| File name: | ChedotSetup_x642sdjL.exe |
| Full analysis: | https://app.any.run/tasks/e88bbacc-8b0c-475b-be45-4e856568c244 |
| Verdict: | Malicious activity |
| Analysis date: | September 23, 2021, 12:58:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | BA22FB9D80693A87E93FDD24076B454A |
| SHA1: | A96AFF68737EA54F8320E7B372D9C1A040F6739C |
| SHA256: | 511F043135CD13EFD87FD3D893E0A4AE8248A11AA3F0C5BB6F264C962D04C721 |
| SSDEEP: | 12288:G3BxPmuW7ECxjjVKlxKE/z3mqxV7W3ZKvcBt6mFw0es4xHq46RbNMUp3401g5kUR:GYEMKCqxc07MQs39RbNBIu1rBm |
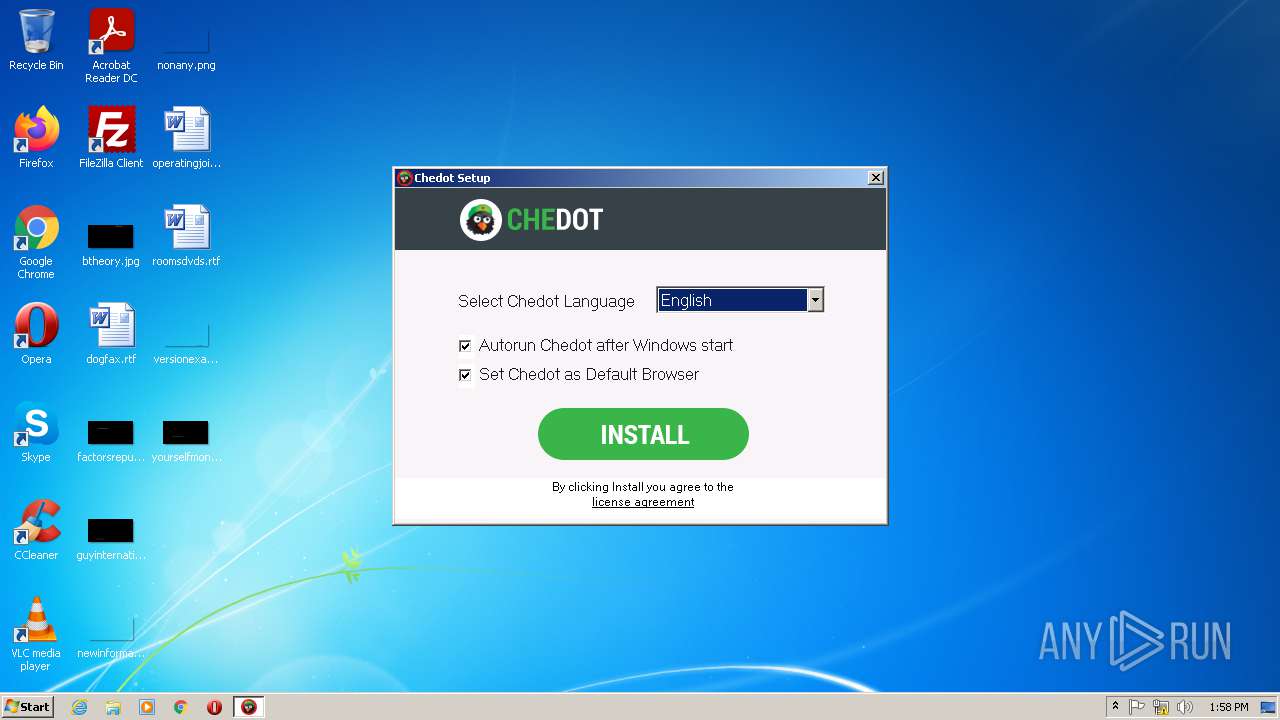
MALICIOUS
Actions looks like stealing of personal data
- ChedotSetup_x642sdjL.exe (PID: 3912)
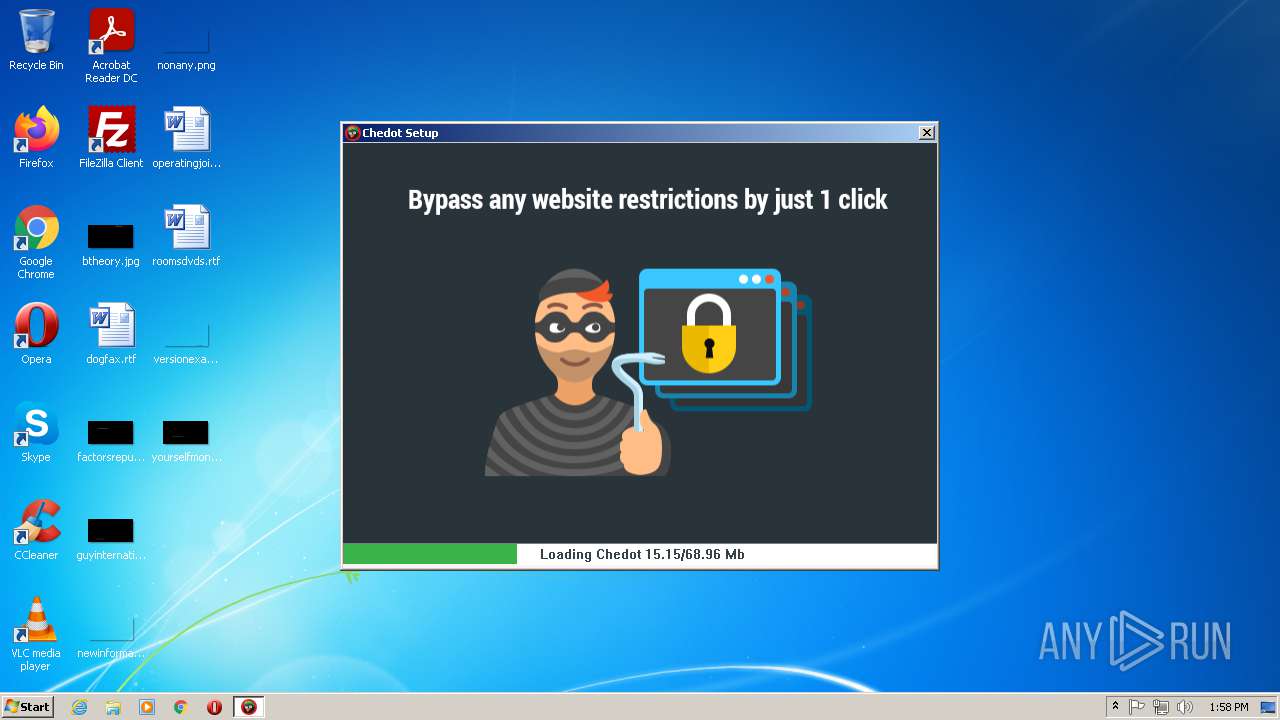
SUSPICIOUS
Reads Environment values
- ChedotSetup_x642sdjL.exe (PID: 3912)
Checks supported languages
- ChedotSetup_x642sdjL.exe (PID: 3912)
Executable content was dropped or overwritten
- ChedotSetup_x642sdjL.exe (PID: 3912)
Drops a file that was compiled in debug mode
- ChedotSetup_x642sdjL.exe (PID: 3912)
Reads the computer name
- ChedotSetup_x642sdjL.exe (PID: 3912)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| ProductVersion: | 9.3.0.0 |
|---|---|
| ProductName: | Chedot Browser |
| OriginalFileName: | chedot-setup.exe |
| LegalCopyright: | (c) Guerrilla Programming OÜ. All rights reserved. |
| InternalName: | chedot-setup.exe |
| FileVersion: | 7.1.9.0 |
| FileDescription: | Chedot Setup |
| CompanyName: | Guerrilla Programming OÜ |
| CharacterSet: | Unicode |
| LanguageCode: | Process default |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 9.3.0.0 |
| FileVersionNumber: | 7.1.9.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x3c3f3 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 591360 |
| CodeSize: | 419328 |
| LinkerVersion: | 14.16 |
| PEType: | PE32 |
| TimeStamp: | 2021:03:29 19:06:41+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-Mar-2021 17:06:41 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Guerrilla Programming OÜ |
| FileDescription: | Chedot Setup |
| FileVersion: | 7.1.9.0 |
| InternalName: | chedot-setup.exe |
| LegalCopyright: | (c) Guerrilla Programming OÜ. All rights reserved. |
| OriginalFilename: | chedot-setup.exe |
| ProductName: | Chedot Browser |
| ProductVersion: | 9.3.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 29-Mar-2021 17:06:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000664F9 | 0x00066600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57917 |
.rdata | 0x00068000 | 0x00021398 | 0x00021400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.08906 |
.data | 0x0008A000 | 0x0000607C | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43903 |
.rsrc | 0x00091000 | 0x00061738 | 0x00061800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.04819 |
.reloc | 0x000F3000 | 0x000076A0 | 0x00007800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.55435 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.18673 | 2318 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.93376 | 218 | UNKNOWN | Russian - Russia | RT_STRING |
3 | 3.68494 | 488 | UNKNOWN | Process Default Language | RT_ICON |
4 | 3.39729 | 296 | UNKNOWN | Process Default Language | RT_ICON |
5 | 4.8938 | 3752 | UNKNOWN | Process Default Language | RT_ICON |
6 | 5.49467 | 2216 | UNKNOWN | Process Default Language | RT_ICON |
7 | 5.46419 | 1736 | UNKNOWN | Process Default Language | RT_ICON |
8 | 6.33137 | 1384 | UNKNOWN | Process Default Language | RT_ICON |
9 | 7.96652 | 30418 | UNKNOWN | Process Default Language | RT_ICON |
10 | 4.97082 | 9640 | UNKNOWN | Process Default Language | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEACC.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
WININET.dll |
Total processes
38
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1616 | "C:\Users\admin\AppData\Local\Temp\ChedotSetup_x642sdjL.exe" | C:\Users\admin\AppData\Local\Temp\ChedotSetup_x642sdjL.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Guerrilla Programming O� Integrity Level: MEDIUM Description: Chedot Setup Exit code: 3221226540 Version: 7.1.9.0 Modules
| |||||||||||||||
| 3912 | "C:\Users\admin\AppData\Local\Temp\ChedotSetup_x642sdjL.exe" | C:\Users\admin\AppData\Local\Temp\ChedotSetup_x642sdjL.exe | Explorer.EXE | ||||||||||||
User: admin Company: Guerrilla Programming O� Integrity Level: HIGH Description: Chedot Setup Exit code: 0 Version: 7.1.9.0 Modules
| |||||||||||||||
Total events
402
Read events
382
Write events
20
Delete events
0
Modification events
| (PID) Process: | (3912) ChedotSetup_x642sdjL.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3912) ChedotSetup_x642sdjL.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000042010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3912) ChedotSetup_x642sdjL.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3912) ChedotSetup_x642sdjL.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3912) ChedotSetup_x642sdjL.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3912) ChedotSetup_x642sdjL.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3912) ChedotSetup_x642sdjL.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3912) ChedotSetup_x642sdjL.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3912) ChedotSetup_x642sdjL.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3912) ChedotSetup_x642sdjL.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{58AF627C-B2EC-4189-8EEA-0267C97F3E7F} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
Executable files
1
Suspicious files
0
Text files
7
