| File name: | DEATHXP.ps1 |
| Full analysis: | https://app.any.run/tasks/679c32c2-4972-4ab7-957f-5933cb561438 |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 15:39:22 |
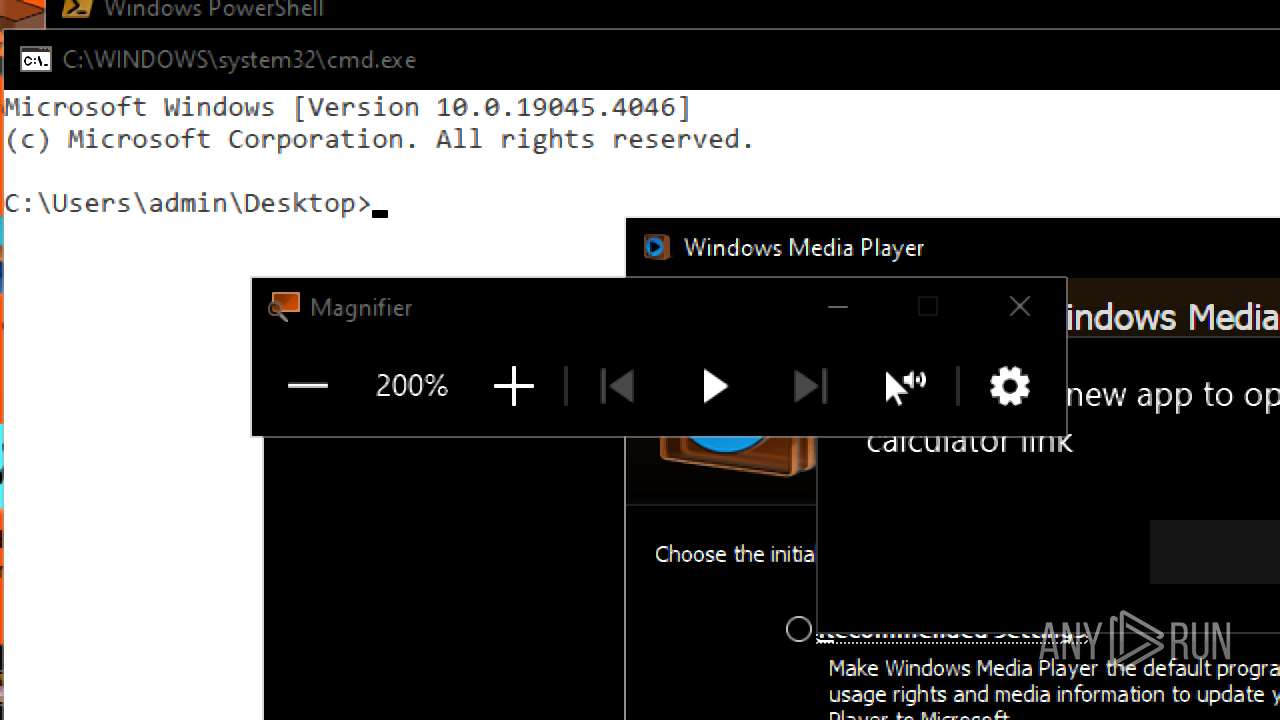
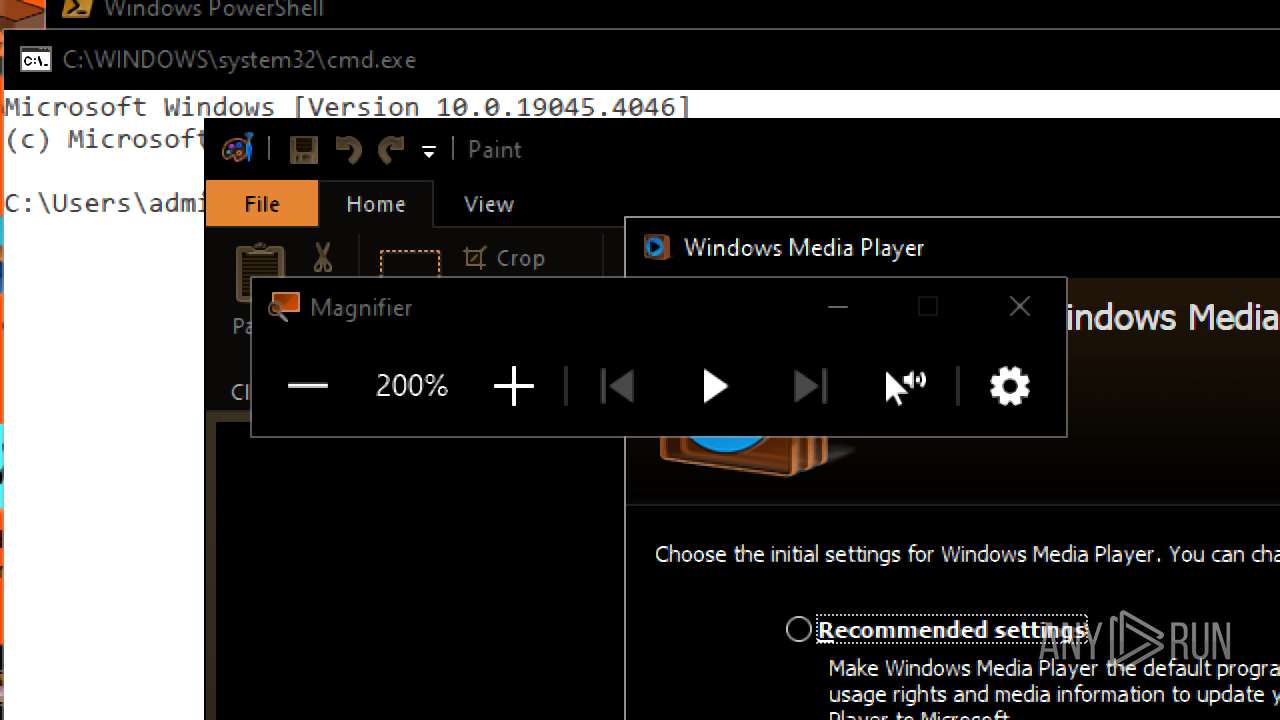
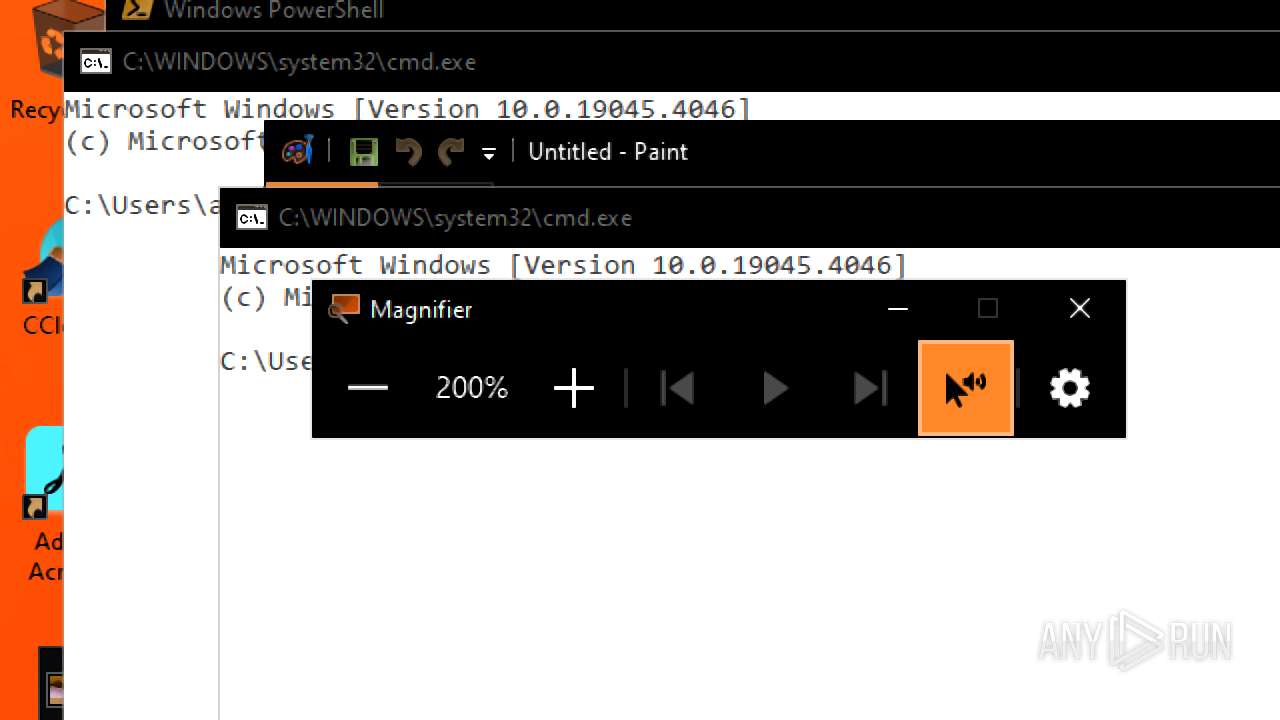
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-8 text, with CRLF line terminators |
| MD5: | EC31ADDF78BDEDB4C5F125F47335CB47 |
| SHA1: | AE81A16AB9750B385D1E5881443C08306BFF24A5 |
| SHA256: | 513F653983B75F14D6A68A7749B8433EDDAD035C9485FF004A78908EA246ADD7 |
| SSDEEP: | 96:f/pTDFv8ypiTQPacVUhj26wtld8gwlMvXVpRkJGVYLr5WPlN8l:Z3lShxo2eidHo6 |
MALICIOUS
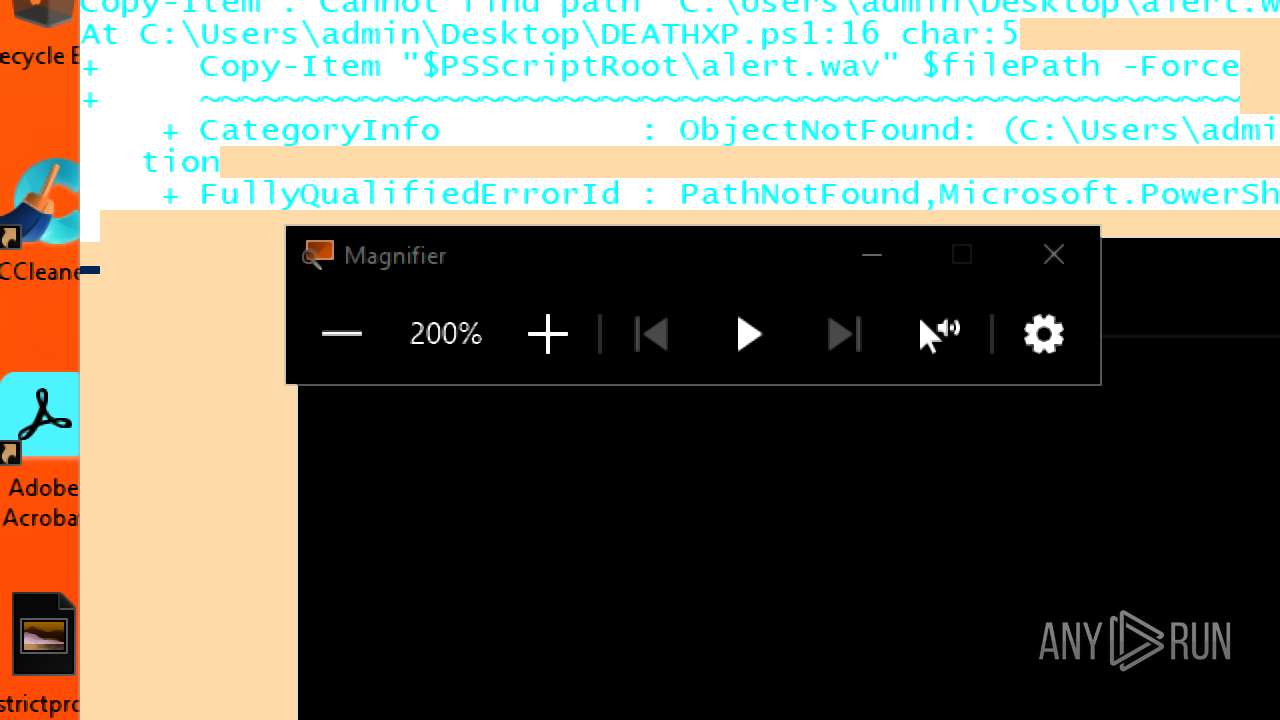
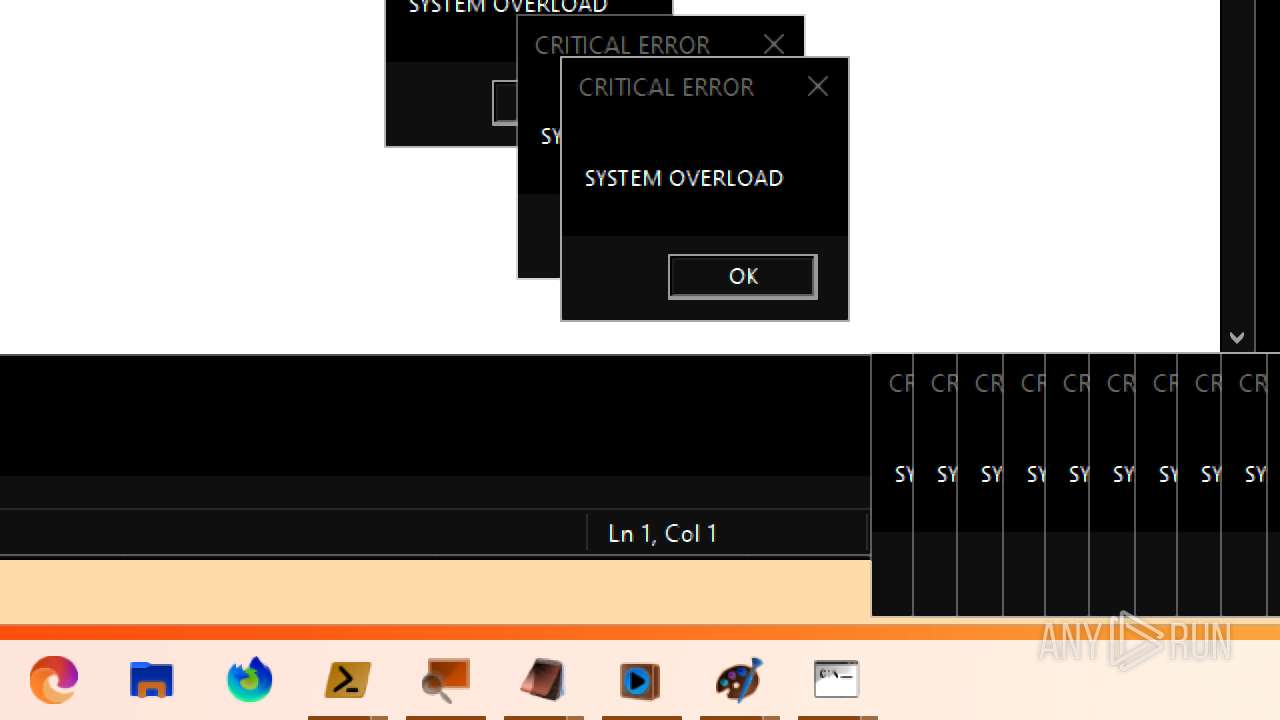
Bypass execution policy to execute commands
- powershell.exe (PID: 3832)
Run PowerShell with an invisible window
- powershell.exe (PID: 7140)
- powershell.exe (PID: 8184)
- powershell.exe (PID: 3460)
- powershell.exe (PID: 7200)
- powershell.exe (PID: 6160)
- powershell.exe (PID: 7316)
- powershell.exe (PID: 3108)
- powershell.exe (PID: 7544)
- powershell.exe (PID: 7420)
- powershell.exe (PID: 7804)
- powershell.exe (PID: 7688)
- powershell.exe (PID: 8024)
- powershell.exe (PID: 7920)
- powershell.exe (PID: 8296)
- powershell.exe (PID: 7492)
- powershell.exe (PID: 4836)
- powershell.exe (PID: 8424)
- powershell.exe (PID: 8568)
- powershell.exe (PID: 8320)
- powershell.exe (PID: 8948)
- powershell.exe (PID: 9108)
- powershell.exe (PID: 8824)
- powershell.exe (PID: 8720)
- powershell.exe (PID: 9224)
- powershell.exe (PID: 9420)
- powershell.exe (PID: 9704)
- powershell.exe (PID: 9580)
- powershell.exe (PID: 9852)
- powershell.exe (PID: 9980)
- powershell.exe (PID: 10136)
