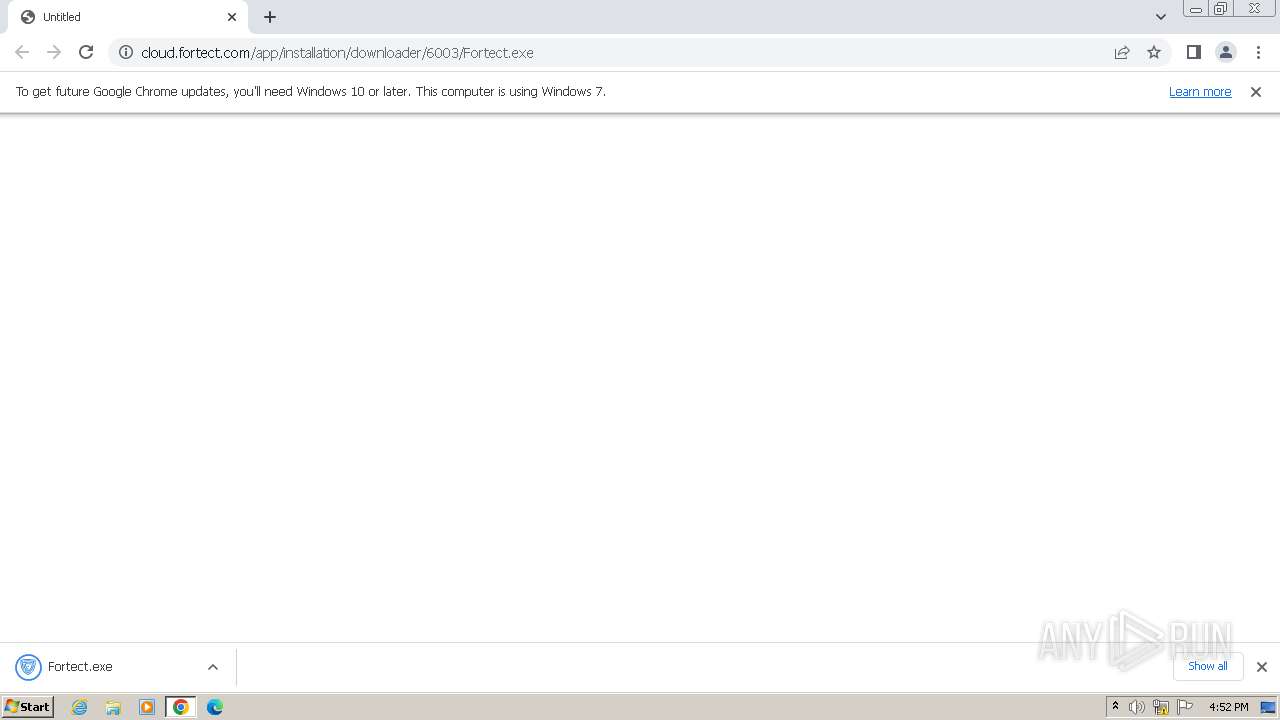
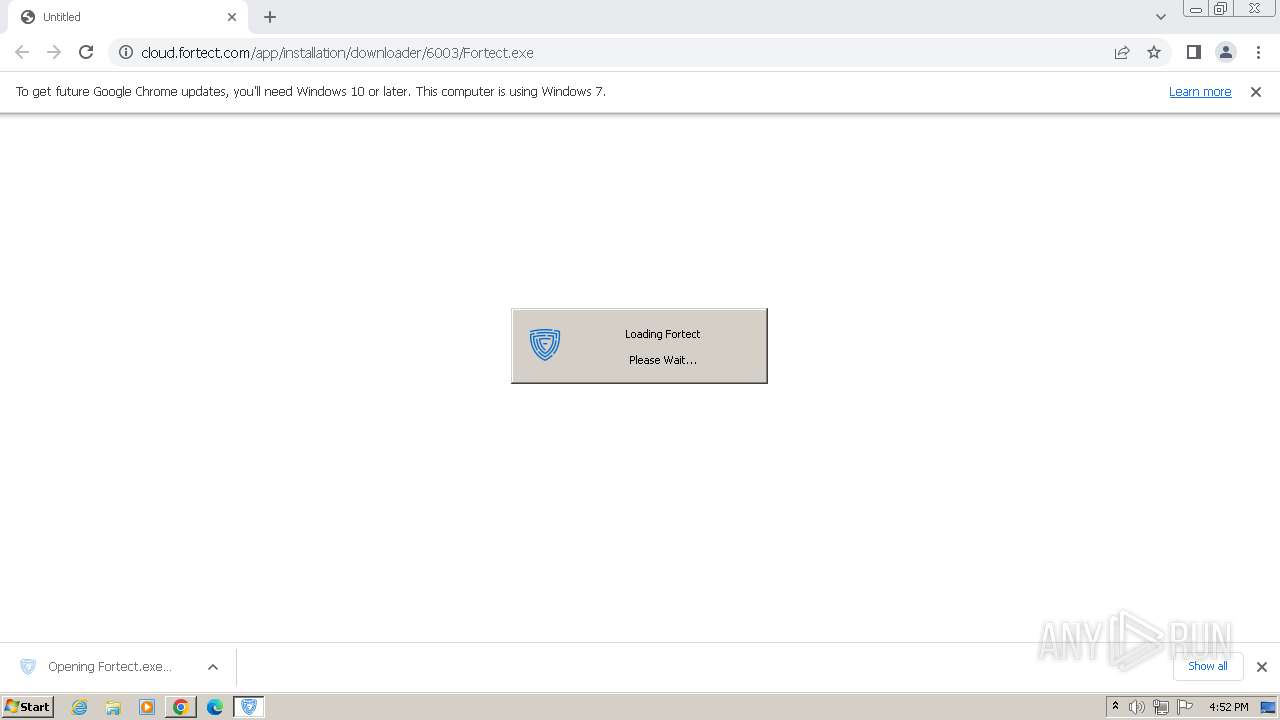
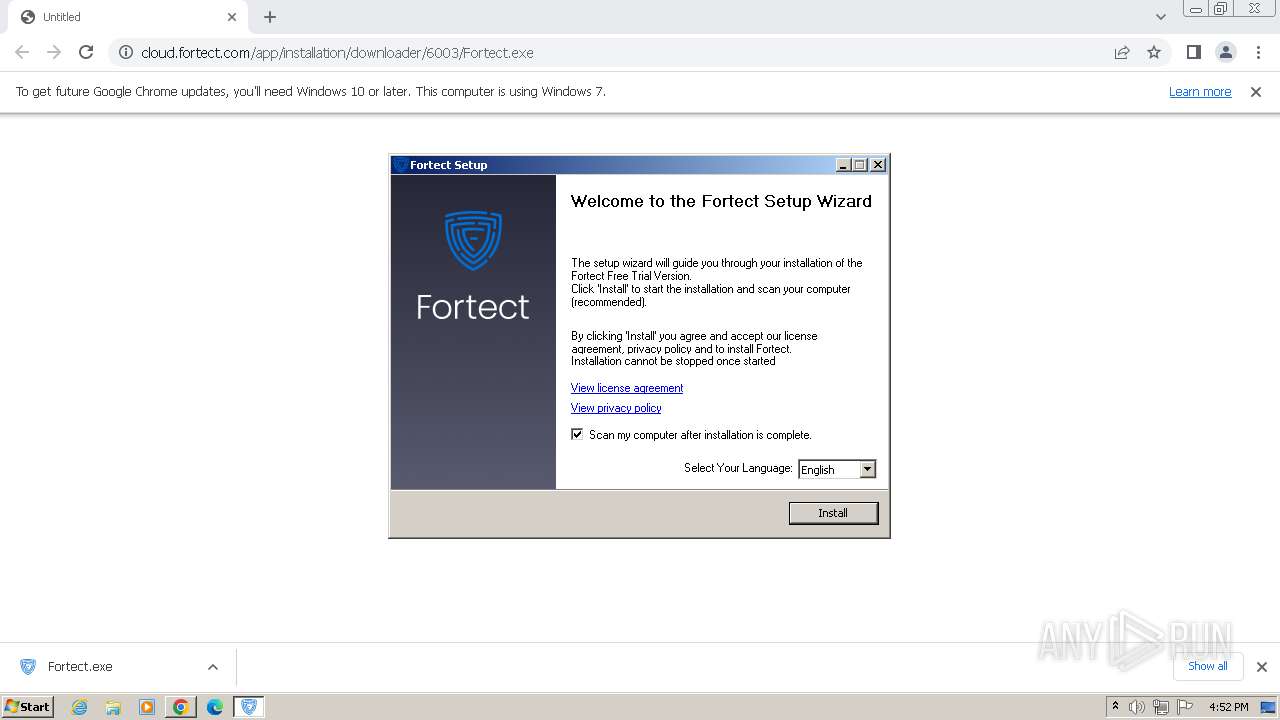
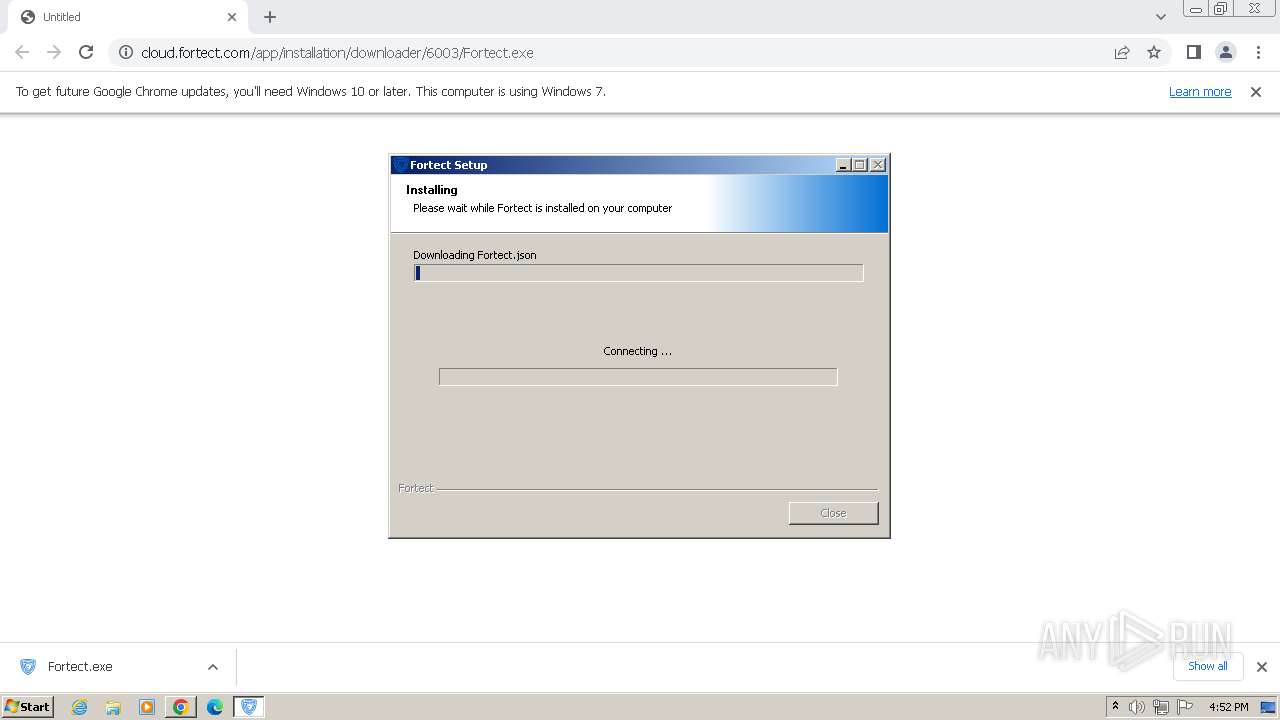
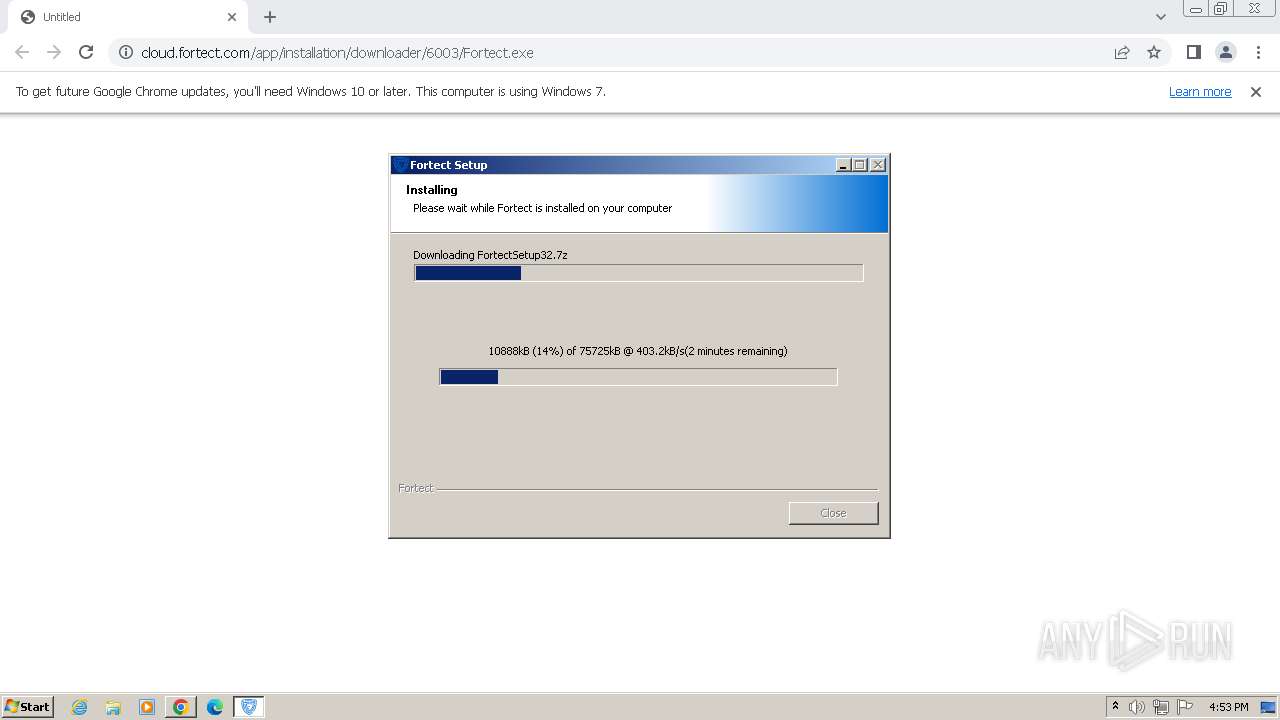
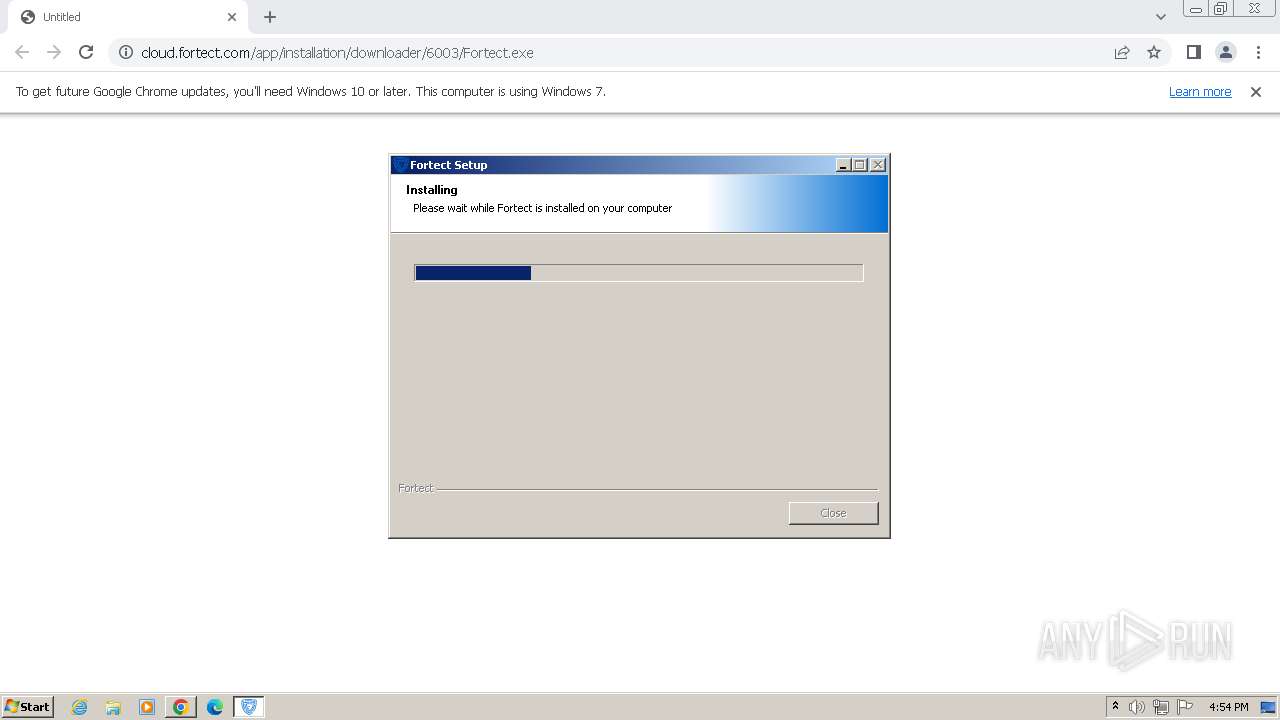
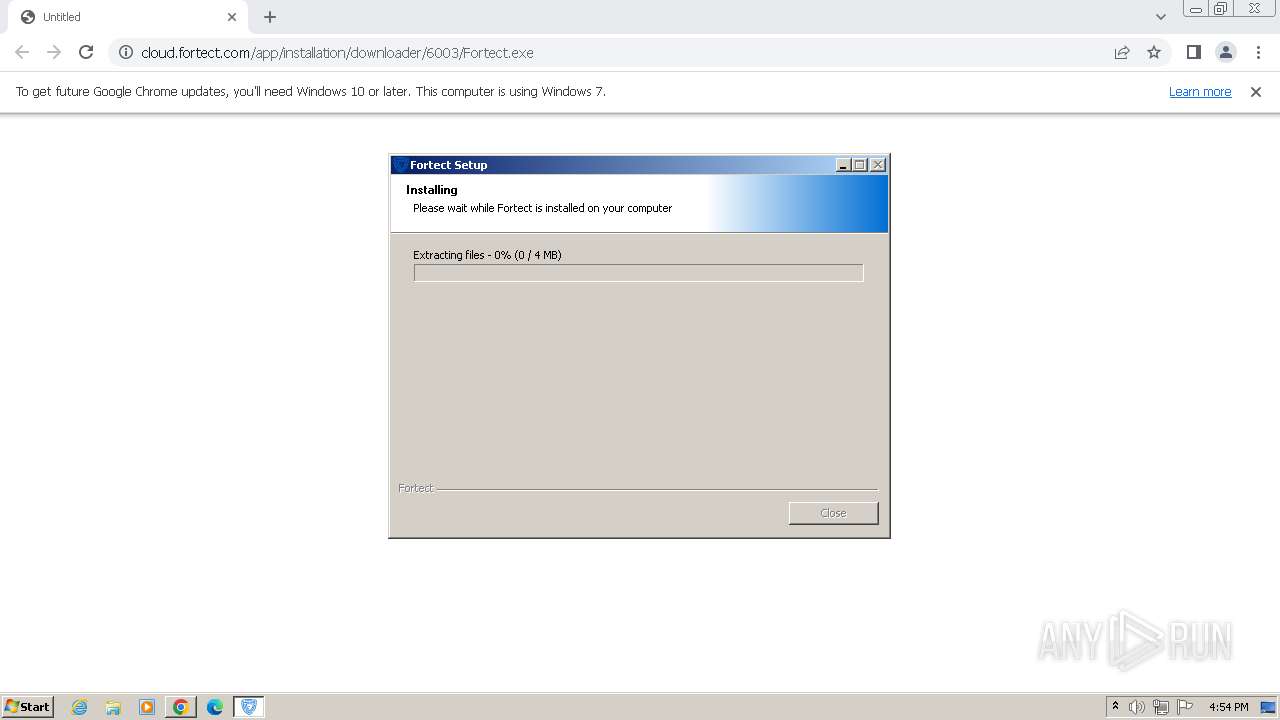
| URL: | https://cloud.fortect.com/app/installation/downloader/6003/Fortect.exe |
| Full analysis: | https://app.any.run/tasks/2238246d-7baa-4b12-bacd-50437d8c0daa |
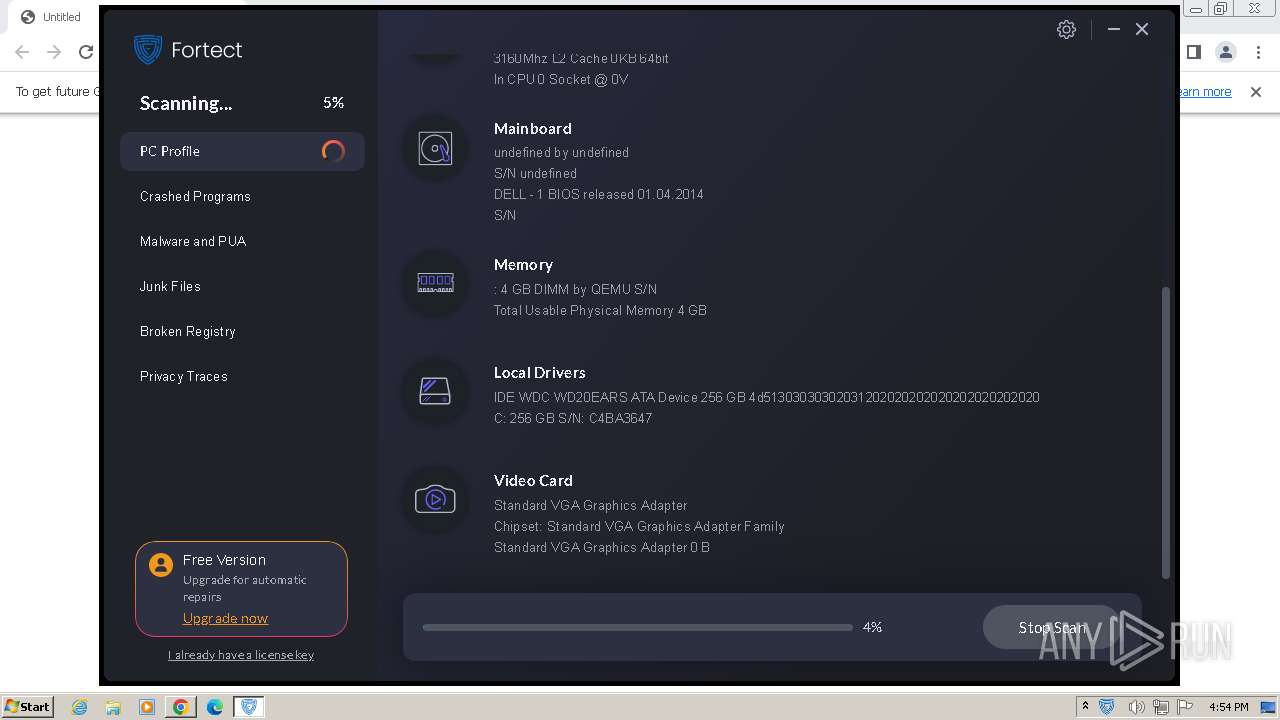
| Verdict: | Malicious activity |
| Analysis date: | November 09, 2023, 16:52:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| SHA1: | 596F351EDE3684AAE57795806AB35CCEDC11FE70 |
| SHA256: | 5103B63DFB90E17BF0D0A548609791F2135432BBD3E70A32CB1763C06115681A |
| SSDEEP: | 3:N8ULBLQX5EJKRL+yXo8hjOA:2UBKRLzhD |
MALICIOUS
Drops the executable file immediately after the start
- Fortect.exe (PID: 2636)
- FortectMain.exe (PID: 2708)
Actions looks like stealing of personal data
- MainService.exe (PID: 476)
SUSPICIOUS
The process creates files with name similar to system file names
- Fortect.exe (PID: 2636)
Starts CMD.EXE for commands execution
- Fortect.exe (PID: 2636)
Uses WMIC.EXE to obtain BIOS management information
- cmd.exe (PID: 1928)
Reads the Internet Settings
- WMIC.exe (PID: 328)
- WMIC.exe (PID: 1848)
- WMIC.exe (PID: 1416)
- Fortect.exe (PID: 2636)
- WMIC.exe (PID: 1068)
- FortectMain.exe (PID: 2708)
Uses WMIC.EXE to obtain data on the partitioned areas of a physical disk
- Fortect.exe (PID: 2636)
Accesses computer name via WMI (SCRIPT)
- WMIC.exe (PID: 1848)
Uses WMIC.EXE to obtain physical disk drive information
- Fortect.exe (PID: 2636)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 1460)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 1068)
Reads security settings of Internet Explorer
- Fortect.exe (PID: 2636)
- MainDaemon.exe (PID: 556)
Checks Windows Trust Settings
- Fortect.exe (PID: 2636)
- MainDaemon.exe (PID: 556)
- MainService.exe (PID: 476)
Reads settings of System Certificates
- Fortect.exe (PID: 2636)
- MainDaemon.exe (PID: 556)
- FortectMain.exe (PID: 2708)
Drops 7-zip archiver for unpacking
- Fortect.exe (PID: 2636)
Process drops legitimate windows executable
- Fortect.exe (PID: 2636)
Executes as Windows Service
- MainDaemon.exe (PID: 1880)
- MainService.exe (PID: 476)
Searches for installed software
- MainDaemon.exe (PID: 1880)
- MainService.exe (PID: 476)
Application launched itself
- FortectMain.exe (PID: 2708)
Reads Internet Explorer settings
- MainService.exe (PID: 476)
Reads Microsoft Outlook installation path
- MainService.exe (PID: 476)
INFO
Drops the executable file immediately after the start
- chrome.exe (PID: 3460)
Reads the computer name
- wmpnscfg.exe (PID: 1924)
- Fortect.exe (PID: 2636)
- MainDaemon.exe (PID: 556)
- MainDaemon.exe (PID: 1880)
- MainService.exe (PID: 3824)
- FortectMain.exe (PID: 2708)
- FortectMain.exe (PID: 1952)
- FortectMain.exe (PID: 2300)
- FortectMain.exe (PID: 3316)
- wmpnscfg.exe (PID: 3888)
- MainService.exe (PID: 476)
The process uses the downloaded file
- chrome.exe (PID: 3548)
- chrome.exe (PID: 3460)
- chrome.exe (PID: 3856)
- chrome.exe (PID: 2548)
- Fortect.exe (PID: 2636)
- chrome.exe (PID: 3032)
Manual execution by a user
- wmpnscfg.exe (PID: 1924)
- FortectMain.exe (PID: 2708)
- wmpnscfg.exe (PID: 3888)
Checks supported languages
- wmpnscfg.exe (PID: 1924)
- Fortect.exe (PID: 2636)
- MainDaemon.exe (PID: 556)
- MainDaemon.exe (PID: 1880)
- MainService.exe (PID: 3824)
- FortectTray.exe (PID: 1420)
- FortectMain.exe (PID: 2708)
- FortectMain.exe (PID: 1952)
- FortectMain.exe (PID: 2300)
- FortectMain.exe (PID: 3000)
- FortectMain.exe (PID: 3316)
- wmpnscfg.exe (PID: 3888)
- MainService.exe (PID: 476)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 1924)
- Fortect.exe (PID: 2636)
- MainDaemon.exe (PID: 556)
- MainService.exe (PID: 476)
- MainDaemon.exe (PID: 1880)
- FortectMain.exe (PID: 2708)
- wmpnscfg.exe (PID: 3888)
Create files in a temporary directory
- Fortect.exe (PID: 2636)
- FortectMain.exe (PID: 2708)
Reads Environment values
- Fortect.exe (PID: 2636)
- MainDaemon.exe (PID: 556)
- MainService.exe (PID: 3824)
- MainService.exe (PID: 476)
- MainDaemon.exe (PID: 1880)
- FortectMain.exe (PID: 2708)
Application launched itself
- chrome.exe (PID: 3460)
Checks proxy server information
- Fortect.exe (PID: 2636)
Creates files or folders in the user directory
- Fortect.exe (PID: 2636)
- FortectMain.exe (PID: 2708)
- FortectMain.exe (PID: 2300)
Creates files in the program directory
- Fortect.exe (PID: 2636)
- MainDaemon.exe (PID: 556)
- MainDaemon.exe (PID: 1880)
- MainService.exe (PID: 3824)
- MainService.exe (PID: 476)
Dropped object may contain TOR URL's
- Fortect.exe (PID: 2636)
Reads product name
- FortectMain.exe (PID: 2708)
Process checks computer location settings
- FortectMain.exe (PID: 3000)
- FortectMain.exe (PID: 2708)
- MainService.exe (PID: 476)
Reads mouse settings
- MainService.exe (PID: 476)
Process checks the number of cached credentials
- MainService.exe (PID: 476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
92
Monitored processes
44
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 328 | C:\Windows\System32\wbem\wmic.exe path Win32_BIOS get SerialNumber | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 476 | "C:\Program Files\Fortect\MainService.exe" | C:\Program Files\Fortect\MainService.exe | services.exe | ||||||||||||
User: SYSTEM Company: Fortect LTD. Integrity Level: SYSTEM Description: Fortect Service Exit code: 0 Version: 6.0.0.3 Modules
| |||||||||||||||
| 556 | "C:\Program Files\Fortect\bin\MainDaemon.exe" --install | C:\Program Files\Fortect\bin\MainDaemon.exe | Fortect.exe | ||||||||||||
User: admin Company: Fortect Ltd. Integrity Level: HIGH Description: Fortect Daemon Exit code: 0 Version: 6.0.0.3 Modules
| |||||||||||||||
| 1068 | C:\Windows\System32\wbem\wmic.exe path Win32_ComputerSystemProduct get UUID | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2868 --field-trial-handle=1172,i,1917692877429765178,774400163305634274,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1416 | "C:\Windows\system32\wbem\wmic.exe" diskdrive where "DeviceID like '%%PHYSICALDRIVE0'" get SerialNumber | C:\Windows\System32\wbem\WMIC.exe | — | Fortect.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1420 | "C:\Program Files\Fortect\bin\FortectTray.exe" | C:\Program Files\Fortect\bin\FortectTray.exe | — | Fortect.exe | |||||||||||
User: admin Company: Fortect Ltd. Integrity Level: HIGH Description: Fortect Tray App Exit code: 0 Version: 6.0.0.3 Modules
| |||||||||||||||
| 1460 | C:\Windows\system32\cmd.exe /Q /C "%SYSTEMROOT%\System32\wbem\wmic.exe" path Win32_ComputerSystemProduct get UUID | C:\Windows\System32\cmd.exe | — | Fortect.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1396 --field-trial-handle=1172,i,1917692877429765178,774400163305634274,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1640 | "C:\Users\admin\Downloads\Fortect.exe" | C:\Users\admin\Downloads\Fortect.exe | — | chrome.exe | |||||||||||
User: admin Company: Fortect Integrity Level: MEDIUM Description: Fortect Setup Exit code: 3221226540 Version: 6.0.0.3 Modules
| |||||||||||||||
Total events
98 284
Read events
98 069
Write events
209
Delete events
6
Modification events
| (PID) Process: | (3460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (3460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3460) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (3460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
61
Suspicious files
258
Text files
93
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF166bce.TMP | — | |
MD5:— | SHA256:— | |||
| 3460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:65635E713D5CFC914717D1CC4CAC6989 | SHA256:4CB3EEB0369758290ABD7868DFD85D663C4AEF6C727FFF43BE693FDDBD0A6C28 | |||
| 3460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF166ebc.TMP | — | |
MD5:— | SHA256:— | |||
| 3460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:E91E138A25FD7E5BCA5E60111F39C91A | SHA256:B1F7E3537A31A4B847F862858E5D2581993CC9372F19ABF19EA2A9185FE42A4F | |||
| 3460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF166bde.TMP | text | |
MD5:CDCC923CEC2CD9228330551E6946A9C2 | SHA256:592F4750166BE662AA88728F9969537163FEC5C3E95E81537C8C6917F8D0929E | |||
| 3460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | text | |
MD5:A5EB529D94D3E97D0EE4A7E07700E0B2 | SHA256:08D211BFC570221AF7995C0625052FA7848F7E707D559C266656CDC3A9CC9F9C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
86
DNS requests
29
Threats
37
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2636 | Fortect.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | binary | 8.38 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 43.3 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 17.8 Kb | unknown |
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 8.38 Kb | unknown |
476 | MainService.exe | GET | 200 | 50.56.4.183:80 | http://cloud.toppcprotection.com/lib/cloud-scan.php?param1=ZEScRsYVkvvS+DjNihSFOedWEQGf1iiVRYVRPnYdvckQMO3Z0Vb8nQI/ySOYBAWoUDJUHEm3TXfl31jnjOKaM2SywjxNX8QG99JbPOImZ3LUFKhafiCFSQSwL60I+Rjwo0Y5XYkLQ+UNL7FRSjofDe7JJ/2gy/qsi76//Hw2ZoFgCw7fM4QK1+u6XW6ExqPsgHMwQzXgslSTHNtr3wtb8Q== | unknown | text | 64 b | unknown |
476 | MainService.exe | GET | 200 | 50.56.4.183:80 | http://cloud.toppcprotection.com/lib/cloud-scan.php?param1=ZEScRsYVkvvS+DjNihSFOZRgvNejhp6VC7ewqln7NvL9N5t1753spCPTDsk+LR2mN9VIUHbmkwYBRtDwKP/vm4E23AQzo5rZy9teb4UYqIKCYqLNJbuEMrI+YVkZqZboce8425JUv79Lmo57jyvymJhgX7392vLakzCRml5Wr7h24xAv8ip6p7T6qaK1ZGhe | unknown | text | 64 b | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | binary | 10.9 Kb | unknown |
476 | MainService.exe | GET | 200 | 50.56.4.183:80 | http://cloud.toppcprotection.com/lib/cloud-scan.php?param1=ZEScRsYVkvvS+DjNihSFObBSEJm7DewGK76AkTDWW8XME0IM5inVRnBjKTSS+724lNJ0UyG8yXbOR6sYRYgm5Vh/TALBdsRTjnSuWR4U9RYI2uKiSF85RvfJK80QEVjWjKRHeJhGNWLgXFc++4Ec4dC195ExG+s6KsRA7FQXXoc= | unknown | text | 64 b | unknown |
476 | MainService.exe | GET | 200 | 50.56.4.183:80 | http://cloud.toppcprotection.com/lib/cloud-scan.php?param1=ZEScRsYVkvvS+DjNihSFOYNvcacLUcHJCiIbCkhU8pqq6LrlsIQb9DeYPZSEioAjvppBpHy+vDnzE94pXNMlXJ/HNXFUC4O6GTKEiuFHXRtDaQJ3DBa5LRDBFPZbuQzlG1GWiO/feASncLxUvv8TUvRTecjJY5tFHxt5tVq4h6lSA7xg/yWApN+EobKIHl0PzwbhRrIL6ylRau5D7bmyDw== | unknown | text | 64 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3460 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3612 | chrome.exe | 142.250.185.109:443 | accounts.google.com | GOOGLE | US | unknown |
3612 | chrome.exe | 104.26.2.16:443 | cloud.fortect.com | CLOUDFLARENET | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3460 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
3612 | chrome.exe | 142.250.185.238:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3612 | chrome.exe | 142.250.185.196:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
cloud.fortect.com |
| unknown |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| whitelisted |
optimizationguide-pa.googleapis.com |
| whitelisted |
app.fortect.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.googleapis.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3612 | chrome.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed DNS Query to PC Optimizer Software Domain (fortect .com) |
3612 | chrome.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed DNS Query to PC Optimizer Software Domain (fortect .com) |
3612 | chrome.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed PC Optimizer Software Domain (fortect .com in TLS SNI) |
1080 | svchost.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed DNS Query to PC Optimizer Software Domain (fortect .com) |
2636 | Fortect.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed PC Optimizer Software Domain (fortect .com in TLS SNI) |
1080 | svchost.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed DNS Query to PC Optimizer Software Domain (fortect .com) |
2636 | Fortect.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed PC Optimizer Software Domain (fortect .com in TLS SNI) |
1080 | svchost.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed DNS Query to PC Optimizer Software Domain (fortect .com) |
556 | MainDaemon.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed PC Optimizer Software Domain (fortect .com in TLS SNI) |
556 | MainDaemon.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed PC Optimizer Software Domain (fortect .com in TLS SNI) |
Process | Message |
|---|---|
Fortect.exe | ExecShellAsUser: got desktop |
Fortect.exe | ExecShellAsUser: elevated process detected |
Fortect.exe | ExecShellAsUser: thread finished |
Fortect.exe | ExecShellAsUser: DLL_PROCESS_DETACH |