| File name: | target.exe |
| Full analysis: | https://app.any.run/tasks/9149a54e-294a-41bc-8e88-105aa0292929 |
| Verdict: | Malicious activity |
| Analysis date: | November 02, 2024, 19:40:02 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 82CE255B411504700BA0D4442B7E26F9 |
| SHA1: | 4A75DD23F947FF0A35085464B8228773E0D0F166 |
| SHA256: | 50B36E9625866C48C68C18DA49663A8A6A5AA6C3D4113F737D98EFDD006E2D3B |
| SSDEEP: | 768:VqeJWZdFE2ECEL8wRfw13zlP+sAFDaLOpJlxnwXbOfq1gkD95e8:Eg2ECELXfwzlWskDaE3ebOiD9z |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- target.exe (PID: 5508)
Starts a new process with hidden mode (POWERSHELL)
- target.exe (PID: 5508)
Uses base64 encoding (POWERSHELL)
- target.exe (PID: 5508)
Checks Windows Trust Settings
- target.exe (PID: 5508)
Executable content was dropped or overwritten
- target.exe (PID: 5508)
- svchost.exe (PID: 7328)
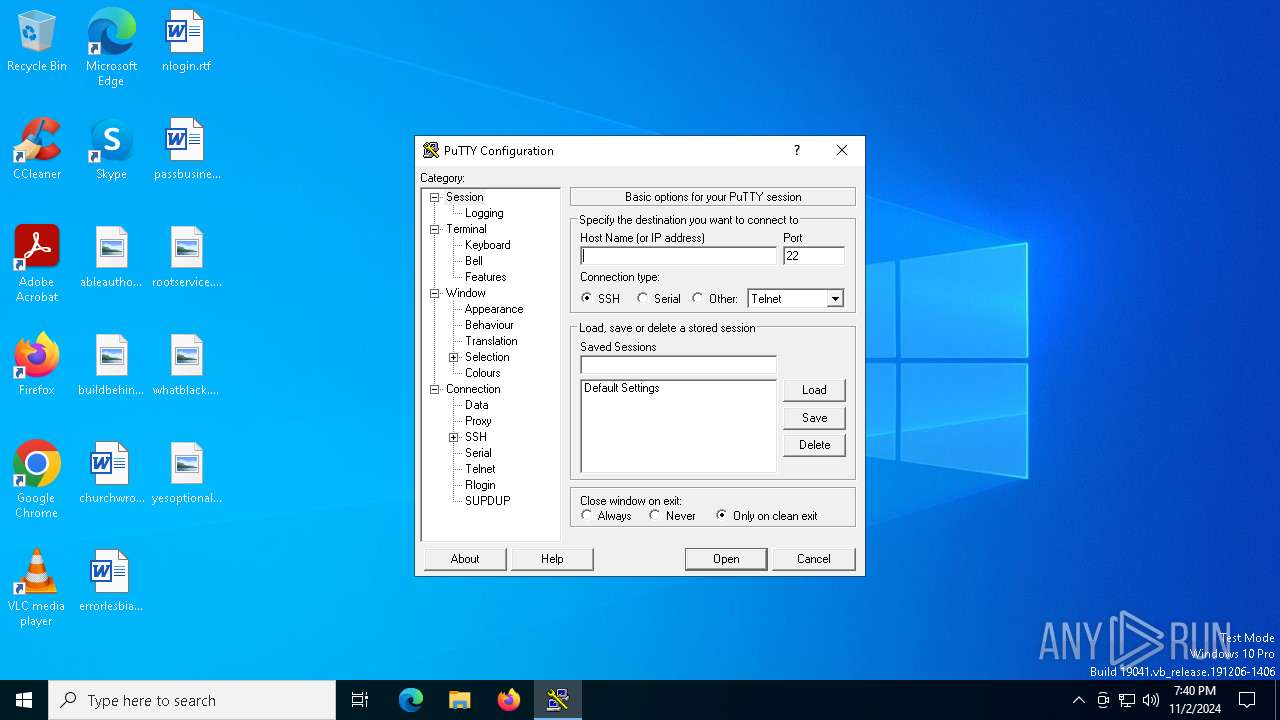
PUTTY has been detected
- svchost.exe (PID: 7384)
- svchost.exe (PID: 7384)
Potential Corporate Privacy Violation
- target.exe (PID: 5508)
Starts a Microsoft application from unusual location
- FileCoAuth.exe (PID: 7772)
INFO
Create files in a temporary directory
- target.exe (PID: 5508)
Reads the computer name
- target.exe (PID: 5508)
Reads the machine GUID from the registry
- target.exe (PID: 5508)
Reads Environment values
- target.exe (PID: 5508)
Reads the software policy settings
- target.exe (PID: 5508)
Checks whether the specified file exists (POWERSHELL)
- target.exe (PID: 5508)
Checks supported languages
- target.exe (PID: 5508)
The process uses the downloaded file
- target.exe (PID: 5508)
Found Base64 encoded reflection usage via PowerShell (YARA)
- target.exe (PID: 5508)
Found Base64 encoded access to Windows Defender via PowerShell (YARA)
- target.exe (PID: 5508)
Checks if a key exists in the options dictionary (POWERSHELL)
- target.exe (PID: 5508)
Found Base64 encoded text manipulation via PowerShell (YARA)
- target.exe (PID: 5508)
Found Base64 encoded network access via PowerShell (YARA)
- target.exe (PID: 5508)
Found Base64 encoded file access via PowerShell (YARA)
- target.exe (PID: 5508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (55.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21) |
| .scr | | | Windows screen saver (9.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:11:02 19:38:48+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 33792 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa1fe |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | target.exe |
| LegalCopyright: | |
| OriginalFileName: | target.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
134
Monitored processes
4
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5508 | "C:\Users\admin\AppData\Local\Temp\target.exe" | C:\Users\admin\AppData\Local\Temp\target.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 7328 | "C:\driver\svchost.exe" | C:\driver\svchost.exe | target.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 7384 | "C:\Users\admin\AppData\Local\Temp\3582-490\svchost.exe" | C:\Users\admin\AppData\Local\Temp\3582-490\svchost.exe | svchost.exe | ||||||||||||
User: admin Company: Simon Tatham Integrity Level: MEDIUM Description: SSH, Telnet, Rlogin, and SUPDUP client Version: Release 0.81 (with embedded help) Modules
| |||||||||||||||
| 7772 | "C:\Users\admin\AppData\Local\Temp\3582-490\FileCoAuth.exe" -Embedding | C:\Users\admin\AppData\Local\Temp\3582-490\FileCoAuth.exe | — | FileCoAuth.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneDriveFile Co-Authoring Executable Exit code: 0 Version: 19.043.0304.0013 Modules
| |||||||||||||||
Total events
6 755
Read events
6 741
Write events
14
Delete events
0
Modification events
| (PID) Process: | (5508) target.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\target_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5508) target.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\target_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5508) target.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\target_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (5508) target.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\target_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (5508) target.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\target_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (5508) target.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\target_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (5508) target.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\target_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (5508) target.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\target_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5508) target.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\target_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5508) target.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\target_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
10
Suspicious files
3
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7328 | svchost.exe | C:\Users\admin\AppData\Local\Temp\3582-490\svchost.exe | executable | |
MD5:5EFEF6CC9CD24BAEEED71C1107FC32DF | SHA256:E61B8F44AB92CF0F9CB1101347967D31E1839979142A4114A7DD02AA237BA021 | |||
| 5508 | target.exe | C:\driver\downloaded.zip | compressed | |
MD5:776CB12185AF594BDF3A722863B74384 | SHA256:8A53E716B4E1A70CDB289201730A721F575C01962DF354DF21E20EE85F0A091C | |||
| 5508 | target.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_f13l0hl1.sl4.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5508 | target.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_j5r534jp.esb.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7328 | svchost.exe | C:\ProgramData\Adobe\ARM\S\388\AdobeARMHelper.exe | executable | |
MD5:85A67D34298E33D2D5A9EC789B6AB594 | SHA256:1DEE143B4F88F2375B85C6271A58E2E78FED081BEAE4090678CB2DD7A37FB2D4 | |||
| 7328 | svchost.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\OneDriveStandaloneUpdater.exe | executable | |
MD5:A747FA4161FE3C00C3FBB4BF391D4D4E | SHA256:B7BA59428AF7AE08C5BF927B57E326D5259E6ED31BD4237AA6A44378177364C1 | |||
| 7328 | svchost.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe | executable | |
MD5:13C2D5BF03C4A2B28E930F990CCC32DB | SHA256:12D24D0BC0E7CDC902E3540A3C6F7B755094F011A8EAD49A47A00563710B8F80 | |||
| 7328 | svchost.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\OneDrive.exe | executable | |
MD5:178B773B3FB050FCE26E40A9E8C2EE9A | SHA256:1E03573733F25B44004049A535E7E79366FD86FE953F6DFEDAAD05513B46A6C5 | |||
| 7328 | svchost.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileSyncHelper.exe | executable | |
MD5:1C0BE16E6ED8F5B6F0910650A25F4FA7 | SHA256:3028F6A6A7A10DC5D63F256FEEB8275F3818BF3371EAF8B20A2D0BF2FCD5F4A9 | |||
| 7328 | svchost.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileSyncConfig.exe | executable | |
MD5:0C5EC1AE9A301408AF26032B445FBB08 | SHA256:3A8010F1E4E028782093877D969EB127B80AE48B7215A8D3F91E8AB9C165AC7A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
35
DNS requests
19
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2776 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7540 | SIHClient.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7540 | SIHClient.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3952 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.32.185.131:80 | www.microsoft.com | AKAMAI-AS | BR | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4360 | SearchApp.exe | 2.16.110.171:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
th.bing.com |
| whitelisted |
paste.ee |
| shared |
go.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
5508 | target.exe | Potential Corporate Privacy Violation | ET POLICY Pastebin-style Service (paste .ee) in TLS SNI |