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3912 | ChedotSetup_x642sdjL.exe | C:\Users\admin\AppData\Local\Temp\chedot_33fa7ab9ac36fd1588c1e886b82d5079\chrome.packed.7z | — | |
MD5:— | SHA256:— | |||
| 3912 | ChedotSetup_x642sdjL.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\chrome.packed[1].7z | — | |
MD5:— | SHA256:— | |||
| 3912 | ChedotSetup_x642sdjL.exe | C:\Users\admin\AppData\Local\Temp\chedot_33fa7ab9ac36fd1588c1e886b82d5079\1.png | gmc | |
MD5:278916B173C12D2F6872A6640A7ED380 | SHA256:18903744E31FD8C91D0A53463839676FFF773C6D79793108813A9899466BDD6E | |||
| 3912 | ChedotSetup_x642sdjL.exe | C:\Users\admin\AppData\Local\Temp\chedot_33fa7ab9ac36fd1588c1e886b82d5079\4.png | gmc | |
MD5:FA6C7D80A9FC6BFB04904C53D12330C9 | SHA256:A89AAB19C03980161958EEB5E8F93624456070B7759BAC3AE2D8AA836CA906F1 | |||
| 3912 | ChedotSetup_x642sdjL.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\5[1].png | image | |
MD5:7DFC78357F288C69BD93E76CCE683E4A | SHA256:168171A20EBA3A6F2853AF6149EC83EB55C89E74496FC2CA048D0810E2A04F39 | |||
| 3912 | ChedotSetup_x642sdjL.exe | C:\Users\admin\AppData\Local\Temp\chedot_33fa7ab9ac36fd1588c1e886b82d5079\2.png | gmc | |
MD5:7B0A1466948DD146506A56E0979C6F34 | SHA256:01D547E7B728707E5564C10E430E490C9A5B0F7CE278A6450357A0F7202440AF | |||
| 3912 | ChedotSetup_x642sdjL.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\1[1].png | image | |
MD5:6F1DC29BF7F1008B40E96D2E93D5E838 | SHA256:D0146947C0A7284E3E1AB55B0327B1938AAED0F563DF53AE7ADE98FCBBF1D4D6 | |||
| 3912 | ChedotSetup_x642sdjL.exe | C:\Users\admin\AppData\Local\Temp\chedot_33fa7ab9ac36fd1588c1e886b82d5079\5.png | gmc | |
MD5:21F20B7A11661640CA71C6A94DFC8F4E | SHA256:C8850900853D581E7CDD3AB34D1E8067021CDE203B5DE06787A466AE3973B0DC | |||
| 3912 | ChedotSetup_x642sdjL.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\2[1].png | image | |
MD5:1BEA9FB247D7C56E40A1C256CEABC371 | SHA256:B5C65D9942EF923AC9E44F7A3702D6948AAA84E46DFA7F294C0BCB093A76B6E9 | |||
| 3912 | ChedotSetup_x642sdjL.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\4[1].png | image | |
MD5:06E88B7EA8FF6F4360EA81F5C5883811 | SHA256:746D62FCA7432E4CDF14B8554B4A7182663DD8505B601FCF21F0FC6C7775207E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
15
DNS requests
4
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3912 | ChedotSetup_x642sdjL.exe | POST | 200 | 88.99.93.38:80 | http://st.chedot-browser.com/data_inst | DE | — | — | suspicious |
3912 | ChedotSetup_x642sdjL.exe | POST | 200 | 88.99.93.38:80 | http://st.chedot-browser.com/data_inst | DE | — | — | suspicious |
3912 | ChedotSetup_x642sdjL.exe | POST | 200 | 88.99.93.38:80 | http://st.chedot-browser.com/data_inst | DE | — | — | suspicious |
3912 | ChedotSetup_x642sdjL.exe | POST | 200 | 88.99.93.38:80 | http://st.chedot-browser.com/data_inst | DE | — | — | suspicious |
3912 | ChedotSetup_x642sdjL.exe | POST | 200 | 88.99.93.38:80 | http://st.chedot-browser.com/data_inst | DE | — | — | suspicious |
3912 | ChedotSetup_x642sdjL.exe | POST | 200 | 88.99.93.38:80 | http://st.chedot-browser.com/data_inst | DE | — | — | suspicious |
3912 | ChedotSetup_x642sdjL.exe | POST | 200 | 88.99.93.38:80 | http://st.chedot-browser.com/data_inst | DE | — | — | suspicious |
3912 | ChedotSetup_x642sdjL.exe | GET | 200 | 138.201.189.46:80 | http://download.chedot-browser.com/releases/banners/v2/banners_en/1.png | DE | image | 12.3 Kb | suspicious |
3912 | ChedotSetup_x642sdjL.exe | GET | 200 | 78.47.218.103:80 | http://chedot-browser.com/latest-version/ | DE | text | 41 b | suspicious |
3912 | ChedotSetup_x642sdjL.exe | GET | 200 | 138.201.189.46:80 | http://download.chedot-browser.com/releases/banners/v2/banners_en/3.png | DE | image | 22.6 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3912 | ChedotSetup_x642sdjL.exe | 88.99.93.38:80 | st.chedot-browser.com | Hetzner Online GmbH | DE | suspicious |
3912 | ChedotSetup_x642sdjL.exe | 138.201.189.46:80 | download.chedot-browser.com | Hetzner Online GmbH | DE | suspicious |
3912 | ChedotSetup_x642sdjL.exe | 78.47.218.103:80 | chedot-browser.com | Hetzner Online GmbH | DE | suspicious |
3912 | ChedotSetup_x642sdjL.exe | 138.201.189.46:21 | download.chedot-browser.com | Hetzner Online GmbH | DE | suspicious |
3912 | ChedotSetup_x642sdjL.exe | 138.201.189.46:47022 | download.chedot-browser.com | Hetzner Online GmbH | DE | suspicious |
— | — | 138.201.189.46:28623 | download.chedot-browser.com | Hetzner Online GmbH | DE | suspicious |
— | — | 138.201.189.46:15505 | download.chedot-browser.com | Hetzner Online GmbH | DE | suspicious |
3912 | ChedotSetup_x642sdjL.exe | 138.201.189.46:23310 | download.chedot-browser.com | Hetzner Online GmbH | DE | suspicious |
3912 | ChedotSetup_x642sdjL.exe | 138.201.189.46:18732 | download.chedot-browser.com | Hetzner Online GmbH | DE | suspicious |
3912 | ChedotSetup_x642sdjL.exe | 138.201.189.46:60468 | download.chedot-browser.com | Hetzner Online GmbH | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
st.chedot-browser.com |
| suspicious |
chedot-browser.com |
| suspicious |
download.chedot-browser.com |
| suspicious |
download.chedot.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3912 | ChedotSetup_x642sdjL.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3912 | ChedotSetup_x642sdjL.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3912 | ChedotSetup_x642sdjL.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3912 | ChedotSetup_x642sdjL.exe | Potential Corporate Privacy Violation | ET INFO .exe File requested over FTP |
3912 | ChedotSetup_x642sdjL.exe | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download |
3912 | ChedotSetup_x642sdjL.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |