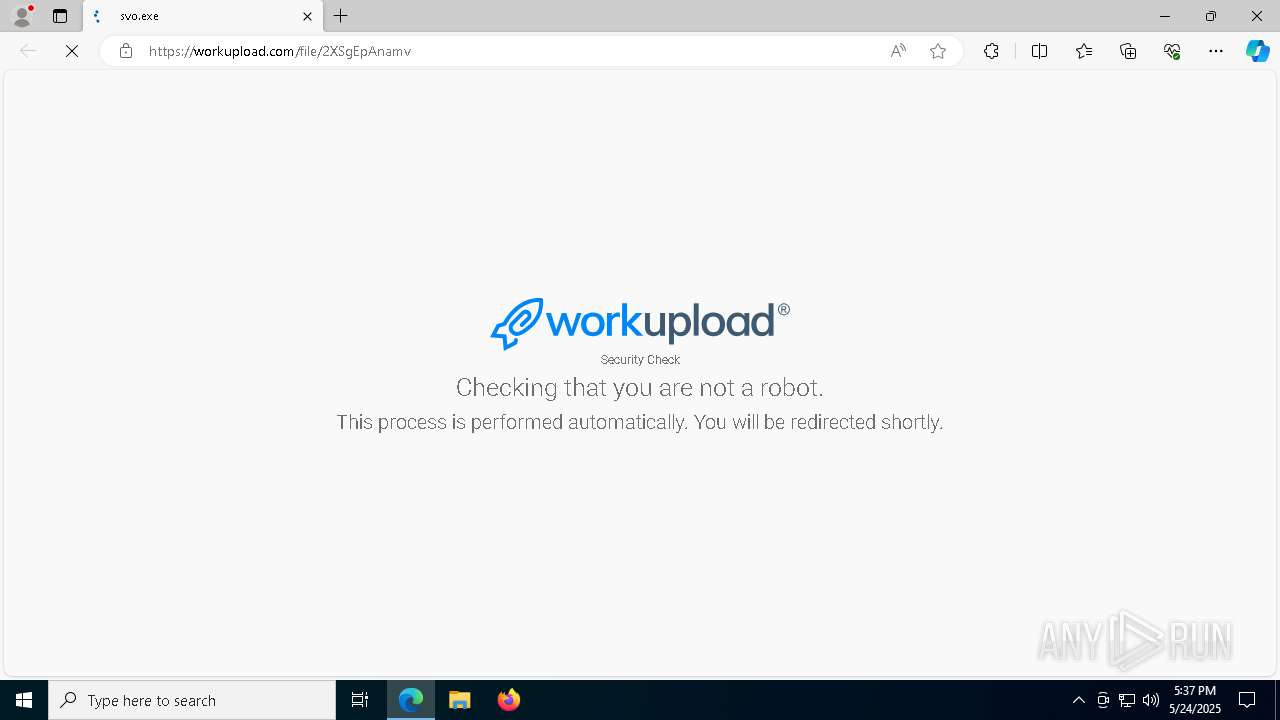
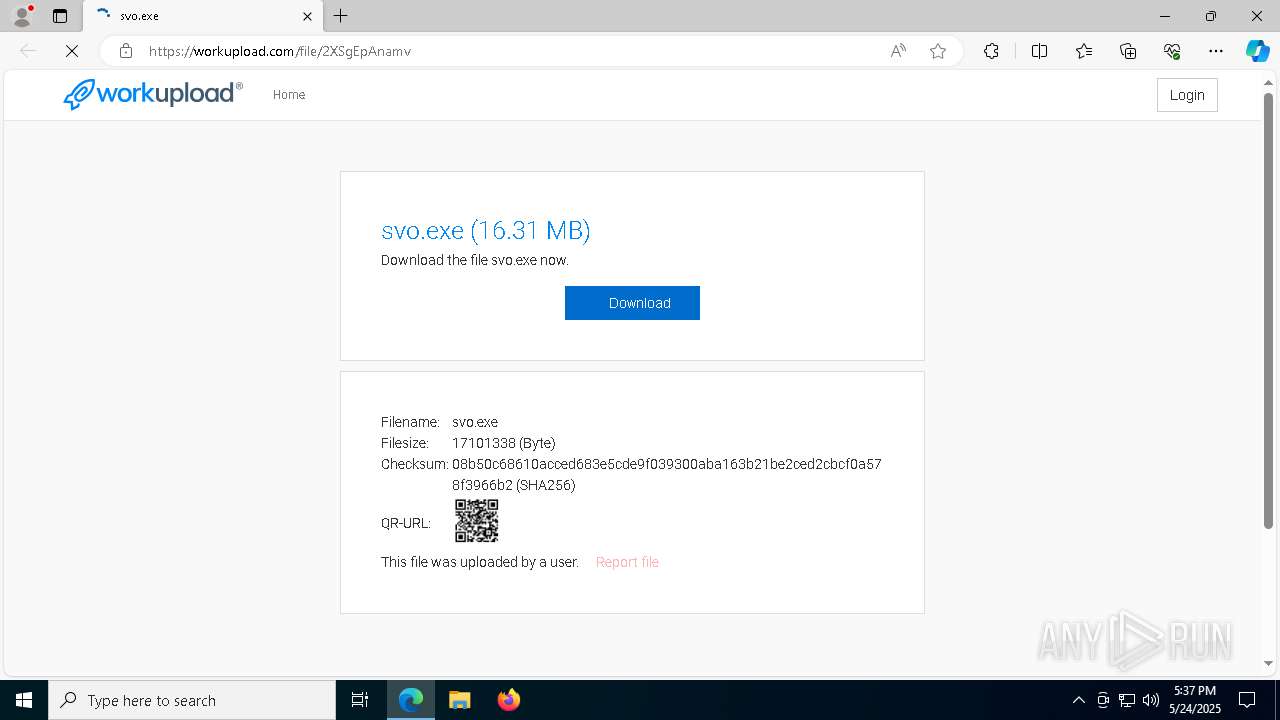
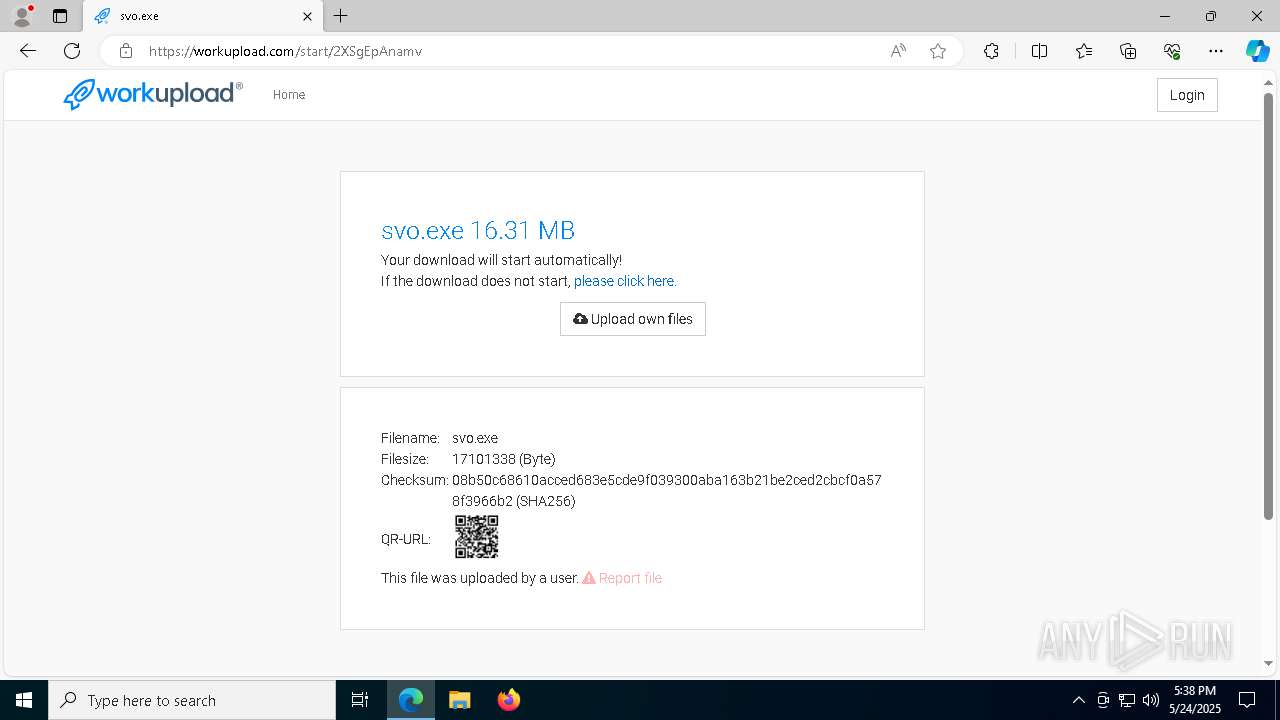
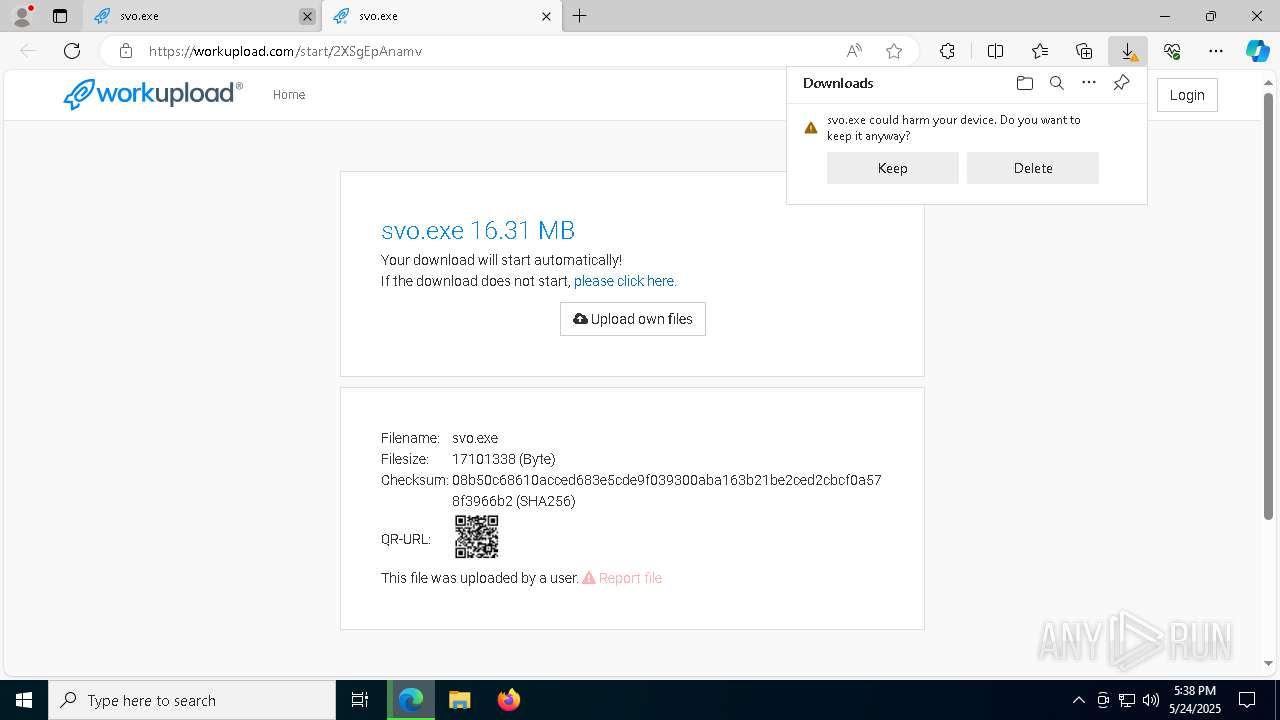
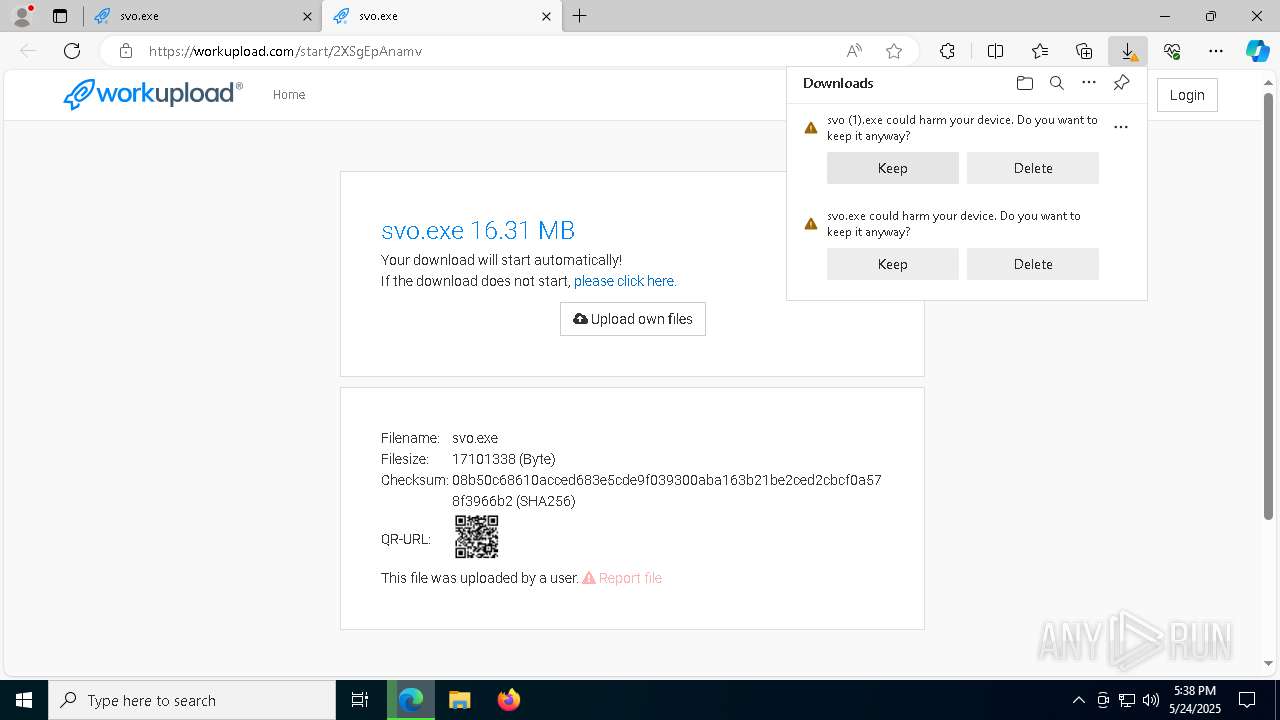
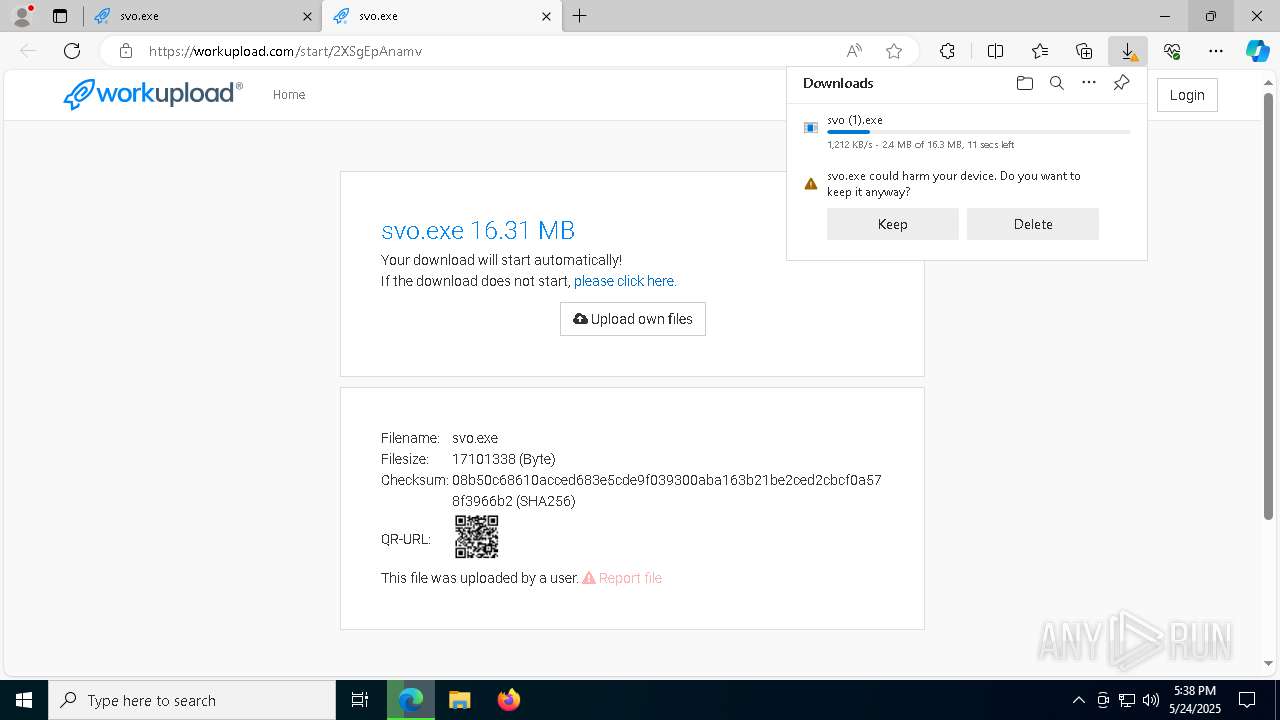
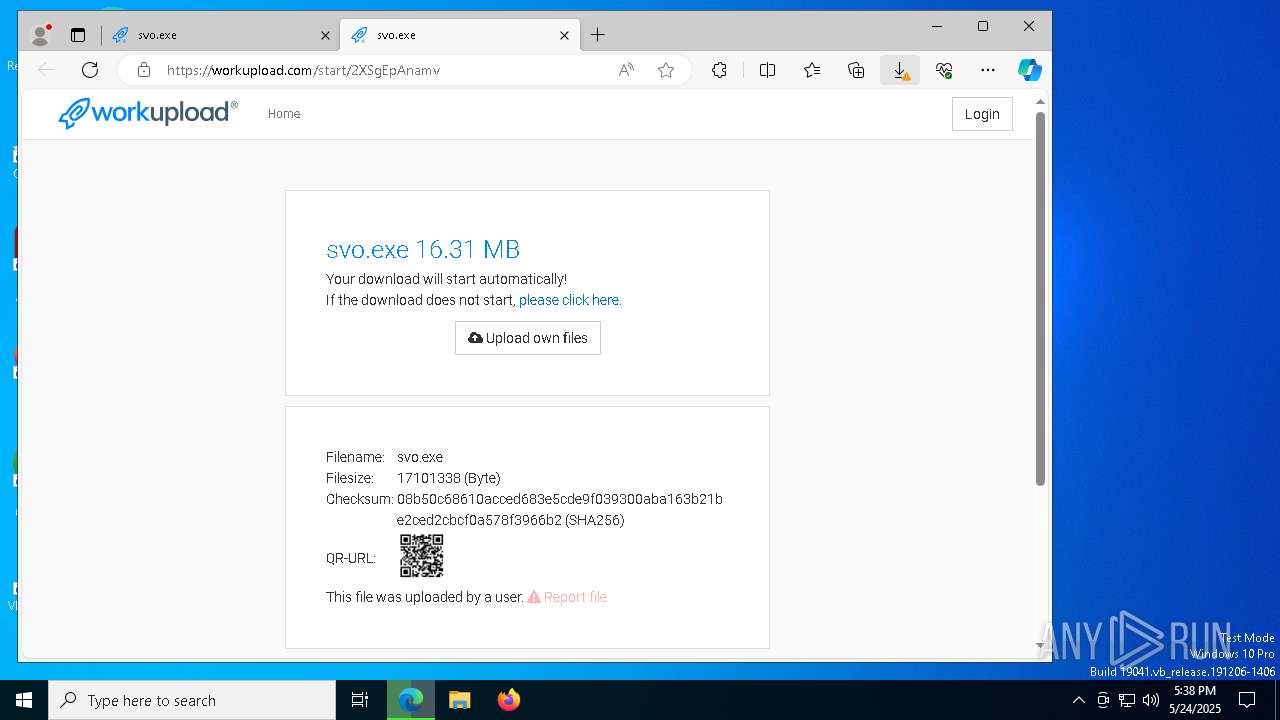
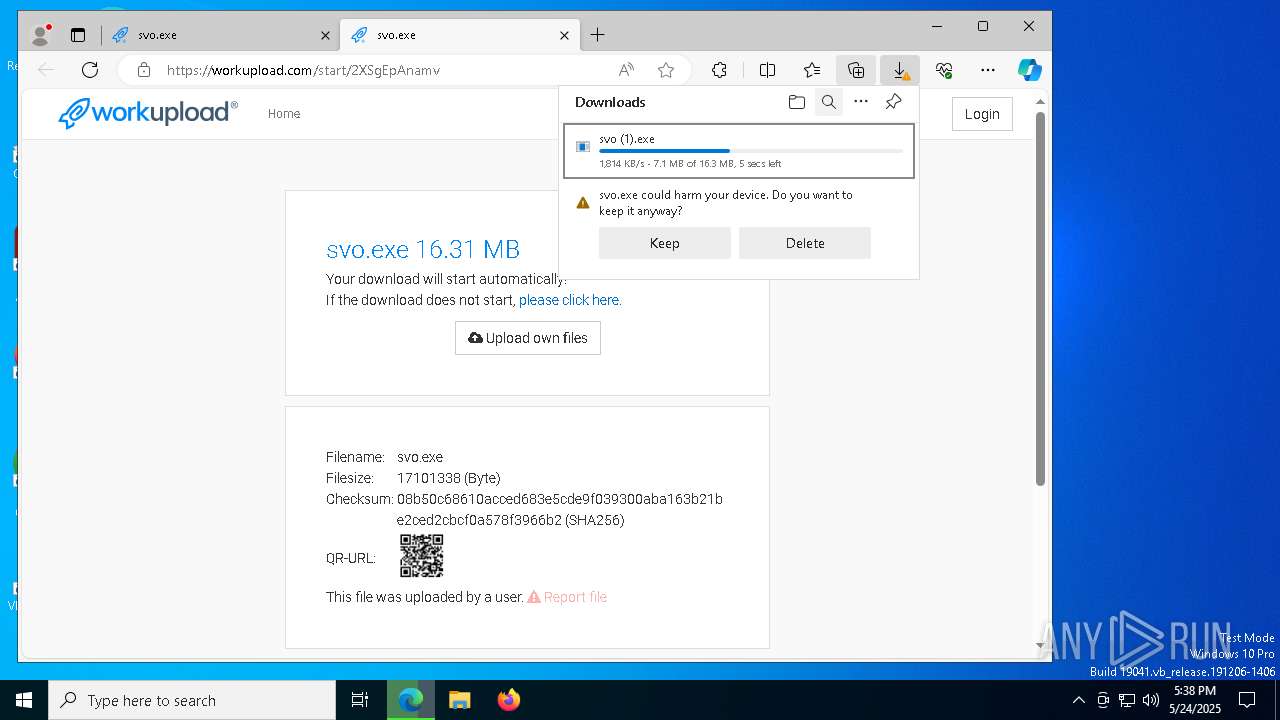
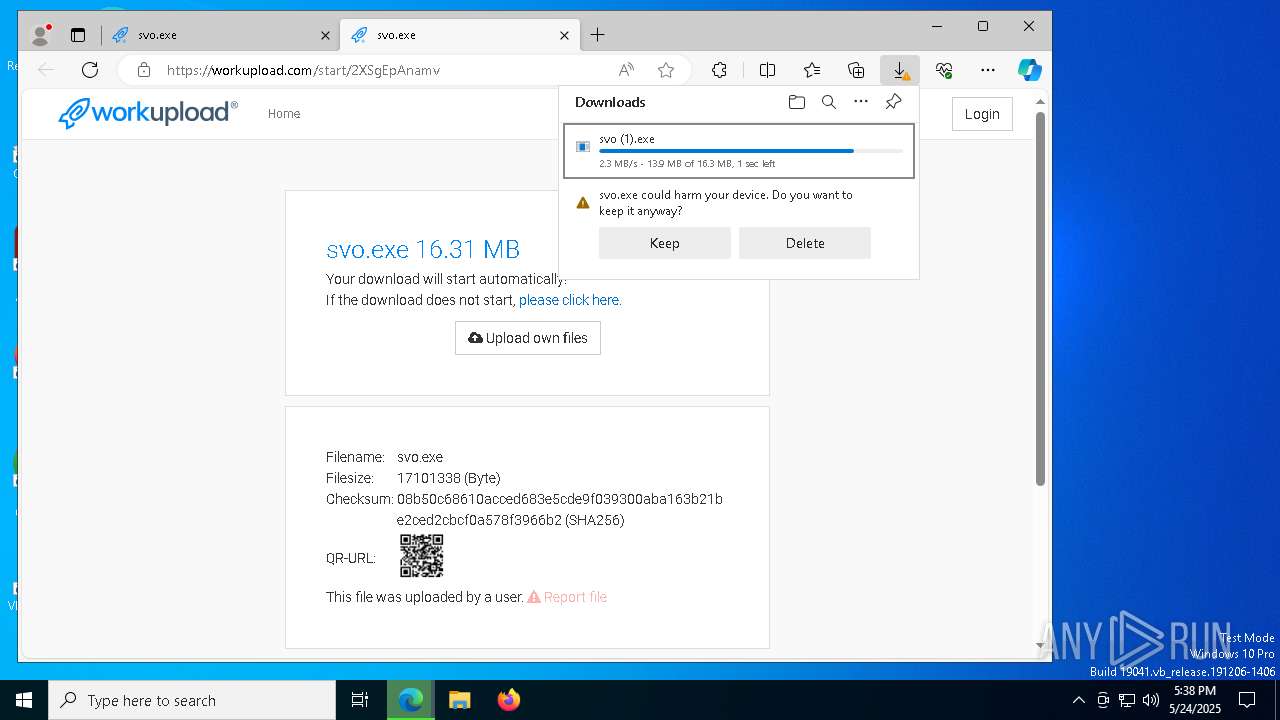
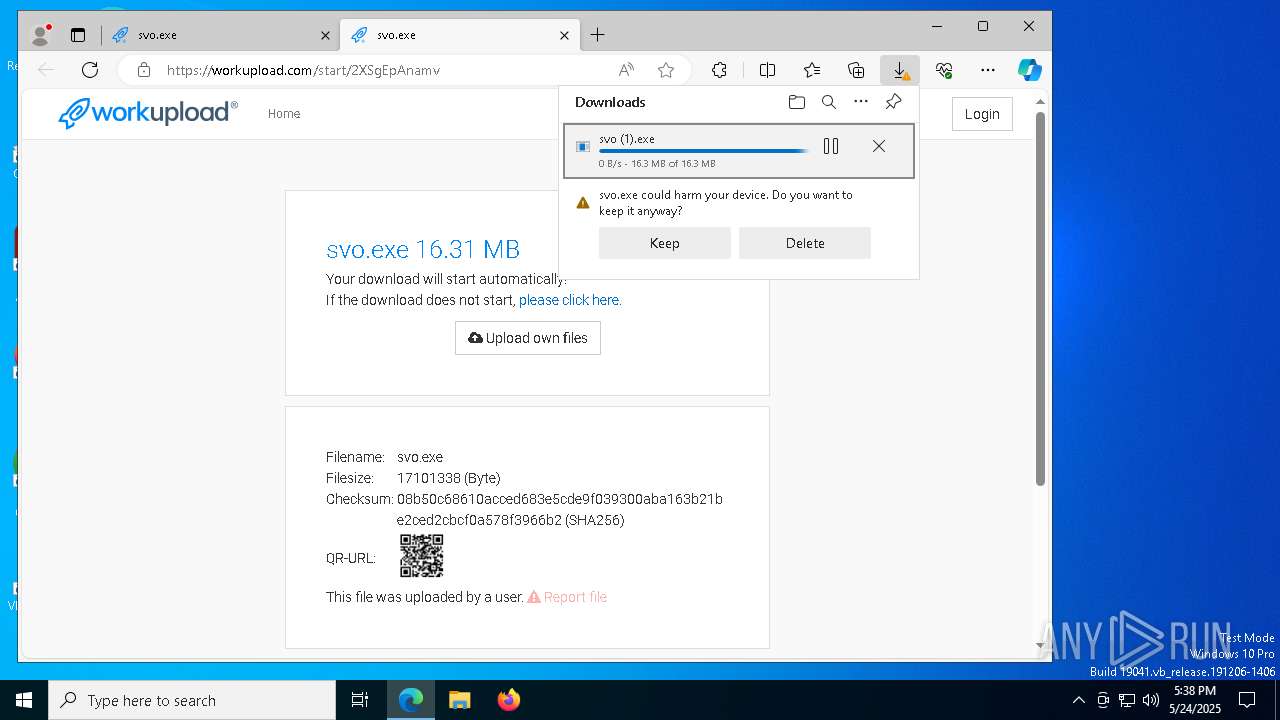
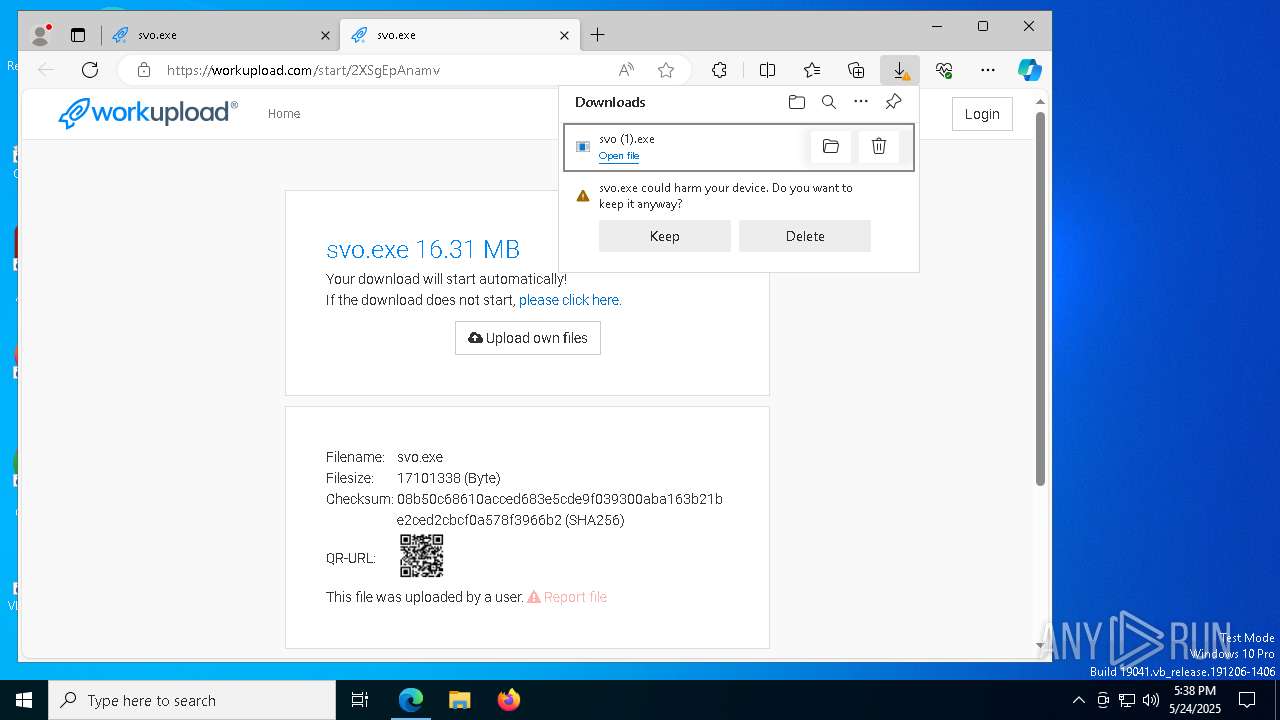
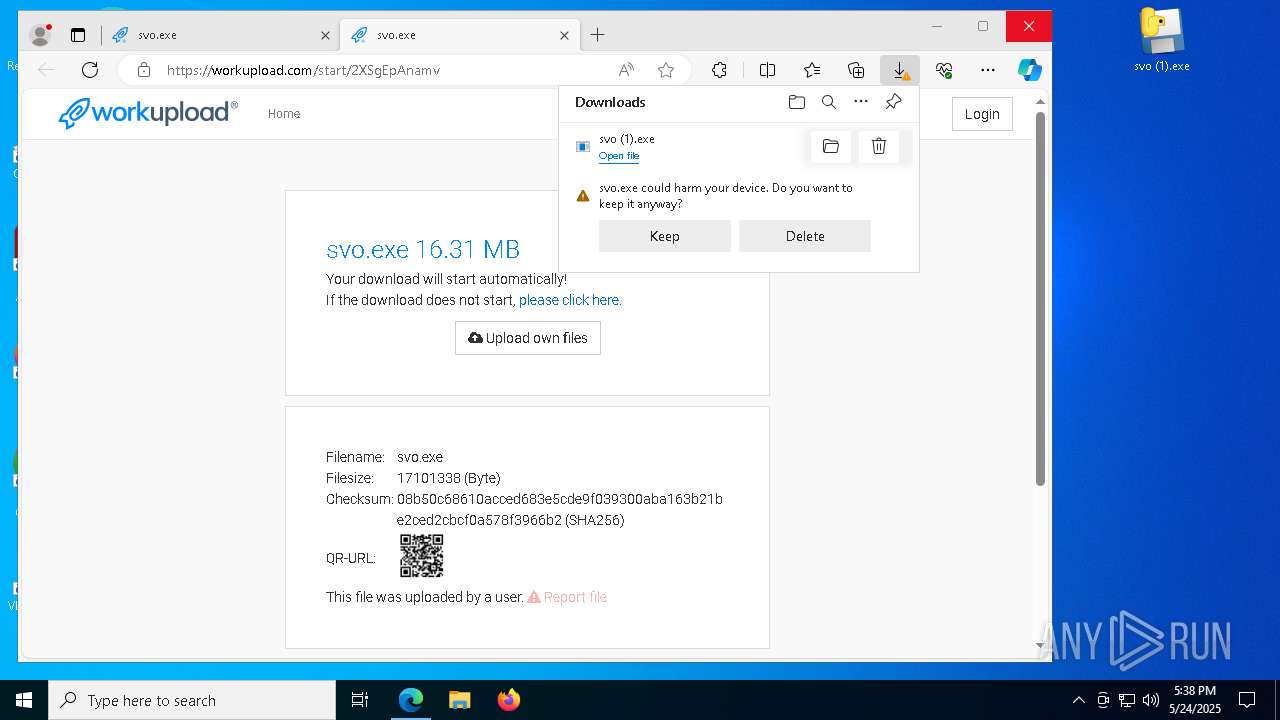
| URL: | https://workupload.com/file/2XSgEpAnamv |
| Full analysis: | https://app.any.run/tasks/986588de-bd87-4da5-b965-2fd3cfeb0e5d |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2025, 17:37:48 |
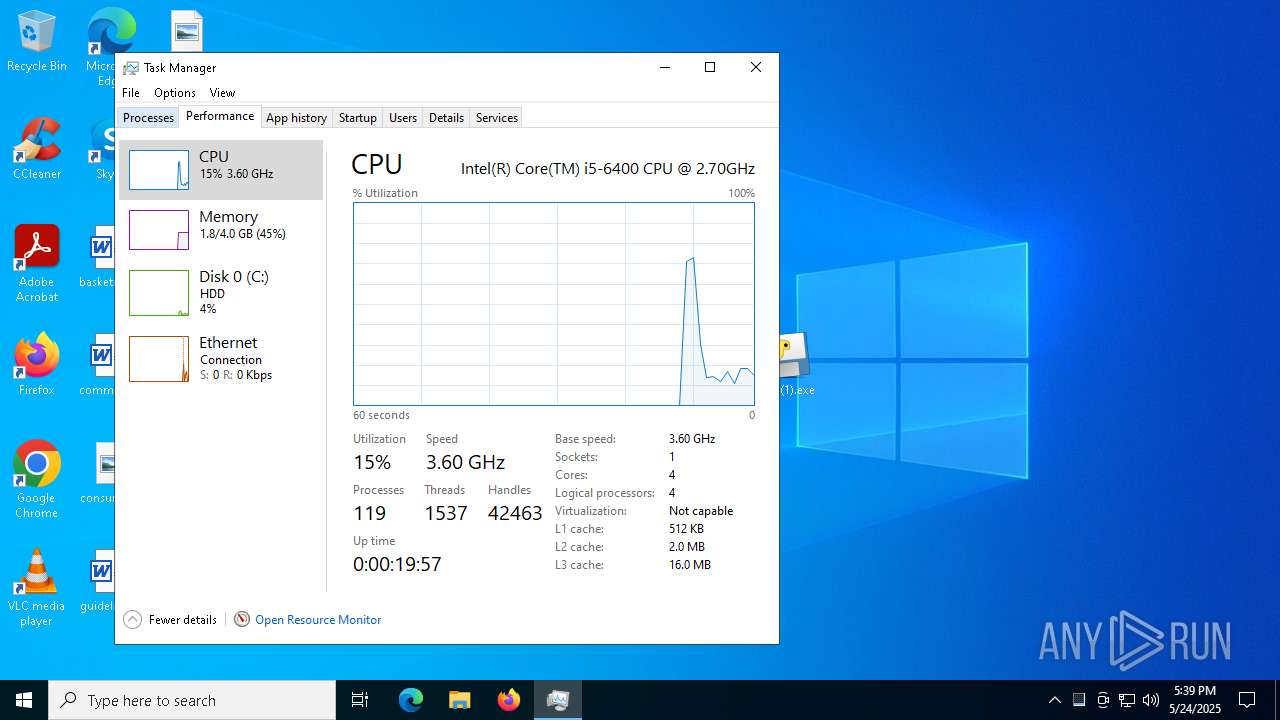
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 91495222AED78C8395F64D3CEF2D6FC3 |
| SHA1: | F7C9010153967F9B151B2EC704A9D7F1E7C12DBC |
| SHA256: | 51044E8A943A5F0D6ABA0794102EF29FA9B1917A2A9AD4BFE0807D44020C9417 |
| SSDEEP: | 3:N8bXOrZXX9bx:2itH3 |
MALICIOUS
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 6600)
SUSPICIOUS
Process drops python dynamic module
- svo (1).exe (PID: 7748)
- svo (1).exe (PID: 5176)
- svo (1).exe (PID: 7512)
- svo (1).exe (PID: 4284)
- svchost.exe (PID: 6712)
Executable content was dropped or overwritten
- svo (1).exe (PID: 7748)
- svo (1).exe (PID: 5176)
- svo (1).exe (PID: 7512)
- svo (1).exe (PID: 4284)
- svo (1).exe (PID: 1144)
- svchost.exe (PID: 6712)
The process drops C-runtime libraries
- svo (1).exe (PID: 7748)
- svo (1).exe (PID: 5176)
- svo (1).exe (PID: 7512)
- svo (1).exe (PID: 4284)
- svchost.exe (PID: 6712)
Process drops legitimate windows executable
- svo (1).exe (PID: 7748)
- svo (1).exe (PID: 5176)
- svo (1).exe (PID: 7512)
- svo (1).exe (PID: 4284)
- svchost.exe (PID: 6712)
There is functionality for taking screenshot (YARA)
- svo (1).exe (PID: 7748)
- svo (1).exe (PID: 7512)
- svo (1).exe (PID: 5176)
- svo (1).exe (PID: 7220)
Application launched itself
- svo (1).exe (PID: 7748)
- svo (1).exe (PID: 4284)
- svo (1).exe (PID: 5176)
Connects to unusual port
- svo (1).exe (PID: 7220)
- svo (1).exe (PID: 7324)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 3848)
Starts CMD.EXE for commands execution
- svo (1).exe (PID: 1144)
Lists all scheduled tasks
- schtasks.exe (PID: 6368)
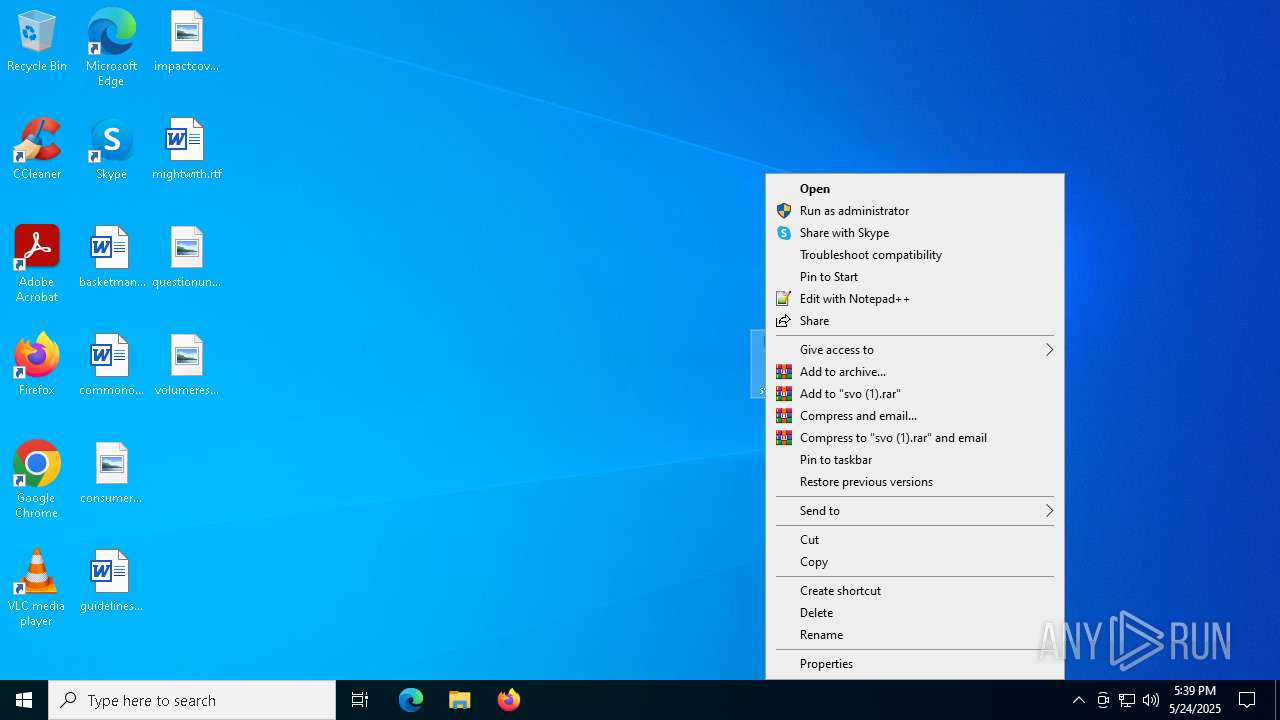
Starts itself from another location
- svo (1).exe (PID: 1144)
INFO
Reads Environment values
- identity_helper.exe (PID: 5164)
- identity_helper.exe (PID: 6252)
Reads the computer name
- identity_helper.exe (PID: 5164)
- svo (1).exe (PID: 7748)
- identity_helper.exe (PID: 6252)
- svo (1).exe (PID: 5176)
- svo (1).exe (PID: 7512)
- svo (1).exe (PID: 7220)
Checks supported languages
- identity_helper.exe (PID: 5164)
- svo (1).exe (PID: 7748)
- identity_helper.exe (PID: 6252)
- svo (1).exe (PID: 5176)
- svo (1).exe (PID: 7512)
- svo (1).exe (PID: 7220)
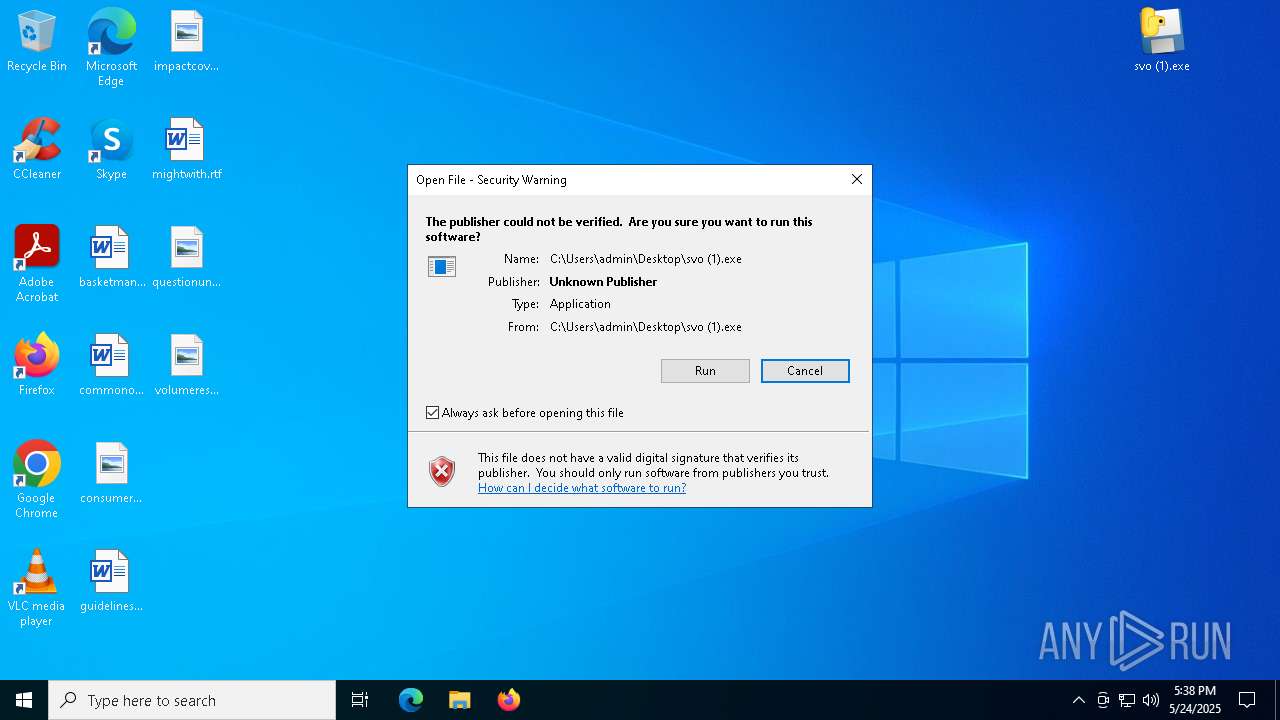
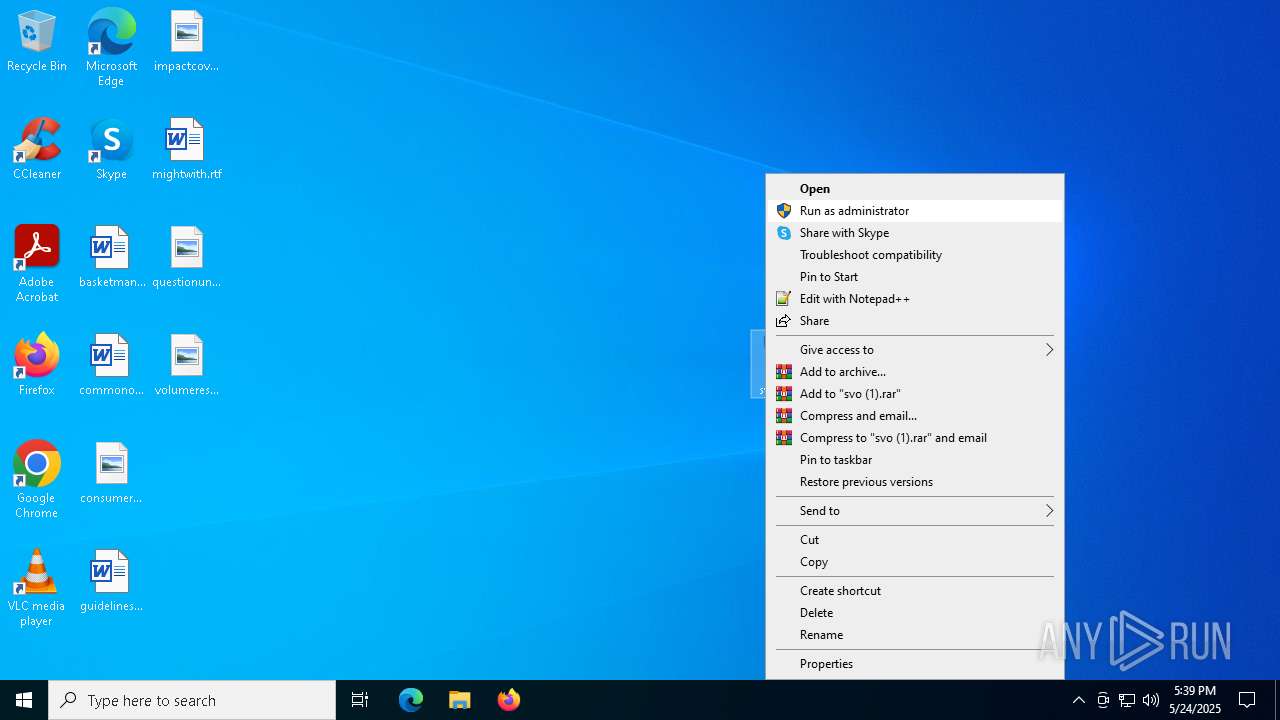
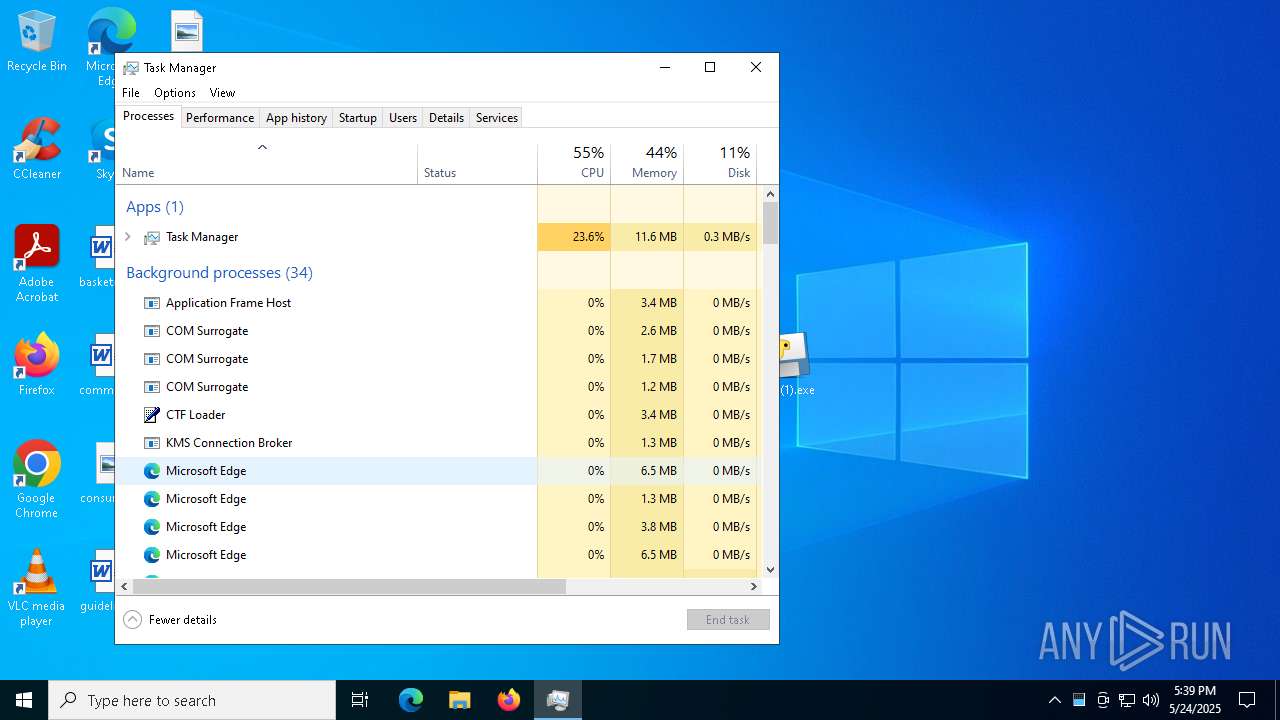
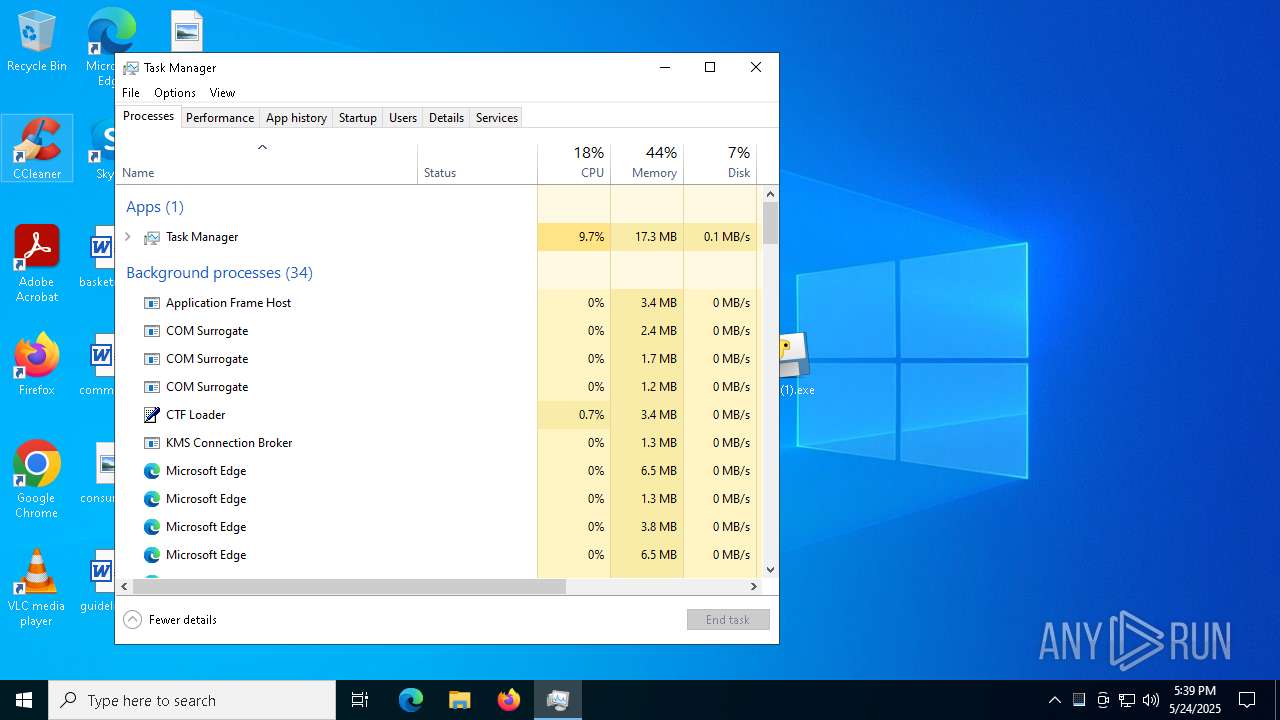
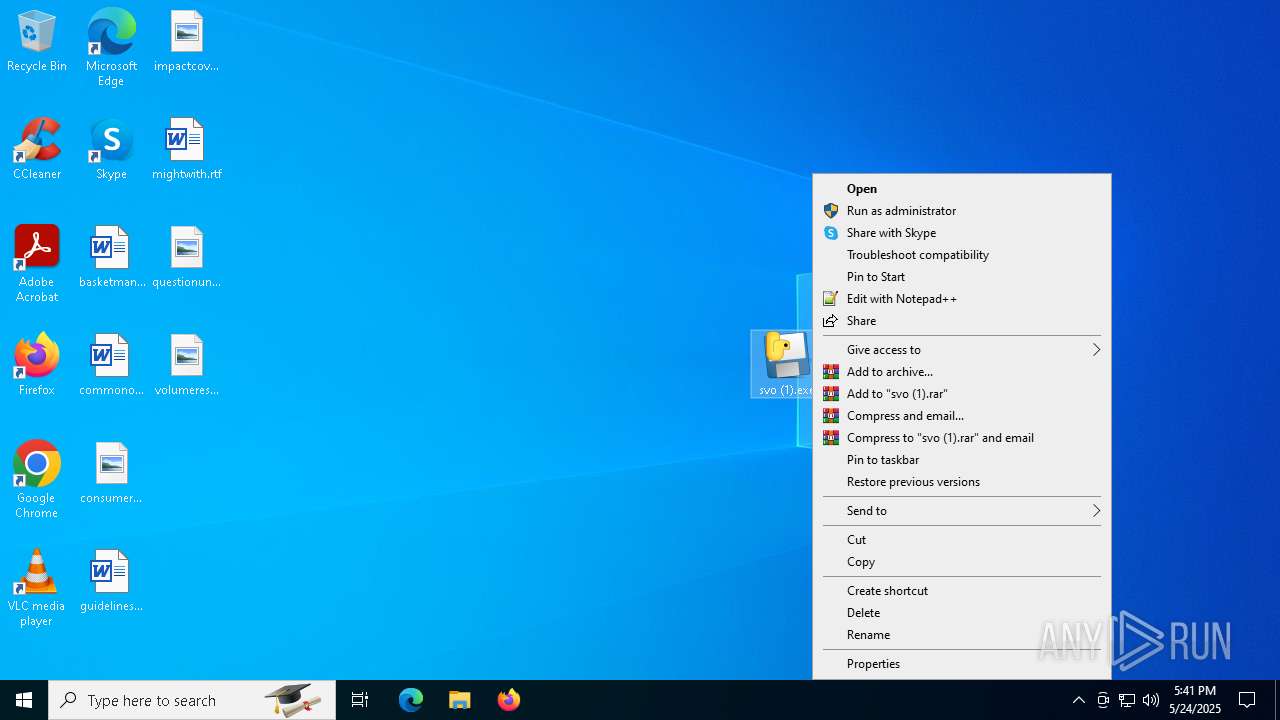
Manual execution by a user
- svo (1).exe (PID: 7748)
- svo (1).exe (PID: 5176)
- svo (1).exe (PID: 7512)
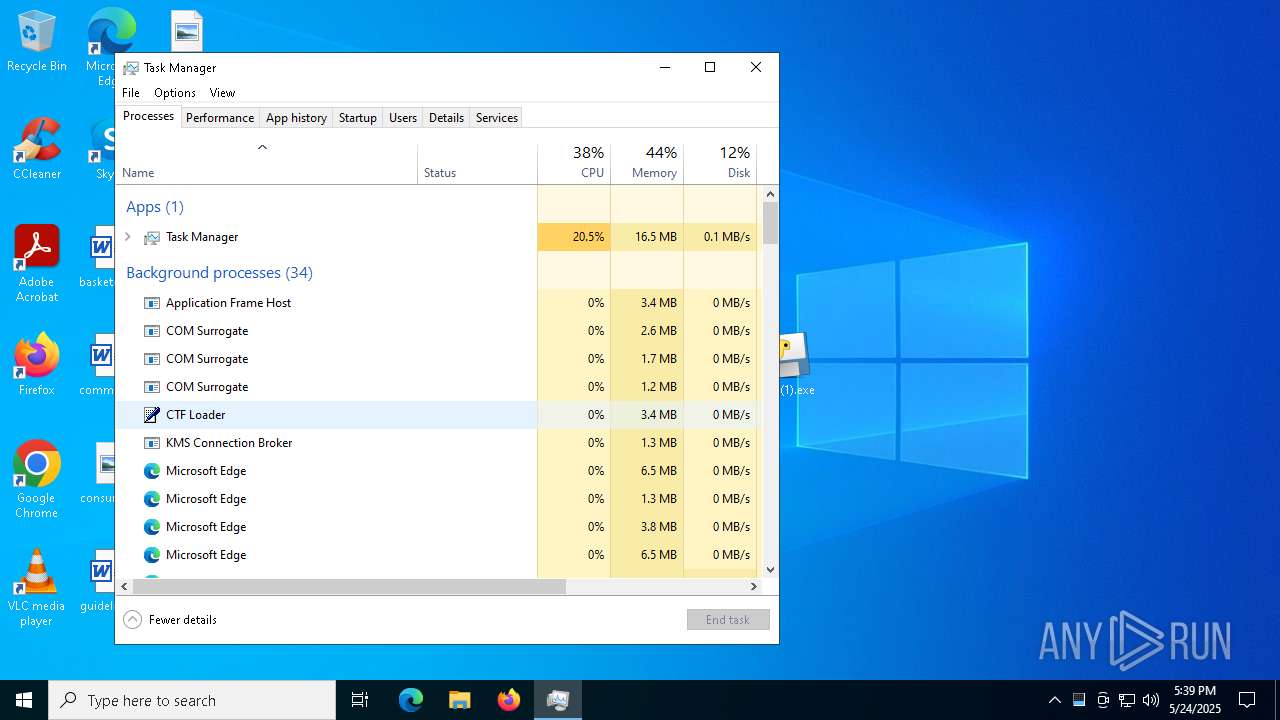
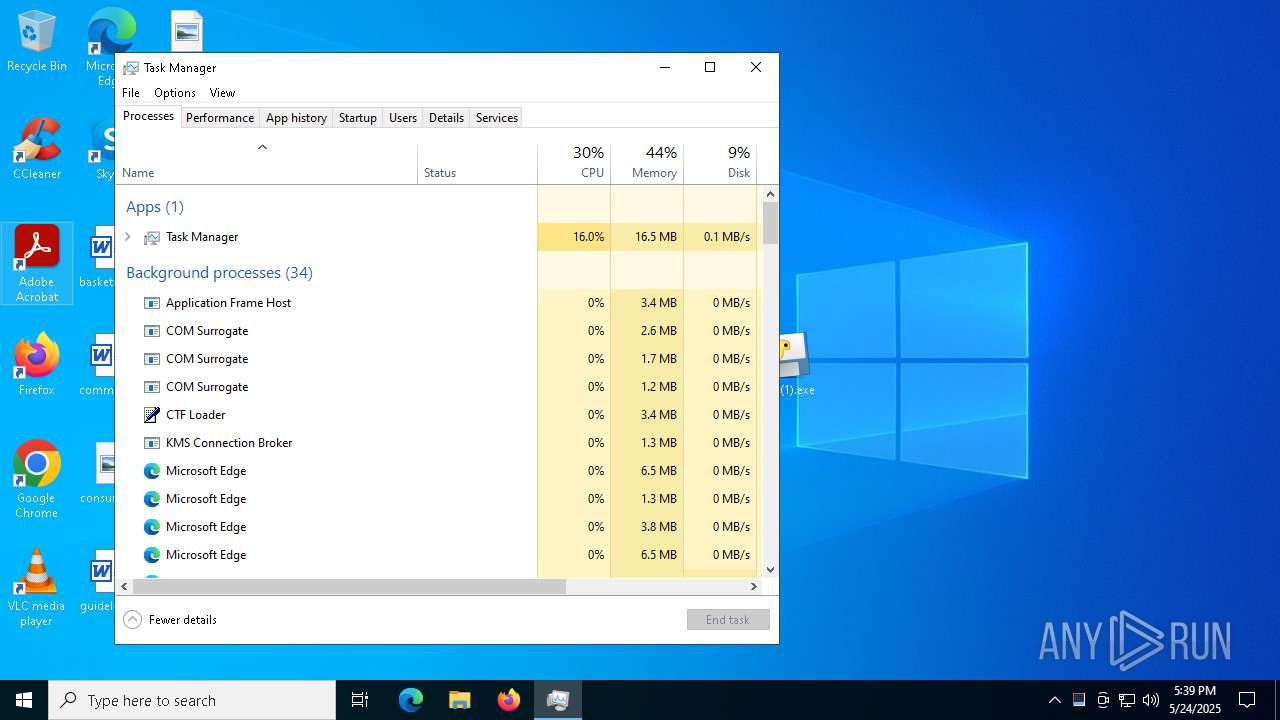
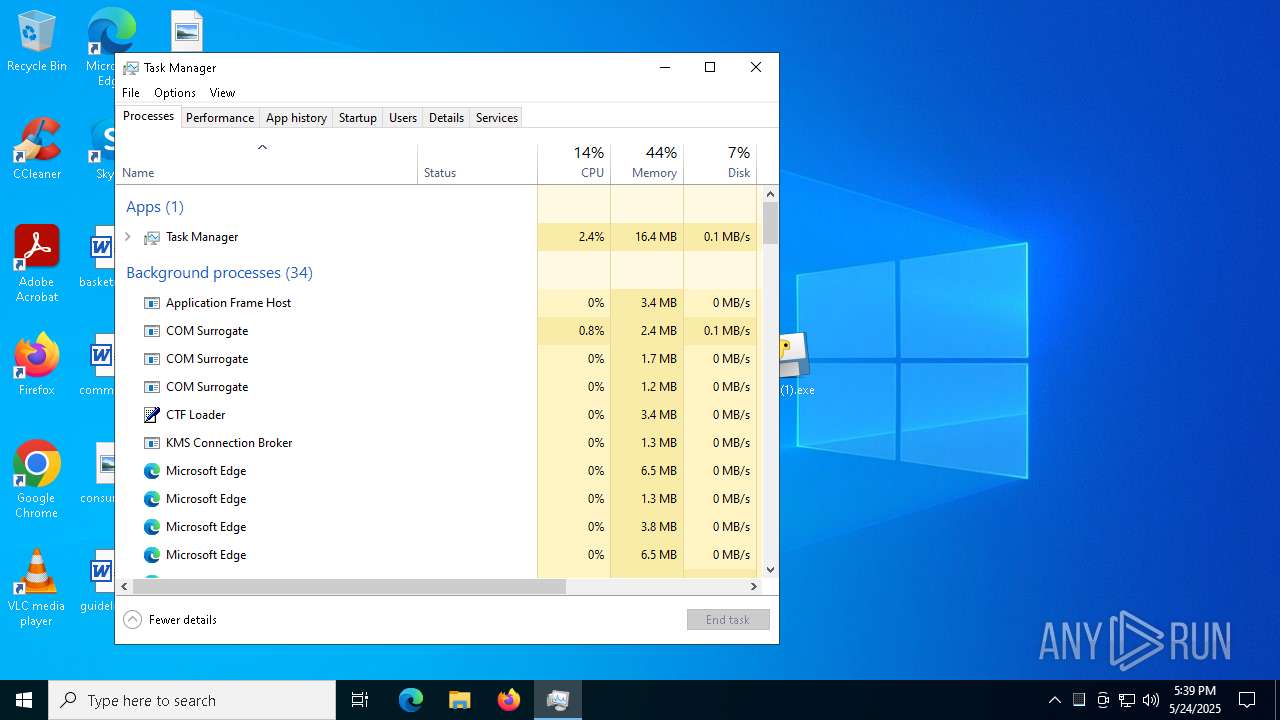
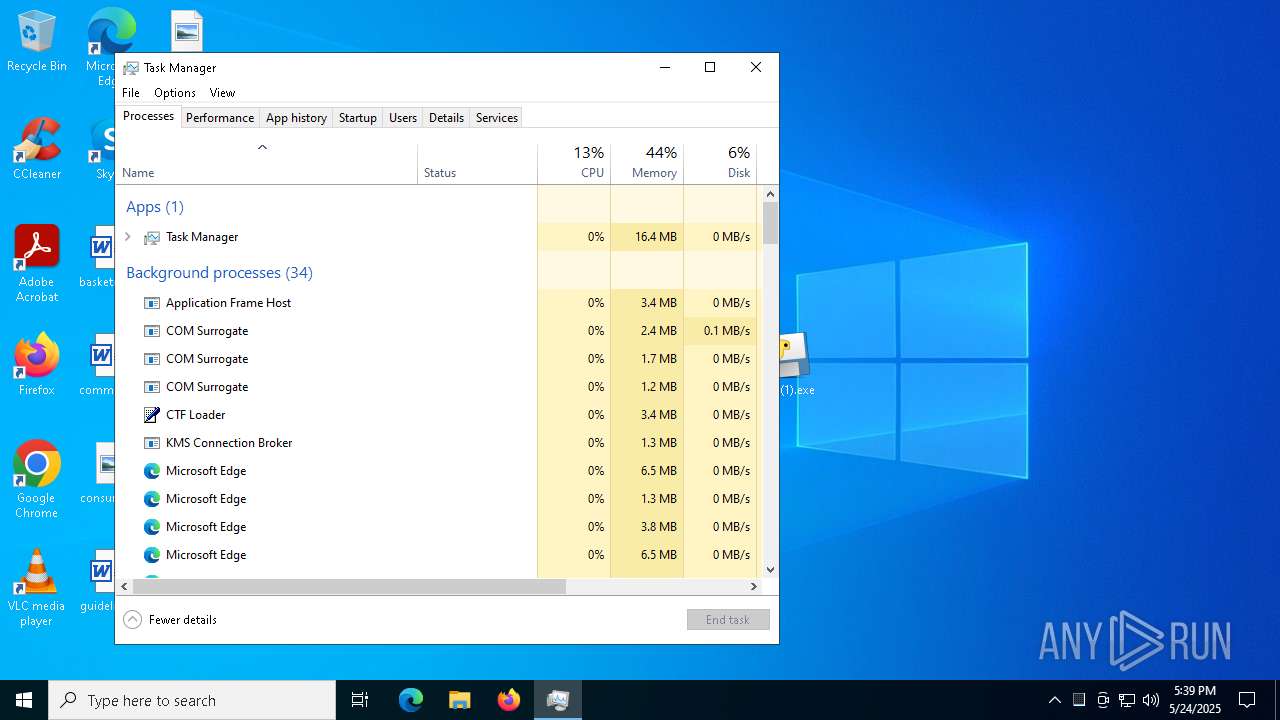
- Taskmgr.exe (PID: 7652)
- Taskmgr.exe (PID: 7552)
- svo (1).exe (PID: 4284)
Executable content was dropped or overwritten
- msedge.exe (PID: 7148)
- msedge.exe (PID: 7396)
Application launched itself
- msedge.exe (PID: 1184)
- msedge.exe (PID: 7148)
Create files in a temporary directory
- svo (1).exe (PID: 7748)
- svo (1).exe (PID: 5176)
- svo (1).exe (PID: 7512)
The sample compiled with english language support
- svo (1).exe (PID: 7748)
- svo (1).exe (PID: 5176)
- svo (1).exe (PID: 7512)
- svo (1).exe (PID: 4284)
- svchost.exe (PID: 6712)
PyInstaller has been detected (YARA)
- svo (1).exe (PID: 7748)
- svo (1).exe (PID: 5176)
- svo (1).exe (PID: 7512)
- svo (1).exe (PID: 7220)
Reads the software policy settings
- slui.exe (PID: 5048)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 7552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
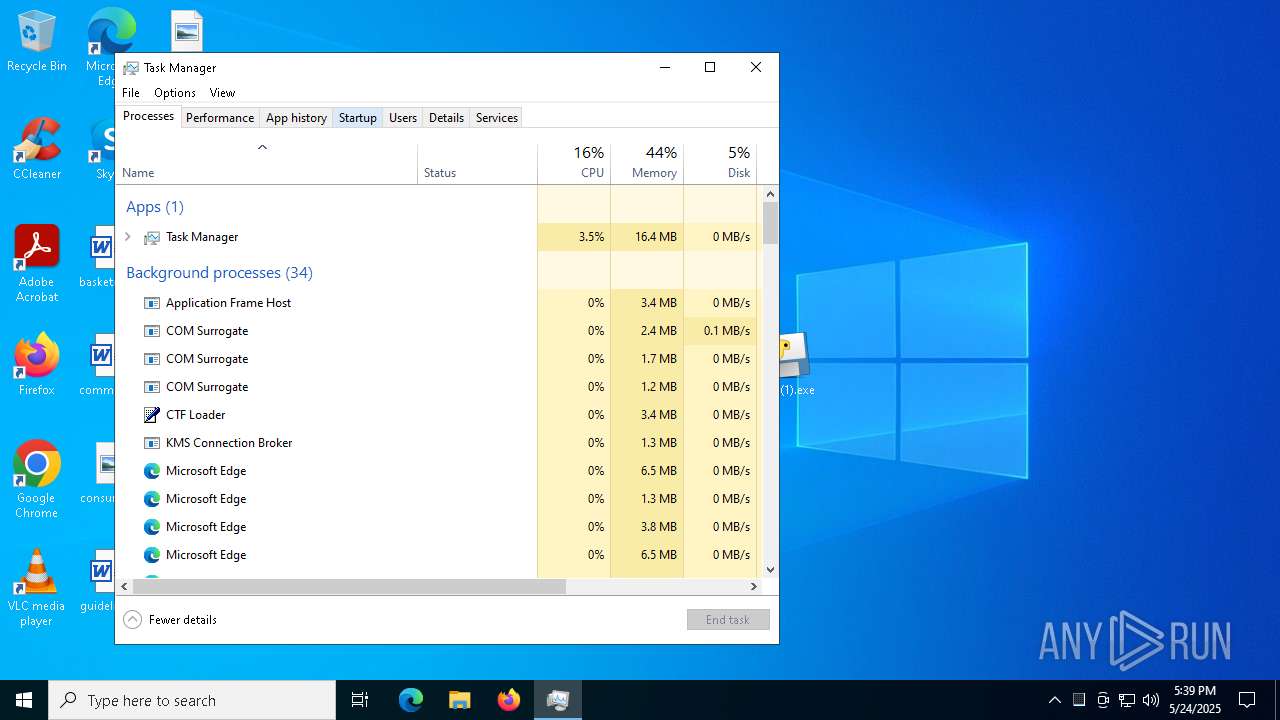
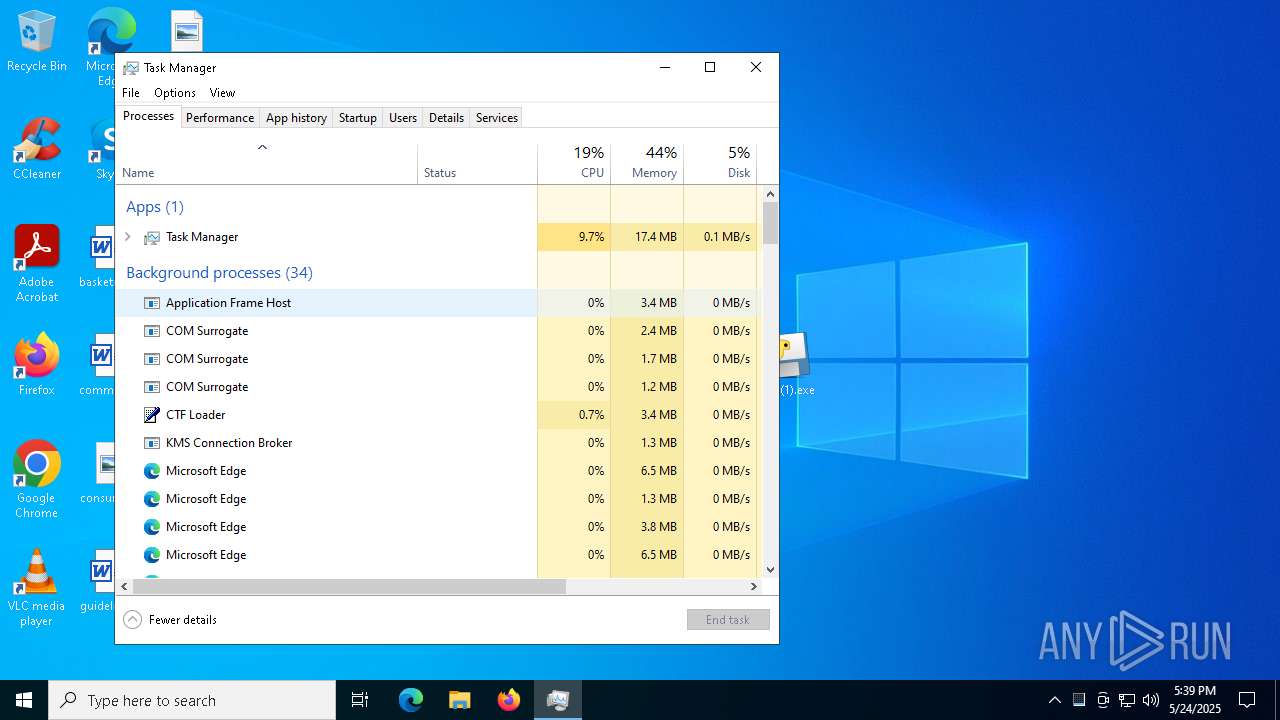
Total processes
366
Monitored processes
74
Malicious processes
2
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7040 --field-trial-handle=2396,i,12954978056768523253,8907635768297604937,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6416 --field-trial-handle=2396,i,12954978056768523253,8907635768297604937,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1020 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5316 --field-trial-handle=2340,i,2335497073241308761,7677295858487271348,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7008 --field-trial-handle=2396,i,12954978056768523253,8907635768297604937,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1144 | "C:\Users\admin\Desktop\svo (1).exe" | C:\Users\admin\Desktop\svo (1).exe | svo (1).exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1184 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1228 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7072 --field-trial-handle=2396,i,12954978056768523253,8907635768297604937,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1272 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4848 --field-trial-handle=2340,i,2335497073241308761,7677295858487271348,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1348 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6992 --field-trial-handle=2396,i,12954978056768523253,8907635768297604937,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1568 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5168 --field-trial-handle=2340,i,2335497073241308761,7677295858487271348,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
12 297
Read events
12 255
Write events
41
Delete events
1
Modification events
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A4A342757B942F00 | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197208 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A855C013-62EC-4BB0-B7B7-B89C9BBC140A} | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197208 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B7104C1D-9B4A-4E54-8286-F0244488DA45} | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197208 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {92DB9C6C-FE44-43F3-9B16-3816DE96CA1C} | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197208 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {BB091602-BF33-4805-9B37-BBBE77F9DA06} | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: DEC135757B942F00 | |||
Executable files
164
Suspicious files
197
Text files
4 631
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bc7c.TMP | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bc7c.TMP | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bc9b.TMP | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bcab.TMP | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bcba.TMP | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
129
DNS requests
81
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
864 | svchost.exe | HEAD | 200 | 208.89.74.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748302680&P2=404&P3=2&P4=RJy%2baesoLrBRYvxbJthT5iW9TCetbXVPJJoFHxdzXsMbJcKZMRlwk6o2LvpJLhGbiQ14w1gPWi4hKLzhqfhggA%3d%3d | unknown | — | — | whitelisted |
8188 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8188 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
864 | svchost.exe | GET | 206 | 208.89.74.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748302680&P2=404&P3=2&P4=RJy%2baesoLrBRYvxbJthT5iW9TCetbXVPJJoFHxdzXsMbJcKZMRlwk6o2LvpJLhGbiQ14w1gPWi4hKLzhqfhggA%3d%3d | unknown | — | — | whitelisted |
708 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
5296 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6084 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7396 | msedge.exe | 193.111.198.62:443 | workupload.com | myLoc managed IT AG | DE | whitelisted |
7396 | msedge.exe | 142.250.185.130:443 | googleads.g.doubleclick.net | — | — | whitelisted |
7396 | msedge.exe | 142.250.186.66:443 | pagead2.googlesyndication.com | — | — | whitelisted |
7148 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7396 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
workupload.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected domain Associated with Malware Distribution (.ply .gg) |
2196 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES Tunneling Service in DNS Lookup (* .ply .gg) |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO playit .gg Tunneling Domain in DNS Lookup |
2196 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected domain Associated with Malware Distribution (.ply .gg) |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO playit .gg Tunneling Domain in DNS Lookup |
2196 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES Tunneling Service in DNS Lookup (* .ply .gg) |