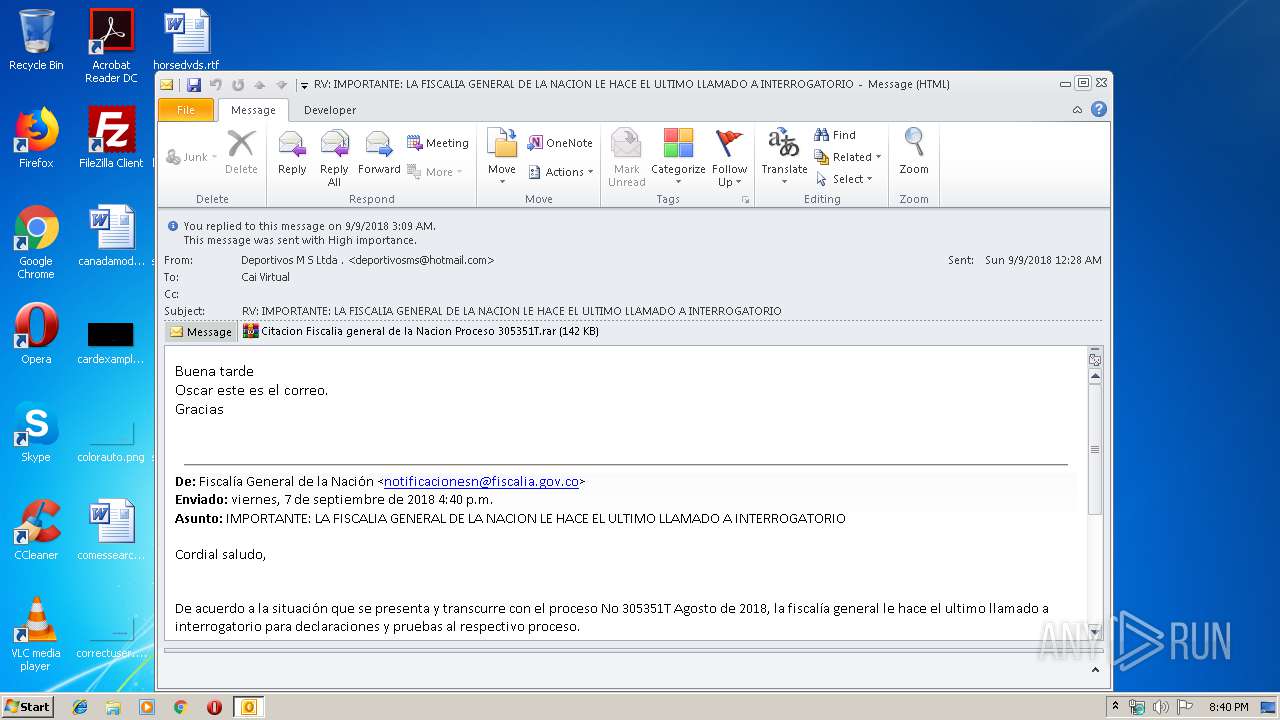
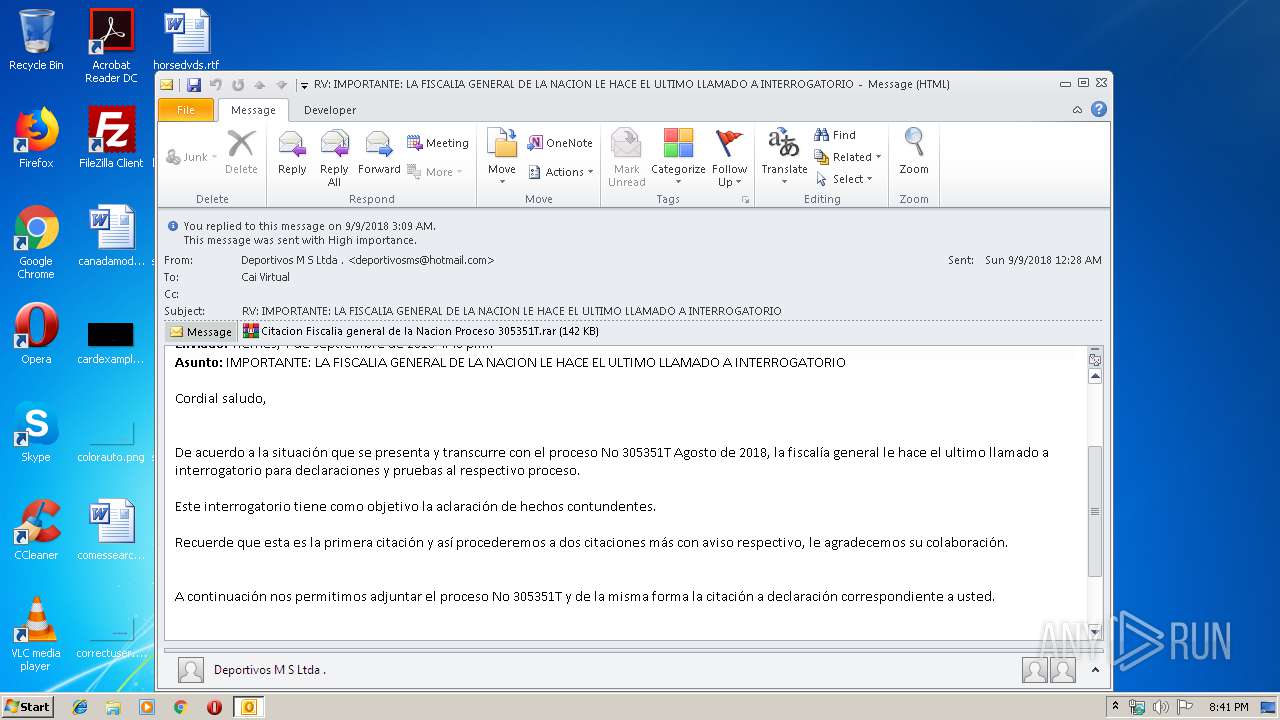
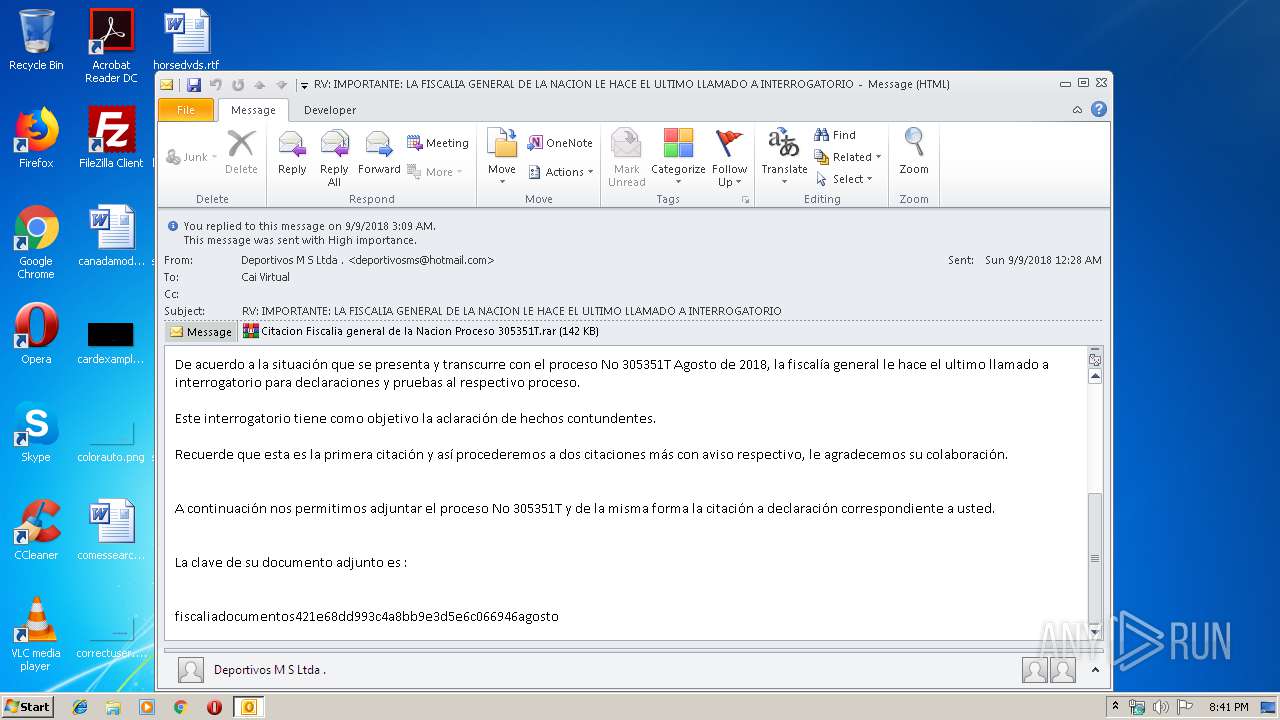
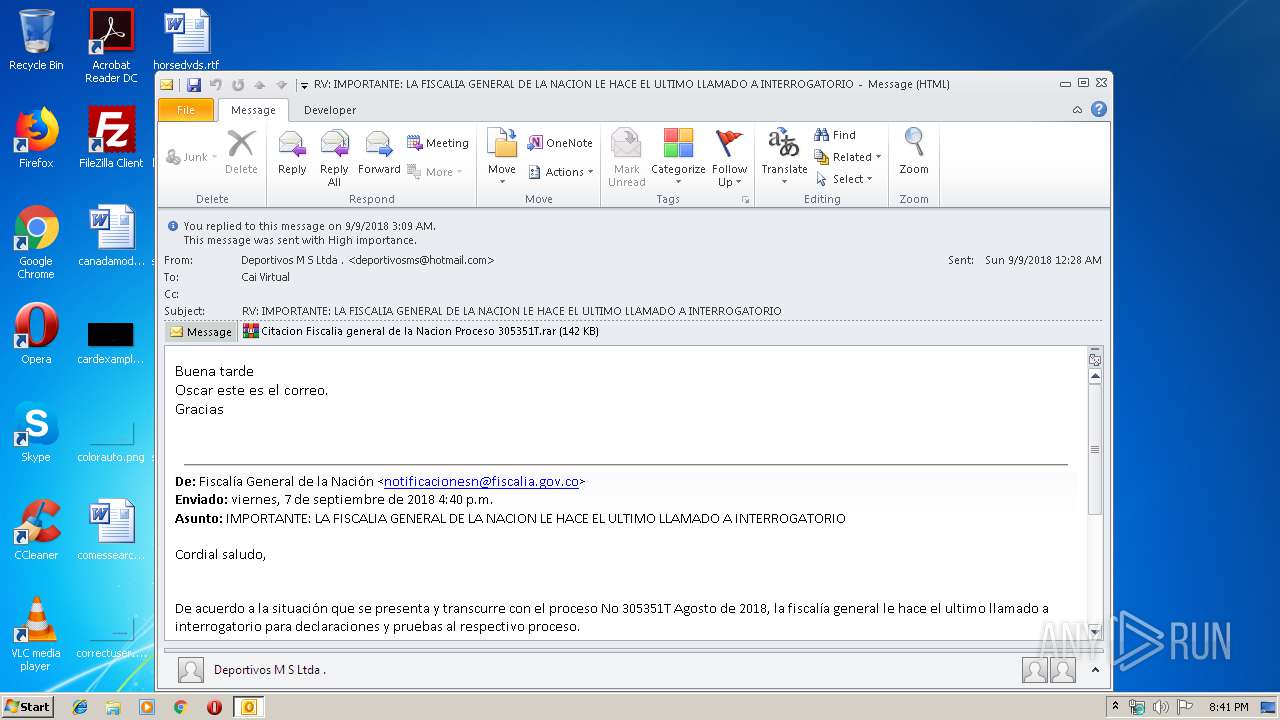
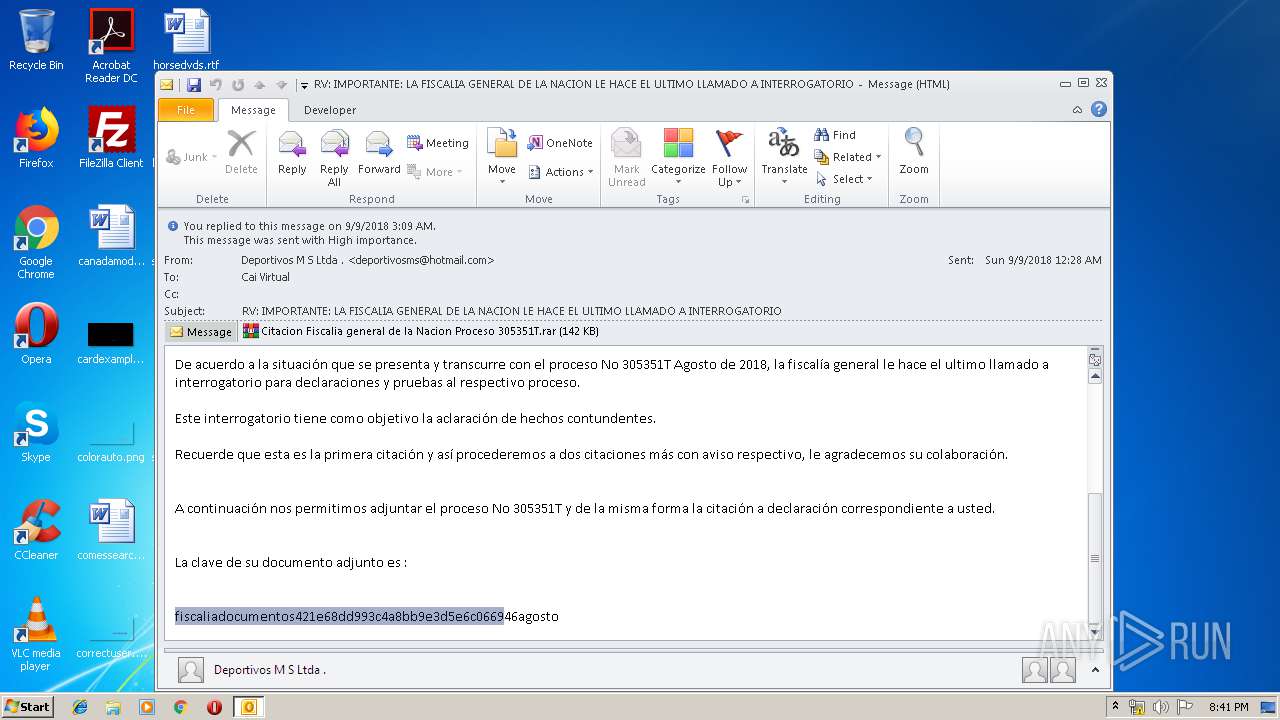
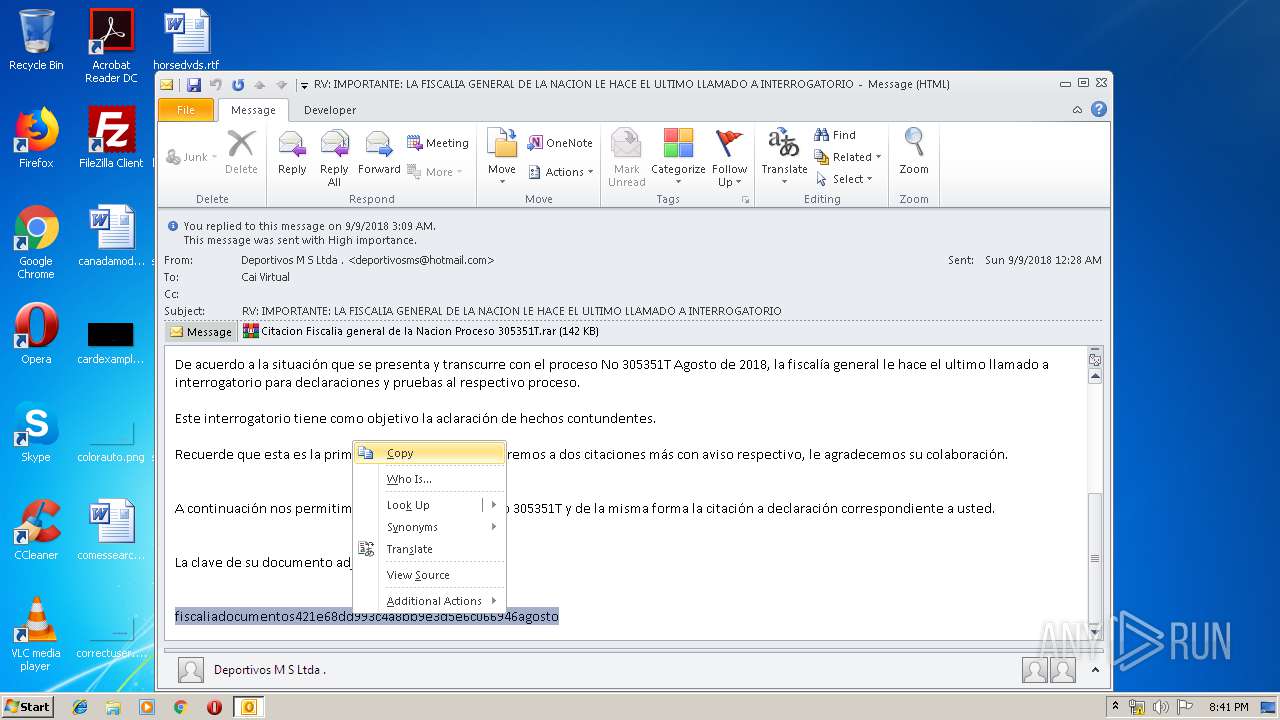
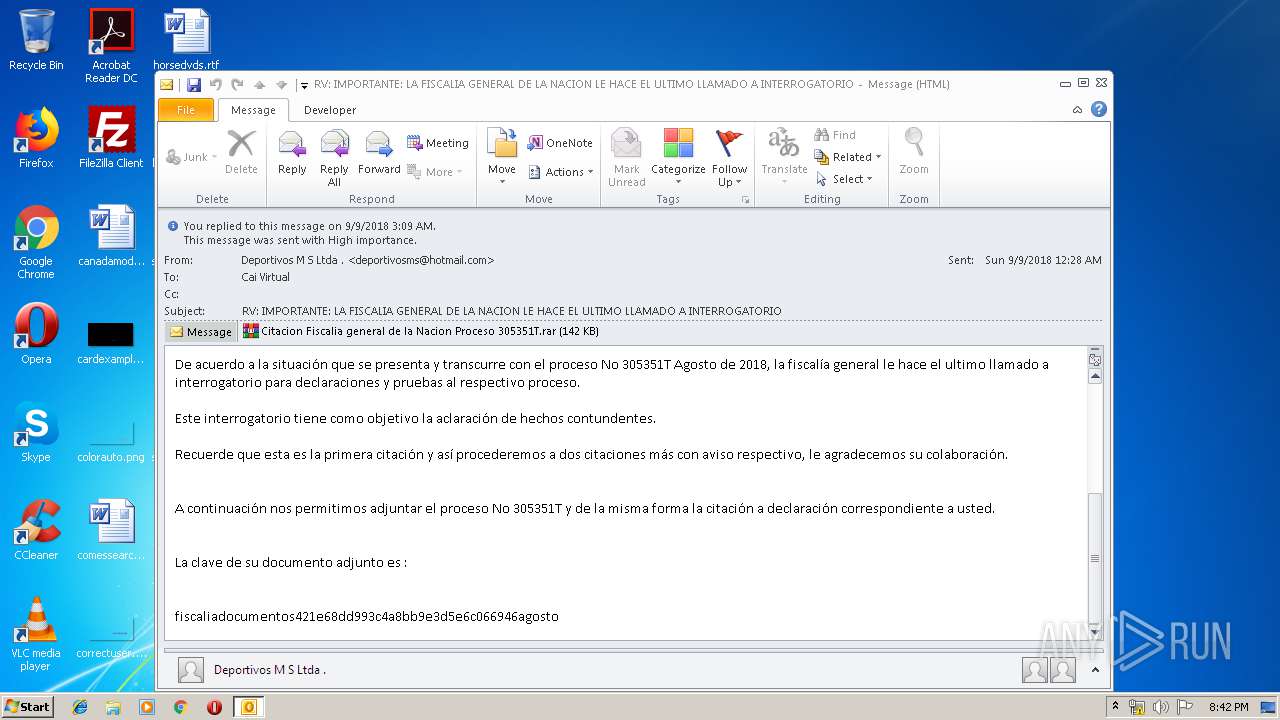
| File name: | RV IMPORTANTE LA FISCALIA GENERAL DE LA NACION LE HACE EL ULTIMO LLAMADO A INTERROGATORIO.msg |
| Full analysis: | https://app.any.run/tasks/96d1e868-35b0-43ad-8fcc-8cf5800e6ec5 |
| Verdict: | Malicious activity |
| Analysis date: | October 09, 2019, 19:40:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 0A454452DCBD5E58AC5C33A2106693DC |
| SHA1: | E0D9A916EAE66CD750E74EF0343C8EB2F228BB2C |
| SHA256: | 511ED8C5EAF4E7567827D3994FA4B194E34EF4B7BAA4E6CEF524D95BF8786D03 |
| SSDEEP: | 3072:wIOdNVMZnybfkb4Xaa46W7p2mtxqoHmjwtEytYOvKgy7BT12F:ienp4X5462dBGjwtDYelAM |
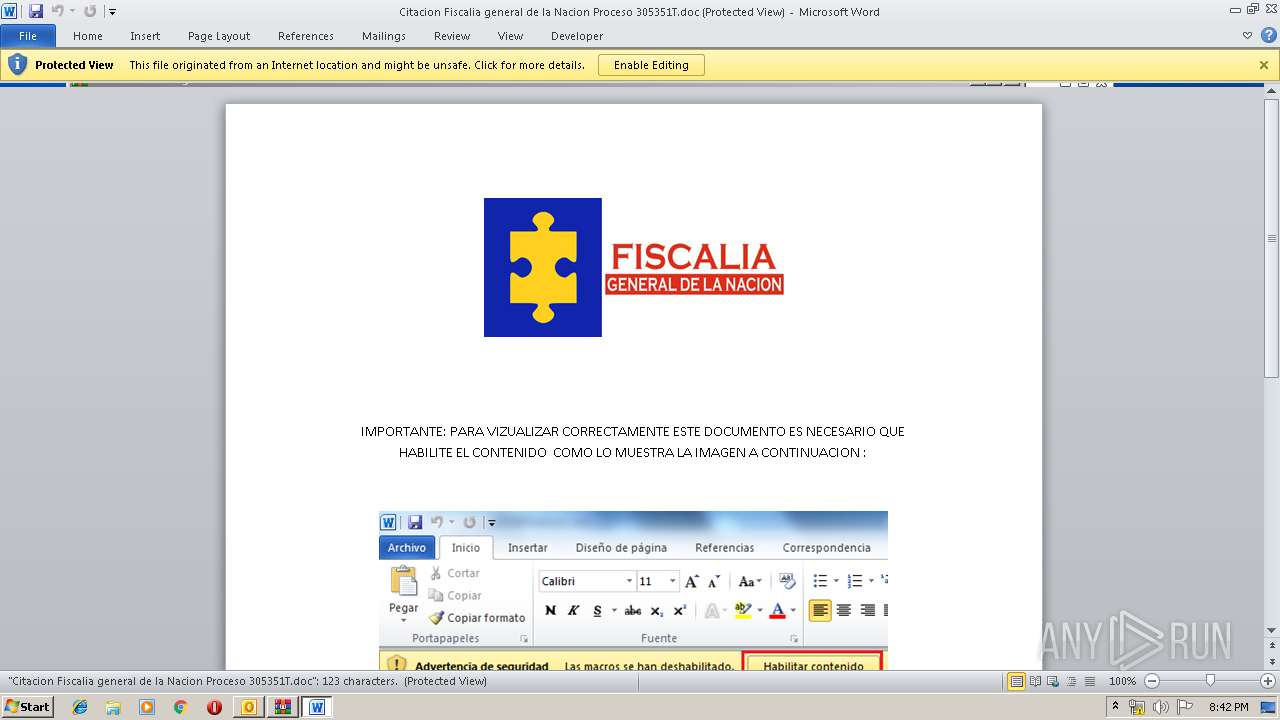
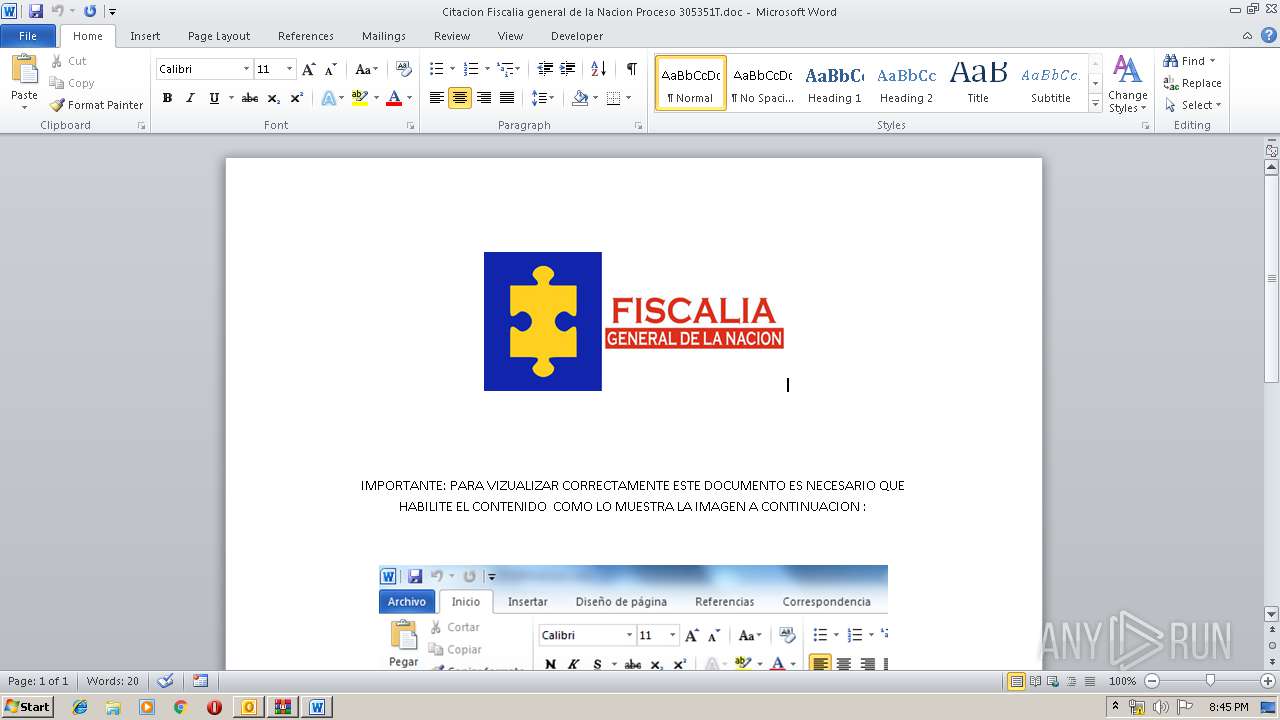
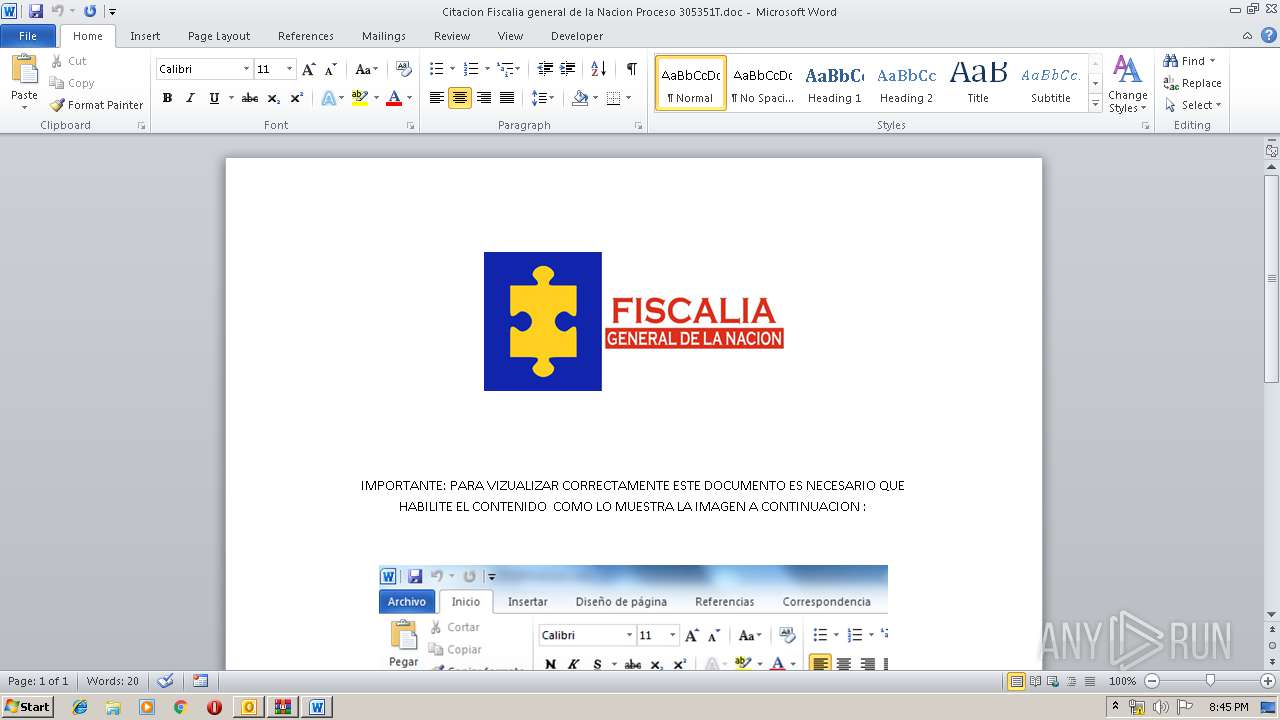
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3184)
Loads the Task Scheduler COM API
- WINWORD.EXE (PID: 2856)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 3184)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3184)
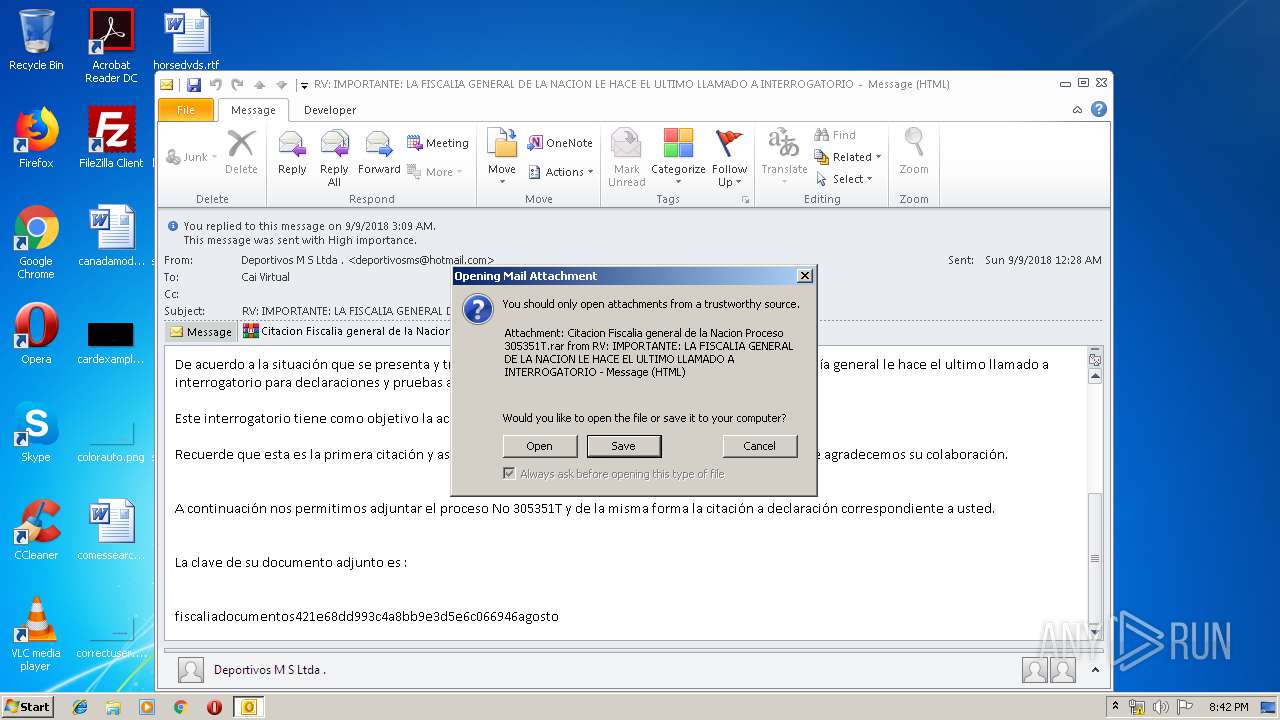
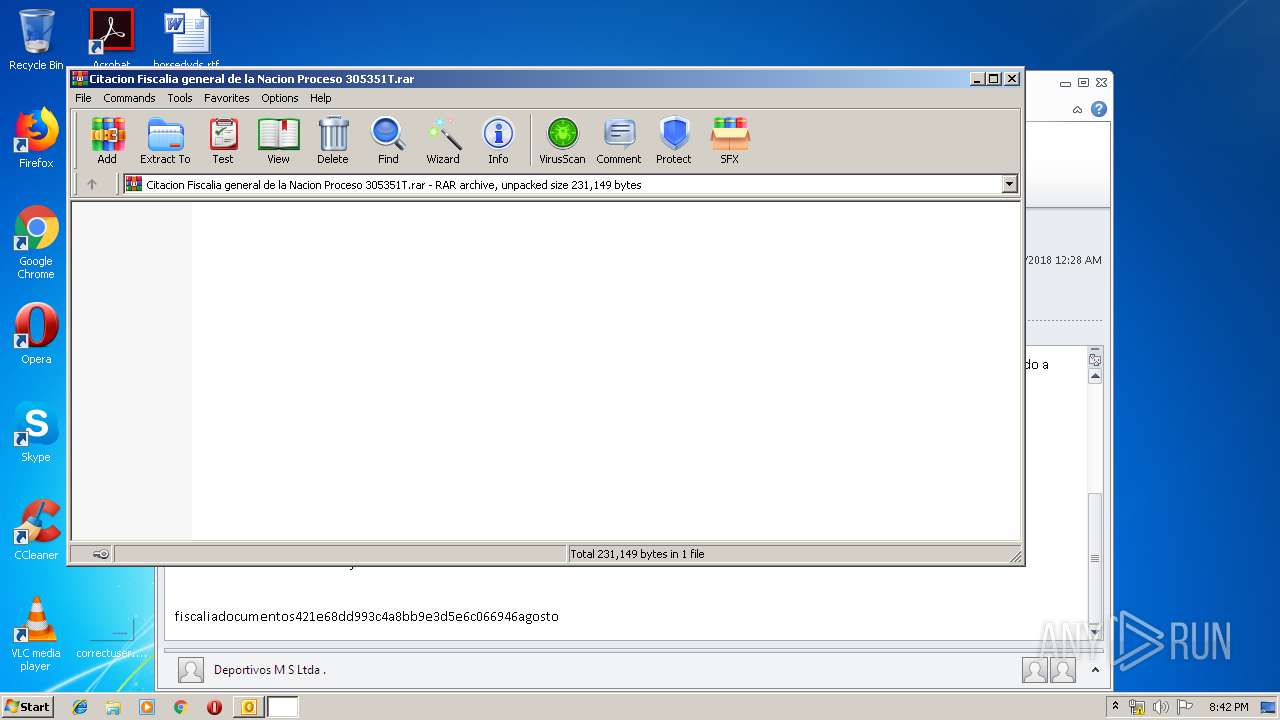
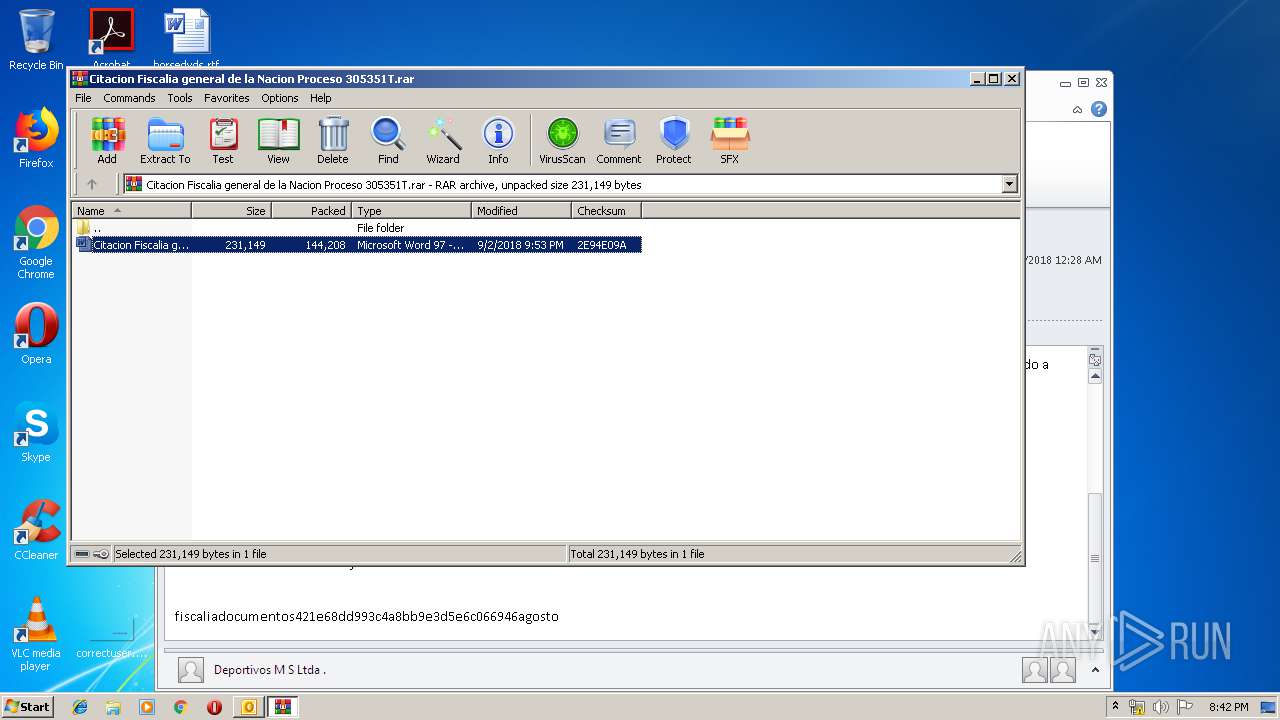
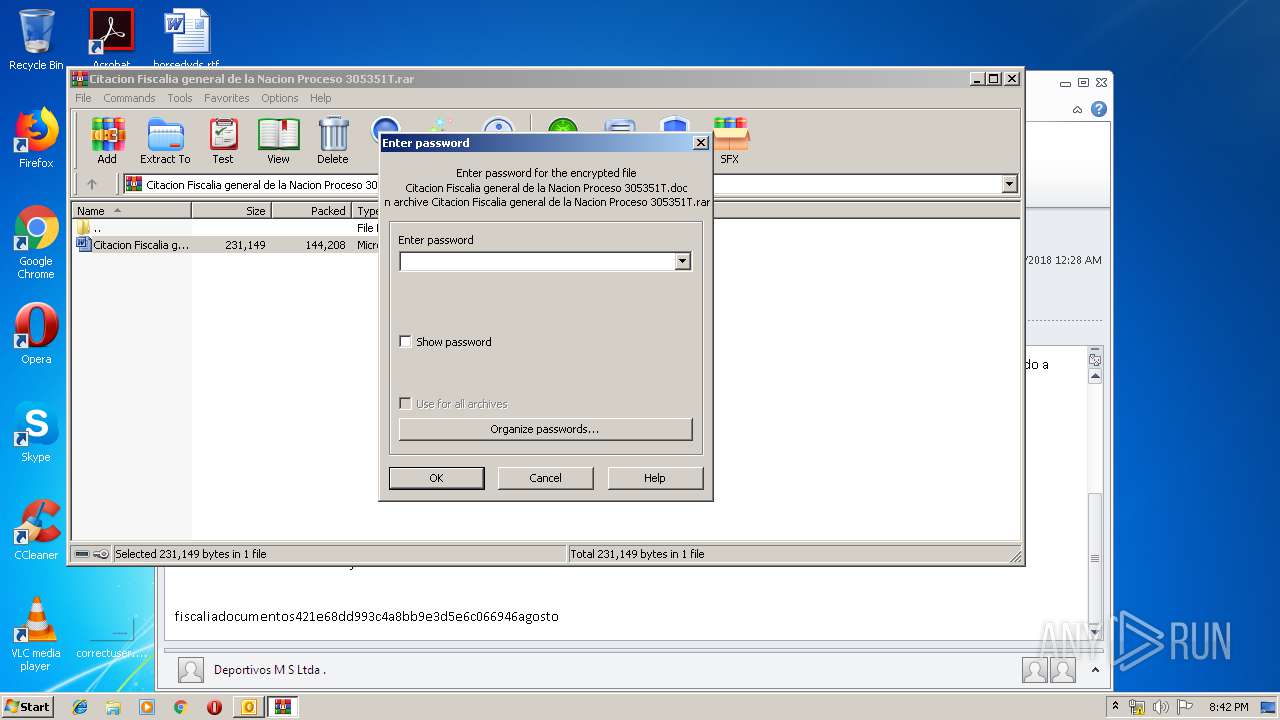
Starts Microsoft Office Application
- WinRAR.exe (PID: 2964)
- WINWORD.EXE (PID: 2856)
Application launched itself
- WINWORD.EXE (PID: 2856)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3184)
- WINWORD.EXE (PID: 2856)
- WINWORD.EXE (PID: 3352)
Creates files in the user directory
- WINWORD.EXE (PID: 2856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
38
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2856 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb2964.13820\Citacion Fiscalia general de la Nacion Proceso 305351T.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2964 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\88TKN8O3\Citacion Fiscalia general de la Nacion Proceso 305351T.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3184 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\RV IMPORTANTE LA FISCALIA GENERAL DE LA NACION LE HACE EL ULTIMO LLAMADO A INTERROGATORIO.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3352 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
3 743
Read events
2 958
Write events
746
Delete events
39
Modification events
| (PID) Process: | (3184) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3184) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3184) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | 1-< |
Value: 312D3C00700C0000010000000000000000000000 | |||
| (PID) Process: | (3184) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 700C0000563EFE6FD97ED50100000000 | |||
| (PID) Process: | (3184) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3184) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220250880 | |||
| (PID) Process: | (3184) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3184) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3184) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3184) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1330184213 | |||
Executable files
0
Suspicious files
3
Text files
28
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3184 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRD02.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3184 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\88TKN8O3\Citacion Fiscalia general de la Nacion Proceso 305351T (2).rar\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9671.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_80B98C90-FF24-488F-AEB6-5CB4F5159163.0\75D1AED1.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3352 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_80B98C90-FF24-488F-AEB6-5CB4F5159163.0\D83CFA48.png | — | |
MD5:— | SHA256:— | |||
| 3352 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_80B98C90-FF24-488F-AEB6-5CB4F5159163.0\E20C7F96.png | — | |
MD5:— | SHA256:— | |||
| 3184 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_97E3AB46A50CA54DA6B6237EA9A2E84E.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
| 2856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\99B6269E.png | — | |
MD5:— | SHA256:— | |||
| 2856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\93C9AC5C.png | — | |
MD5:— | SHA256:— | |||
| 3352 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_80B98C90-FF24-488F-AEB6-5CB4F5159163.0\EB1E3E9F.png | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3184 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
dns.msftncsi.com |
| shared |
ismaboli.com |
| malicious |