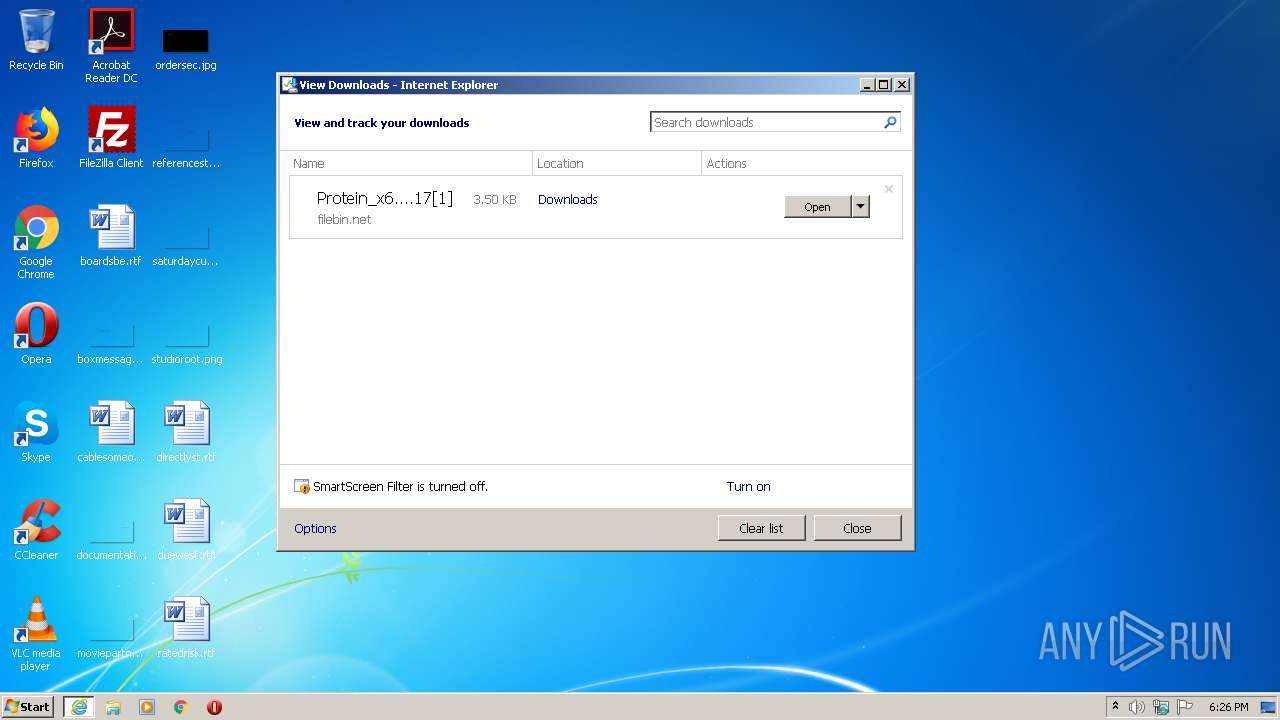
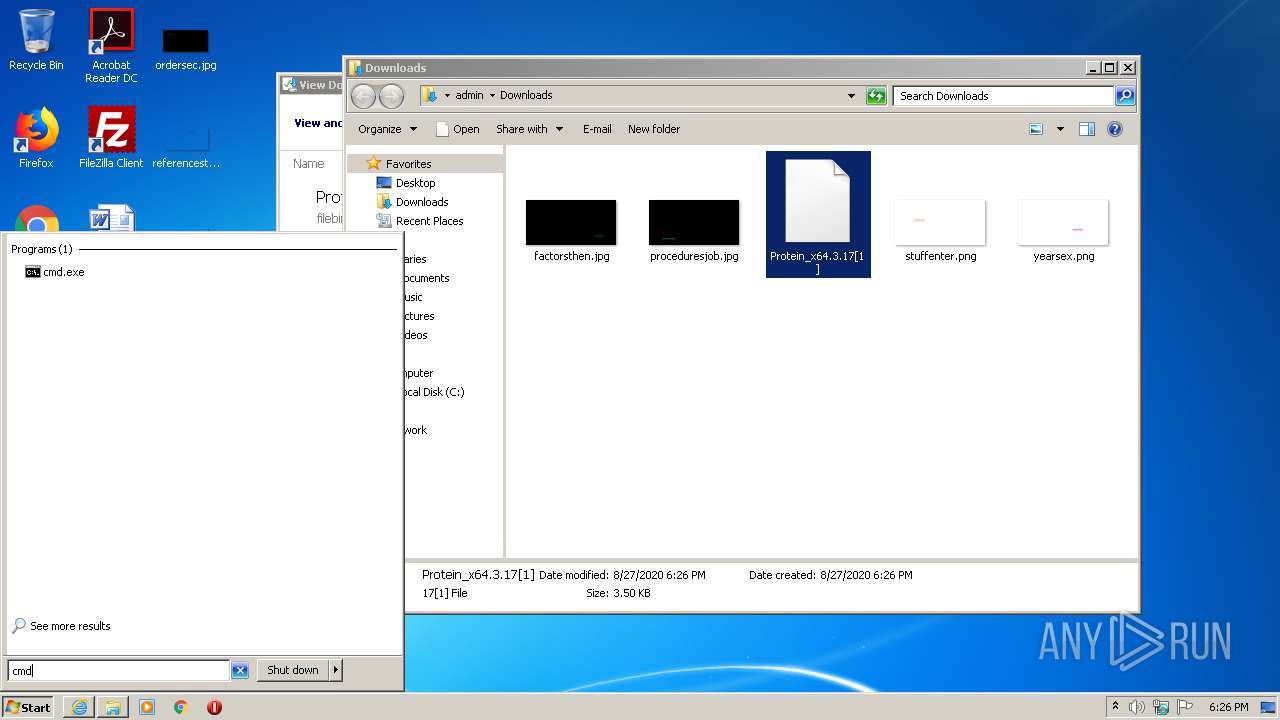
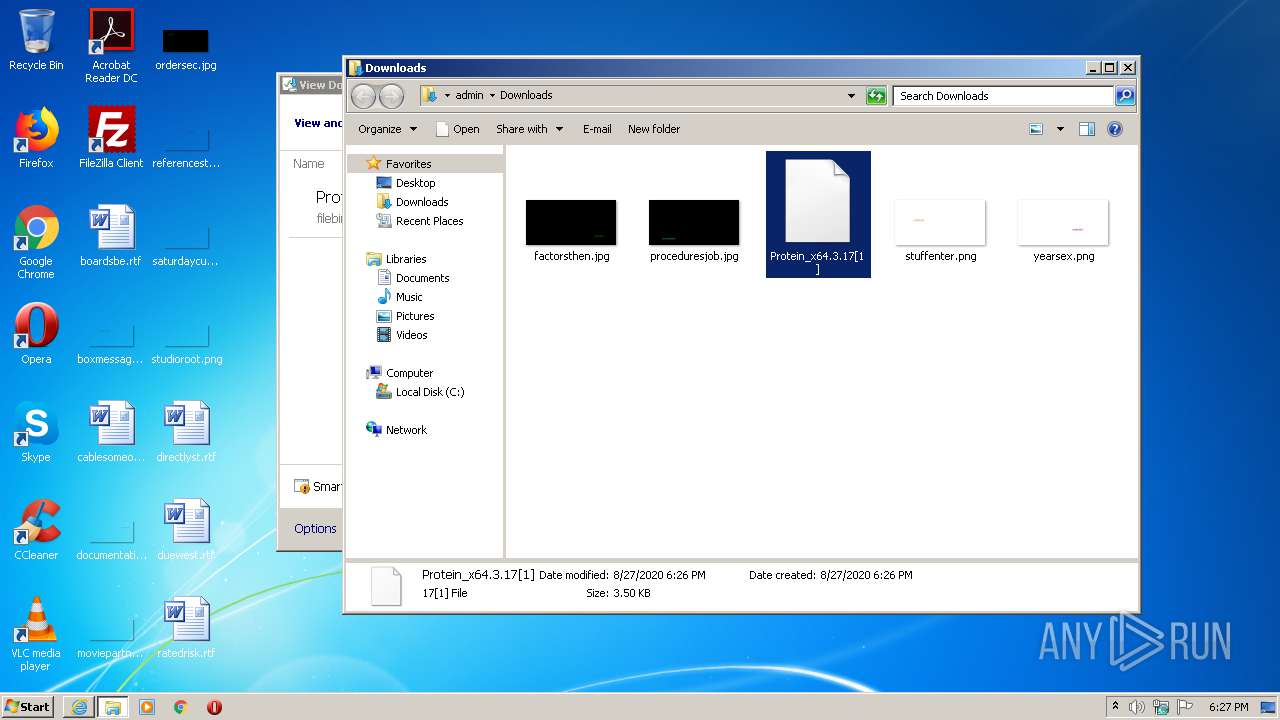
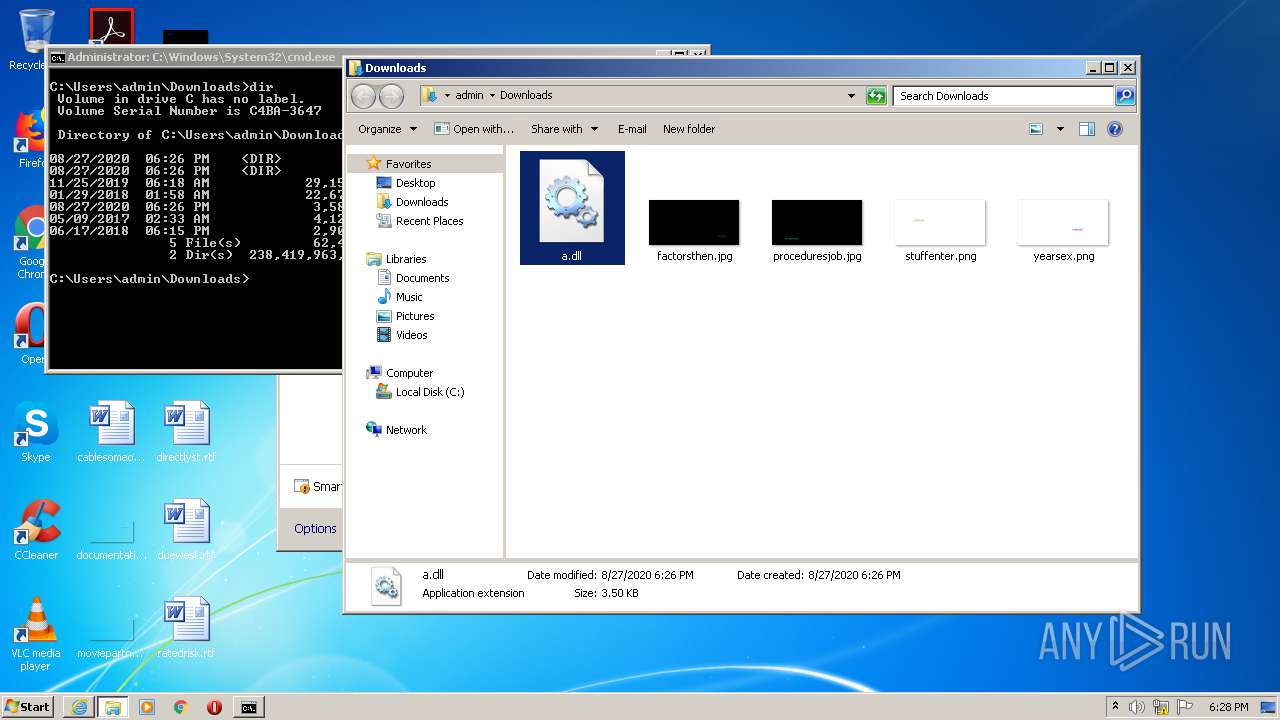
| URL: | https://filebin.net/icb3wnev8fxh0h6d/Protein_x64.3.17.dll?t=y0zkdlhf |
| Full analysis: | https://app.any.run/tasks/b6e824ea-017a-439a-96d6-b7227793d4fd |
| Verdict: | Suspicious activity |
| Analysis date: | August 27, 2020, 17:26:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | EF93D6DFF0D8CFA3B08C23276AEB7E2E |
| SHA1: | A855A706EE4F1B27C2F1723BA49AD52EFC9DA231 |
| SHA256: | 50B1ED72C71C35B0CE8CA98BE7E7A38E299CC531213DF3962C7D1794A803B92A |
| SSDEEP: | 3:N8wLBLoNK1X97ML1HaYJ5:2xY1t4LVaY3 |
MALICIOUS
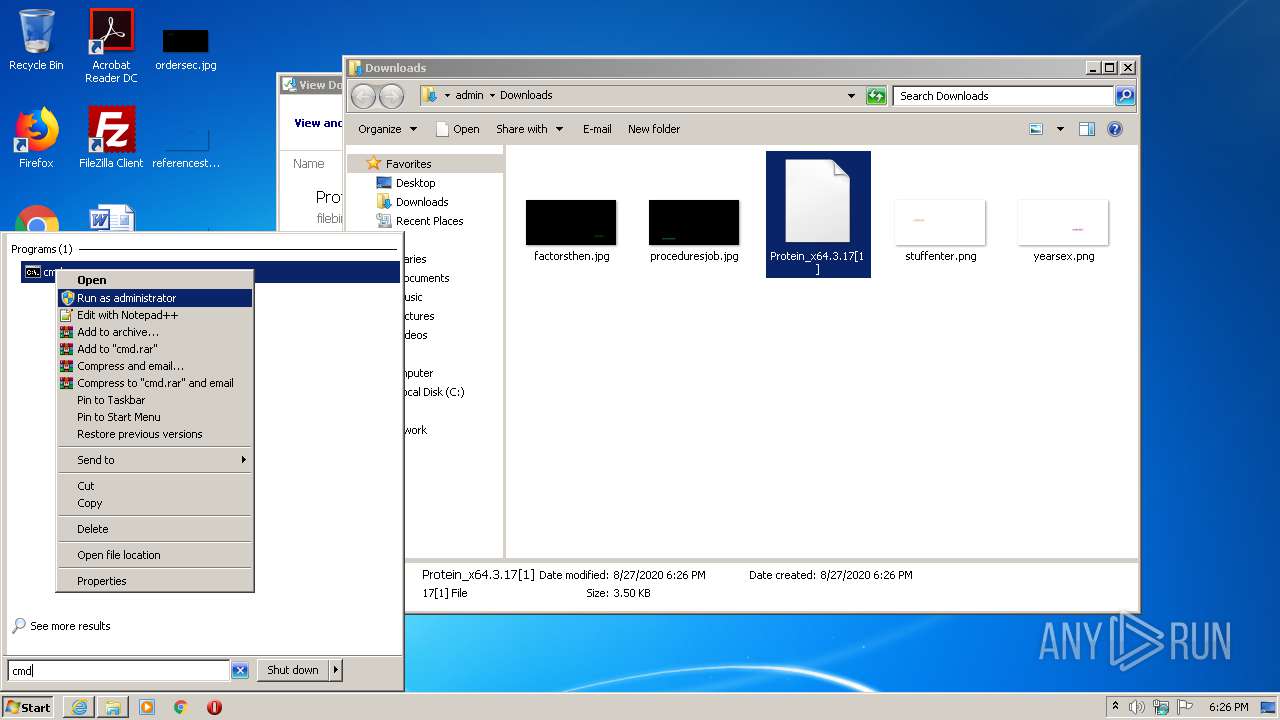
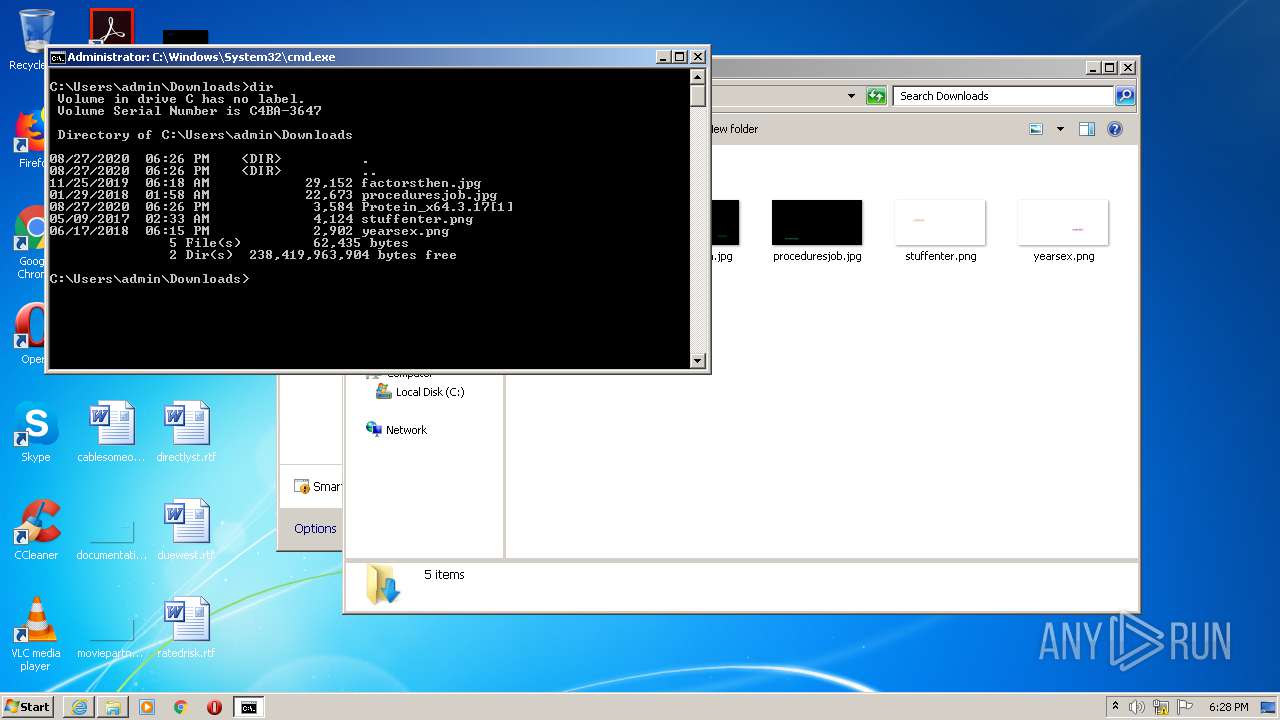
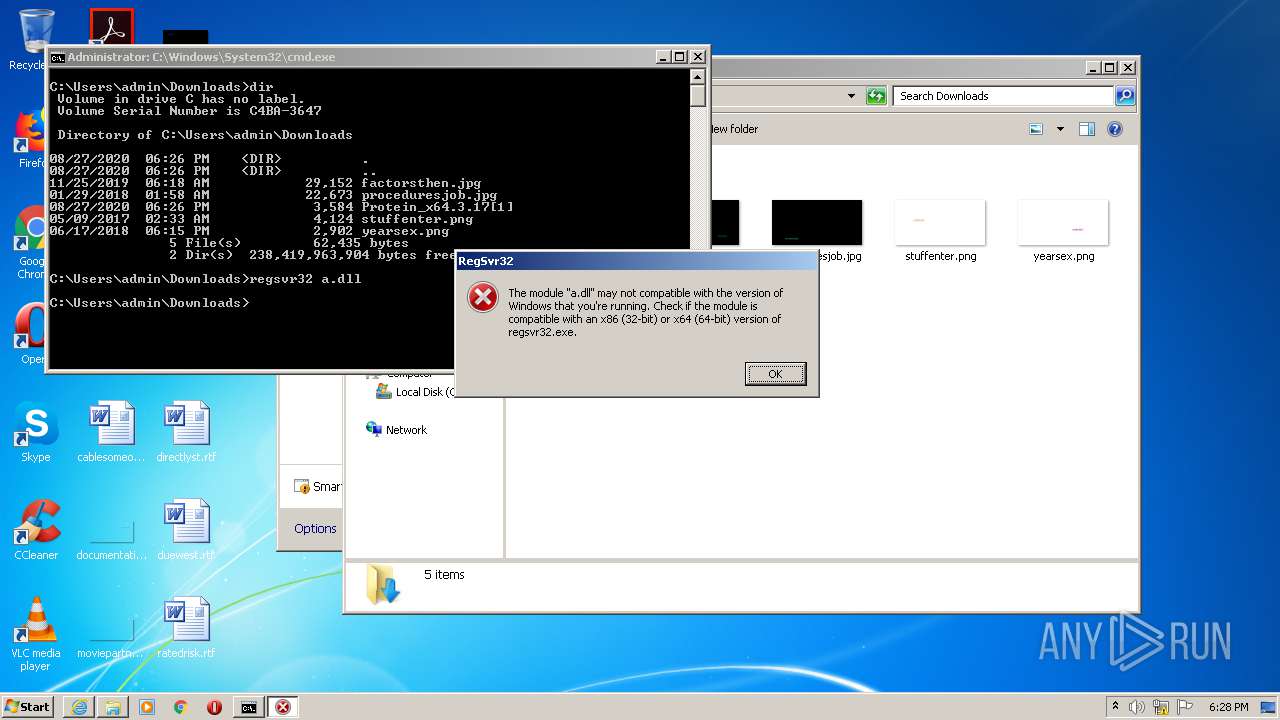
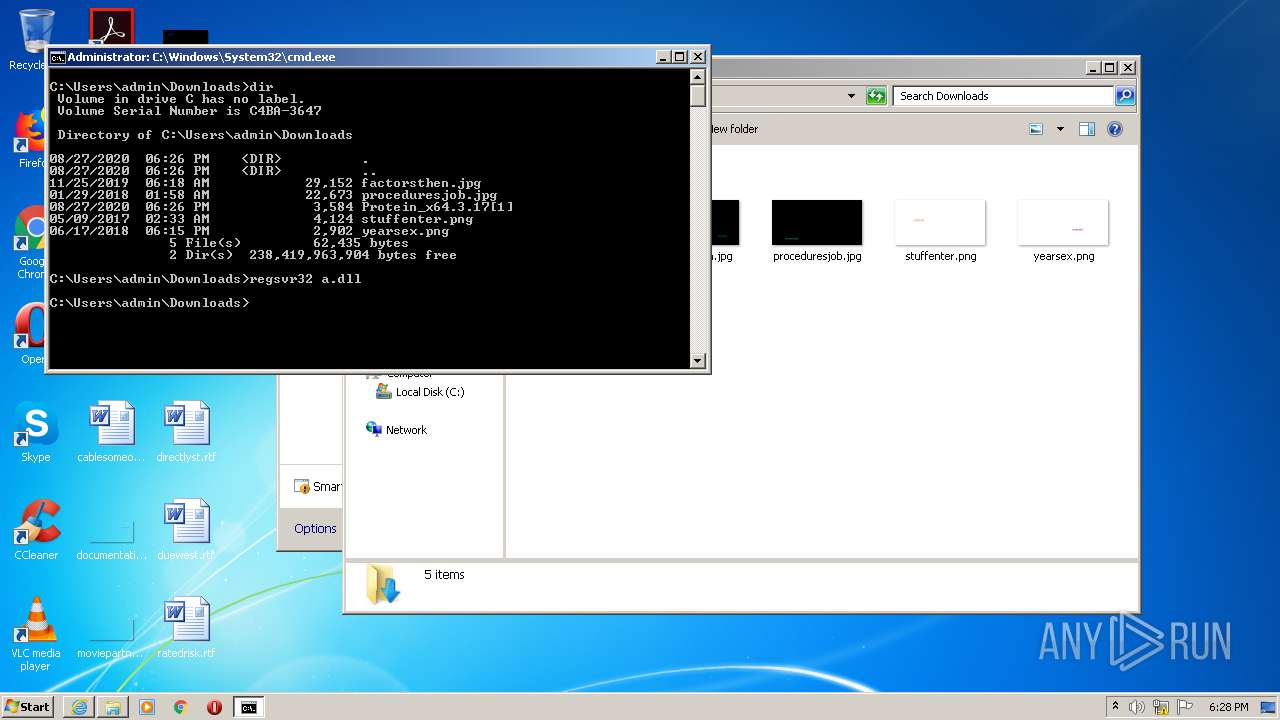
Registers / Runs the DLL via REGSVR32.EXE
- cmd.exe (PID: 2620)
SUSPICIOUS
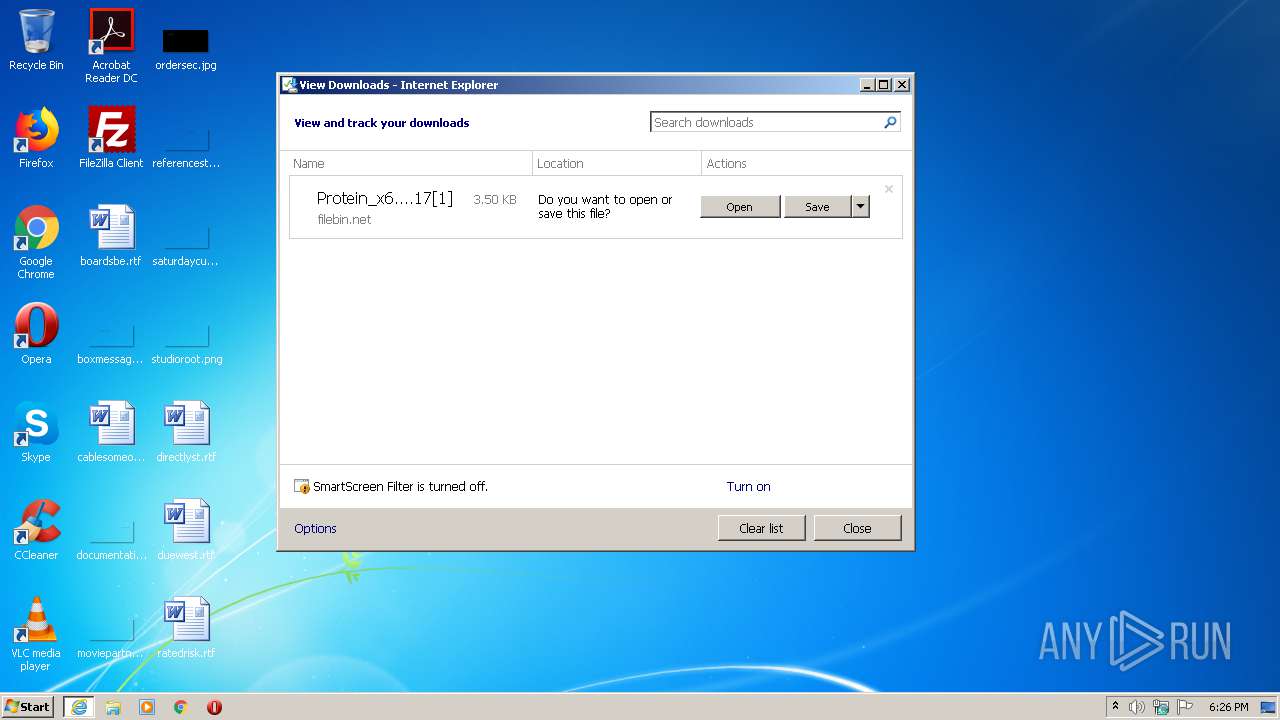
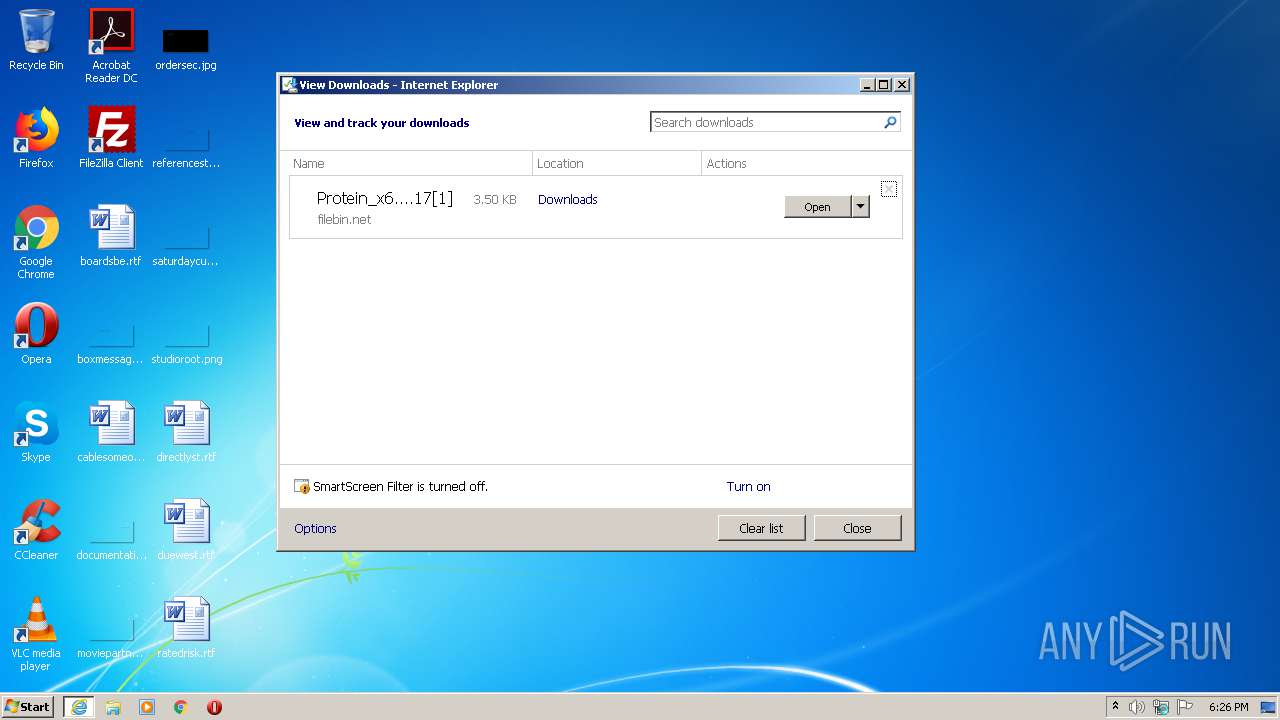
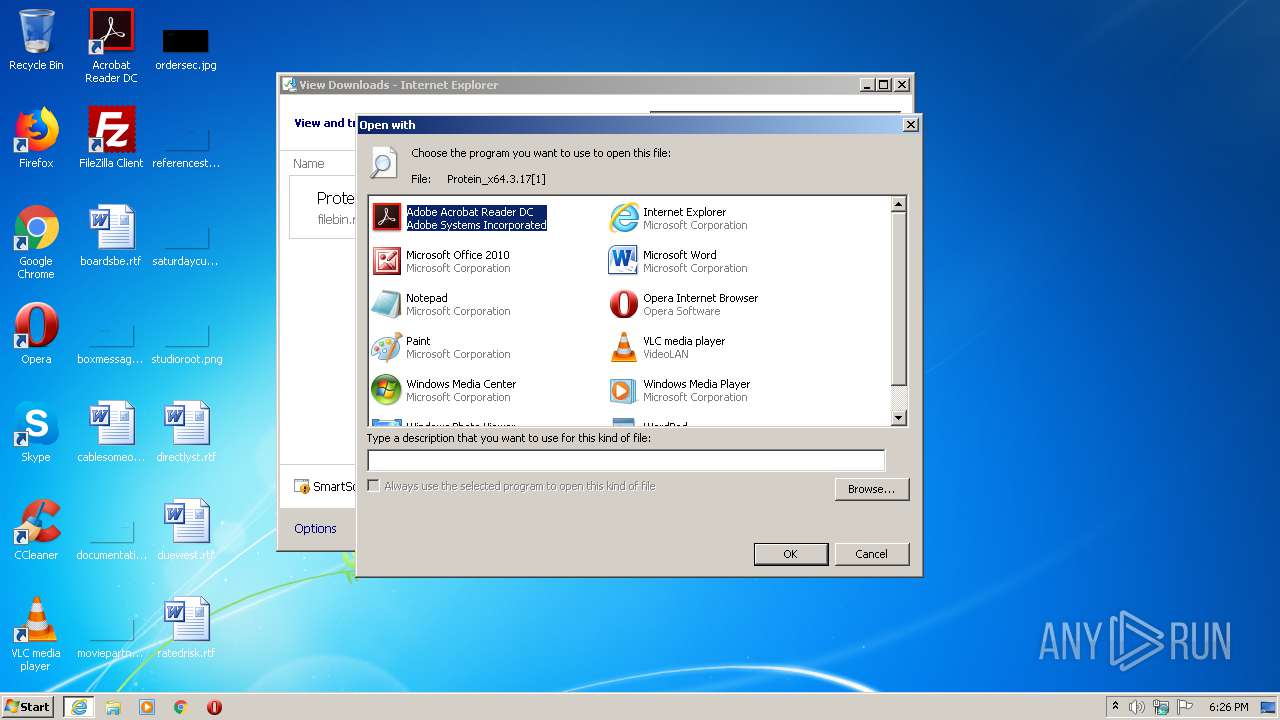
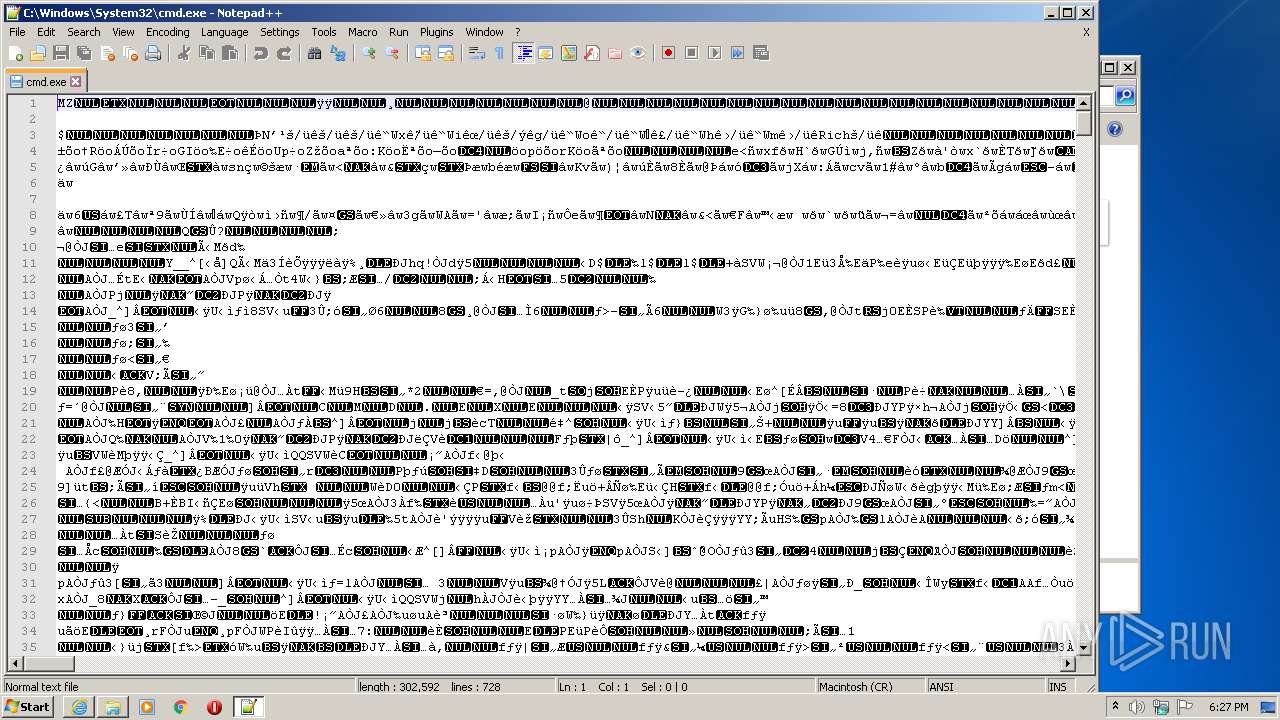
Executable content was dropped or overwritten
- iexplore.exe (PID: 3804)
- iexplore.exe (PID: 3900)
Creates files in the user directory
- notepad++.exe (PID: 3764)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3900)
Reads Internet Cache Settings
- iexplore.exe (PID: 3804)
- iexplore.exe (PID: 3900)
Application launched itself
- iexplore.exe (PID: 3900)
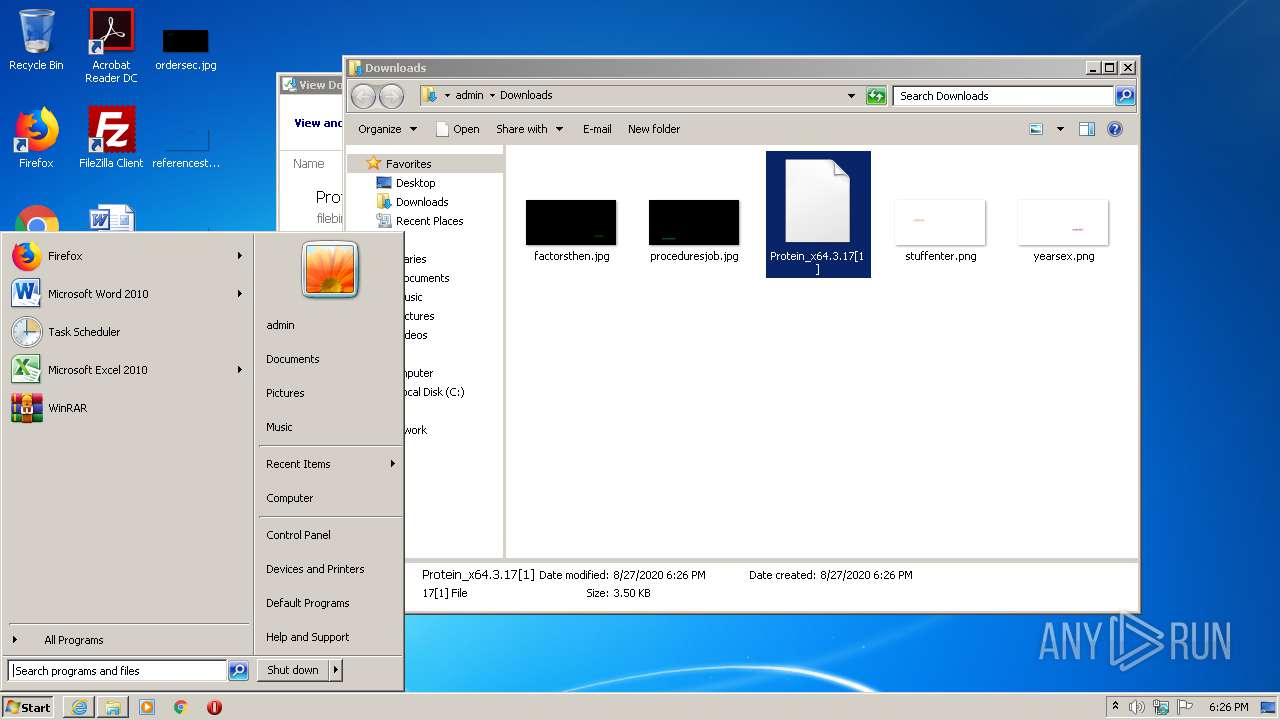
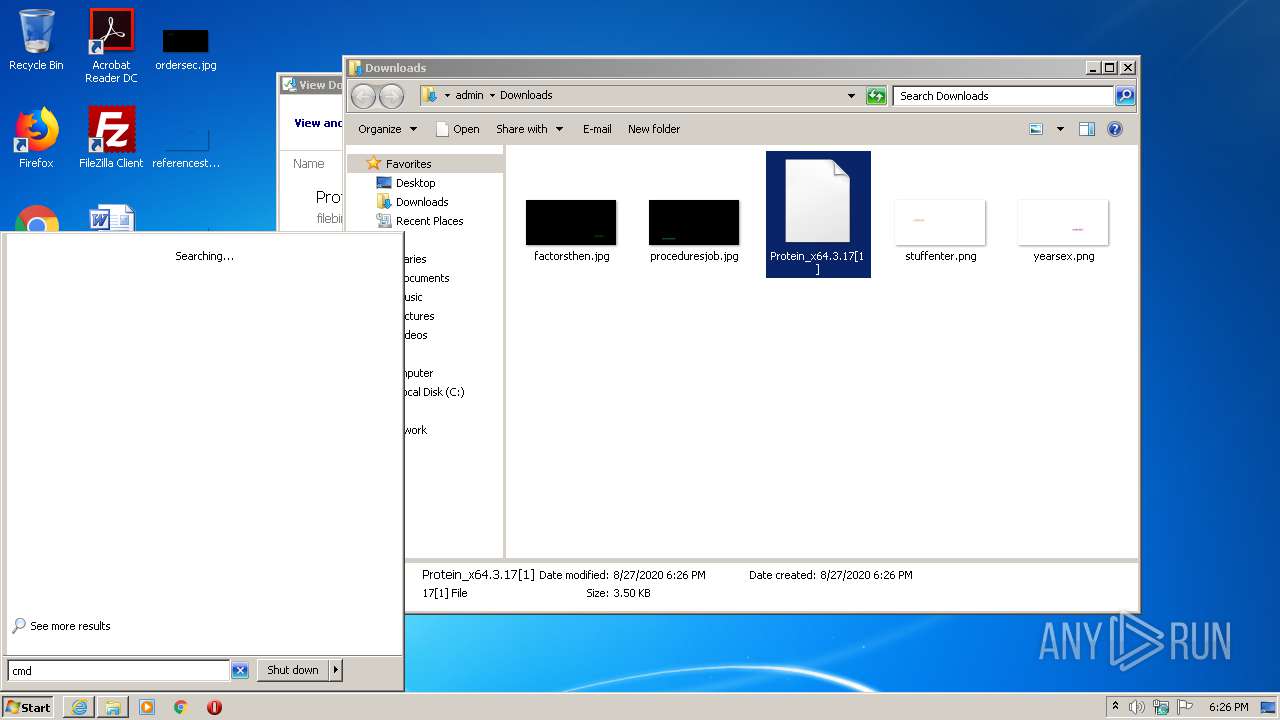
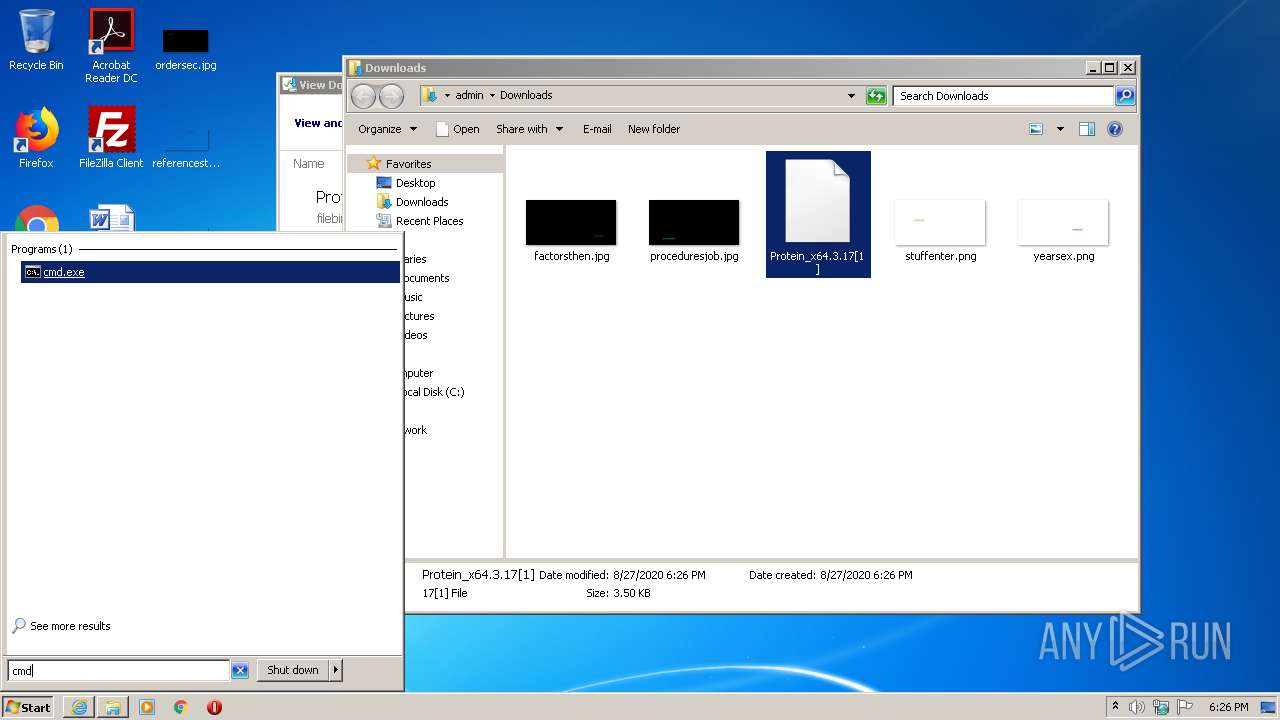
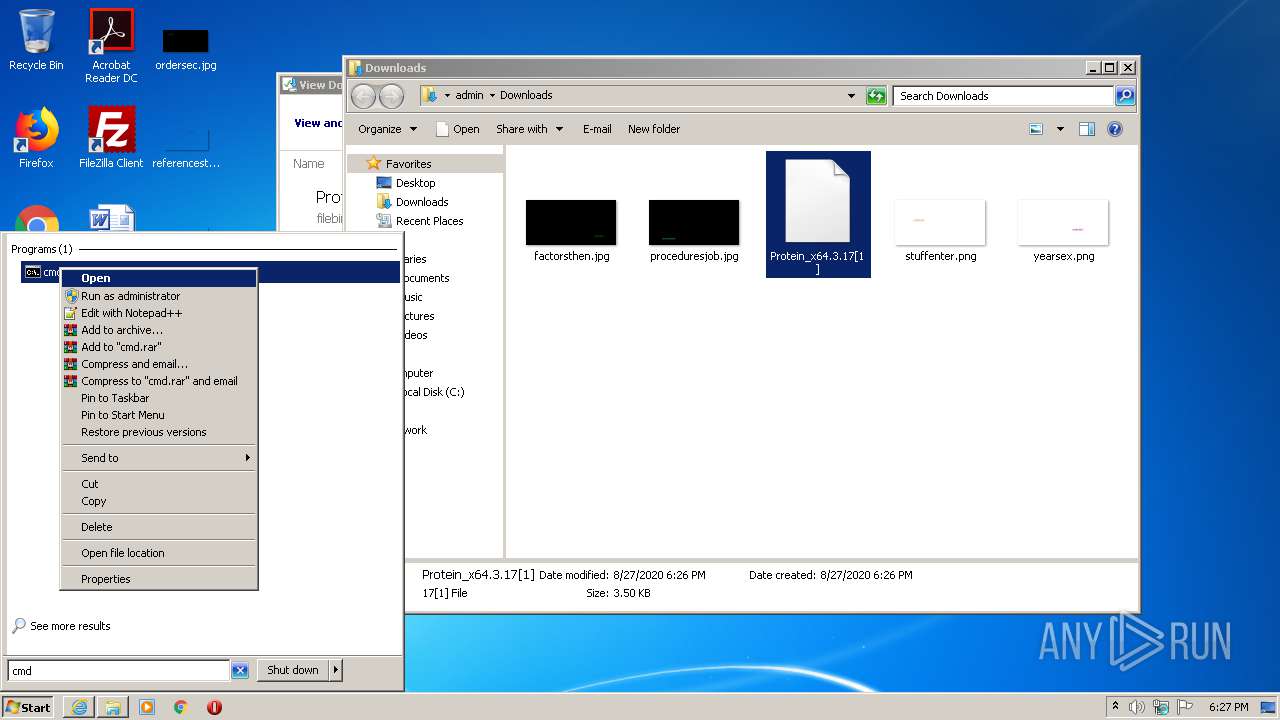
Manual execution by user
- notepad++.exe (PID: 3764)
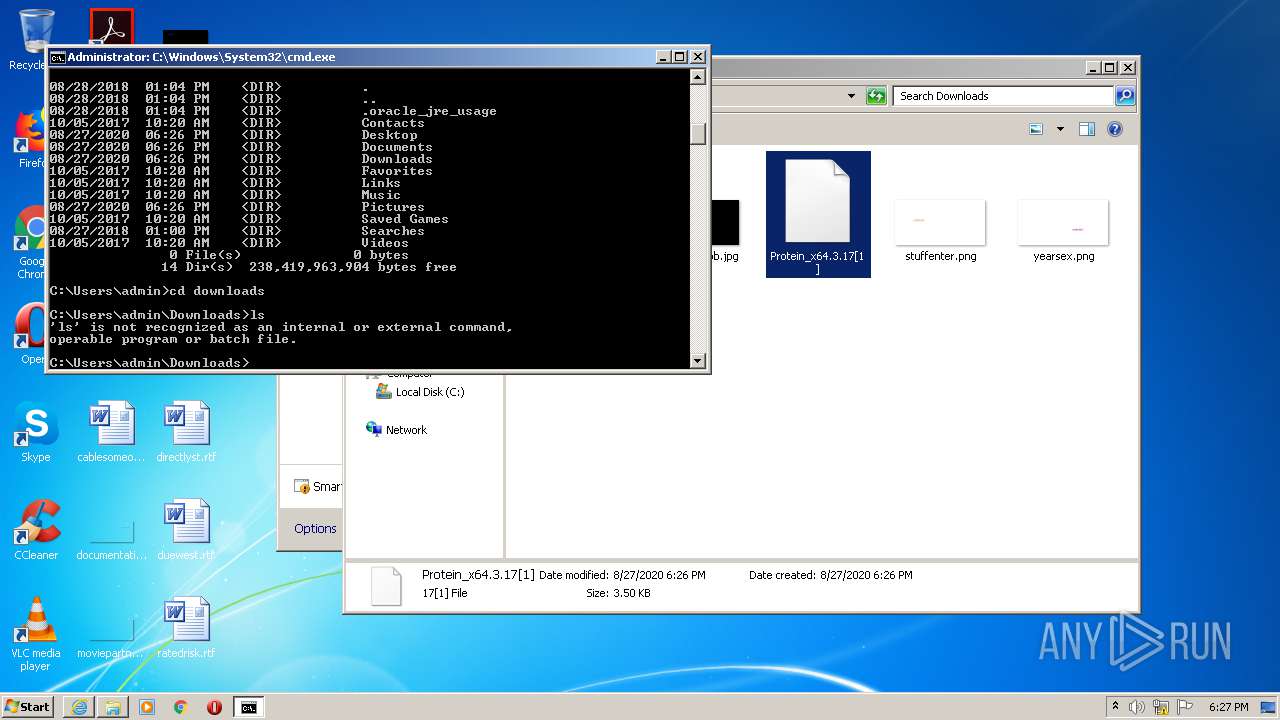
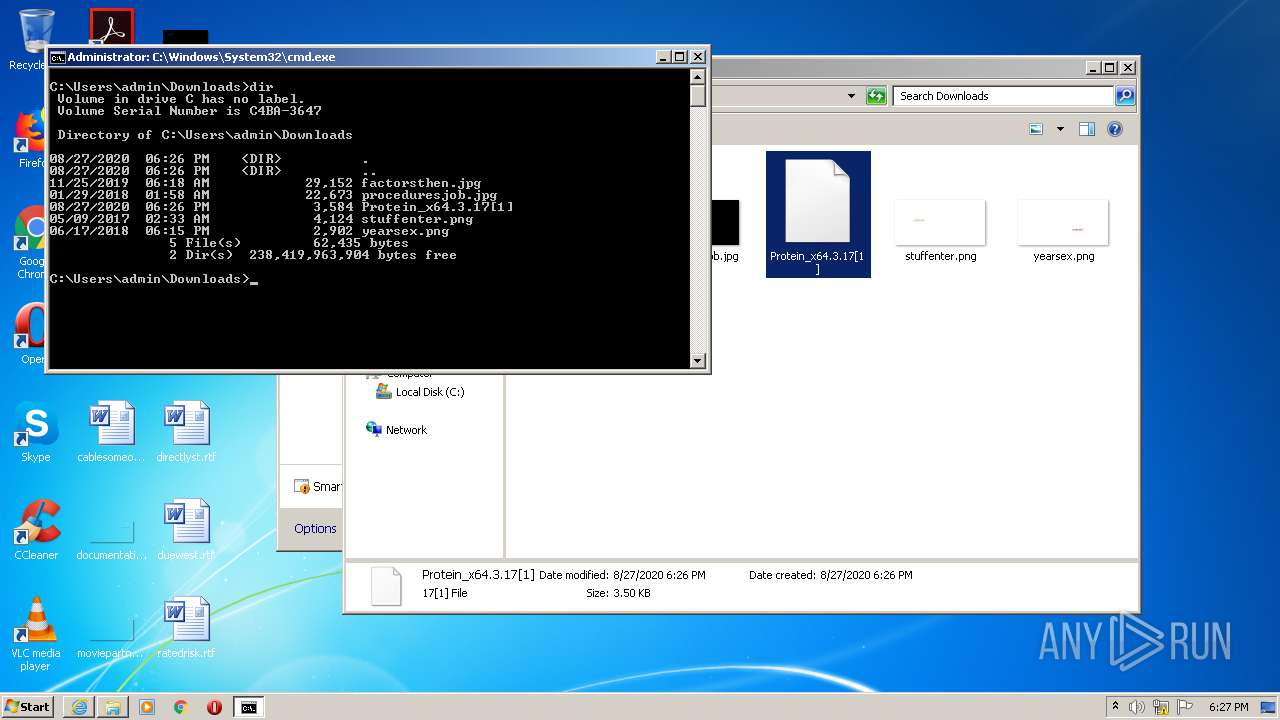
- cmd.exe (PID: 2620)
Reads settings of System Certificates
- iexplore.exe (PID: 3900)
Creates files in the user directory
- iexplore.exe (PID: 3900)
Changes settings of System certificates
- iexplore.exe (PID: 3900)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3900)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
50
Monitored processes
6
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
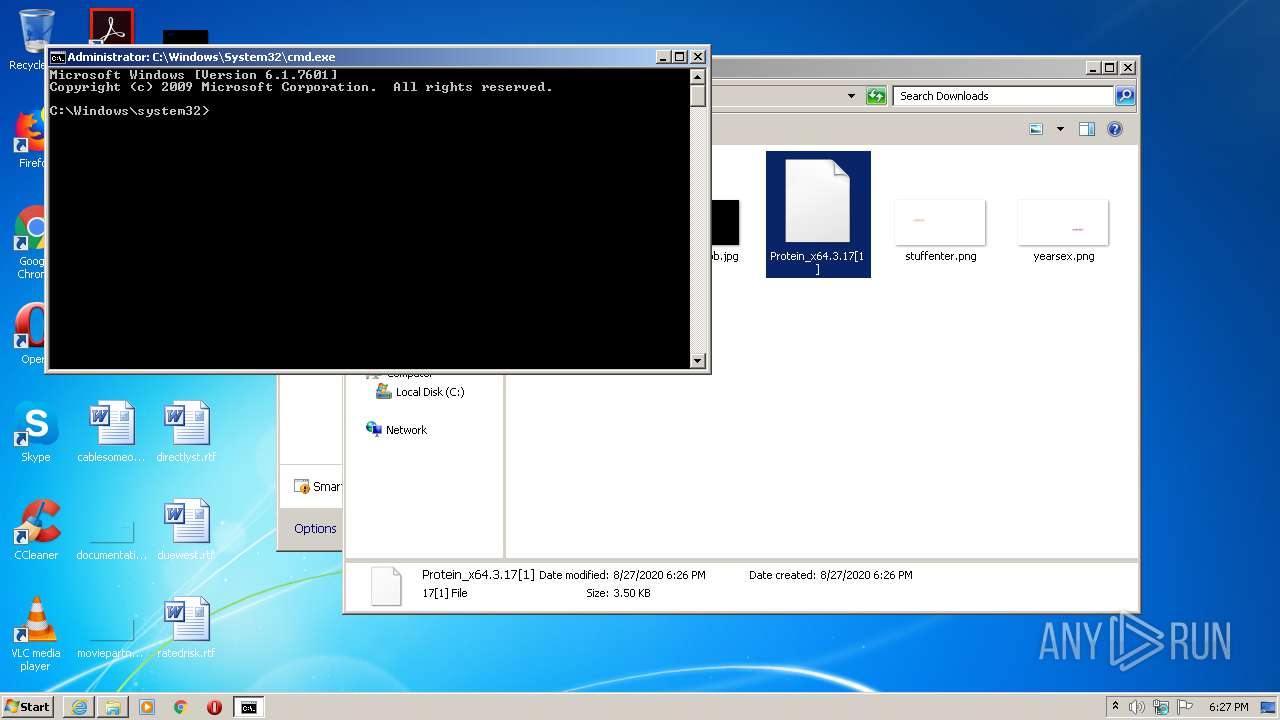
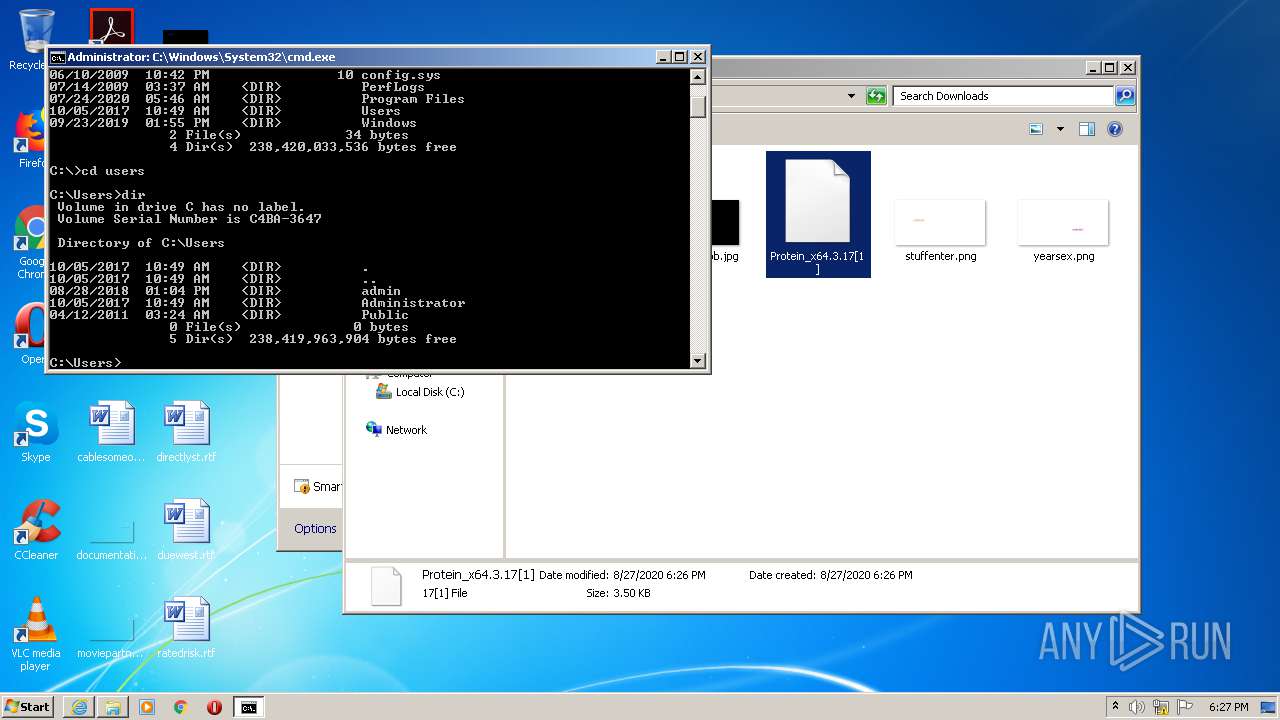
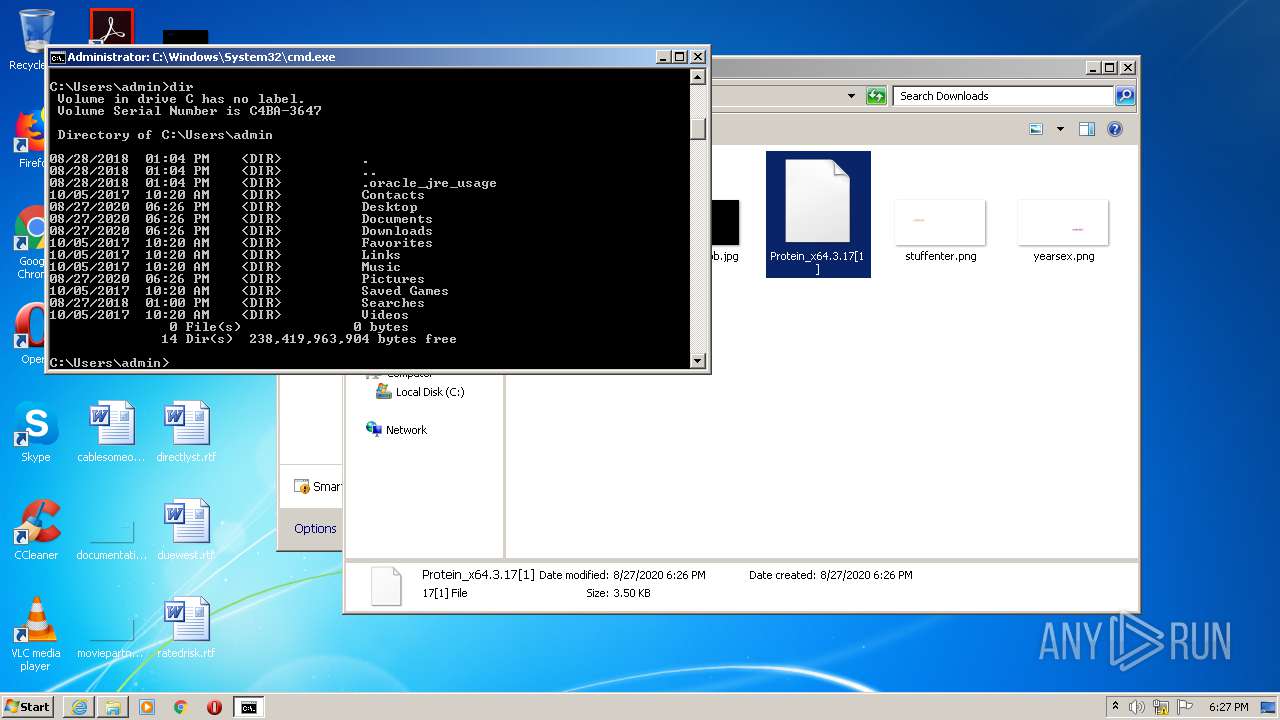
| 2620 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3736 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 4294967295 Version: 4.1 Modules
| |||||||||||||||
| 3764 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Windows\System32\cmd.exe" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
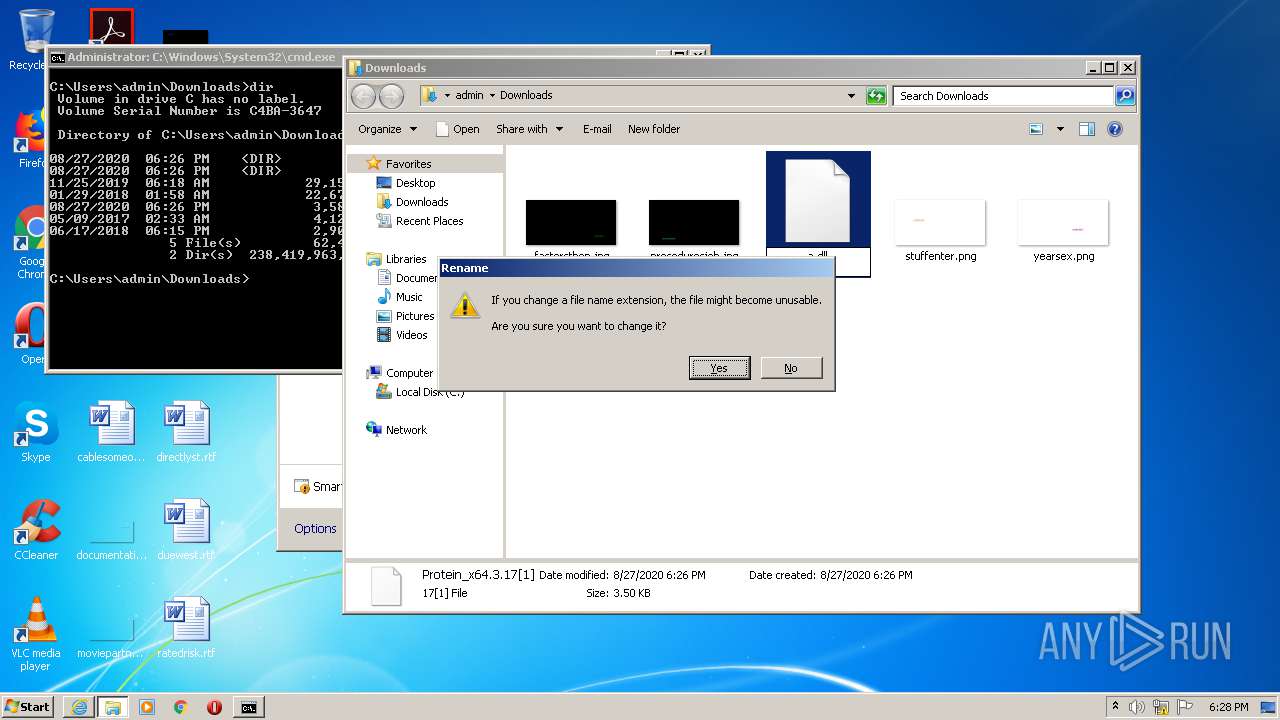
| 3772 | regsvr32 a.dll | C:\Windows\system32\regsvr32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3804 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3900 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3900 | "C:\Program Files\Internet Explorer\iexplore.exe" https://filebin.net/icb3wnev8fxh0h6d/Protein_x64.3.17.dll?t=y0zkdlhf | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
967
Read events
866
Write events
100
Delete events
1
Modification events
| (PID) Process: | (3900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1089668260 | |||
| (PID) Process: | (3900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30833815 | |||
| (PID) Process: | (3900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3900) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
2
Suspicious files
6
Text files
9
Unknown types
1
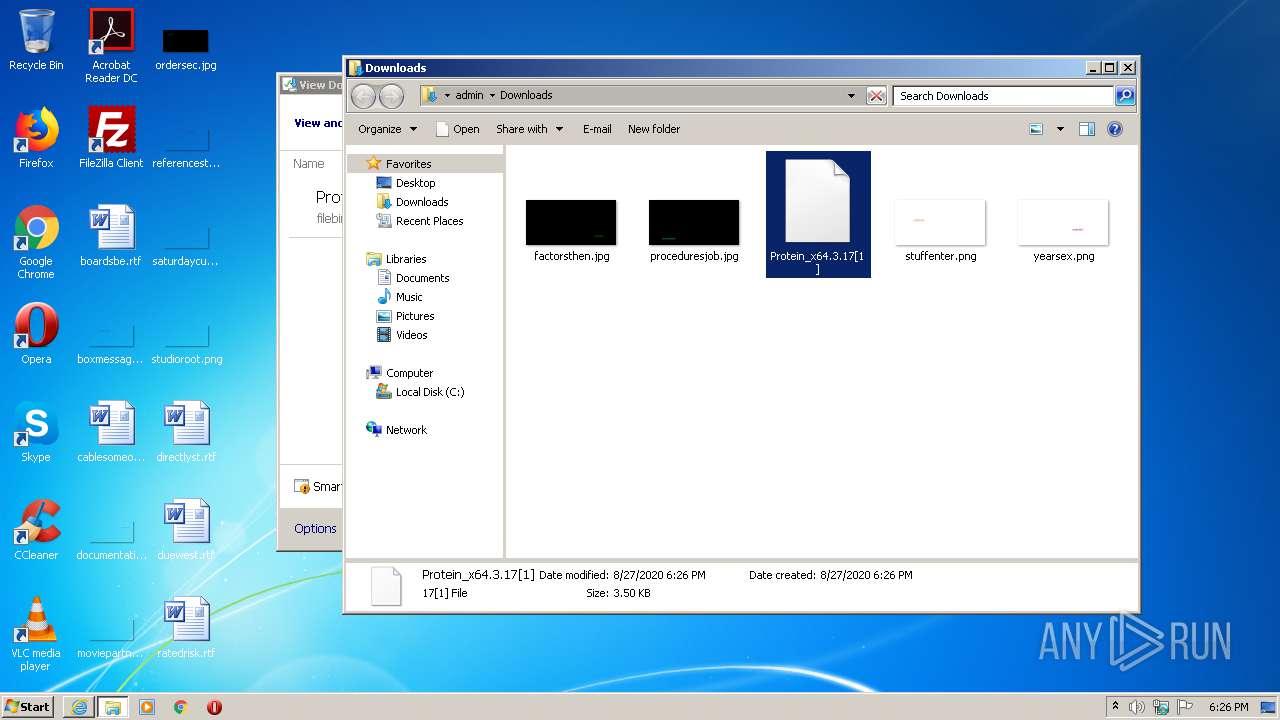
Dropped files
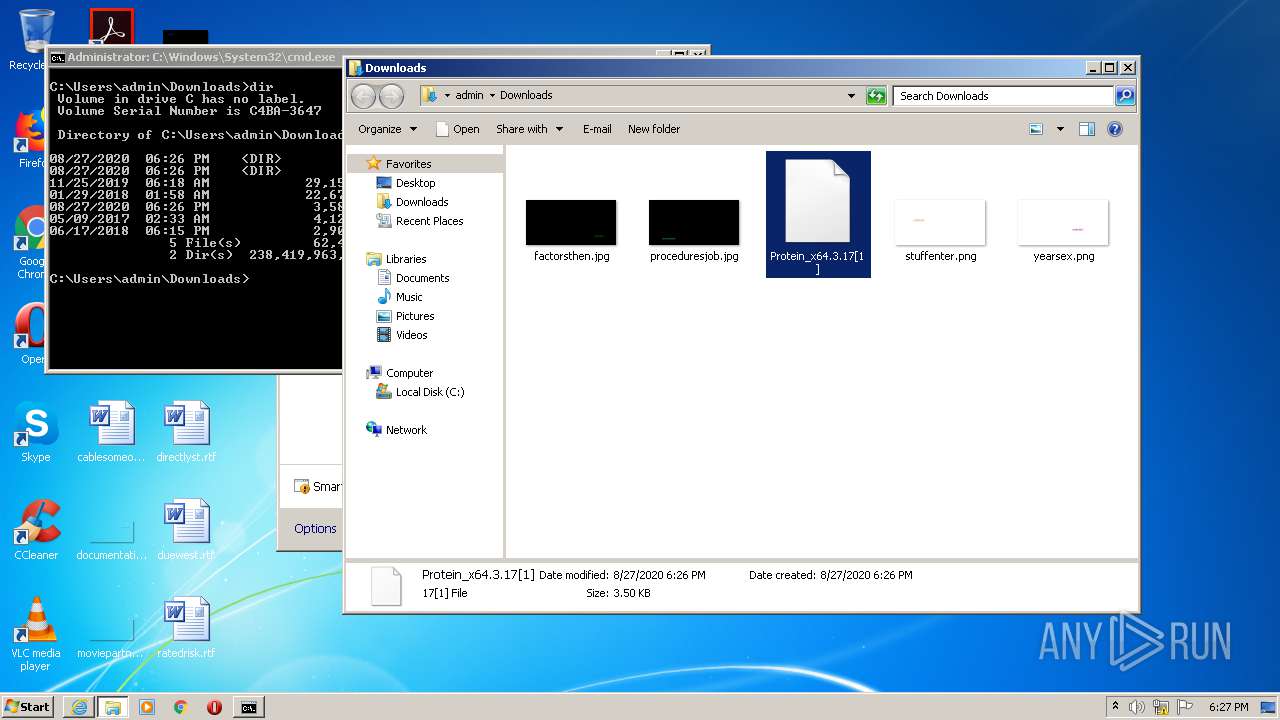
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3804 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab2518.tmp | — | |
MD5:— | SHA256:— | |||
| 3804 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar2519.tmp | — | |
MD5:— | SHA256:— | |||
| 3804 | iexplore.exe | C:\Users\admin\Downloads\Protein_x64.3.17[1].39rursv.partial | — | |
MD5:— | SHA256:— | |||
| 3900 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF5D353F50327710B7.TMP | — | |
MD5:— | SHA256:— | |||
| 3900 | iexplore.exe | C:\Users\admin\Downloads\Protein_x64.3.17[1].39rursv.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 3900 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabCC8.tmp | — | |
MD5:— | SHA256:— | |||
| 3900 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarCC9.tmp | — | |
MD5:— | SHA256:— | |||
| 3900 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\verCE9.tmp | — | |
MD5:— | SHA256:— | |||
| 3900 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\7WSXUJI3.txt | — | |
MD5:— | SHA256:— | |||
| 3900 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\DGAHGVPE.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
15
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEA7yTSbUNi7CXXtef0luXqk%3D | US | der | 280 b | whitelisted |
1048 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
1048 | svchost.exe | GET | 200 | 2.16.186.120:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | der | 550 b | whitelisted |
3804 | iexplore.exe | GET | 200 | 2.16.186.35:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
— | — | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 5.42 Kb | whitelisted |
1048 | svchost.exe | GET | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/GTSGIAG3/MEkwRzBFMEMwQTAJBgUrDgMCGgUABBT27bBjYjKBmjX2jXWgnQJKEapsrQQUd8K4UJpndnaxLcKG0IOgfqZ%2BuksCCCR1UqpKNfC0 | US | binary | 5 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3804 | iexplore.exe | 185.47.40.36:443 | filebin.net | Redpill Linpro AS | NO | malicious |
3804 | iexplore.exe | 2.16.186.35:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3736 | gup.exe | 104.31.88.28:443 | notepad-plus-plus.org | Cloudflare Inc | US | shared |
3900 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3900 | iexplore.exe | 204.79.197.200:443 | ieonline.microsoft.com | Microsoft Corporation | US | whitelisted |
1048 | svchost.exe | 216.58.208.35:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
— | — | 2.16.186.120:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
filebin.net |
| suspicious |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
dns.msftncsi.com |
| shared |
notepad-plus-plus.org |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabl |
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|