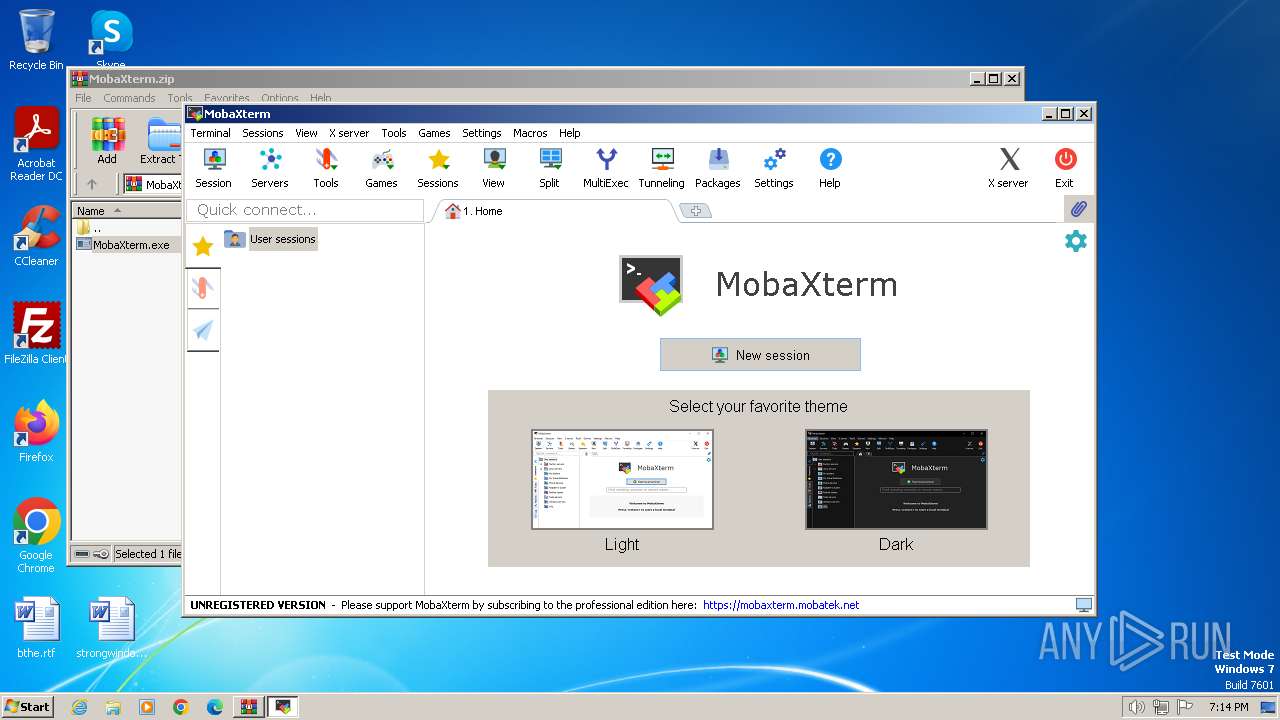
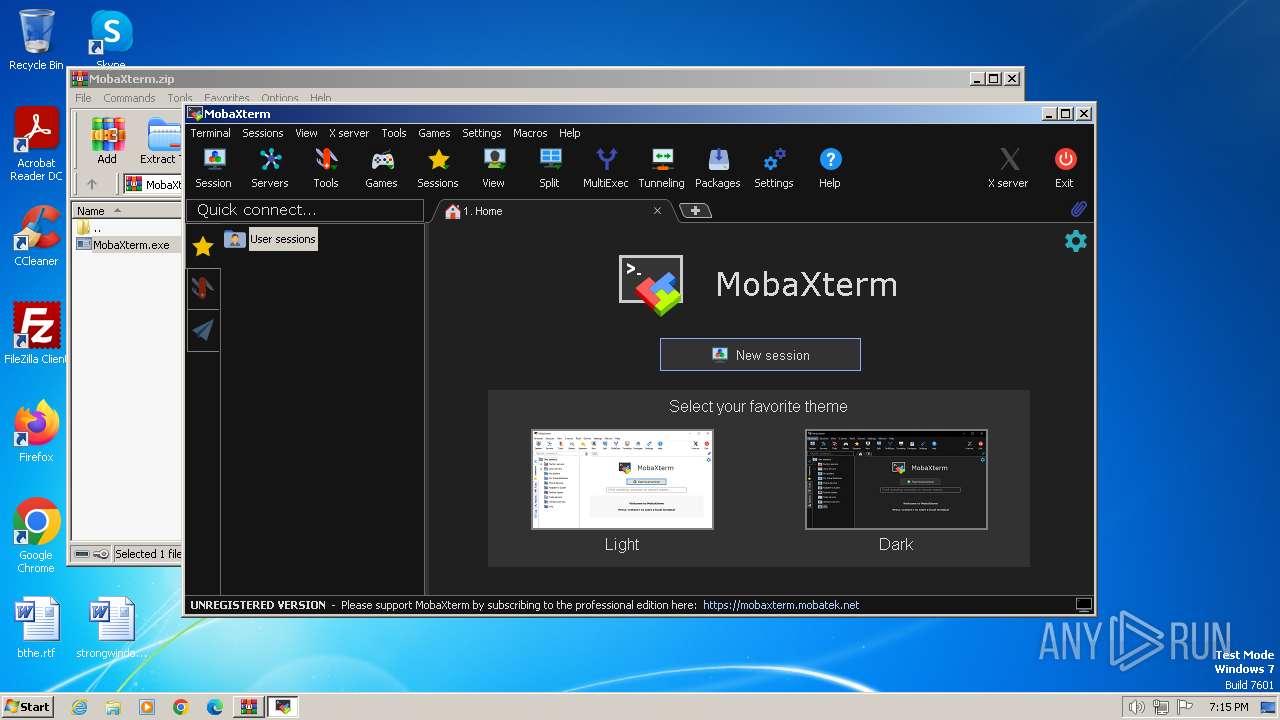
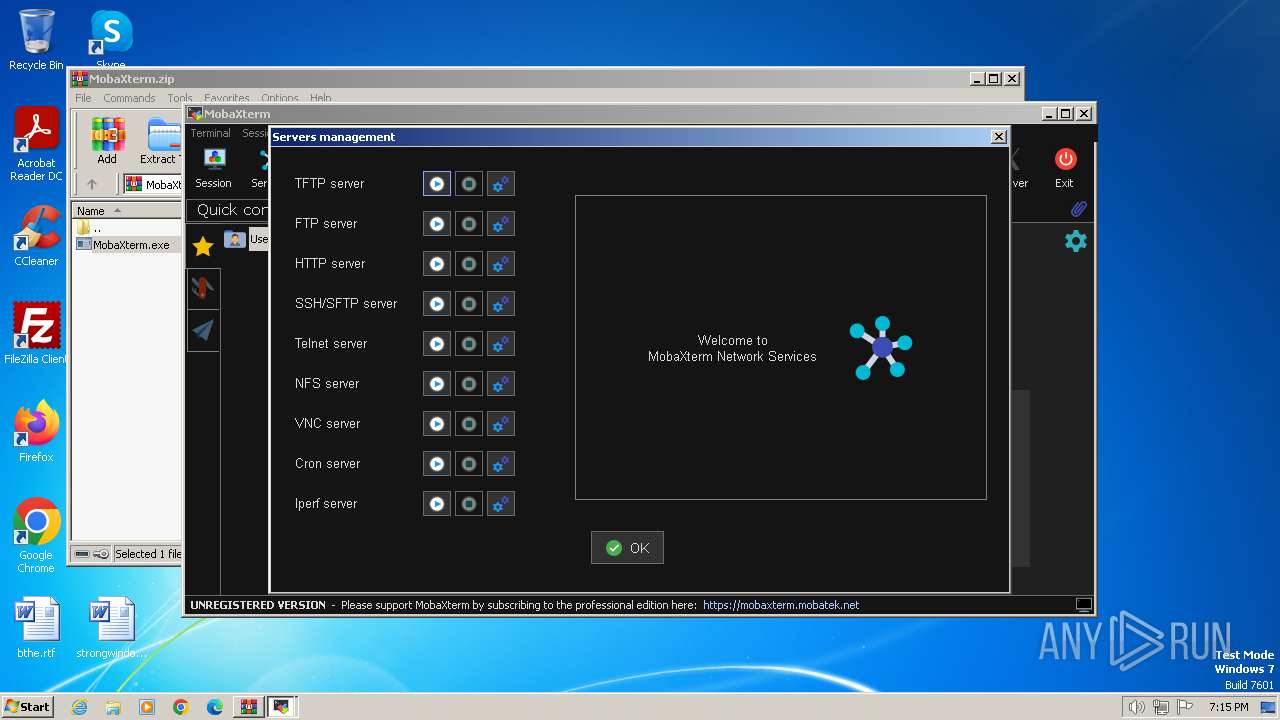
| File name: | MobaXterm.zip |
| Full analysis: | https://app.any.run/tasks/118c699f-cf2c-413b-8c7c-6e2d5765a532 |
| Verdict: | Malicious activity |
| Analysis date: | April 11, 2024, 18:14:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
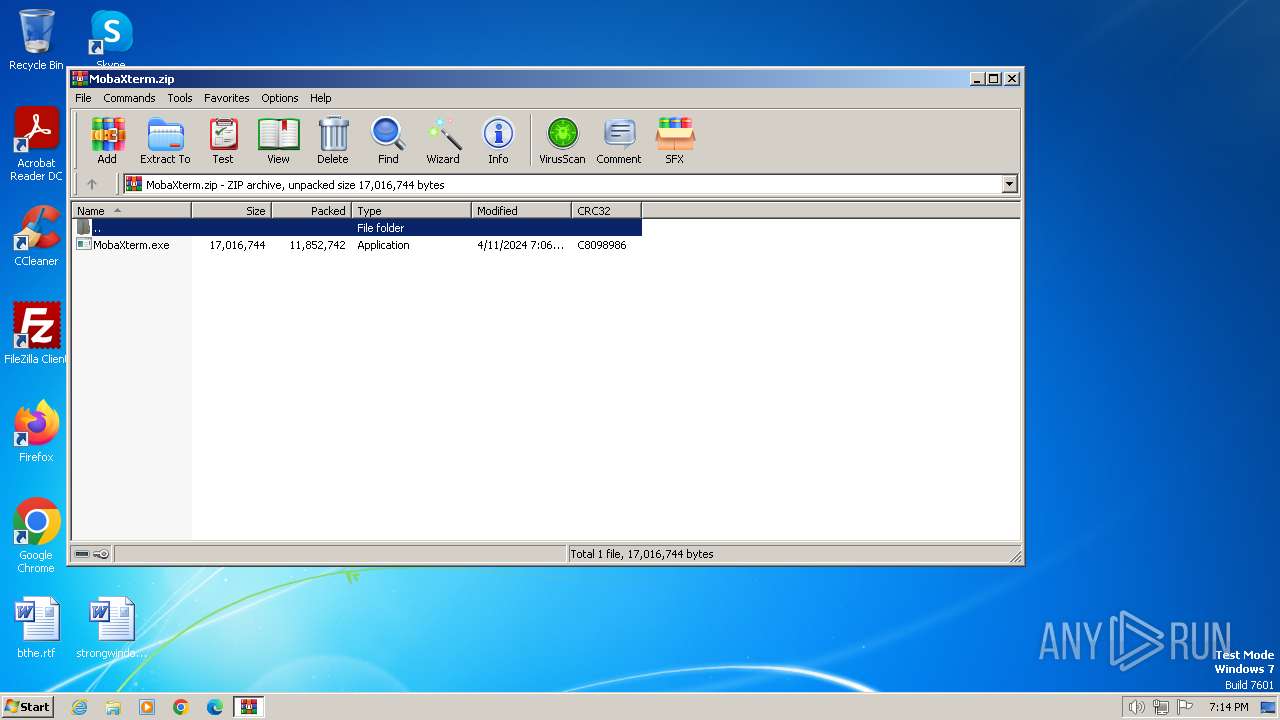
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 23293203AE3FCEB3936630C420FADDD5 |
| SHA1: | F32B258B923410E5C0F5A29487D3B951C2187EB1 |
| SHA256: | 5169BAA91D2C69D1C9D4C9FBAD6A04883252F6E85A2C8B218C201F4EE33C4A69 |
| SSDEEP: | 98304:bOeUFpByOd456xSGXewiBJSmzNJ99rh3cJsve5h1RzbLBQqO0vsDawor3fiT1Csv:4LU2aXL17a6ibGshv5HodW6t1 |
MALICIOUS
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1836)
- MobaXterm.exe (PID: 3276)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 1836)
- MobaXterm.exe (PID: 3276)
The process creates files with name similar to system file names
- MobaXterm.exe (PID: 3276)
Executable content was dropped or overwritten
- MobaXterm.exe (PID: 3276)
Reads the Internet Settings
- MobaXterm.exe (PID: 3276)
Checks Windows Trust Settings
- MobaXterm.exe (PID: 3276)
Reads settings of System Certificates
- MobaXterm.exe (PID: 3276)
INFO
Reads the computer name
- MobaXterm.exe (PID: 3276)
- XWin_MobaX.exe (PID: 3488)
- wmpnscfg.exe (PID: 848)
Checks supported languages
- MobaXterm.exe (PID: 3276)
- XWin_MobaX.exe (PID: 3488)
- xkbcomp_w32.exe (PID: 1824)
- wmpnscfg.exe (PID: 848)
Reads product name
- MobaXterm.exe (PID: 3276)
Reads mouse settings
- MobaXterm.exe (PID: 3276)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1836)
Reads Environment values
- MobaXterm.exe (PID: 3276)
Create files in a temporary directory
- MobaXterm.exe (PID: 3276)
- XWin_MobaX.exe (PID: 3488)
- xkbcomp_w32.exe (PID: 1824)
Reads the machine GUID from the registry
- MobaXterm.exe (PID: 3276)
Creates files or folders in the user directory
- MobaXterm.exe (PID: 3276)
Manual execution by a user
- wmpnscfg.exe (PID: 848)
Checks proxy server information
- MobaXterm.exe (PID: 3276)
Reads the software policy settings
- MobaXterm.exe (PID: 3276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:04:11 15:06:04 |
| ZipCRC: | 0xc8098986 |
| ZipCompressedSize: | 11852742 |
| ZipUncompressedSize: | 17016744 |
| ZipFileName: | MobaXterm.exe |
Total processes
42
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 848 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1824 | "C:\Users\admin\AppData\Local\Temp\Mxt240\bin\xkbcomp_w32.exe" -w 1 "-RC:\Users\admin\AppData\Local\Temp\Mxt240\usr\share\X11\xkb" -xkm "C:\Users\admin\AppData\Local\Temp\Mxt240\var\log\xwin\xkb_a00956" -em1 "The XKEYBOARD keymap compiler (xkbcomp) reports:" -emp "> " -eml "Errors from xkbcomp are not fatal to the X server" "C:\Users\admin\AppData\Local\Temp\Mxt240\var\log\xwin\server-0.xkm" | C:\Users\admin\AppData\Local\Temp\Mxt240\bin\xkbcomp_w32.exe | — | XWin_MobaX.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
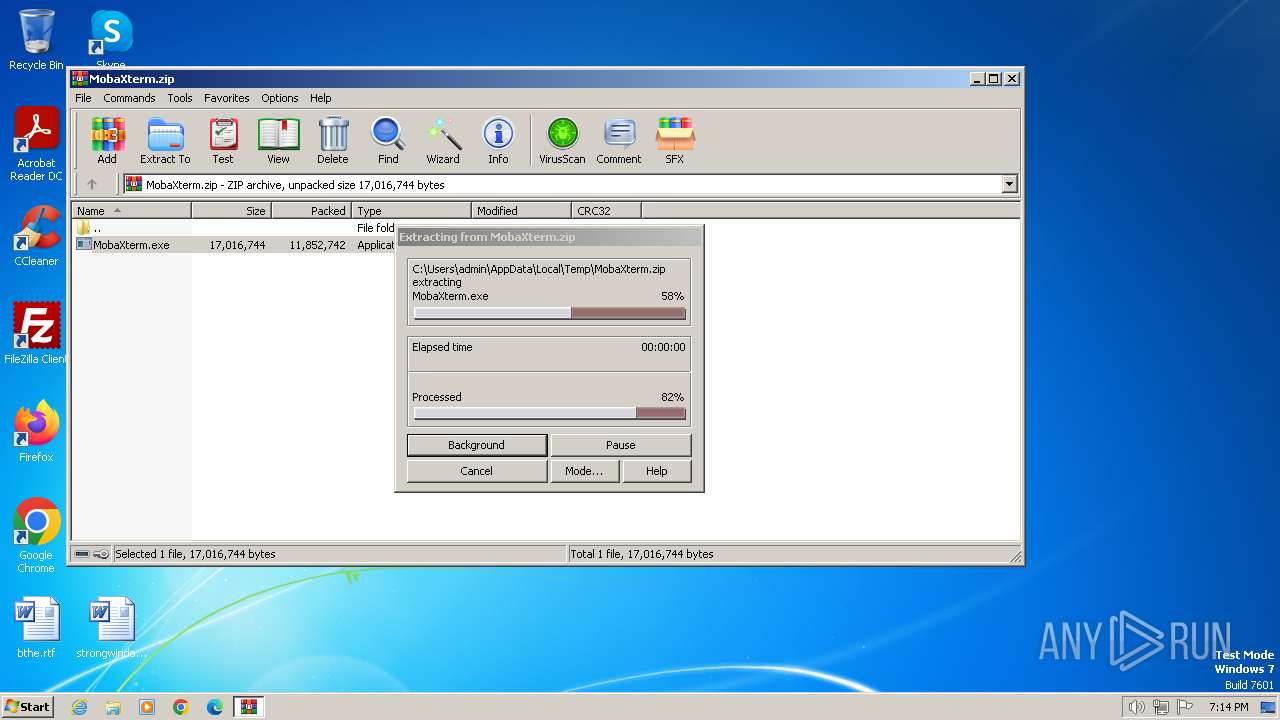
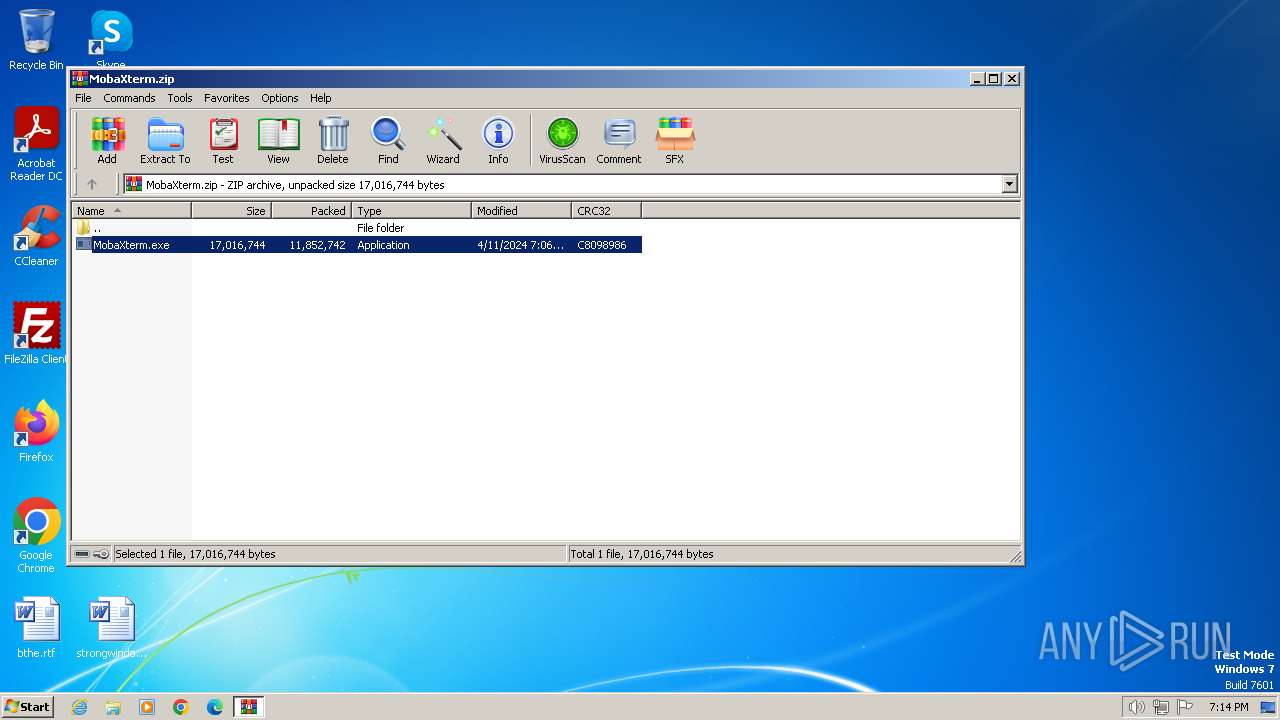
| 1836 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\MobaXterm.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
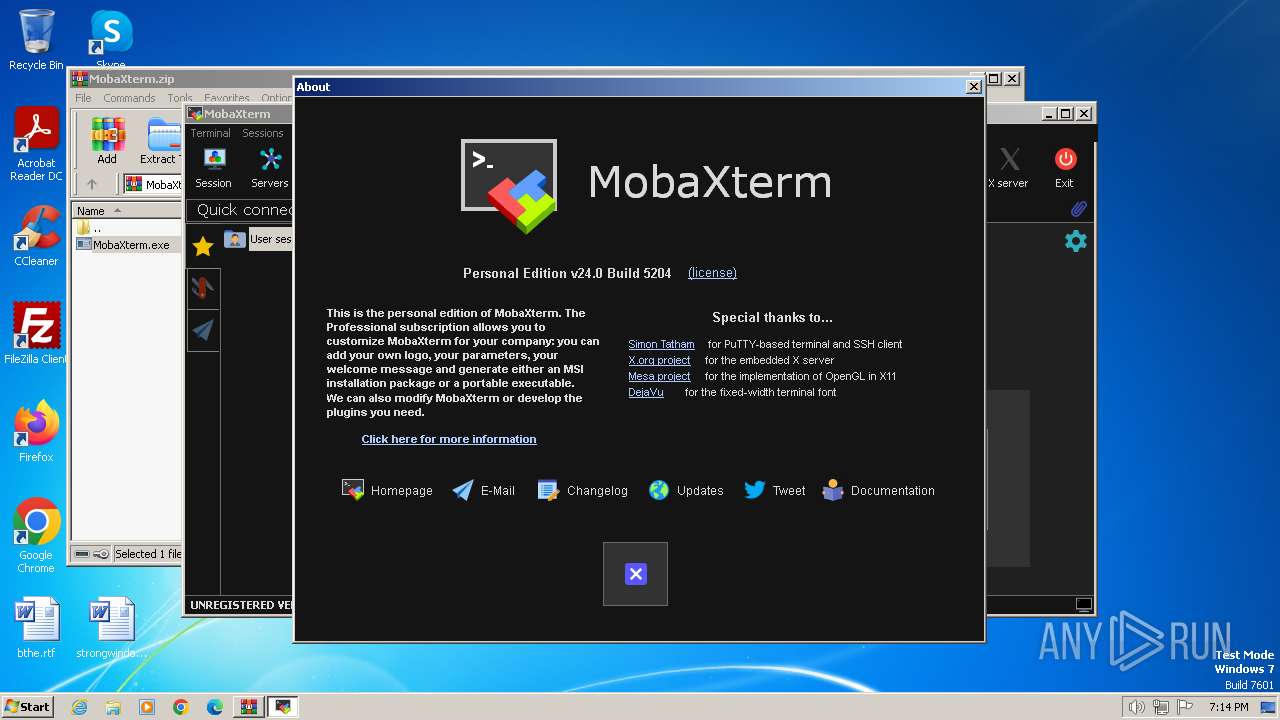
| 3276 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1836.26553\MobaXterm.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1836.26553\MobaXterm.exe | WinRAR.exe | ||||||||||||
User: admin Company: Mobatek Integrity Level: MEDIUM Description: MobaXterm Version: 24.0.0.5204 Modules
| |||||||||||||||
| 3488 | "C:\Users\admin\AppData\Local\Temp\Mxt240\bin\XWin_MobaX.exe" -silent-dup-error -notrayicon -nolisten inet6 -hostintitle +bs -clipboard -nowgl -multiwindow -noreset :0 | C:\Users\admin\AppData\Local\Temp\Mxt240\bin\XWin_MobaX.exe | — | MobaXterm.exe | |||||||||||
User: admin Company: Mobatek Integrity Level: MEDIUM Description: MobaXterm embedded X11 server Version: 21.1.8 Modules
| |||||||||||||||
Total events
10 650
Read events
10 277
Write events
367
Delete events
6
Modification events
| (PID) Process: | (1836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1836) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (1836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (1836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\MobaXterm.zip | |||
| (PID) Process: | (1836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
43
Suspicious files
134
Text files
467
Unknown types
74
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1836 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1836.26553\MobaXterm.exe | executable | |
MD5:— | SHA256:— | |||
| 3276 | MobaXterm.exe | C:\Users\admin\AppData\Local\Temp\Mxt240\etc\fstab | text | |
MD5:— | SHA256:— | |||
| 3276 | MobaXterm.exe | C:\Users\admin\AppData\Local\Temp\Mxt240\etc\profile | text | |
MD5:— | SHA256:— | |||
| 3276 | MobaXterm.exe | C:\Users\admin\AppData\Local\Temp\Mxt240\etc\ssh_config | text | |
MD5:— | SHA256:— | |||
| 3276 | MobaXterm.exe | C:\Users\admin\AppData\Local\Temp\Mxt240\etc\baseprofile | text | |
MD5:— | SHA256:— | |||
| 3276 | MobaXterm.exe | C:\Users\admin\AppData\Local\Temp\Mxt240\etc\group | text | |
MD5:— | SHA256:— | |||
| 3276 | MobaXterm.exe | C:\Users\admin\AppData\Local\Temp\Mxt240\etc\passwd | text | |
MD5:— | SHA256:— | |||
| 3276 | MobaXterm.exe | C:\Users\admin\AppData\Local\Temp\Mxt240\etc\nsswitch.conf | text | |
MD5:— | SHA256:— | |||
| 3276 | MobaXterm.exe | C:\Users\admin\AppData\Local\Temp\Mxt240\etc\init.d\tftp | binary | |
MD5:— | SHA256:— | |||
| 3276 | MobaXterm.exe | C:\Users\admin\AppData\Local\Temp\Mxt240\etc\init.d\ftp | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
9
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3276 | MobaXterm.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEQDpB%2BX%2FgHUiQQmQfWcoygAQ | unknown | — | — | unknown |
3276 | MobaXterm.exe | GET | 304 | 184.24.77.193:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?34ee46b993003101 | unknown | — | — | unknown |
3276 | MobaXterm.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSVjktWKi1hNQg7TUhR%2BeV%2F9eAiRQQUgRGS3mYypbBbMz1lQ4X81AQt8a4CEQDVBiEN0Dn%2BssMx6CvXMhYr | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3276 | MobaXterm.exe | 46.105.198.129:443 | mobaxterm.mobatek.net | OVH SAS | FR | unknown |
3276 | MobaXterm.exe | 184.24.77.193:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3276 | MobaXterm.exe | 104.18.38.233:80 | ocsp.usertrust.com | CLOUDFLARENET | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mobaxterm.mobatek.net |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |