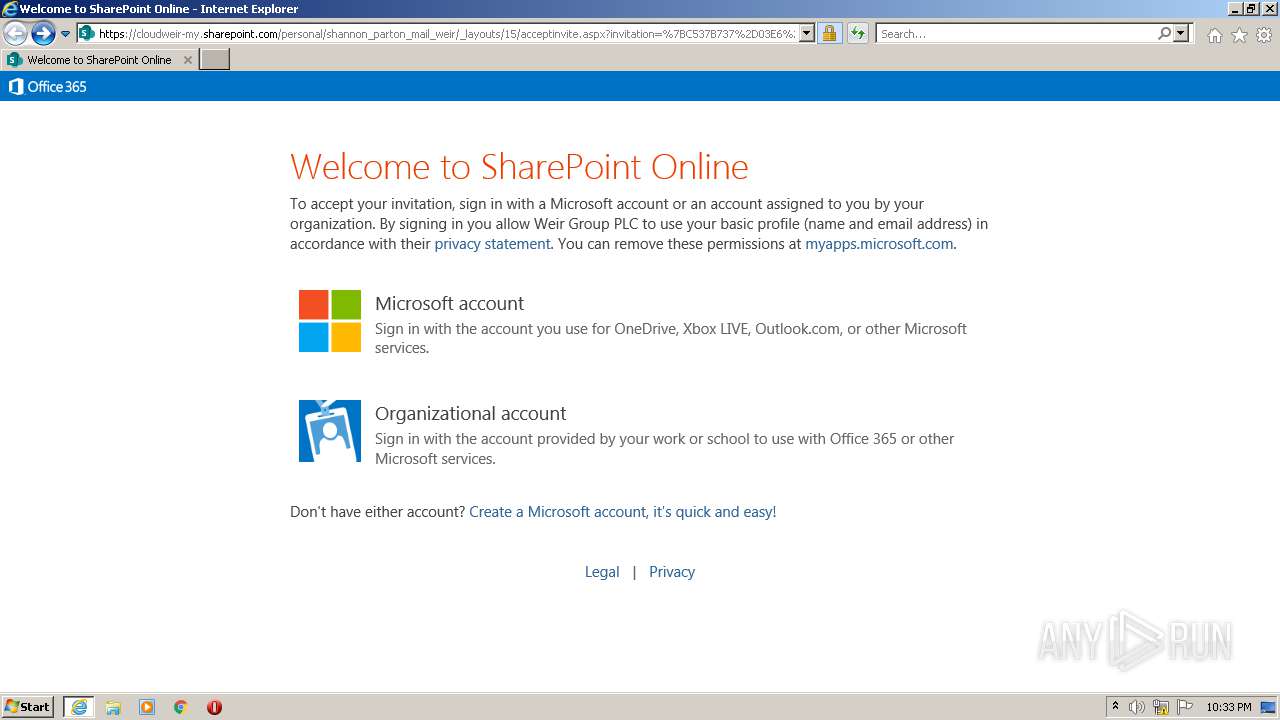
| URL: | https://cloudweir-my.sharepoint.com/personal/shannon_parton_mail_weir/_layouts/15/acceptinvite.aspx?invitation=%7BC537B737%2D03E6%2D47B0%2D83A5%2DA6BD8AFA8F0A%7D&listId=b6359586%2D513c%2D4d9d%2D8807%2D9533e81c0577&itemId=c72b0793%2Dc956%2D4794%2Da45f%2D07bb2fae56fb |
| Full analysis: | https://app.any.run/tasks/ad51dbd9-c906-4700-b282-270d6ef2909f |
| Verdict: | Malicious activity |
| Analysis date: | October 01, 2021, 21:32:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | ED47D29D781BD61A1E384FFC00660BB8 |
| SHA1: | 18B3AAB009A0E81F10937BD2326449F725392582 |
| SHA256: | 50ABE55C90CED260824976B2BE9DBA1D301E5FCD13614E2D16024D0813198CF7 |
| SSDEEP: | 6:2UY5WL/AfsXJm9PfVm2yNd019sEfFyhR9SSDI3B0ckER+X2H:2UY5cJ+P82ys19HFyhRwd3BLRMg |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3052)
INFO
Application launched itself
- iexplore.exe (PID: 1200)
Checks supported languages
- iexplore.exe (PID: 3052)
- iexplore.exe (PID: 1200)
Checks Windows Trust Settings
- iexplore.exe (PID: 1200)
- iexplore.exe (PID: 3052)
Reads settings of System Certificates
- iexplore.exe (PID: 3052)
- iexplore.exe (PID: 1200)
Changes settings of System certificates
- iexplore.exe (PID: 1200)
Reads the computer name
- iexplore.exe (PID: 3052)
- iexplore.exe (PID: 1200)
Changes internet zones settings
- iexplore.exe (PID: 1200)
Reads internet explorer settings
- iexplore.exe (PID: 3052)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1200)
Creates files in the user directory
- iexplore.exe (PID: 3052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
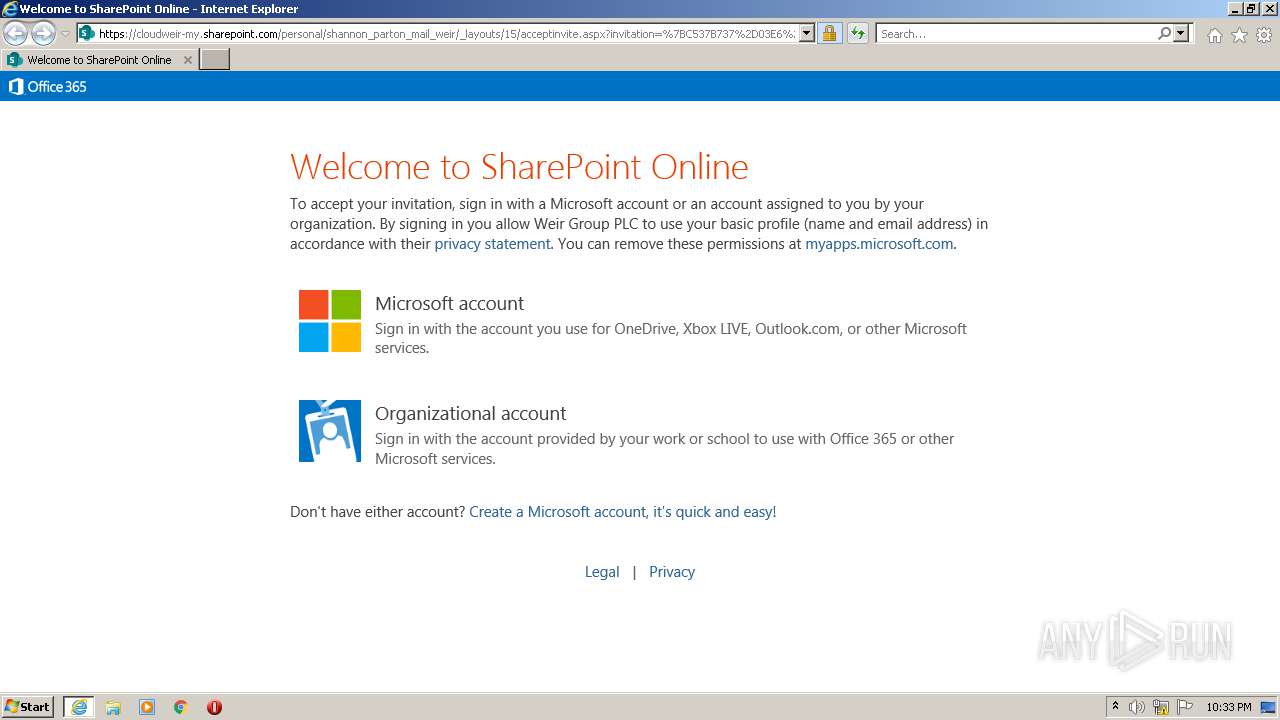
| 1200 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://cloudweir-my.sharepoint.com/personal/shannon_parton_mail_weir/_layouts/15/acceptinvite.aspx?invitation=%7BC537B737%2D03E6%2D47B0%2D83A5%2DA6BD8AFA8F0A%7D&listId=b6359586%2D513c%2D4d9d%2D8807%2D9533e81c0577&itemId=c72b0793%2Dc956%2D4794%2Da45f%2D07bb2fae56fb" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
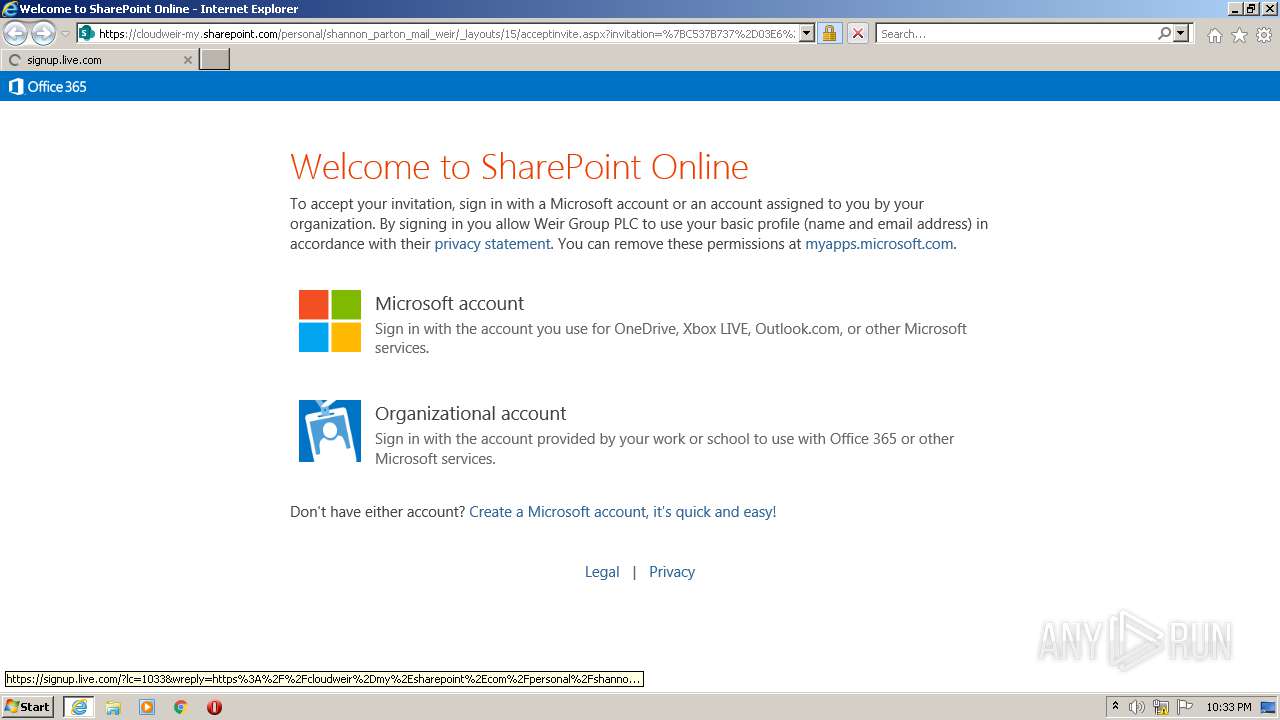
| 3052 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1200 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
16 720
Read events
16 601
Write events
117
Delete events
2
Modification events
| (PID) Process: | (1200) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1200) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1200) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30914315 | |||
| (PID) Process: | (1200) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1200) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30914315 | |||
| (PID) Process: | (1200) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1200) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1200) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1200) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1200) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
10
Text files
44
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3052 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\2F23D0F5E4D72862517E1CB26A329742_F6FACC49395CFA949BCE851E73323C49 | der | |
MD5:— | SHA256:— | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\2F23D0F5E4D72862517E1CB26A329742_F6FACC49395CFA949BCE851E73323C49 | binary | |
MD5:— | SHA256:— | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:— | SHA256:— | |||
| 1200 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\WindowsLiveHotmail[1].png | image | |
MD5:2F6B2AC283DCE9A4930FF7AAD20556B0 | SHA256:DA7B1E7C0E95A9CABA46BE191F562268CEE236556F67E4B10F2B3A05785B9CAD | |||
| 1200 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\acceptinvite[1].htm | html | |
MD5:— | SHA256:— | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:— | SHA256:— | |||
| 1200 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\MicrosoftOnlineServiceID[1].png | image | |
MD5:5E933C5F37ACCD2769A2E3DBC91FC4AF | SHA256:989B447AE71AF111EF417AC1C41B09E8F6A6C34AB4B222E78CFA2B0F3C935B11 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
43
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3052 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | US | der | 471 b | whitelisted |
3052 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAGewca9P1l7sgwzOOVR2Hc%3D | US | der | 471 b | whitelisted |
1200 | iexplore.exe | GET | 200 | 67.27.159.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7c04b079e6b67941 | US | compressed | 4.70 Kb | whitelisted |
1200 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
1200 | iexplore.exe | GET | 200 | 67.27.159.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a9ed038dc7e640df | US | compressed | 4.70 Kb | whitelisted |
3052 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3052 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | der | 471 b | whitelisted |
3052 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1200 | iexplore.exe | 67.27.159.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | malicious |
1200 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1200 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3052 | iexplore.exe | 13.107.42.22:443 | signup.live.com | Microsoft Corporation | US | suspicious |
3052 | iexplore.exe | 20.190.160.67:443 | login.live.com | Microsoft Corporation | US | suspicious |
1200 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1200 | iexplore.exe | 152.199.21.175:443 | acctcdn.msauth.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3052 | iexplore.exe | 13.69.109.131:443 | browser.events.data.microsoft.com | Microsoft Corporation | NL | suspicious |
3052 | iexplore.exe | 152.199.21.175:443 | acctcdn.msauth.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 192.229.221.185:443 | logincdn.msauth.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cloudweir-my.sharepoint.com |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
signup.live.com |
| whitelisted |
login.live.com |
| whitelisted |
acctcdn.msauth.net |
| whitelisted |
browser.events.data.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |