| URL: | http://adpop.club/ad/ad?p=38636&w=424119&d=8f334274d593d1bb5613-1547746567424119 |
| Full analysis: | https://app.any.run/tasks/65f881a2-73dc-49d8-9fad-f2560ea6bcb0 |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 13:35:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CE9C0A940FBAFEC85E4D7B0368B5D6E5 |
| SHA1: | AC5A9206AEF9391936FA3C55A015B8ED6B4A516E |
| SHA256: | 51A01FABC1C6BA27D9EEFF6219B4C98AE2082E0B5219B133976450C30047394F |
| SSDEEP: | 3:N1KfyLeSNsVZTUDSYEJWxSQiQYxprsn:Cgeisnu3T6K |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Changes internet zones settings
- iexplore.exe (PID: 2676)
Application launched itself
- iexplore.exe (PID: 2676)
Creates files in the user directory
- iexplore.exe (PID: 3272)
Reads Internet Cache Settings
- iexplore.exe (PID: 3272)
Reads internet explorer settings
- iexplore.exe (PID: 3272)
Reads settings of System Certificates
- iexplore.exe (PID: 3272)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
33
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2676 | "C:\Program Files\Internet Explorer\iexplore.exe" http://adpop.club/ad/ad?p=38636&w=424119&d=8f334274d593d1bb5613-1547746567424119 | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3272 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2676 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
365
Read events
320
Write events
45
Delete events
0
Modification events
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006E000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {BA6955F3-65CC-11E9-B3B3-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070400020017000D0023003B00C703 | |||
Executable files
0
Suspicious files
0
Text files
61
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2676 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2676 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3272 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@mybestmv[1].txt | — | |
MD5:— | SHA256:— | |||
| 3272 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\AP9SBRCG\letsdoitquick_site[1].txt | — | |
MD5:— | SHA256:— | |||
| 3272 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3272 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\AP9SBRCG\reset[1].css | text | |
MD5:— | SHA256:— | |||
| 3272 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3272 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\AP9SBRCG\form[1].js | text | |
MD5:— | SHA256:— | |||
