| File name: | PotatoNV-next-v2.1.0-x86.exe |
| Full analysis: | https://app.any.run/tasks/b6021c3b-ca24-4c1c-b50a-5576b1e02ade |
| Verdict: | Malicious activity |
| Analysis date: | May 26, 2021, 14:19:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 03C58D0EE21144EAFA2CD7B5F2E07F87 |
| SHA1: | C29D31889FBF999A1F6B13084545FE1AC1A2CB82 |
| SHA256: | 51432FCD90869FBEECD70BCCDB51632303FE7AFDDDFC3321EFD71DE009F01A83 |
| SSDEEP: | 49152:jtPtJmDMH9XGrZlUs/9mrHAsJCP8KAUrULYkOvDbNlCgn9xJOMyvwHdVZO:jtP6MHpYFlmjj7KMzChlCgn9+s9VZO |
MALICIOUS
Application was dropped or rewritten from another process
- PotatoNV-next.exe (PID: 2376)
Loads dropped or rewritten executable
- PotatoNV-next.exe (PID: 2376)
SUSPICIOUS
Executable content was dropped or overwritten
- PotatoNV-next-v2.1.0-x86.exe (PID: 748)
Drops a file that was compiled in debug mode
- PotatoNV-next-v2.1.0-x86.exe (PID: 748)
Drops a file with too old compile date
- PotatoNV-next-v2.1.0-x86.exe (PID: 748)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| SpecialBuild: | - |
|---|---|
| PrivateBuild: | - |
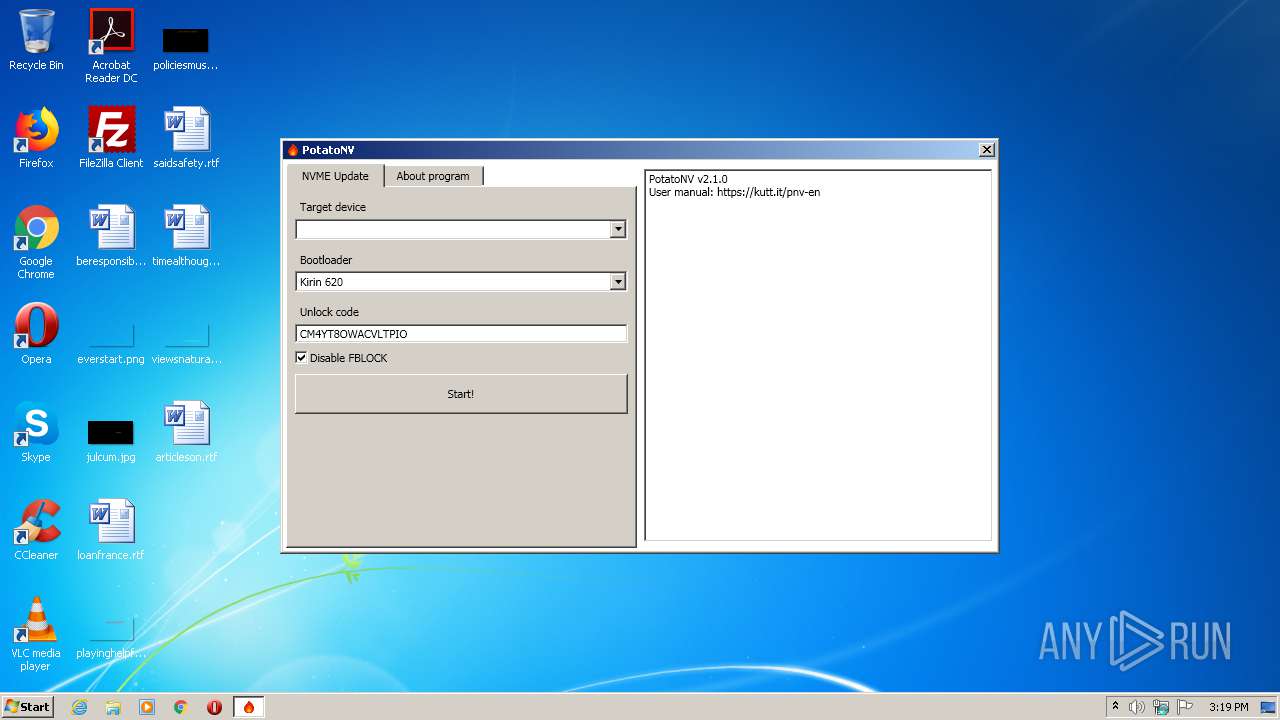
| Comments: | Unlock bootloader of Huawei devices on Kirin SoC. |
| ProductVersion: | 2.0.1.0 |
| FileVersion: | 2.0.1.0 |
| OriginalFileName: | PotatoNV-next.exe |
| ProductName: | PotatoNV |
| InternalName: | PotatoNV-next.exe |
| LegalTrademarks: | mashed-potatoes |
| LegalCopyright: | Copyright © mashed-potatoes 2020 |
| FileDescription: | PotatoNV |
| CompanyName: | mashed-potatoes |
| CharacterSet: | Unicode |
| LanguageCode: | Russian |
| FileSubtype: | - |
| ObjectFileType: | Unknown |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 2.0.1.0 |
| FileVersionNumber: | 2.0.1.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1638f |
| UninitializedDataSize: | - |
| InitializedDataSize: | 61440 |
| CodeSize: | 89600 |
| LinkerVersion: | 8 |
| PEType: | PE32 |
| TimeStamp: | 2012:12:31 01:38:38+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-Dec-2012 00:38:38 |
| Detected languages: |
|
| CompanyName: | mashed-potatoes |
| FileDescription: | PotatoNV |
| LegalCopyright: | Copyright © mashed-potatoes 2020 |
| LegalTrademarks: | mashed-potatoes |
| InternalName: | PotatoNV-next.exe |
| ProductName: | PotatoNV |
| OriginalFilename: | PotatoNV-next.exe |
| FileVersion: | 2.0.1.0 |
| ProductVersion: | 2.0.1.0 |
| Comments: | Unlock bootloader of Huawei devices on Kirin SoC. |
| PrivateBuild: | - |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0060 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000060 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 31-Dec-2012 00:38:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00015CFE | 0x00015E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.6445 |
.rdata | 0x00017000 | 0x00003982 | 0x00003A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.70129 |
.data | 0x0001B000 | 0x00004C8C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.35632 |
.rsrc | 0x00020000 | 0x0000AA48 | 0x0000AC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.32913 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.23138 | 838 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.60602 | 744 | Latin 1 / Western European | Russian - Russia | RT_ICON |
3 | 2.63074 | 488 | Latin 1 / Western European | Russian - Russia | RT_ICON |
4 | 2.3817 | 296 | Latin 1 / Western European | Russian - Russia | RT_ICON |
50 | 1.86117 | 38056 | Latin 1 / Western European | Russian - Russia | RT_ICON |
101 | 2.0815 | 20 | Latin 1 / Western European | Russian - Russia | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
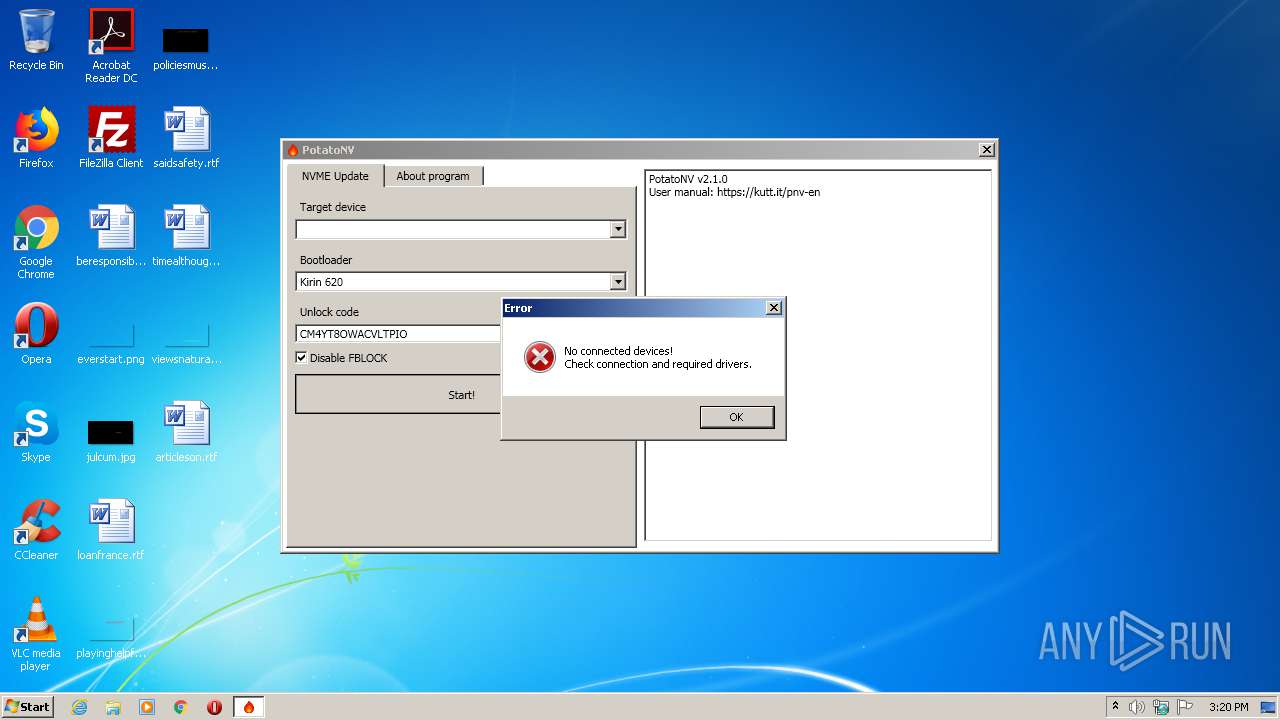
Total processes
39
Monitored processes
2
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 748 | "C:\Users\admin\AppData\Local\Temp\PotatoNV-next-v2.1.0-x86.exe" | C:\Users\admin\AppData\Local\Temp\PotatoNV-next-v2.1.0-x86.exe | explorer.exe | ||||||||||||
User: admin Company: mashed-potatoes Integrity Level: MEDIUM Description: PotatoNV Exit code: 0 Version: 2.0.1.0 Modules
| |||||||||||||||
| 2376 | "C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\PotatoNV-next.exe" | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\PotatoNV-next.exe | — | PotatoNV-next-v2.1.0-x86.exe | |||||||||||
User: admin Company: mashed-potatoes Integrity Level: MEDIUM Description: PotatoNV Exit code: 0 Version: 2.1.0.0 Modules
| |||||||||||||||
Total events
365
Read events
360
Write events
5
Delete events
0
Modification events
| (PID) Process: | (748) PotatoNV-next-v2.1.0-x86.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (748) PotatoNV-next-v2.1.0-x86.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2376) PotatoNV-next.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: PotatoNV-next.exe | |||
Executable files
5
Suspicious files
9
Text files
6
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 748 | PotatoNV-next-v2.1.0-x86.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\PotatoNV-next.exe.config | xml | |
MD5:— | SHA256:— | |||
| 748 | PotatoNV-next-v2.1.0-x86.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Potato.Fastboot.dll | executable | |
MD5:— | SHA256:— | |||
| 748 | PotatoNV-next-v2.1.0-x86.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\bootloaders\hisi620\manifest.xml | xml | |
MD5:B51AF4B61806D9C4E5F4884A6E81BC54 | SHA256:111BCDC509BF6272FA5DE52DD2C41E3E82C6233F65C30487E539D869920C0C40 | |||
| 748 | PotatoNV-next-v2.1.0-x86.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\bootloaders\hisi65x_a\manifest.xml | xml | |
MD5:E1E91A33EFEF4E1A5D5A79DFEFCE97F3 | SHA256:D18FED3B74BE14D648FB03D5C051A6751A0FC8F610610F5CFF63B25C5C8D3F8A | |||
| 748 | PotatoNV-next-v2.1.0-x86.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\bootloaders\hisi65x_a\fastboot.img | binary | |
MD5:4F782A46BBA9BCF460B2451EAFE2C555 | SHA256:C019E3E9ACEBE2A7E835D83EFD170F8867973C5F7DBA808958C2E02E1054A145 | |||
| 748 | PotatoNV-next-v2.1.0-x86.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\bootloaders\hisi950\xloader.img | binary | |
MD5:1E92A3236A633DD0F0A669A526193CC5 | SHA256:8E36A4A6642325D5F9CE6ECF16AF089AB5FB34C5B03AFD3D1E7BC307C7CA504D | |||
| 748 | PotatoNV-next-v2.1.0-x86.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\bootloaders\hisi960\manifest.xml | xml | |
MD5:612192103ED7D0C52E4BD70BEC2B5D95 | SHA256:CFD09ABA545055D3B3DD74D21A1455466E567BFF7385FDED0B052E1646A47D30 | |||
| 748 | PotatoNV-next-v2.1.0-x86.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\bootloaders\hisi950\manifest.xml | xml | |
MD5:A4C965975735642CFB1CCB82DE885847 | SHA256:26FA2769A66BA8E3C7A1D2D6F3D7D62DCE2DF1100E9A356FC29DA99262FDCD4C | |||
| 748 | PotatoNV-next-v2.1.0-x86.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\bootloaders\hisi960\xloader.img | binary | |
MD5:D4699092C50F49EB5A41C037A3ACC929 | SHA256:6285C8FD6597712D0B4ED1C58929DE9B9365AEAC221535251D49B8335EDC18AE | |||
| 748 | PotatoNV-next-v2.1.0-x86.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\bootloaders\hisi960\fastboot.img | binary | |
MD5:CBAC4A49FC38CA4ED11A9A3010F4CEBE | SHA256:C7B70AB16C052B194D7AAF87A3D993CCD34FF177084A28FAAF04F58E13877CF9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report