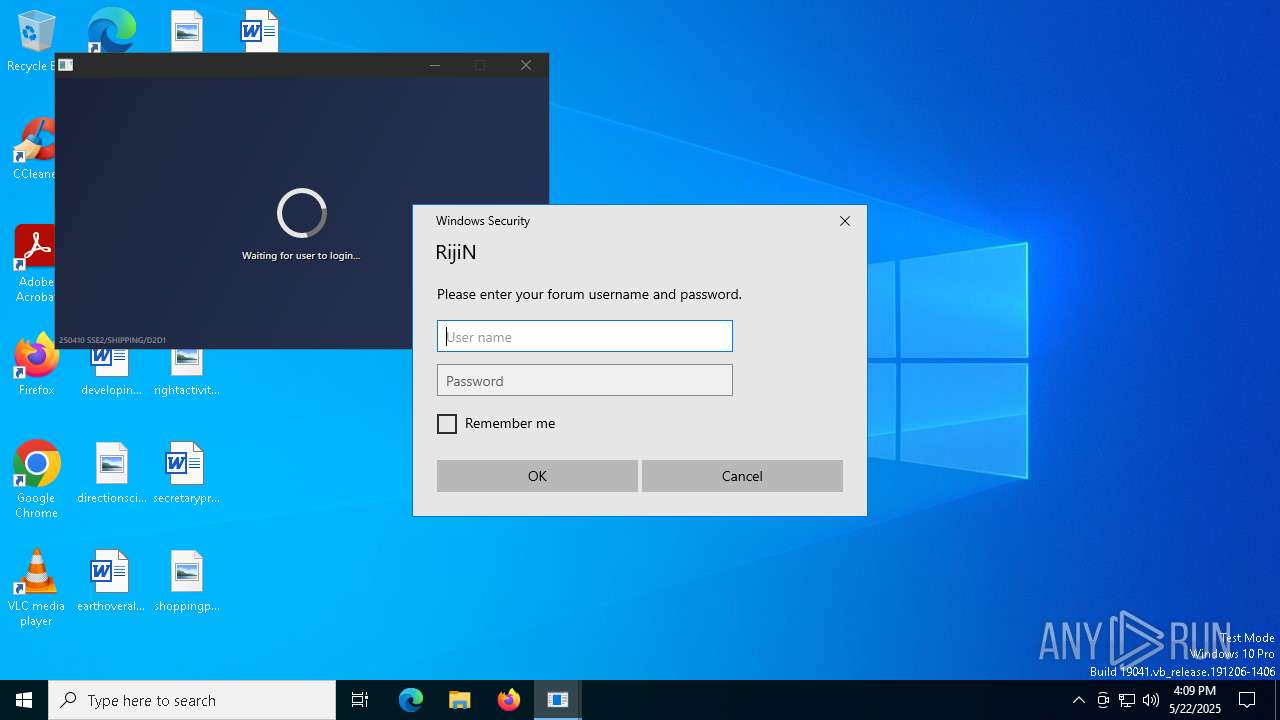
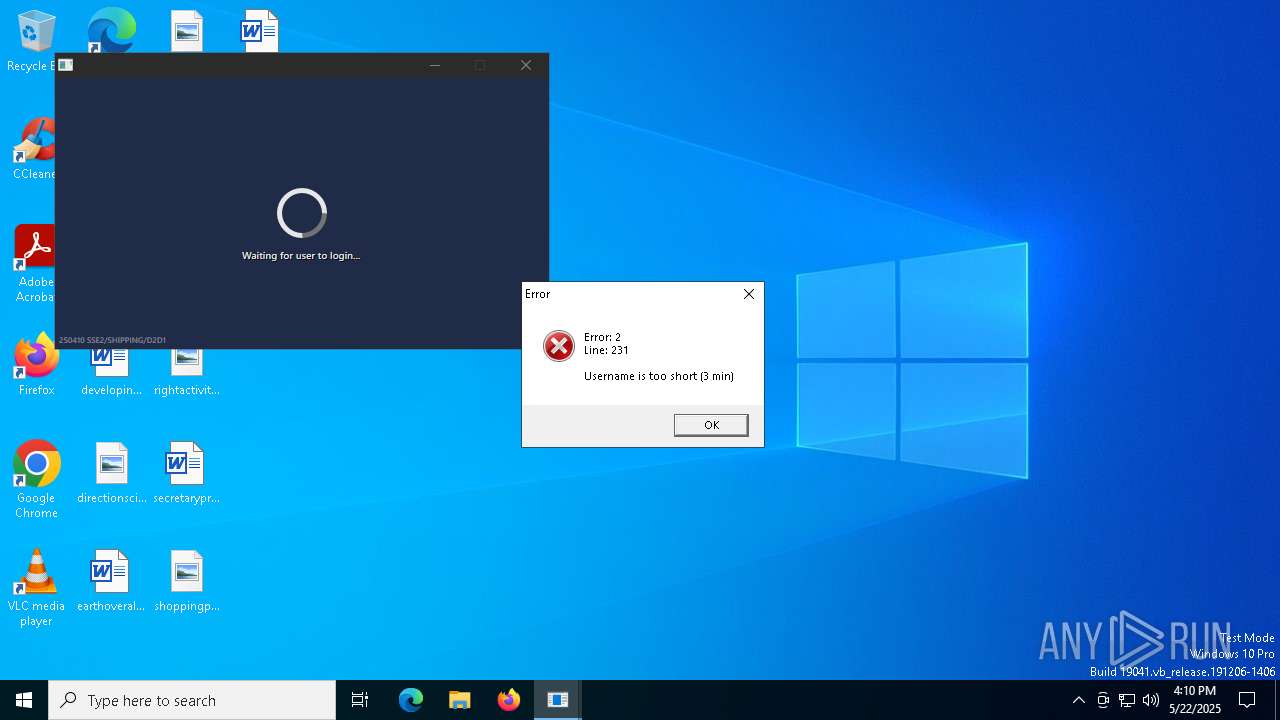
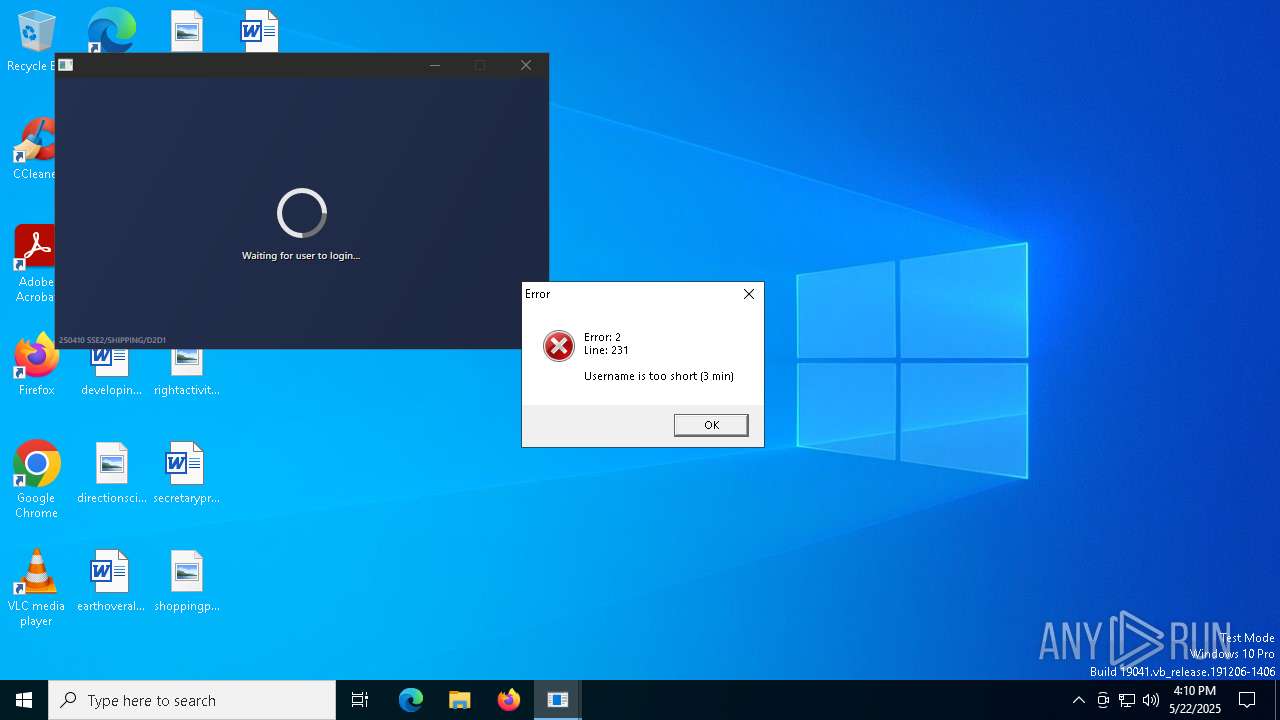
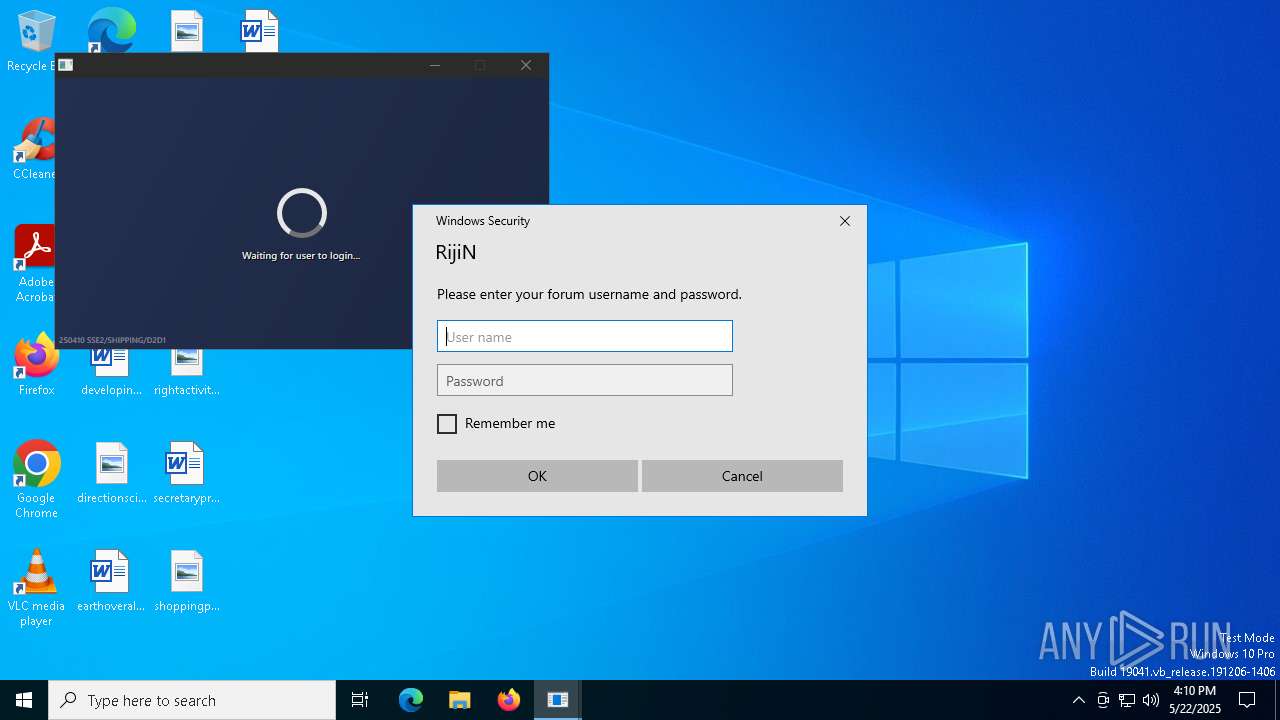
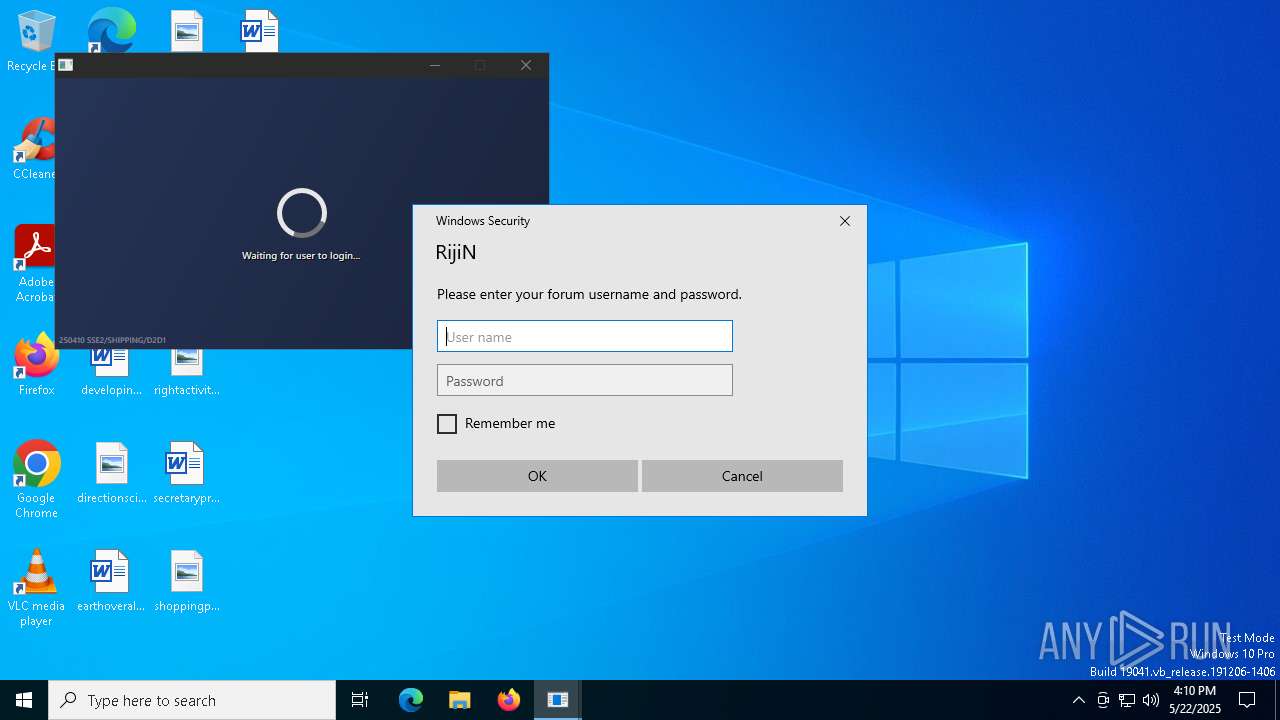
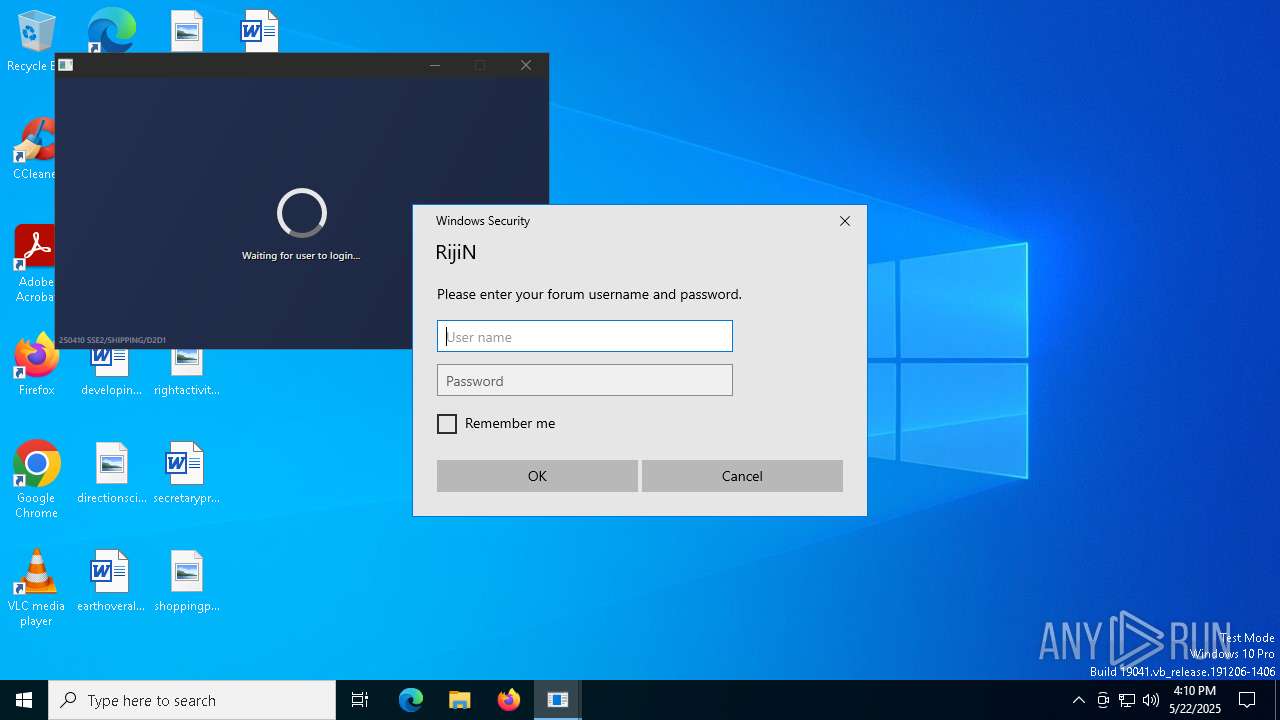
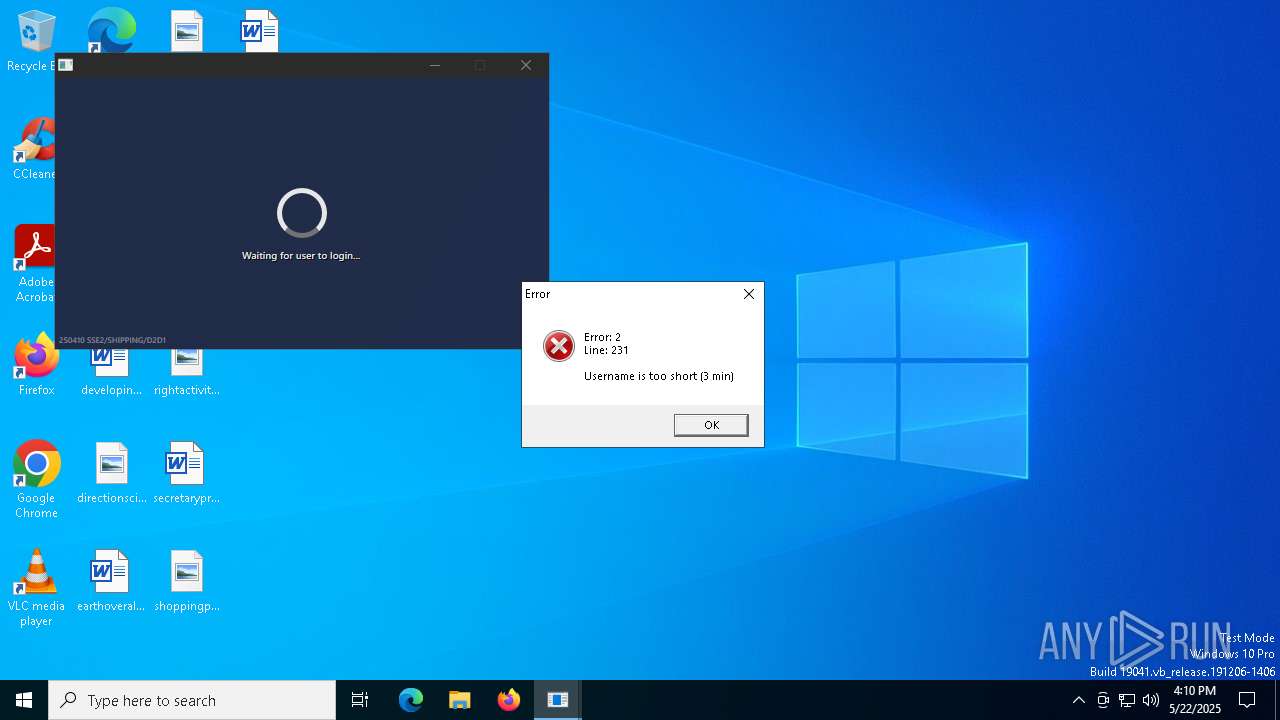
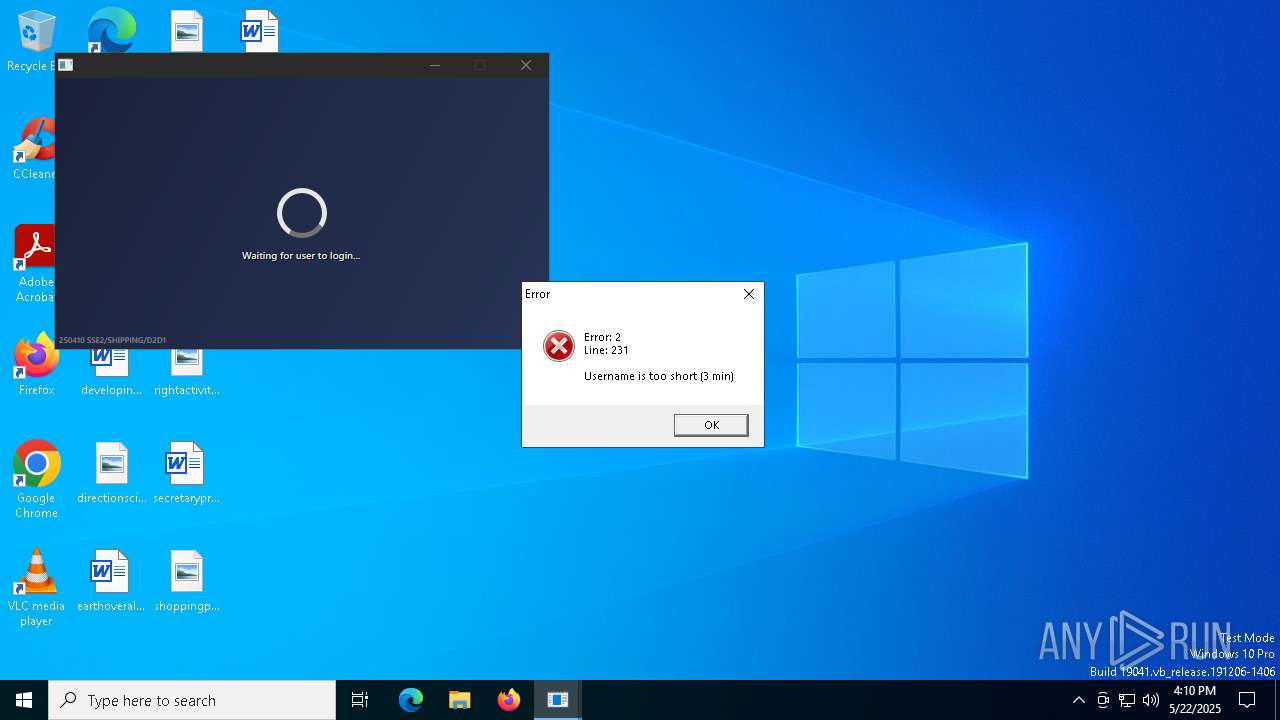
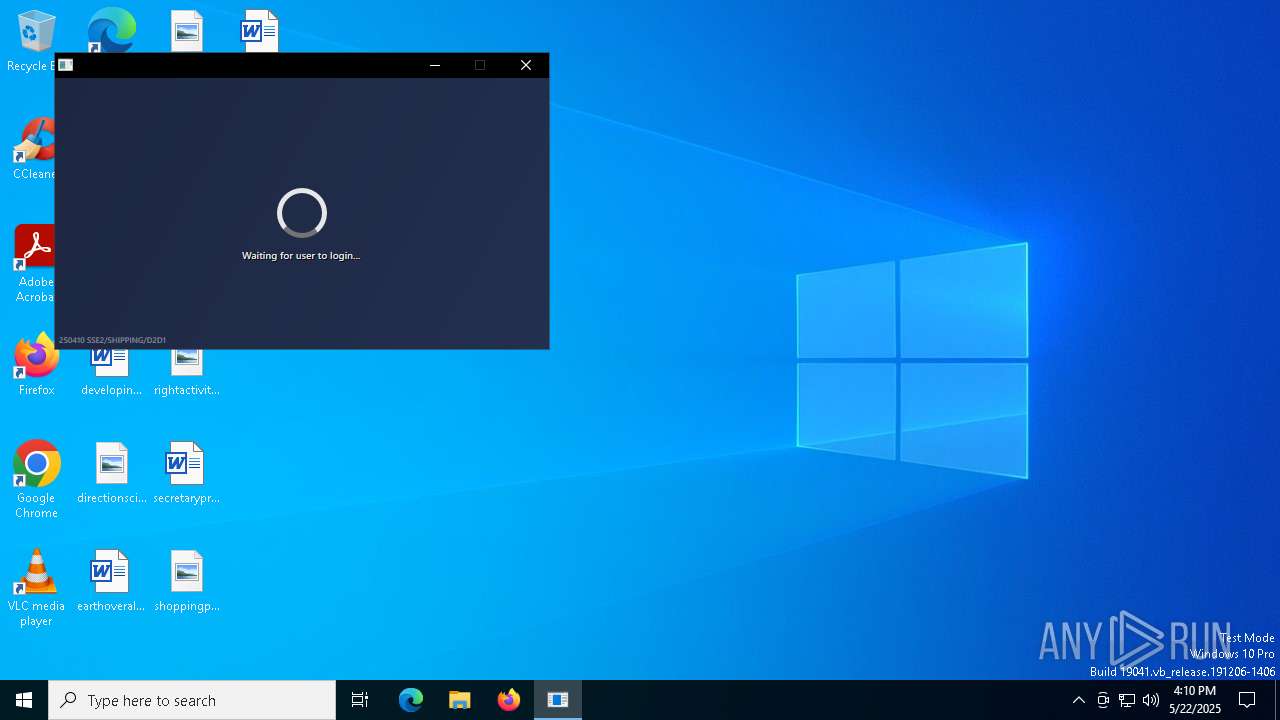
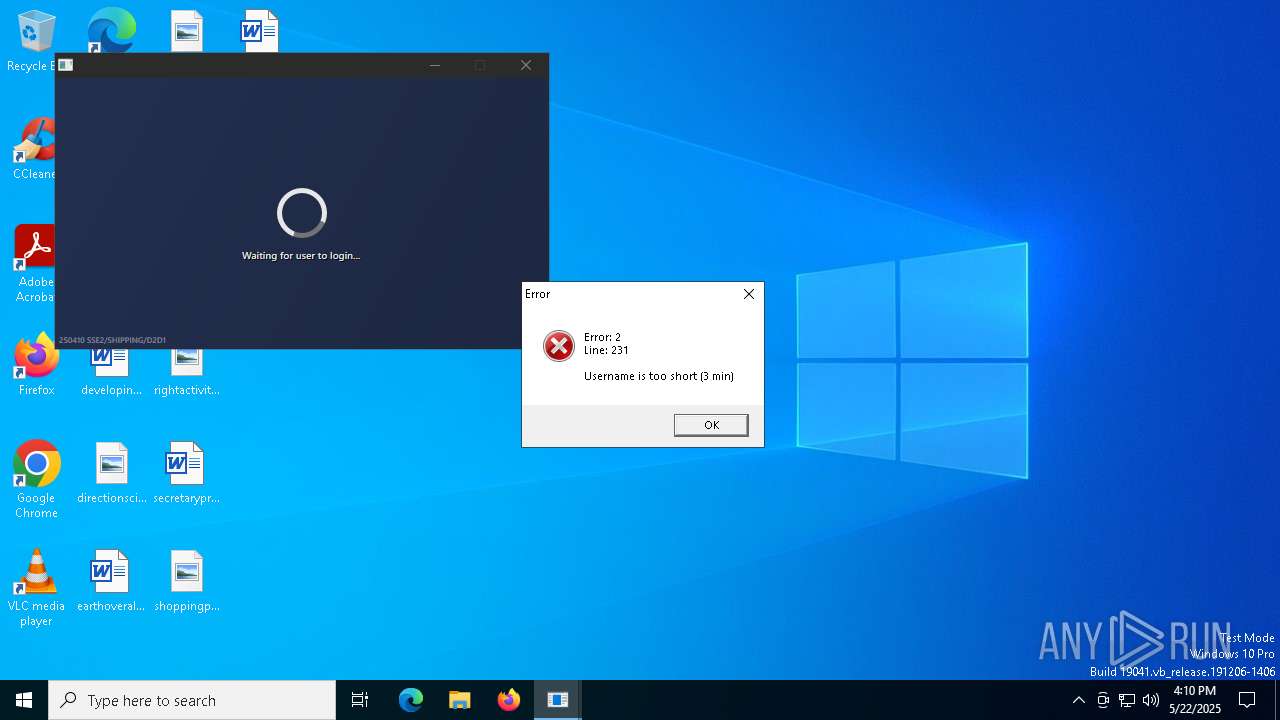
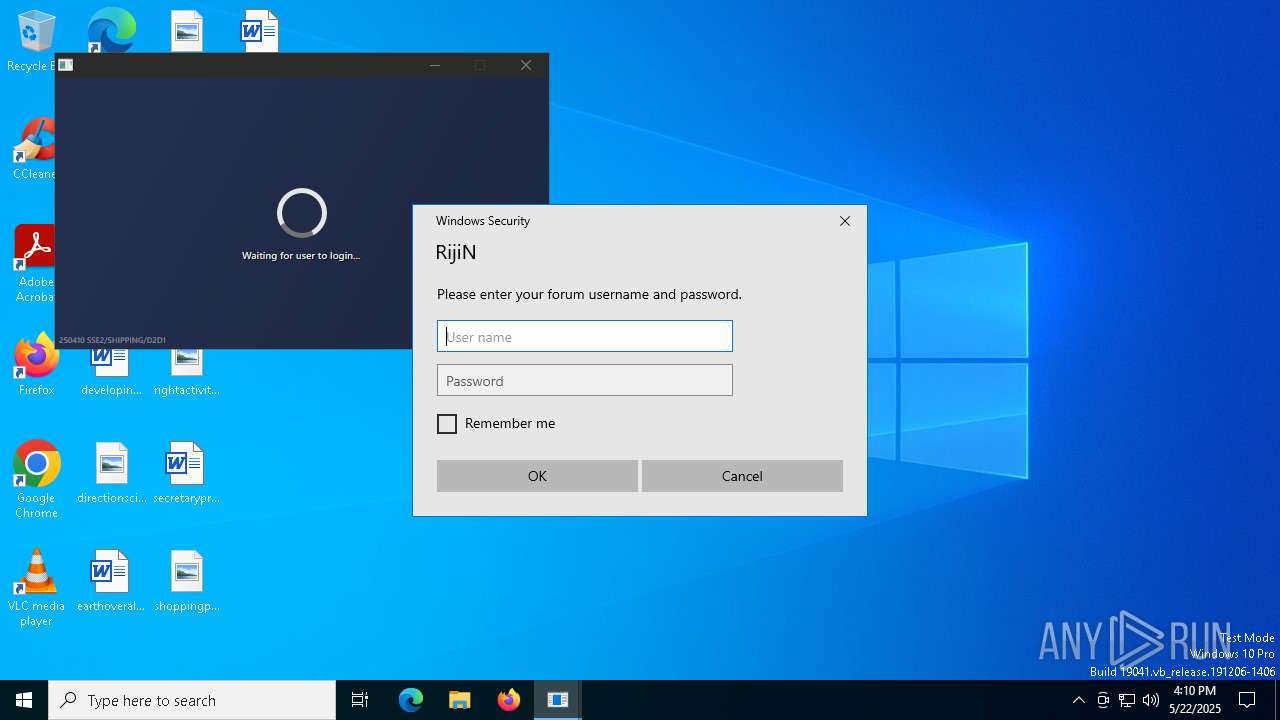
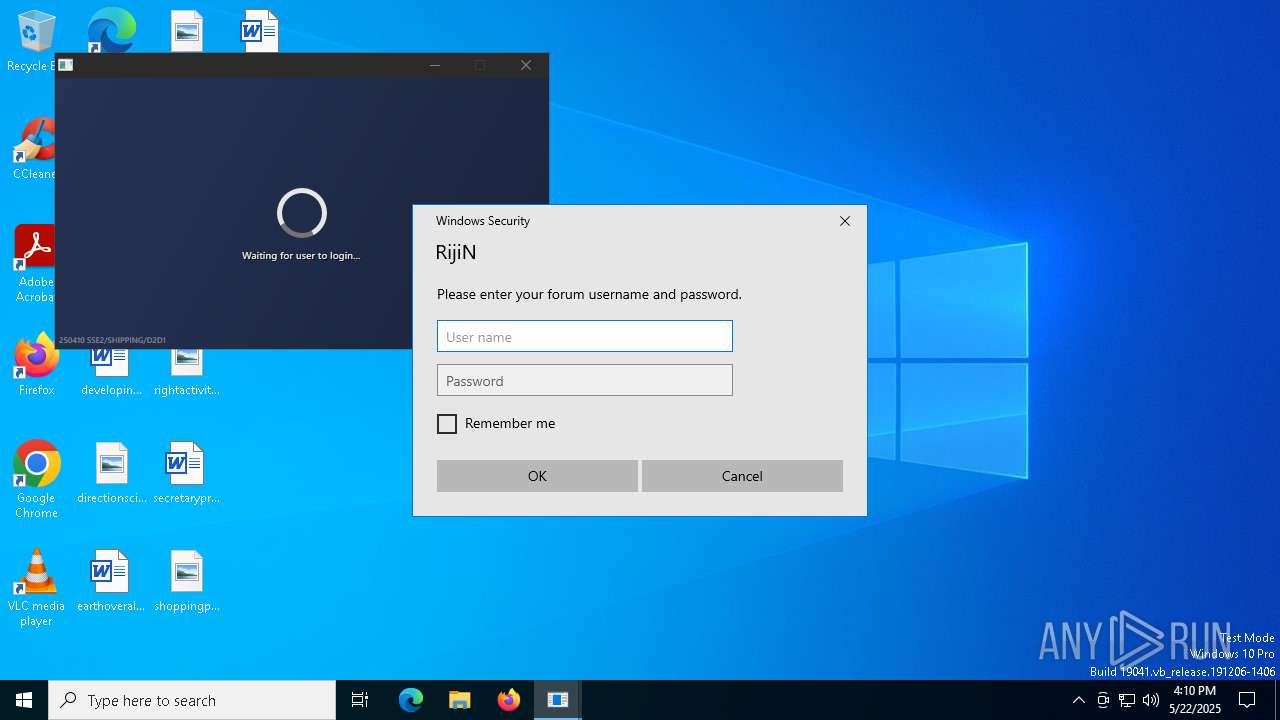
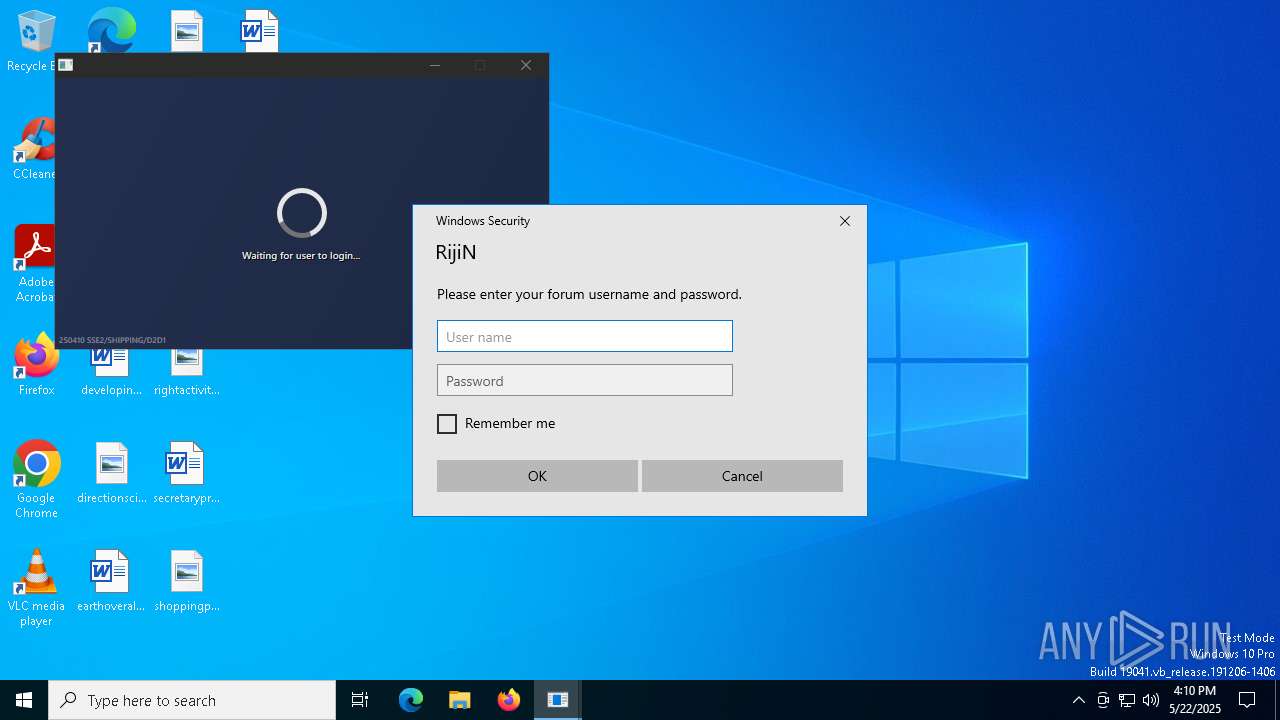
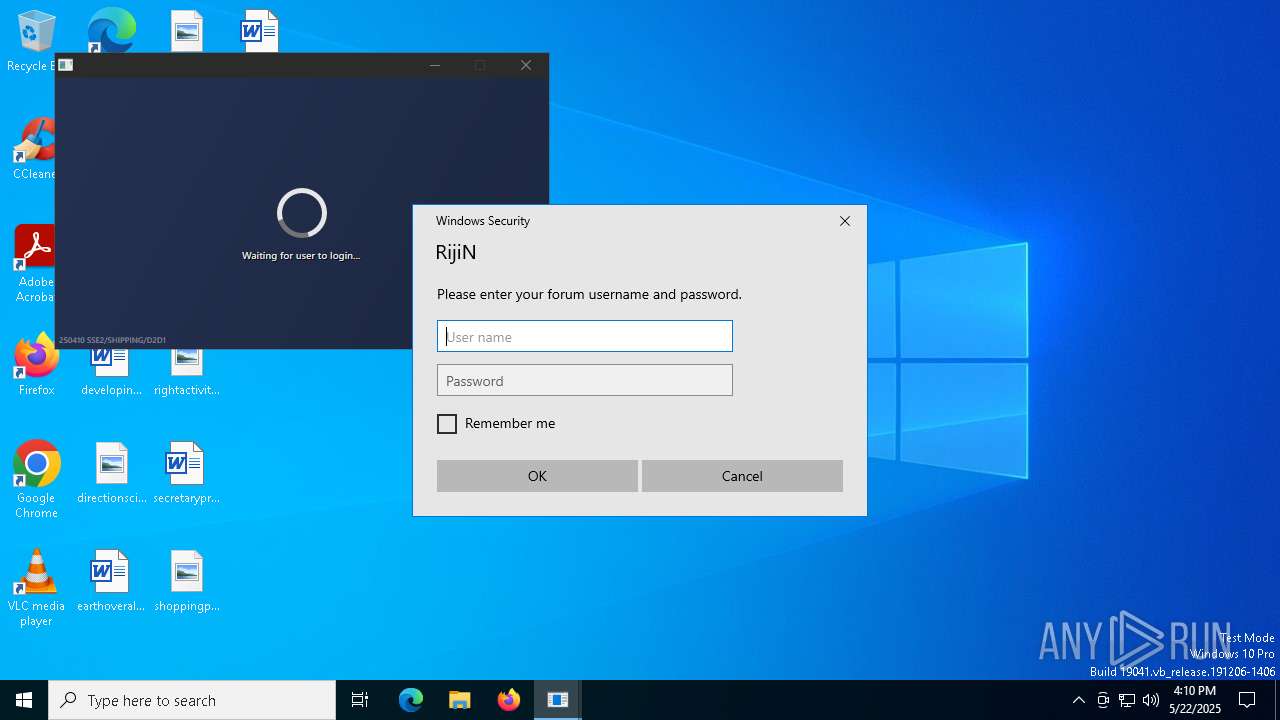
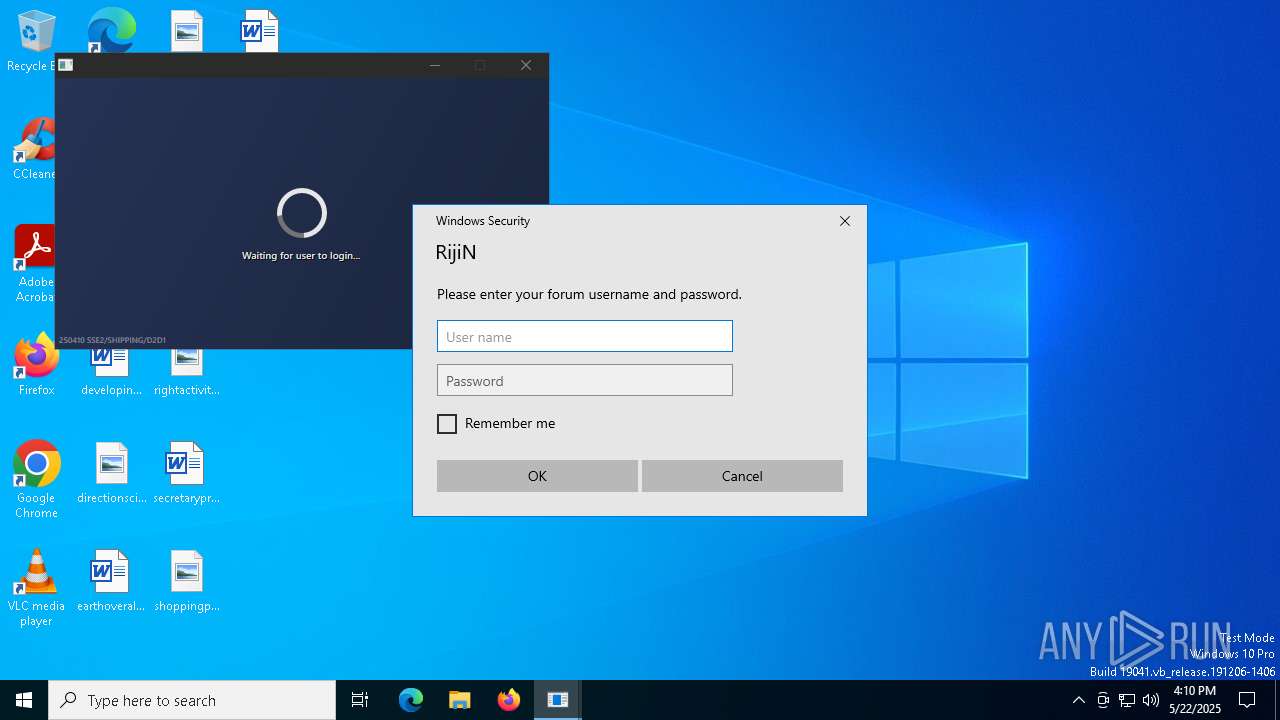
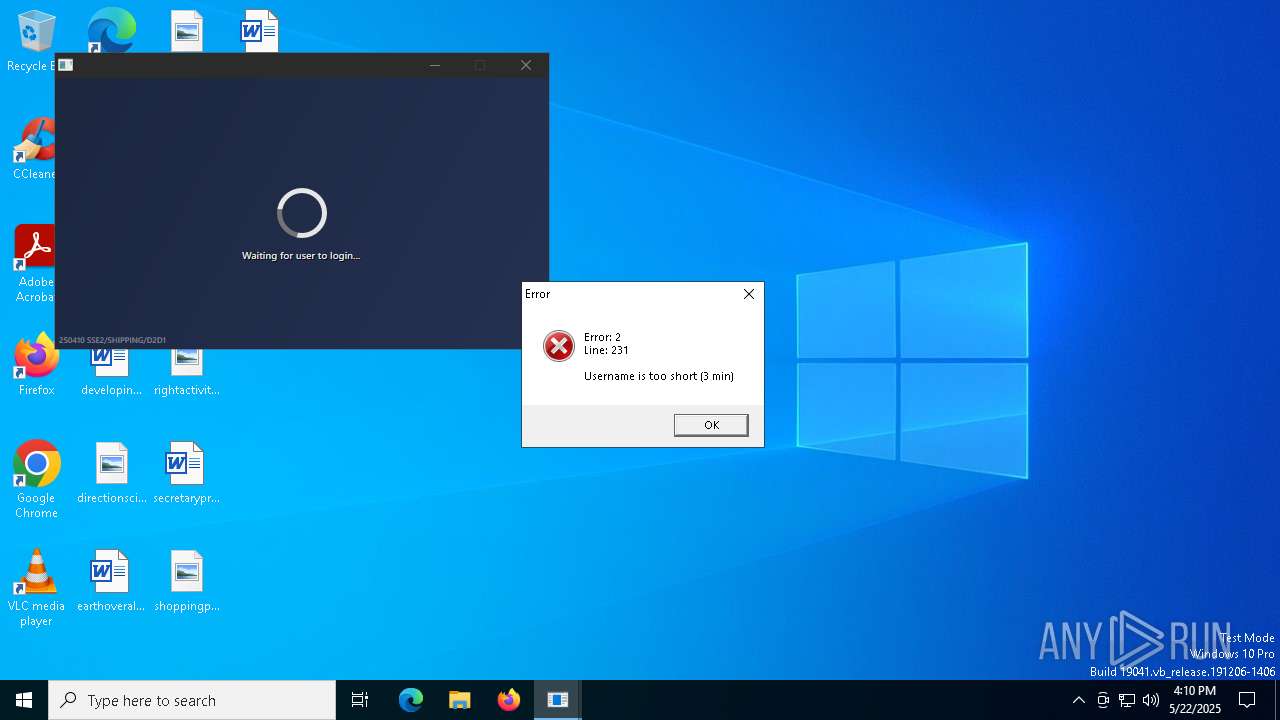
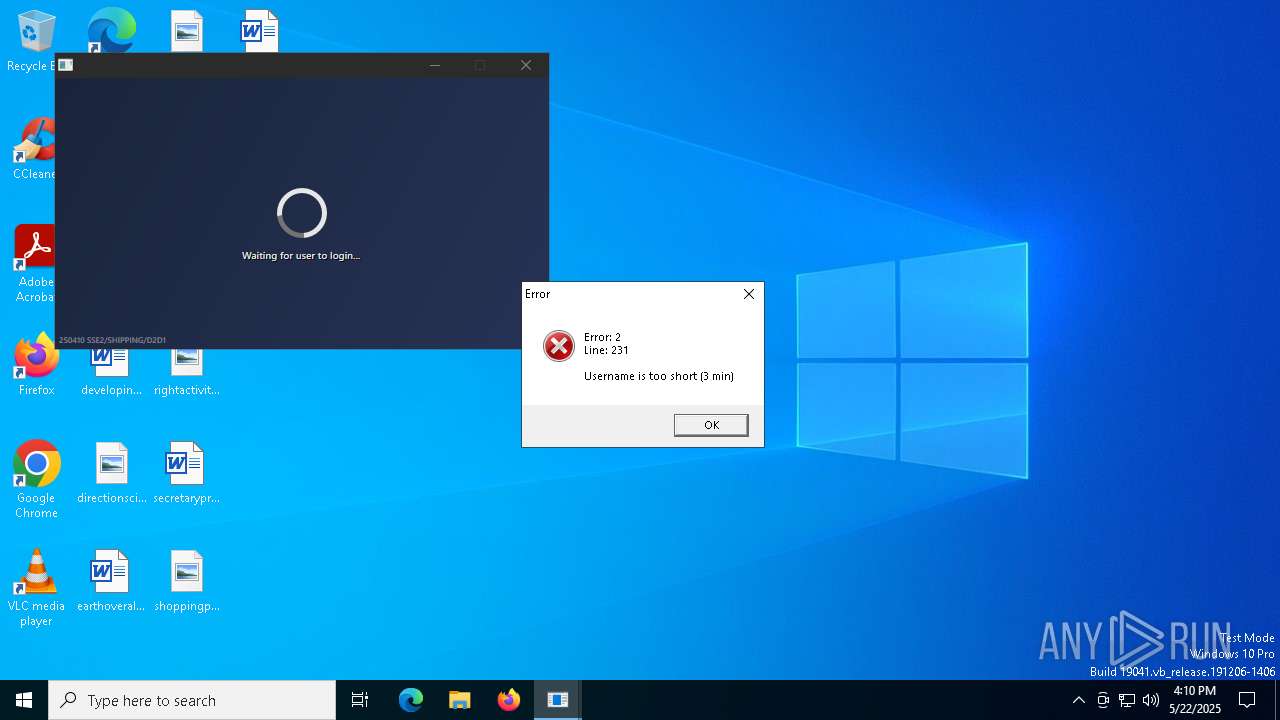
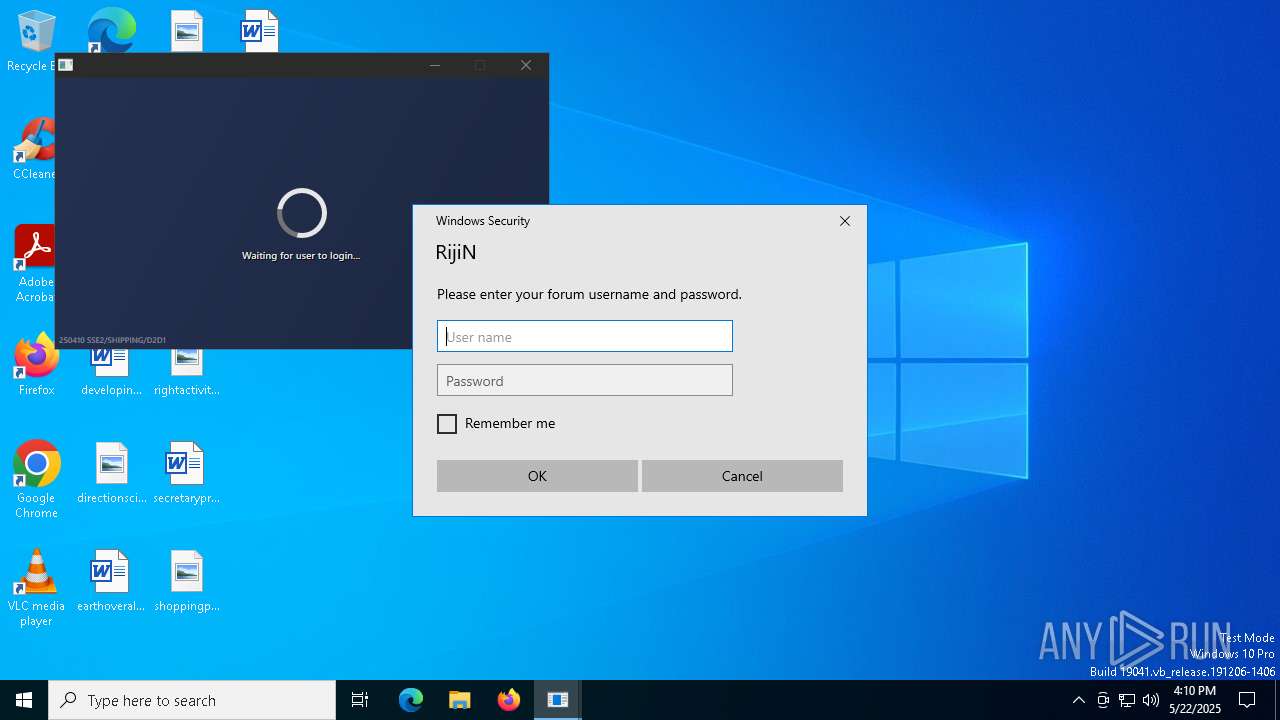
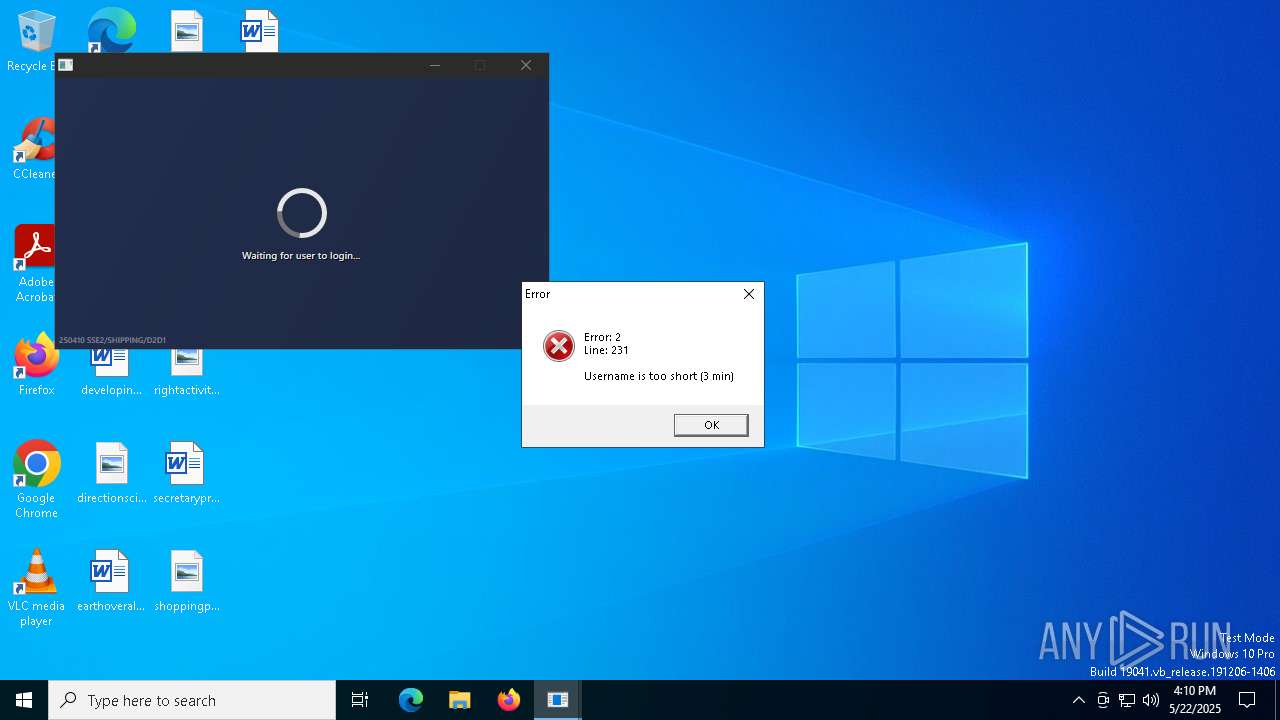
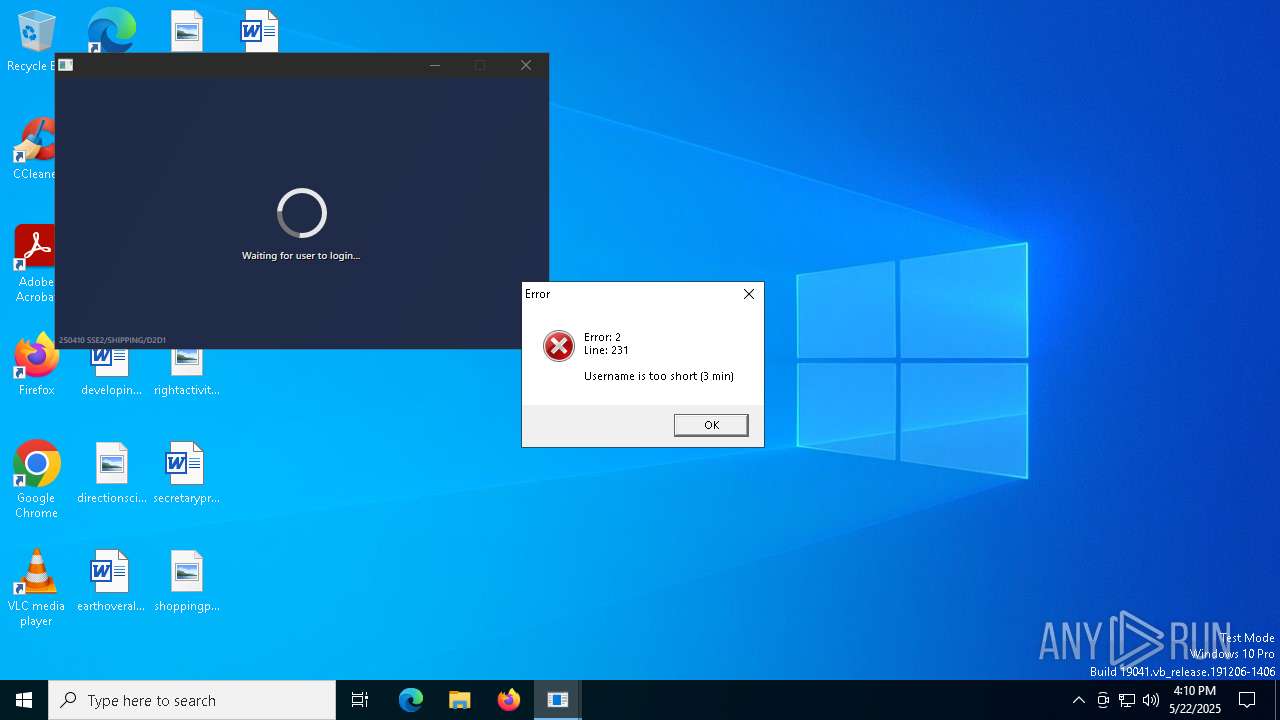
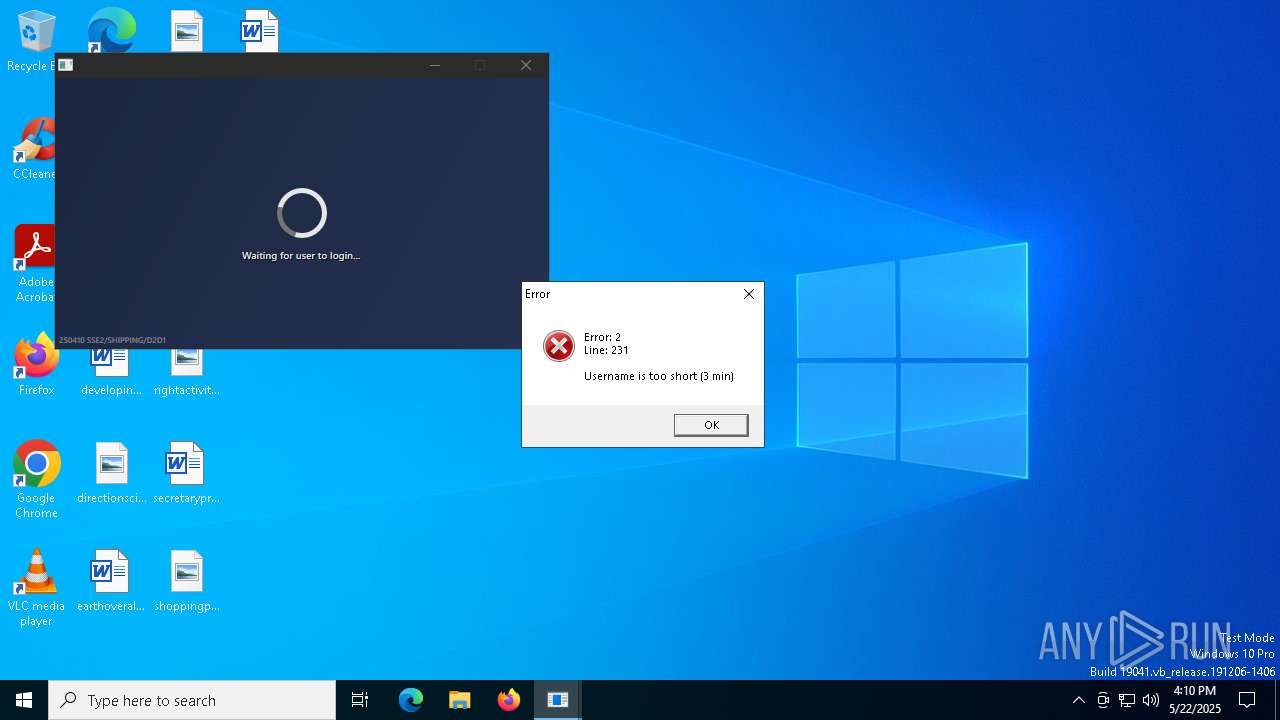
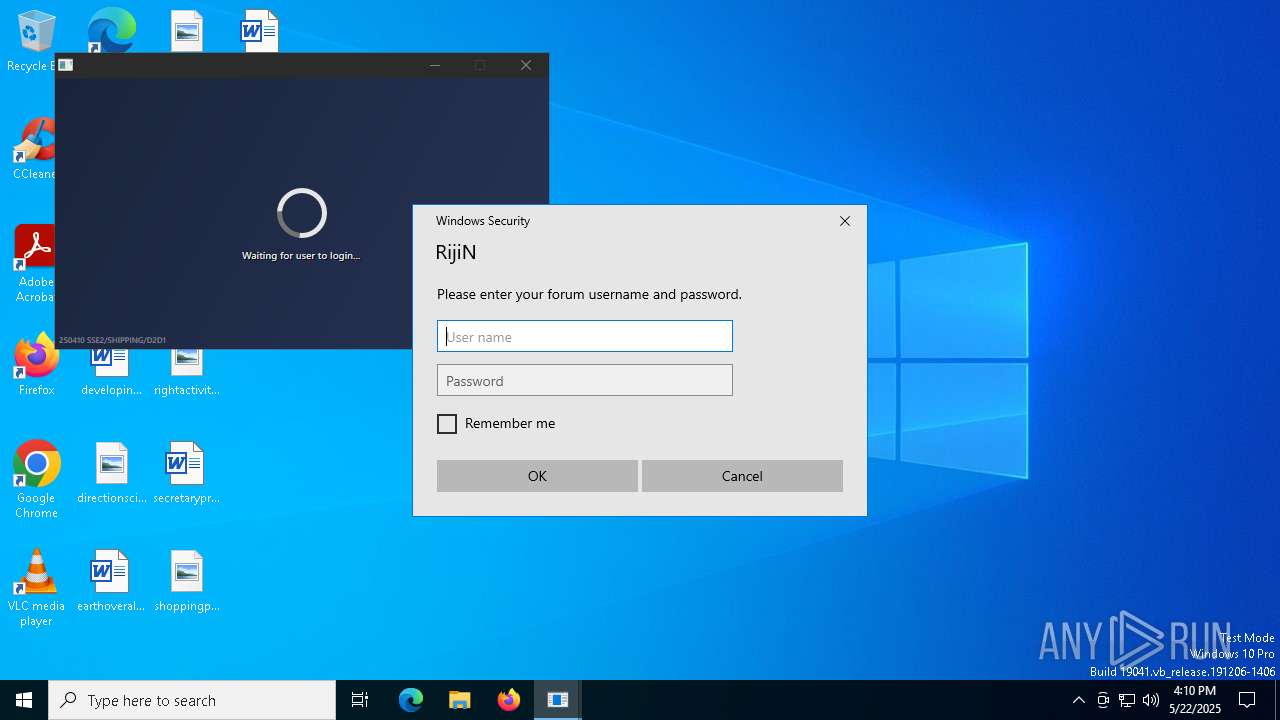
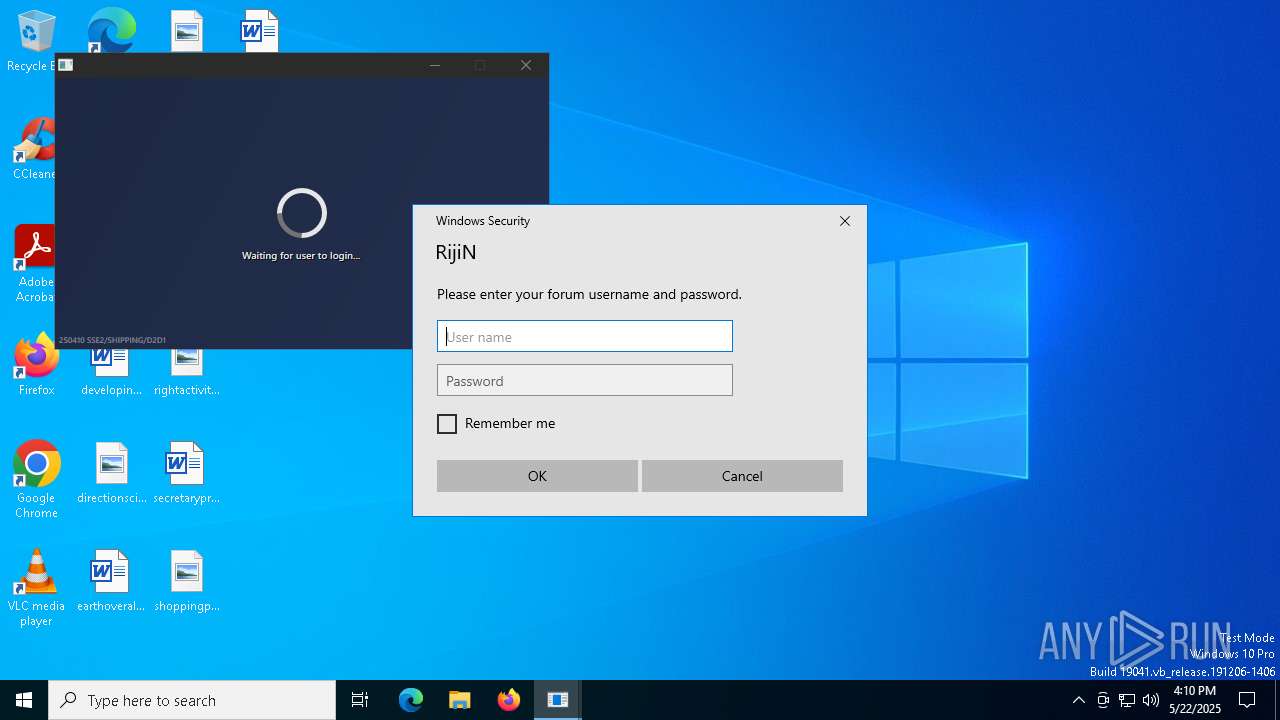
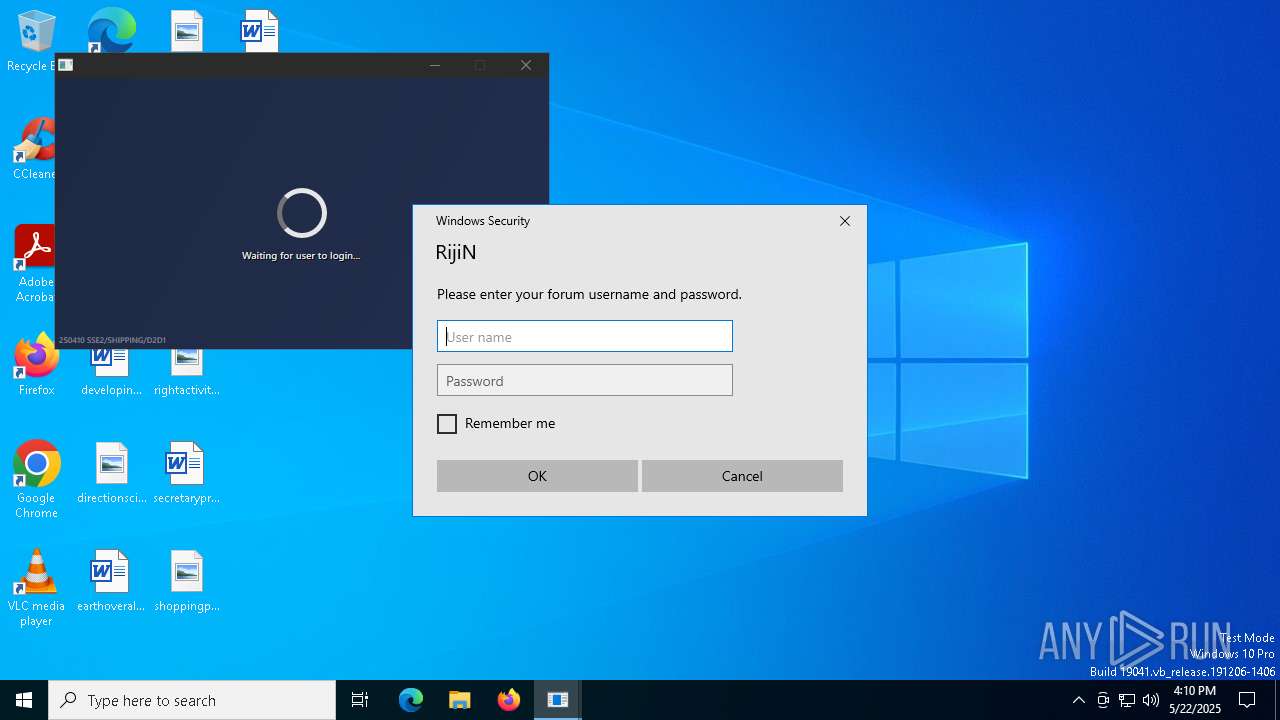