SUSPICIOUS
Gets path to any of the special folders (POWERSHELL)
- powershell.exe (PID: 3832)
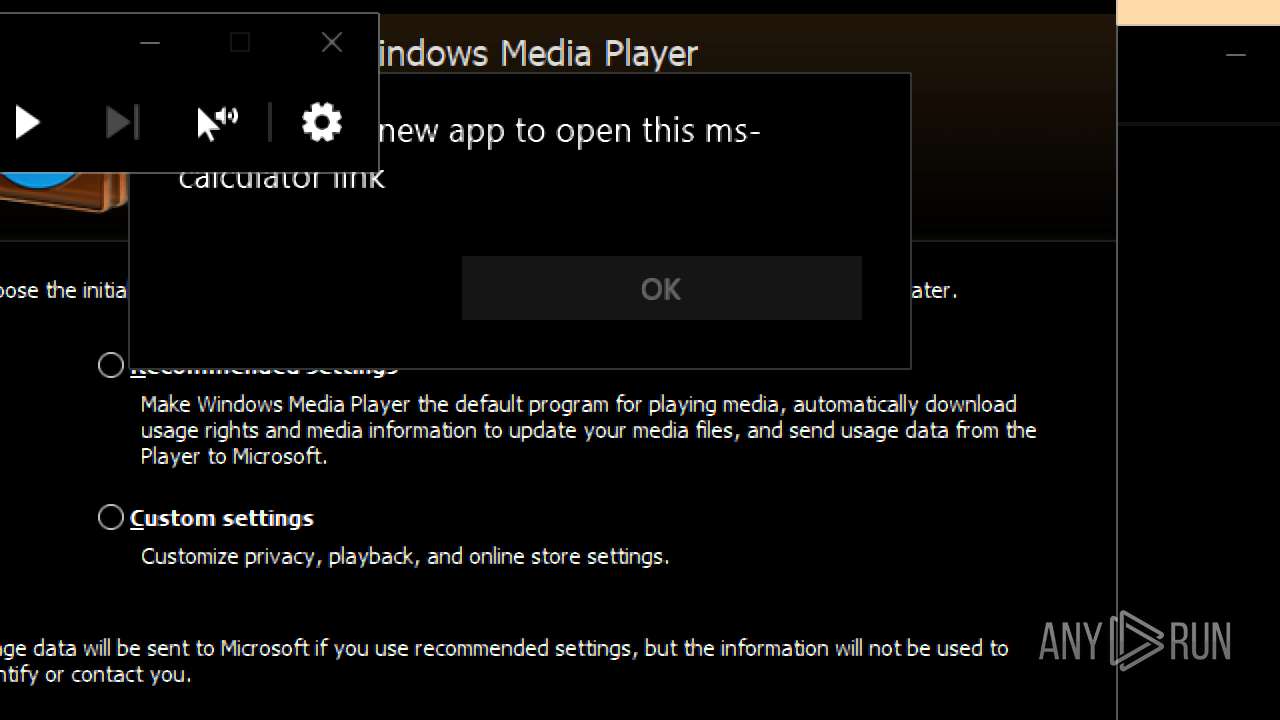
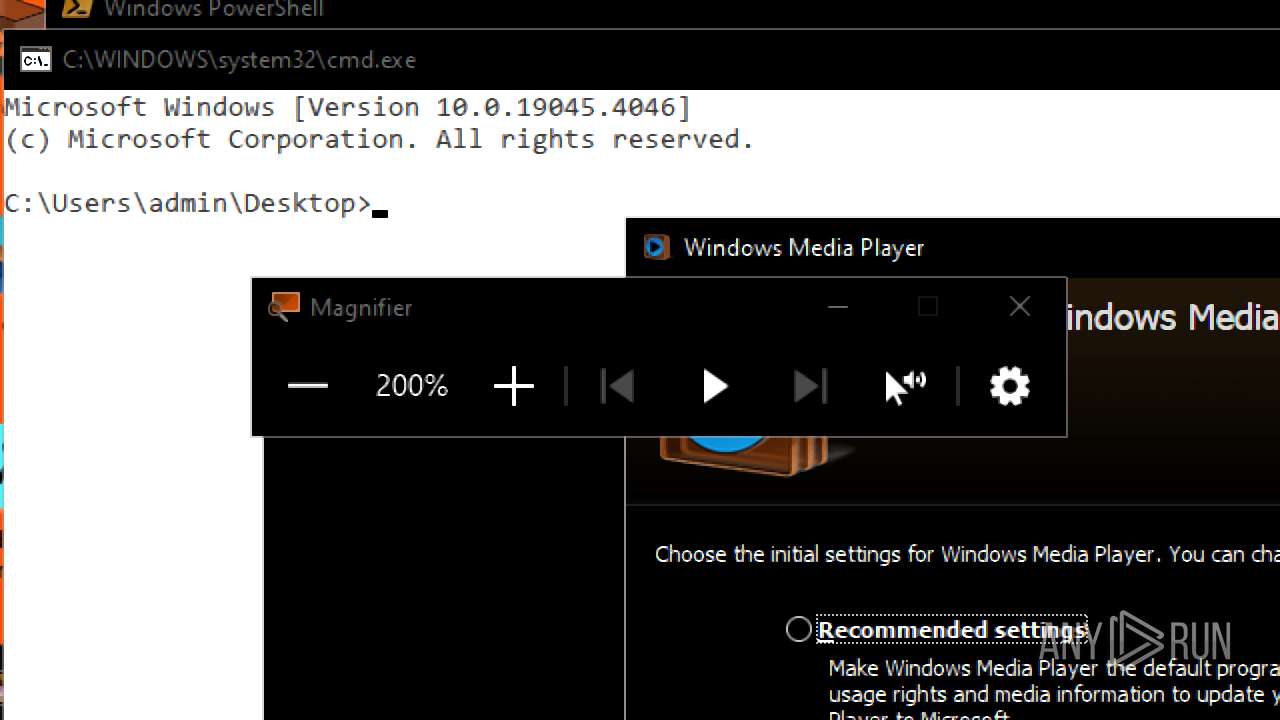
Reads security settings of Internet Explorer
- wmplayer.exe (PID: 5628)
- setup_wm.exe (PID: 6688)
- wmplayer.exe (PID: 5232)
- wmplayer.exe (PID: 4892)
- wmplayer.exe (PID: 6960)
- wmplayer.exe (PID: 2668)
- wmplayer.exe (PID: 4312)
- wmplayer.exe (PID: 4172)
- wmplayer.exe (PID: 5552)
- wmplayer.exe (PID: 6900)
- wmplayer.exe (PID: 4752)
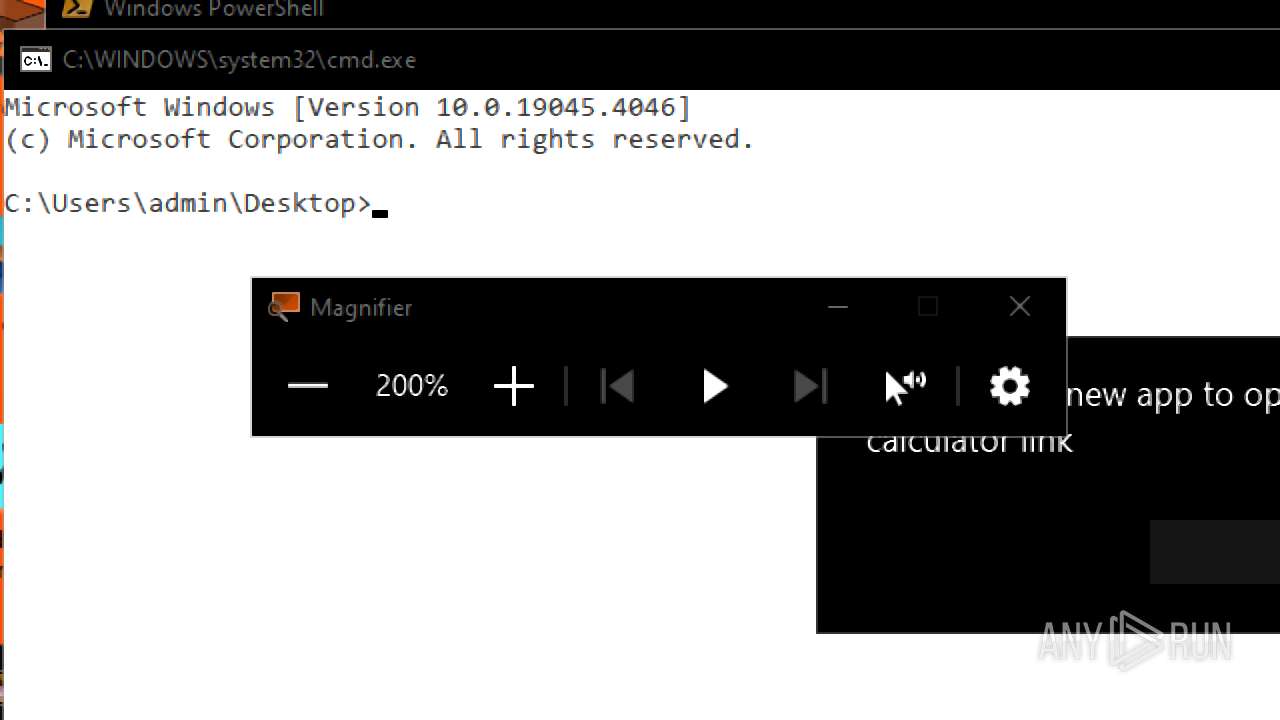
Starts CMD.EXE for commands execution
- powershell.exe (PID: 3832)
SQL CE related mutex has been found
- unregmp2.exe (PID: 3396)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 3832)
Application launched itself
- powershell.exe (PID: 3832)
Executable content was dropped or overwritten
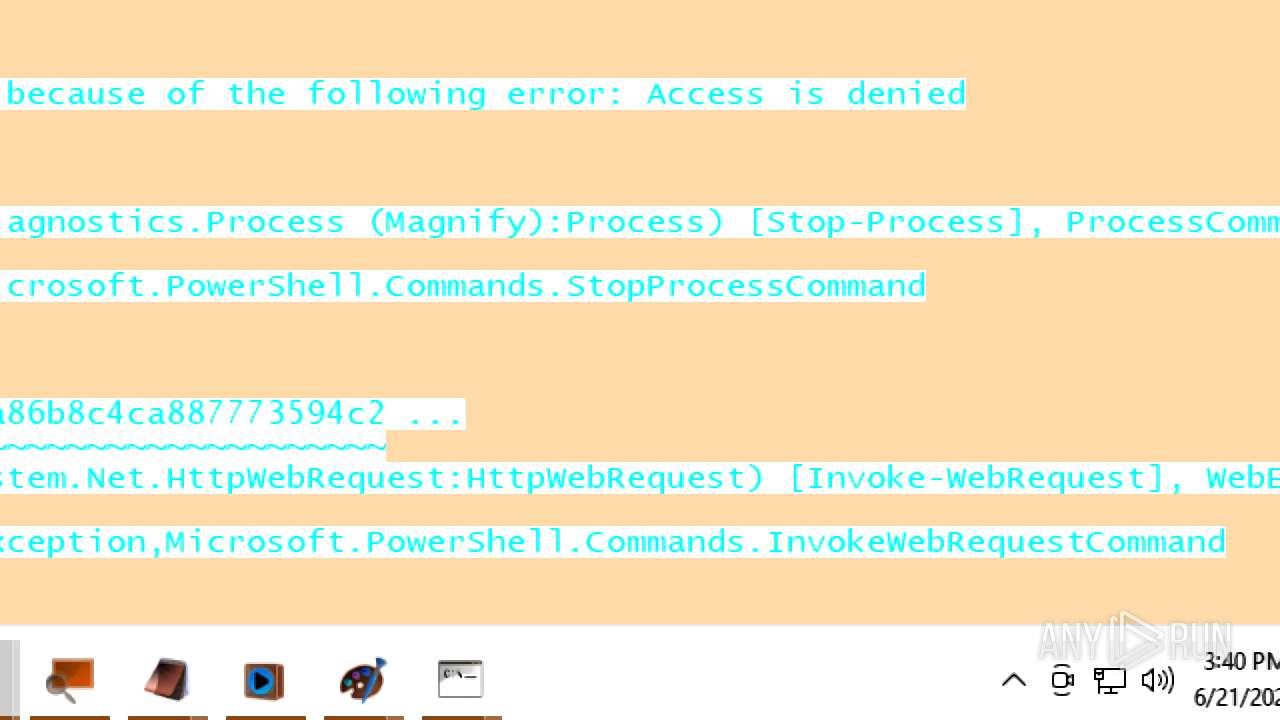
- csc.exe (PID: 10860)
CSC.EXE is used to compile C# code
- csc.exe (PID: 10860)
INFO
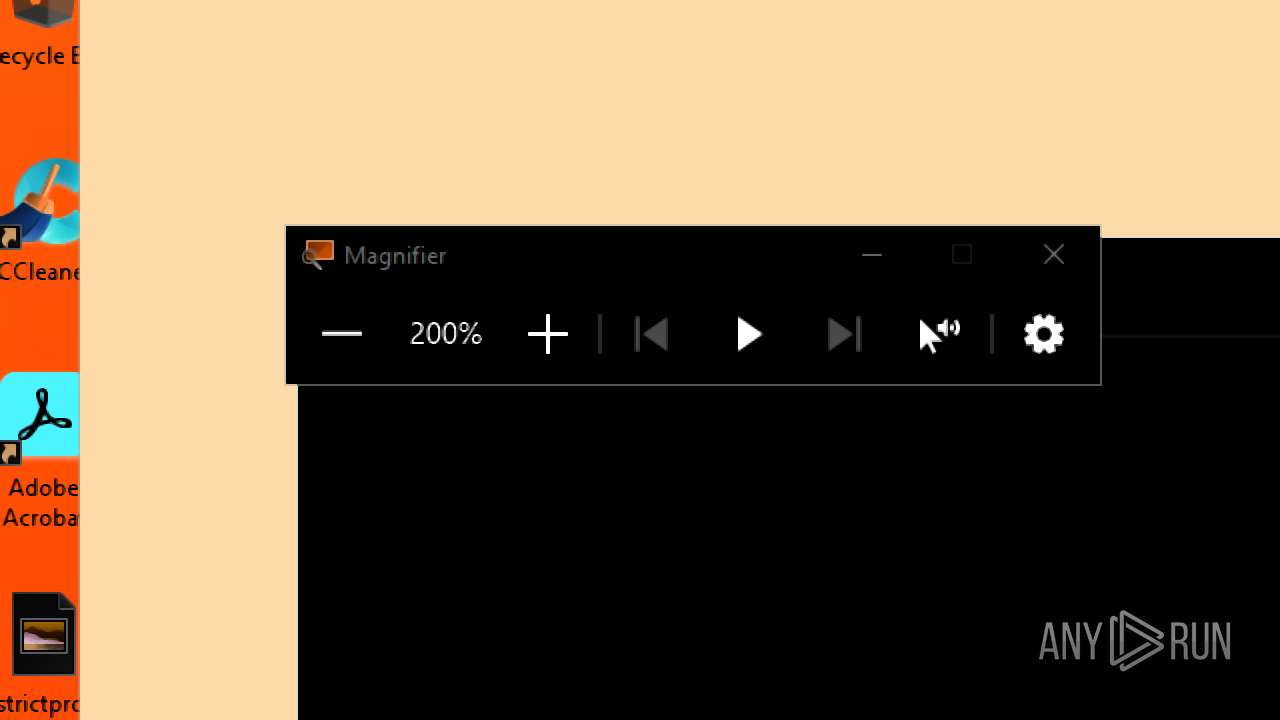
Creates files or folders in the user directory
- Magnify.exe (PID: 4236)
- unregmp2.exe (PID: 3396)
Reads security settings of Internet Explorer
- Magnify.exe (PID: 4236)
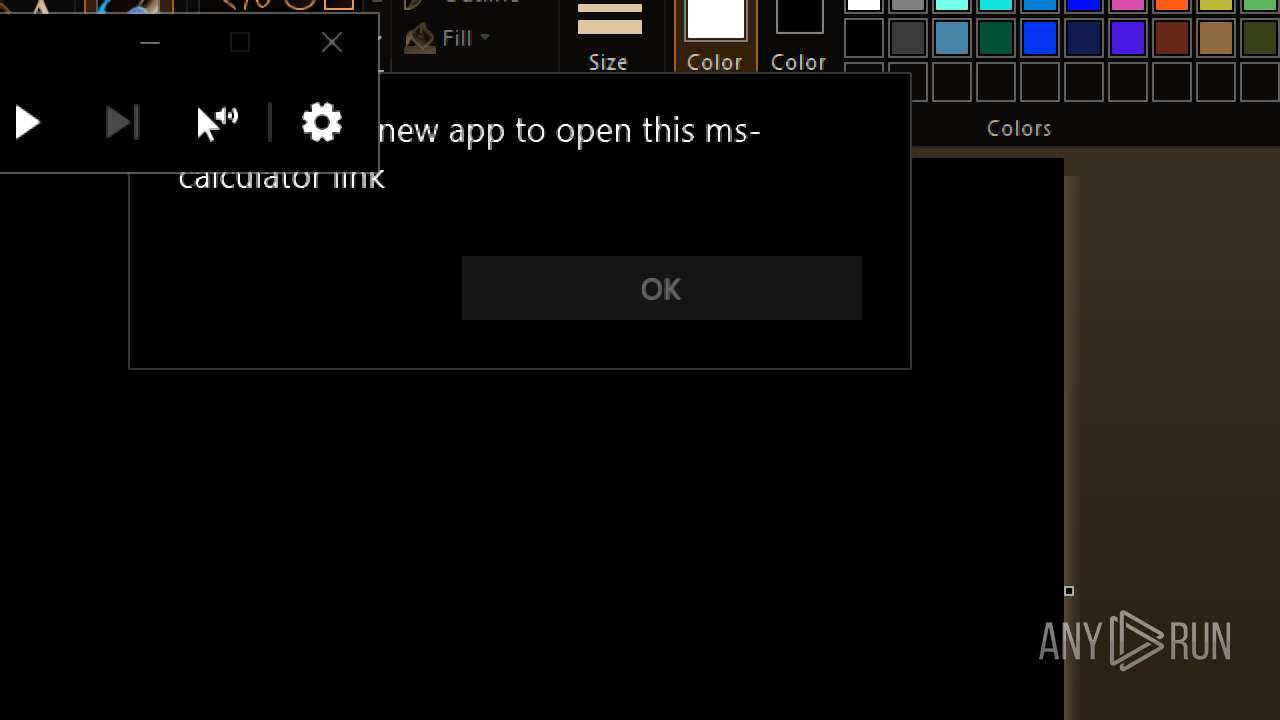
- calc.exe (PID: 6776)
- unregmp2.exe (PID: 3576)
- OpenWith.exe (PID: 3844)
- calc.exe (PID: 5908)
- OpenWith.exe (PID: 4156)
- calc.exe (PID: 316)
- OpenWith.exe (PID: 1332)
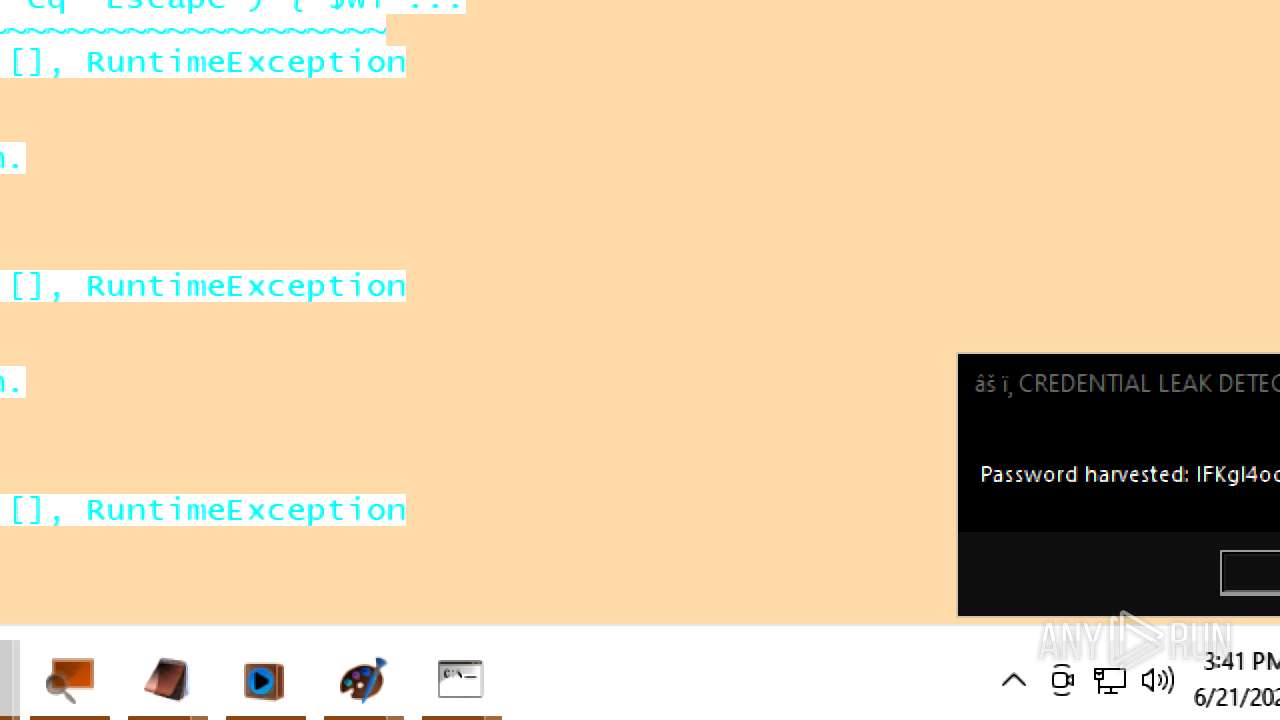
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3832)
Checks supported languages
- wmplayer.exe (PID: 5628)
- setup_wm.exe (PID: 6688)
- setup_wm.exe (PID: 6012)
- wmplayer.exe (PID: 4892)
- setup_wm.exe (PID: 5116)
- wmplayer.exe (PID: 5232)
- wmplayer.exe (PID: 6960)
- setup_wm.exe (PID: 6896)
- wmplayer.exe (PID: 4172)
- setup_wm.exe (PID: 5252)
- wmplayer.exe (PID: 2668)
- setup_wm.exe (PID: 1200)
- setup_wm.exe (PID: 1036)
- wmplayer.exe (PID: 4312)
- setup_wm.exe (PID: 5904)
- wmplayer.exe (PID: 6900)
- setup_wm.exe (PID: 2032)
- wmplayer.exe (PID: 4752)
- wmplayer.exe (PID: 5552)
- setup_wm.exe (PID: 4528)
- csc.exe (PID: 10860)
- cvtres.exe (PID: 10924)
Reads the computer name
- wmplayer.exe (PID: 5628)
- setup_wm.exe (PID: 6688)
- wmplayer.exe (PID: 5232)
- setup_wm.exe (PID: 6012)
- wmplayer.exe (PID: 4892)
- setup_wm.exe (PID: 5116)
- wmplayer.exe (PID: 4172)
- wmplayer.exe (PID: 6960)
- setup_wm.exe (PID: 6896)
- setup_wm.exe (PID: 5252)
- setup_wm.exe (PID: 1200)
- setup_wm.exe (PID: 1036)
- wmplayer.exe (PID: 5552)
- wmplayer.exe (PID: 2668)
- wmplayer.exe (PID: 4312)
- setup_wm.exe (PID: 5904)
- wmplayer.exe (PID: 6900)
- setup_wm.exe (PID: 2032)
- wmplayer.exe (PID: 4752)
- setup_wm.exe (PID: 4528)
Gets data length (POWERSHELL)
- powershell.exe (PID: 3832)
Process checks computer location settings
- wmplayer.exe (PID: 5628)
- setup_wm.exe (PID: 6688)
- wmplayer.exe (PID: 5232)
- wmplayer.exe (PID: 4892)
- wmplayer.exe (PID: 6960)
- wmplayer.exe (PID: 4172)
- wmplayer.exe (PID: 2668)
- wmplayer.exe (PID: 4312)
- wmplayer.exe (PID: 5552)
- wmplayer.exe (PID: 6900)
- wmplayer.exe (PID: 4752)
Create files in a temporary directory
- unregmp2.exe (PID: 3576)
- setup_wm.exe (PID: 6688)
- csc.exe (PID: 10860)
- cvtres.exe (PID: 10924)
Checks proxy server information
- setup_wm.exe (PID: 6688)
- powershell.exe (PID: 3832)
- slui.exe (PID: 6148)
Disables trace logs
- powershell.exe (PID: 3832)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 3832)
Reads Internet Explorer settings
- powershell.exe (PID: 3832)
Reads the machine GUID from the registry
- csc.exe (PID: 10860)
Reads the software policy settings
- slui.exe (PID: 6148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
241
Monitored processes
106
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\WINDOWS\system32\calc.exe" | C:\Windows\System32\calc.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Calculator Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 620 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1036 | "C:\Program Files (x86)\Windows Media Player\setup_wm.exe" /RunOnce:"C:\Program Files (x86)\Windows Media Player\wmplayer.exe" "C:\Users\admin\Desktop\Unknown_file_6.wav" | C:\Program Files (x86)\Windows Media Player\setup_wm.exe | — | wmplayer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Media Configuration Utility Exit code: 0 Version: 12.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1200 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{60A90A2F-858D-42AF-8929-82BE9D99E8A1} | C:\Windows\SysWOW64\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1200 | "C:\Program Files (x86)\Windows Media Player\setup_wm.exe" /RunOnce:"C:\Program Files (x86)\Windows Media Player\wmplayer.exe" "C:\Users\admin\Desktop\Unknown_file_5.wav" | C:\Program Files (x86)\Windows Media Player\setup_wm.exe | — | wmplayer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Media Configuration Utility Exit code: 0 Version: 12.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1332 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1520 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1660 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2032 | "C:\Program Files (x86)\Windows Media Player\setup_wm.exe" /RunOnce:"C:\Program Files (x86)\Windows Media Player\wmplayer.exe" "C:\Users\admin\Desktop\Unknown_file_8.wav" | C:\Program Files (x86)\Windows Media Player\setup_wm.exe | — | wmplayer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Media Configuration Utility Exit code: 0 Version: 12.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
163 524
Read events
163 032
Write events
486
Delete events
6
Modification events
| (PID) Process: | (4236) Magnify.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AccessibilityTemp |
| Operation: | write | Name: | magnifierpane |
Value: 3 | |||
| (PID) Process: | (4236) Magnify.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Speech_OneCore\Isolated\EU1fm5Ah6wU5J3yMy_IFWU4dyxYBJx7YBhneEUVpyAU\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\Voices\Tokens\MSTTS_V110_enUS_ZiraM |
| Operation: | write | Name: | LangDataPath |
Value: %windir%\Speech_OneCore\Engines\TTS\en-US\MSTTSLocenUS.dat | |||
| (PID) Process: | (4236) Magnify.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Speech_OneCore\Isolated\EU1fm5Ah6wU5J3yMy_IFWU4dyxYBJx7YBhneEUVpyAU\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\Voices\Tokens\MSTTS_V110_enUS_ZiraM |
| Operation: | write | Name: | VoicePath |
Value: %windir%\Speech_OneCore\Engines\TTS\en-US\M1033Zira | |||
| (PID) Process: | (4236) Magnify.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Speech_OneCore\Isolated\EU1fm5Ah6wU5J3yMy_IFWU4dyxYBJx7YBhneEUVpyAU\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\Voices\Tokens\MSTTS_V110_enUS_ZiraM |
| Operation: | write | Name: | 409 |
Value: Microsoft Zira - English (United States) | |||
| (PID) Process: | (4236) Magnify.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Speech_OneCore\Isolated\EU1fm5Ah6wU5J3yMy_IFWU4dyxYBJx7YBhneEUVpyAU\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\Voices\Tokens\MSTTS_V110_enUS_ZiraM |
| Operation: | write | Name: | CLSID |
Value: {179F3D56-1B0B-42B2-A962-59B7EF59FE1B} | |||
| (PID) Process: | (4236) Magnify.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Speech_OneCore\Isolated\EU1fm5Ah6wU5J3yMy_IFWU4dyxYBJx7YBhneEUVpyAU\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\Voices\Tokens\MSTTS_V110_enUS_ZiraM\Attributes |
| Operation: | write | Name: | Version |
Value: 11.0 | |||
| (PID) Process: | (4236) Magnify.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Speech_OneCore\Isolated\EU1fm5Ah6wU5J3yMy_IFWU4dyxYBJx7YBhneEUVpyAU\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\Voices\Tokens\MSTTS_V110_enUS_ZiraM\Attributes |
| Operation: | write | Name: | Language |
Value: 409 | |||
| (PID) Process: | (4236) Magnify.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Speech_OneCore\Isolated\EU1fm5Ah6wU5J3yMy_IFWU4dyxYBJx7YBhneEUVpyAU\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\Voices\Tokens\MSTTS_V110_enUS_ZiraM\Attributes |
| Operation: | write | Name: | Gender |
Value: Female | |||
| (PID) Process: | (4236) Magnify.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Speech_OneCore\Isolated\EU1fm5Ah6wU5J3yMy_IFWU4dyxYBJx7YBhneEUVpyAU\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\Voices\Tokens\MSTTS_V110_enUS_ZiraM\Attributes |
| Operation: | write | Name: | Age |
Value: Adult | |||
| (PID) Process: | (4236) Magnify.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Speech_OneCore\Isolated\EU1fm5Ah6wU5J3yMy_IFWU4dyxYBJx7YBhneEUVpyAU\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\Voices\Tokens\MSTTS_V110_enUS_ZiraM\Attributes |
| Operation: | write | Name: | DataVersion |
Value: 11.0.2013.1022 | |||
Executable files
1
Suspicious files
74
Text files
72
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3832 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2peo5ojm.y0n.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3832 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF176a14.TMP | binary | |
MD5:00A03B286E6E0EBFF8D9C492365D5EC2 | SHA256:4DBFC417D053BA6867308671F1C61F4DCAFC61F058D4044DB532DA6D3BDE3615 | |||
| 3832 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\IBJK73F6IR8G7Y4K5XKW.temp | binary | |
MD5:6F22749034224BD7EBA3611EDA894E2E | SHA256:E6842B565CBAE7C24243AC67CB0F9357182ED0927E0F87B6EC721D5E4EBD8AAF | |||
| 4836 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1T7EFNWMKB80Q1XJSFO5.temp | binary | |
MD5:BA6412A12B52F40A2351AE493AB7660B | SHA256:0D7516391A4E25F0863E7130242B969DC04BB2706DF91AB7C74393A0E0A4CEC6 | |||
| 3396 | unregmp2.exe | C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNS.DTD | xml | |
MD5:90BE2701C8112BEBC6BD58A7DE19846E | SHA256:644FBCDC20086E16D57F31C5BAD98BE68D02B1C061938D2F5F91CBE88C871FBF | |||
| 3832 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4kitcreh.sqs.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3396 | unregmp2.exe | C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNS.XML | text | |
MD5:5433EAB10C6B5C6D55B7CBD302426A39 | SHA256:23DBF7014E99E93AF5F2760F18EE1370274F06A453145C8D539B66D798DAD131 | |||
| 3396 | unregmp2.exe | C:\Users\admin\AppData\Local\Microsoft\Media Player\LocalMLS_3.wmdb | binary | |
MD5:75E180213F09400C01692A0F23CF23FA | SHA256:2954408624C8F9148235B057443FC5A7CA725CB161E8E24F819E4FF5265941F0 | |||
| 3396 | unregmp2.exe | C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNS.XML.bak | text | |
MD5:7050D5AE8ACFBE560FA11073FEF8185D | SHA256:CB87767C4A384C24E4A0F88455F59101B1AE7B4FB8DE8A5ADB4136C5F7EE545B | |||
| 4836 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:BA6412A12B52F40A2351AE493AB7660B | SHA256:0D7516391A4E25F0863E7130242B969DC04BB2706DF91AB7C74393A0E0A4CEC6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
43
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 184.24.77.11:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 40.126.32.72:443 | https://login.live.com/RST2.srf | unknown | xml | 11.0 Kb | whitelisted |
— | — | GET | 304 | 4.245.163.56:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
— | — | GET | 200 | 4.245.163.56:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | compressed | 23.9 Kb | whitelisted |
4692 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
4692 | SIHClient.exe | GET | 200 | 23.55.104.172:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
4692 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
4692 | SIHClient.exe | GET | 200 | 23.55.104.172:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
4692 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.24.77.11:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5116 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 184.24.77.11:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 184.24.77.11:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5116 | RUXIMICS.exe | 184.24.77.11:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
wmploc.dll |
| unknown |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |