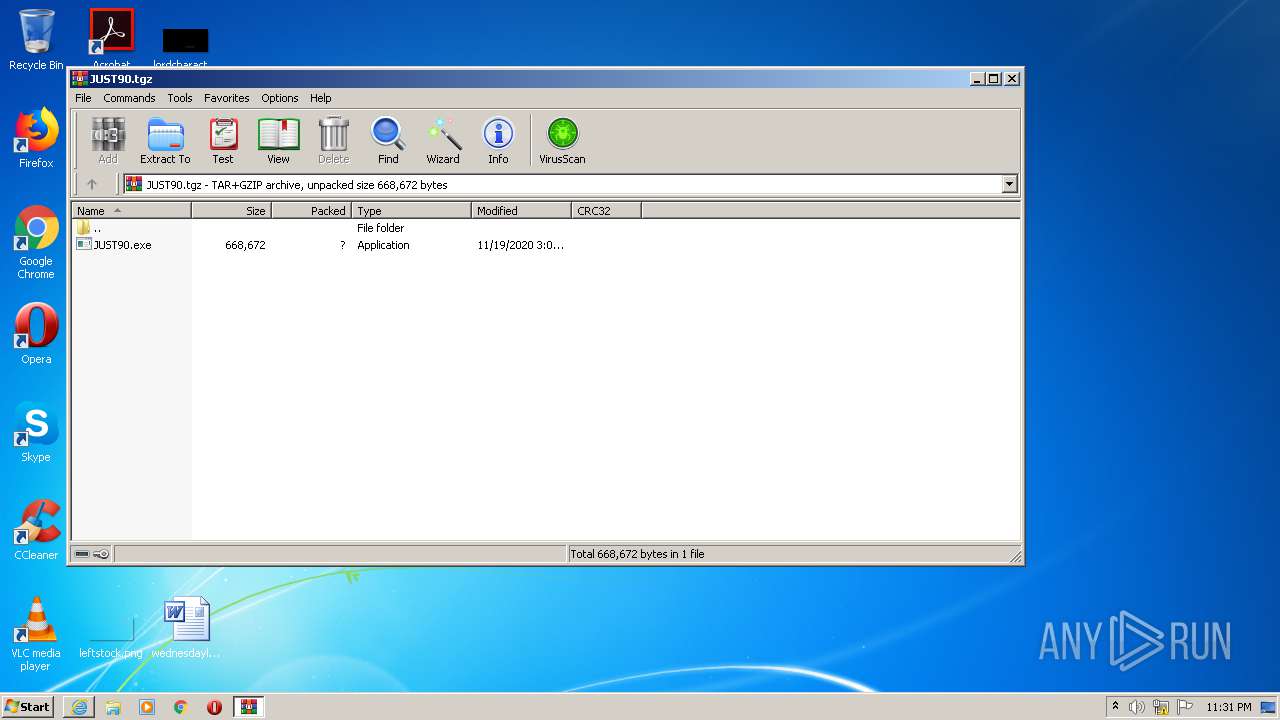
| URL: | http://www.mediafire.com/file/4diaf0cqb0vappn/JUST90.tgz/file |
| Full analysis: | https://app.any.run/tasks/fb1008eb-2ee2-4019-8e36-8628c4078d59 |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 23:28:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
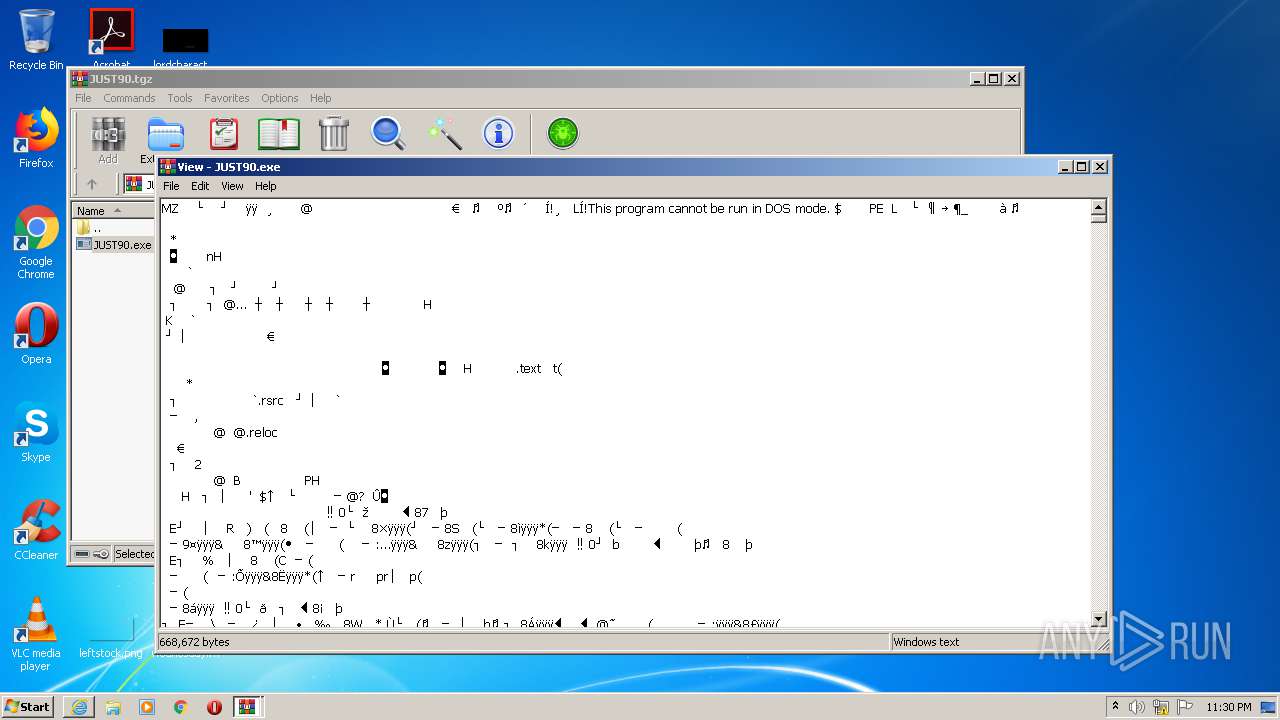
| MD5: | 4DEE727F8990566BD11752B89A95EF97 |
| SHA1: | 185E29D58E2A4E506BF0C8932F548FFC7FB26662 |
| SHA256: | 50E2DE879C4936A777BF6A77A777BEAF5613F5190E0C708D8778F4AB402156AB |
| SSDEEP: | 3:N1KJS4w3eGUoRAe5E/LKlCRsO:Cc4w3eG1viKlCqO |
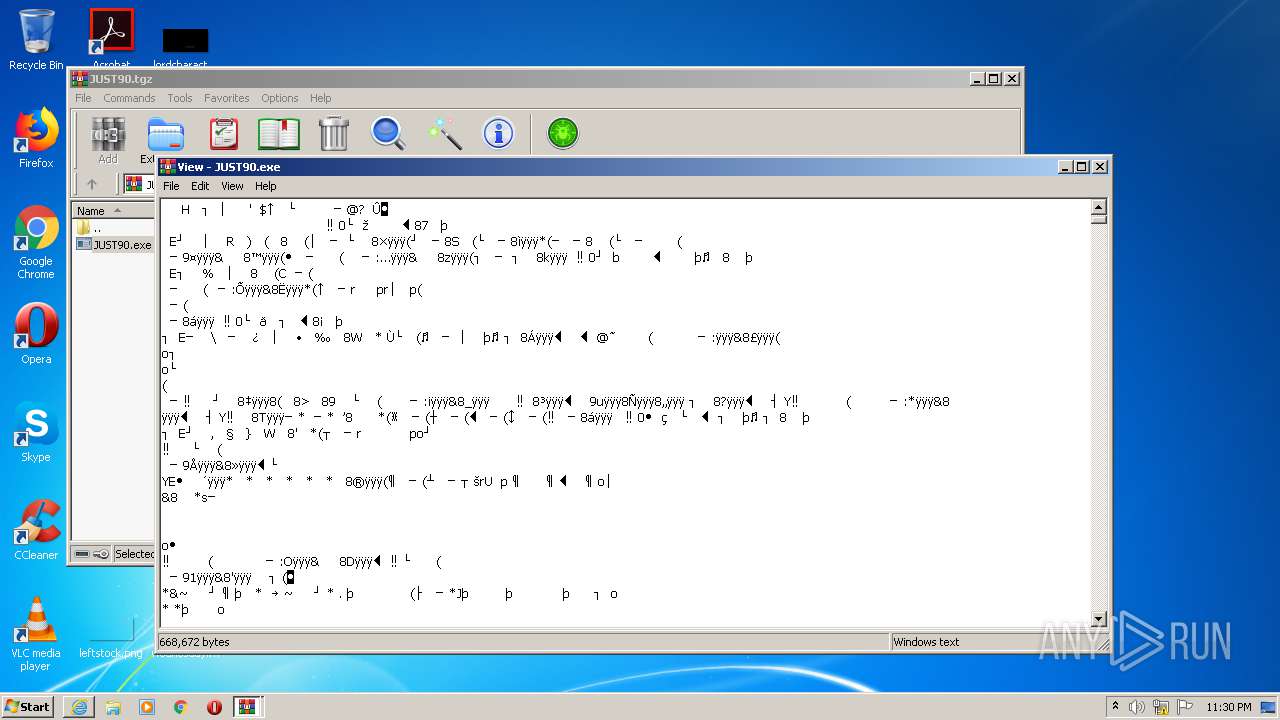
MALICIOUS
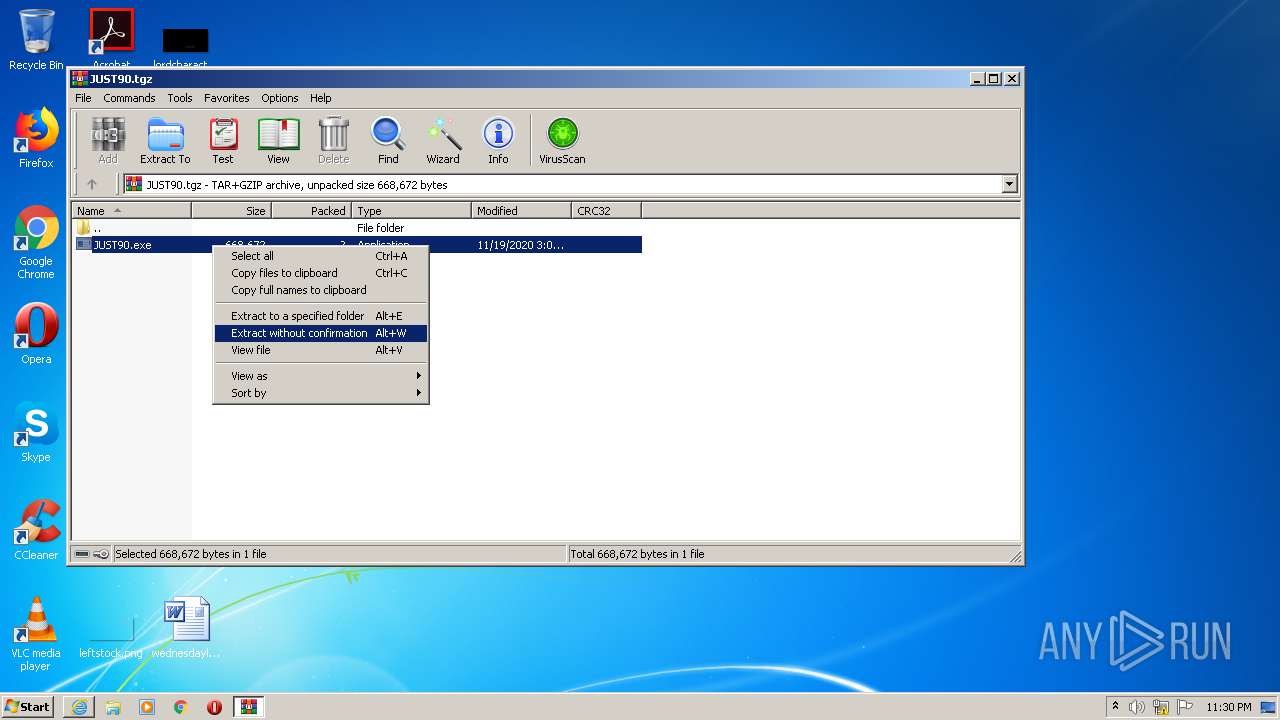
Application was dropped or rewritten from another process
- JUST90.exe (PID: 992)
- JUST90.exe (PID: 3204)
- JUST90.exe (PID: 4008)
- JUST90.exe (PID: 3668)
- JUST90.exe (PID: 532)
Actions looks like stealing of personal data
- JUST90.exe (PID: 4008)
- JUST90.exe (PID: 532)
SUSPICIOUS
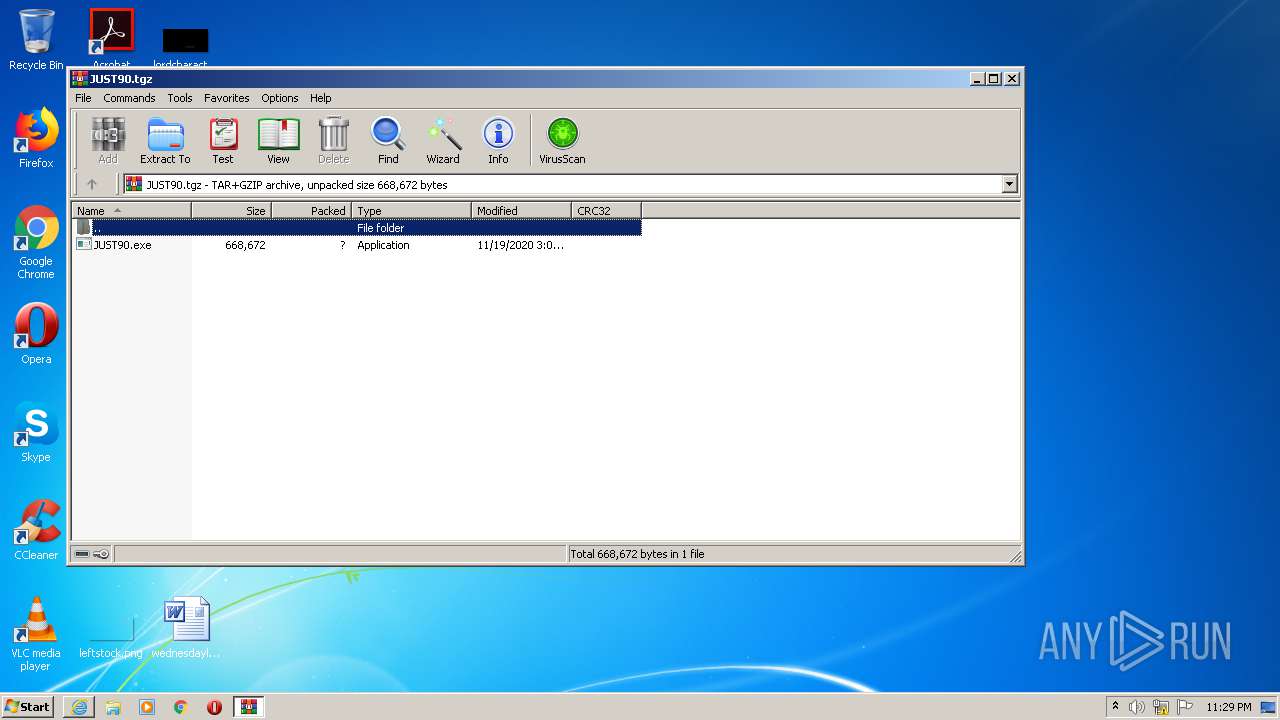
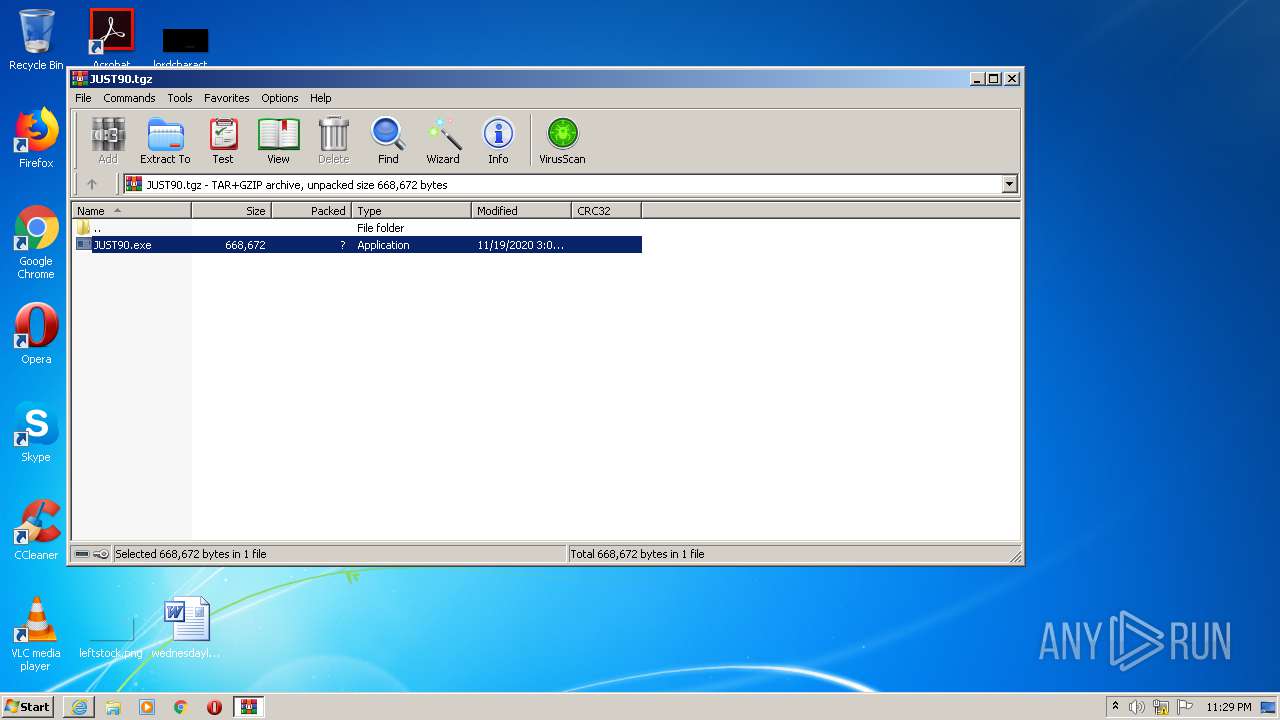
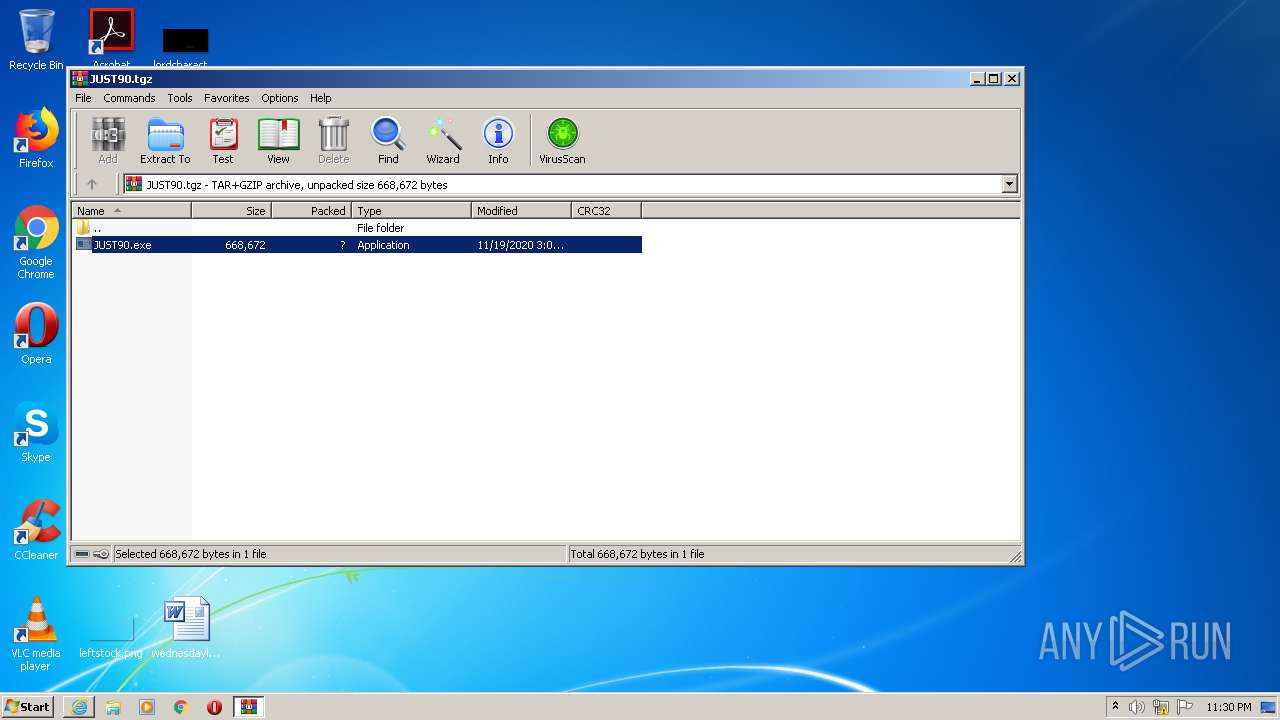
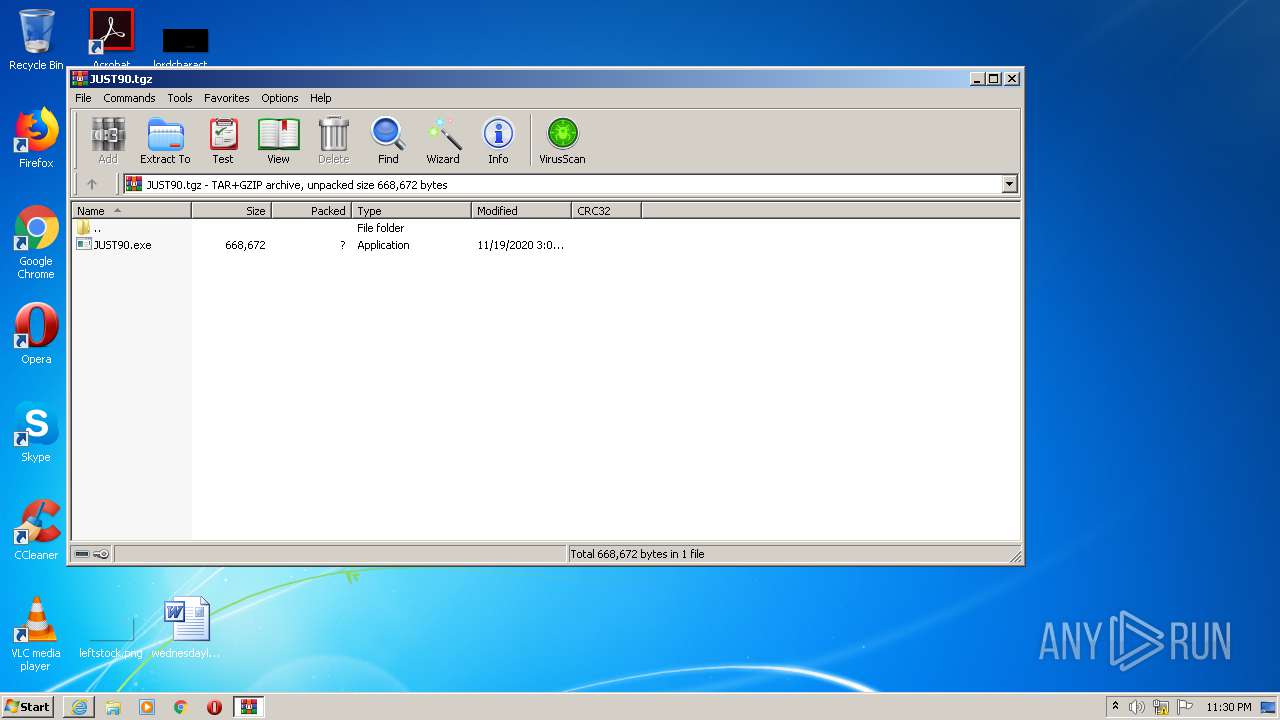
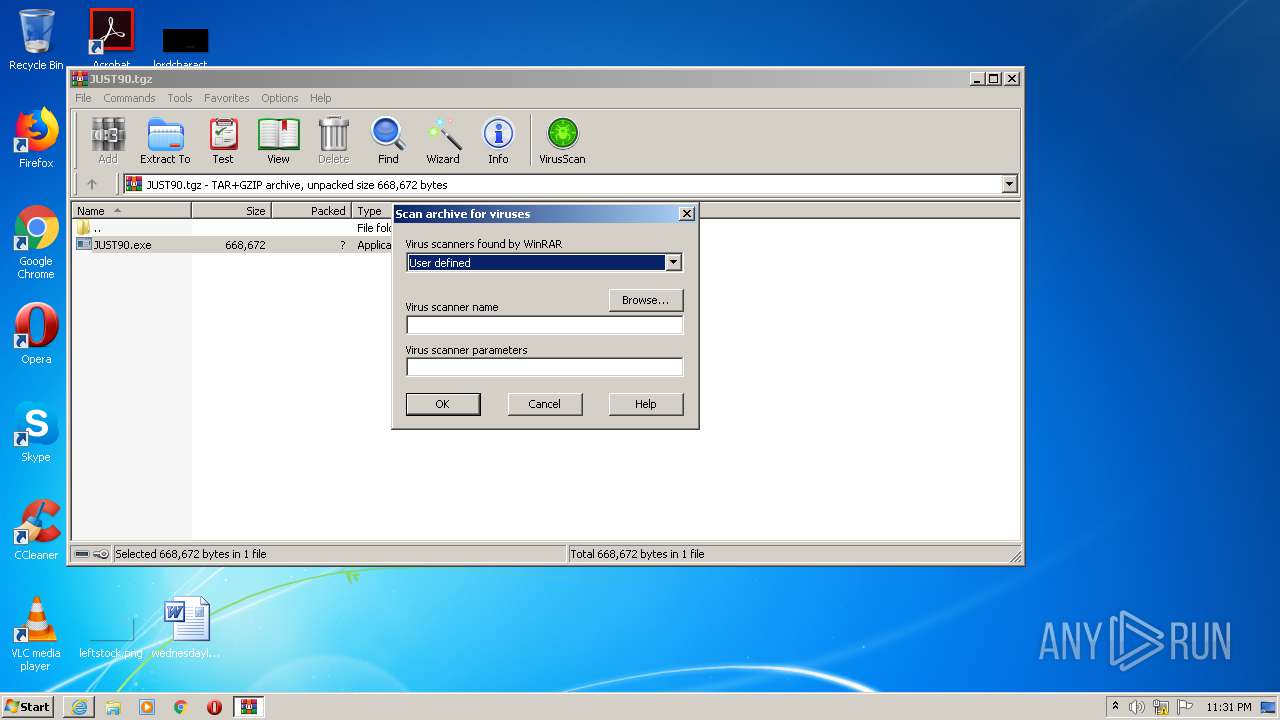
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2708)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2708)
Application launched itself
- JUST90.exe (PID: 3204)
- JUST90.exe (PID: 3668)
INFO
Application launched itself
- iexplore.exe (PID: 2944)
Changes internet zones settings
- iexplore.exe (PID: 2944)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2944)
Creates files in the user directory
- iexplore.exe (PID: 1716)
- iexplore.exe (PID: 2944)
Reads settings of System Certificates
- iexplore.exe (PID: 2944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
8
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2708.48226\JUST90.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2708.48226\JUST90.exe | JUST90.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 992 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2708.41680\JUST90.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2708.41680\JUST90.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1716 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2944 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
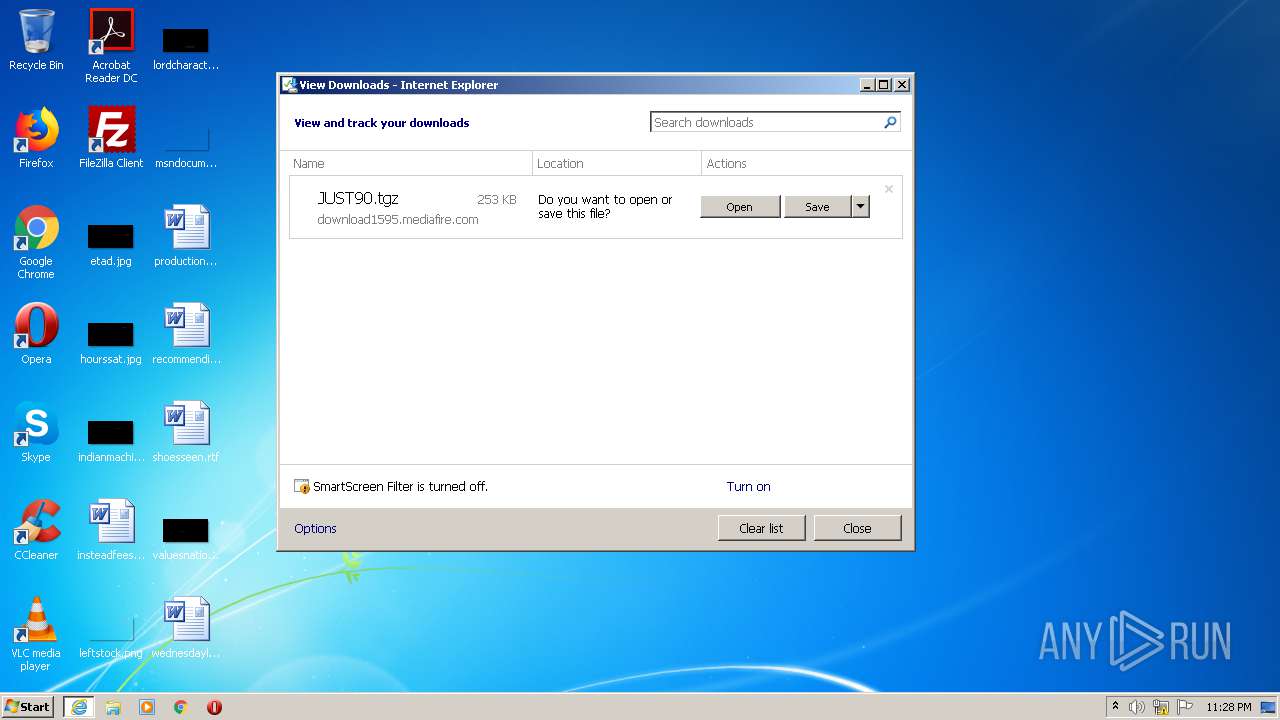
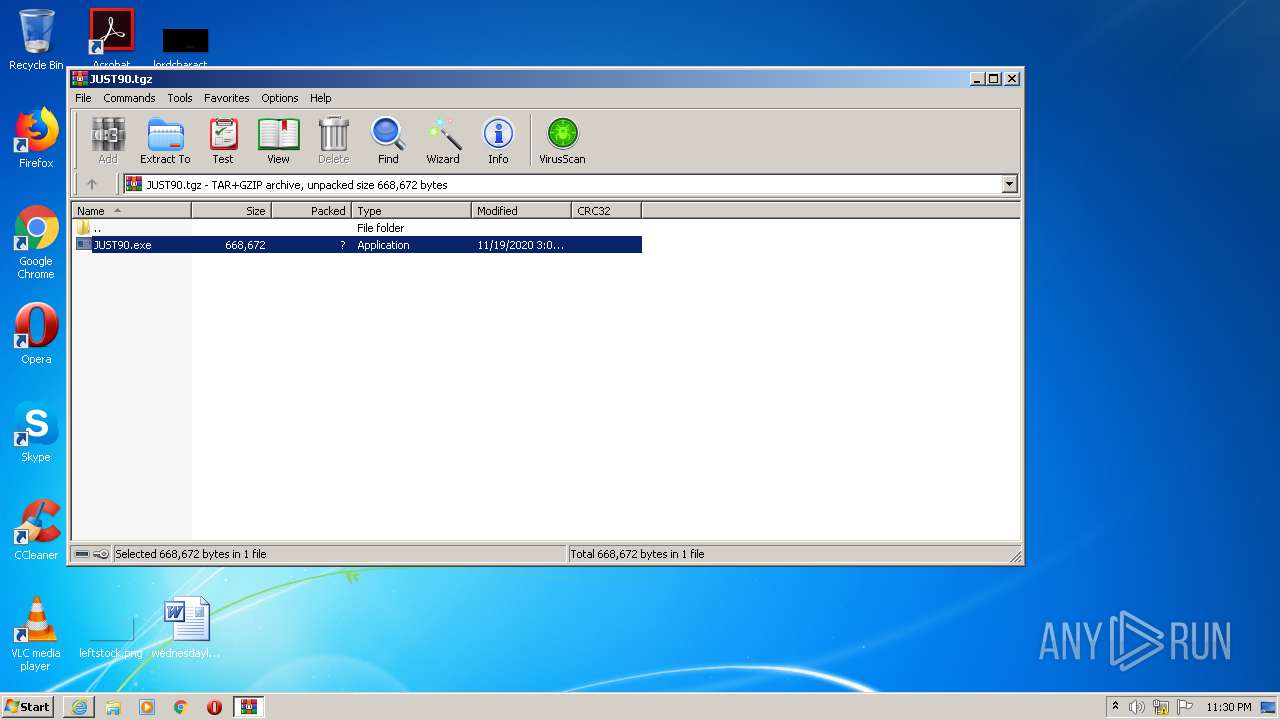
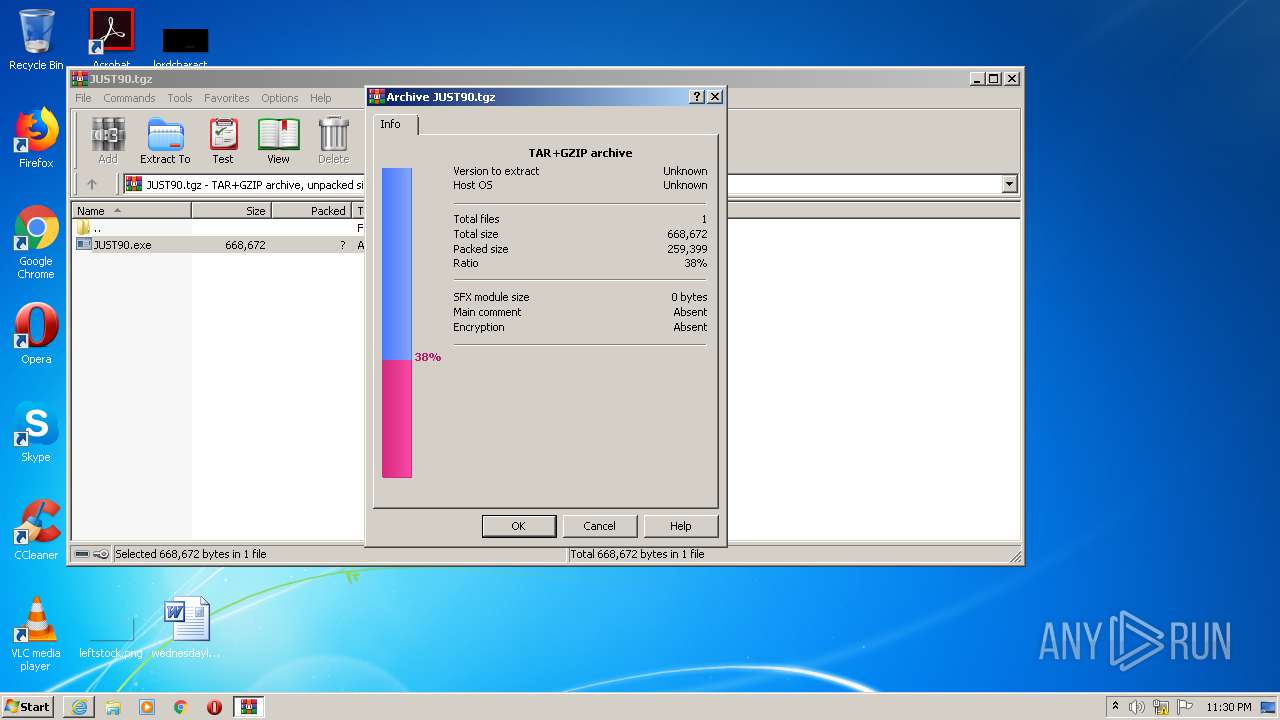
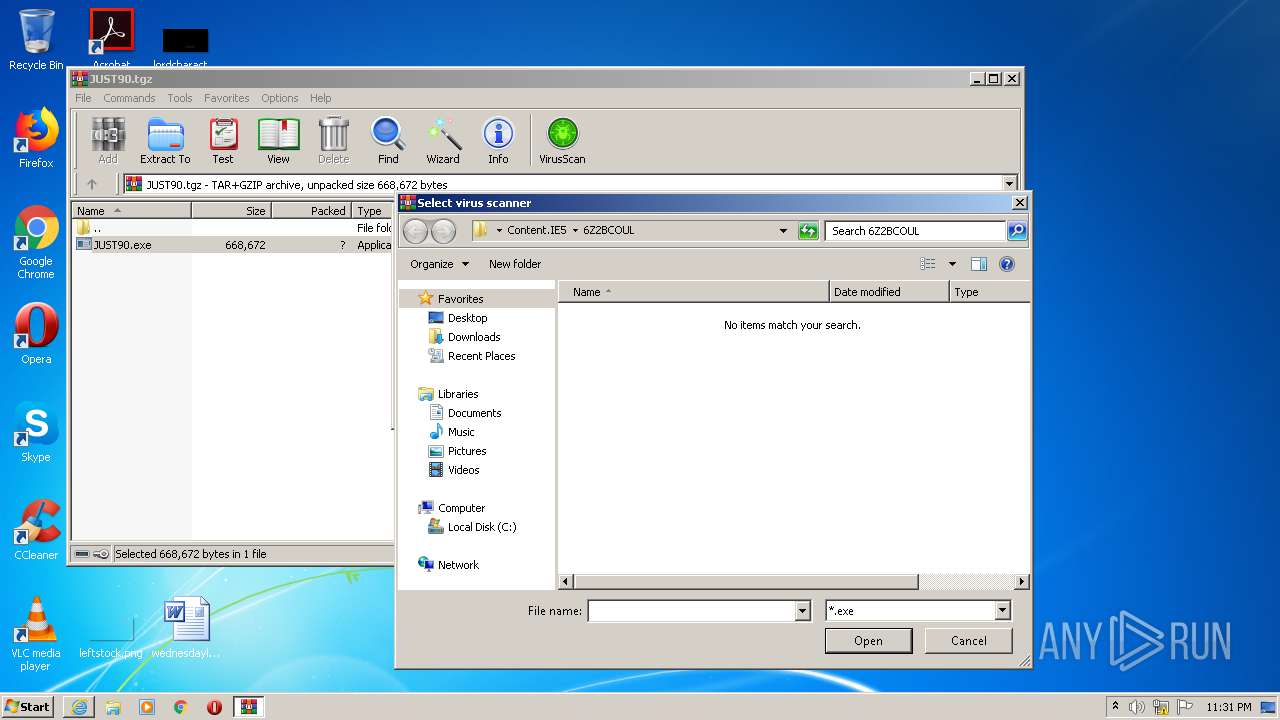
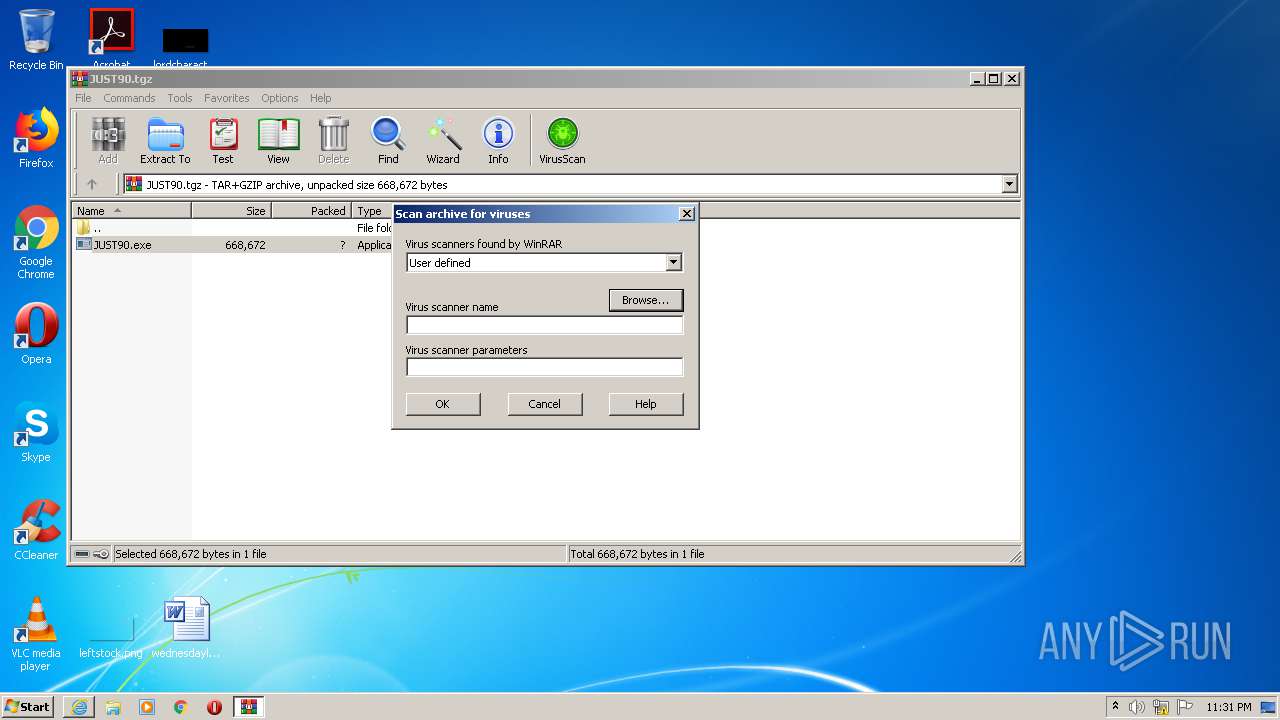
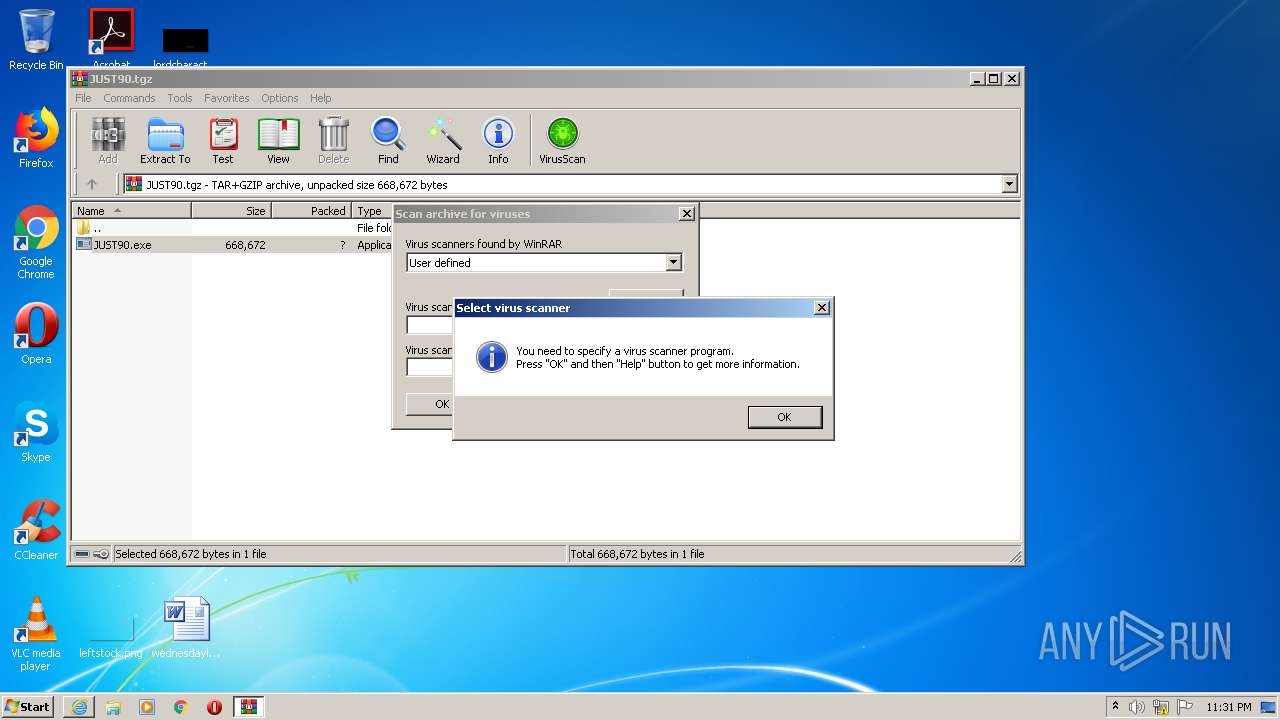
| 2708 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\JUST90.tgz" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2944 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://www.mediafire.com/file/4diaf0cqb0vappn/JUST90.tgz/file" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3204 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2708.38183\JUST90.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2708.38183\JUST90.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3668 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2708.48226\JUST90.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2708.48226\JUST90.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4008 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2708.38183\JUST90.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2708.38183\JUST90.exe | JUST90.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
2 267
Read events
2 118
Write events
147
Delete events
2
Modification events
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2023242350 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30852775 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
4
Suspicious files
20
Text files
4
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1716 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\CO8QQ0RI.txt | — | |
MD5:— | SHA256:— | |||
| 1716 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\JUST90.tgz.xvk7xcj.partial | — | |
MD5:— | SHA256:— | |||
| 2944 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF582377B6D4CE6529.TMP | — | |
MD5:— | SHA256:— | |||
| 2944 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\JUST90.tgz.xvk7xcj.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2944 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab5152.tmp | — | |
MD5:— | SHA256:— | |||
| 2944 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar5153.tmp | — | |
MD5:— | SHA256:— | |||
| 2944 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver521F.tmp | — | |
MD5:— | SHA256:— | |||
| 2944 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\BJPBTDSN.txt | — | |
MD5:— | SHA256:— | |||
| 2944 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\YAC3VVUX.txt | — | |
MD5:— | SHA256:— | |||
| 1716 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\JUST90[1].tgz | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
16
DNS requests
8
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1716 | iexplore.exe | GET | 200 | 199.91.152.95:80 | http://download1595.mediafire.com/9qcrys9olrwg/4diaf0cqb0vappn/JUST90.tgz | US | compressed | 253 Kb | unknown |
1716 | iexplore.exe | GET | 302 | 104.16.202.237:80 | http://www.mediafire.com/file/4diaf0cqb0vappn/JUST90.tgz/file | US | — | — | shared |
2944 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 471 b | whitelisted |
2944 | iexplore.exe | GET | 200 | 104.18.24.243:80 | http://ocsp.msocsp.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIGkp0%2Fv9GUvNUu1EP06Tu7%2BChyAQUkZ47RGw9V5xCdyo010%2FRzEqXLNoCExwAFF8jA2u85i8%2FLFYAAAAUXyM%3D | US | der | 1.75 Kb | whitelisted |
2944 | iexplore.exe | GET | 200 | 104.18.24.243:80 | http://ocsp.msocsp.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIGkp0%2Fv9GUvNUu1EP06Tu7%2BChyAQUkZ47RGw9V5xCdyo010%2FRzEqXLNoCExwAFF8jA2u85i8%2FLFYAAAAUXyM%3D | US | der | 1.75 Kb | whitelisted |
2944 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 471 b | whitelisted |
2944 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2944 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2944 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2944 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1716 | iexplore.exe | 104.16.202.237:80 | www.mediafire.com | Cloudflare Inc | US | unknown |
1716 | iexplore.exe | 199.91.152.95:80 | download1595.mediafire.com | MediaFire, LLC | US | unknown |
2944 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2944 | iexplore.exe | 204.79.197.200:443 | ieonline.microsoft.com | Microsoft Corporation | US | whitelisted |
2944 | iexplore.exe | 104.18.24.243:80 | ocsp.msocsp.com | Cloudflare Inc | US | shared |
4008 | JUST90.exe | 212.227.15.142:587 | smtp.1and1.es | 1&1 Internet SE | DE | suspicious |
532 | JUST90.exe | 212.227.15.142:587 | smtp.1and1.es | 1&1 Internet SE | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| shared |
download1595.mediafire.com |
| unknown |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.msocsp.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
smtp.1and1.es |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1716 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
4008 | JUST90.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
532 | JUST90.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |