| File name: | MailsBruTe - [c0d3d by @julia_pcret].exe |
| Full analysis: | https://app.any.run/tasks/9a50c891-730a-4e03-addd-025255a25776 |
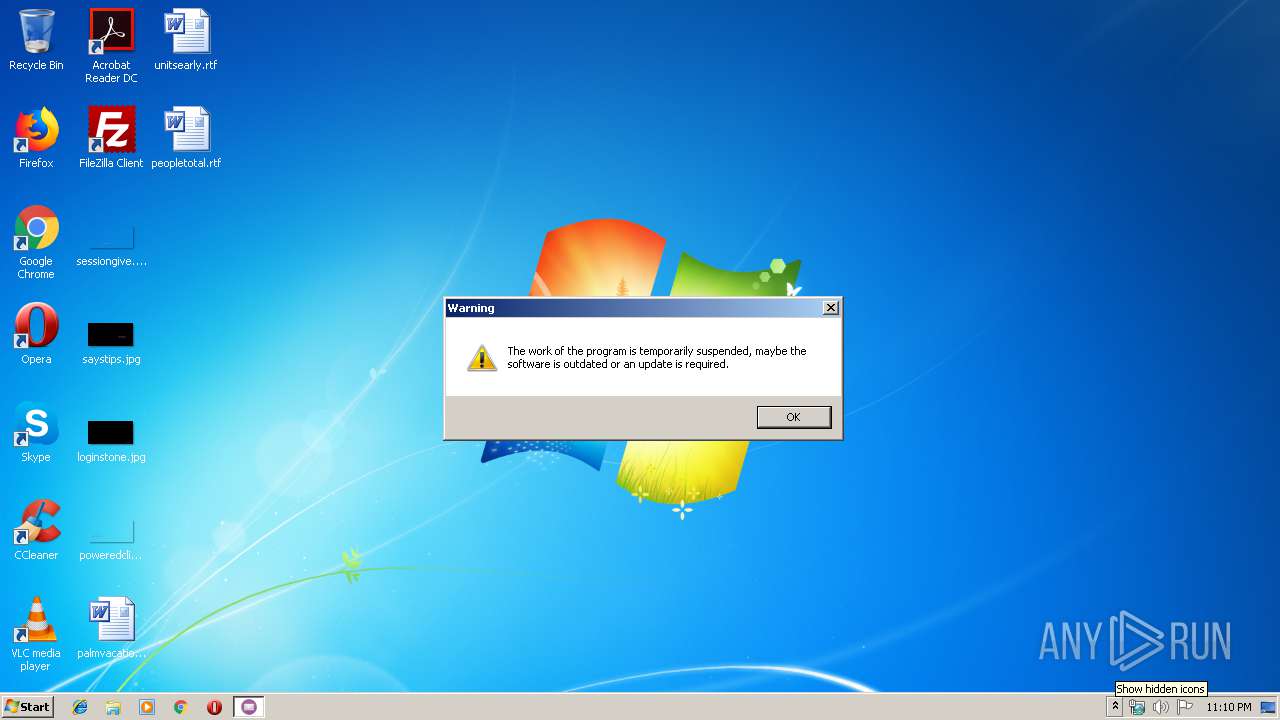
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 23:09:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AAE46FCDFC6C533727D91E25A9886C63 |
| SHA1: | 0C5C8EFA4F9F7A4E7C6F96ADA1161BAABA4D1AE9 |
| SHA256: | 51970D03E48D93628D42AE3E45FA0827487D0323C7BDD43F5C5F1FAE4B5EC506 |
| SSDEEP: | 196608:gSORJLbneCyLPRKi9WNmTgFlIgefFu9E/pVYDxYYufqaZBjHfiU6kQ:gZJDiqogFlIgetuiVYDxYYGZBTJ6kQ |
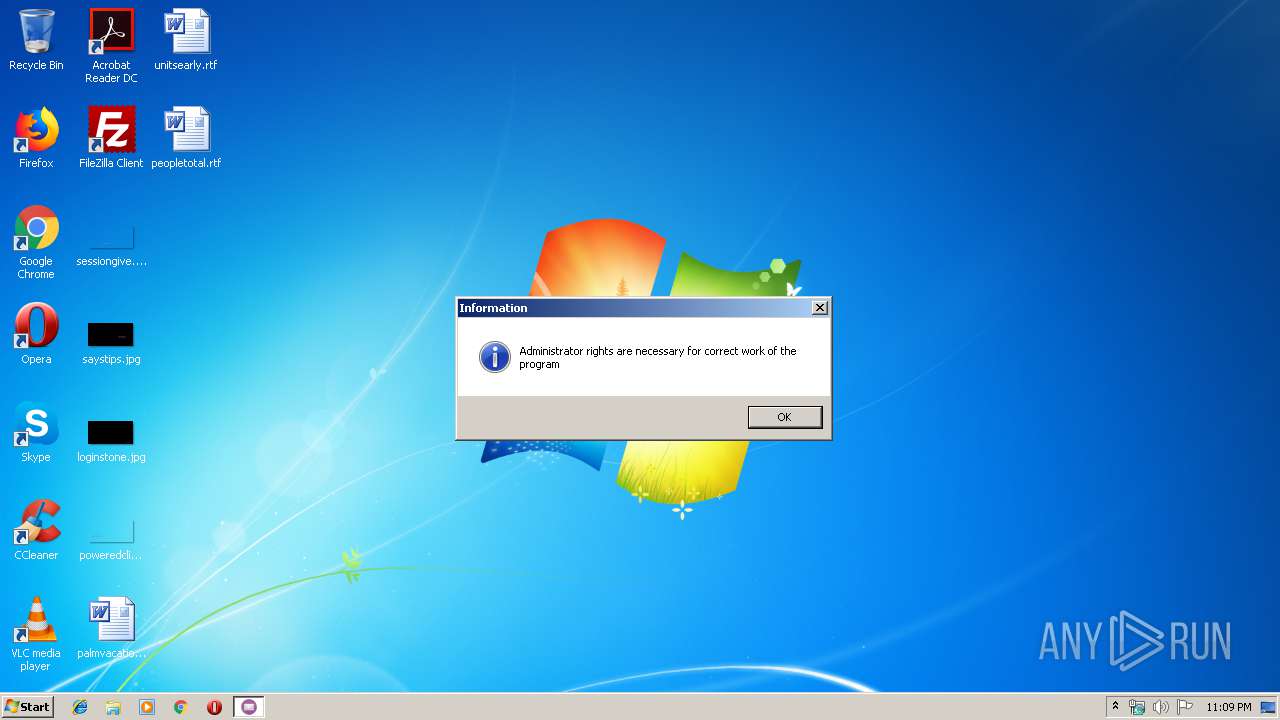
MALICIOUS
Loads dropped or rewritten executable
- MailsBruTe.exe (PID: 1448)
- MailsBruTe.exe (PID: 1768)
Application was dropped or rewritten from another process
- MailsBruTe.exe (PID: 1448)
- MailsBruTe.exe (PID: 1768)
SUSPICIOUS
Executable content was dropped or overwritten
- MailsBruTe - [c0d3d by @julia_pcret].exe (PID: 1764)
Creates files in the user directory
- MailsBruTe - [c0d3d by @julia_pcret].exe (PID: 1764)
Application launched itself
- MailsBruTe.exe (PID: 1448)
INFO
Reads the hosts file
- MailsBruTe.exe (PID: 1768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:08:14 21:15:49+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 188416 |
| InitializedDataSize: | 69632 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1cab5 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Aug-2016 19:15:49 |
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 14-Aug-2016 19:15:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002DFE8 | 0x0002E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.71025 |
.rdata | 0x0002F000 | 0x000099D0 | 0x00009A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.15287 |
.data | 0x00039000 | 0x0001F8B8 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.29547 |
.gfids | 0x00059000 | 0x000000F0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.12367 |
.rsrc | 0x0005A000 | 0x00004714 | 0x00004800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.17139 |
.reloc | 0x0005F000 | 0x00001F8C | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.62986 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 3.88998 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 4.12176 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 4.68705 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 3.66634 | 508 | Latin 1 / Western European | UNKNOWN | RT_STRING |
8 | 3.71728 | 582 | Latin 1 / Western European | UNKNOWN | RT_STRING |
9 | 3.74776 | 476 | Latin 1 / Western European | UNKNOWN | RT_STRING |
10 | 3.55807 | 220 | Latin 1 / Western European | UNKNOWN | RT_STRING |
11 | 3.90128 | 1128 | Latin 1 / Western European | UNKNOWN | RT_STRING |
12 | 3.68258 | 356 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
COMCTL32.dll (delay-loaded) |
KERNEL32.dll |
Total processes
38
Monitored processes
3
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1448 | "C:\Users\admin\AppData\Roaming\MailsBruTe.exe" | C:\Users\admin\AppData\Roaming\MailsBruTe.exe | — | MailsBruTe - [c0d3d by @julia_pcret].exe | |||||||||||
User: admin Company: MailsBruTe c0d3d by @julia_pcret Integrity Level: MEDIUM Description: MailsBruTe c0d3d by @julia_pcret Exit code: 0 Version: 2.7.0.0 Modules
| |||||||||||||||
| 1764 | "C:\Users\admin\AppData\Local\Temp\MailsBruTe - [c0d3d by @julia_pcret].exe" | C:\Users\admin\AppData\Local\Temp\MailsBruTe - [c0d3d by @julia_pcret].exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1768 | "C:\Users\admin\AppData\Roaming\MailsBruTe.exe" | C:\Users\admin\AppData\Roaming\MailsBruTe.exe | MailsBruTe.exe | ||||||||||||
User: admin Company: MailsBruTe c0d3d by @julia_pcret Integrity Level: HIGH Description: MailsBruTe c0d3d by @julia_pcret Exit code: 0 Version: 2.7.0.0 Modules
| |||||||||||||||
Total events
719
Read events
711
Write events
8
Delete events
0
Modification events
| (PID) Process: | (1764) MailsBruTe - [c0d3d by @julia_pcret].exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1764) MailsBruTe - [c0d3d by @julia_pcret].exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1448) MailsBruTe.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1448) MailsBruTe.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
8
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1764 | MailsBruTe - [c0d3d by @julia_pcret].exe | C:\Users\admin\AppData\Roaming\MailsBruTe.exe | executable | |
MD5:— | SHA256:— | |||
| 1764 | MailsBruTe - [c0d3d by @julia_pcret].exe | C:\Users\admin\AppData\Roaming\#SYSTEM Utilities\tregsvr.exe | executable | |
MD5:— | SHA256:— | |||
| 1764 | MailsBruTe - [c0d3d by @julia_pcret].exe | C:\Users\admin\AppData\Roaming\Fixing midas.dll errors.txt | text | |
MD5:— | SHA256:— | |||
| 1764 | MailsBruTe - [c0d3d by @julia_pcret].exe | C:\Users\admin\AppData\Roaming\#SYSTEM Utilities\midas_register.bat | text | |
MD5:— | SHA256:— | |||
| 1764 | MailsBruTe - [c0d3d by @julia_pcret].exe | C:\Users\admin\AppData\Roaming\midas.dll | executable | |
MD5:A82285DDA6F4778E5504FDF463F263E8 | SHA256:0B0EDF7067ECB7A9554FFE5743FB65BA6E25C6407C137CB3657F7B8DD046138E | |||
| 1764 | MailsBruTe - [c0d3d by @julia_pcret].exe | C:\Users\admin\AppData\Roaming\#SYSTEM Utilities\midas.dll | executable | |
MD5:A82285DDA6F4778E5504FDF463F263E8 | SHA256:0B0EDF7067ECB7A9554FFE5743FB65BA6E25C6407C137CB3657F7B8DD046138E | |||
| 1764 | MailsBruTe - [c0d3d by @julia_pcret].exe | C:\Users\admin\AppData\Roaming\libssl32.dll | executable | |
MD5:0FE22A92CA281CE90559B271C59720E0 | SHA256:697DBE0B9635F723568D0911D1C48A91C326F116F674003B26D5653EC157B4DE | |||
| 1764 | MailsBruTe - [c0d3d by @julia_pcret].exe | C:\Users\admin\AppData\Roaming\ssleay32.dll | executable | |
MD5:5023F4C4AAAA1B6E9D992D6BBDCD340B | SHA256:59B1BE1072DD4ACA5DDCF9B66D5DF8BEC327B4891925BA2339FE6AC6A1BF6D19 | |||
| 1764 | MailsBruTe - [c0d3d by @julia_pcret].exe | C:\Users\admin\AppData\Roaming\msvcr71.dll | executable | |
MD5:5D70D744B237A3A1F57C475600764C3E | SHA256:525B896A6DE9D1C400A61D09CBD1248376F64559DA5EF22380600EFEFDD06078 | |||
| 1764 | MailsBruTe - [c0d3d by @julia_pcret].exe | C:\Users\admin\AppData\Roaming\libeay32.dll | executable | |
MD5:177BDA0C92482DFA2C162A3750932B9C | SHA256:17A4B75EF43A4FDEEDAEF86C39BEAD6719144E3E368B55898B79ECB371012854 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1768 | MailsBruTe.exe | GET | 200 | 185.179.191.128:80 | http://felixw.pushfd.su/SyncModuleApi/syncApiModule.php?id=MailsBruTe&hwsession=F081A4F9057006AA | RU | text | 128 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1768 | MailsBruTe.exe | 185.179.191.128:80 | felixw.pushfd.su | — | RU | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
felixw.pushfd.su |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1768 | MailsBruTe.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |