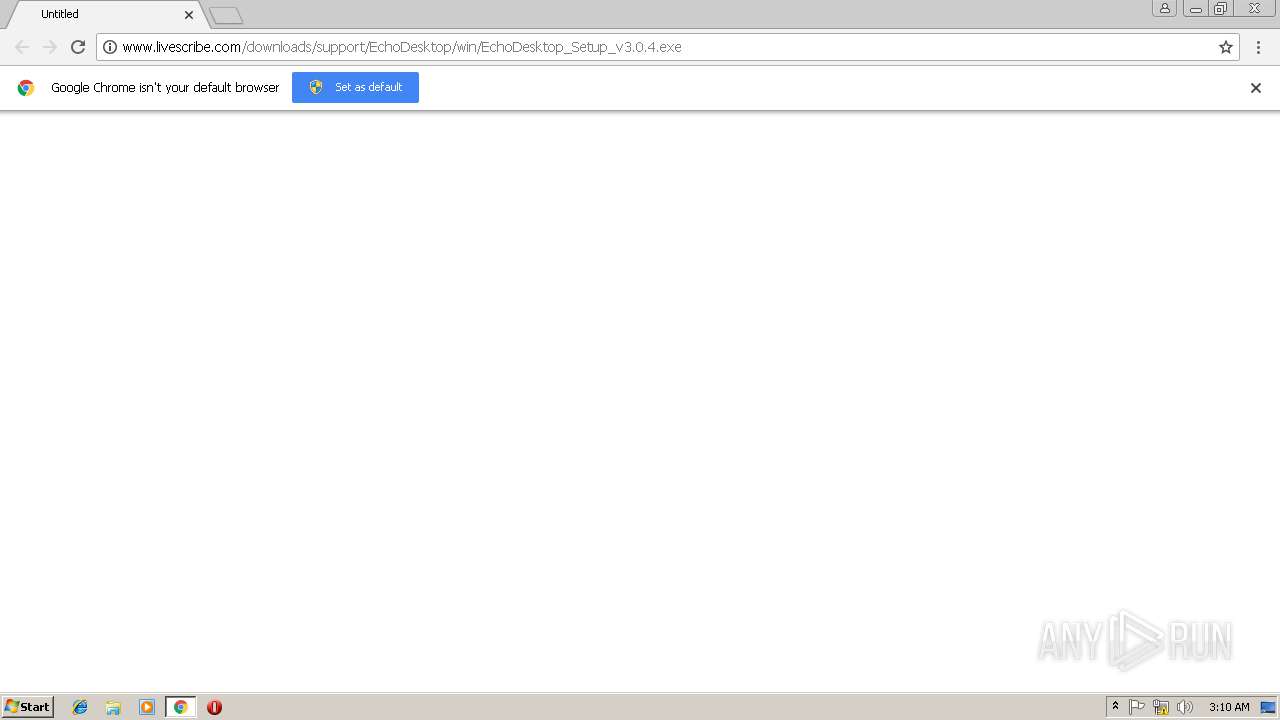
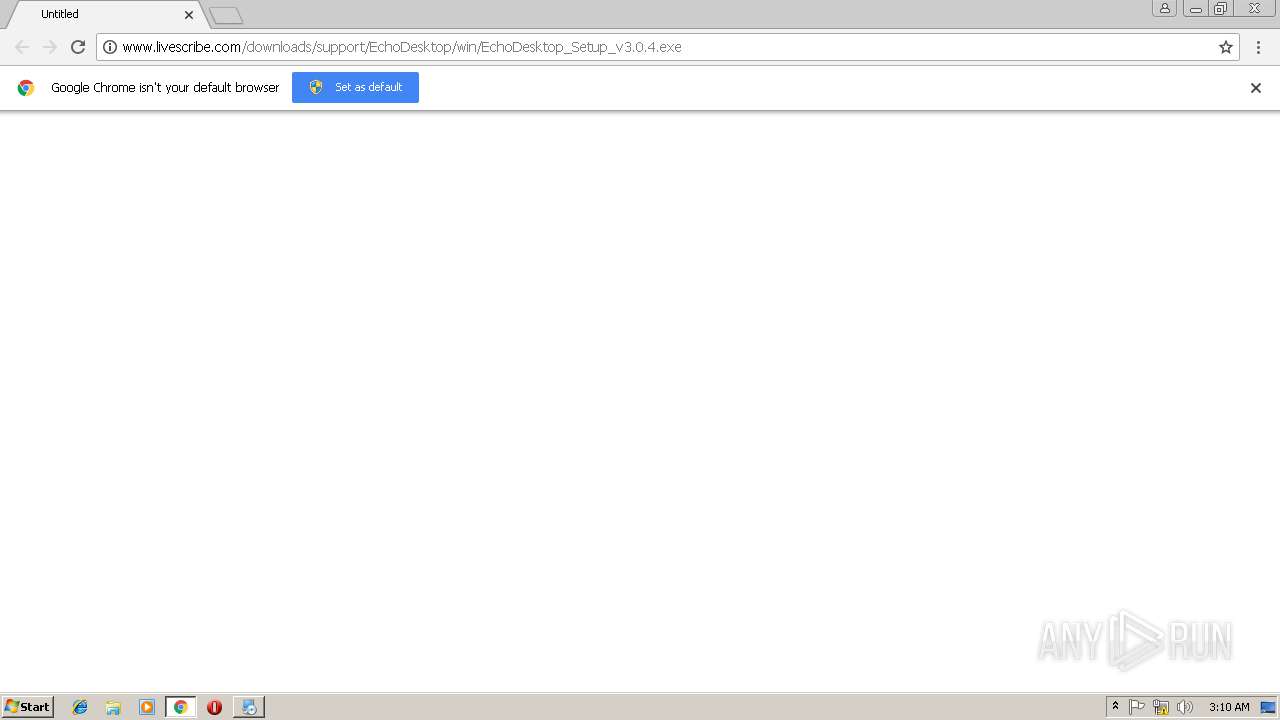
| URL: | http://www.livescribe.com/downloads/support/EchoDesktop/win/EchoDesktop_Setup_v3.0.4.exe |
| Full analysis: | https://app.any.run/tasks/4f8c3f9f-3242-4009-b314-783c47f1a01a |
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2019, 03:08:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DA0CACBB9CBB6B1DAE499B096DDF99A4 |
| SHA1: | 5FF14BD582EF9D036DF8171E75B5D1F4D37196F4 |
| SHA256: | 511A18148FB29BCCC3CC62A178890C0DD5284B83CF902B3969D3069D9D93AC2B |
| SSDEEP: | 3:N1KJS4QsX2KBKXKXViKgDORKgSMuNKRORKQ9WdRJ:Cc4H2aYGUNDrWt |
MALICIOUS
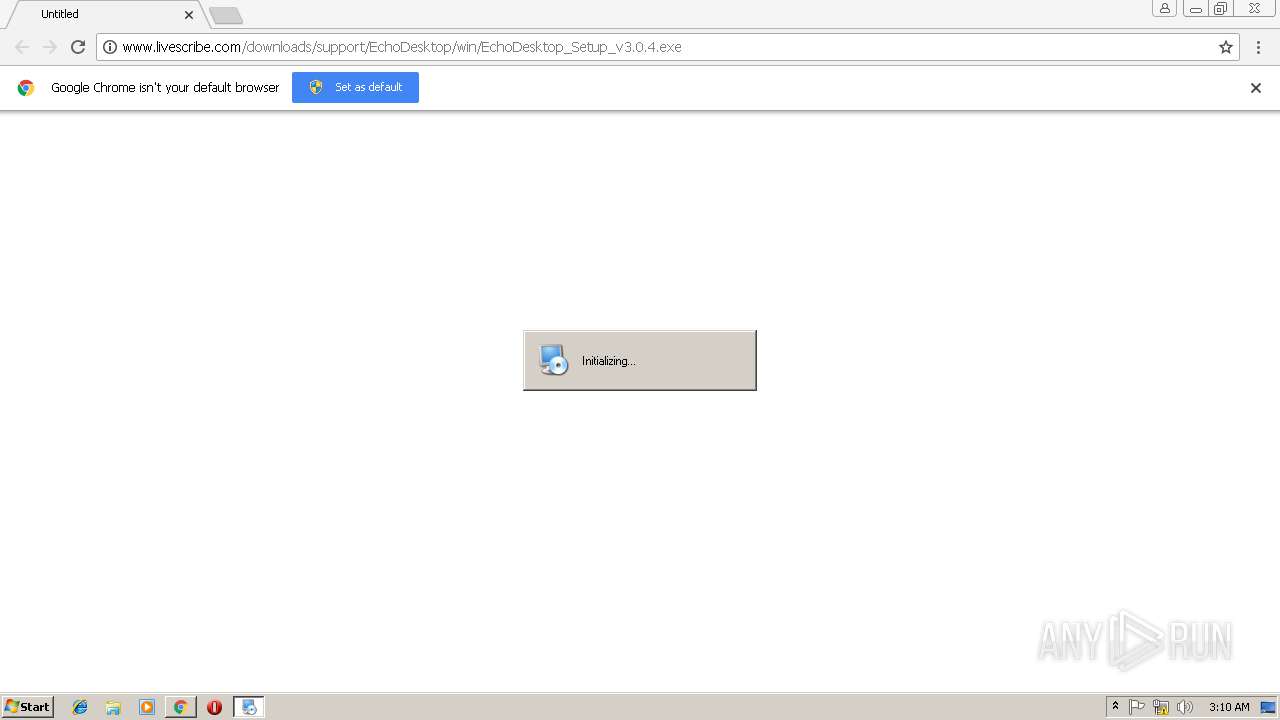
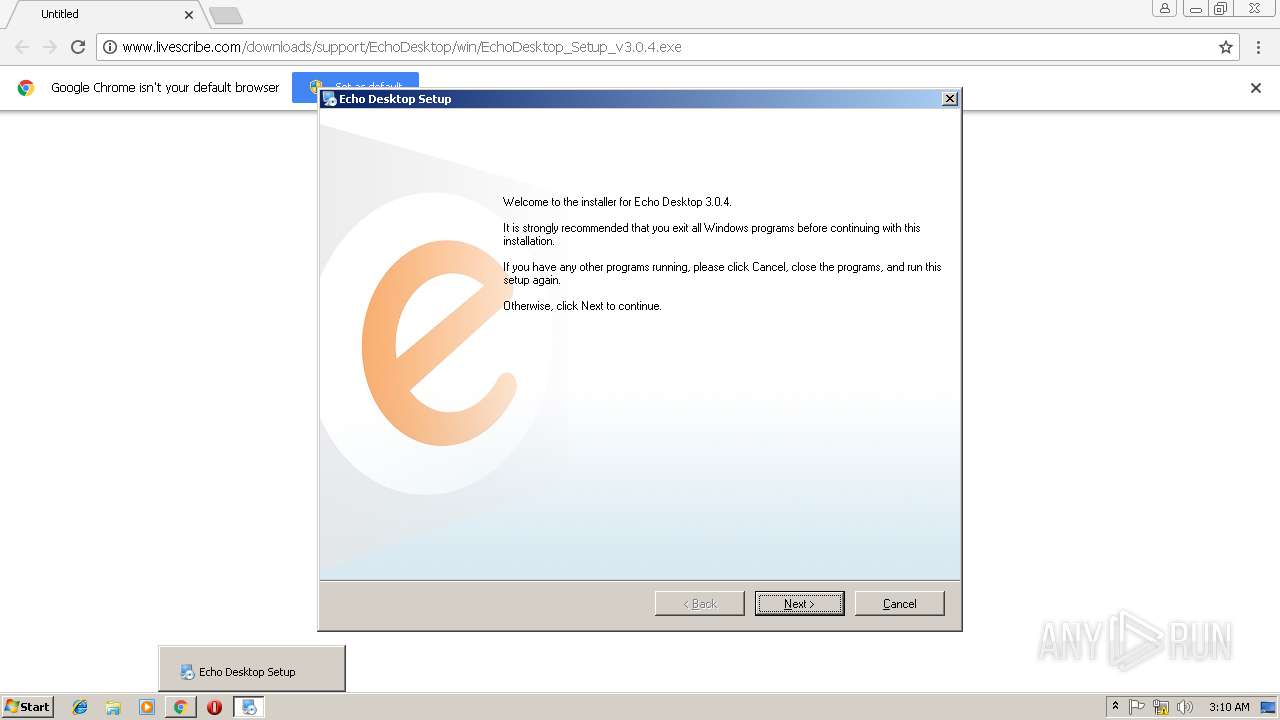
Application was dropped or rewritten from another process
- EchoDesktop_Setup_v3.0.4.exe (PID: 3164)
- EchoDesktop_Setup_v3.0.4.exe (PID: 3704)
- irsetup.exe (PID: 3952)
- NetFx20SP1_x86.exe (PID: 4036)
- setup.exe (PID: 3676)
- arh.exe (PID: 2444)
- Echo Desktop.exe (PID: 1428)
- dpinst.exe (PID: 2596)
- PenCommService.exe (PID: 2728)
- PenCommService.exe (PID: 2328)
Loads dropped or rewritten executable
- irsetup.exe (PID: 3952)
- setup.exe (PID: 3676)
- PenCommService.exe (PID: 2328)
- PenCommService.exe (PID: 2728)
- Echo Desktop.exe (PID: 1428)
Loads the Task Scheduler COM API
- ngen.exe (PID: 3160)
- ngen.exe (PID: 2504)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2744)
- EchoDesktop_Setup_v3.0.4.exe (PID: 3164)
- NetFx20SP1_x86.exe (PID: 4036)
- dpinst.exe (PID: 2596)
- DrvInst.exe (PID: 880)
- irsetup.exe (PID: 3952)
Creates files in the Windows directory
- ngen.exe (PID: 3160)
- ngen.exe (PID: 2504)
- dpinst.exe (PID: 2596)
- DrvInst.exe (PID: 880)
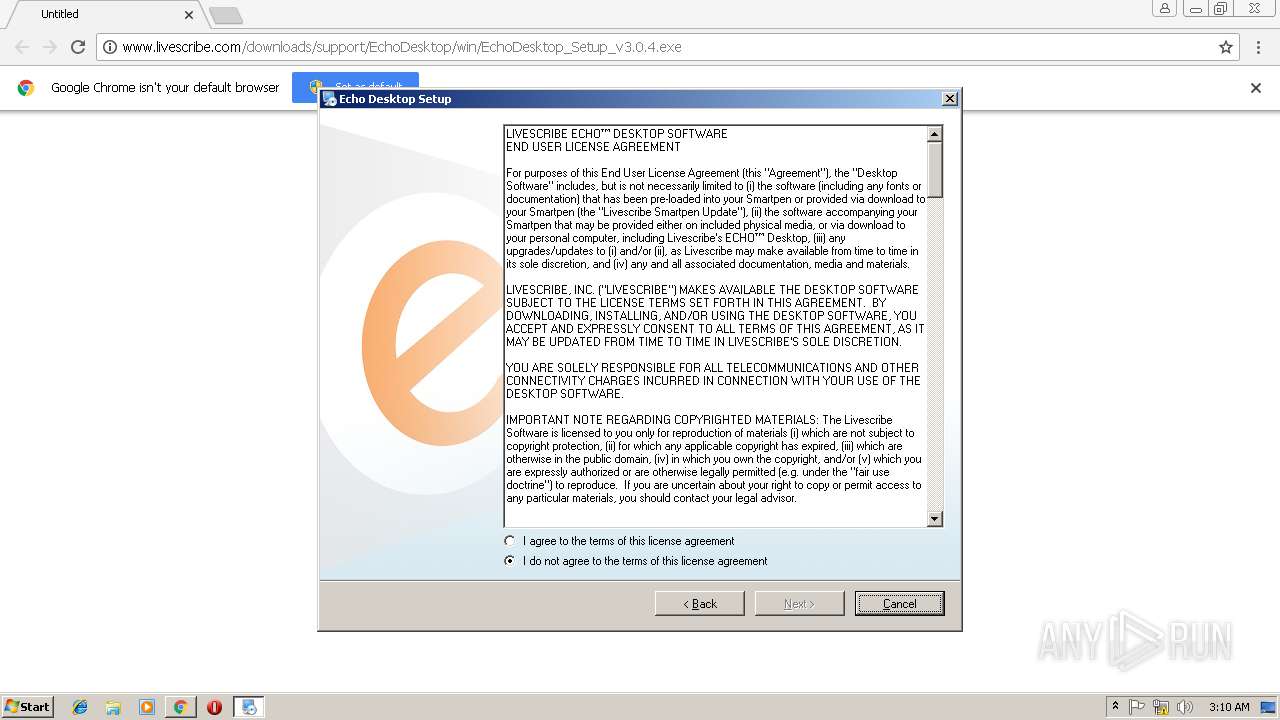
Creates a software uninstall entry
- irsetup.exe (PID: 3952)
Modifies the open verb of a shell class
- irsetup.exe (PID: 3952)
Removes files from Windows directory
- DrvInst.exe (PID: 880)
Creates files in the driver directory
- DrvInst.exe (PID: 880)
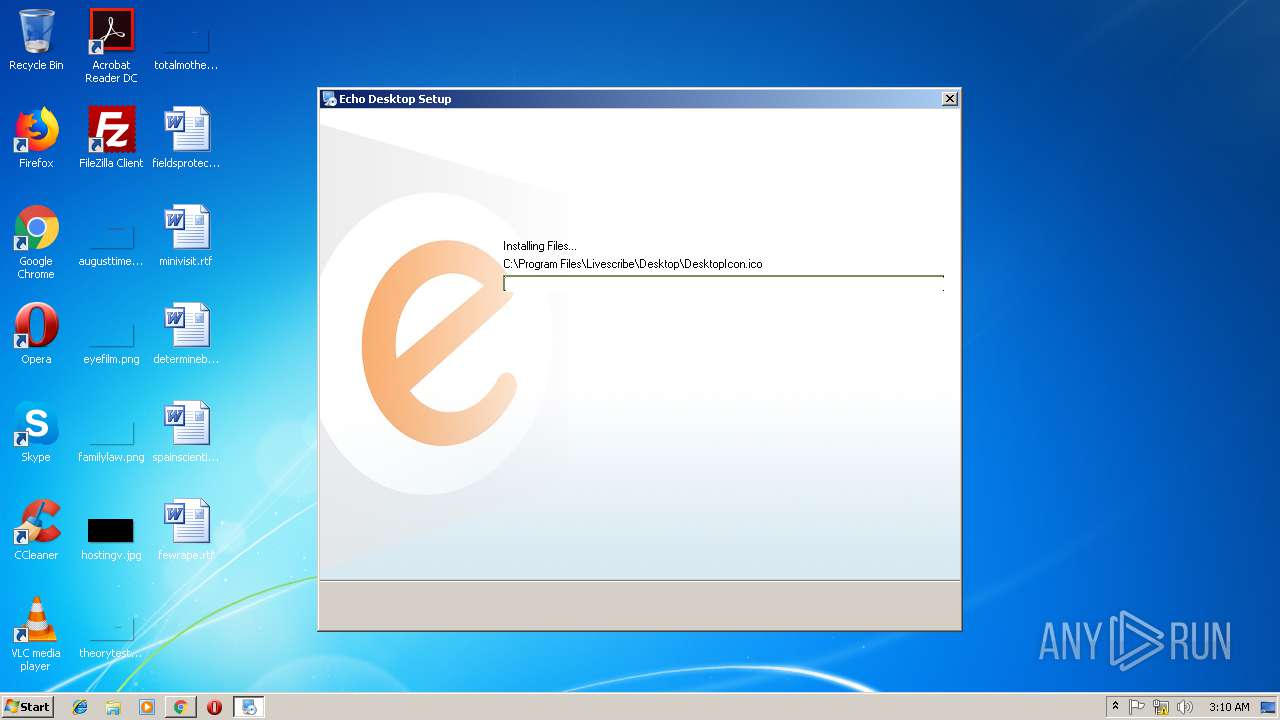
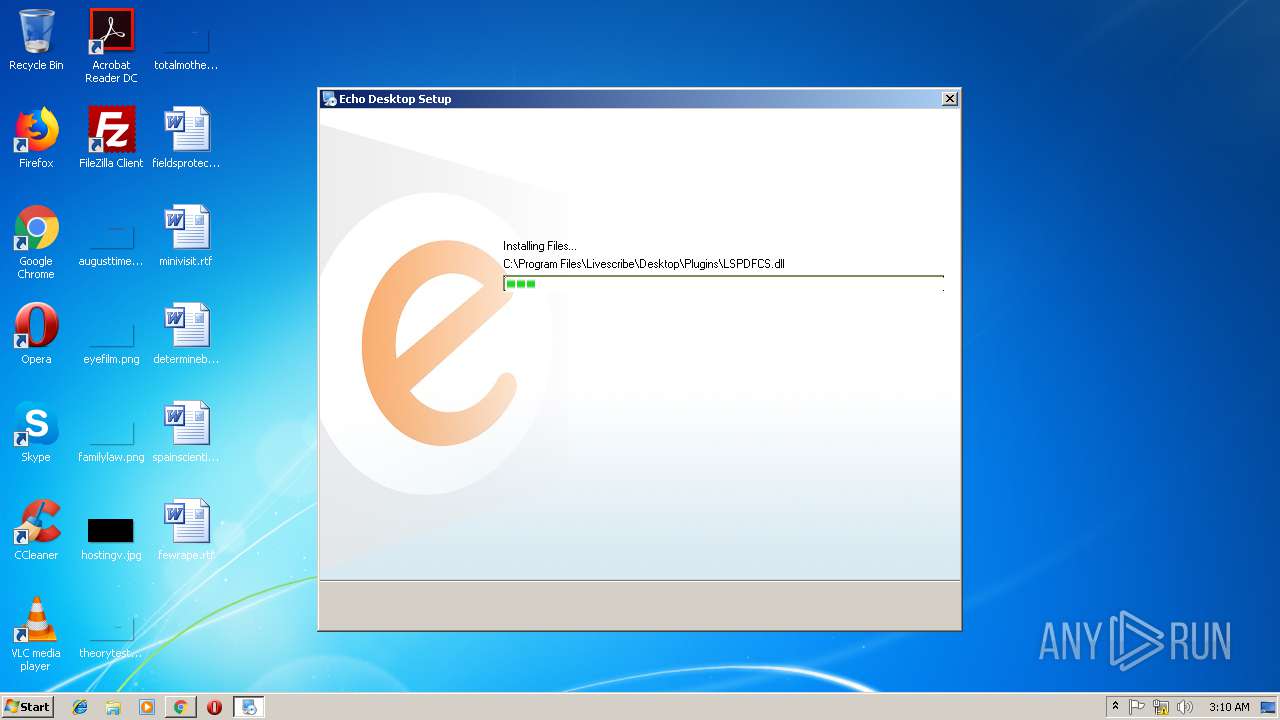
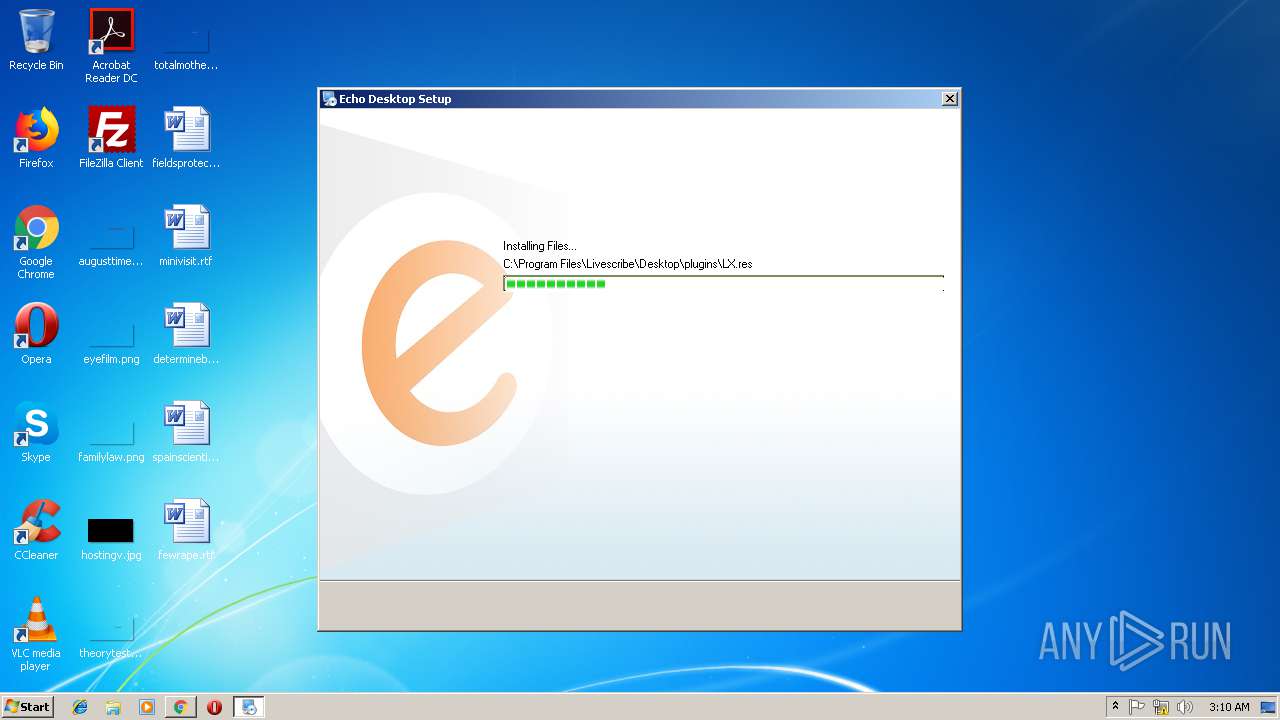
Creates files in the program directory
- PenCommService.exe (PID: 2328)
- irsetup.exe (PID: 3952)
INFO
Application launched itself
- chrome.exe (PID: 2744)
Reads Internet Cache Settings
- chrome.exe (PID: 2744)
Reads settings of System Certificates
- chrome.exe (PID: 2744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
24
Malicious processes
9
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 880 | DrvInst.exe "4" "8" "C:\Users\admin\AppData\Local\Temp\{04d894c5-204f-13c1-3bb0-477628bbf64e}\pulseusb.inf" "0" "6ef71d017" "000004A4" "WinSta0\Default" "00000308" "208" "c:\program files\common files\livescribe\pendriverv2.2" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
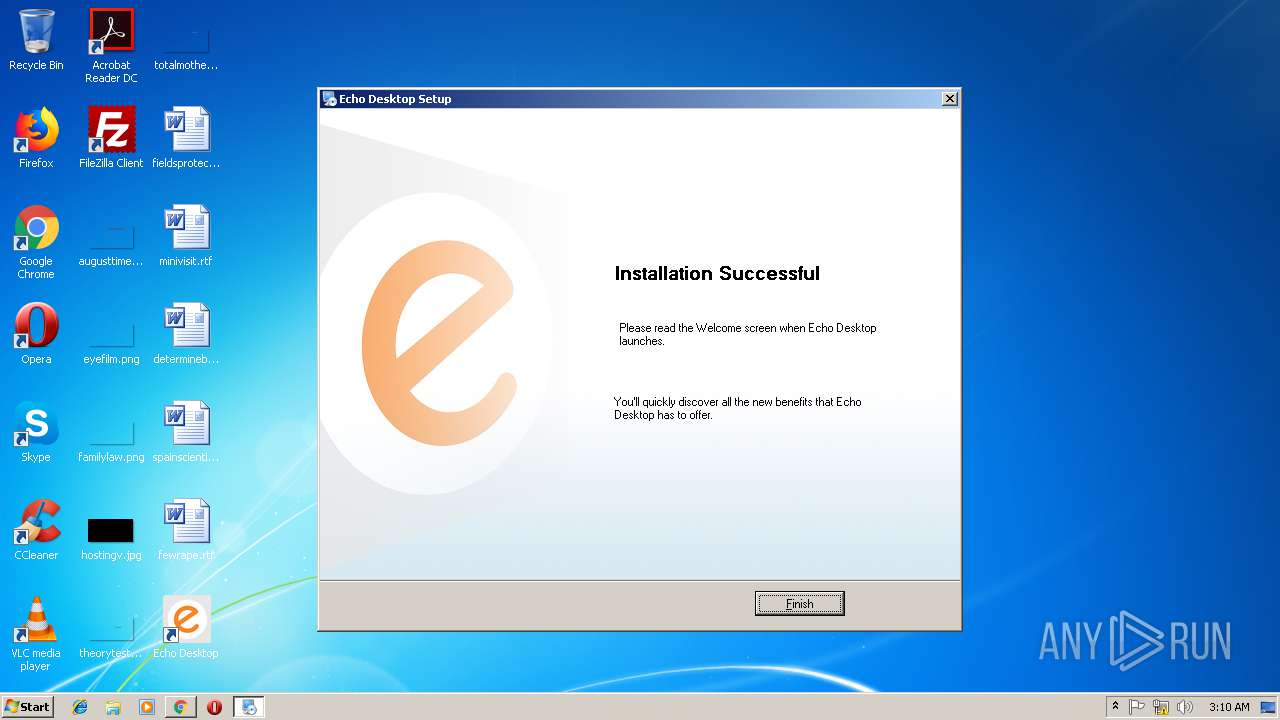
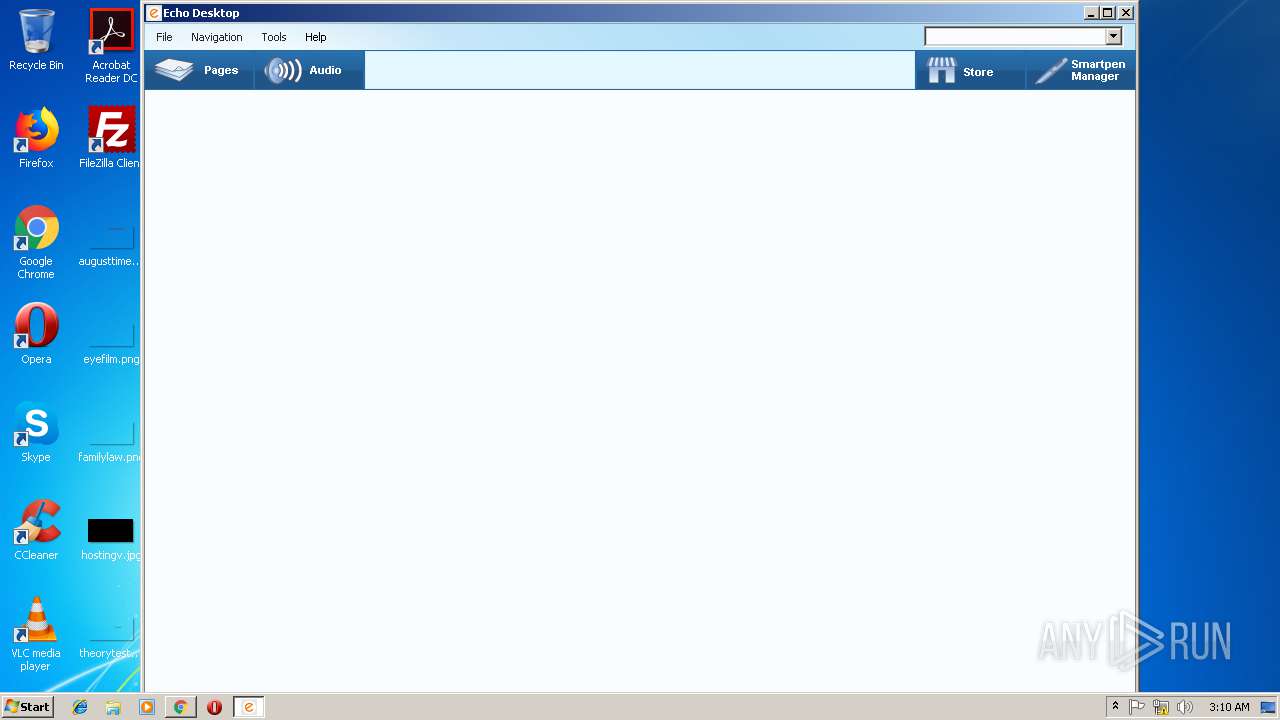
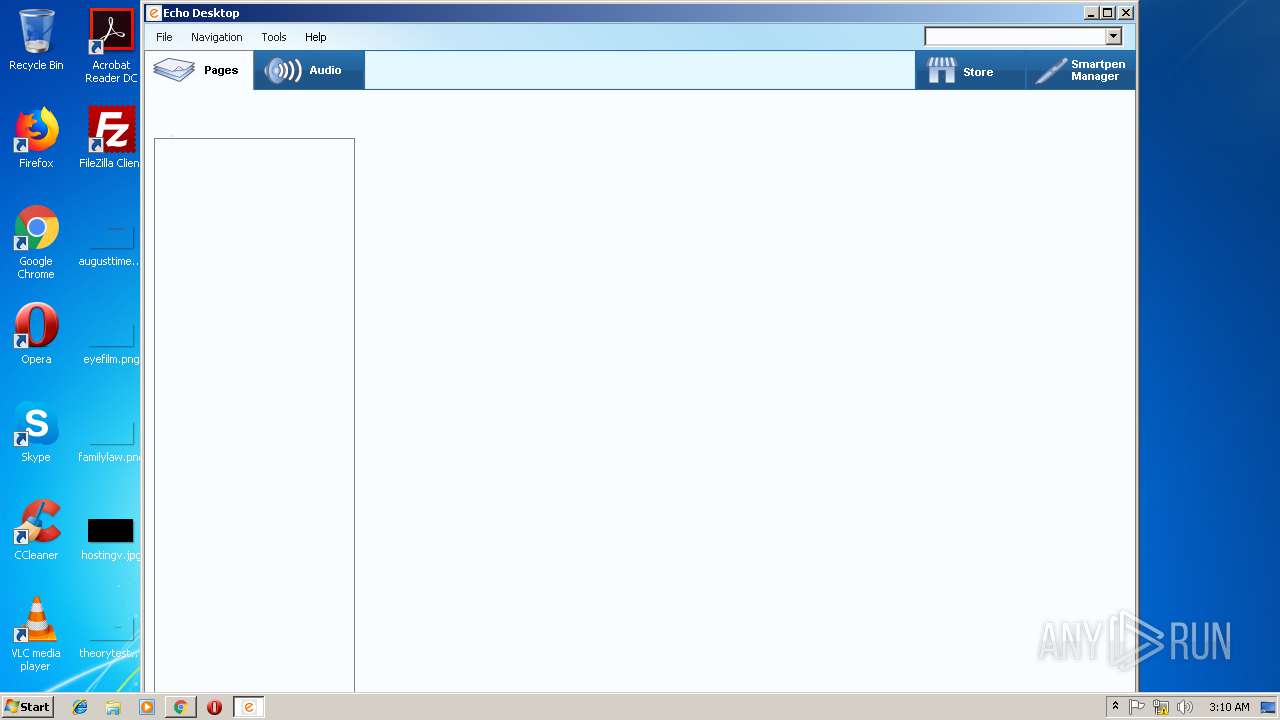
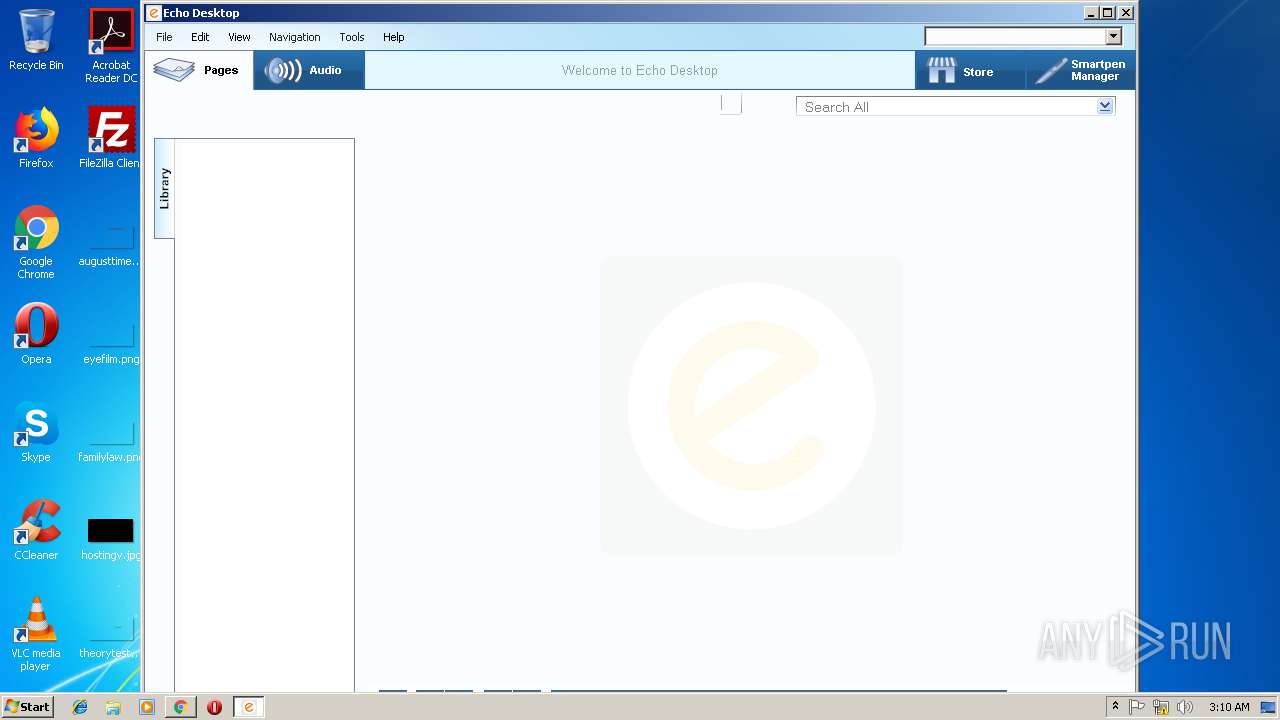
| 1428 | "C:\Program Files\Livescribe\Desktop\Echo Desktop.exe" | C:\Program Files\Livescribe\Desktop\Echo Desktop.exe | explorer.exe | ||||||||||||
User: admin Company: Livescribe Integrity Level: MEDIUM Description: Echo Desktop Exit code: 0 Version: 3.0.4.0 Modules
| |||||||||||||||
| 1948 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2328 | "C:\Program Files\Common Files\Livescribe\PenComm\PenCommService.exe" | C:\Program Files\Common Files\Livescribe\PenComm\PenCommService.exe | services.exe | ||||||||||||
User: SYSTEM Company: Livescribe Integrity Level: SYSTEM Description: Livescribe Smartpen Communication Service Exit code: 0 Version: 2, 6, 36, 1576" Modules
| |||||||||||||||
| 2444 | "C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\arh.exe" -uninstallAppSilent com.livescribe.LivescribeConnect | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\arh.exe | — | irsetup.exe | |||||||||||
User: admin Company: Adobe Systems Inc. Integrity Level: HIGH Description: Adobe AIR Redistribution Helper Exit code: 1 Version: 2.7.1.19610 Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=908,6446415706175171745,7615301987602728214,131072 --enable-features=PasswordImport --service-pipe-token=51ED6FA61BDC52E740339FBF3FD5FF58 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=51ED6FA61BDC52E740339FBF3FD5FF58 --renderer-client-id=4 --mojo-platform-channel-handle=1900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2504 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\ngen.exe queue continue | C:\Windows\Microsoft.NET\Framework\v2.0.50727\ngen.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2596 | "C:\Program Files\Common Files\Livescribe\PenDriverV2.2\dpinst-32\dpinst.exe" /q /F /SA /PATH .. | C:\Program Files\Common Files\Livescribe\PenDriverV2.2\dpinst-32\dpinst.exe | irsetup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Driver Package Installer Exit code: 256 Version: 2.1 Modules
| |||||||||||||||
| 2728 | "C:\Program Files\Common Files\Livescribe\PenComm\PenCommService.exe" -i | C:\Program Files\Common Files\Livescribe\PenComm\PenCommService.exe | — | irsetup.exe | |||||||||||
User: admin Company: Livescribe Integrity Level: HIGH Description: Livescribe Smartpen Communication Service Exit code: 0 Version: 2, 6, 36, 1576" Modules
| |||||||||||||||
| 2744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://www.livescribe.com/downloads/support/EchoDesktop/win/EchoDesktop_Setup_v3.0.4.exe | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 844
Read events
1 641
Write events
197
Delete events
6
Modification events
| (PID) Process: | (2744) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2744) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2744) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2844) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2744-13195019363512875 |
Value: 259 | |||
| (PID) Process: | (2744) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2744) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2744) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2744) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2744) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2744-13195019363512875 |
Value: 259 | |||
| (PID) Process: | (2744) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
236
Suspicious files
47
Text files
240
Unknown types
39
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c8dbff58-6399-4147-9864-68e1d9188705.tmp | — | |
MD5:— | SHA256:— | |||
| 2744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\623e03f7-6b42-4206-ab69-952ae5d283bc.tmp | — | |
MD5:— | SHA256:— | |||
| 2744 | chrome.exe | C:\Users\admin\Downloads\34200a35-7144-41bb-8bfc-43cb084966f0.tmp | — | |
MD5:— | SHA256:— | |||
| 2744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\cf68b9e7-f53b-4eef-a840-599986bc8d10.tmp | — | |
MD5:— | SHA256:— | |||
| 2744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF1993ba.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
7
DNS requests
5
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2744 | chrome.exe | GET | — | 52.40.165.26:80 | http://www.livescribe.com/downloads/support/EchoDesktop/win/EchoDesktop_Setup_v3.0.4.exe | US | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2744 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2744 | chrome.exe | 52.40.165.26:80 | www.livescribe.com | Amazon.com, Inc. | US | suspicious |
2744 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2744 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.livescribe.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2744 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2744 | chrome.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
Process | Message |
|---|---|
Echo Desktop.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
Echo Desktop.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|