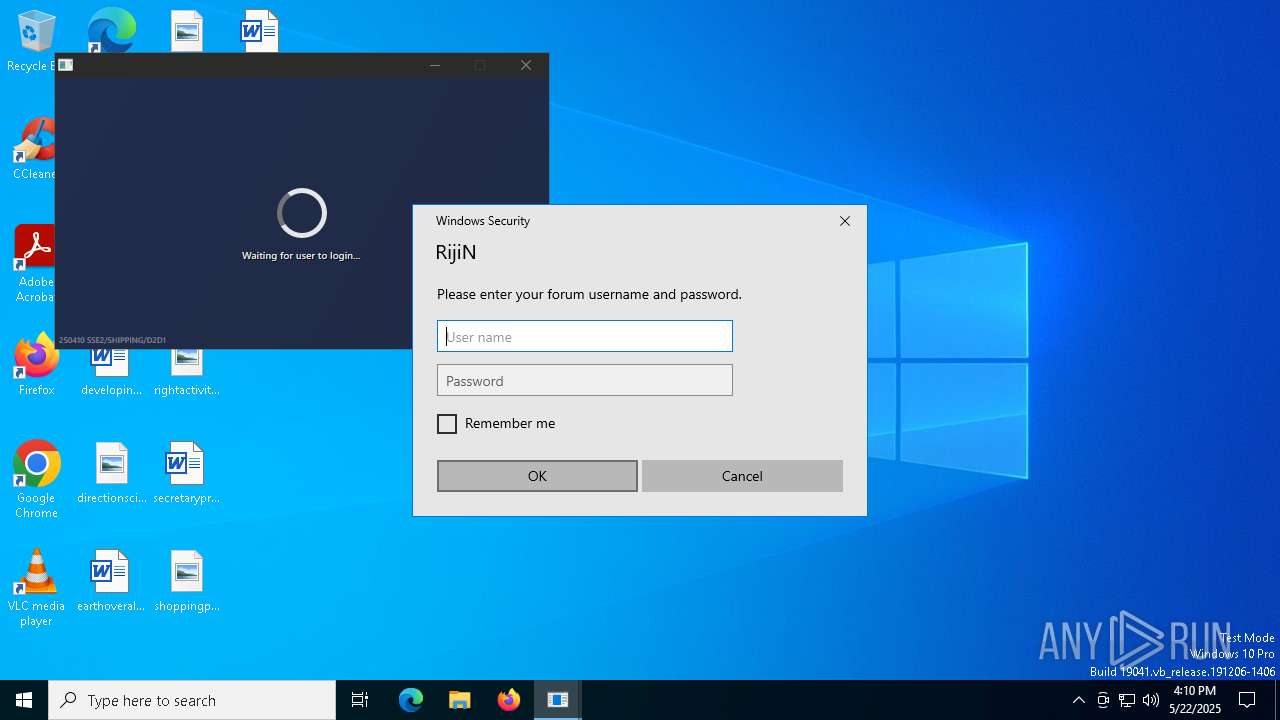
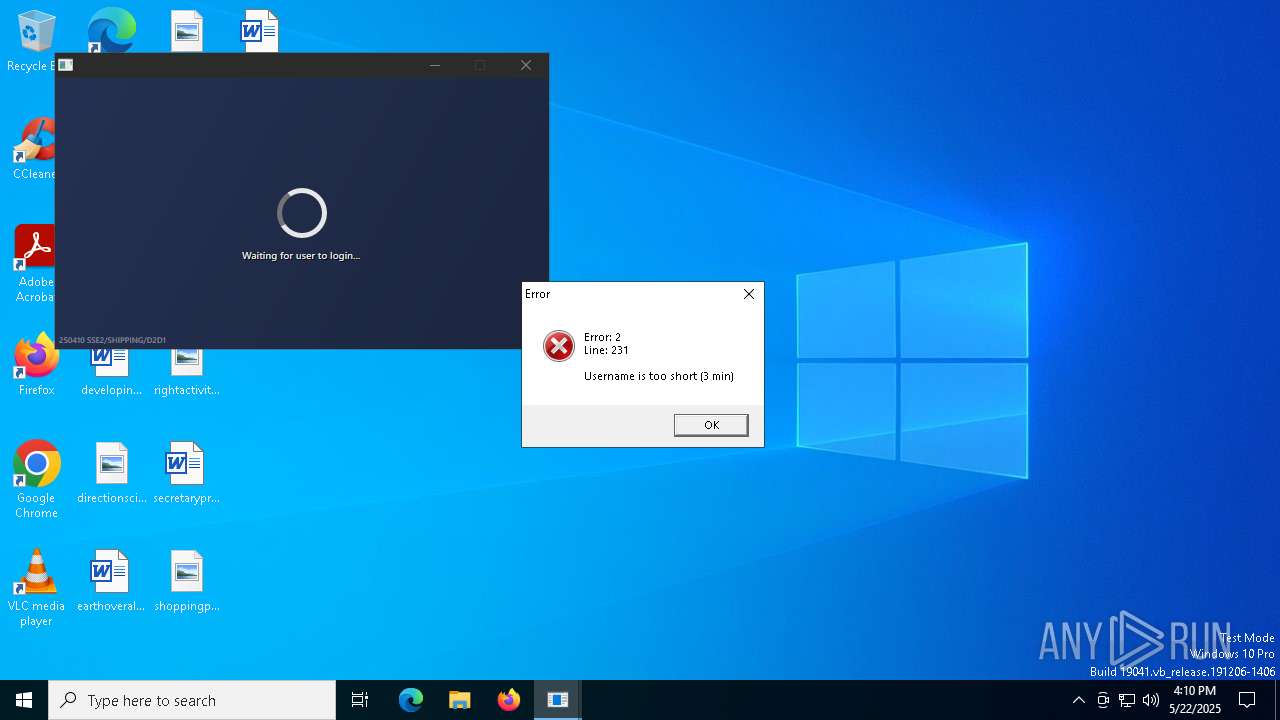
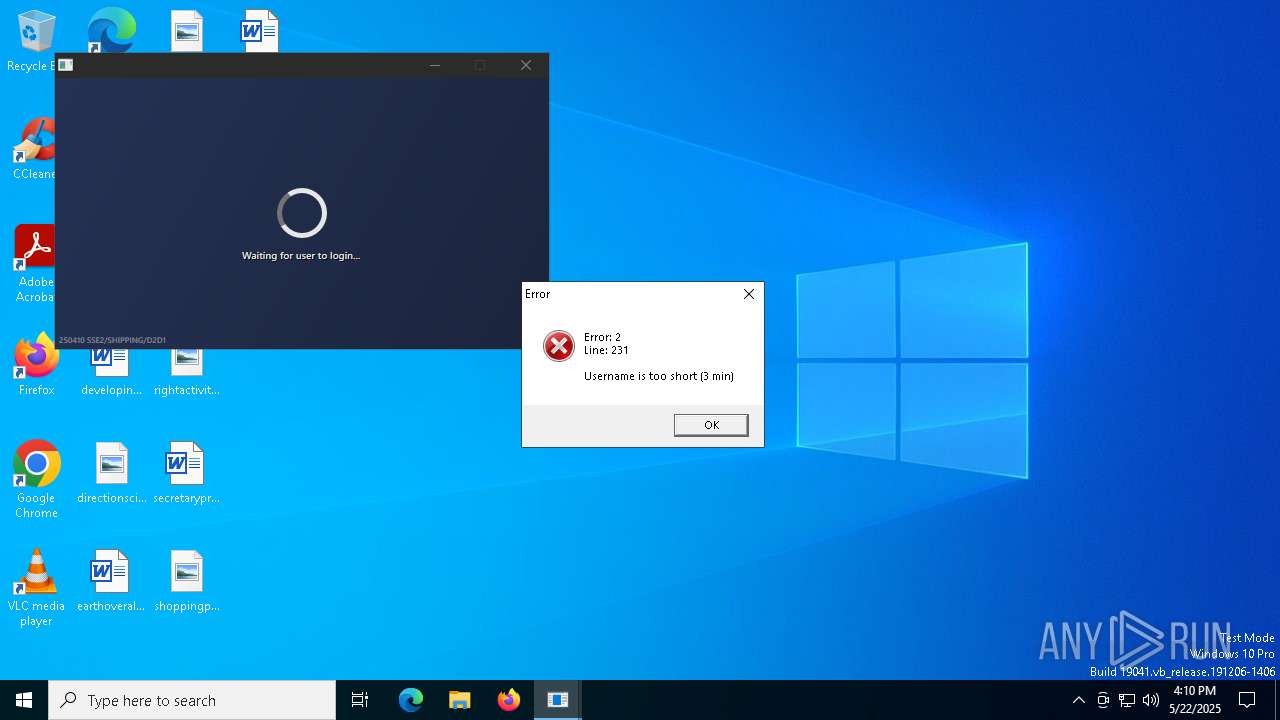
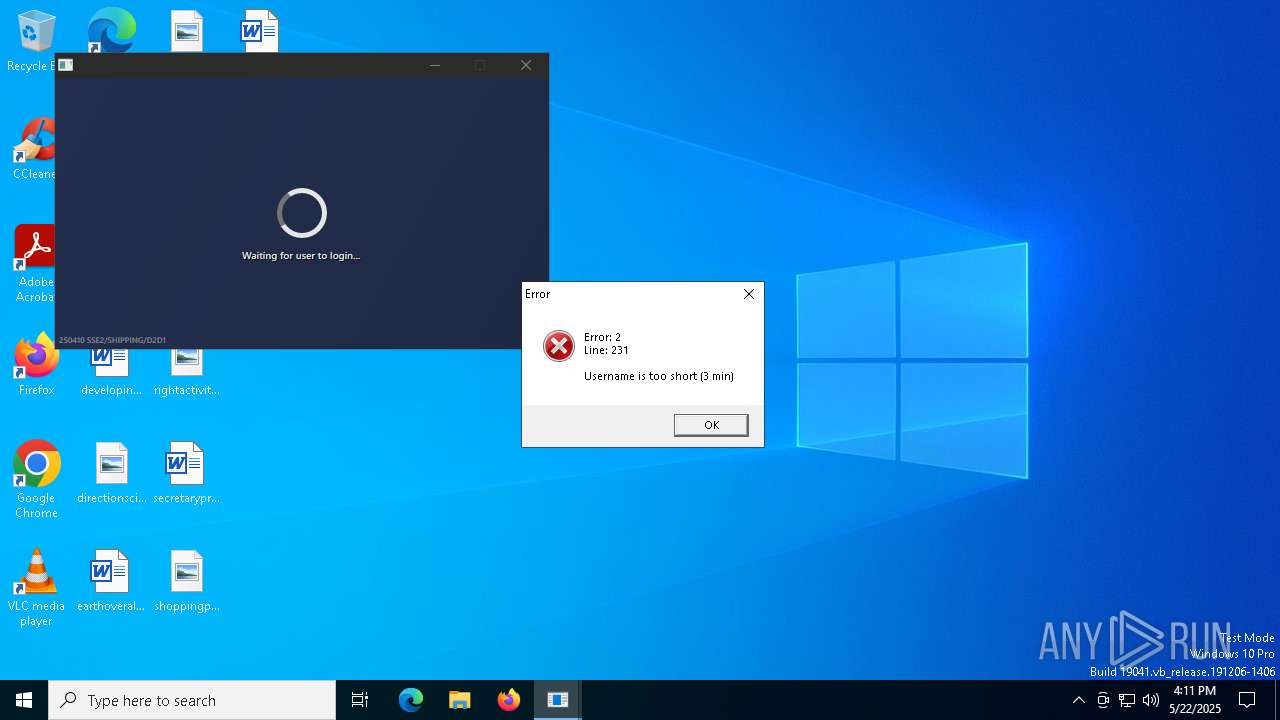
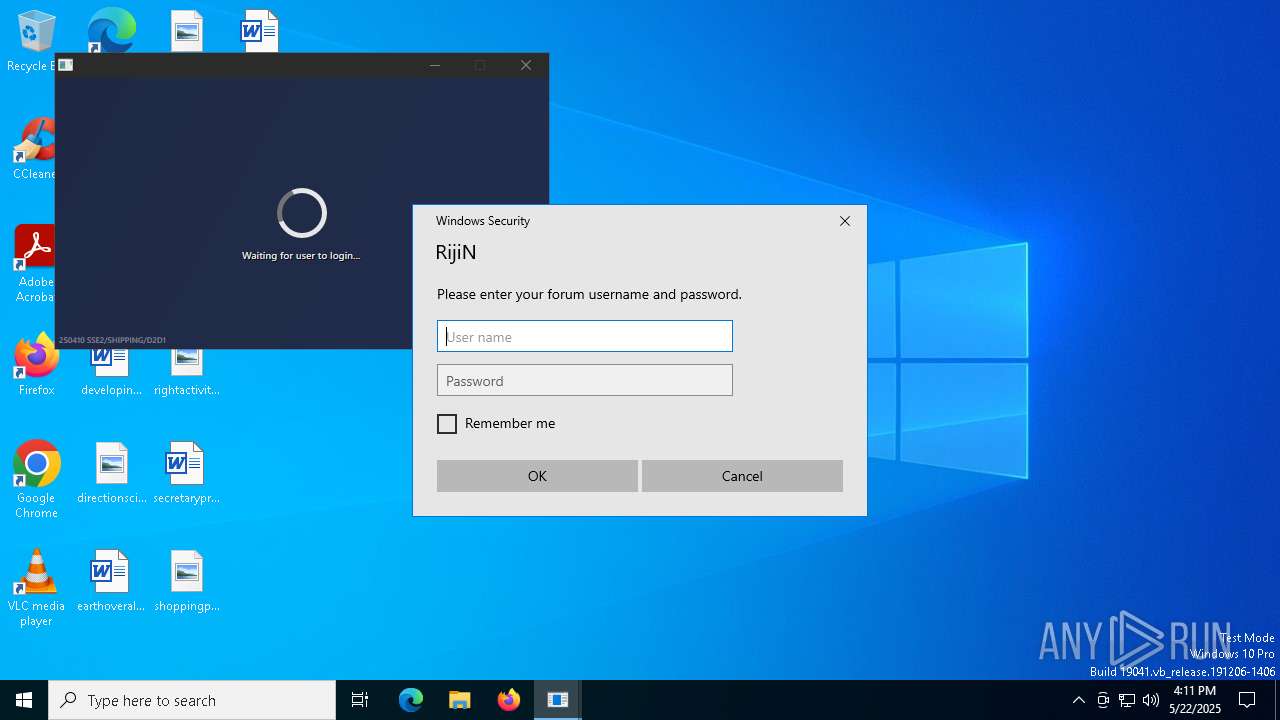
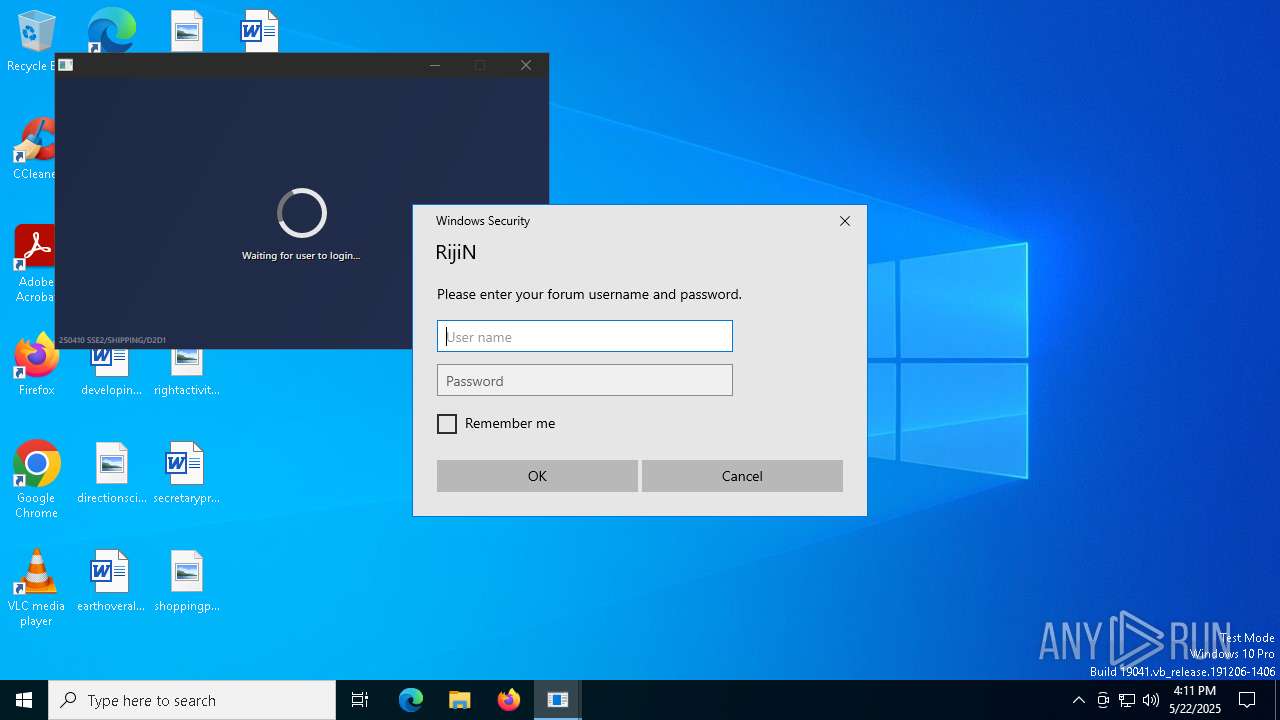
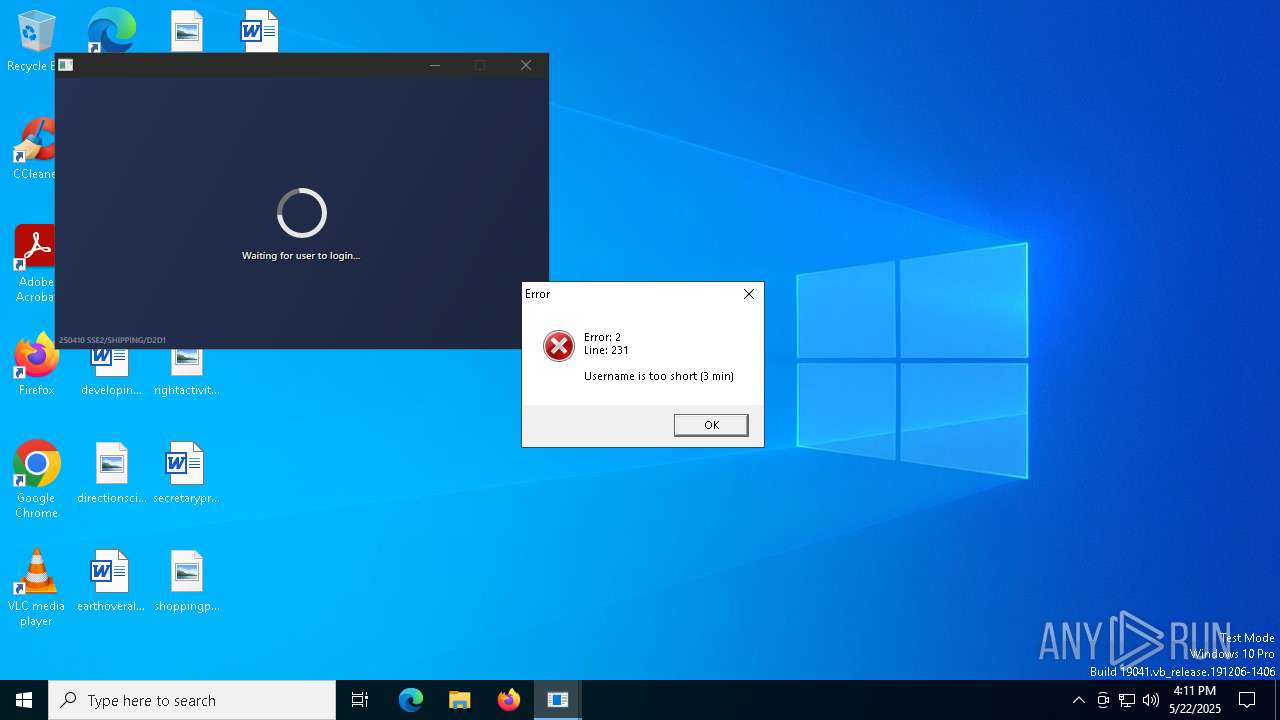
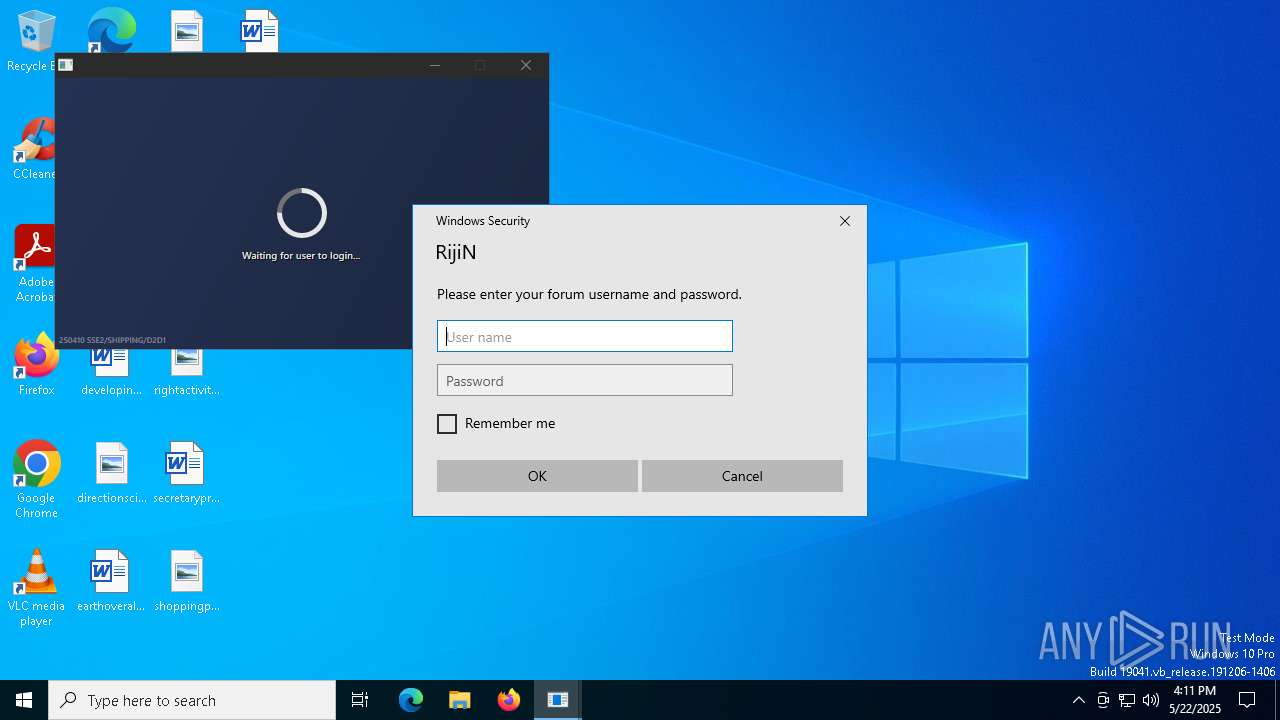
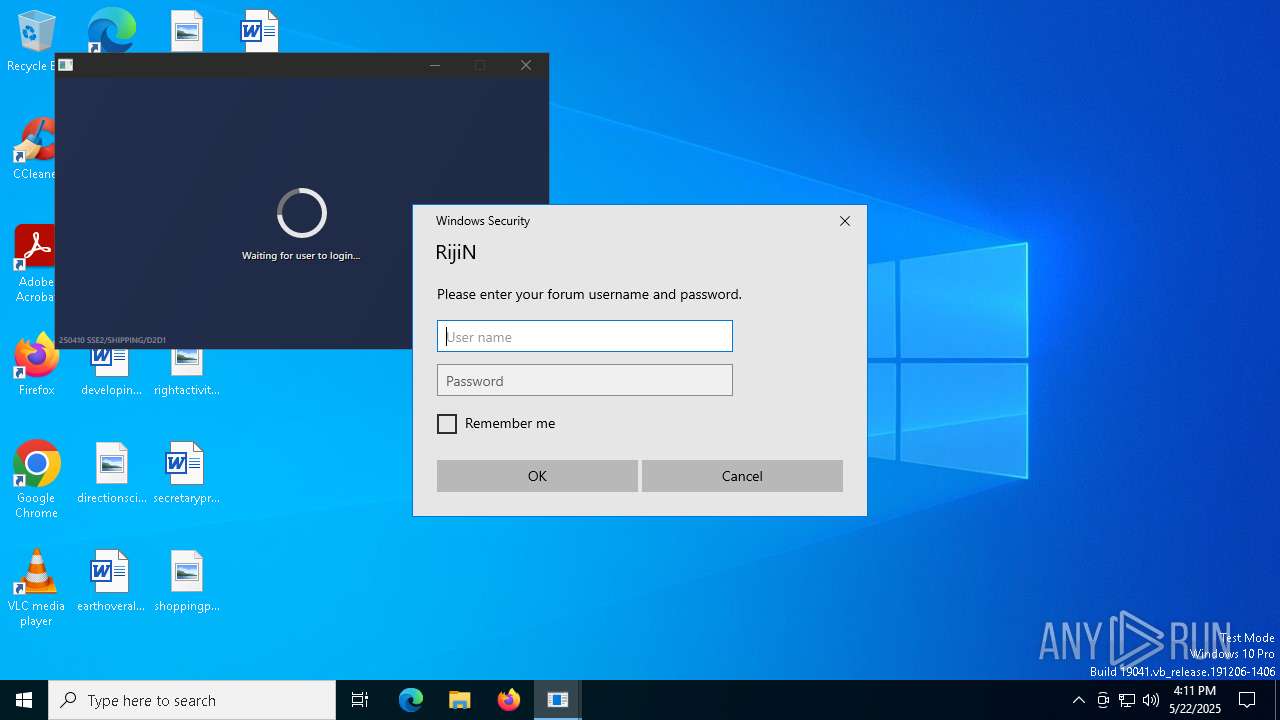
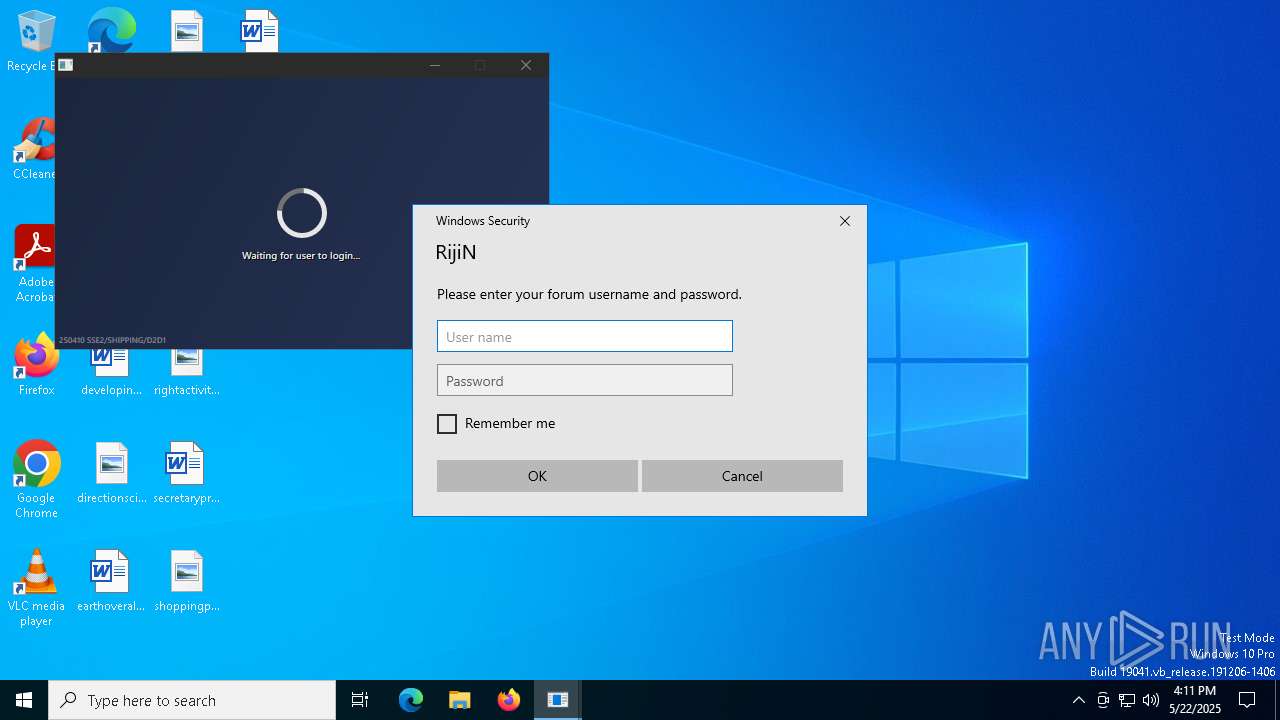
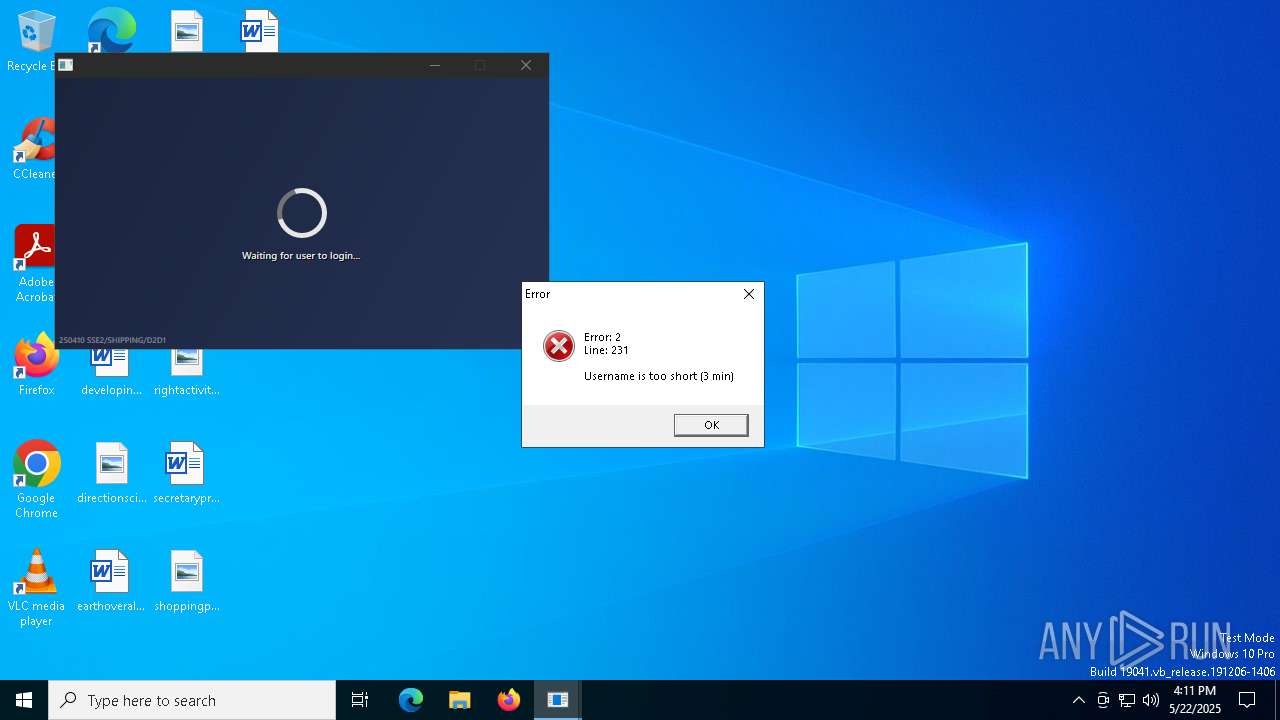
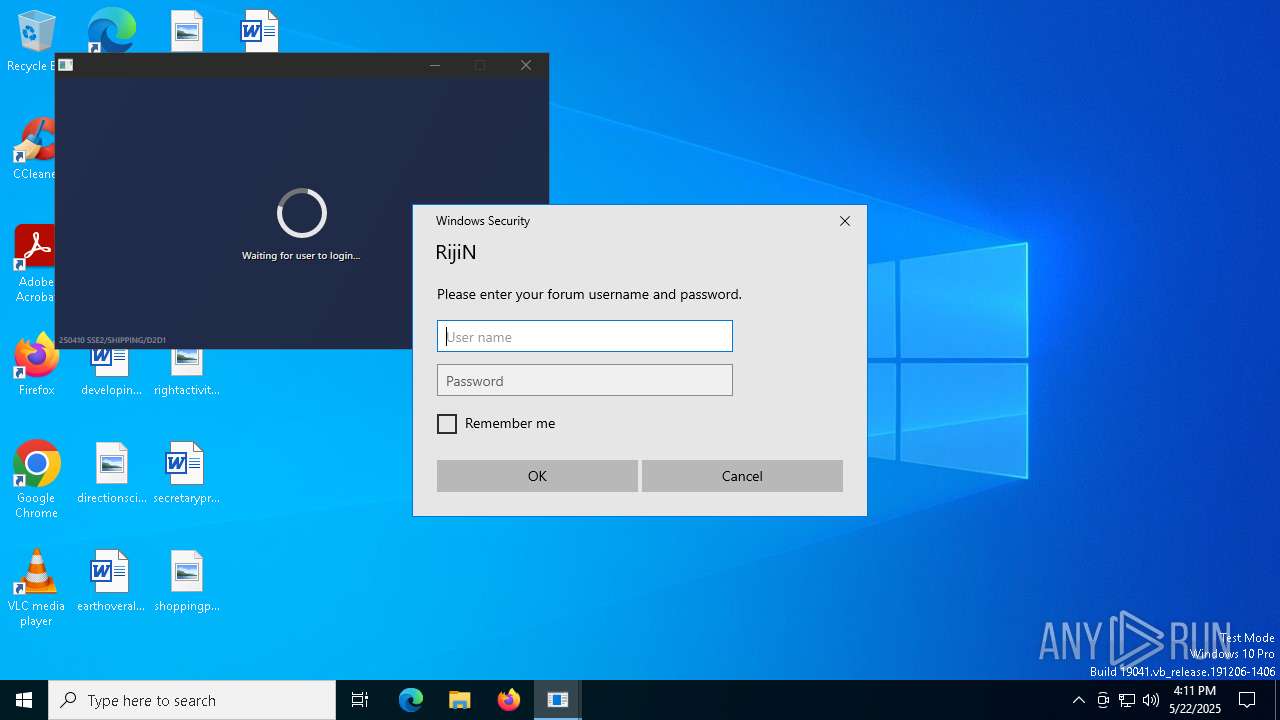
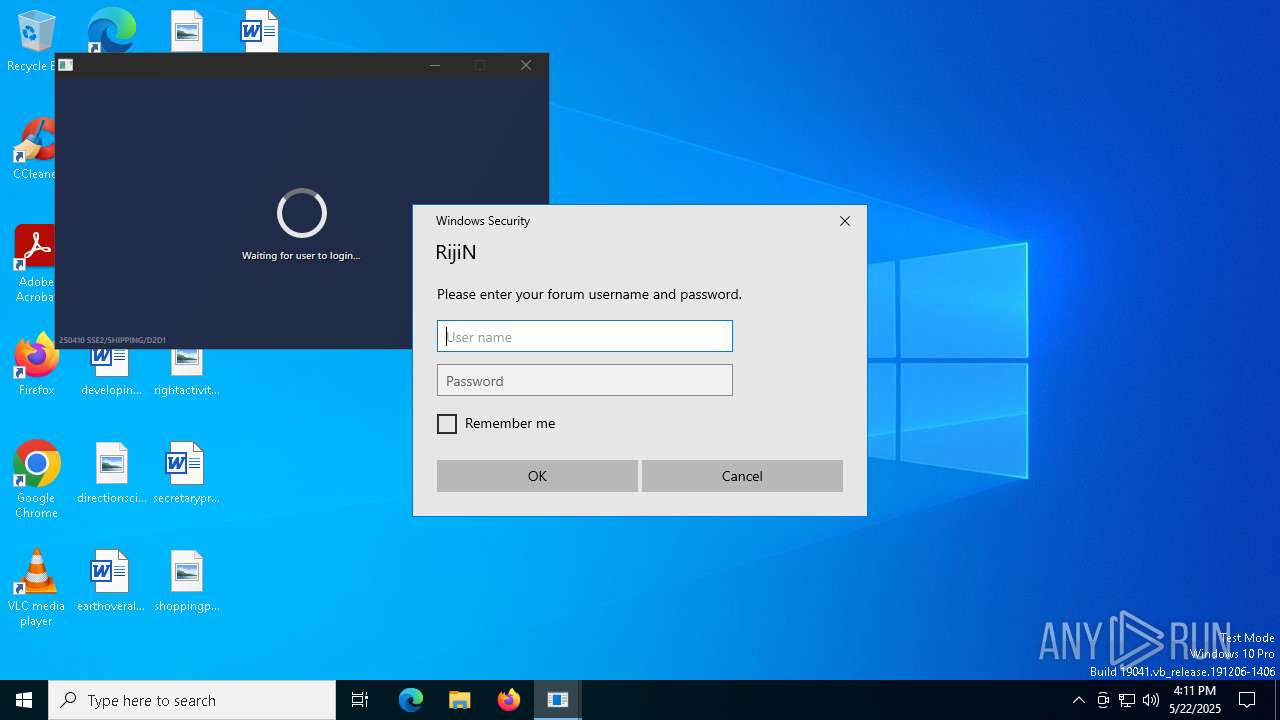
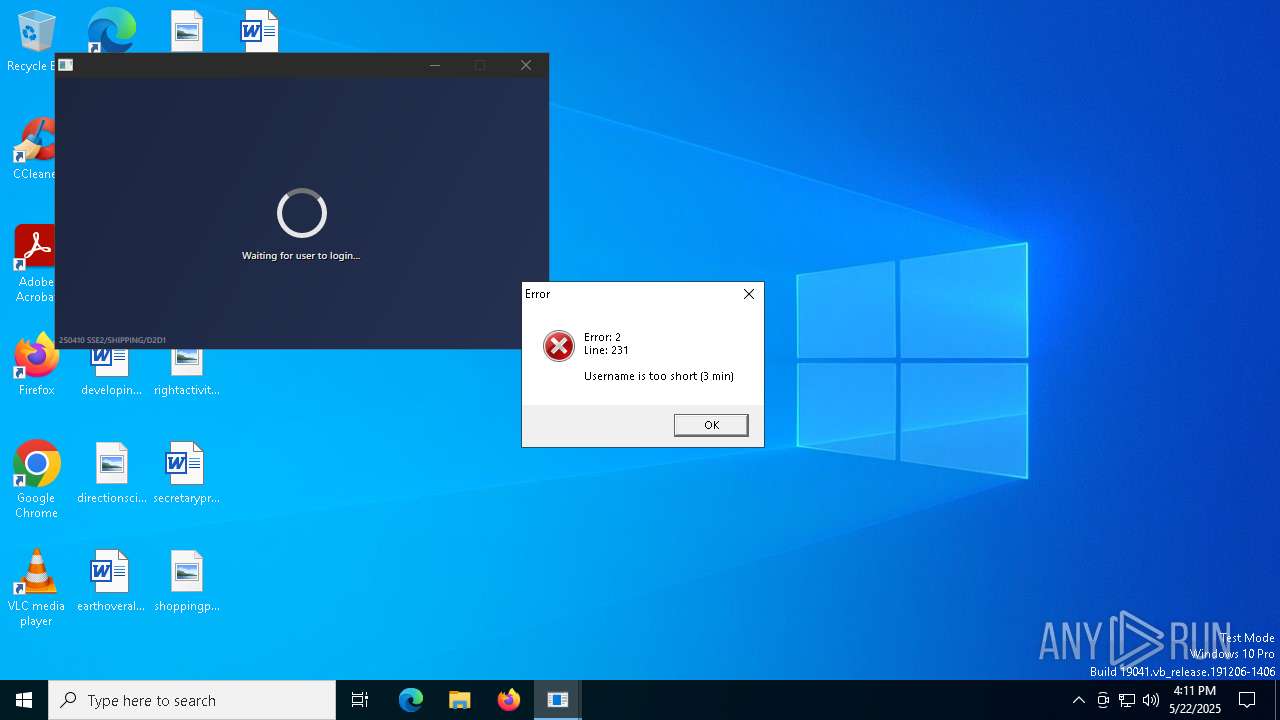
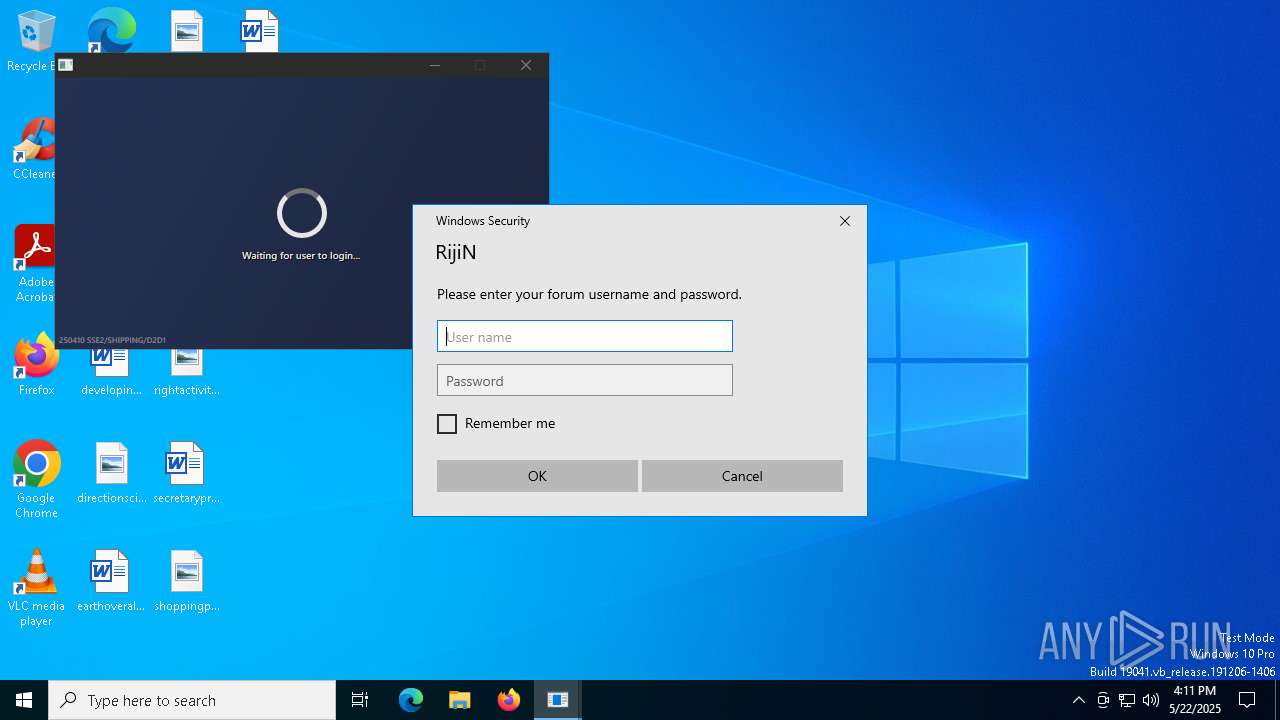
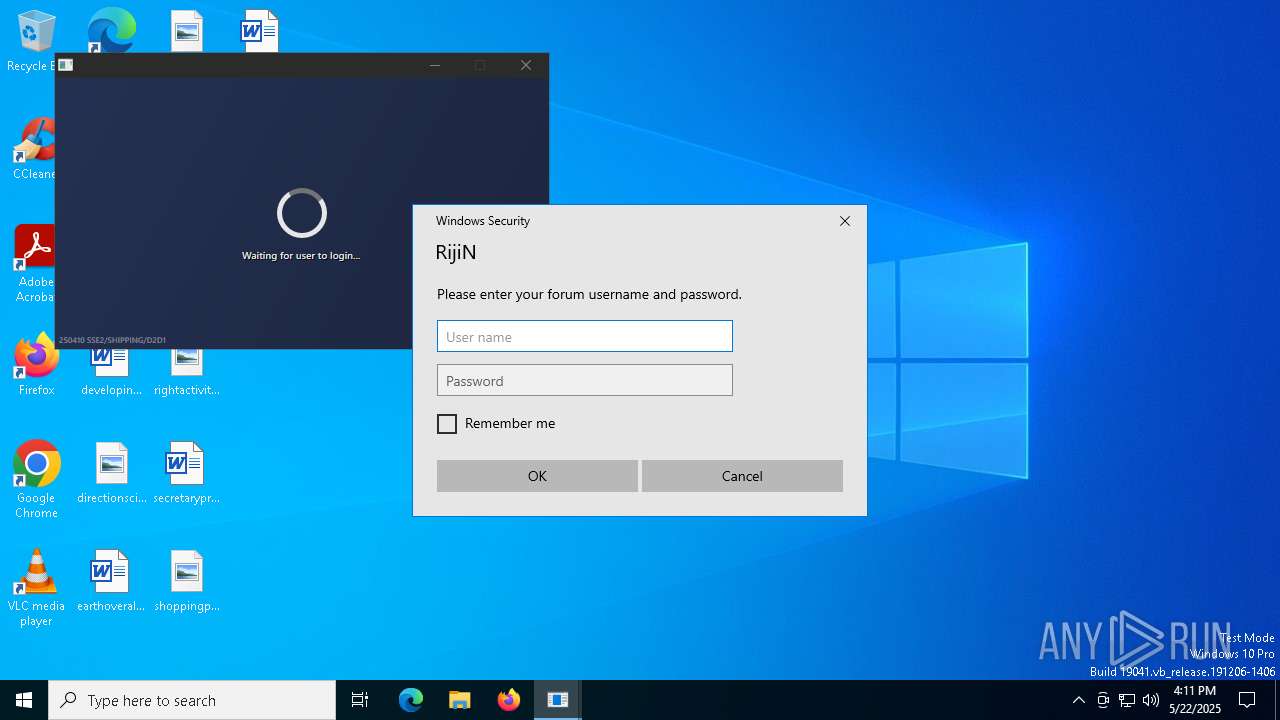
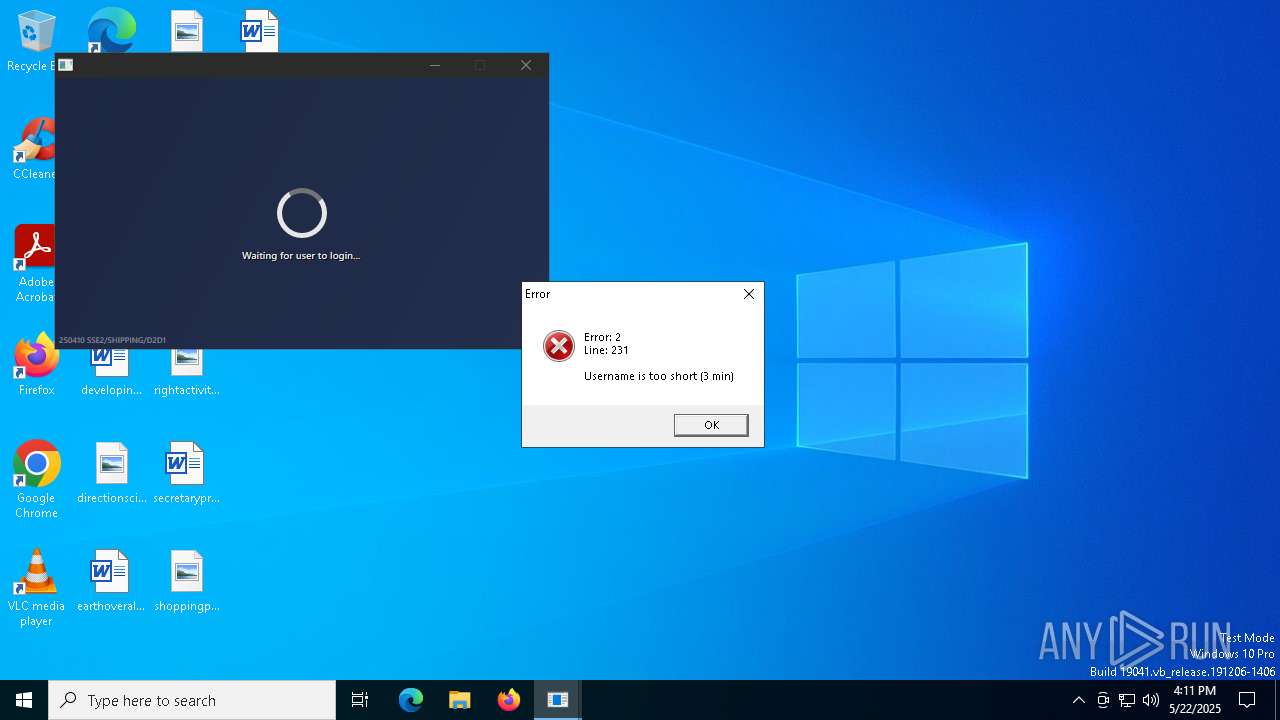
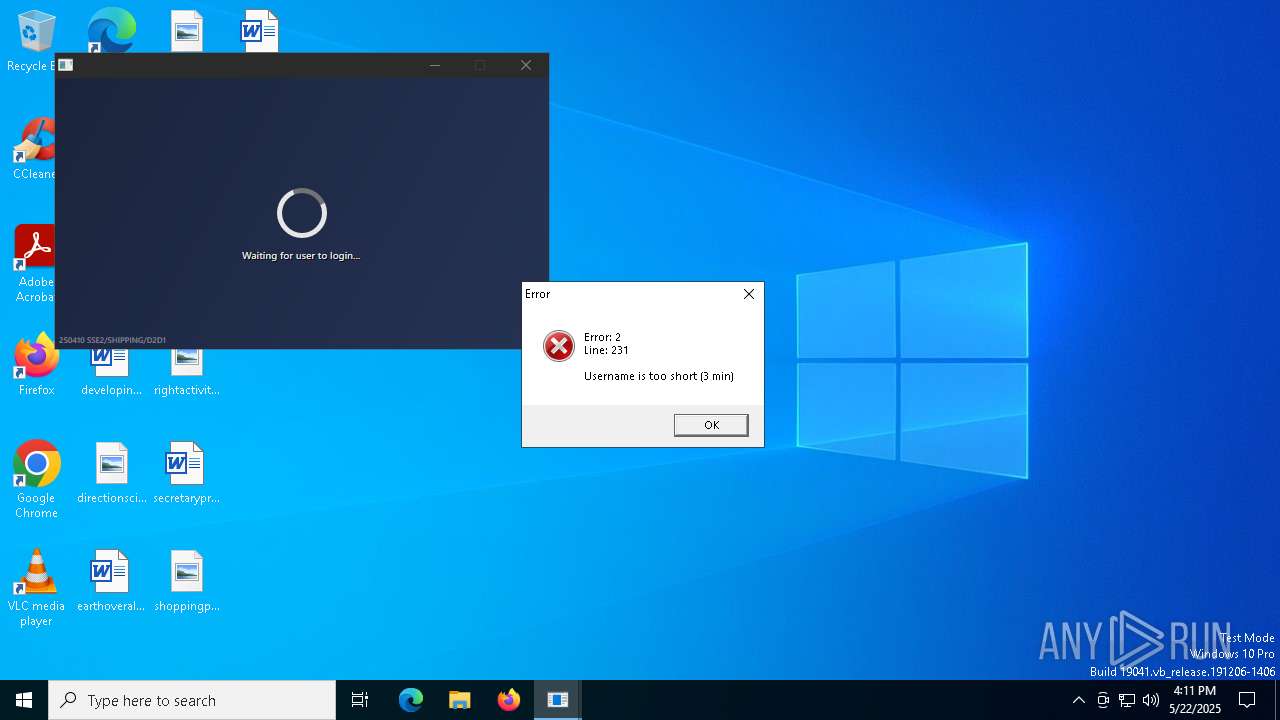
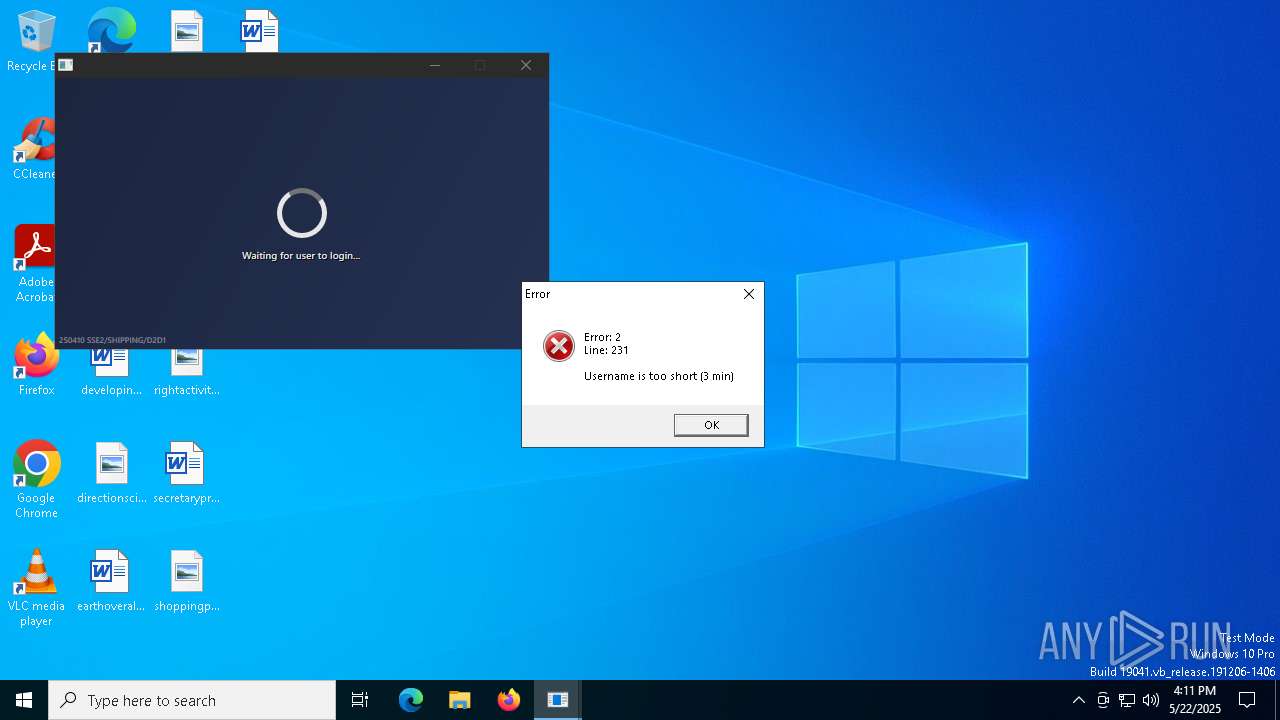
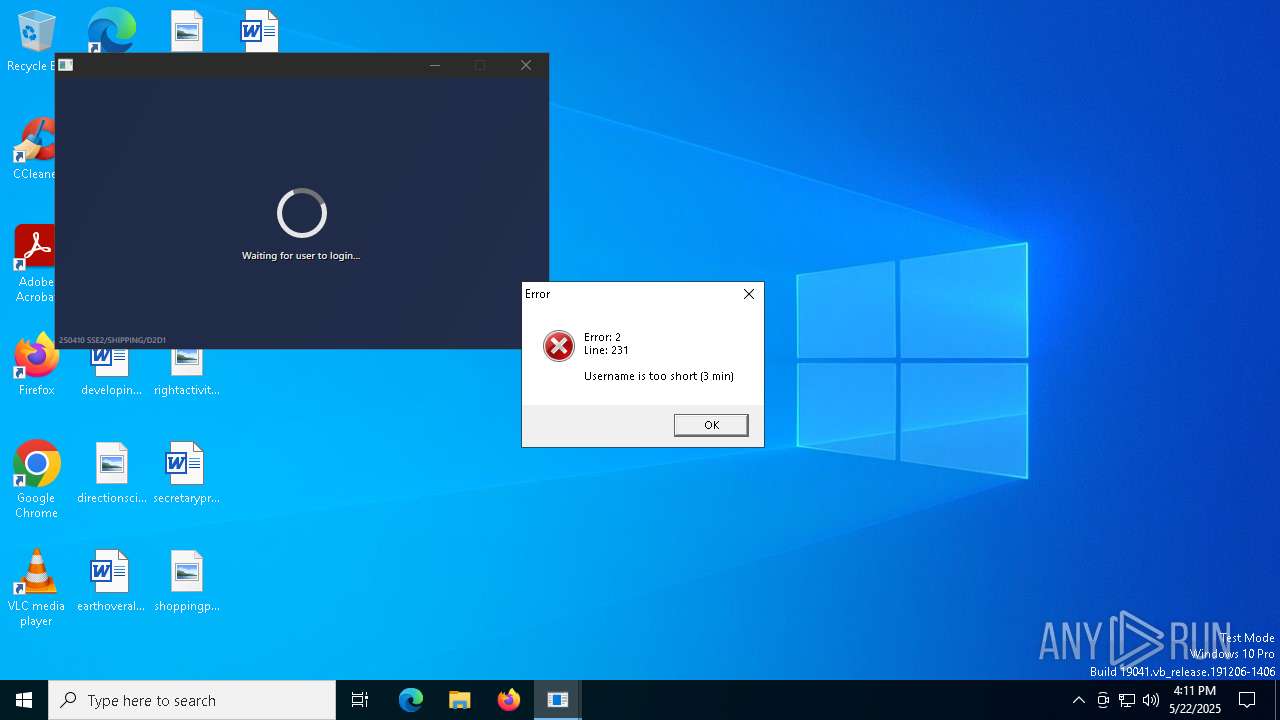
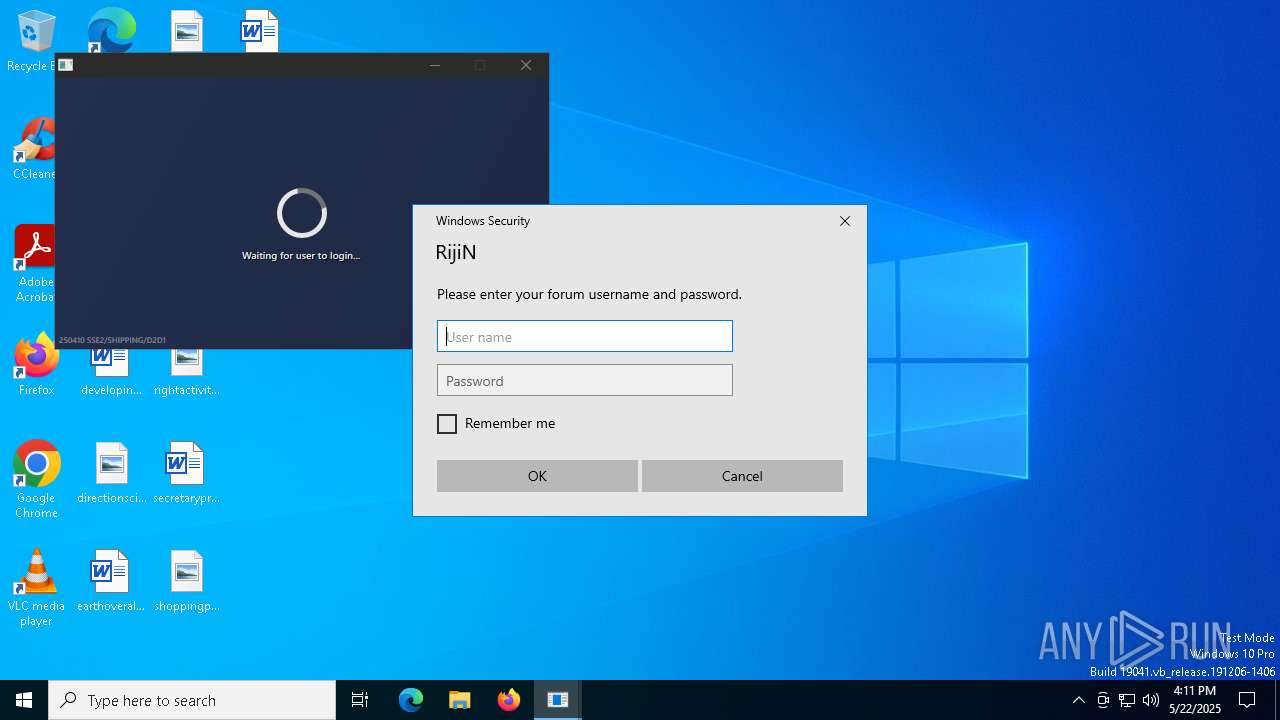
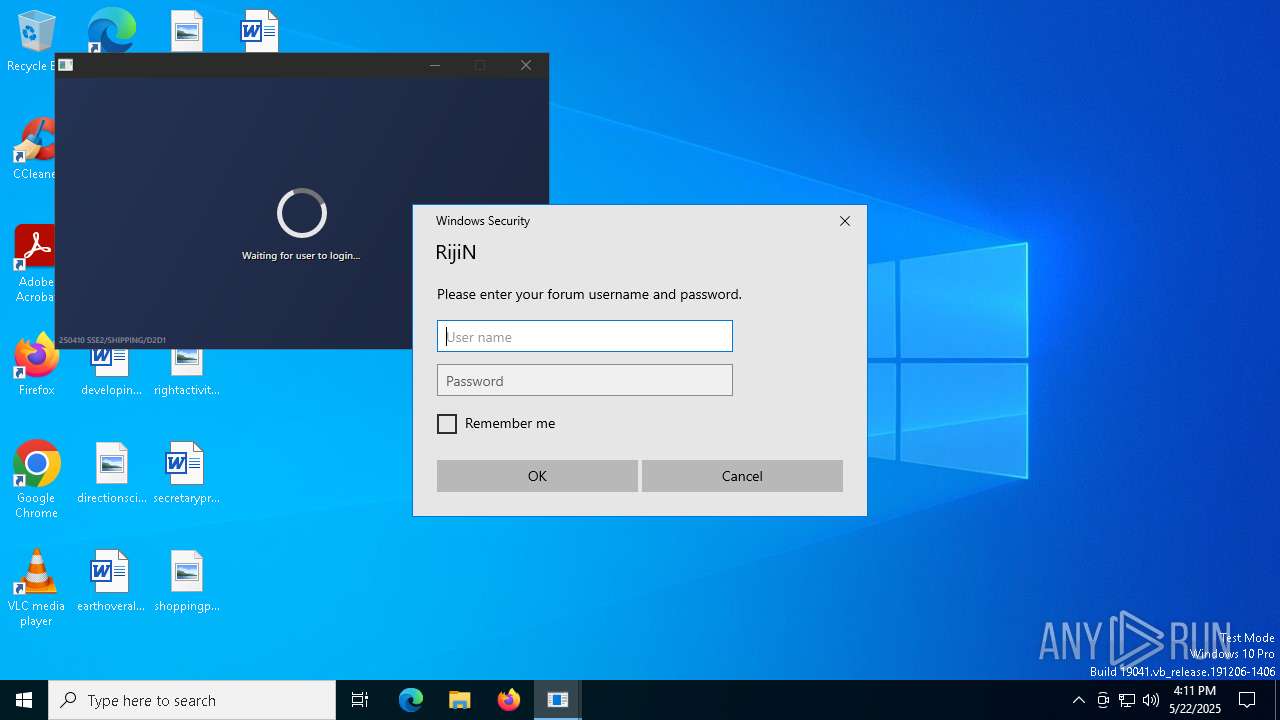
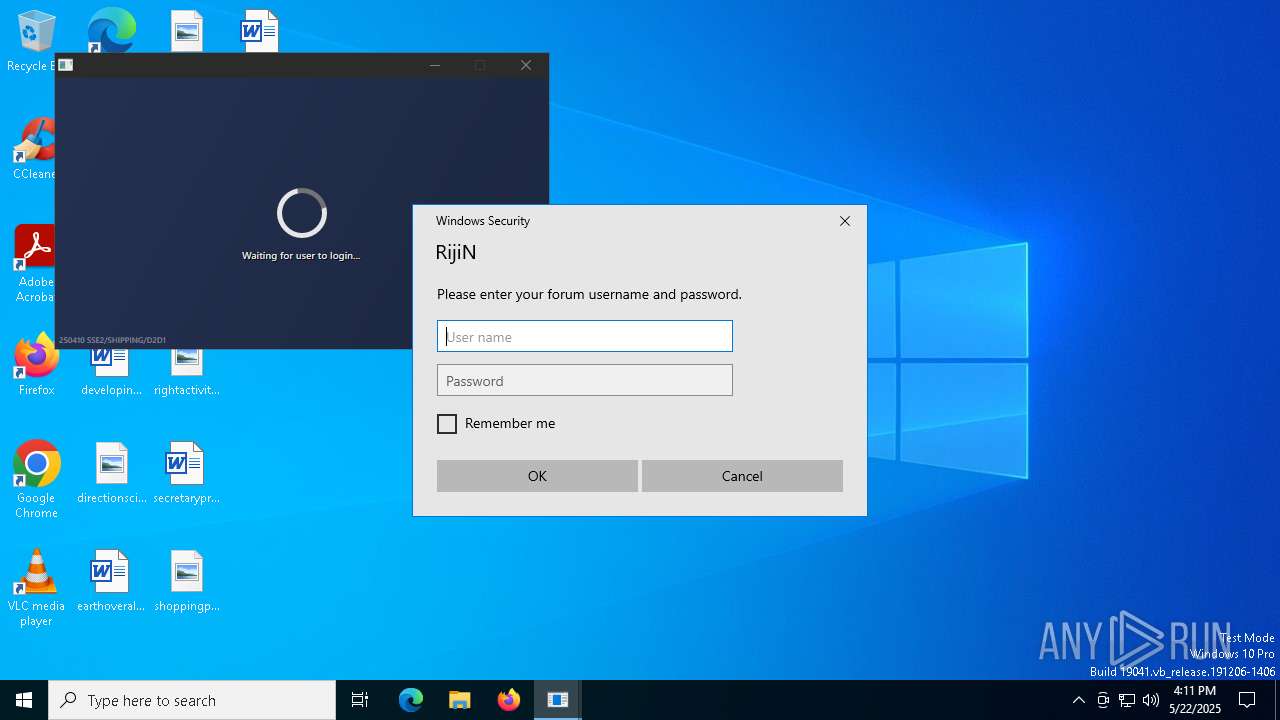
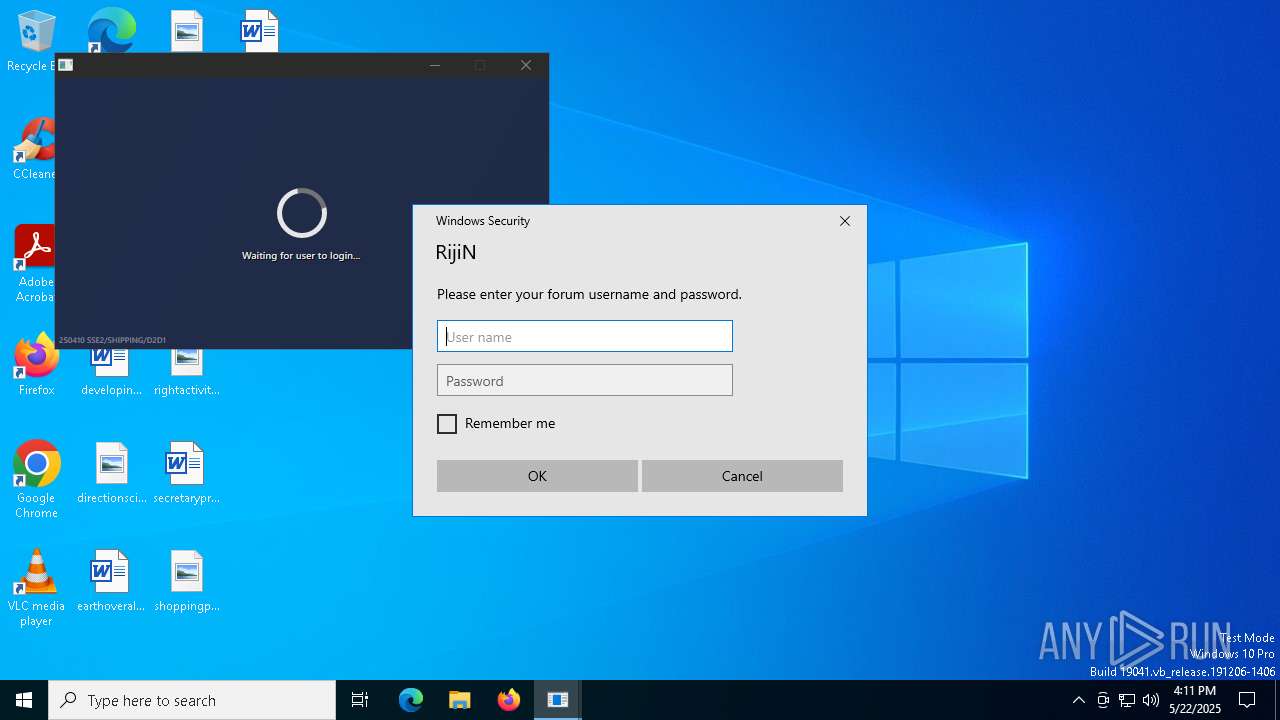
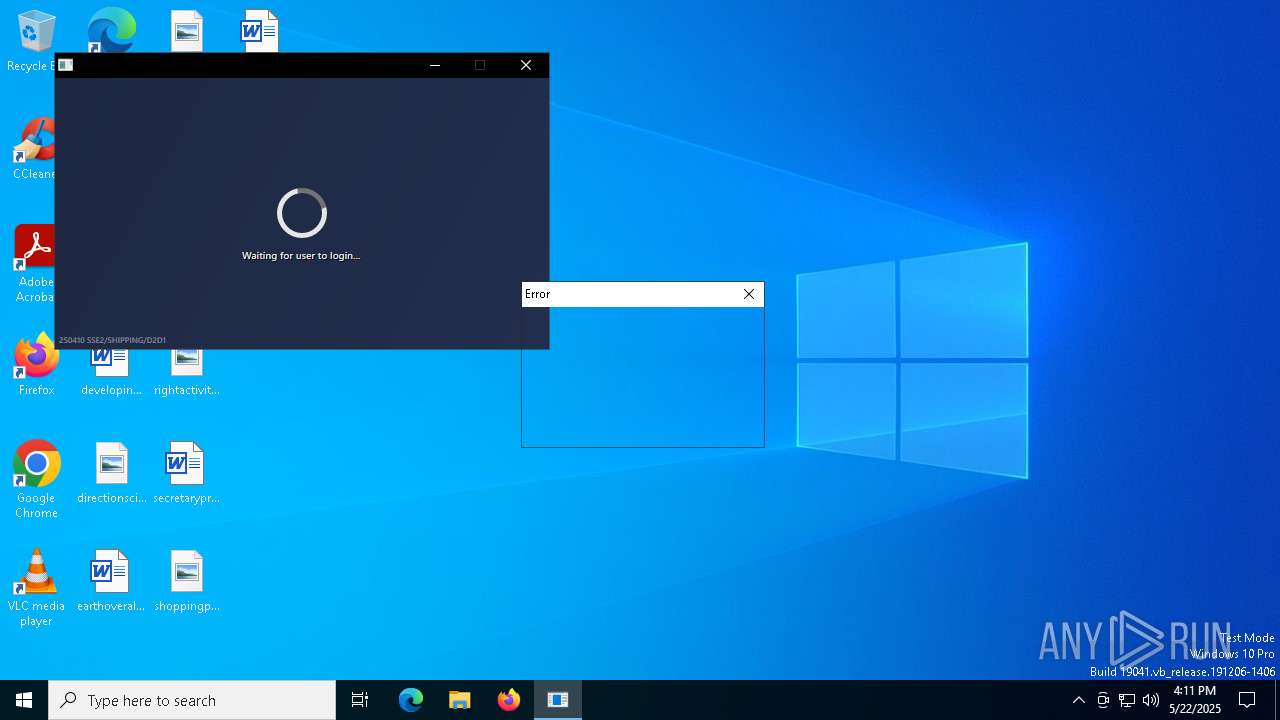
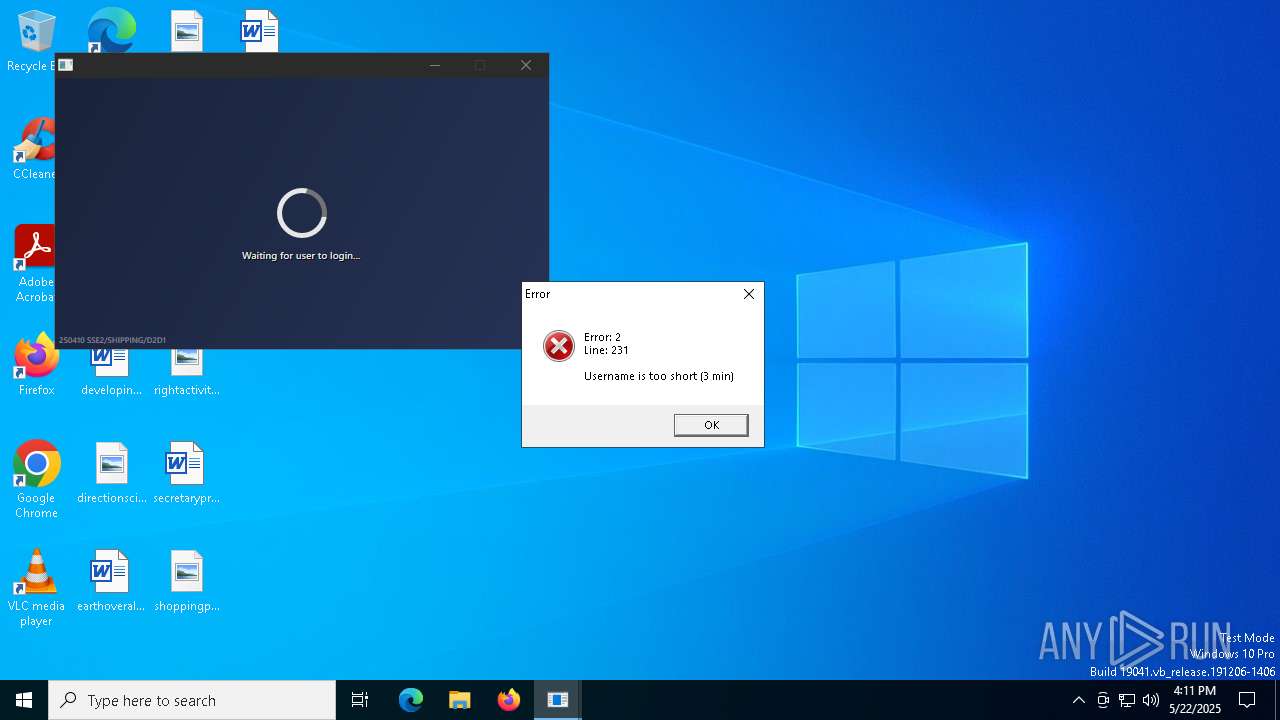
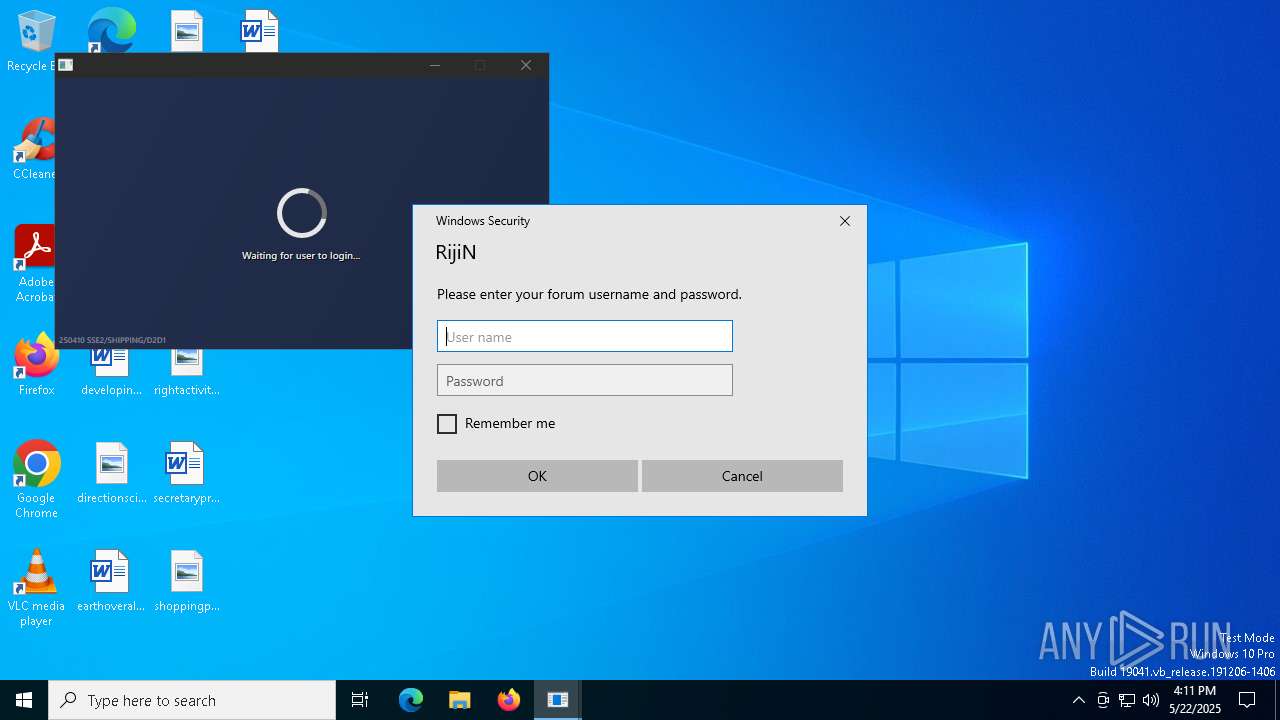
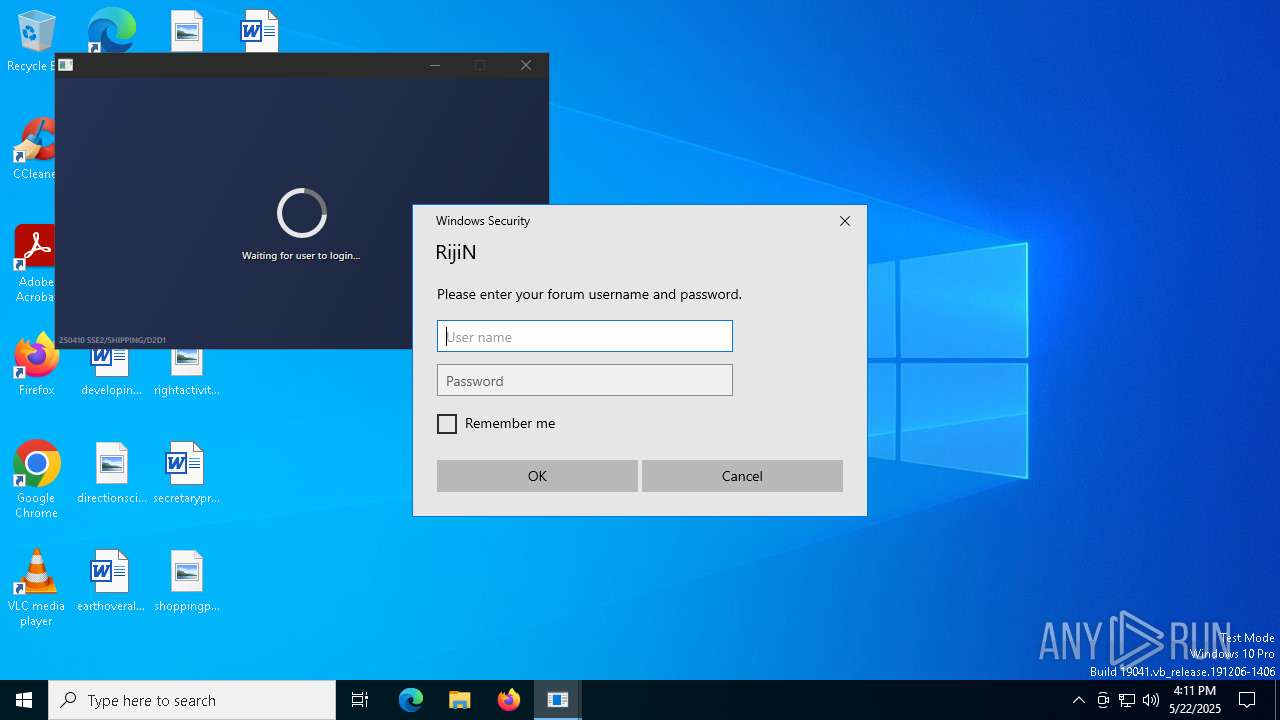
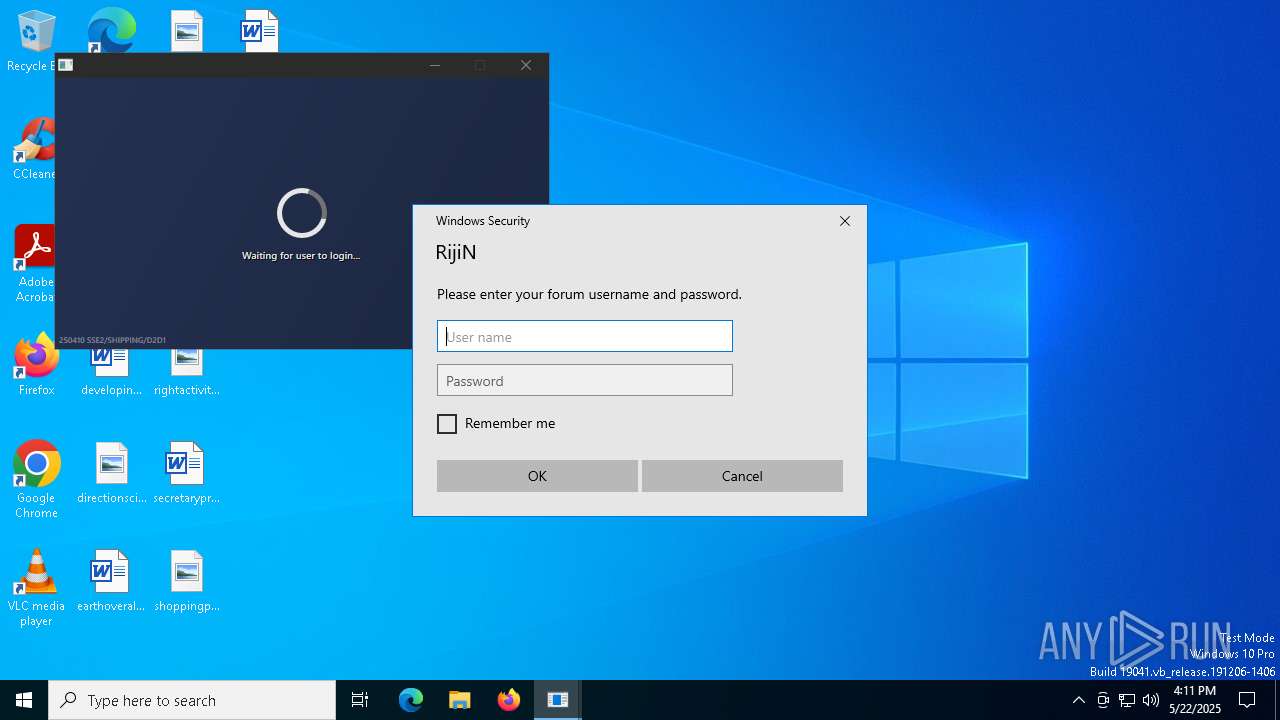
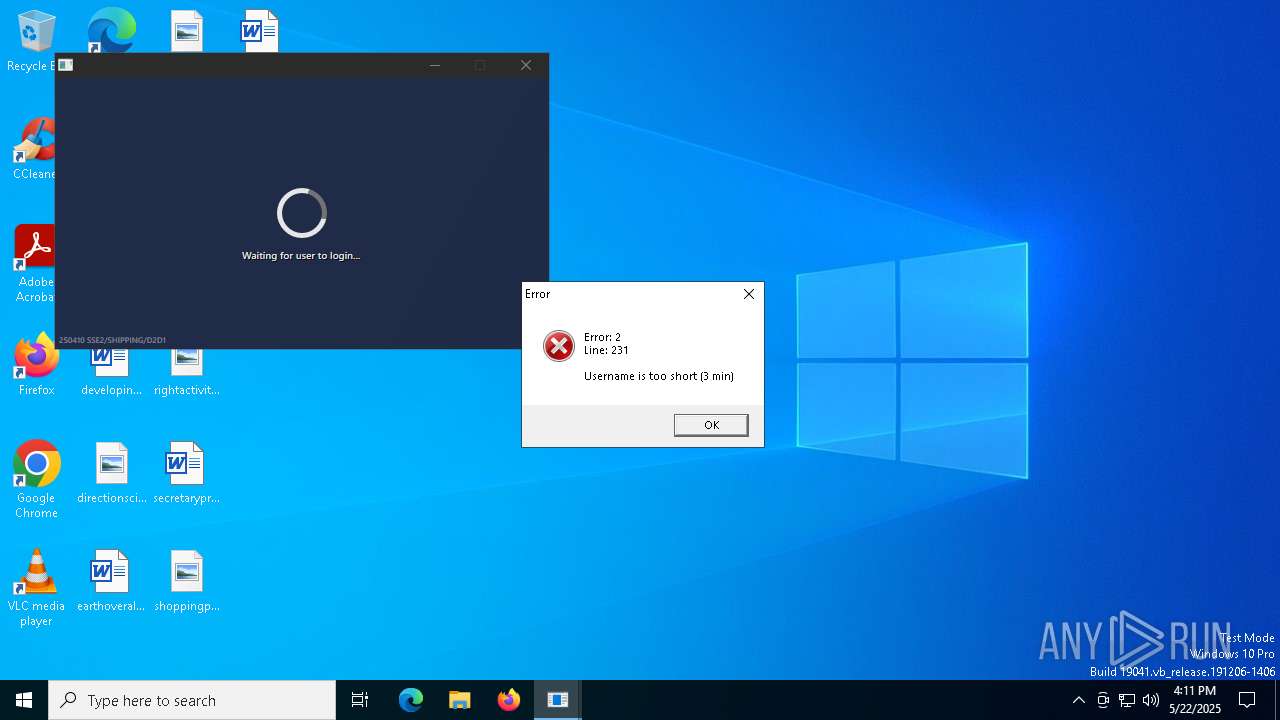
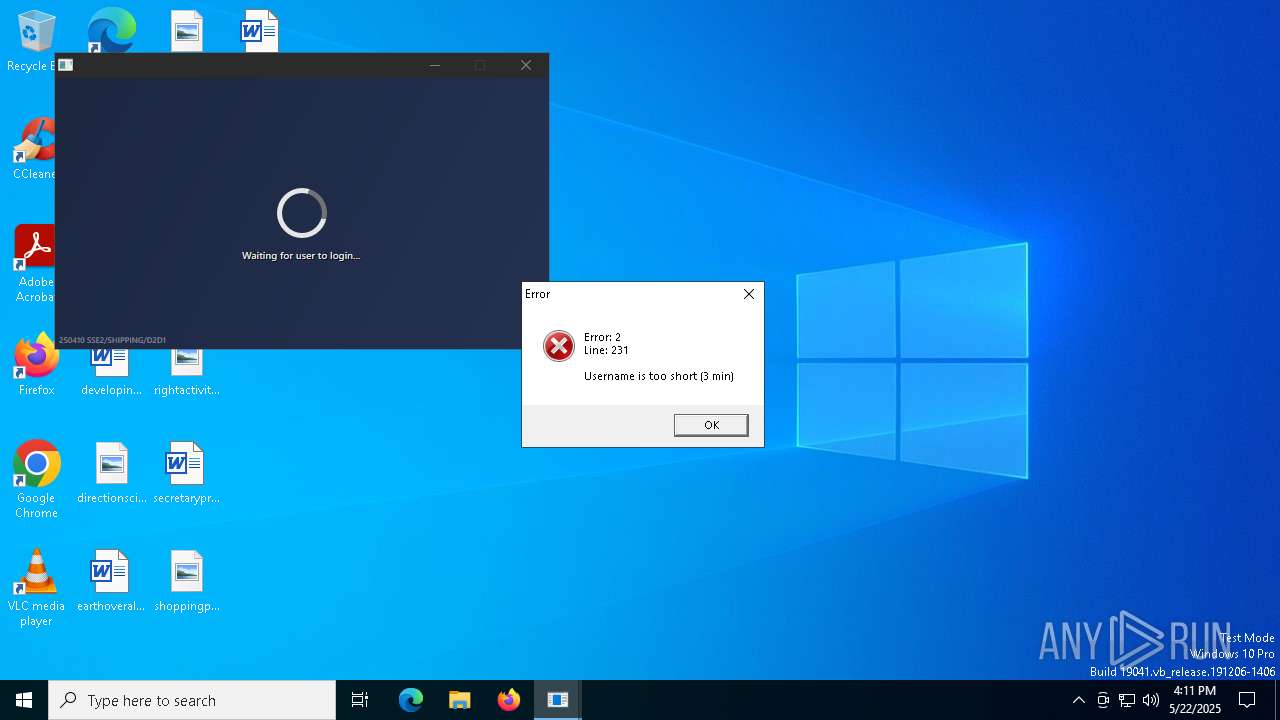
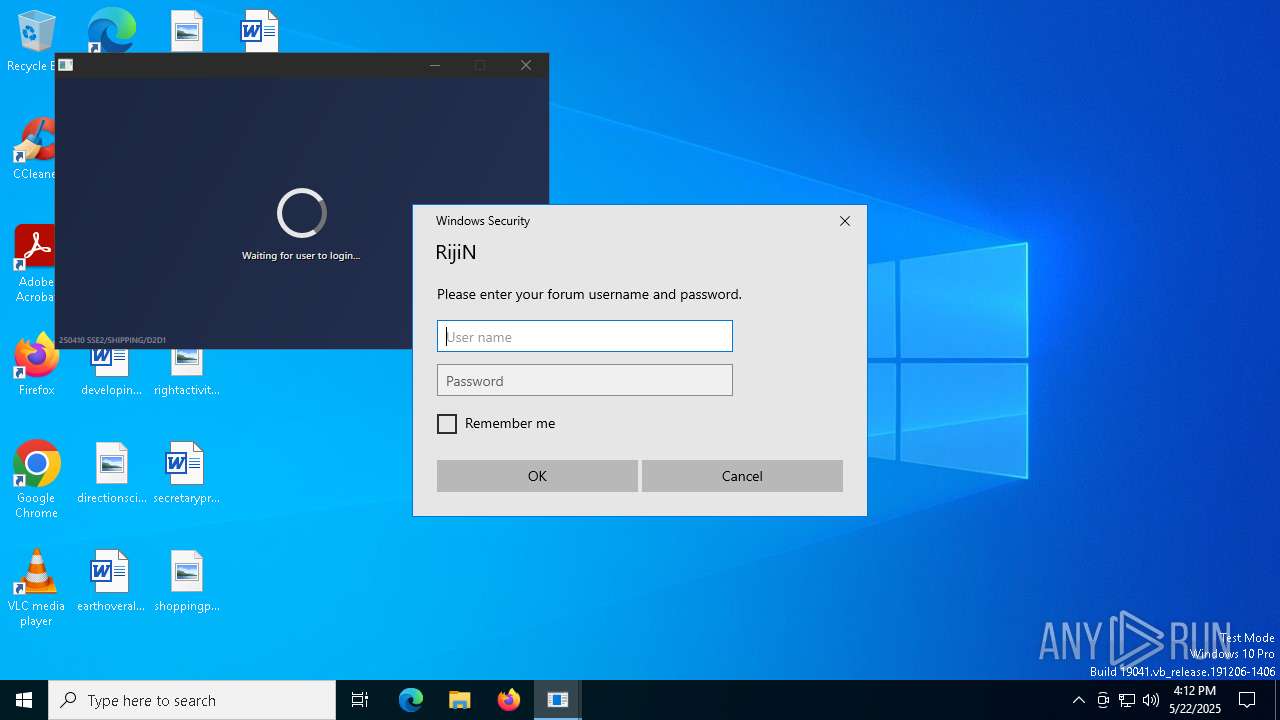
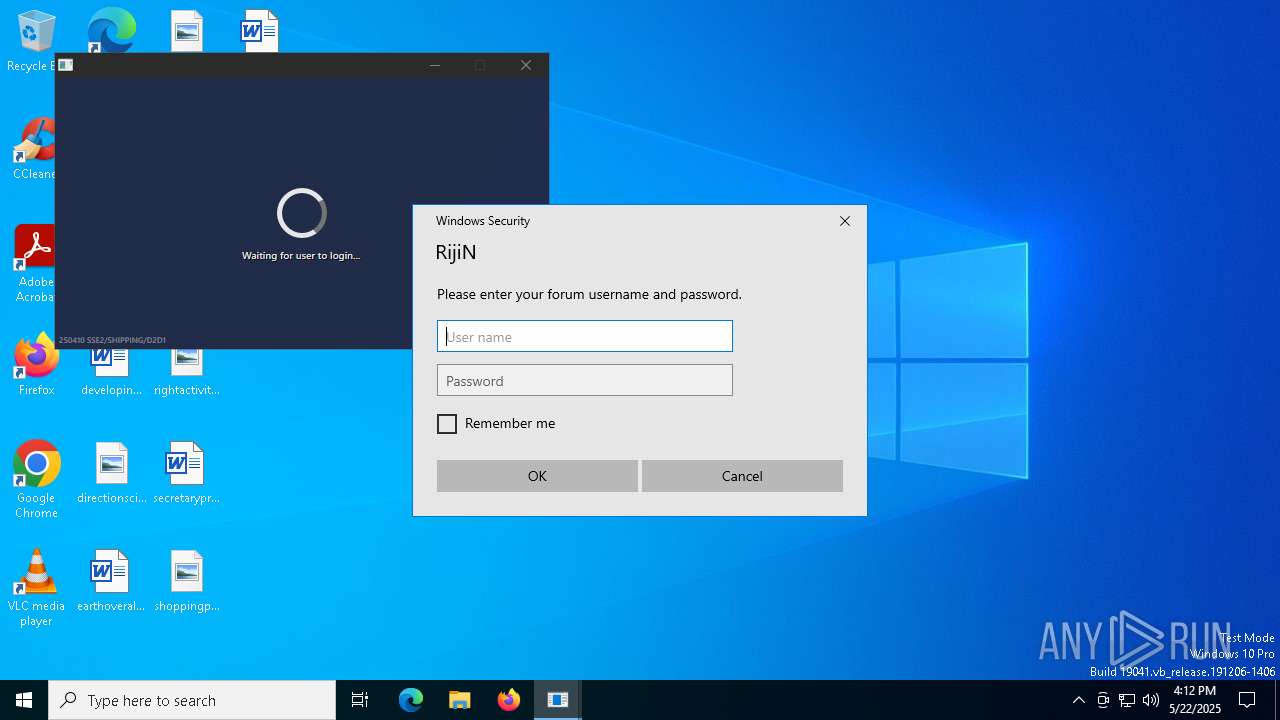
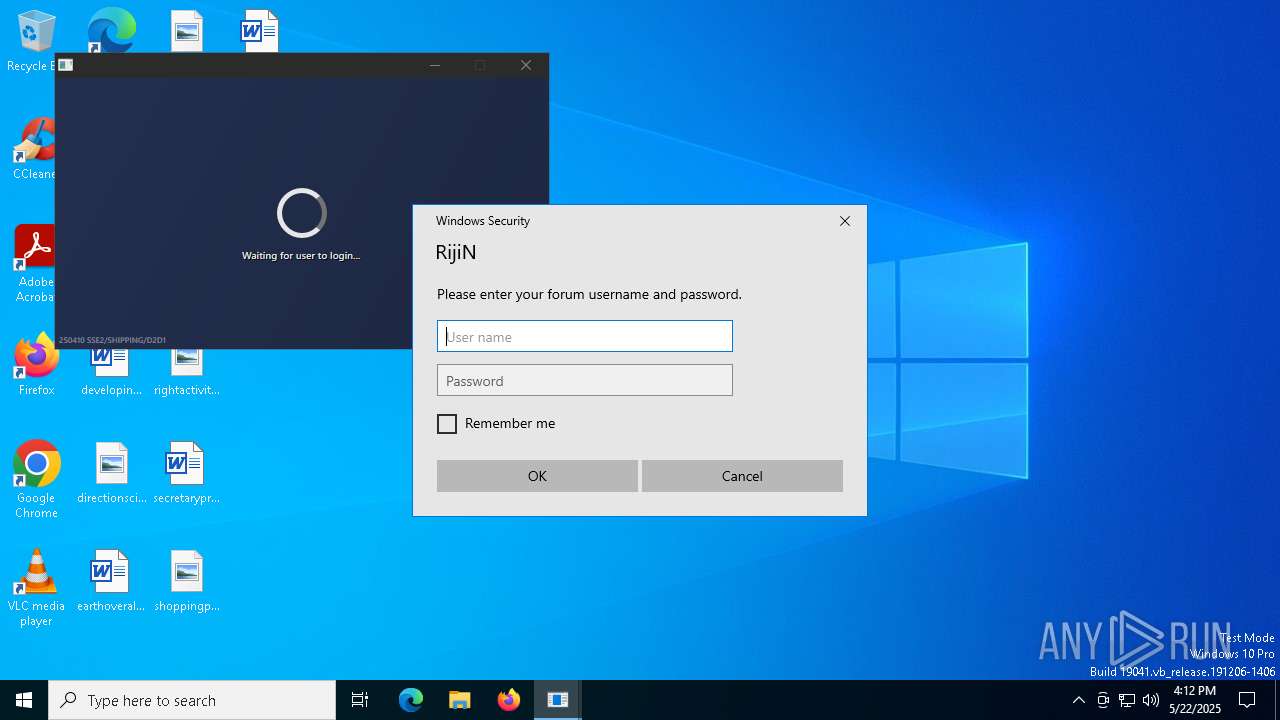
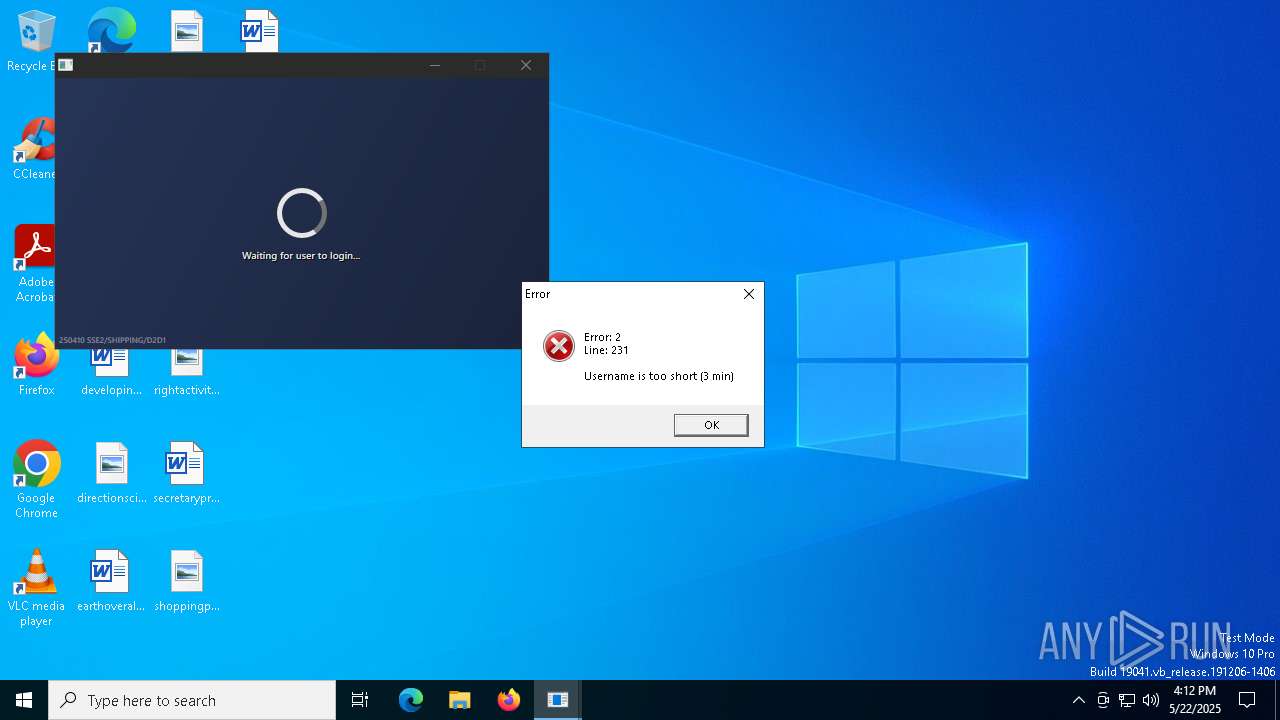
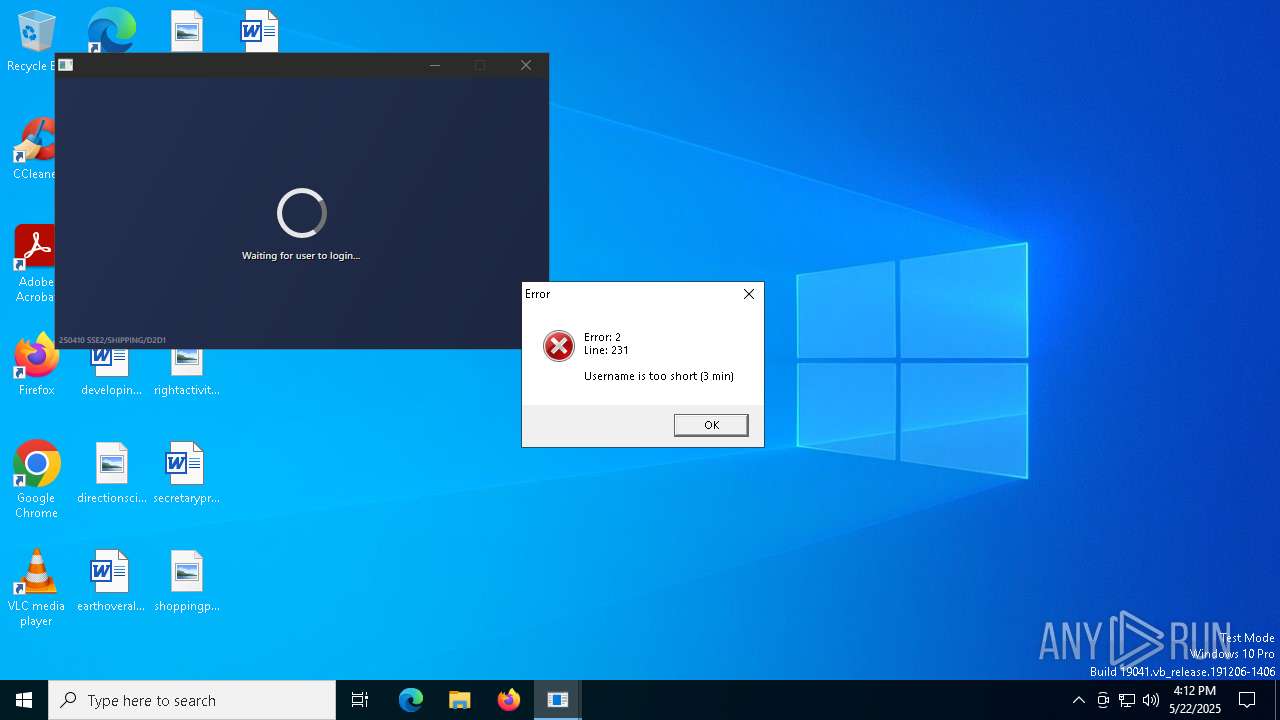
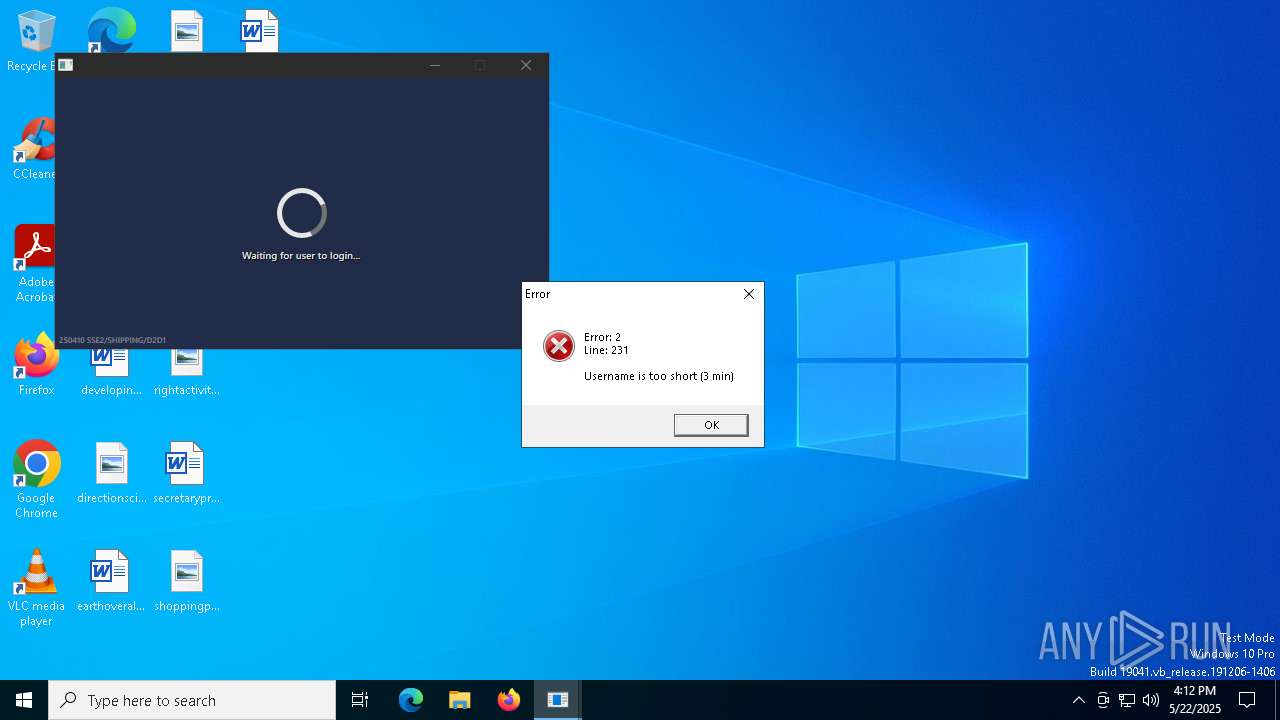
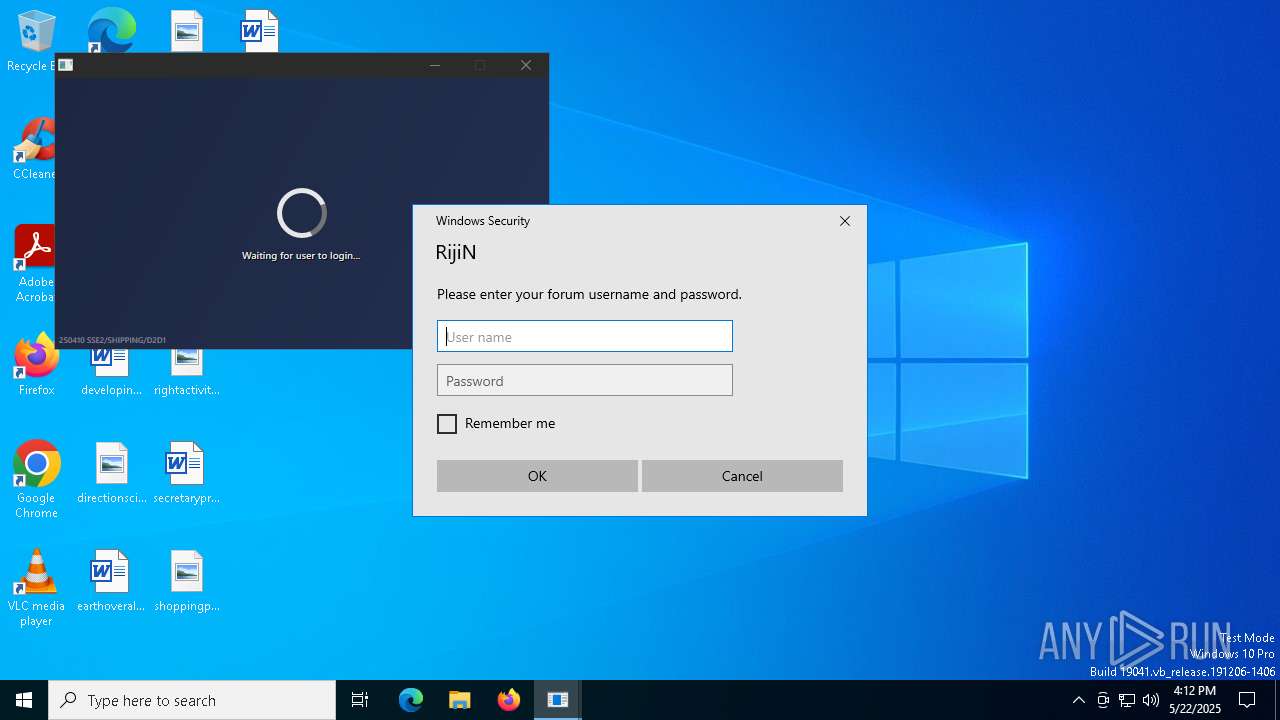
— | — | GET | 200 | 172.67.75.147:443 | https://loader.rijin.solutions/ | unknown | binary | 25 b | unknown |
— | — | GET | 200 | 23.48.23.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 172.67.75.147:443 | https://loader.rijin.solutions/ | unknown | binary | 16 b | unknown |
— | — | GET | 200 | 104.26.5.55:443 | https://loader.rijin.solutions/ | unknown | binary | 16 b | unknown |
— | — | GET | 200 | 104.26.5.55:443 | https://loader.rijin.solutions/ | unknown | binary | 16 b | unknown |
— | — | GET | 200 | 104.26.4.55:443 | https://loader.rijin.solutions/ | unknown | — | — | unknown |
— | — | GET | 200 | 172.67.75.147:443 | https://loader.rijin.solutions/ | unknown | — | — | unknown |
— | — | GET | 200 | 104.26.4.55:443 | https://loader.rijin.solutions/ | unknown | — | — | unknown |
— | — | GET | 200 | 104.26.5.55:443 | https://loader.rijin.solutions/ | unknown | binary | 16 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.48.23.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
1312 | 2687cce9b128142e1abe21d641.exe | 104.26.5.55:443 | loader.rijin.solutions | CLOUDFLARENET | US | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5176 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4272 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
loader.rijin.solutions |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Generic Protocol Command Decode | SURICATA STREAM suspected RST injection |