| File name: | Transwiz.msi |
| Full analysis: | https://app.any.run/tasks/2407c828-8d34-4b63-8493-5ec7474eec1c |
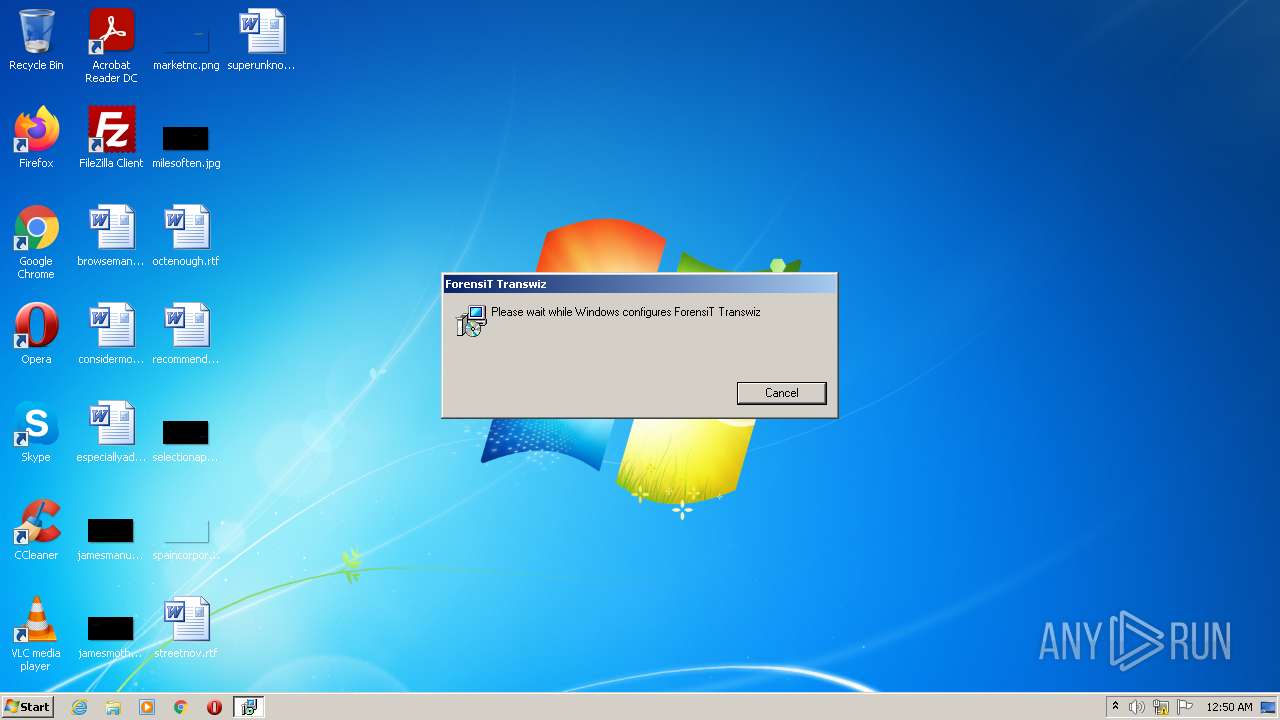
| Verdict: | Malicious activity |
| Analysis date: | May 02, 2022, 23:50:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Last Printed: Fri Dec 11 11:47:44 2009, Create Time/Date: Fri Dec 11 11:47:44 2009, Last Saved Time/Date: Fri Sep 18 15:06:51 2020, Security: 0, Code page: 1252, Revision Number: {B034C77C-C017-4926-8EB2-88DF6F1F336B}, Number of Words: 2, Subject: ForensiT Transwiz, Author: ForensiT, Name of Creating Application: Advanced Installer 18.6 build 099b4b9a, Template: ;2057, Comments: This installer database contains the logic and data required to install ForensiT Transwiz., Title: Installation Database, Keywords: Installer, MSI, Database, Number of Pages: 200 |
| MD5: | CF1DD0006C422C2C85C46A6FE4506406 |
| SHA1: | DA48EC07CEA7407B6B2D38DBB54D2CD472BD7563 |
| SHA256: | 511C2C0908883BC9D05295E5145B767F2633461C93A31D1CB8D765EE09CDD801 |
| SSDEEP: | 49152:fx3AY5aeGDcQ8KmLVR97uAHSvVPcAANEoW7SAmEzkGl7KMGzu7dhlwe50Qe2:GYTGDP8KmHHSVAvW7SAhxQMG67Zwe6r |
MALICIOUS
Drops executable file immediately after starts
- msiexec.exe (PID: 4092)
Application was dropped or rewritten from another process
- licfldr.exe (PID: 2364)
SUSPICIOUS
Checks supported languages
- msiexec.exe (PID: 4092)
- MsiExec.exe (PID: 3300)
- MsiExec.exe (PID: 2512)
- licfldr.exe (PID: 2364)
Reads Windows owner or organization settings
- msiexec.exe (PID: 3120)
- msiexec.exe (PID: 4092)
Reads the computer name
- msiexec.exe (PID: 4092)
- MsiExec.exe (PID: 3300)
- MsiExec.exe (PID: 2512)
- licfldr.exe (PID: 2364)
Reads the Windows organization settings
- msiexec.exe (PID: 3120)
- msiexec.exe (PID: 4092)
Executed as Windows Service
- vssvc.exe (PID: 3488)
Reads Environment values
- vssvc.exe (PID: 3488)
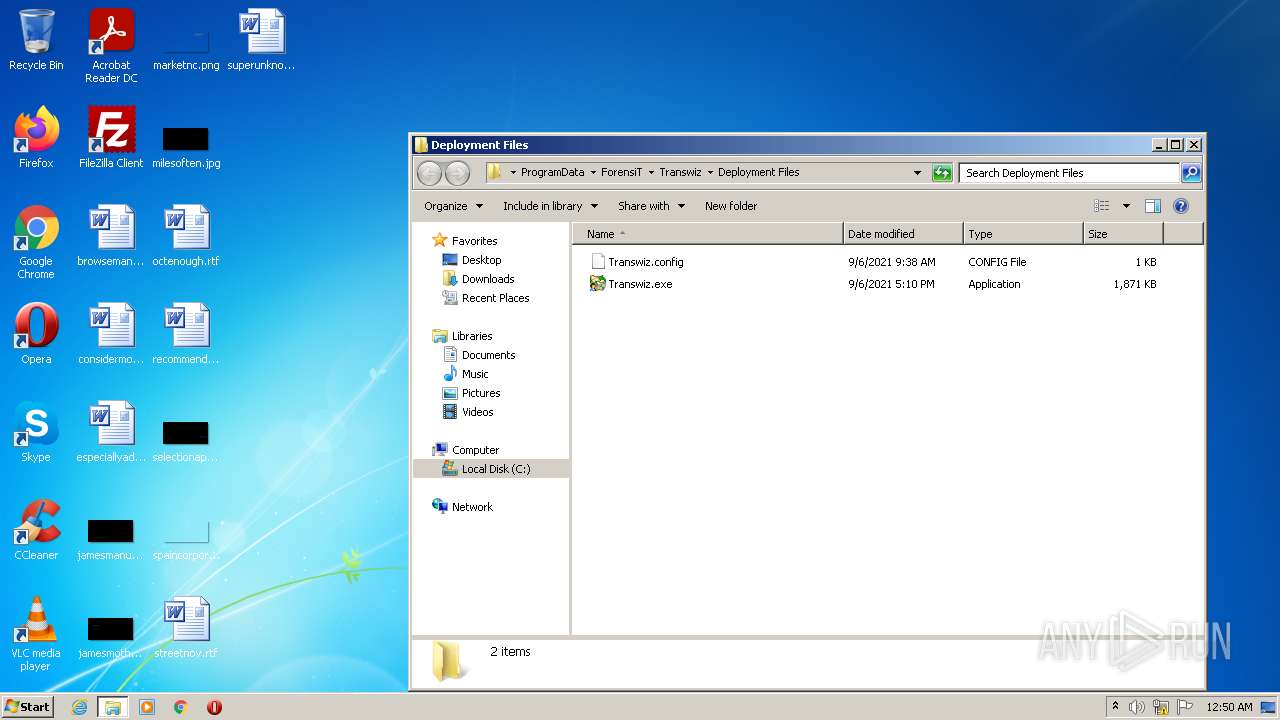
Executable content was dropped or overwritten
- msiexec.exe (PID: 4092)
Drops a file with a compile date too recent
- msiexec.exe (PID: 4092)
Creates a directory in Program Files
- msiexec.exe (PID: 4092)
INFO
Checks Windows Trust Settings
- msiexec.exe (PID: 3120)
- msiexec.exe (PID: 4092)
Reads settings of System Certificates
- msiexec.exe (PID: 3120)
- msiexec.exe (PID: 4092)
Reads the computer name
- vssvc.exe (PID: 3488)
- msiexec.exe (PID: 3120)
Checks supported languages
- msiexec.exe (PID: 3120)
- vssvc.exe (PID: 3488)
Application launched itself
- msiexec.exe (PID: 4092)
Creates files in the program directory
- msiexec.exe (PID: 4092)
Creates a software uninstall entry
- msiexec.exe (PID: 4092)
Searches for installed software
- msiexec.exe (PID: 4092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (81.9) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (9.2) |
| .msp | | | Windows Installer Patch (7.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Pages: | 200 |
|---|---|
| Keywords: | Installer, MSI, Database |
| Title: | Installation Database |
| Comments: | This installer database contains the logic and data required to install ForensiT Transwiz. |
| Template: | ;2057 |
| Software: | Advanced Installer 18.6 build 099b4b9a |
| LastModifiedBy: | - |
| Author: | ForensiT |
| Subject: | ForensiT Transwiz |
| Words: | 2 |
| RevisionNumber: | {B034C77C-C017-4926-8EB2-88DF6F1F336B} |
| CodePage: | Windows Latin 1 (Western European) |
| Security: | None |
| ModifyDate: | 2020:09:18 14:06:51 |
| CreateDate: | 2009:12:11 11:47:44 |
| LastPrinted: | 2009:12:11 11:47:44 |
Total processes
40
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2364 | "C:\Program Files\ForensiT\ForensiT Transwiz\licfldr.exe" -tf | C:\Program Files\ForensiT\ForensiT Transwiz\licfldr.exe | — | msiexec.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2512 | C:\Windows\system32\MsiExec.exe -Embedding F5420F24C1DC18B203D4DFFCADE912A6 E Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3120 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\Transwiz.msi" | C:\Windows\System32\msiexec.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3300 | C:\Windows\system32\MsiExec.exe -Embedding 0E85A14E8EDFDB5799A746B10705C4BB | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3488 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4092 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
9 142
Read events
8 863
Write events
267
Delete events
12
Modification events
| (PID) Process: | (3120) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4092) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000243FB26E7F5ED801FC0F00004C070000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4092) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000243FB26E7F5ED801FC0F00004C070000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4092) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 69 | |||
| (PID) Process: | (4092) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 400000000000000072B1056F7F5ED801FC0F00004C070000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4092) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000CC13086F7F5ED801FC0F00001C090000E80300000100000000000000000000008F468A716DD72A4B9DBCBB9BAD5256F10000000000000000 | |||
| (PID) Process: | (3488) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000349D116F7F5ED801A00D0000280D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3488) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000349D116F7F5ED801A00D0000980E0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3488) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000349D116F7F5ED801A00D0000F00F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3488) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000349D116F7F5ED801A00D000038080000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
10
Suspicious files
7
Text files
2
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4092 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 4092 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
| 4092 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{718a468f-d76d-4b2a-9dbc-bb9bad5256f1}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
| 4092 | msiexec.exe | C:\Windows\Installer\1367a8.ipi | binary | |
MD5:— | SHA256:— | |||
| 4092 | msiexec.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\ForensiT Transwiz\Deployment Files.lnk | lnk | |
MD5:— | SHA256:— | |||
| 4092 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFAF4D33B7021BBFD6.TMP | gmc | |
MD5:— | SHA256:— | |||
| 4092 | msiexec.exe | C:\Windows\Installer\MSI6EAF.tmp | binary | |
MD5:— | SHA256:— | |||
| 4092 | msiexec.exe | C:\Program Files\ForensiT\ForensiT Transwiz\licfldr.exe | executable | |
MD5:4B312A18215E358F06308D2ACBBBE103 | SHA256:00BCC6BA3E27FA3A3F1B9418749FBBE8D5C2C5537C346E27AE9F7EA5BB988E11 | |||
| 4092 | msiexec.exe | C:\ProgramData\ForensiT\Transwiz\Deployment Files\Transwiz.exe | executable | |
MD5:471CE7E66C5C66F1CDE267D0DABBFE8E | SHA256:7B557A3D47416E5E15964AC00161BCC3EB9BF97617085501C0EF60A1B4F3795E | |||
| 4092 | msiexec.exe | C:\Windows\Installer\MSI6E31.tmp | executable | |
MD5:36E2EDBDE4F98A27F31FEF1932D51E95 | SHA256:D9A307D175C72EA0922296F0686AB5A2A72F67E3C8C848E6623CB36AEADDF2EF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report