| 3272 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@mybestmv[2].txt | text | |
MD5:— | SHA256:— | |||
| 3272 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\Y0LV9QQL\isValidNumber[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
90
TCP/UDP connections
20
DNS requests
7
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3272 | iexplore.exe | GET | 302 | 108.168.193.189:80 | http://mybestmv.com/aS/feedclick?s=Un8YNmzNixonPJYKKps9d_ZKRsqpyl7xExJj-rHjFyq2B9pS1AP6z7UC6hWIeTga6IkCbg7sKEuYDMm3vSUGcJORlQ2rbxGECjkov8YM76EuKFV3LeOk4LCyP0WpYsxEdK1dP10-rENdY6mfGvI2XPFJKZLgl4KMhFZMCD59ZCBddpb8E2I8-S7hO2rh_Lg9qlYPbaXGIyebQMIT6sAQO5tS2NK2Kx2zHS-5wBg_2Im67lYTUL2wb1fTBEY8lHgjoqIAk3C7e3Z9CaY8rQvI2t7cWzkbsNLWY1vddW45Mo1ebCHjdDvADxRK3CUwUYvZOkNilTjSUkKyXO_jzx49lndmxoUc5e52J0_MmJ6cfbKv_Gjg3ynxTLgefl8uXiTQNzRWkMJ-zlKeuxgCPMctn0bNeY6IWcigYBbscOSat2nHlnyvmVBRTZK59CpqvpJLYyN02eNUH6phA-4K1BuJROjGJFSuZbKq_bwKnac_58omFPuDshHnkMNWEyObfloiLbUPJ_QFkPxnT8CHTcmrOUEymqLXOrJntsvlN--Gh3eoANVd5amvNregidcrOCkYcVT1yeguxxm82IKrOgwIDKI3hUugwXxnepP95uGdXpybiPc-mvqsqXeAbHINNLnfmWLhoKNLe_Sw6V6FQUqFUqUGB-hTo_x2bKsBrNYoYHF7-prIrMxZF3PI_nuafp0gRyg5BHHuNQCc1iS55-BzTAFGl60mOtmCr7N4w23V5aIDNjyO9r6XHRJPXOUAcShJyH7PubPaaKC-k5l2l3k0a7zBQyyFdInSvBcIMZ57u3WE_imsilis1qDPrtRGDzW5qW1xLpUl6ipQY24NBFDdkiltLtTSwQQsGJA41-tnBh1_M_7YGnEy062bP0wB66DRqB6NUit6FEYLRbLirBn0pYvVfe-HEL7Zszbue15UP6Uxs03P2Xe8w_0Xg_elpkgoR0CabMsVe5sbMaImtnvHgghjo2cNd3ap3wycnespMyveOvO9uK7YZEWvFb9cvSH1olvMisrk30QMecdJiaig-2XsvX-afd2iXFgJChCtmxvzoNZ4tkGvqQYR6M0vAVhtZXk3QBiLZvrUpwaHS_HGb-Xv_IUuOYIu_ZrlQFraq8Rl6_B92KWGq22hORw9frNRXWibSMfwjb5fXMMQdbWjRCjzGkeDKKcfn-JBRc9k5n4f15kq1T9YmKkvyUj-INHFP9Rlbk9t-tSJUfDBQbtezsFpVXlReYscojdNBE7WA-68Uu_gjHQsr-UmGy2dMibIge9R_vETjn174qiv9l7bc1FFbmSk5V33hXa_lsNcujJ4w9oyqdMtzLa_BrSOi9wcgWZ8-ZgMANHyYWAdJYTdNsVc1IeBtu8wlowVyVizsrk8_aN4FOYP9nmrpF2dWKFVkziLpJGwgptML-6AWwHD61QWT_43dYpkcQk5JcAoyAc2RaImiQoPPbIUB5p-3Z35_Qn9yMrHpZve9ujfy_lhR4YqnWUdg75ONpp96xGc3tfuquOMc5Hpzh2fjeAc5t0jNSFAykqe2j-0e3JF--dkN6WOcdglUQS0wrCJ-zZCr9k | US | — | — | suspicious |
3272 | iexplore.exe | GET | 302 | 108.168.193.189:80 | http://p149800.mybestmv.com/adServe/adClick?ai=TrP5_tk6CgzWsE8MbjWJovXD0bhlaABzGZ5OeOwR8FN-aymSJqAJgvWba3rqvBjMYeGH5Bbb_Dp4S1RRoBu74sUJHM76nA6vEHVhE4C762NEcVMqZBH3Dg92Eaff8LU-fMzFNJbfcT6WWmDgWFl_FI0PZh-lEizEI3kQKm0756fN0guj_pizTGDQyTIsw_XM-vexgvrnfbYfs6Cn0z345hNjid0jYo97YJ7YT0u4bz4vuynfPFs_KFxhBIuZvoGPvsB0iuJvaA4l_jIE1GWrF0-cSEhrDbOxEkcnN0O_o7n7N9RLydVTTptZB4PUkMcort_GhLNyjcewpth3iNEvd_P4BsKUl697UgDHGPx9sdOxxaLzhkg6TSol4S5osn5YR0Ng4Sbb-ewIqJ00PG5Xmw&ui=Un8YNmzNixonPJYKKps9dwGrA0T5v6goqr6t-KMioAN2jjNx9HC2P8dMIdM2cP0aEJVQ1V6618o7nGO1z2fQtdr_okiJEF_9KE5PIJyK0nVZxQb1ROvnGFhhZLybLMBFzb8xqxPI4f4&si=1&oref=4befd9d7b1c0ee8d28b77358ff33eb64&rb=g023FNjug5I&rr=0 | US | — | — | malicious |
3272 | iexplore.exe | GET | 200 | 5.23.49.230:80 | http://ceomax.xyz/landers/bitcoin/index_files/css.css | RU | text | 1013 b | suspicious |
3272 | iexplore.exe | GET | 200 | 5.23.49.230:80 | http://ceomax.xyz/landers/bitcoin/index_files/style.css | RU | text | 94.9 Kb | suspicious |
3272 | iexplore.exe | GET | 303 | 107.23.44.231:80 | http://adpop.club/ad/ad?p=38636&w=424119&d=8f334274d593d1bb5613-1547746567424119 | US | html | 1.61 Kb | suspicious |
3272 | iexplore.exe | GET | 200 | 5.23.49.230:80 | http://ceomax.xyz/landers/bitcoin/js/form.js | RU | text | 12.7 Kb | suspicious |
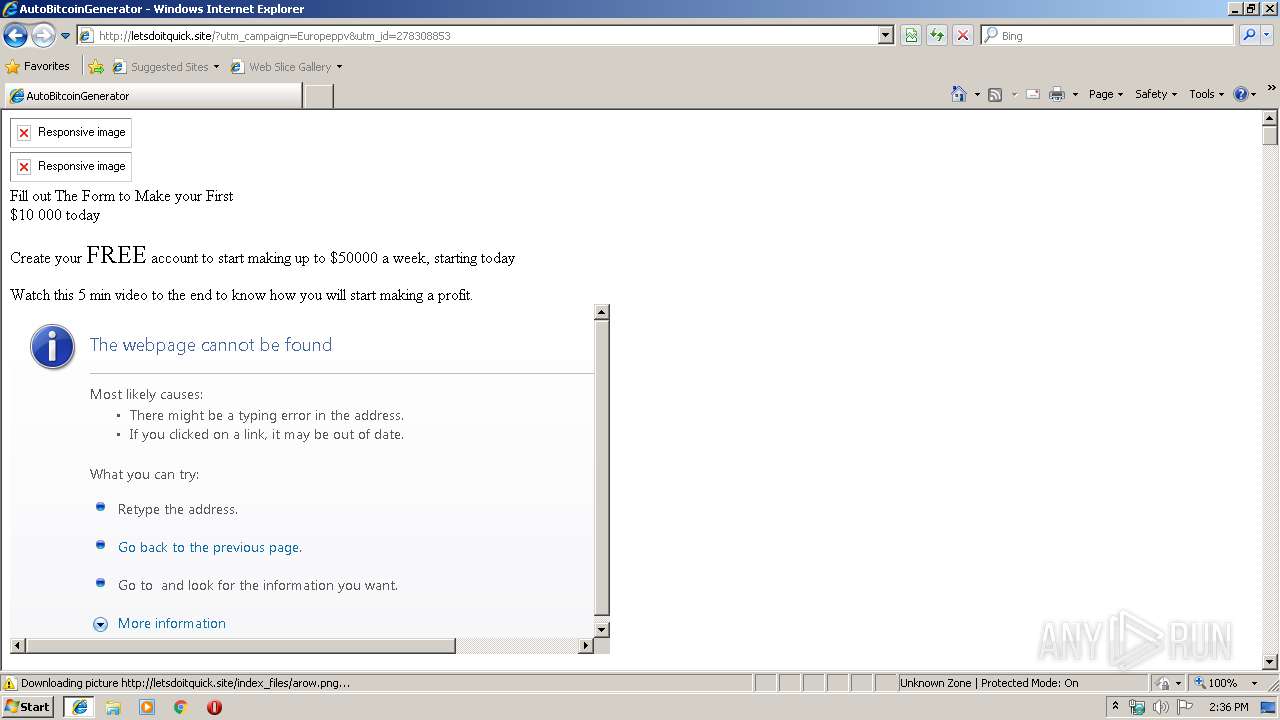
3272 | iexplore.exe | GET | 200 | 91.235.129.60:80 | http://letsdoitquick.site/?utm_campaign=Europeppv&utm_id=278308853 | NL | html | 28.2 Kb | malicious |
3272 | iexplore.exe | GET | 200 | 5.23.49.230:80 | http://ceomax.xyz/landers/bitcoin/js/rdrCookieModule.js | RU | text | 827 b | suspicious |
3272 | iexplore.exe | GET | 200 | 5.23.49.230:80 | http://ceomax.xyz/landers/bitcoin/index_files/logo.png | RU | image | 4.58 Kb | suspicious |
3272 | iexplore.exe | GET | 404 | 91.235.129.60:80 | http://letsdoitquick.site/js/form.js | NL | html | 208 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3272 | iexplore.exe | 107.23.44.231:80 | adpop.club | Amazon.com, Inc. | US | suspicious |
2676 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3272 | iexplore.exe | 108.168.193.189:80 | mybestmv.com | SoftLayer Technologies Inc. | US | suspicious |
3272 | iexplore.exe | 91.235.129.60:80 | letsdoitquick.site | ITL Company | NL | suspicious |
3272 | iexplore.exe | 5.23.49.230:80 | ceomax.xyz | — | RU | suspicious |
3272 | iexplore.exe | 205.185.208.52:443 | code.jquery.com | Highwinds Network Group, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
adpop.club |
| suspicious |
www.bing.com |
| whitelisted |
mybestmv.com |
| unknown |
p149800.mybestmv.com |
| malicious |
letsdoitquick.site |
| malicious |
ceomax.xyz |
| suspicious |
code.jquery.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3272 | iexplore.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
3272 | iexplore.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |