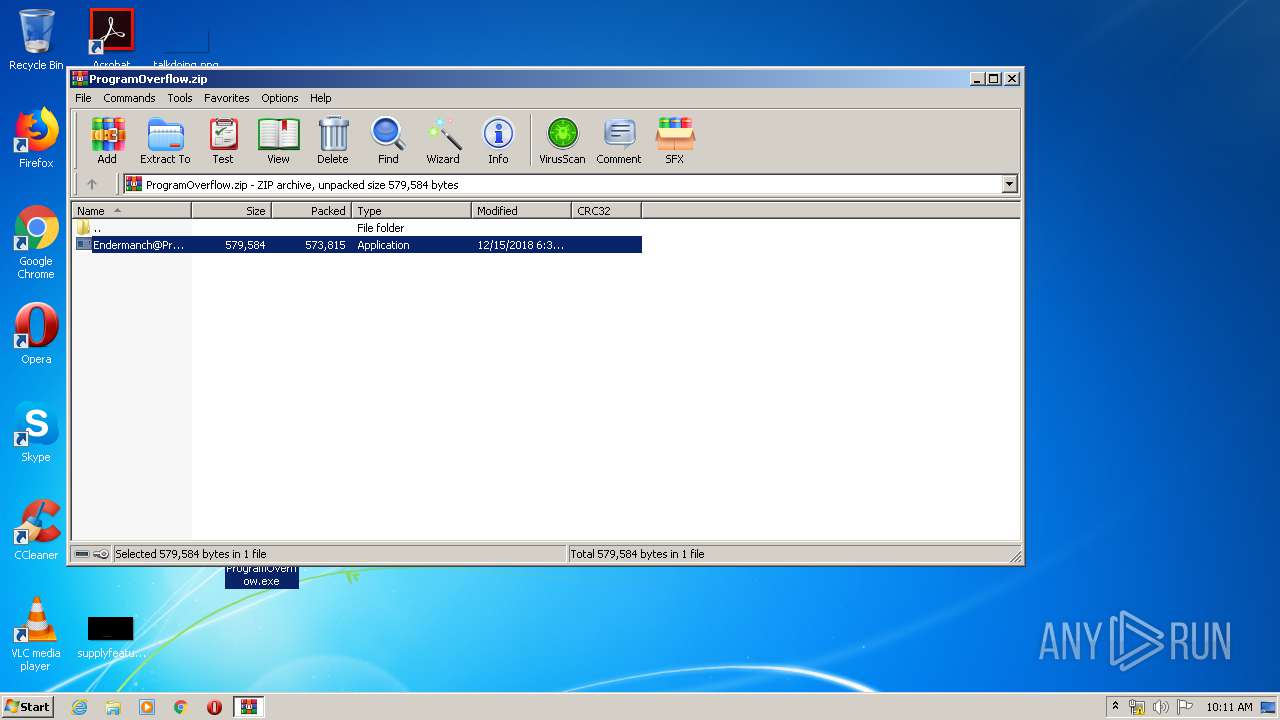
| URL: | https://github.com/Endermanch/MalwareDatabase/raw/master/enderware/ProgramOverflow.zip |
| Full analysis: | https://app.any.run/tasks/8e36c9f2-6a37-4ffe-8042-8bcdc5a4a266 |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2020, 09:09:35 |
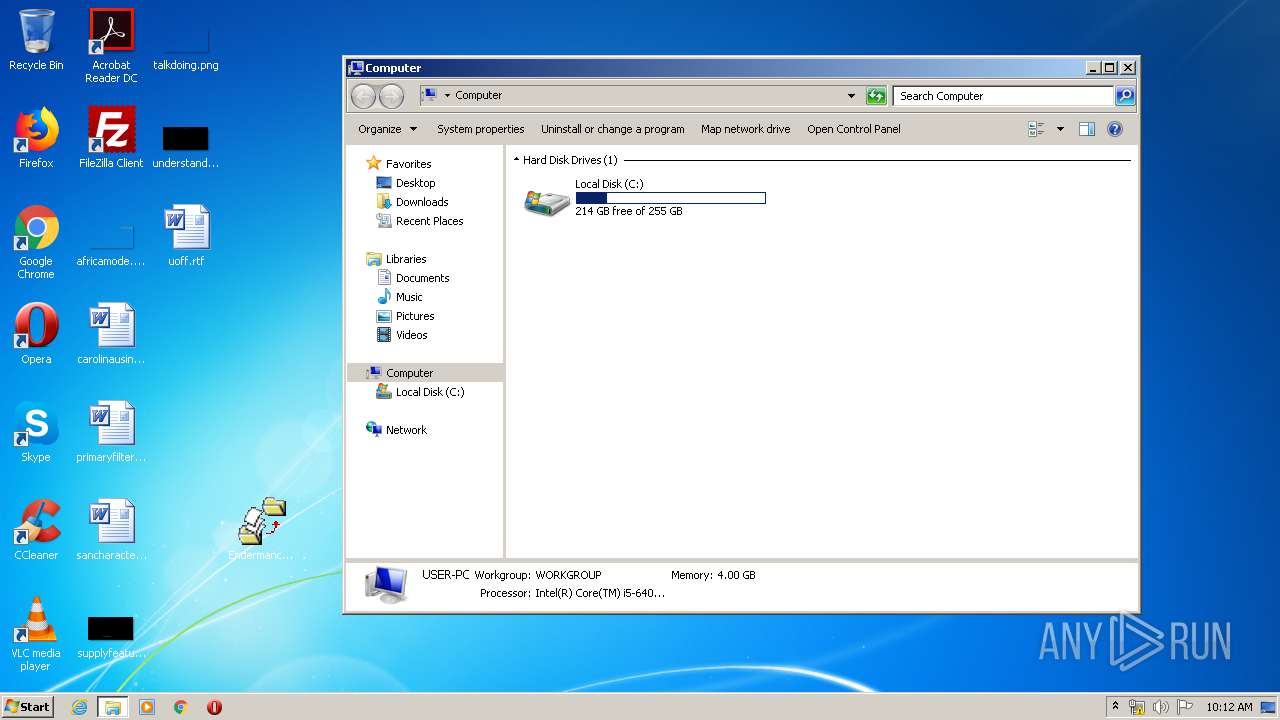
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7C4EC68378EEB059D3BA1A974BBF70E2 |
| SHA1: | 232E945EE5ABA6093B69BCB0DB7C66C800410FF6 |
| SHA256: | 518FE216BD96BE35DD9EDBAB148E03E4C8201A4EFCFB2C4B25ED1C5BC3D73538 |
| SSDEEP: | 3:N8tEdegLaKoEJ3PqLKRMnXUDQPc:2ufLtf34XSQPc |
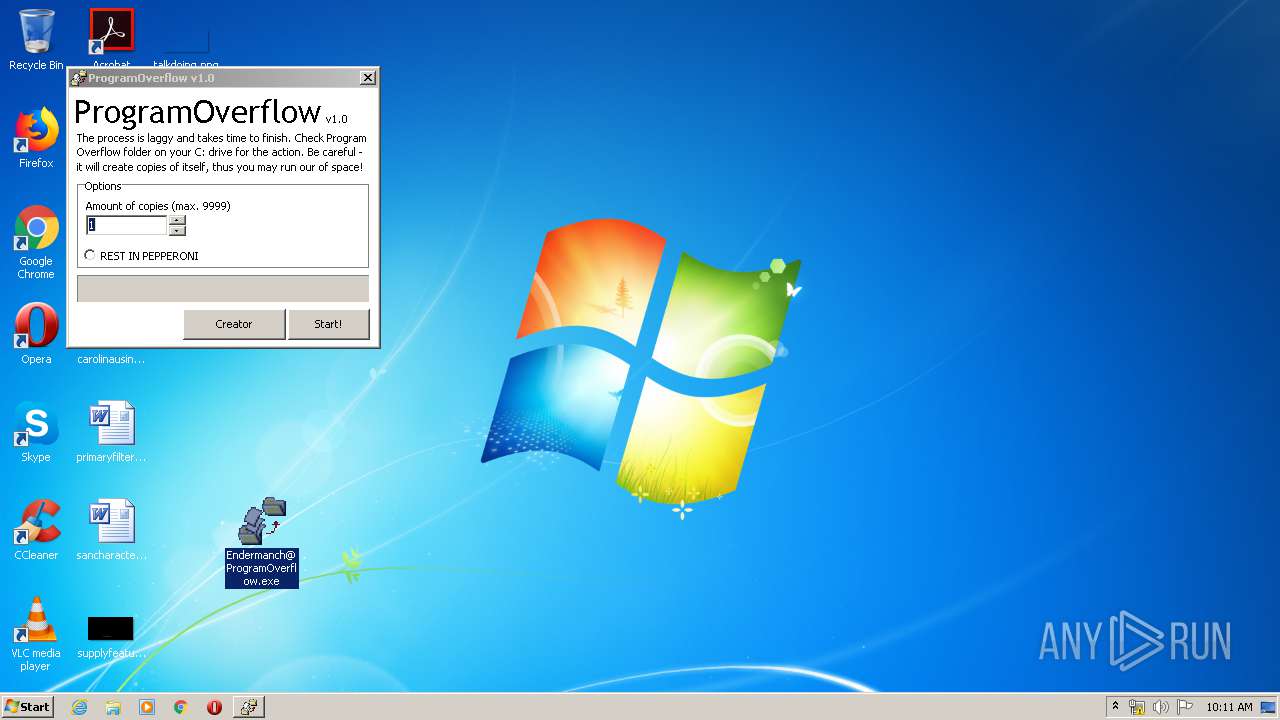
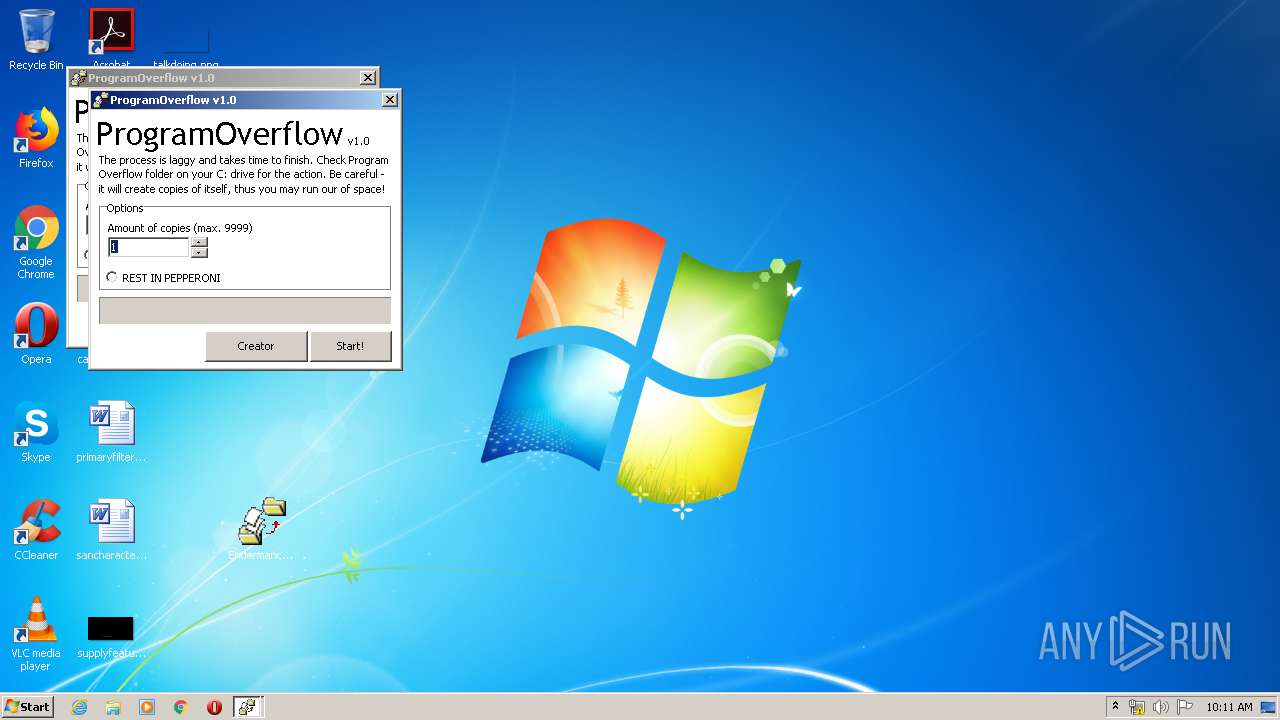
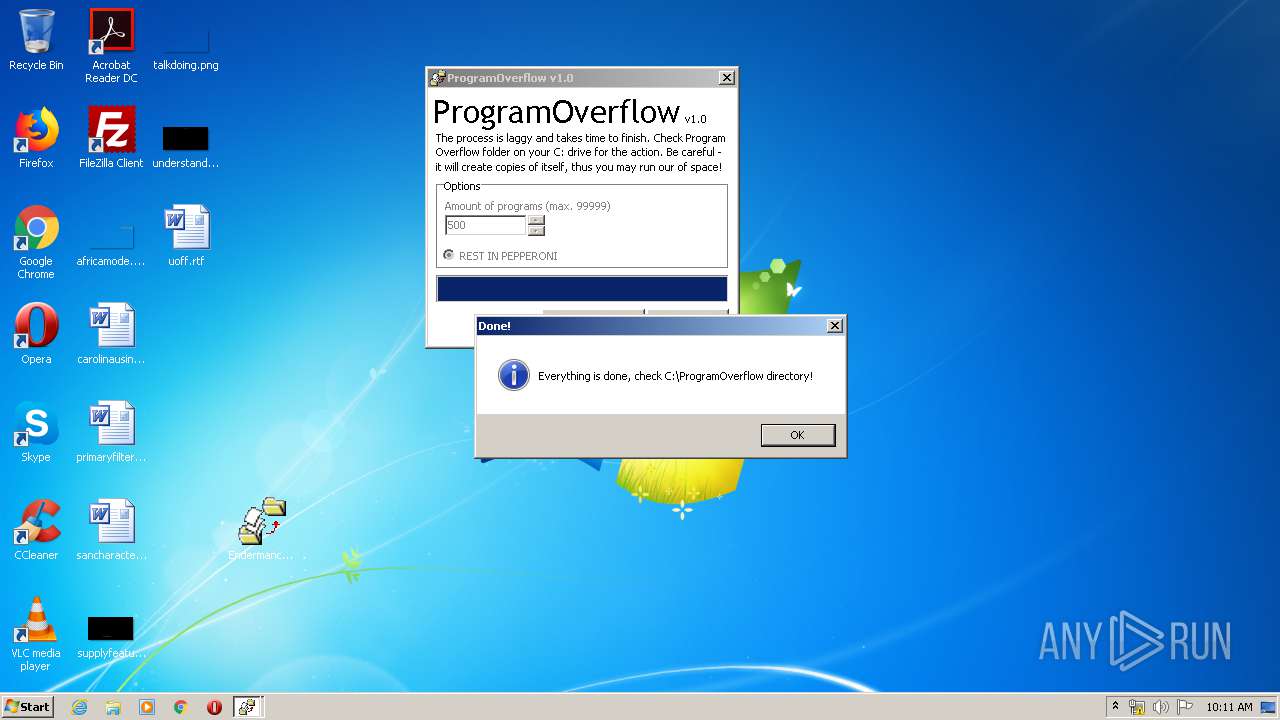
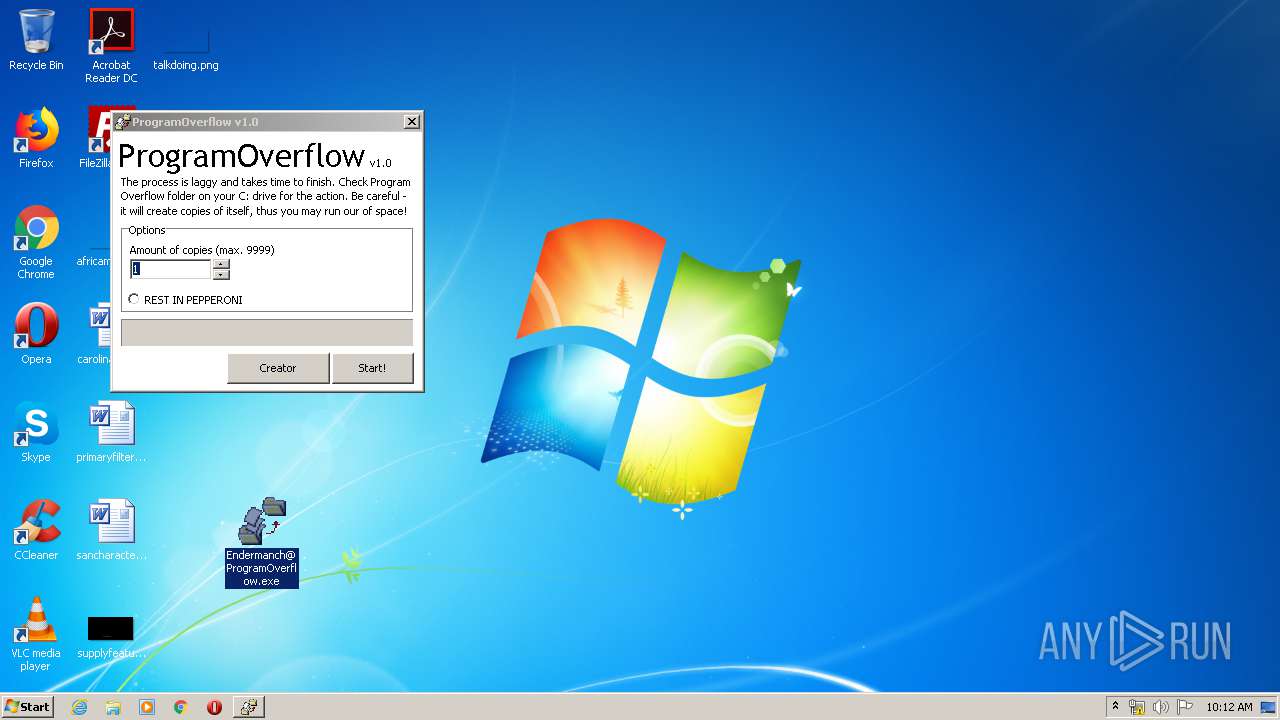
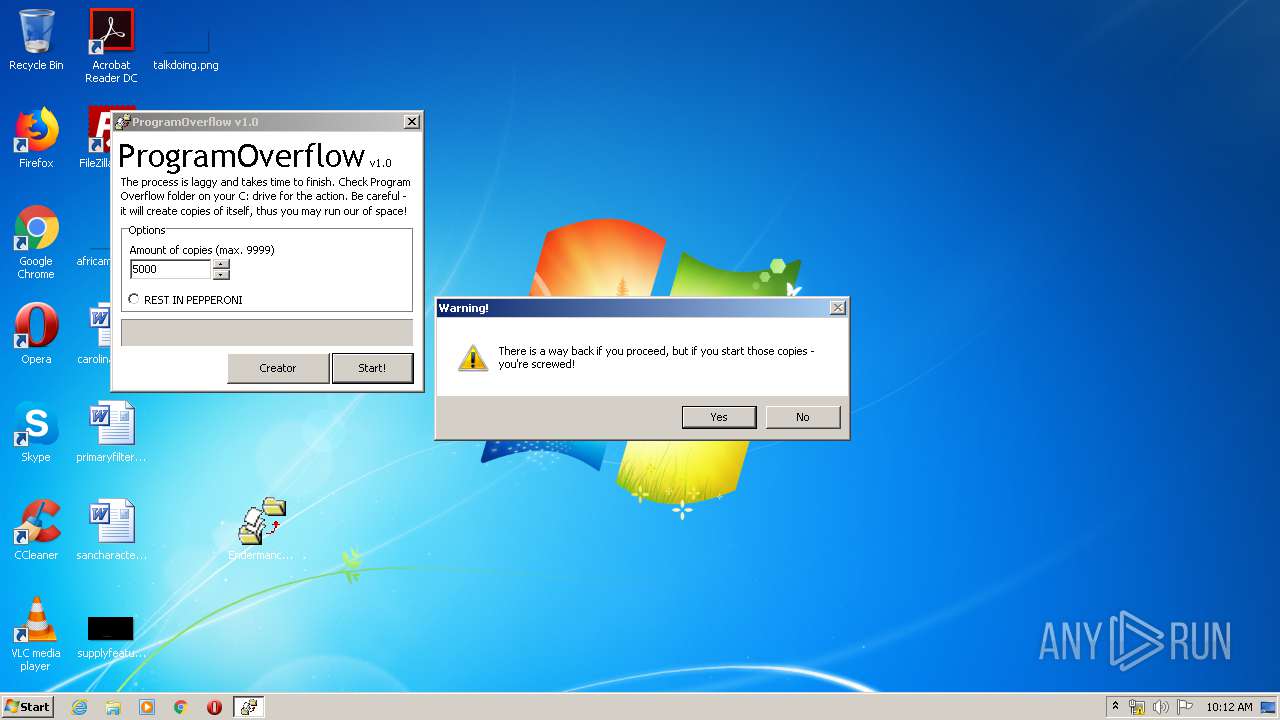
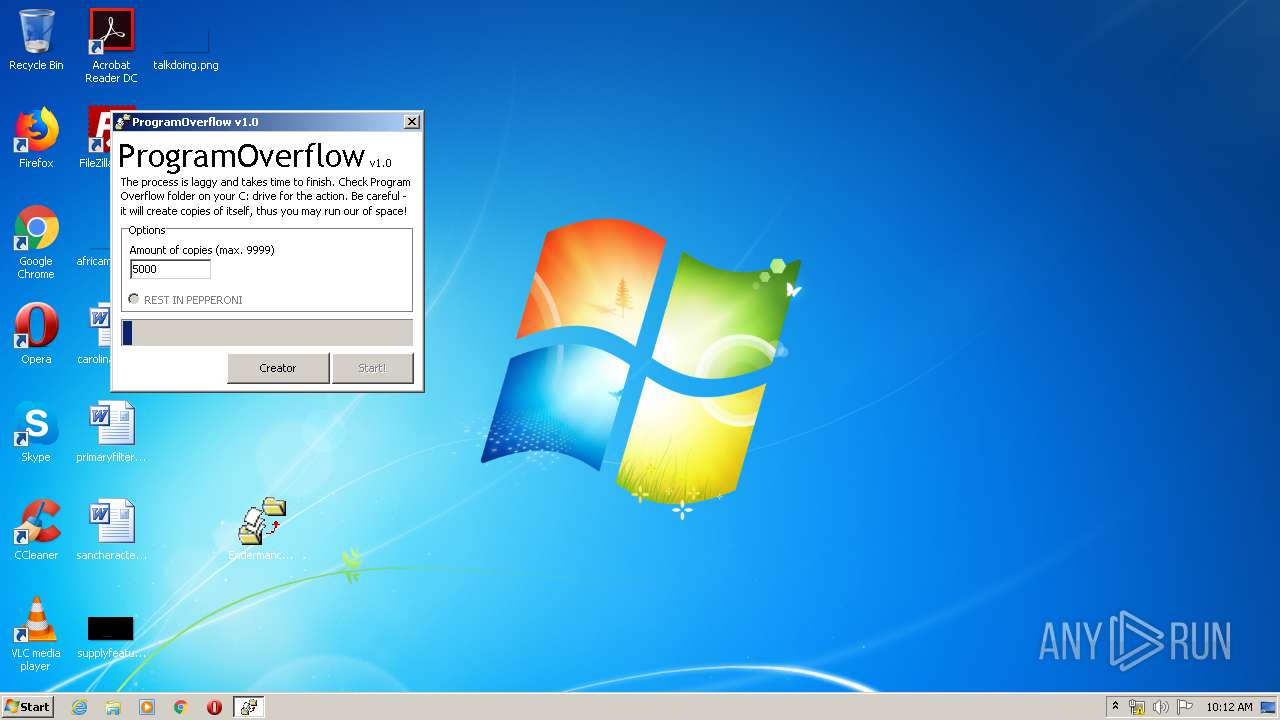
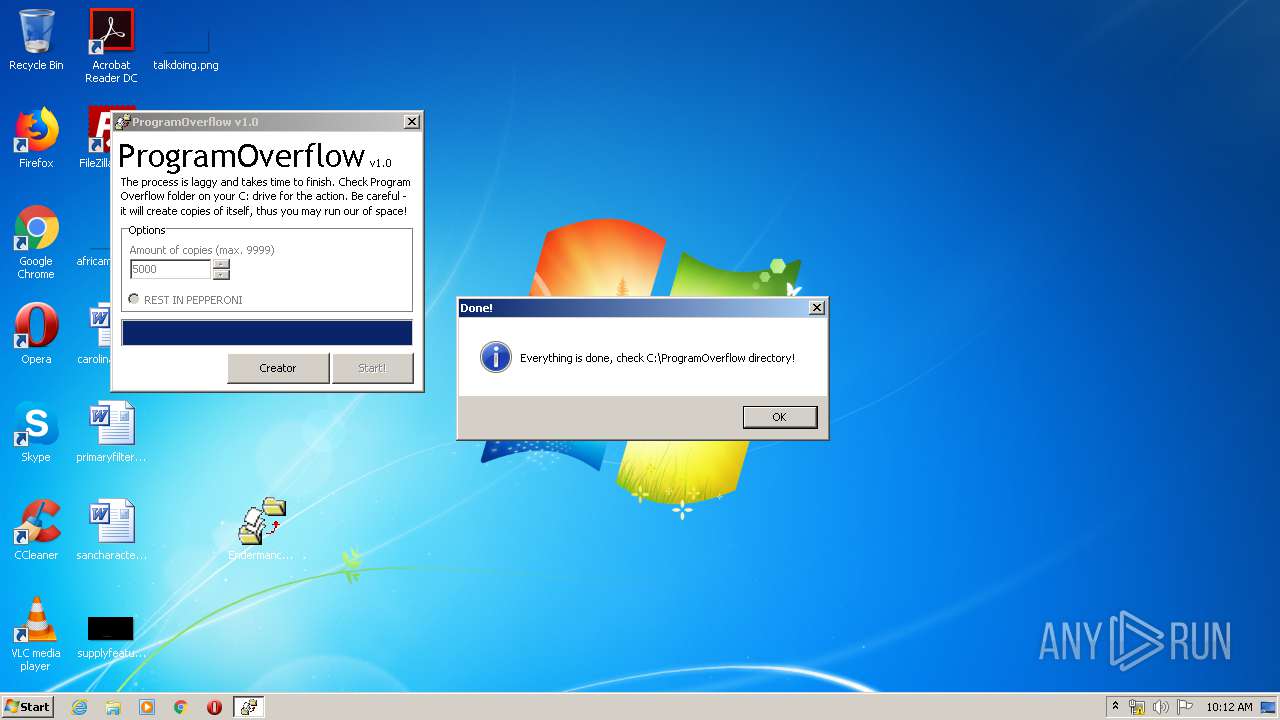
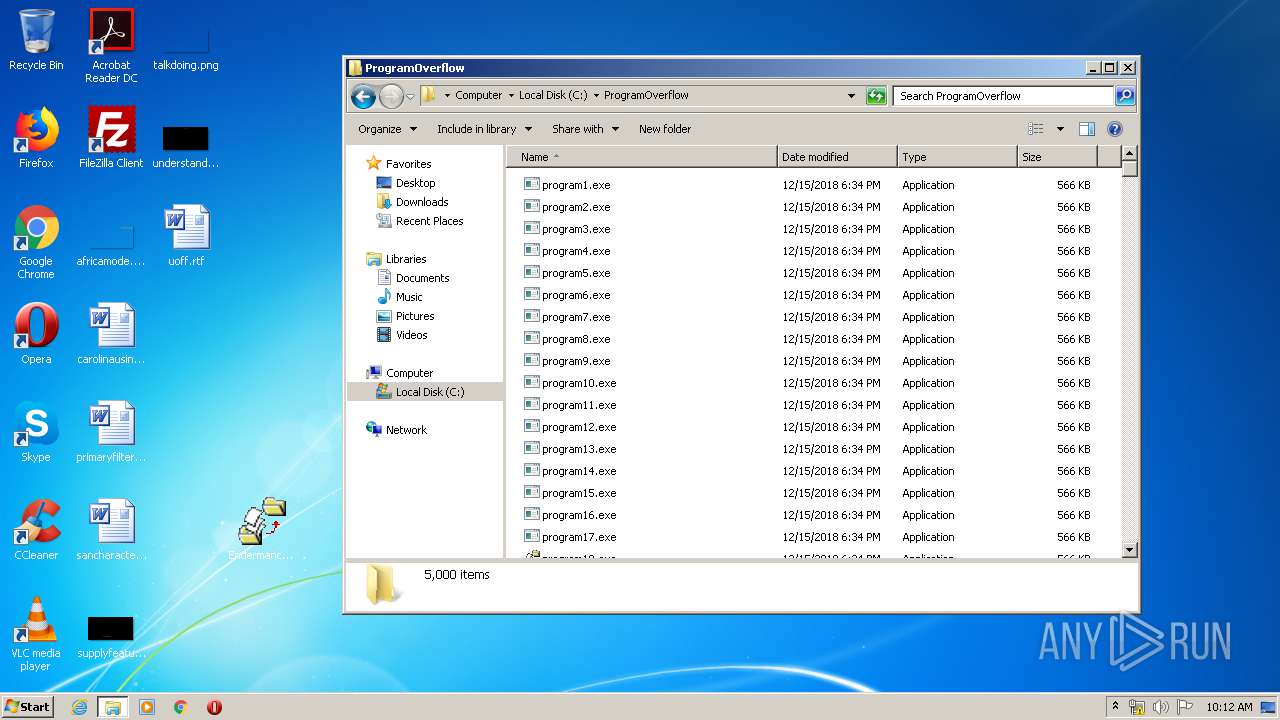
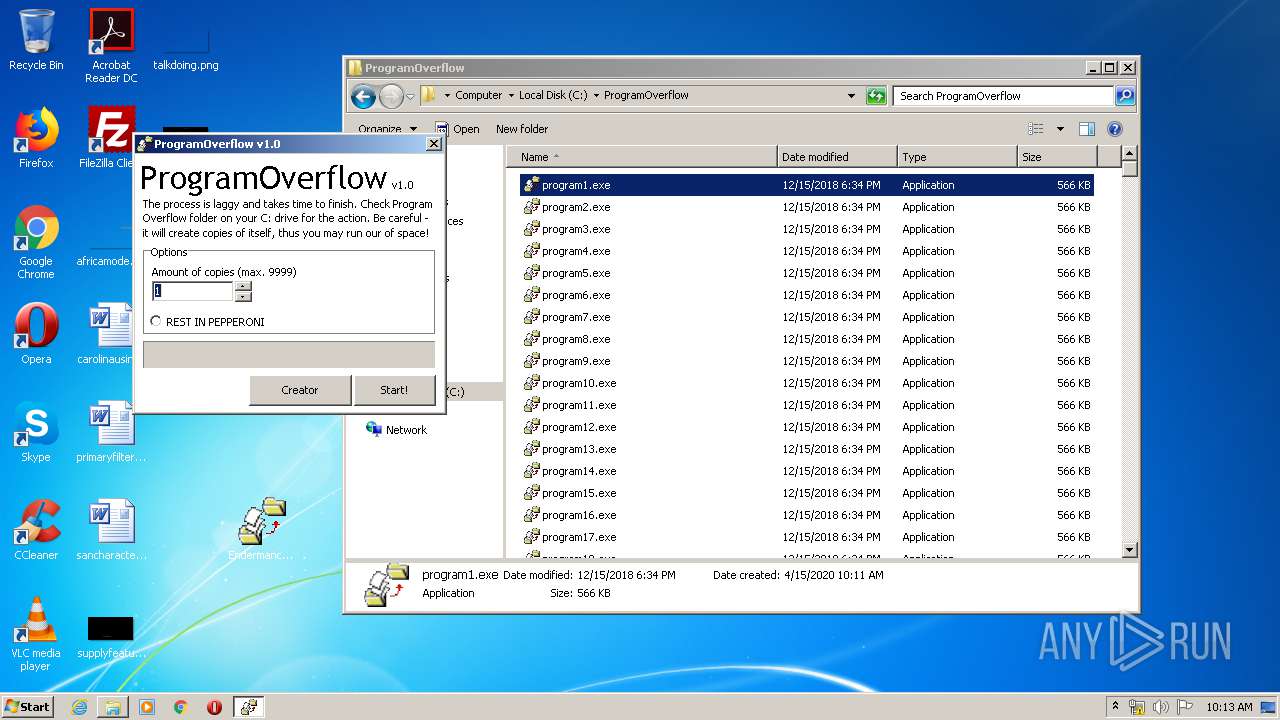
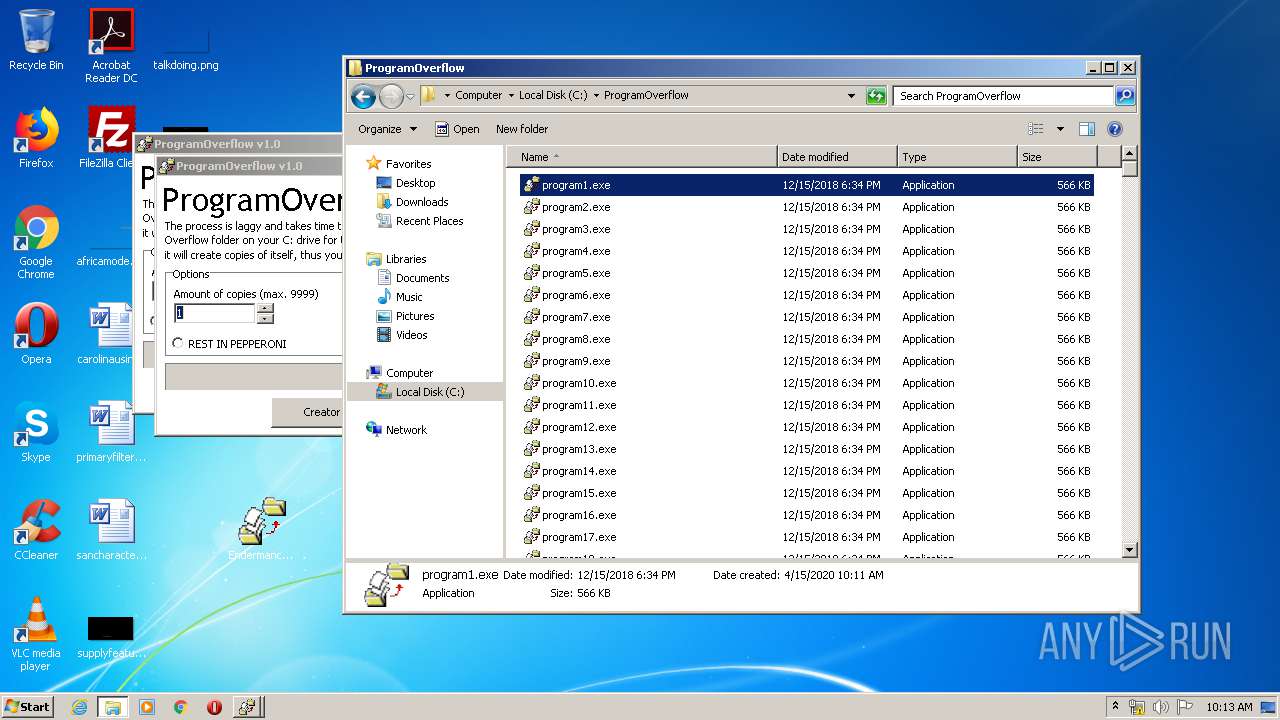
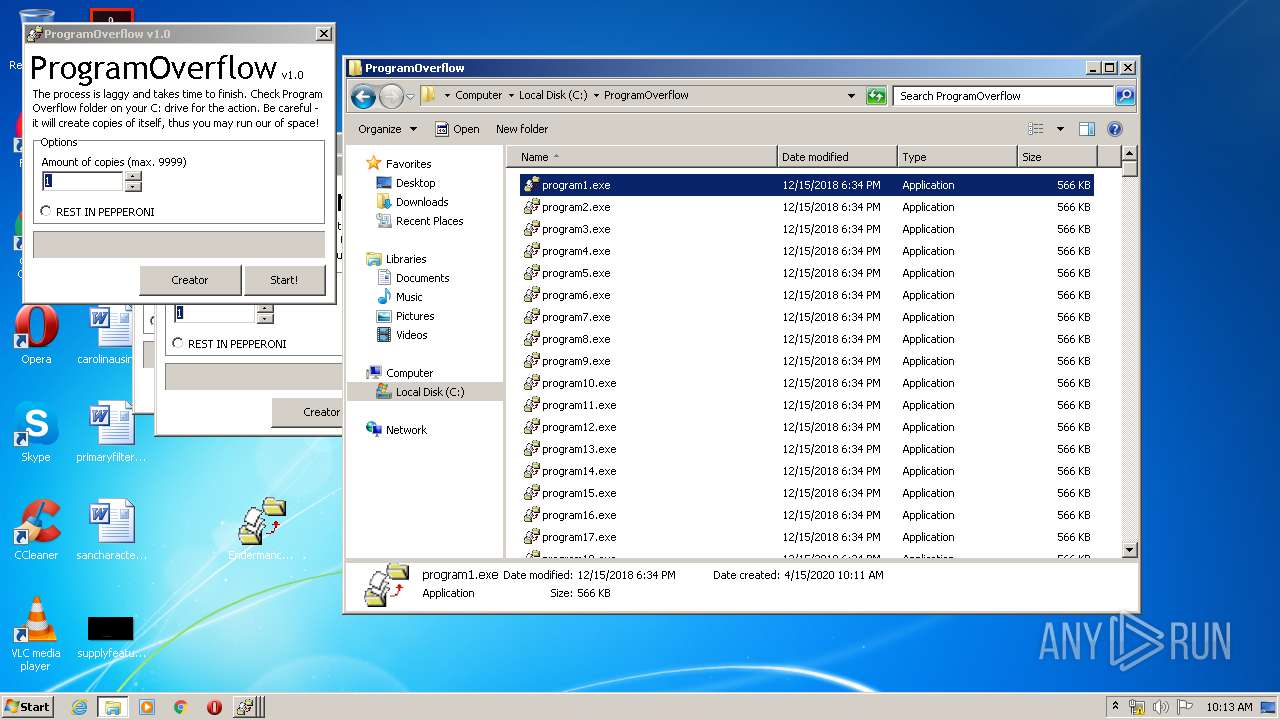
MALICIOUS
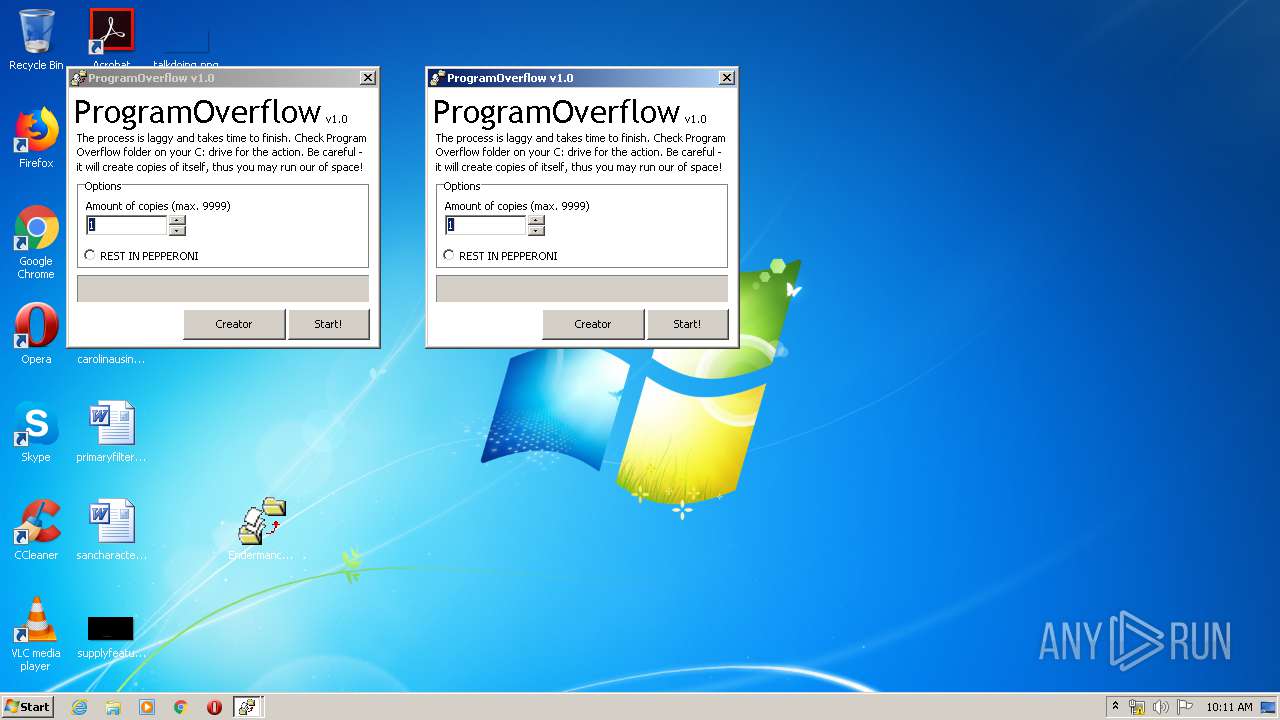
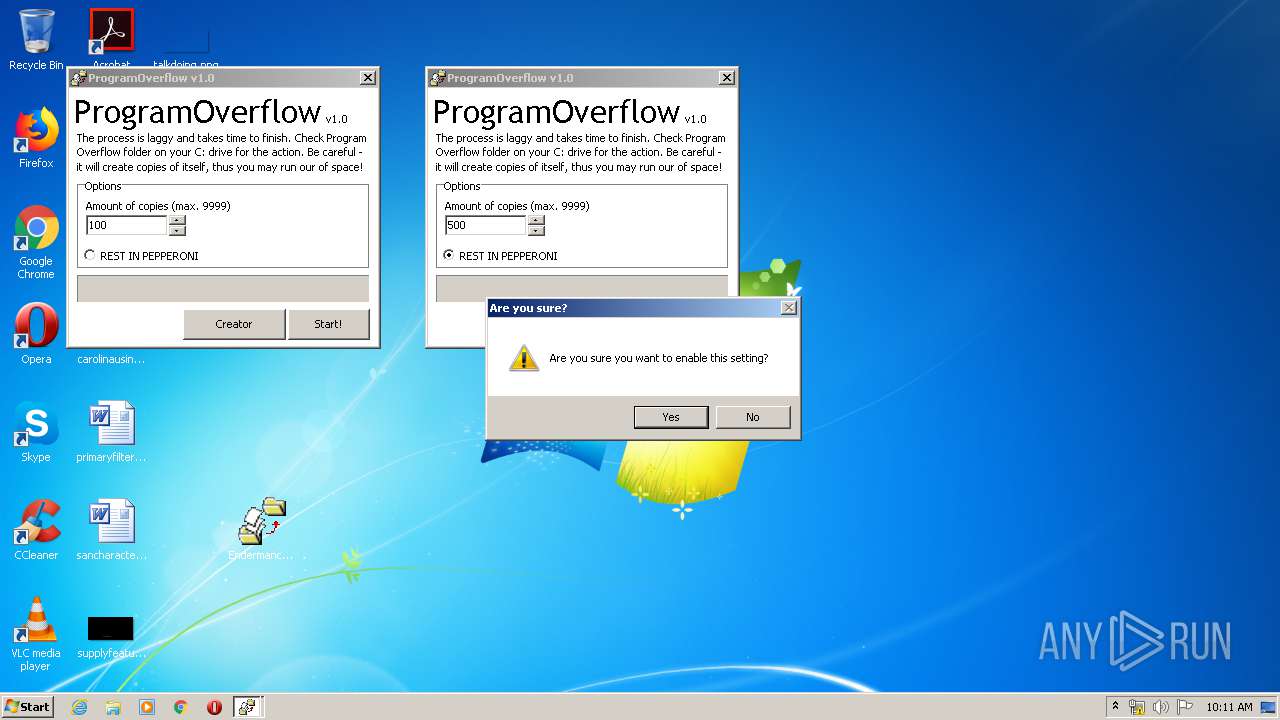
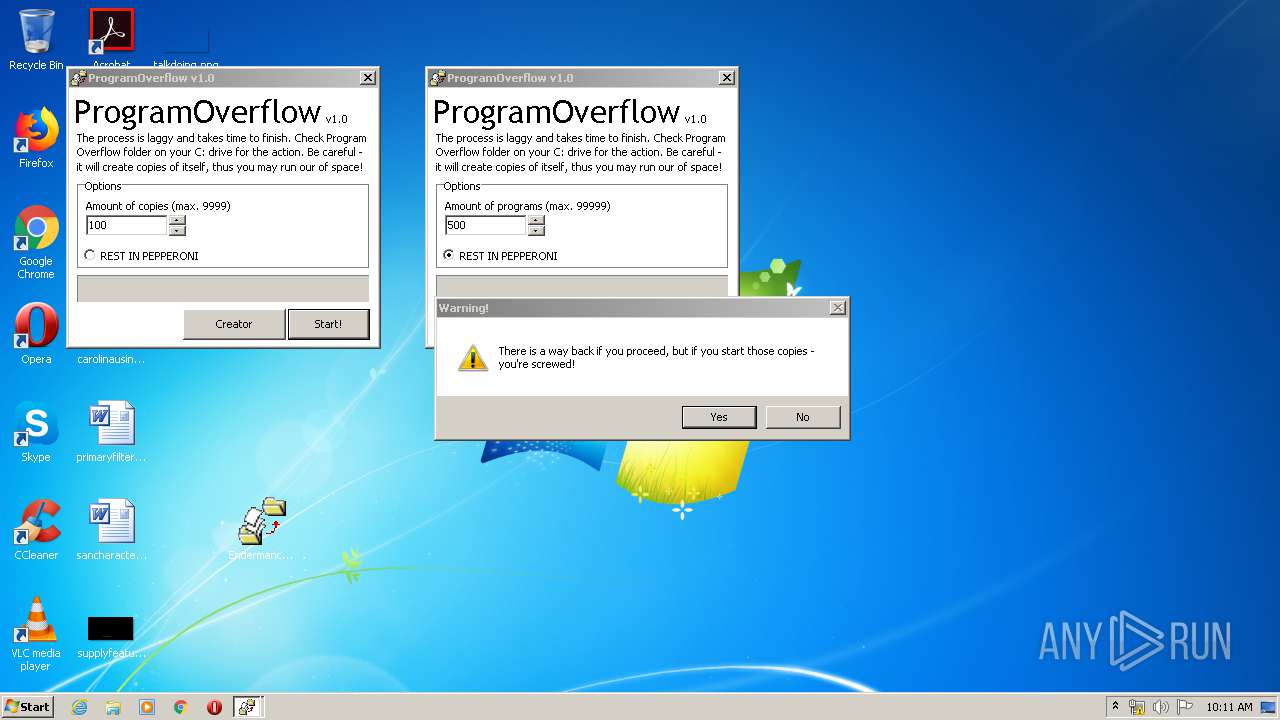
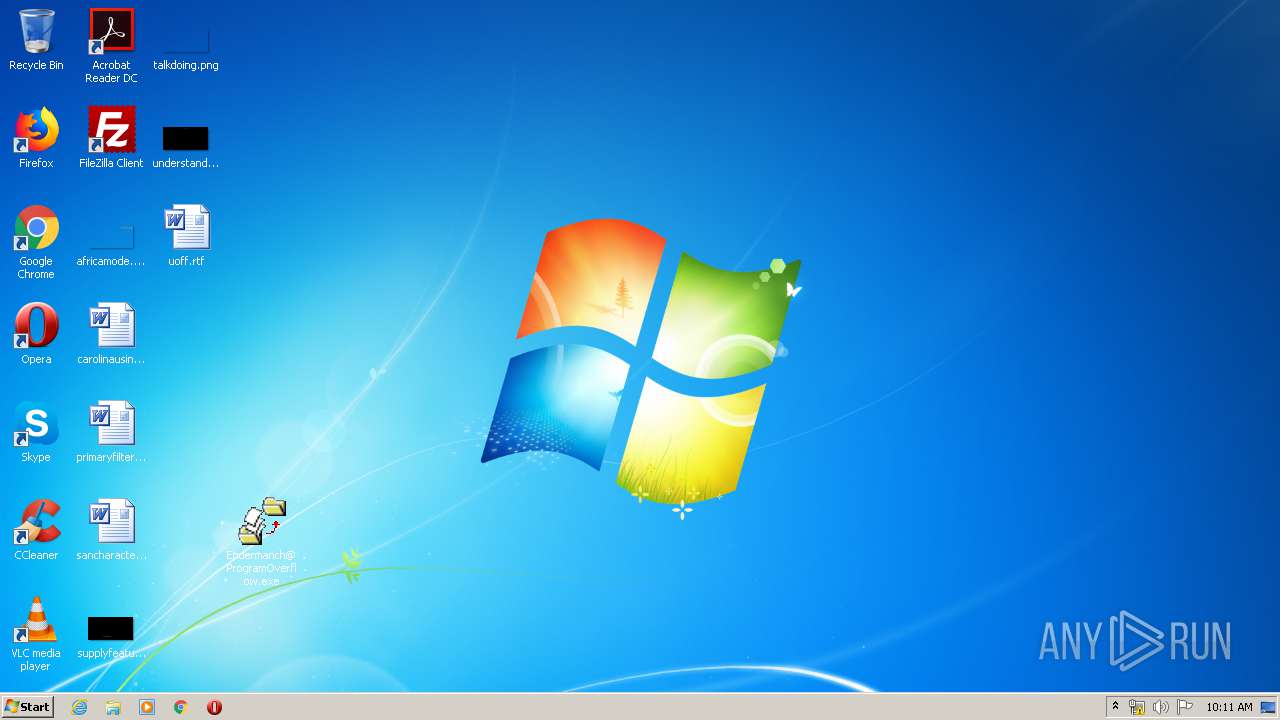
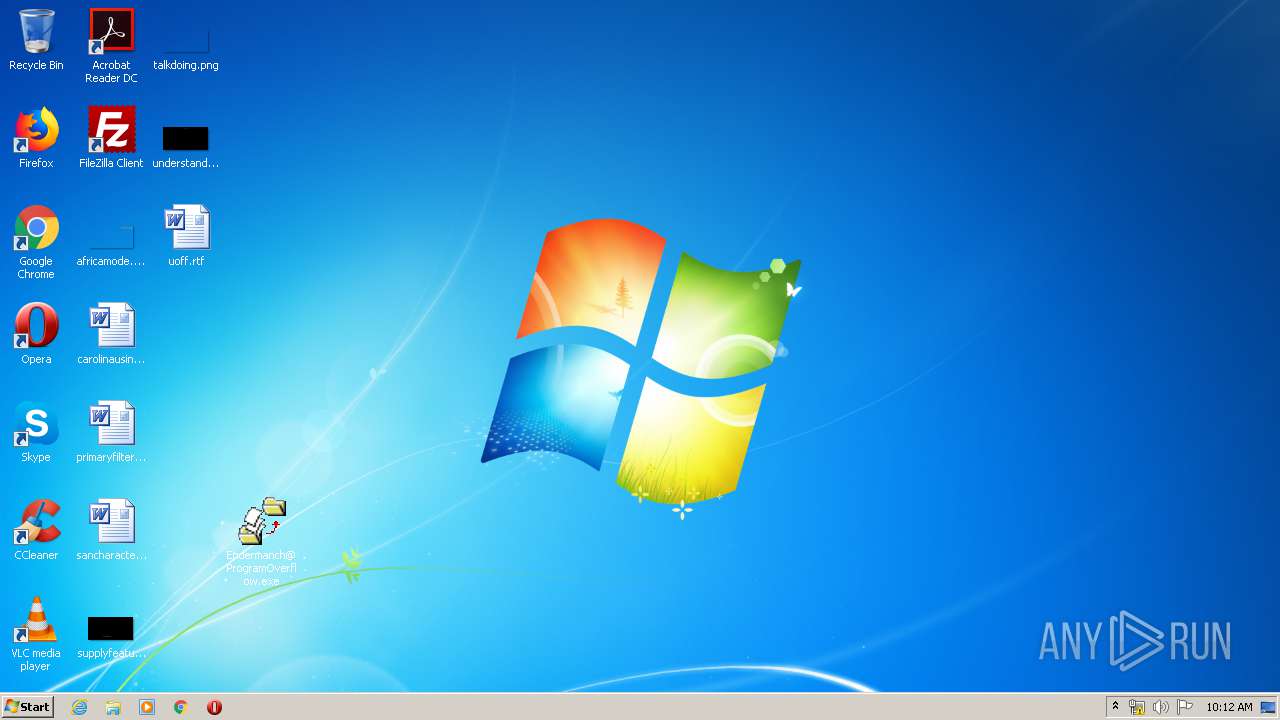
Application was dropped or rewritten from another process
- Endermanch@ProgramOverflow.exe (PID: 4088)
- Endermanch@ProgramOverflow.exe (PID: 620)
- Endermanch@ProgramOverflow.exe (PID: 2732)
SUSPICIOUS
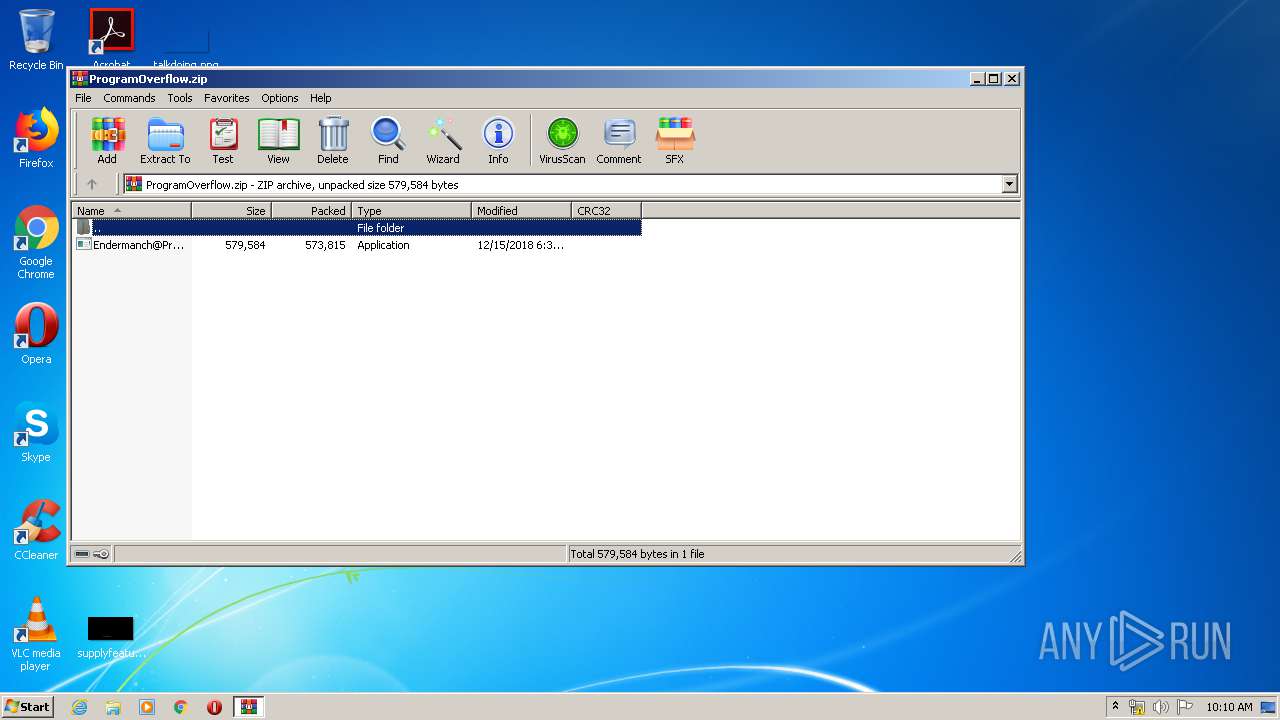
Executable content was dropped or overwritten
- WinRAR.exe (PID: 540)
- Endermanch@ProgramOverflow.exe (PID: 620)
- Endermanch@ProgramOverflow.exe (PID: 2732)
- Endermanch@ProgramOverflow.exe (PID: 4088)
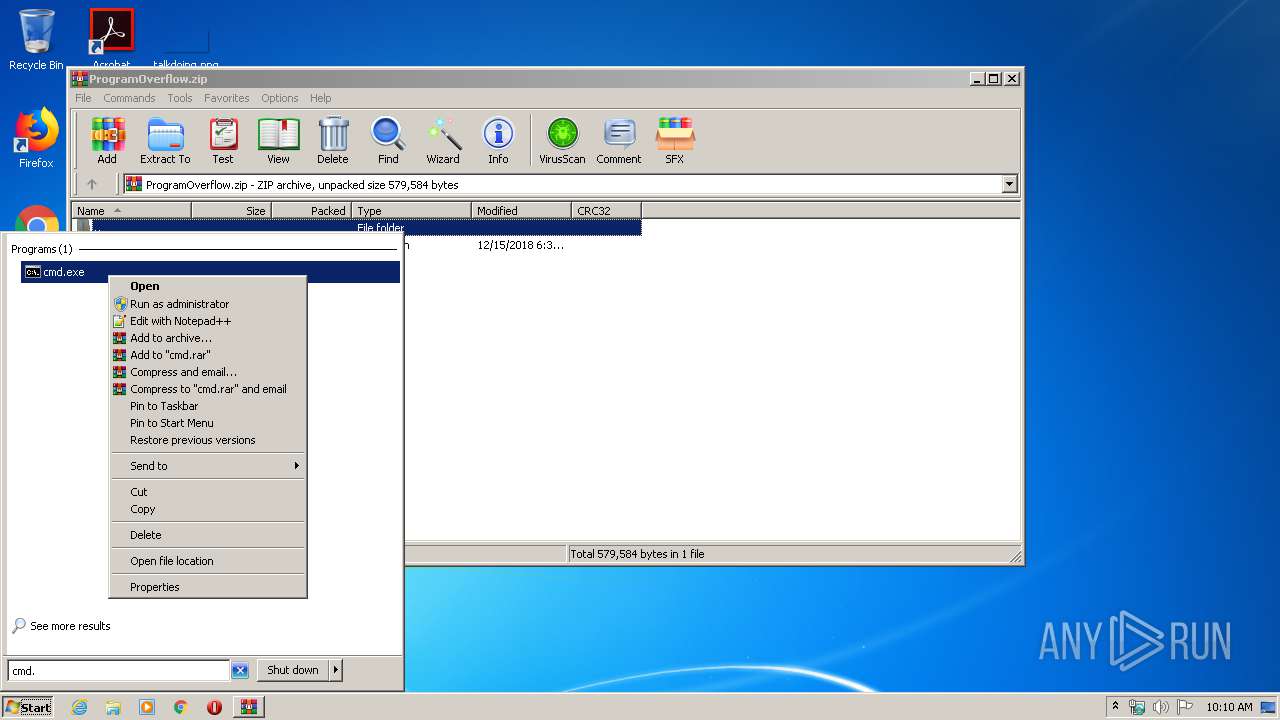
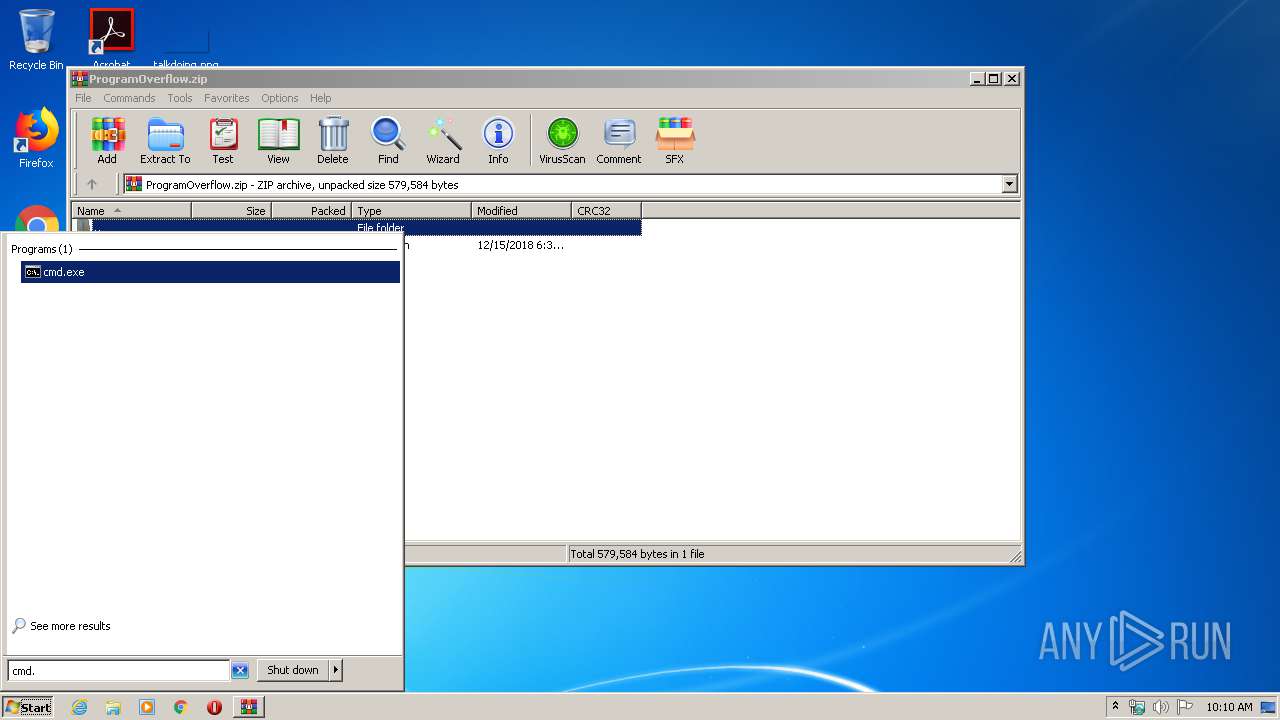
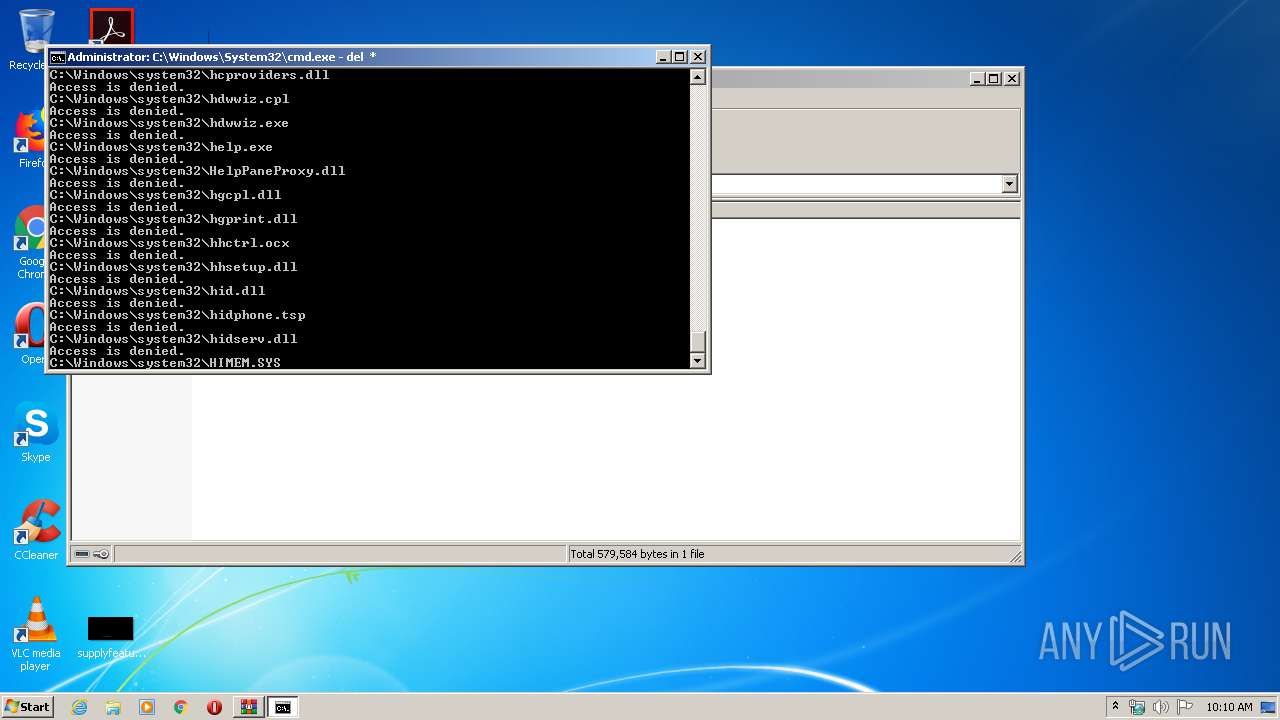
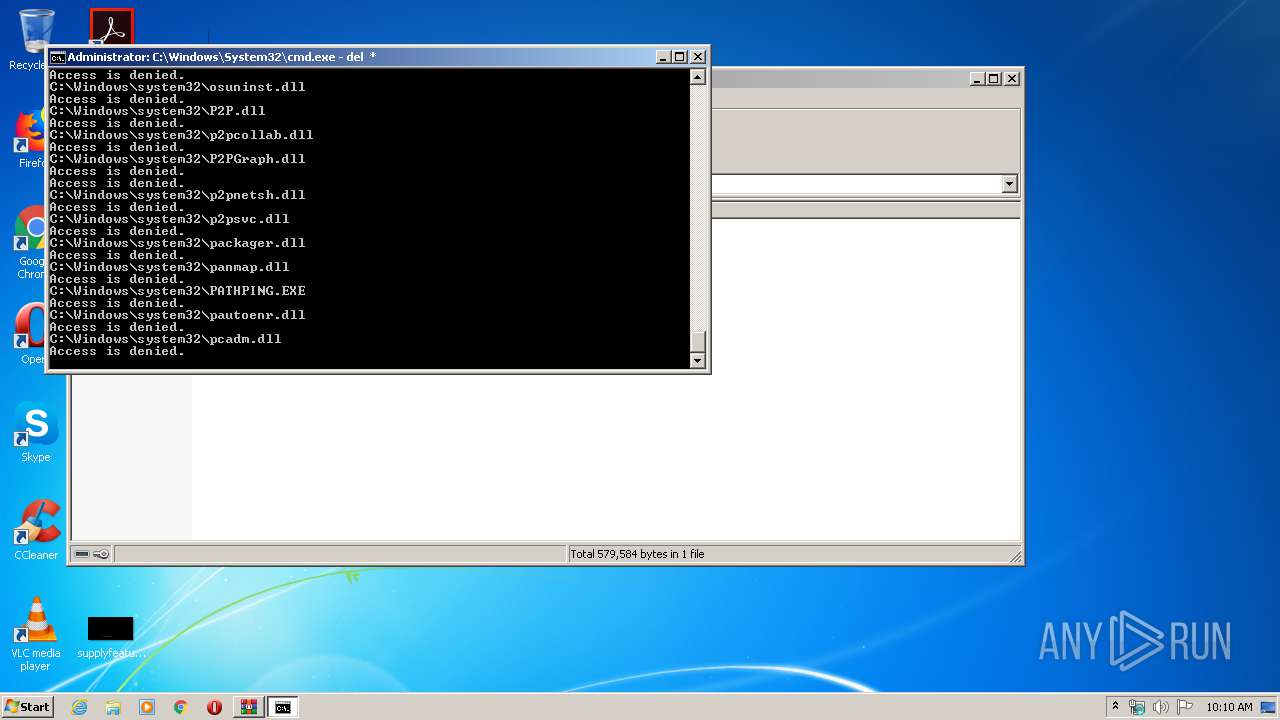
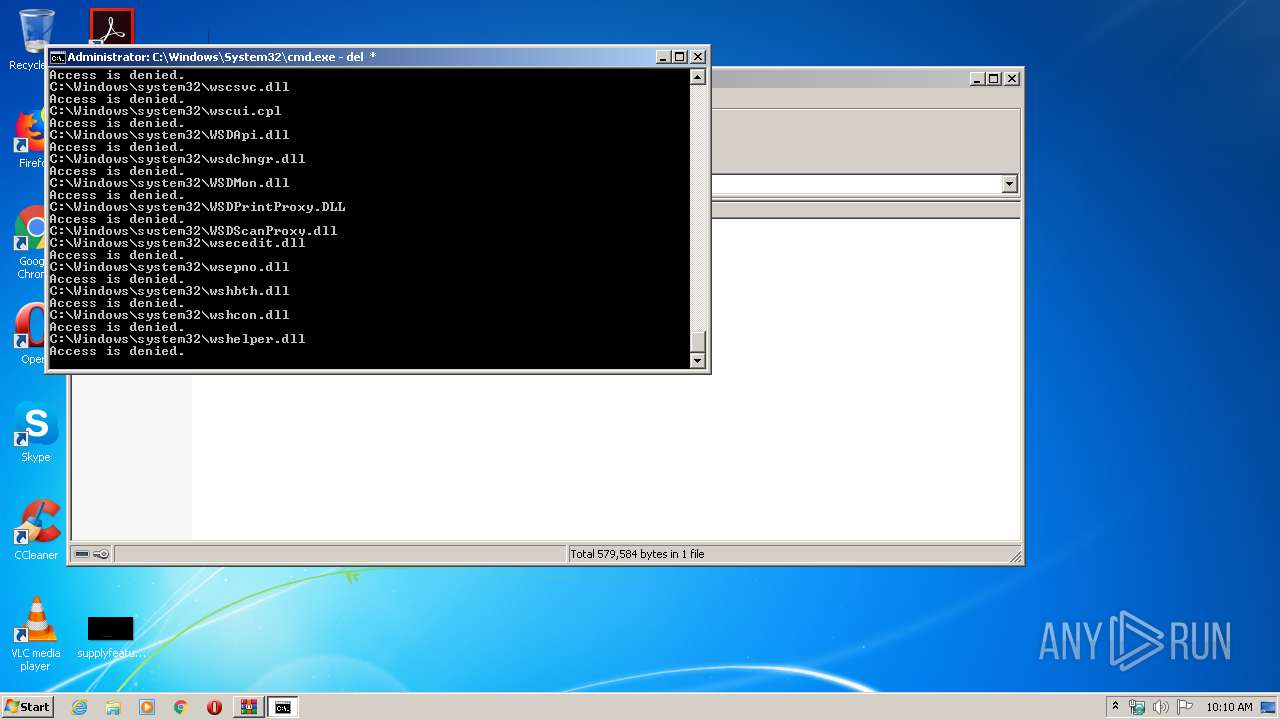
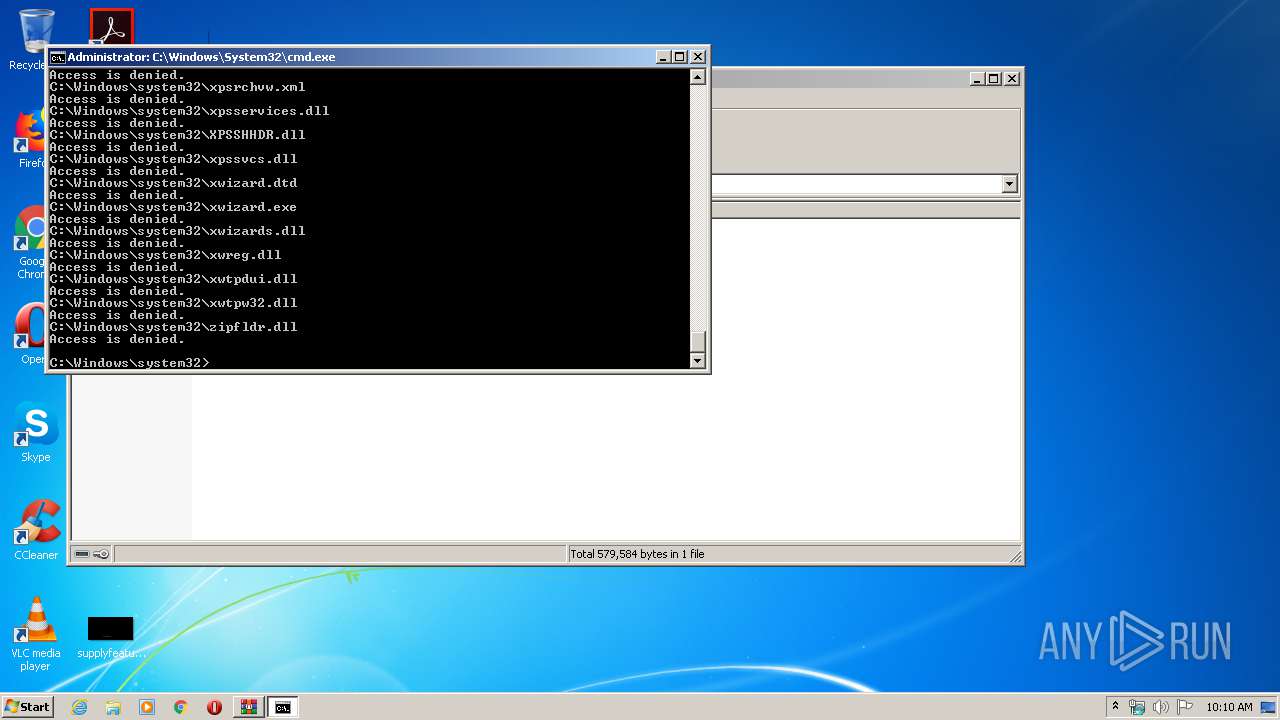
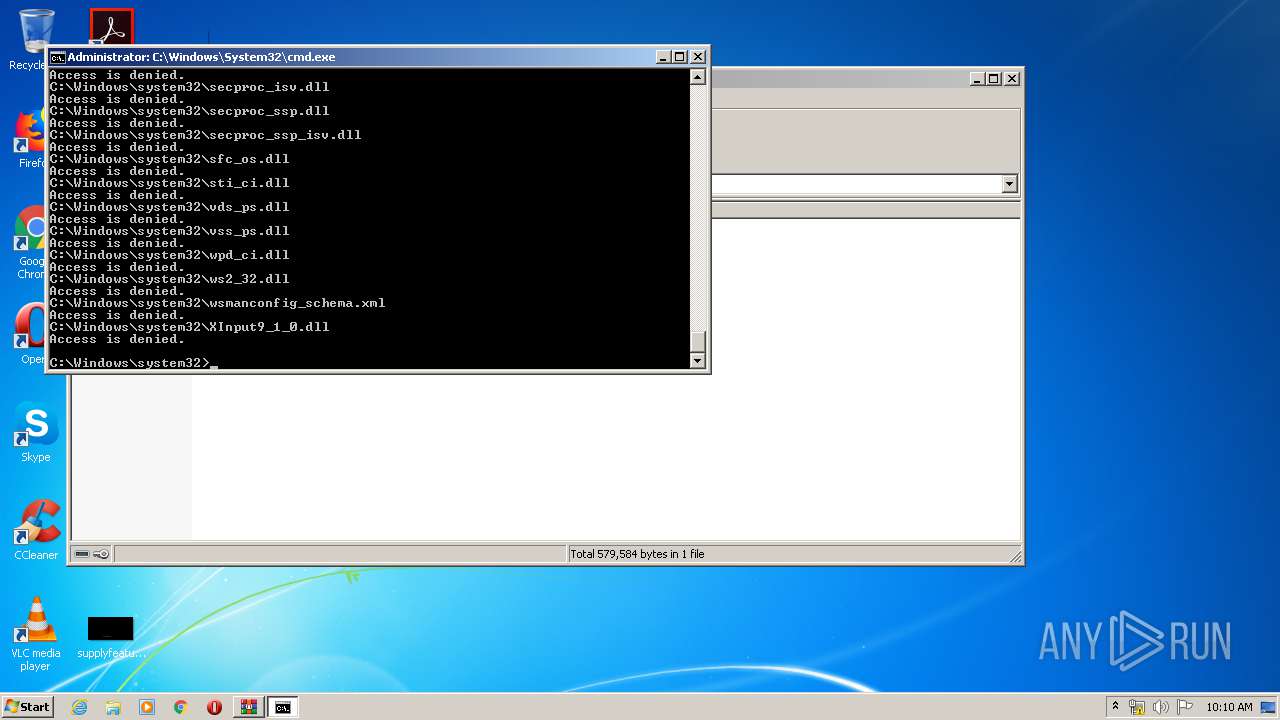
Removes files from Windows directory
- cmd.exe (PID: 2928)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3260)
Reads Internet Cache Settings
- iexplore.exe (PID: 3152)
- iexplore.exe (PID: 3260)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3260)
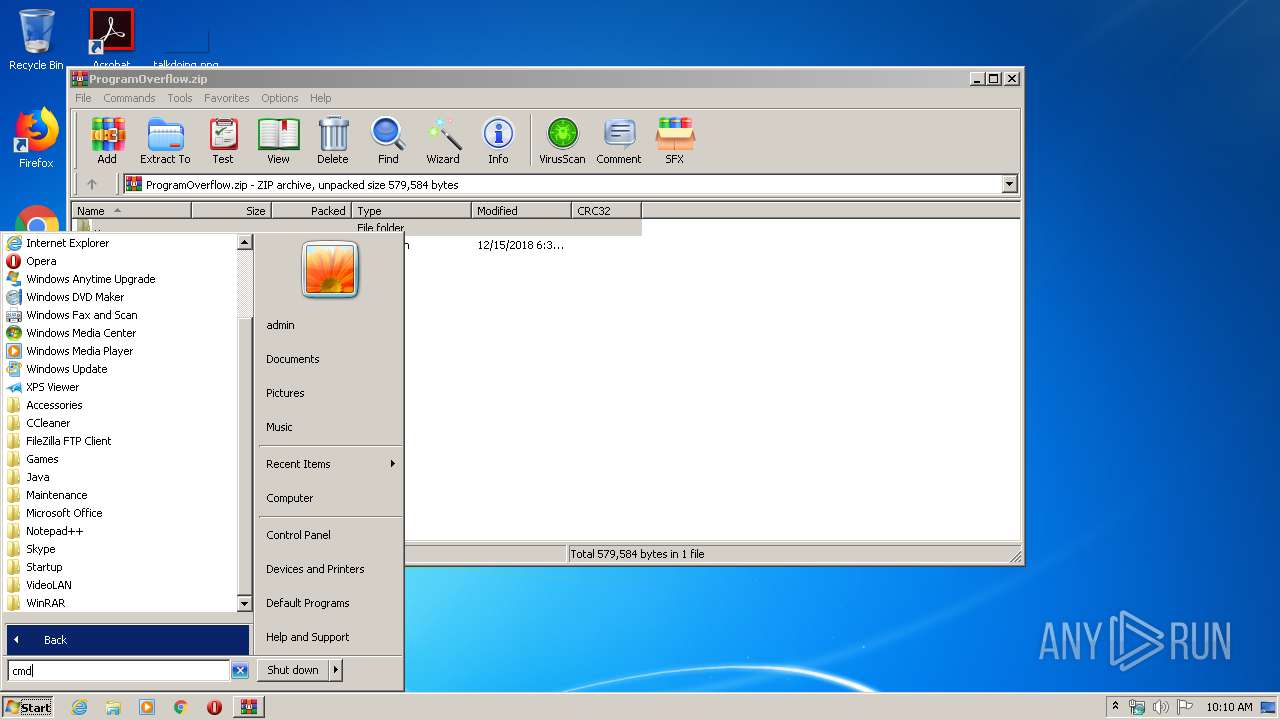
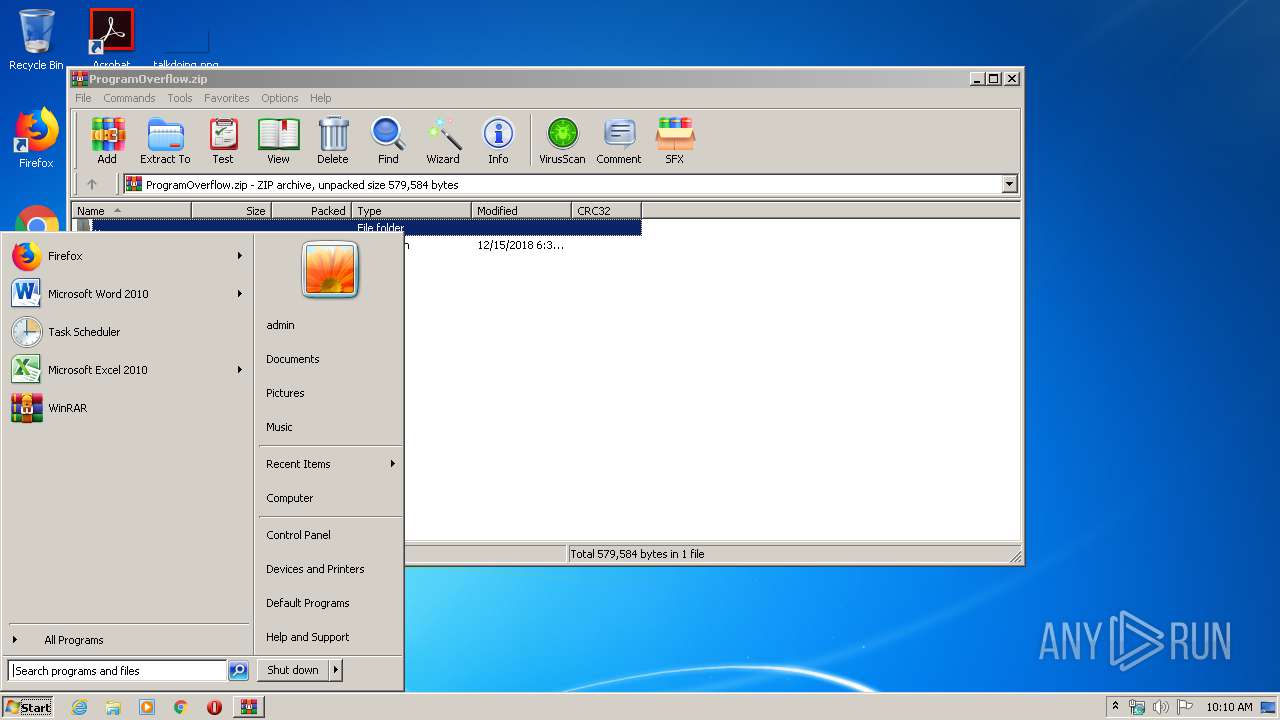
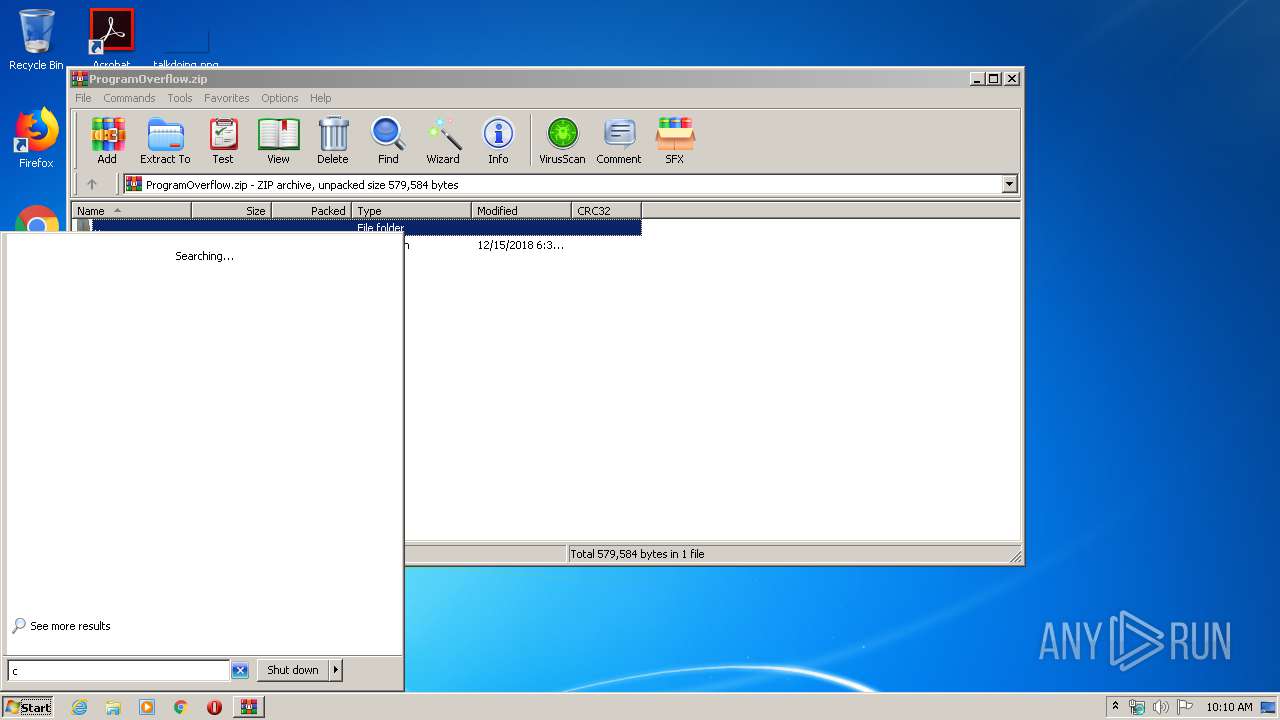
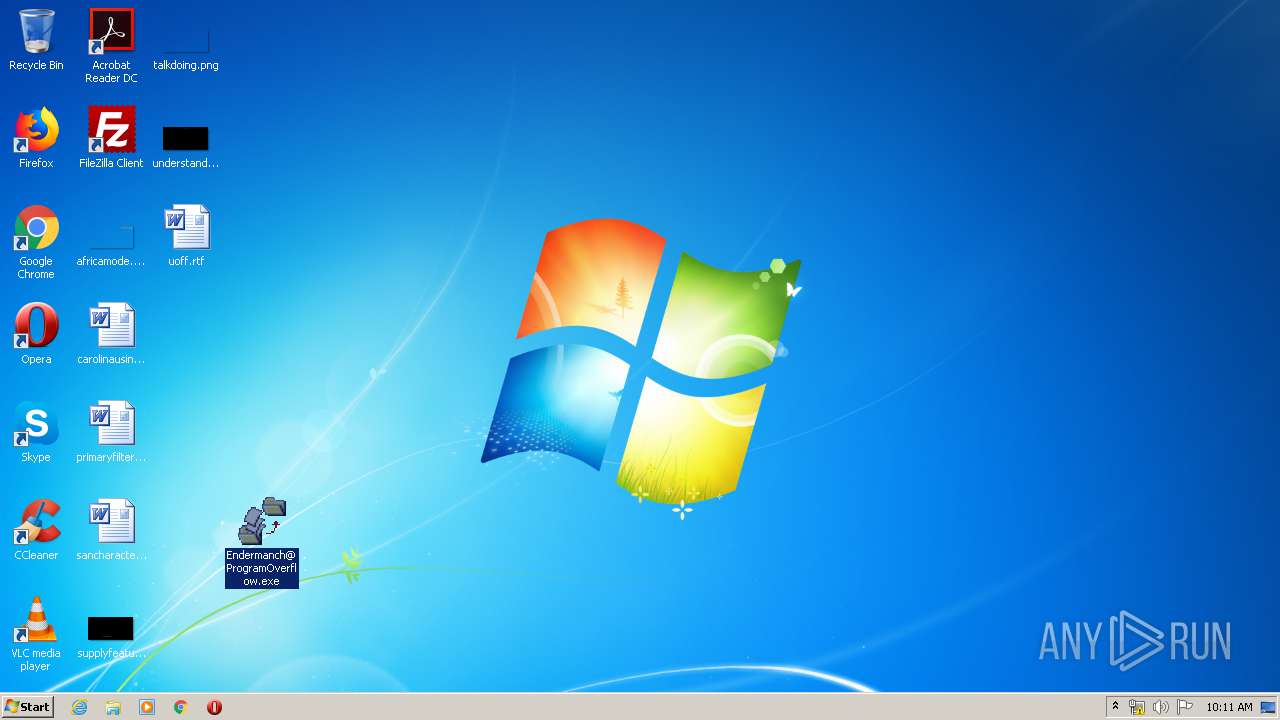
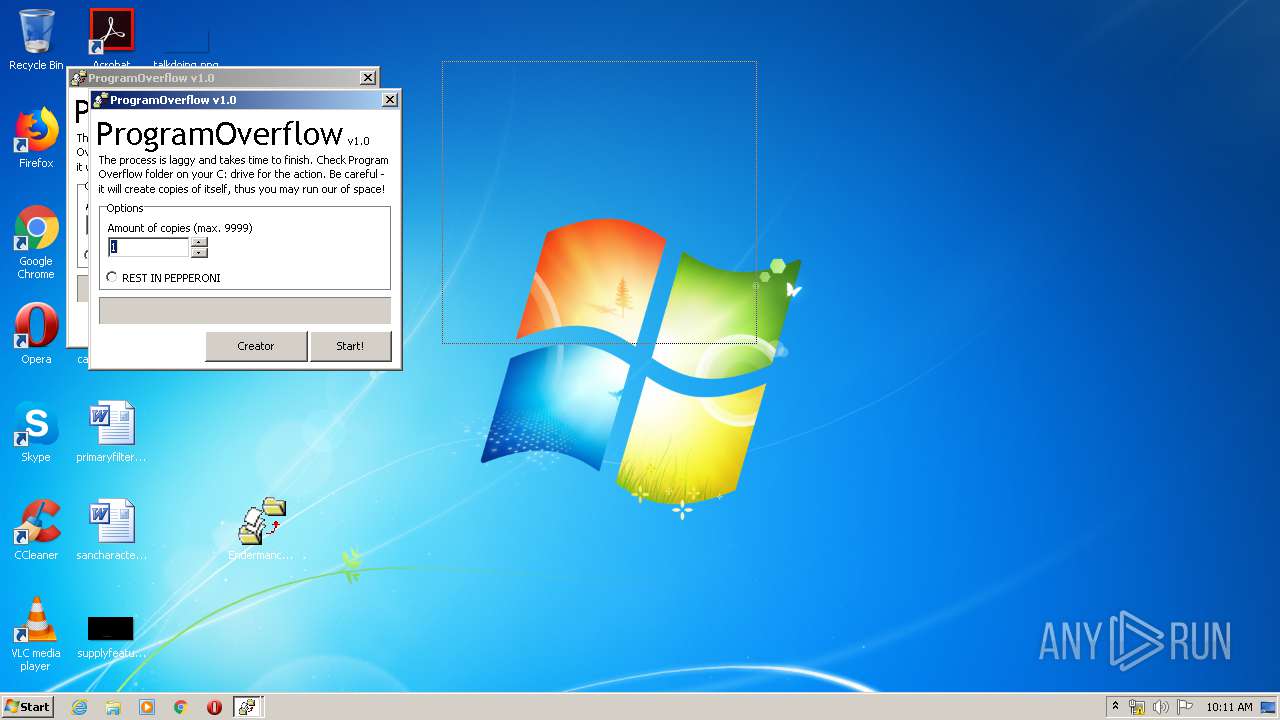
Manual execution by user
- Endermanch@ProgramOverflow.exe (PID: 4088)
- Endermanch@ProgramOverflow.exe (PID: 620)
- Endermanch@ProgramOverflow.exe (PID: 2732)
- cmd.exe (PID: 2928)
Application launched itself
- iexplore.exe (PID: 3260)
Reads settings of System Certificates
- iexplore.exe (PID: 3152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
50
Monitored processes
7
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
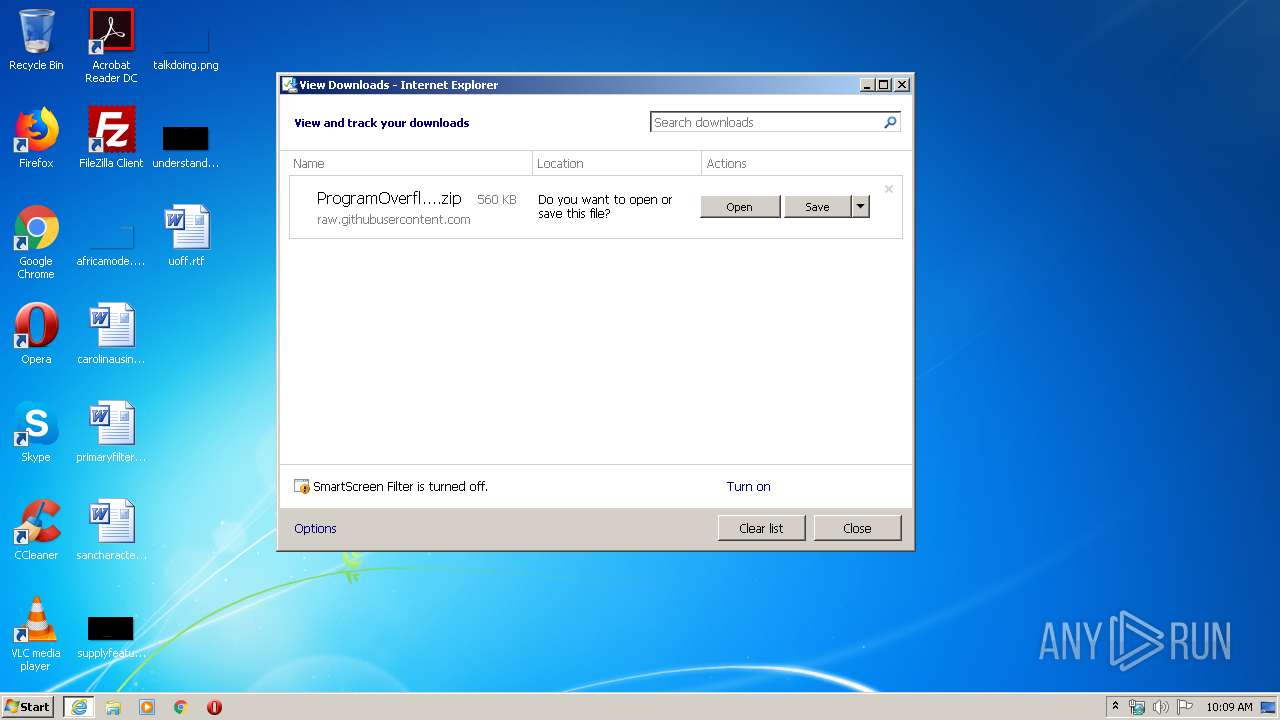
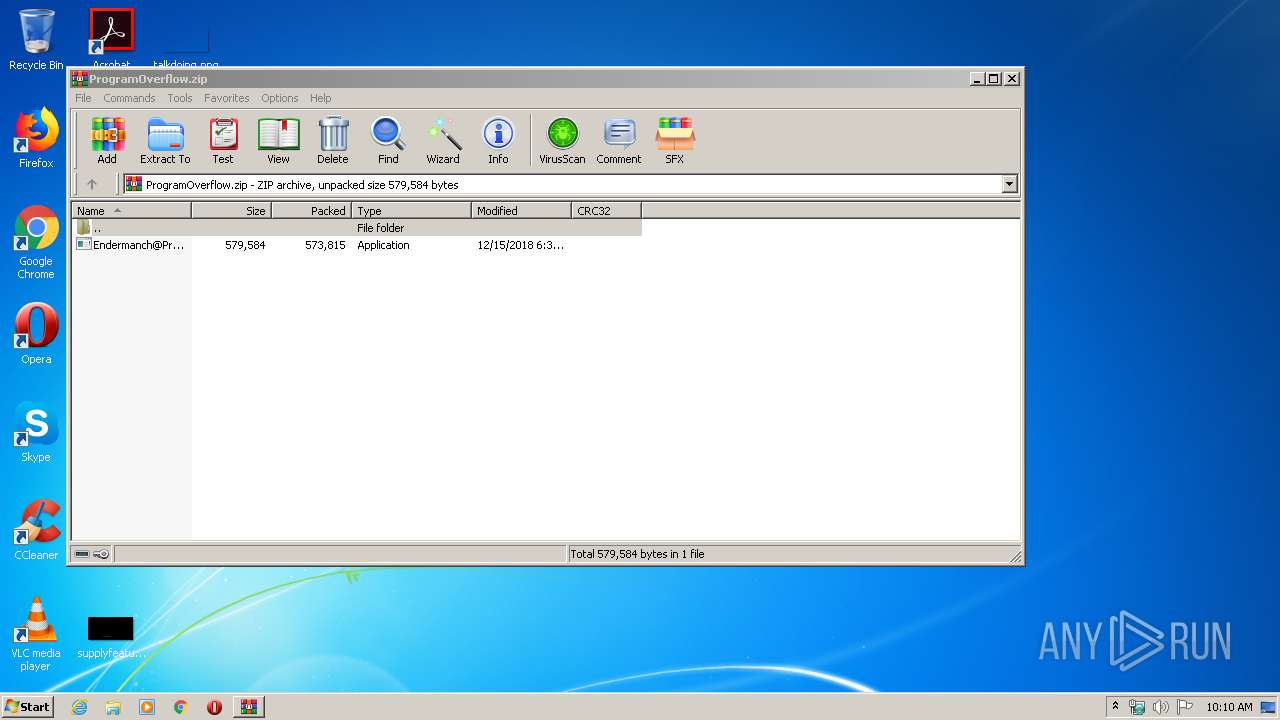
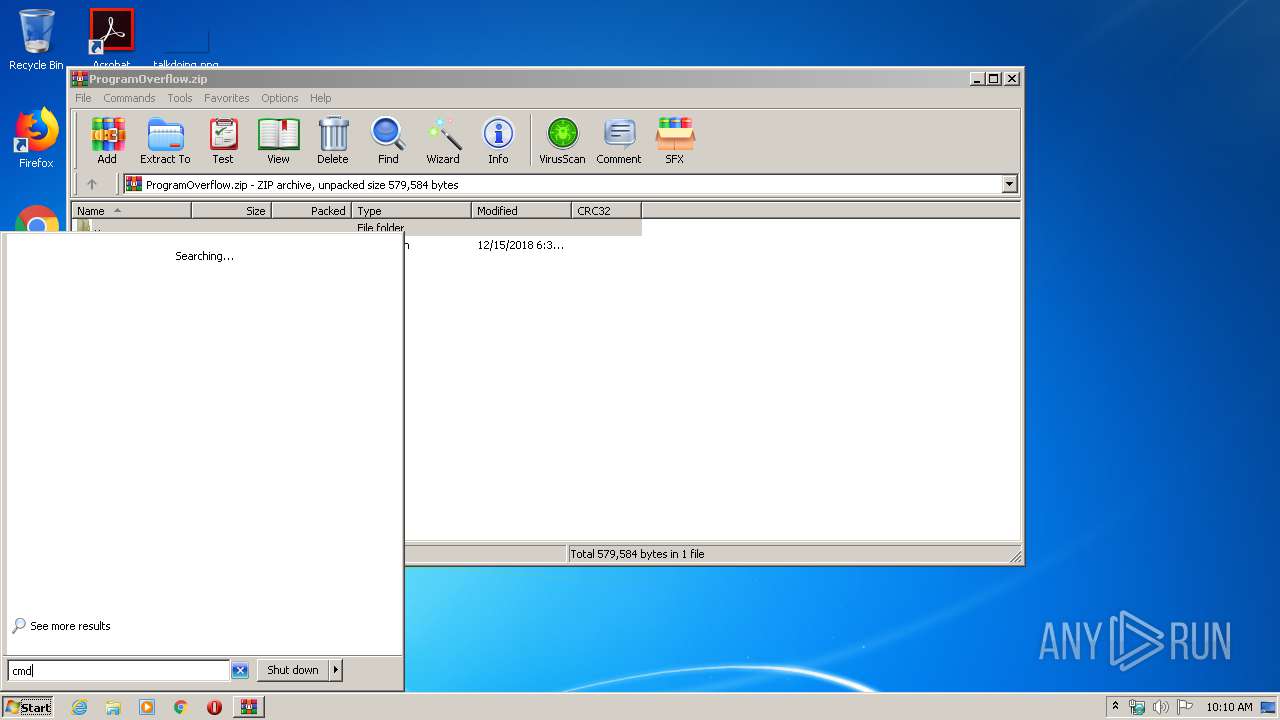
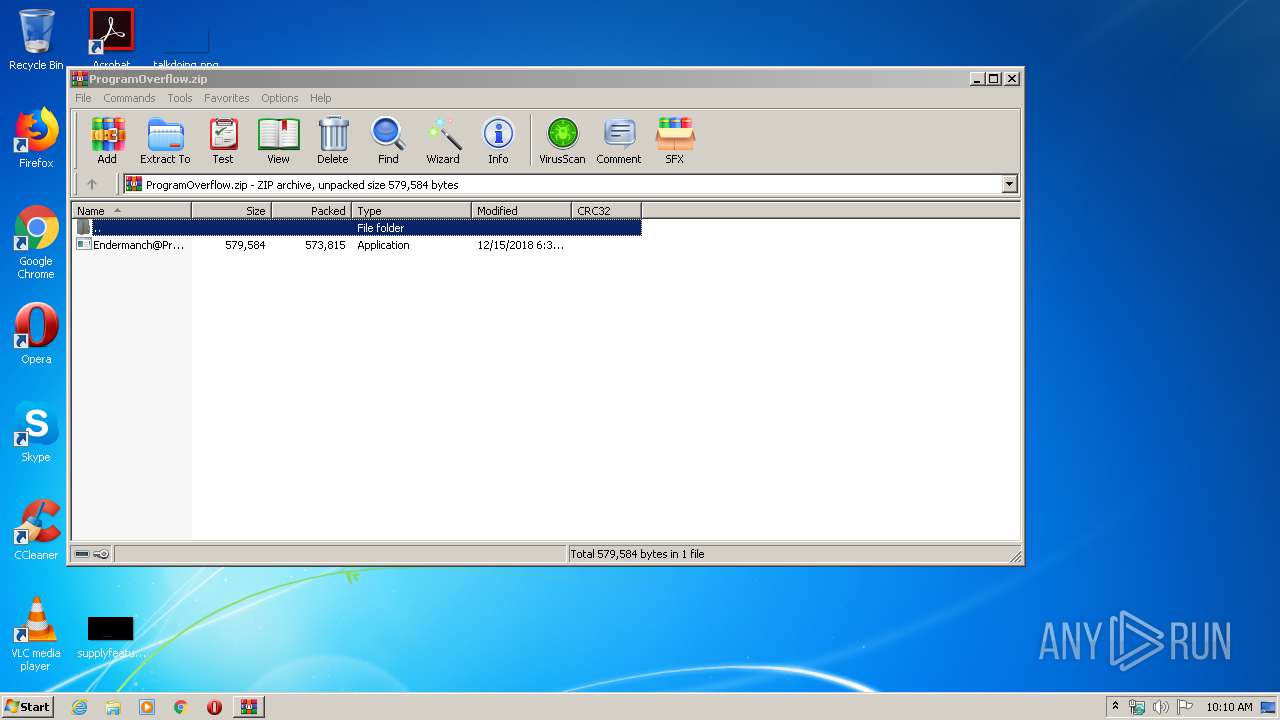
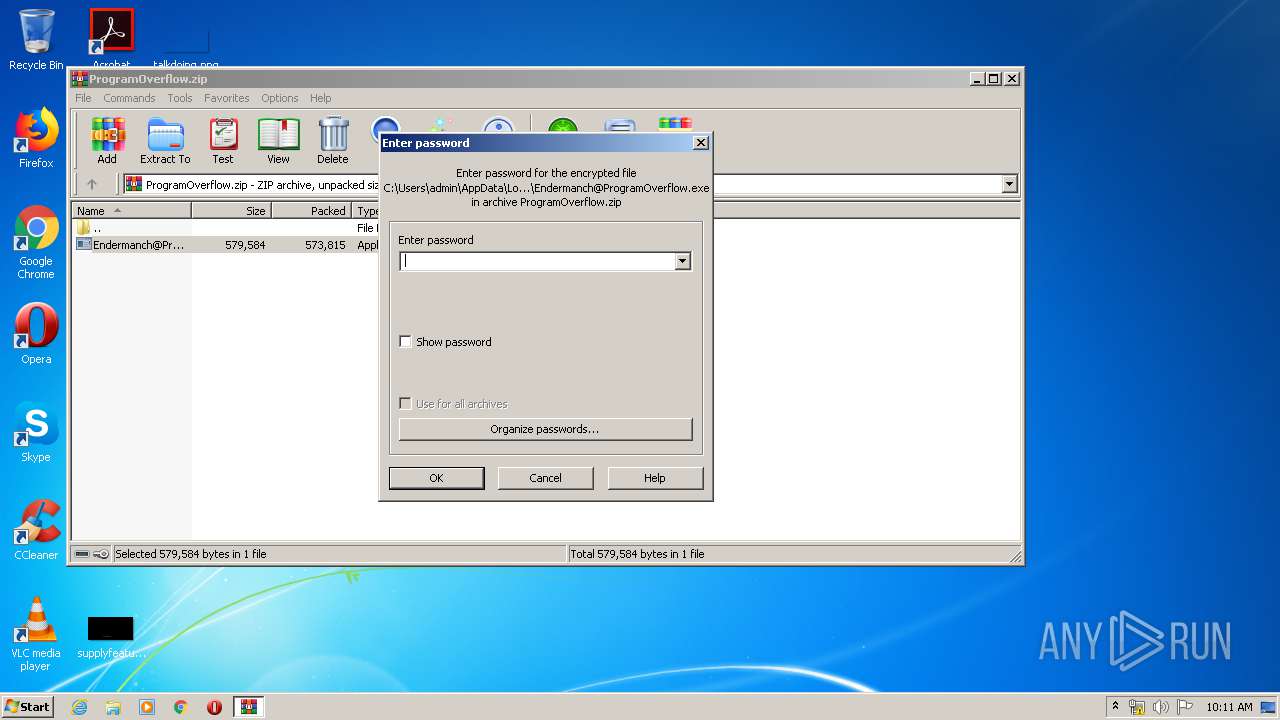
| 540 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\ProgramOverflow.zip" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 620 | "C:\Users\admin\Desktop\Endermanch@ProgramOverflow.exe" | C:\Users\admin\Desktop\Endermanch@ProgramOverflow.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Project1 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2732 | "C:\Users\admin\Desktop\Endermanch@ProgramOverflow.exe" | C:\Users\admin\Desktop\Endermanch@ProgramOverflow.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Project1 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2928 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3152 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3260 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3260 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://github.com/Endermanch/MalwareDatabase/raw/master/enderware/ProgramOverflow.zip" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4088 | "C:\Users\admin\Desktop\Endermanch@ProgramOverflow.exe" | C:\Users\admin\Desktop\Endermanch@ProgramOverflow.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Project1 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 258
Read events
1 189
Write events
65
Delete events
4
Modification events
| (PID) Process: | (3260) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2960659956 | |||
| (PID) Process: | (3260) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30806789 | |||
| (PID) Process: | (3260) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3260) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3260) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3260) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3260) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3260) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3260) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3260) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
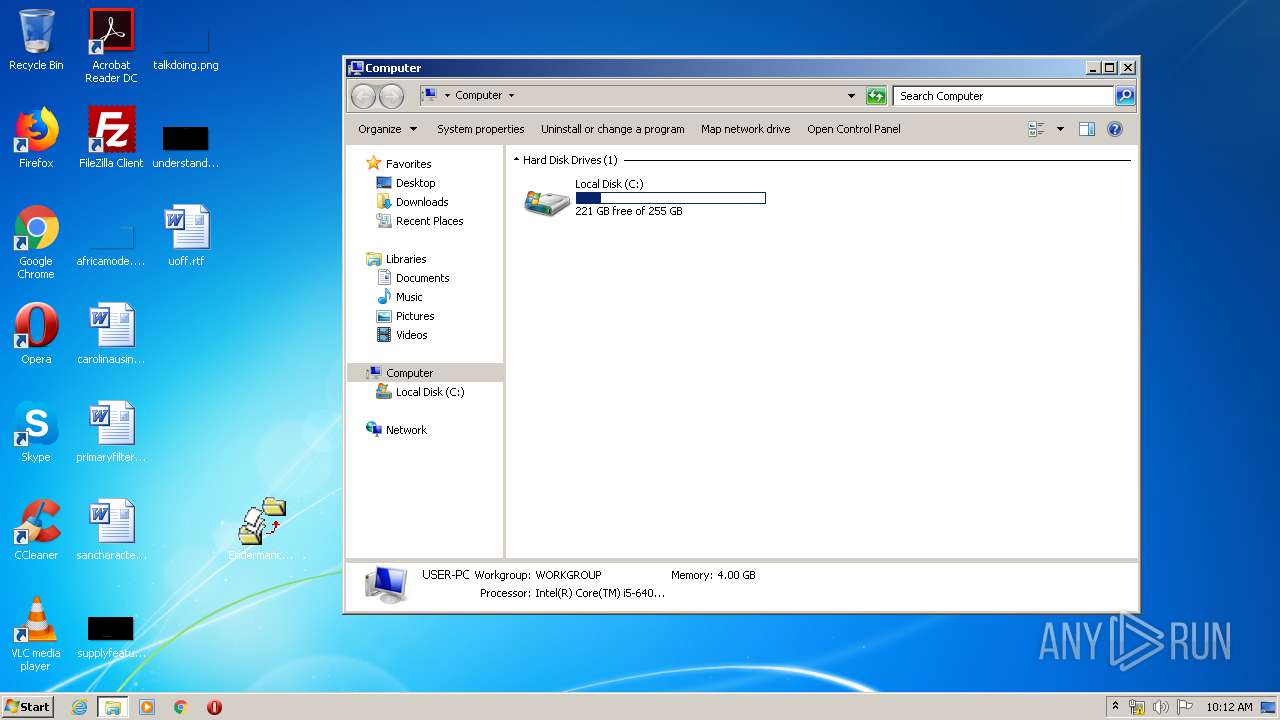
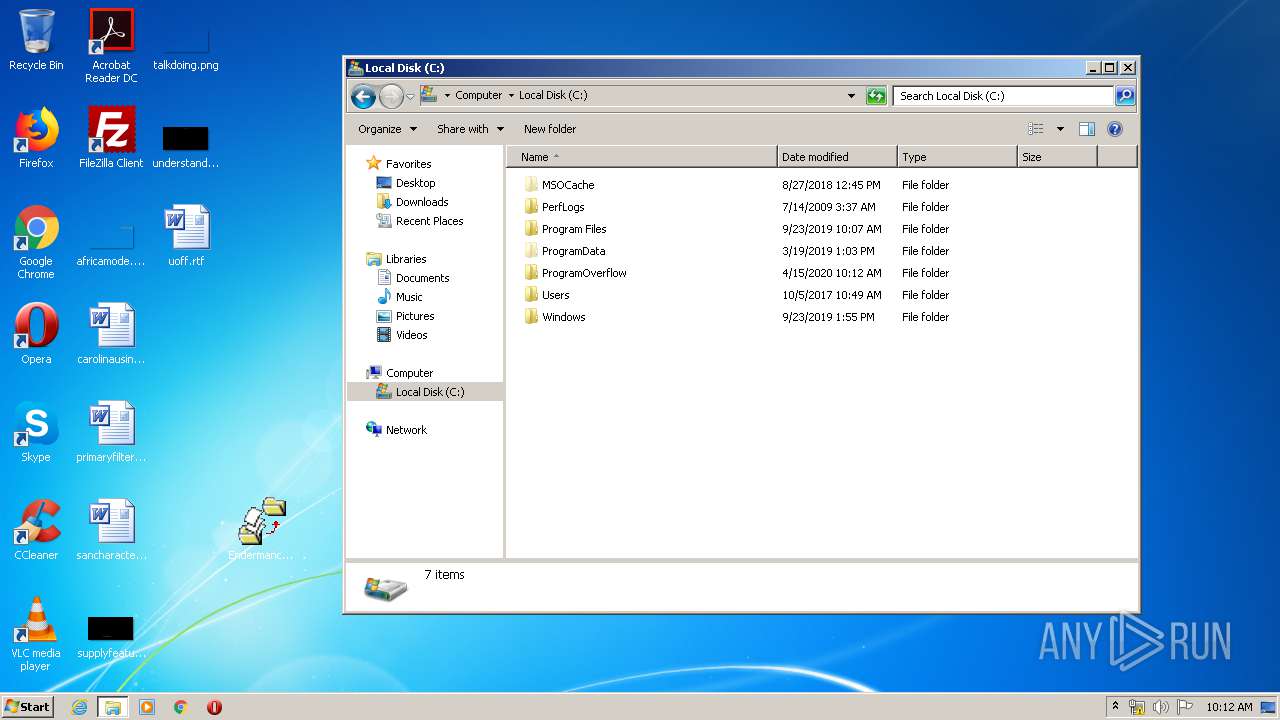
Executable files
453
Suspicious files
16
Text files
1
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3152 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabE864.tmp | — | |
MD5:— | SHA256:— | |||
| 3152 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarE865.tmp | — | |
MD5:— | SHA256:— | |||
| 3260 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF82B0C1F8F13B4D3C.TMP | — | |
MD5:— | SHA256:— | |||
| 3260 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\ProgramOverflow.zip.gb9ay00.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 3260 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF203C6EC08B9EAB8F.TMP | — | |
MD5:— | SHA256:— | |||
| 3260 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{DC2FEBFF-7EF8-11EA-972D-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3152 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\5887976EDAA817EEF5159B09F6FCD000_F64DCBBA399D666280C86776448D3B95 | der | |
MD5:— | SHA256:— | |||
| 3152 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | der | |
MD5:— | SHA256:— | |||
| 3152 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | binary | |
MD5:— | SHA256:— | |||
| 3260 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{DC2FEC01-7EF8-11EA-972D-5254004A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
6
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3152 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
3152 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3152 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3152 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAoGMEJ%2FW7ztaVc5ZZO2RR8%3D | US | der | 471 b | whitelisted |
3152 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
3152 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAoGMEJ%2FW7ztaVc5ZZO2RR8%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3152 | iexplore.exe | 151.101.0.133:443 | raw.githubusercontent.com | Fastly | US | malicious |
3152 | iexplore.exe | 140.82.118.3:443 | github.com | — | US | malicious |
3152 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| malicious |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
raw.githubusercontent.com |
| shared |