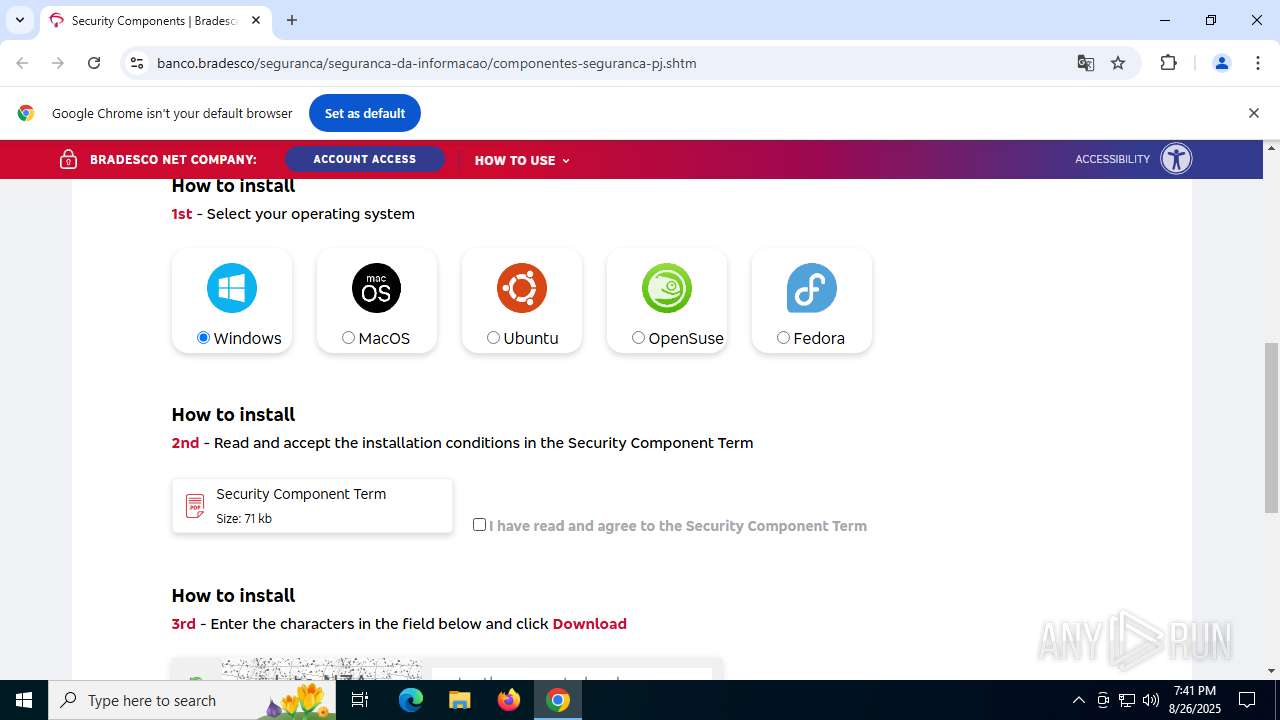
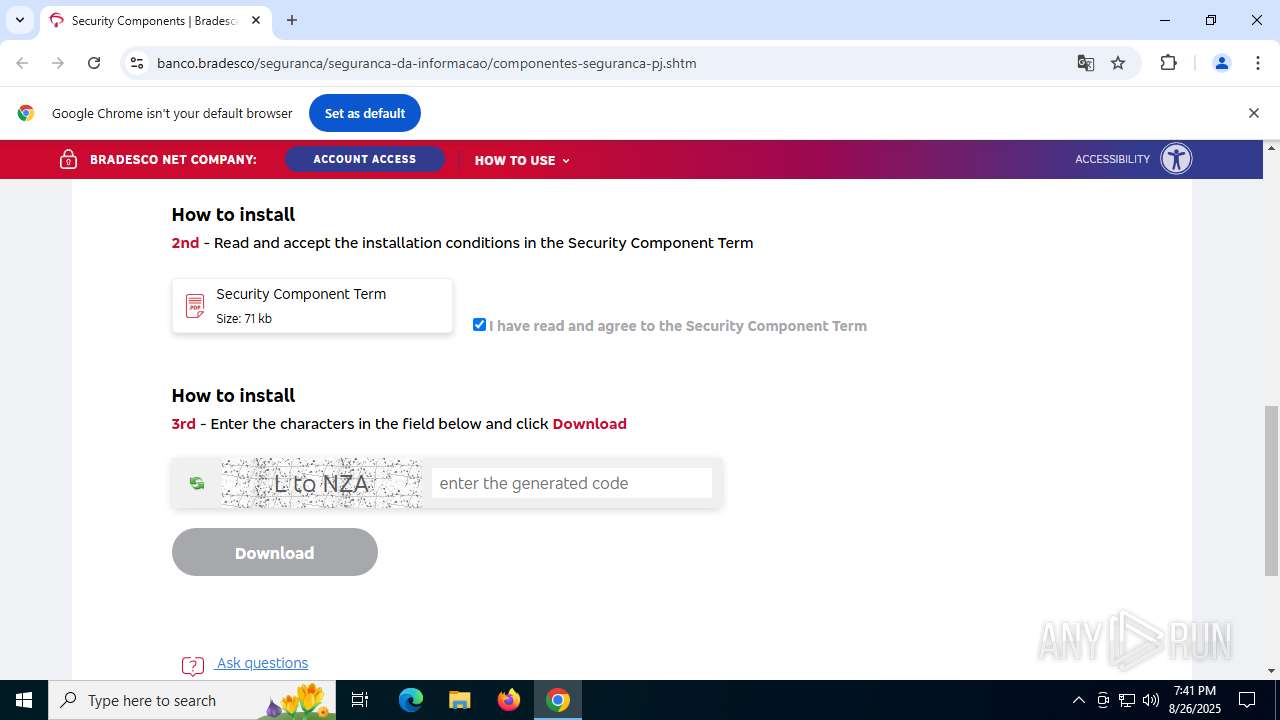
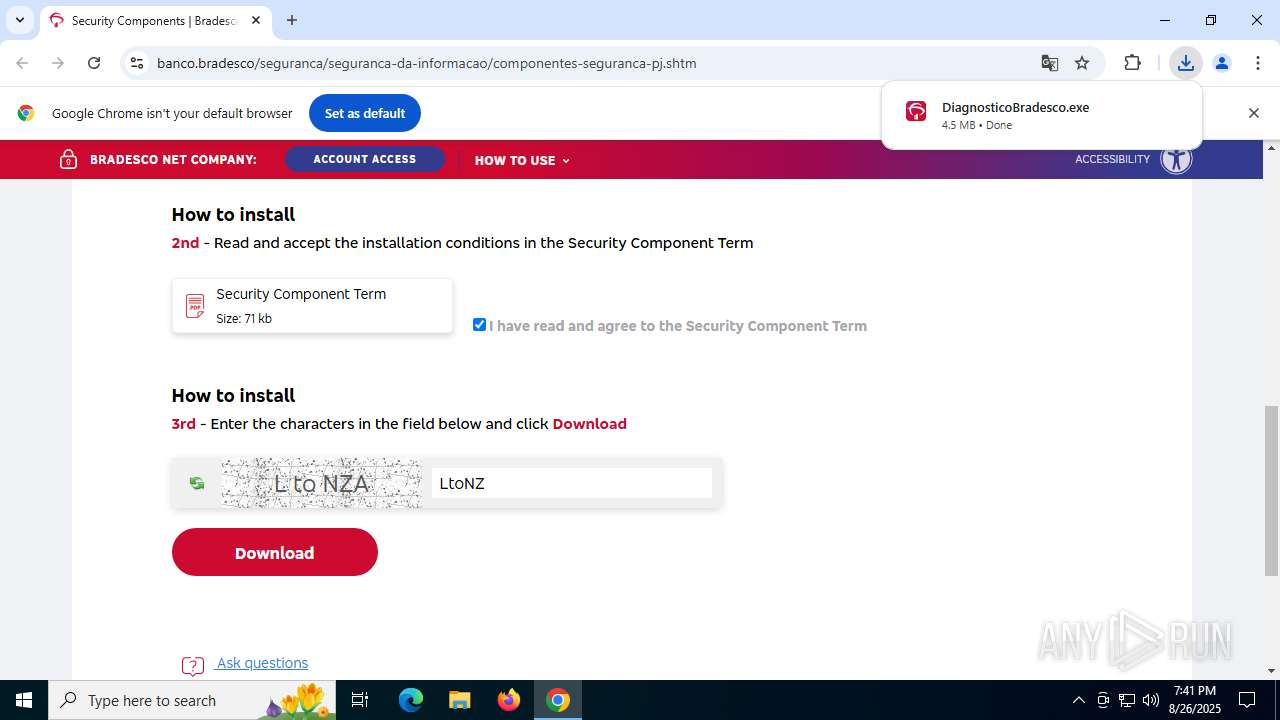
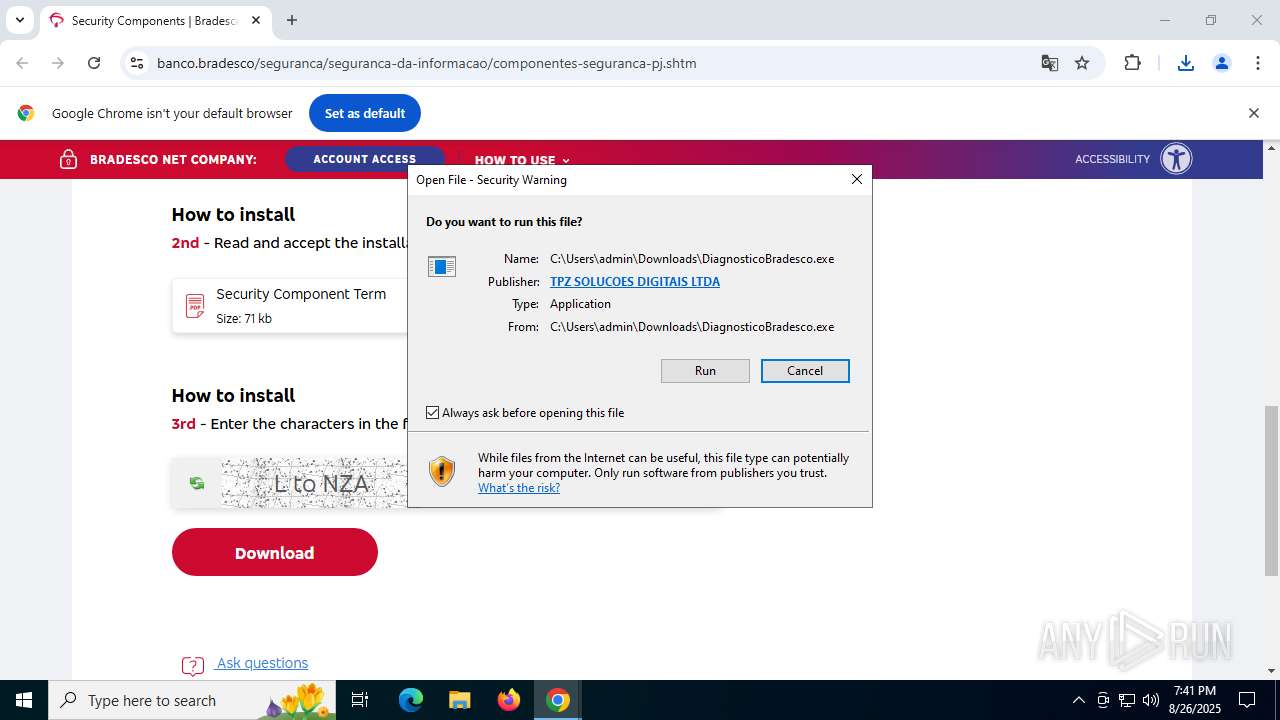
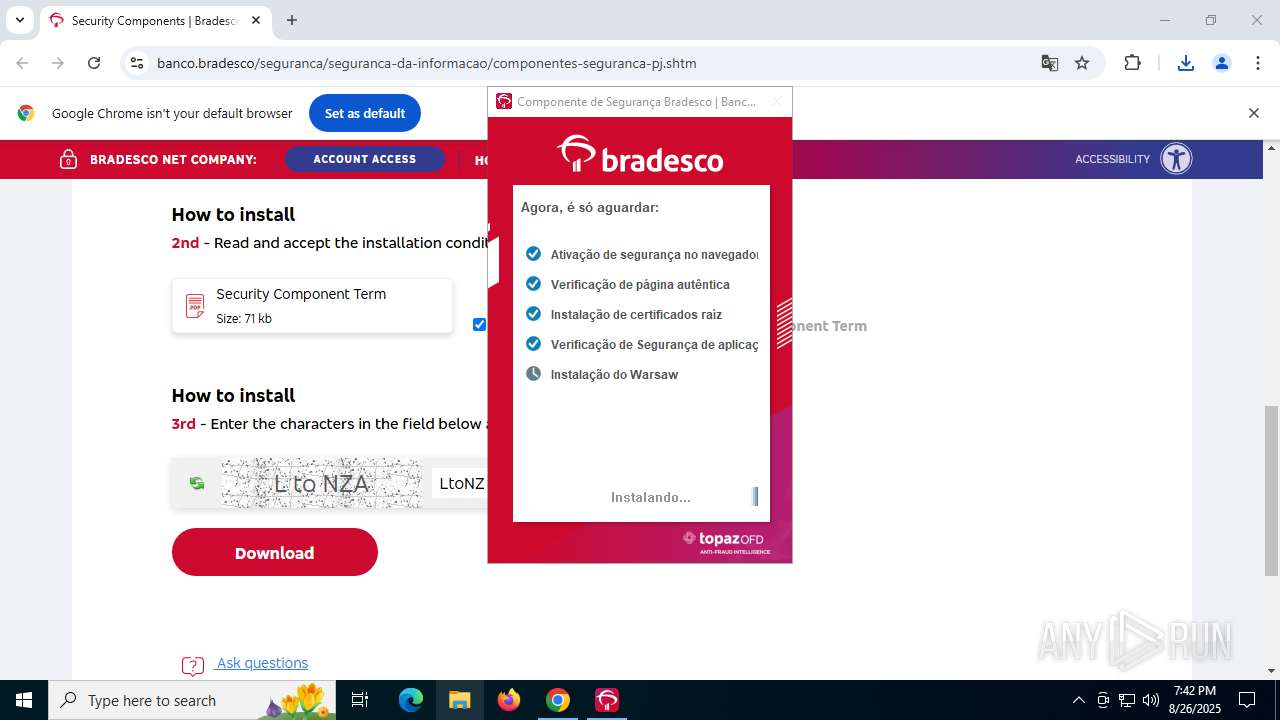
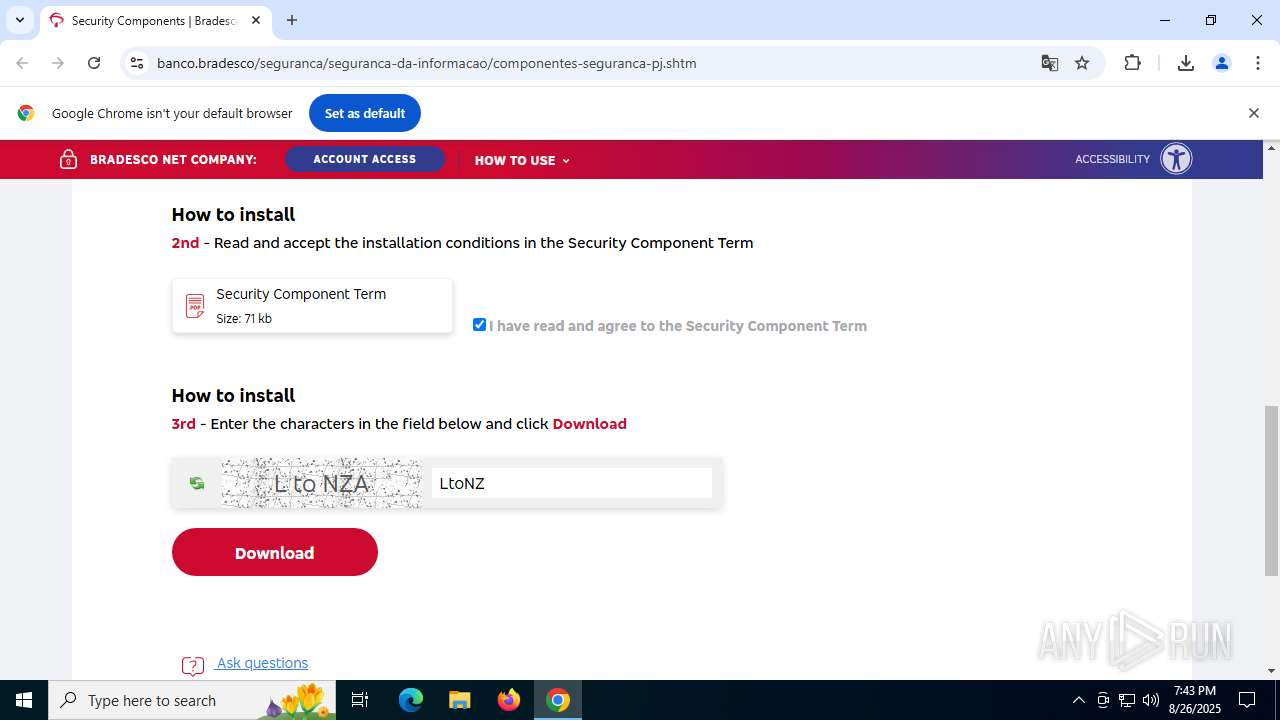
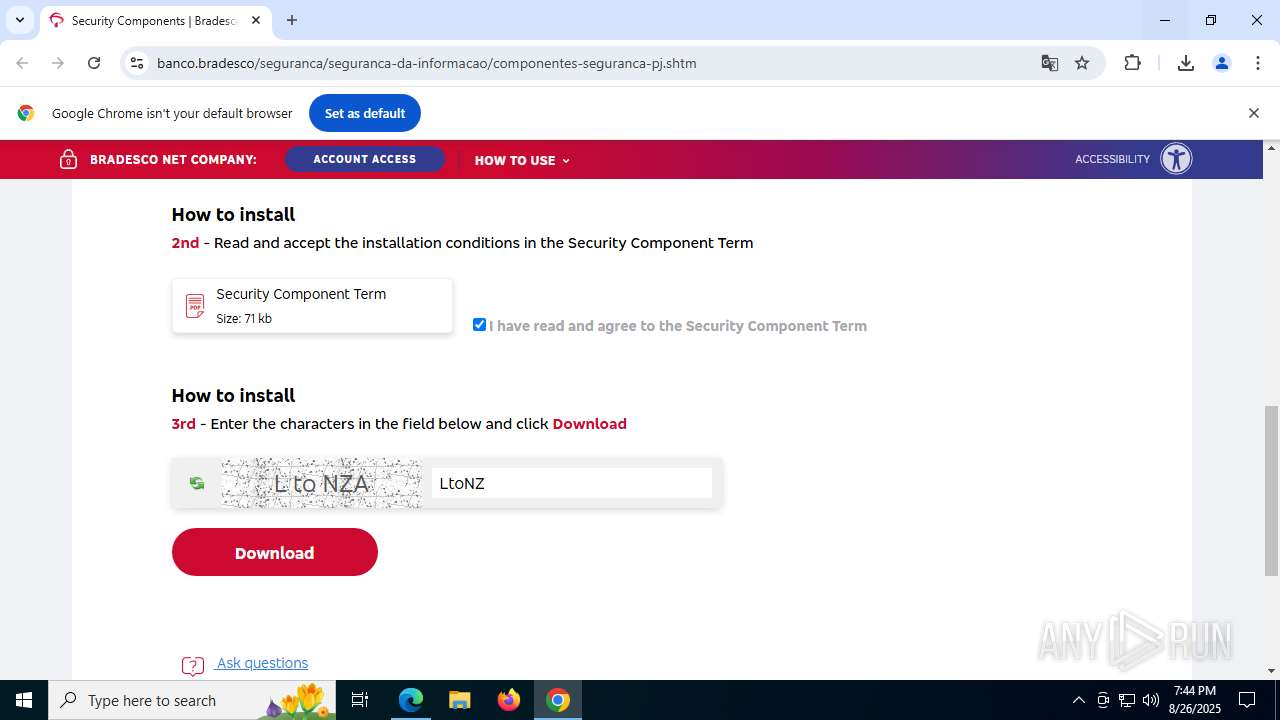
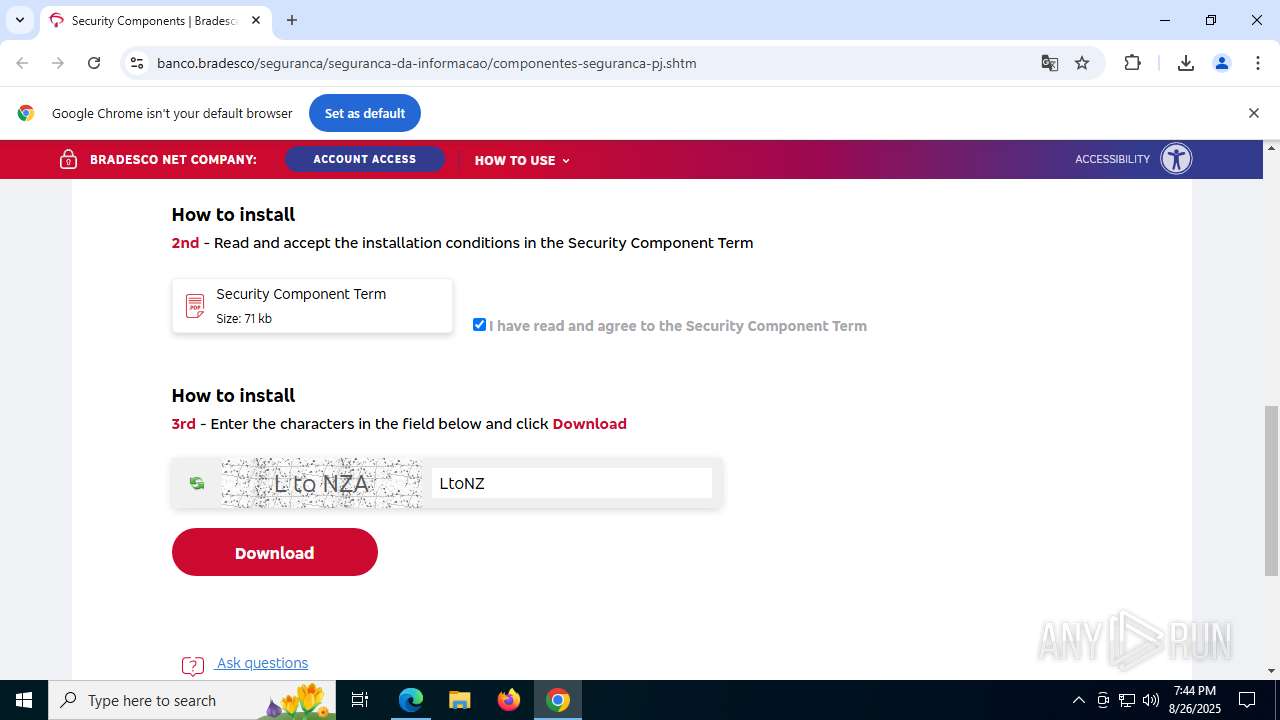
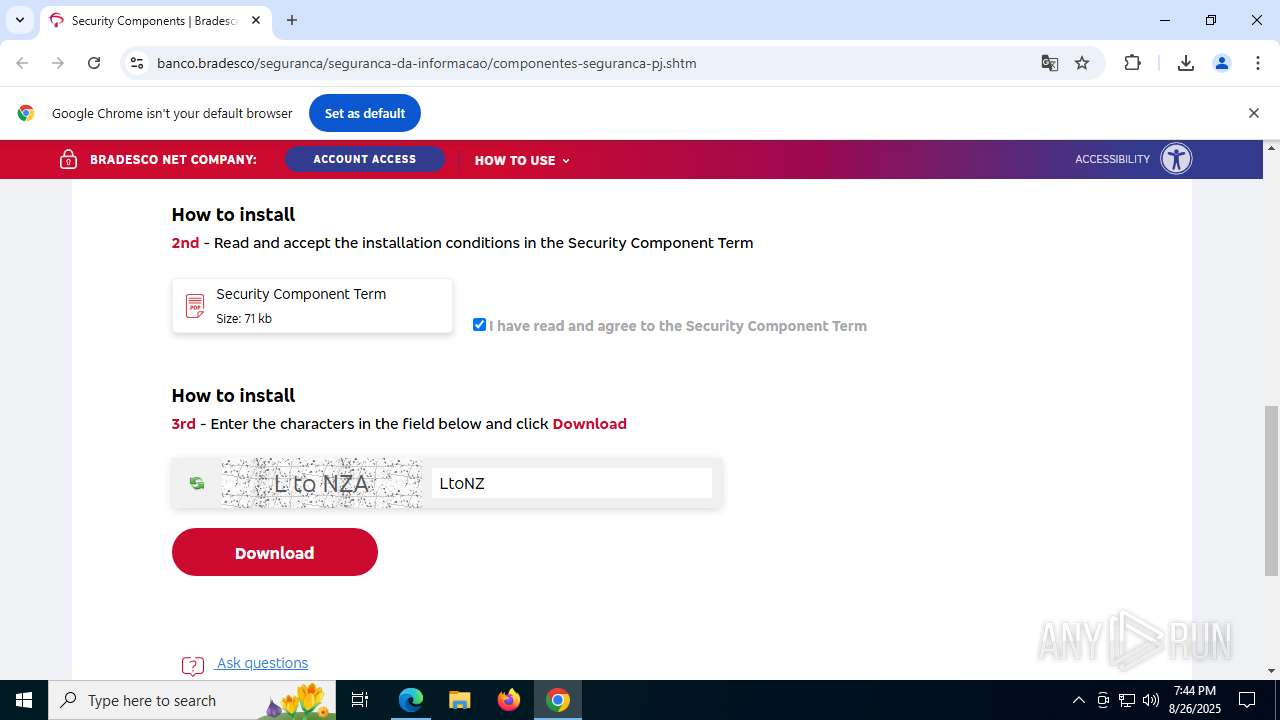
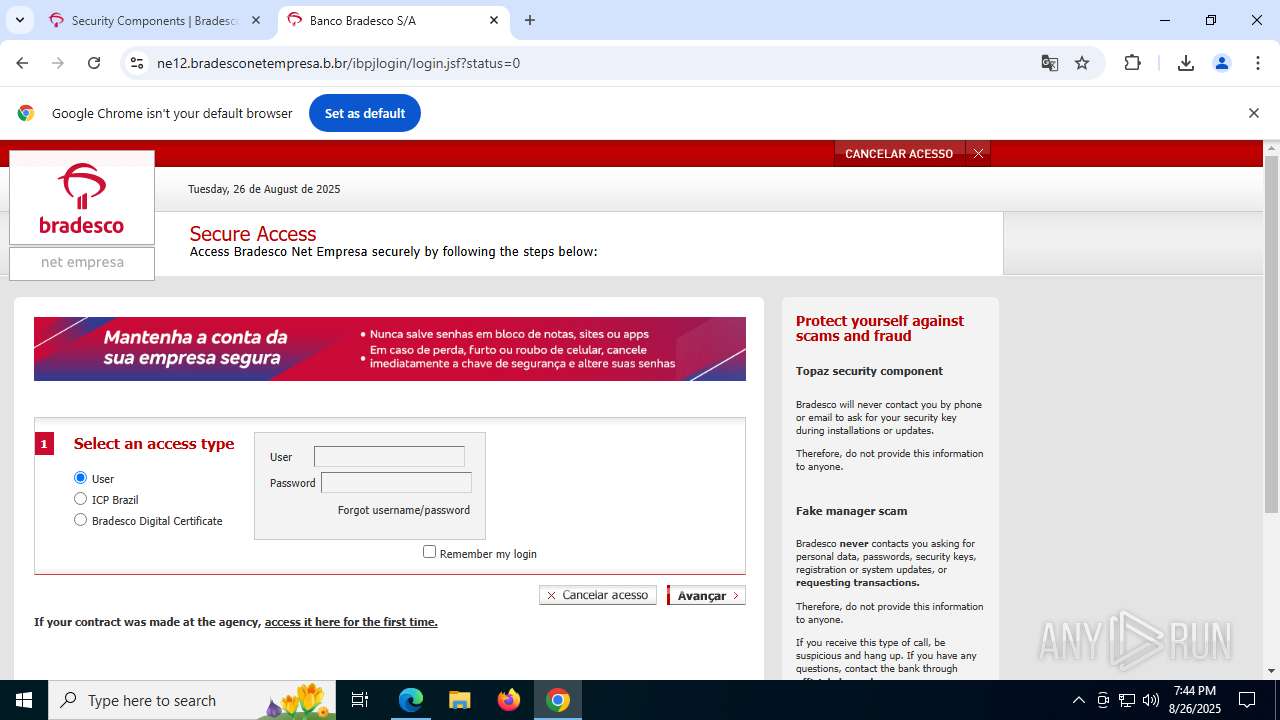
| URL: | https://banco.bradesco/seguranca/seguranca-da-informacao/componentes-seguranca-pj.shtm |
| Full analysis: | https://app.any.run/tasks/b5c0243b-a408-4fa2-ba8d-442c40fe2179 |
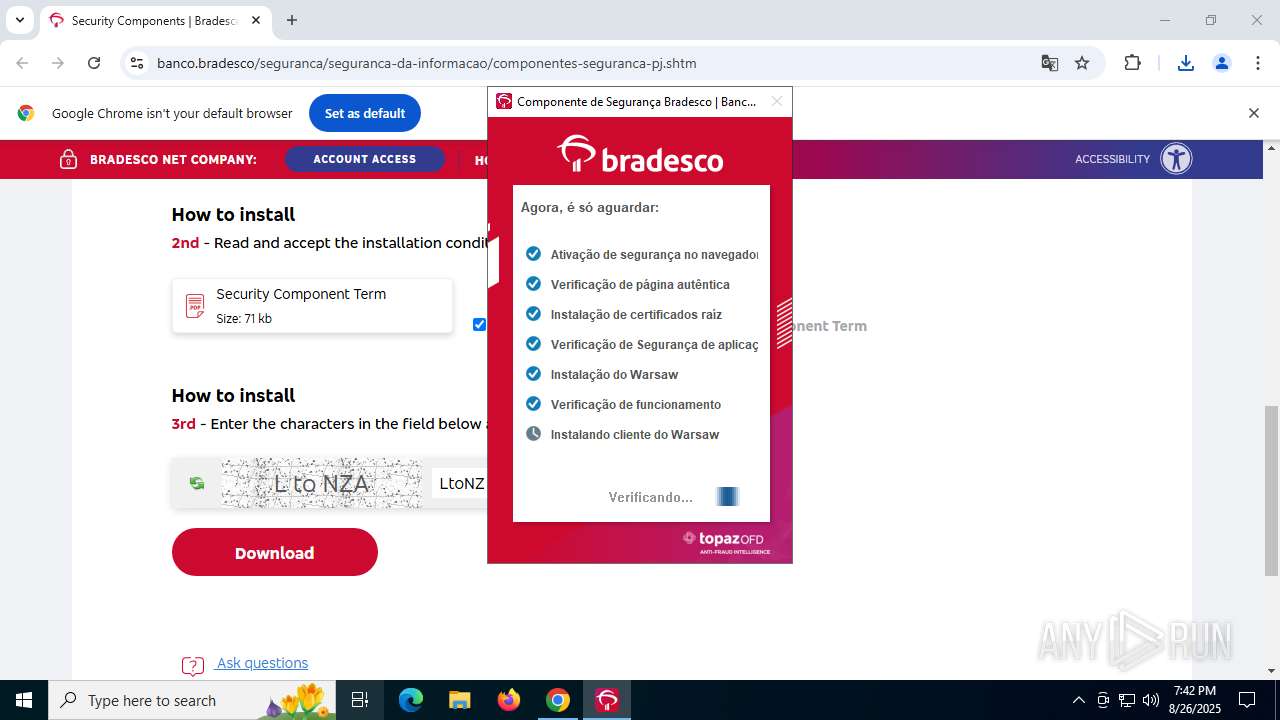
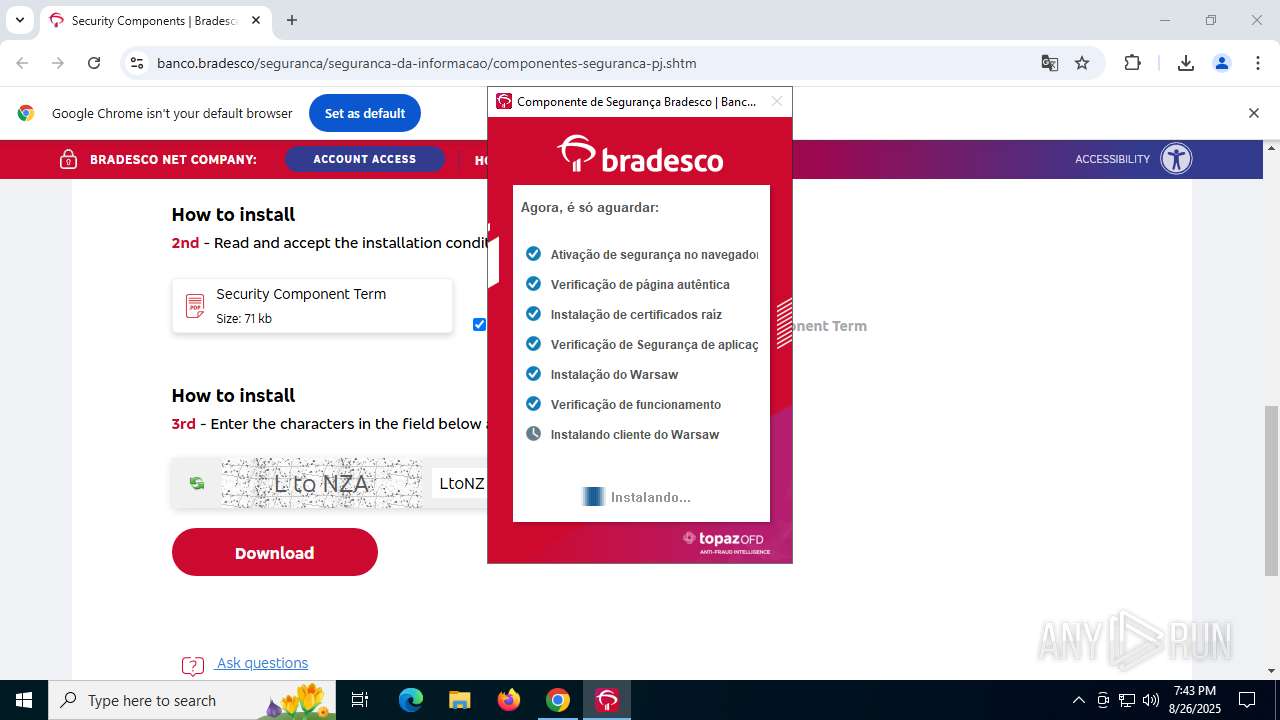
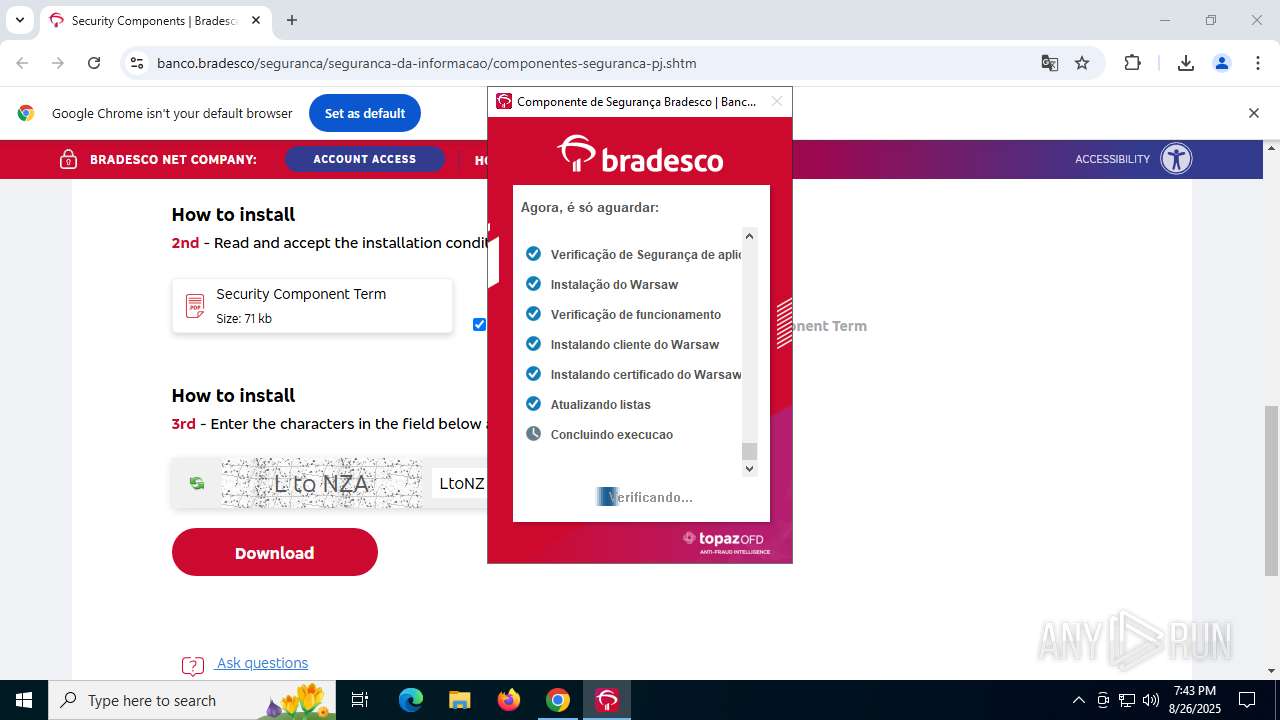
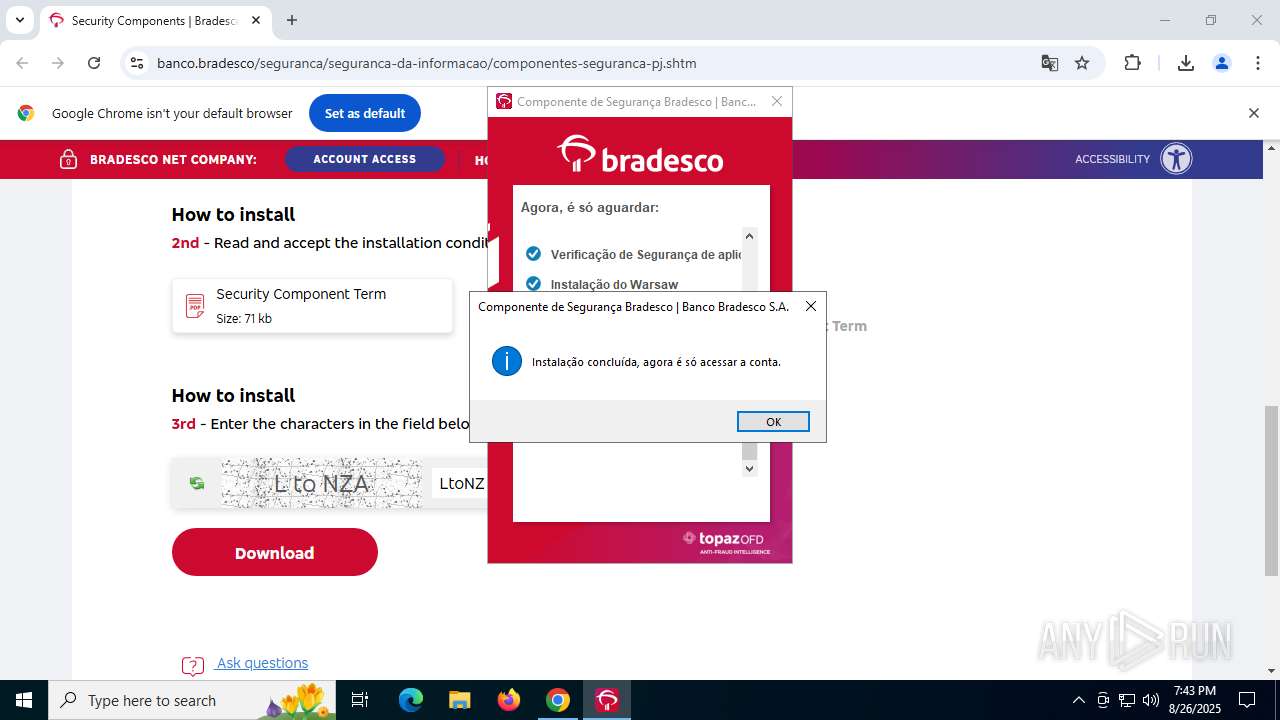
| Verdict: | Malicious activity |
| Analysis date: | August 26, 2025, 19:41:21 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A3CFEC38924DFF3204DDE576A0801E37 |
| SHA1: | 81ADD49FB0075548E4B866F8CD94A87D9827F34E |
| SHA256: | 50A58D1CF9F8C612C9C742DE465FA2545458E5DF4205ECF54DAD80FB27DC1BA3 |
| SSDEEP: | 3:N8zQHZWnCEaHbEYWDKoEPbAdrCXRWUn:2857ECbEDDKdmCp |
MALICIOUS
Deletes shadow copies
- cmd.exe (PID: 7304)
- cmd.exe (PID: 7380)
- cmd.exe (PID: 7276)
Application was injected by another process
- ctfmon.exe (PID: 4468)
- dllhost.exe (PID: 5604)
- dllhost.exe (PID: 2484)
Runs injected code in another process
- core.exe (PID: 7104)
XORed URL has been found (YARA)
- core.exe (PID: 7104)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- DiagnosticoBradesco.exe (PID: 7884)
- DiagnosticoBradesco.exe (PID: 8008)
- core.exe (PID: 7812)
Reads security settings of Internet Explorer
- DiagnosticoBradesco.exe (PID: 7884)
- core.exe (PID: 7812)
Application launched itself
- DiagnosticoBradesco.exe (PID: 7884)
- core.exe (PID: 7104)
- cmd.exe (PID: 5548)
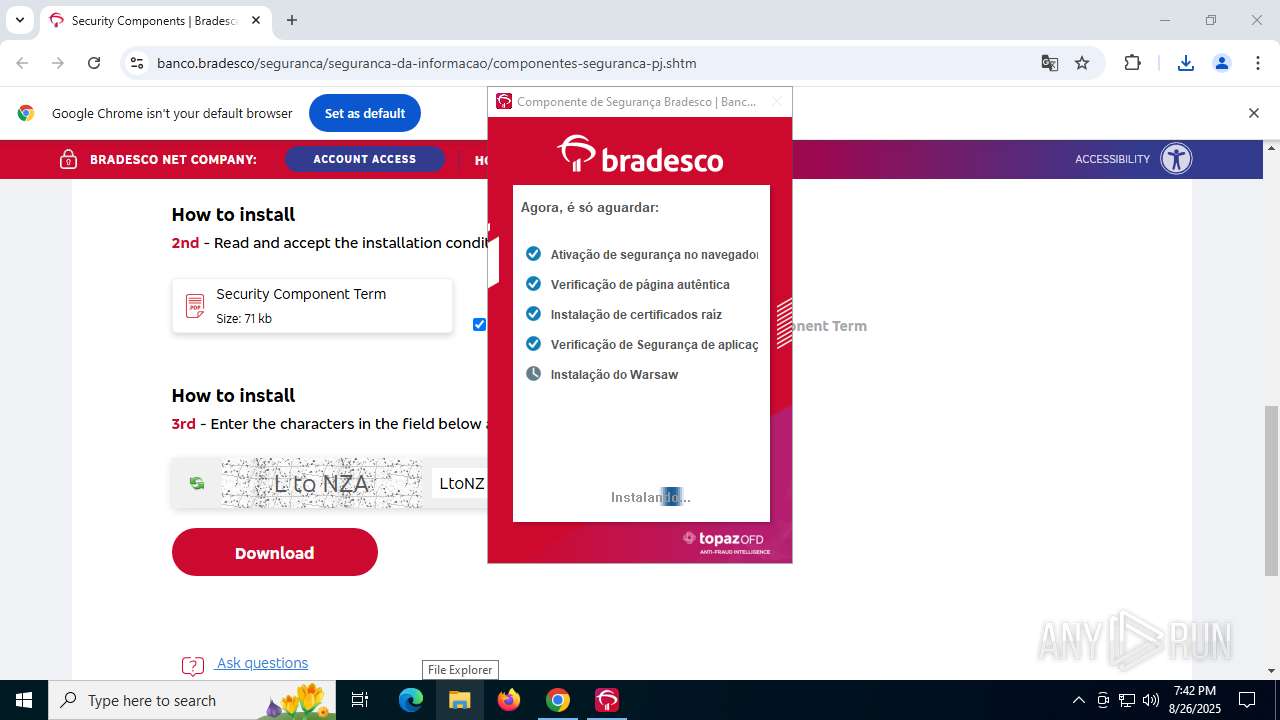
Executes as Windows Service
- DiagnosticoBradesco.exe (PID: 8008)
- core.exe (PID: 7104)
Executable content was dropped or overwritten
- warsaw_setup_64.exe (PID: 8104)
- DiagnosticoBradesco.exe (PID: 7884)
- warsaw_setup_64.tmp (PID: 8124)
- core.exe (PID: 7104)
- drvinst.exe (PID: 7984)
- DiagnosticoBradesco.exe (PID: 8008)
Reads the Windows owner or organization settings
- warsaw_setup_64.tmp (PID: 8124)
Uses WMIC.EXE to obtain data on processes
- cmd.exe (PID: 7276)
- cmd.exe (PID: 7304)
- cmd.exe (PID: 7380)
Detected use of alternative data streams (AltDS)
- warsaw_setup_64.tmp (PID: 8124)
- core.exe (PID: 7104)
- DiagnosticoBradesco.exe (PID: 7884)
Process drops legitimate windows executable
- warsaw_setup_64.tmp (PID: 8124)
- core.exe (PID: 7104)
Starts CMD.EXE for commands execution
- warsaw_setup_64.tmp (PID: 8124)
- cmd.exe (PID: 5548)
- core.exe (PID: 7104)
Creates a software uninstall entry
- warsaw_setup_64.tmp (PID: 8124)
- core.exe (PID: 7104)
The process drops C-runtime libraries
- warsaw_setup_64.tmp (PID: 8124)
- core.exe (PID: 7104)
Drops a system driver (possible attempt to evade defenses)
- warsaw_setup_64.tmp (PID: 8124)
- drvinst.exe (PID: 7984)
Creates files in the driver directory
- warsaw_setup_64.tmp (PID: 8124)
- core.exe (PID: 7104)
- drvinst.exe (PID: 7984)
Creates or modifies Windows services
- core.exe (PID: 7104)
Reads the BIOS version
- core.exe (PID: 7104)
- DiagnosticoBradesco.exe (PID: 7884)
Windows service management via SC.EXE
- sc.exe (PID: 7768)
Starts SC.EXE for service management
- warsaw_setup_64.tmp (PID: 8124)
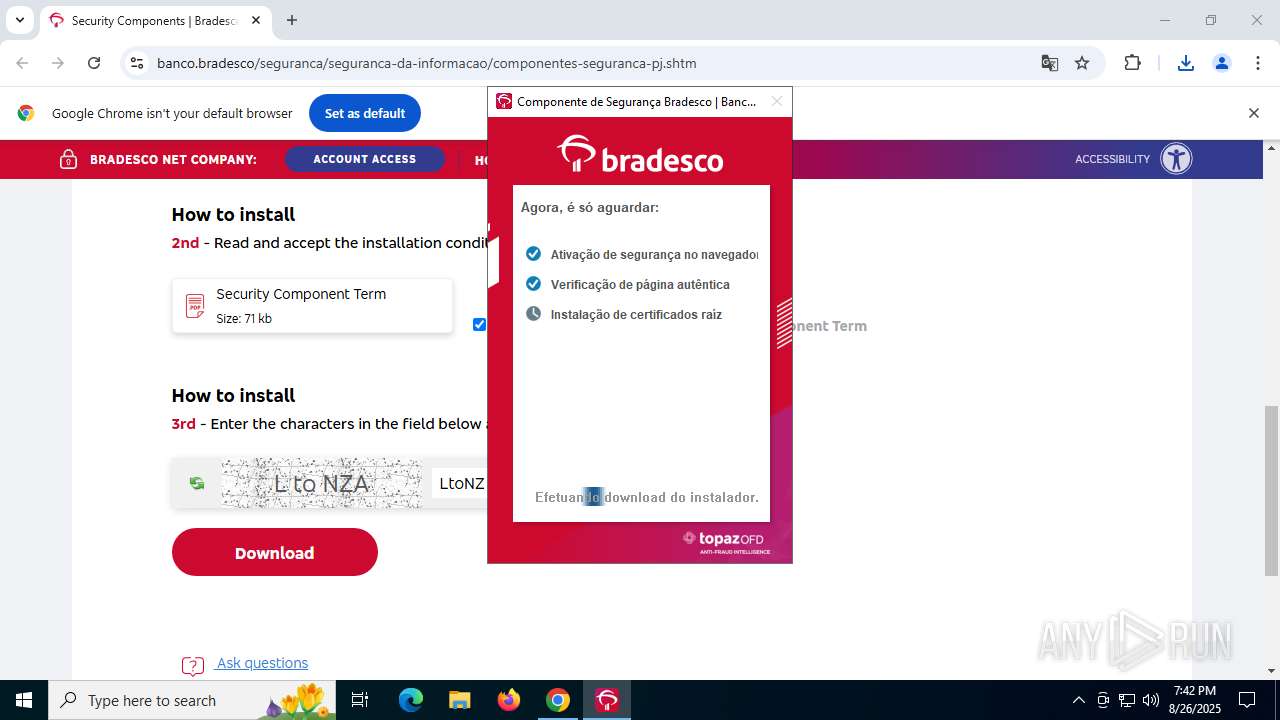
Adds/modifies Windows certificates
- core.exe (PID: 7104)
- wsffcmgr64.exe (PID: 4012)
Executing commands from a ".bat" file
- warsaw_setup_64.tmp (PID: 8124)
Get information on the list of running processes
- cmd.exe (PID: 5548)
- cmd.exe (PID: 4044)
Creates/Modifies COM task schedule object
- core.exe (PID: 7104)
Loads DLL from Mozilla Firefox
- wsffcmgr64.exe (PID: 4012)
- wsffcmgr64.exe (PID: 5576)
- wsffcmgr64.exe (PID: 3476)
- ffcu.dat (PID: 7300)
Reads the date of Windows installation
- core.exe (PID: 7104)
Searches for installed software
- core.exe (PID: 7104)
Found regular expressions for crypto-addresses (YARA)
- core.exe (PID: 7104)
Starts application with an unusual extension
- DiagnosticoBradesco.exe (PID: 8008)
Executes application which crashes
- DiagnosticoBradesco.exe (PID: 8008)
INFO
Creates files in the program directory
- DiagnosticoBradesco.exe (PID: 7884)
- DiagnosticoBradesco.exe (PID: 8008)
- warsaw_setup_64.tmp (PID: 8124)
- core.exe (PID: 7104)
Reads the computer name
- DiagnosticoBradesco.exe (PID: 7884)
- DiagnosticoBradesco.exe (PID: 7984)
- DiagnosticoBradesco.exe (PID: 8008)
- warsaw_setup_64.tmp (PID: 8124)
- warsaw_setup_64.exe (PID: 8104)
- corefixer.exe (PID: 7644)
- core.exe (PID: 7812)
- core.exe (PID: 1652)
- core.exe (PID: 7104)
- drvinst.exe (PID: 7984)
- wsffcmgr64.exe (PID: 4012)
- wsffcmgr64.exe (PID: 5576)
- wsffcmgr64.exe (PID: 3476)
- identity_helper.exe (PID: 3840)
- ffcu.dat (PID: 7300)
Application launched itself
- chrome.exe (PID: 5952)
- msedge.exe (PID: 236)
Launching a file from the Downloads directory
- chrome.exe (PID: 5952)
Checks supported languages
- DiagnosticoBradesco.exe (PID: 7884)
- DiagnosticoBradesco.exe (PID: 7984)
- DiagnosticoBradesco.exe (PID: 8008)
- warsaw_setup_64.tmp (PID: 8124)
- get_version.exe (PID: 8144)
- get_version.exe (PID: 4044)
- warsaw_setup_64.exe (PID: 8104)
- wstlcup.exe (PID: 7700)
- corefixer.exe (PID: 7644)
- core.exe (PID: 1652)
- core.exe (PID: 7812)
- core.exe (PID: 7104)
- drvinst.exe (PID: 7984)
- wsffcmgr64.exe (PID: 4012)
- wsffcmgr64.exe (PID: 5576)
- wsffcmgr64.exe (PID: 3476)
- ffcu.dat (PID: 7300)
- identity_helper.exe (PID: 3840)
Executable content was dropped or overwritten
- chrome.exe (PID: 5952)
Reads the machine GUID from the registry
- DiagnosticoBradesco.exe (PID: 7884)
- DiagnosticoBradesco.exe (PID: 7984)
- DiagnosticoBradesco.exe (PID: 8008)
- get_version.exe (PID: 8144)
- get_version.exe (PID: 4044)
- core.exe (PID: 1652)
- core.exe (PID: 7104)
- core.exe (PID: 7812)
- drvinst.exe (PID: 7984)
- wsffcmgr64.exe (PID: 4012)
- wsffcmgr64.exe (PID: 5576)
- wsffcmgr64.exe (PID: 3476)
- ffcu.dat (PID: 7300)
Checks proxy server information
- DiagnosticoBradesco.exe (PID: 7884)
- core.exe (PID: 7812)
- slui.exe (PID: 6620)
Process checks computer location settings
- DiagnosticoBradesco.exe (PID: 7884)
Process checks whether UAC notifications are on
- DiagnosticoBradesco.exe (PID: 7884)
- core.exe (PID: 7104)
Reads the software policy settings
- DiagnosticoBradesco.exe (PID: 7884)
- core.exe (PID: 7104)
- core.exe (PID: 7812)
- drvinst.exe (PID: 7984)
- wsffcmgr64.exe (PID: 4012)
- wsffcmgr64.exe (PID: 5576)
- wsffcmgr64.exe (PID: 3476)
- slui.exe (PID: 6620)
- WerFault.exe (PID: 6392)
- ffcu.dat (PID: 7300)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 7328)
- WMIC.exe (PID: 7412)
- WMIC.exe (PID: 3644)
The sample compiled with english language support
- warsaw_setup_64.tmp (PID: 8124)
- core.exe (PID: 7104)
Detects InnoSetup installer (YARA)
- warsaw_setup_64.tmp (PID: 8124)
- warsaw_setup_64.exe (PID: 8104)
The sample compiled with portuguese language support
- warsaw_setup_64.tmp (PID: 8124)
- core.exe (PID: 7104)
- DiagnosticoBradesco.exe (PID: 8008)
Compiled with Borland Delphi (YARA)
- warsaw_setup_64.exe (PID: 8104)
- warsaw_setup_64.tmp (PID: 8124)
Reads Windows Product ID
- core.exe (PID: 7104)
- ctfmon.exe (PID: 4468)
- chrome.exe (PID: 5952)
Creates files or folders in the user directory
- wsffcmgr64.exe (PID: 4012)
- wsffcmgr64.exe (PID: 5576)
- wsffcmgr64.exe (PID: 3476)
- core.exe (PID: 7812)
- ffcu.dat (PID: 7300)
Reads Environment values
- identity_helper.exe (PID: 3840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
255
Monitored processes
102
Malicious processes
11
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
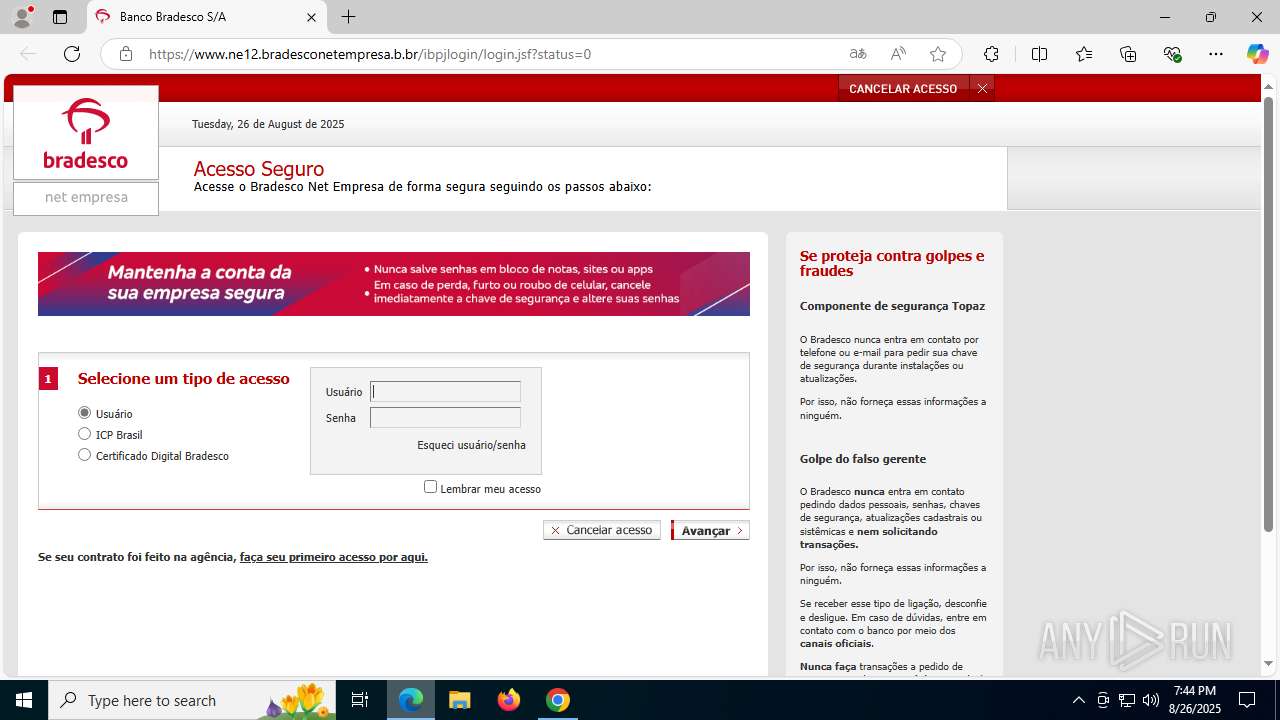
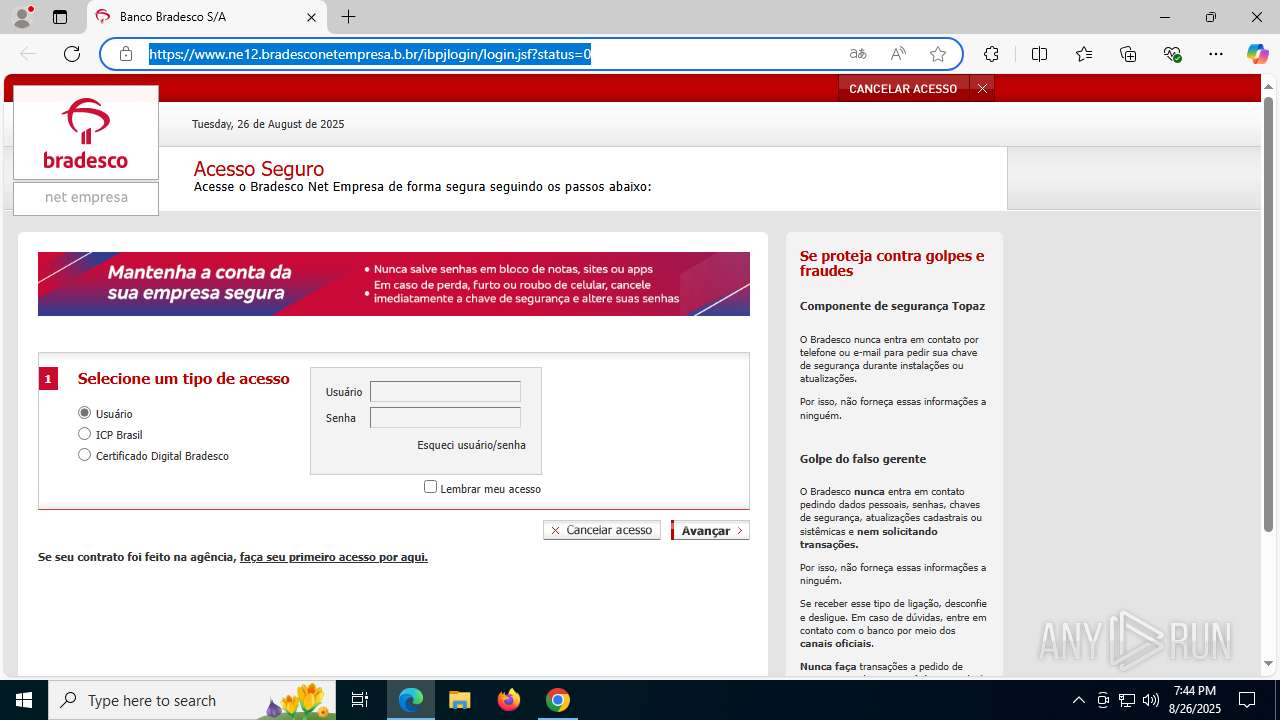
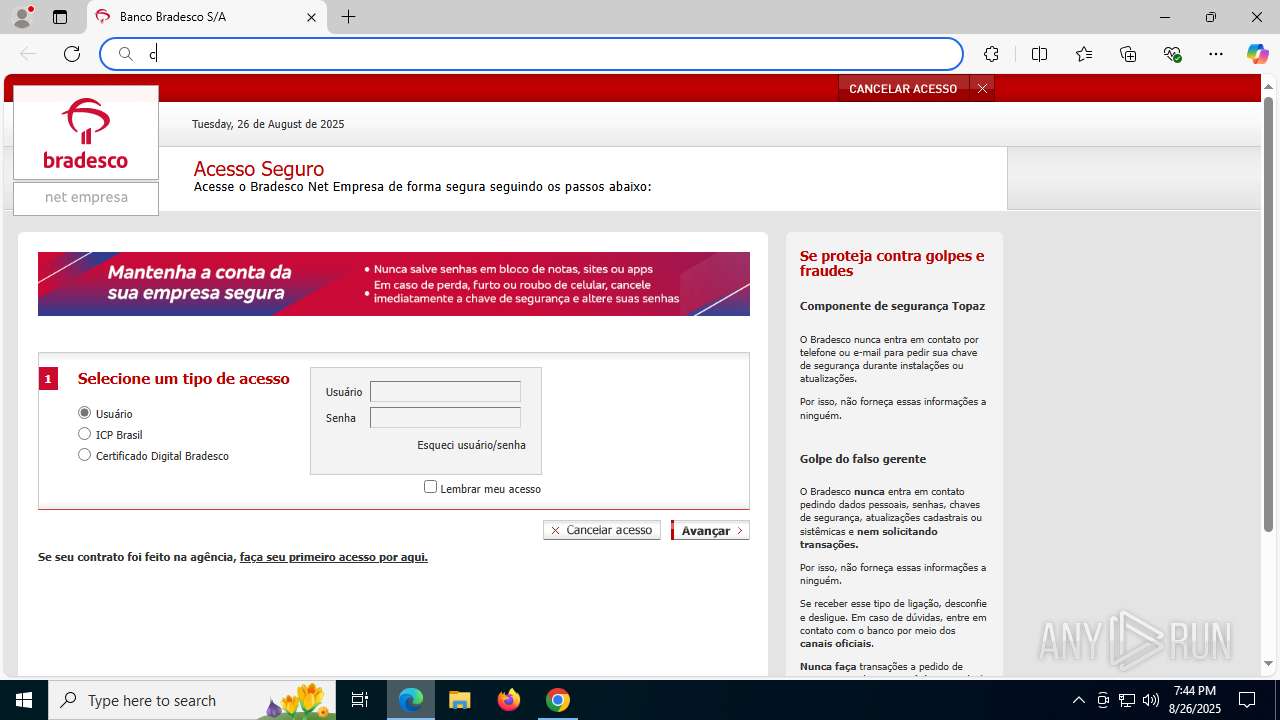
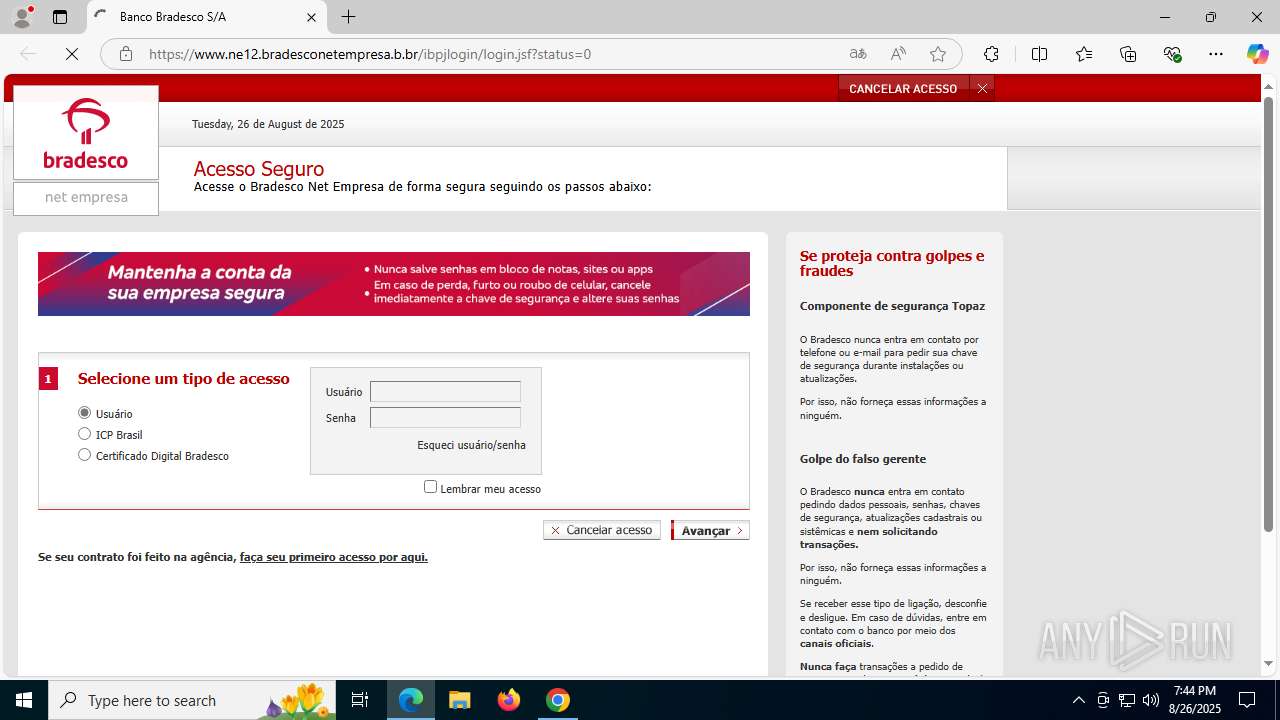
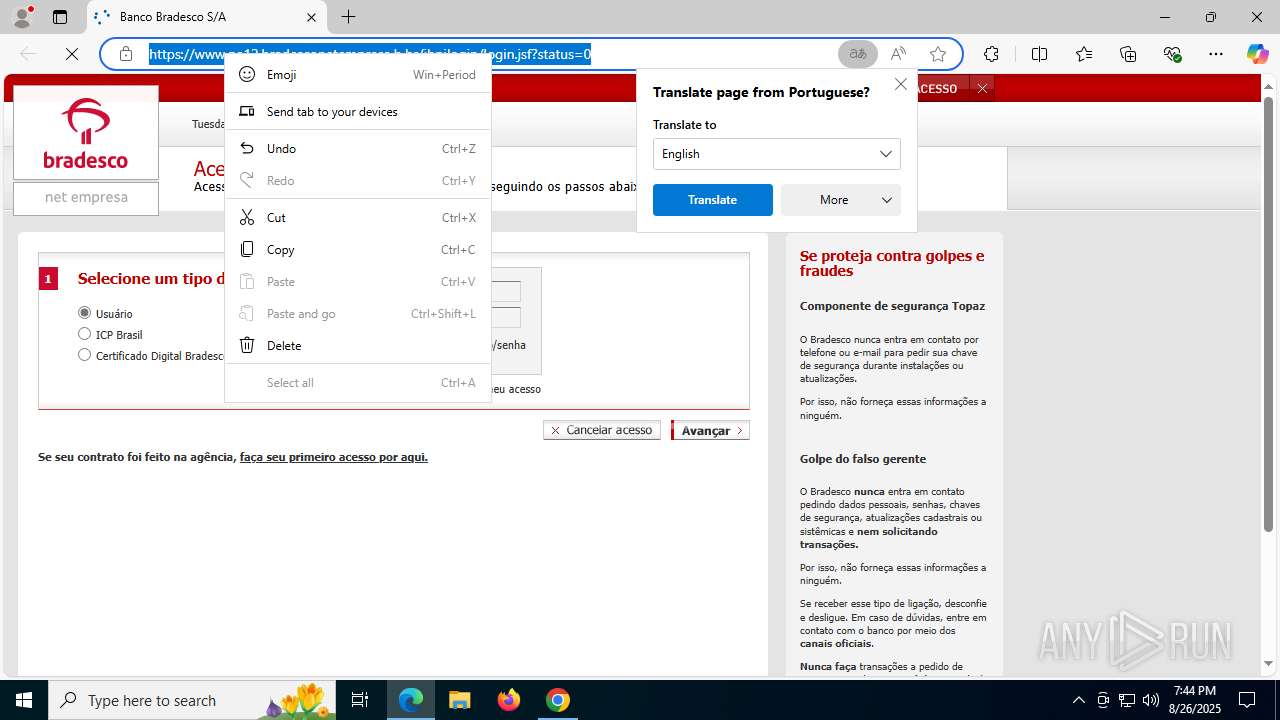
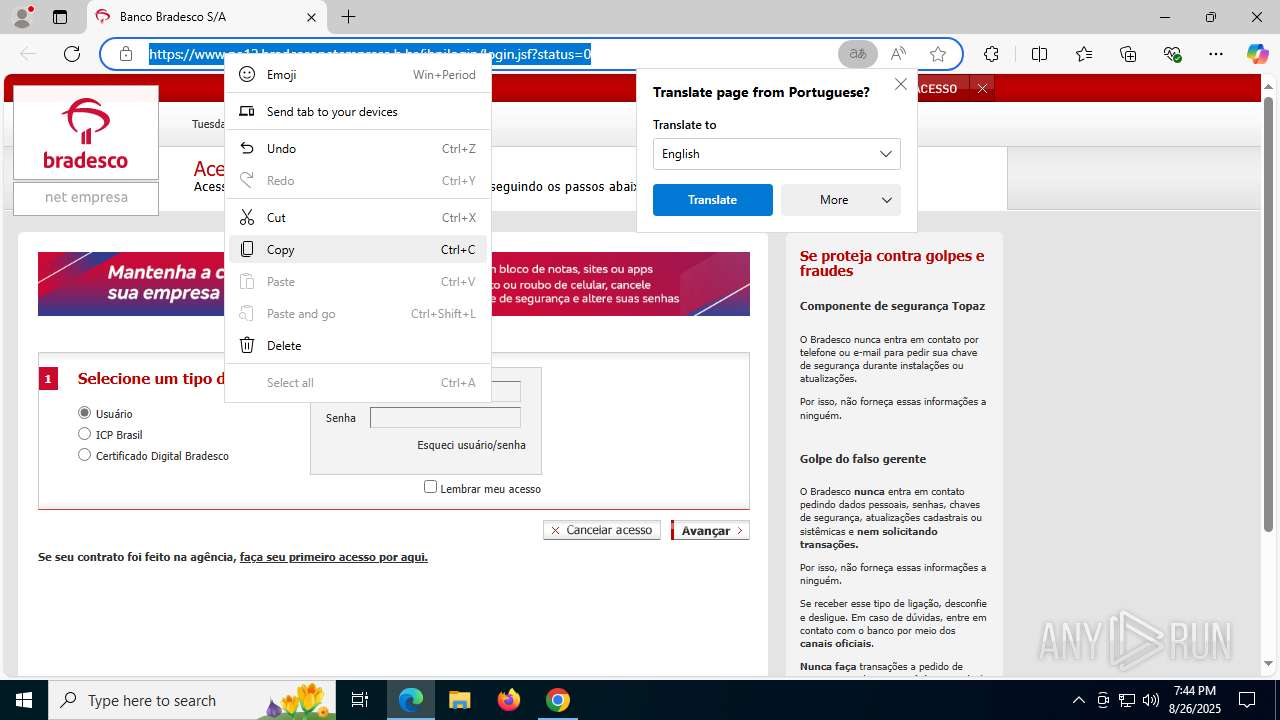
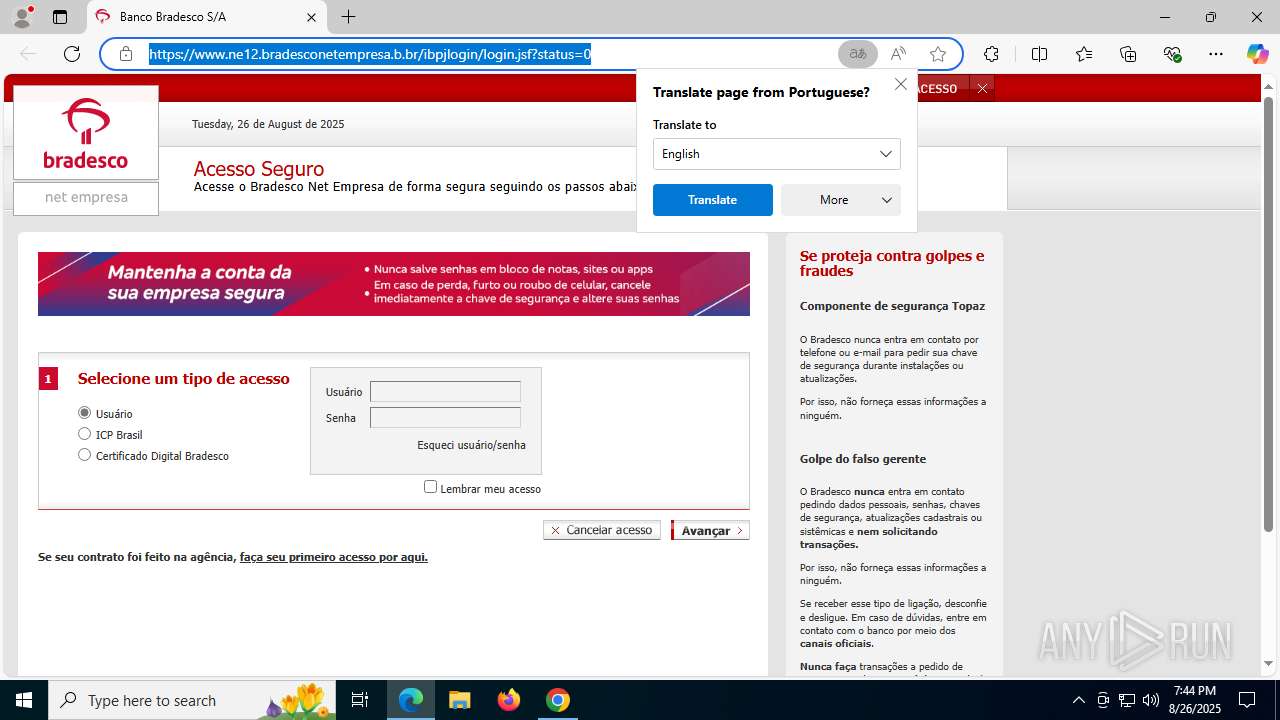
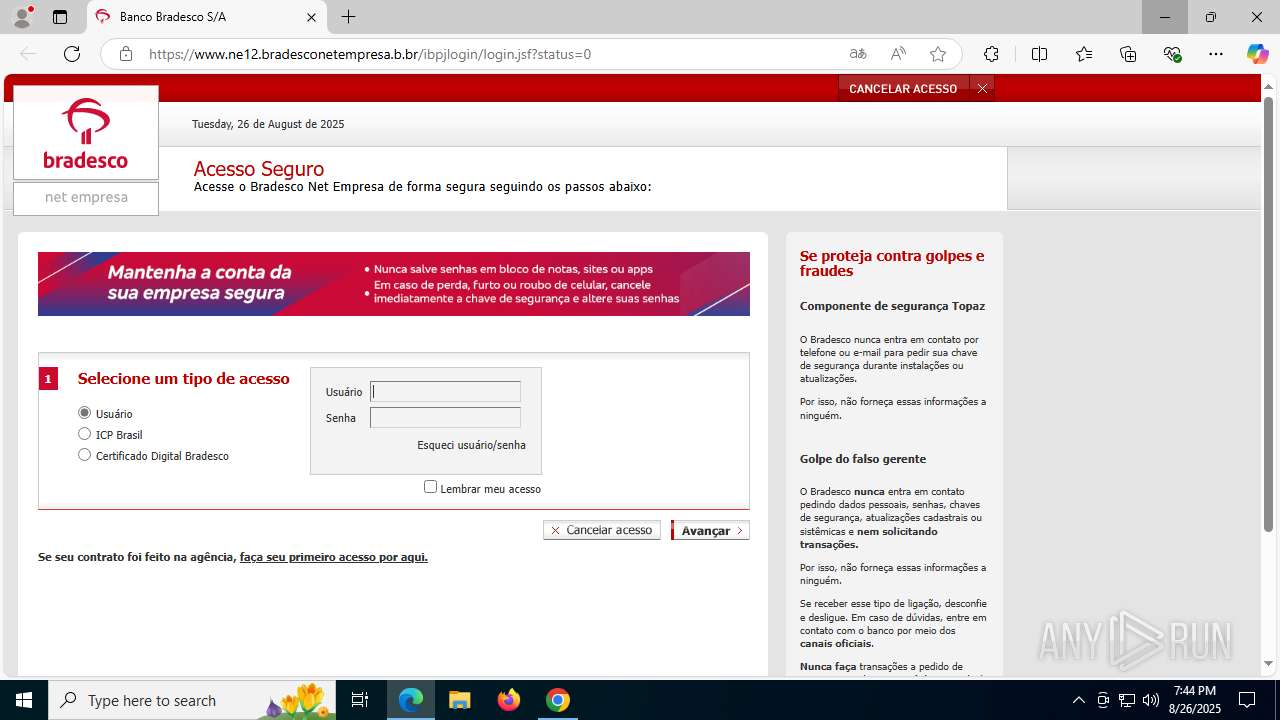
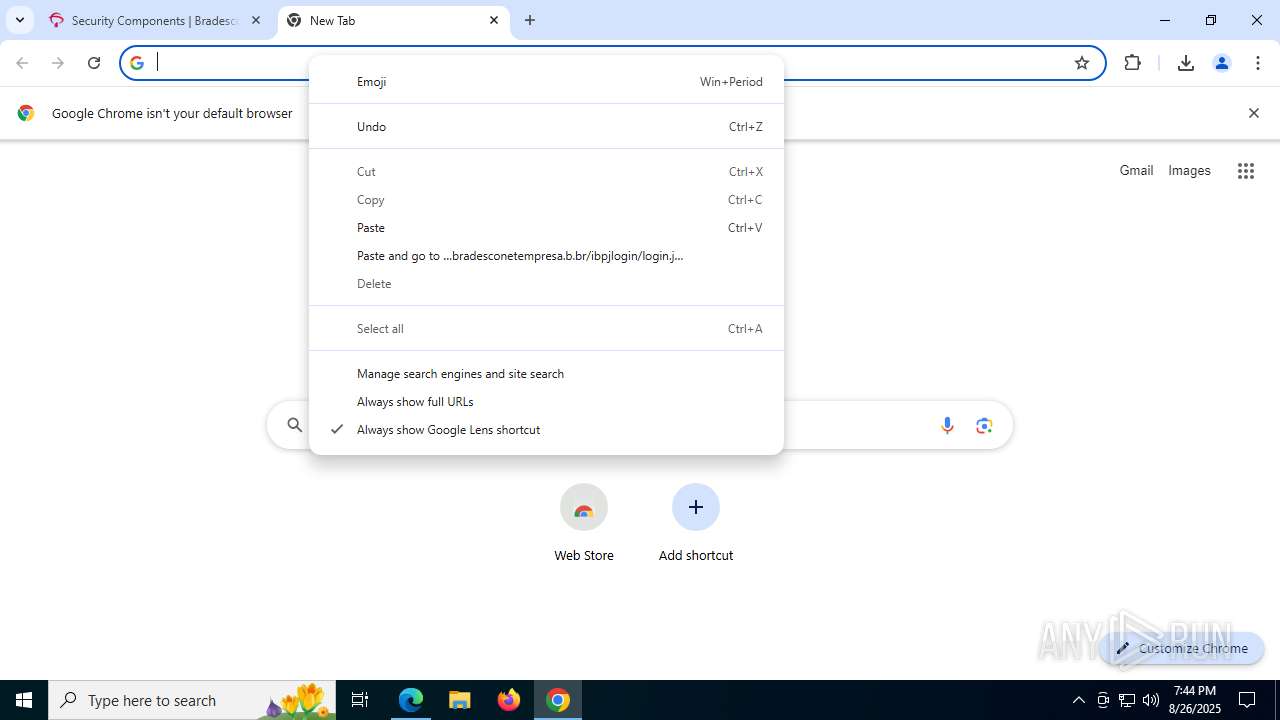
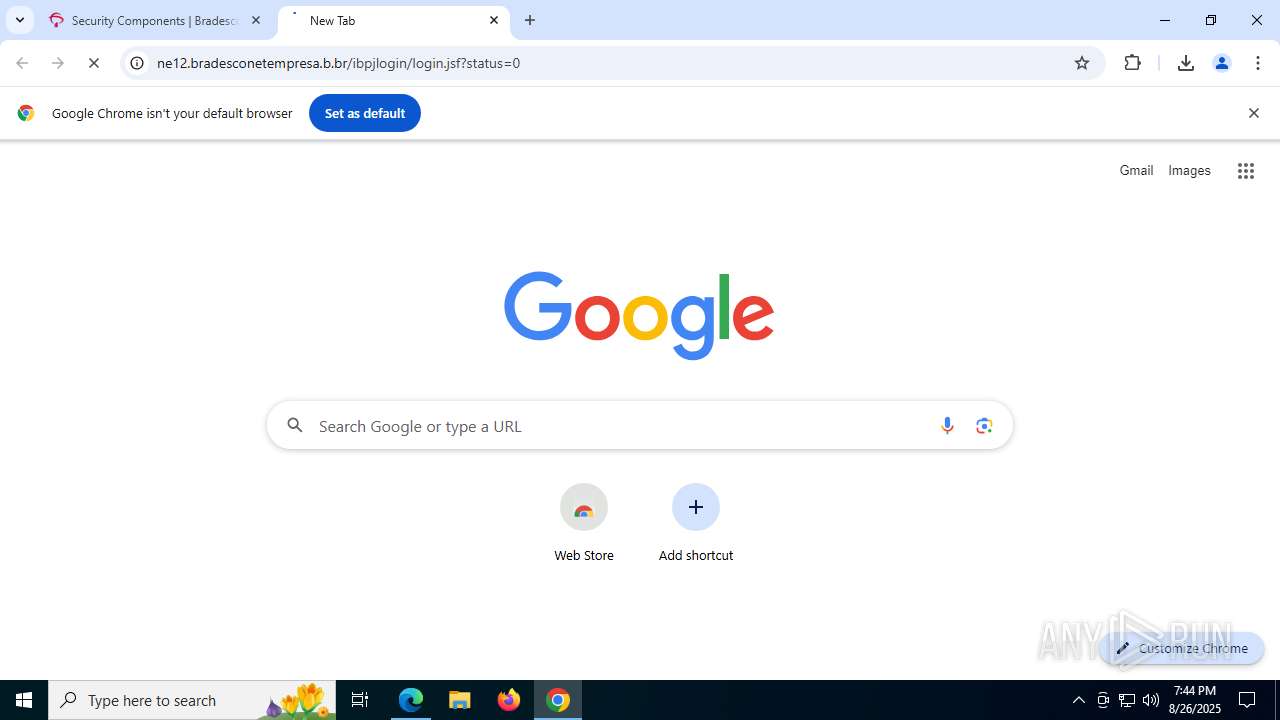
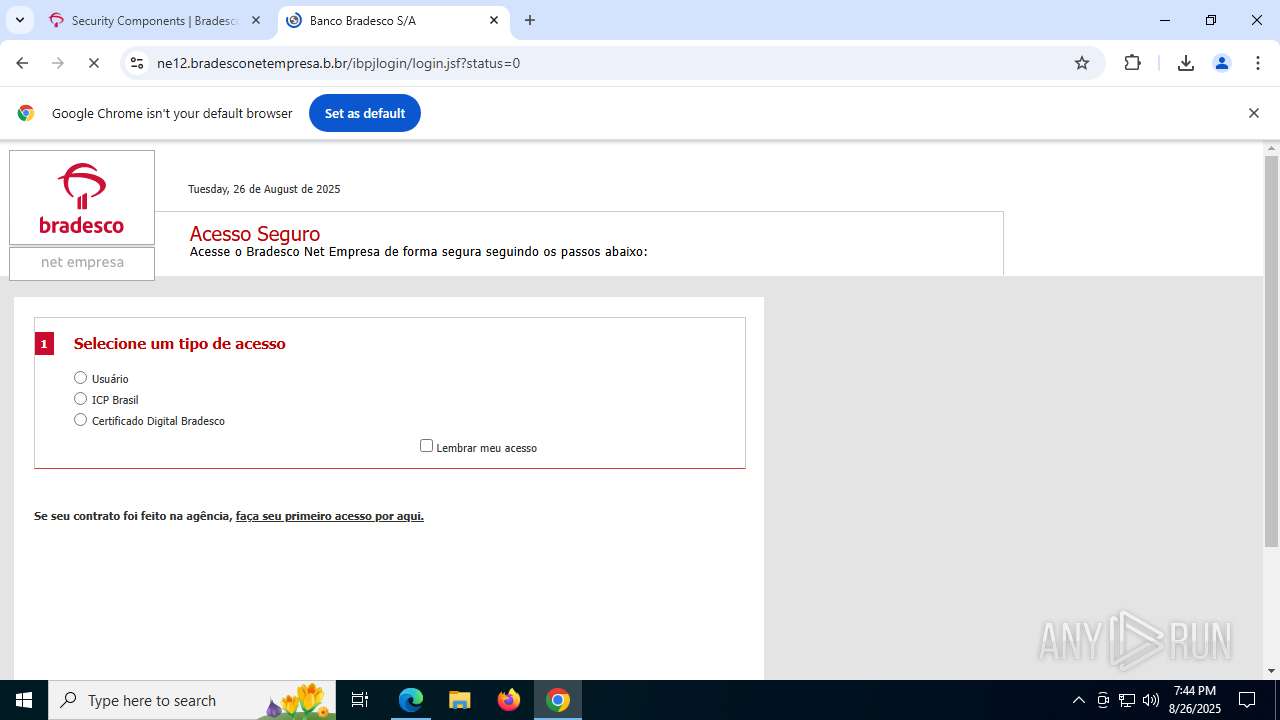
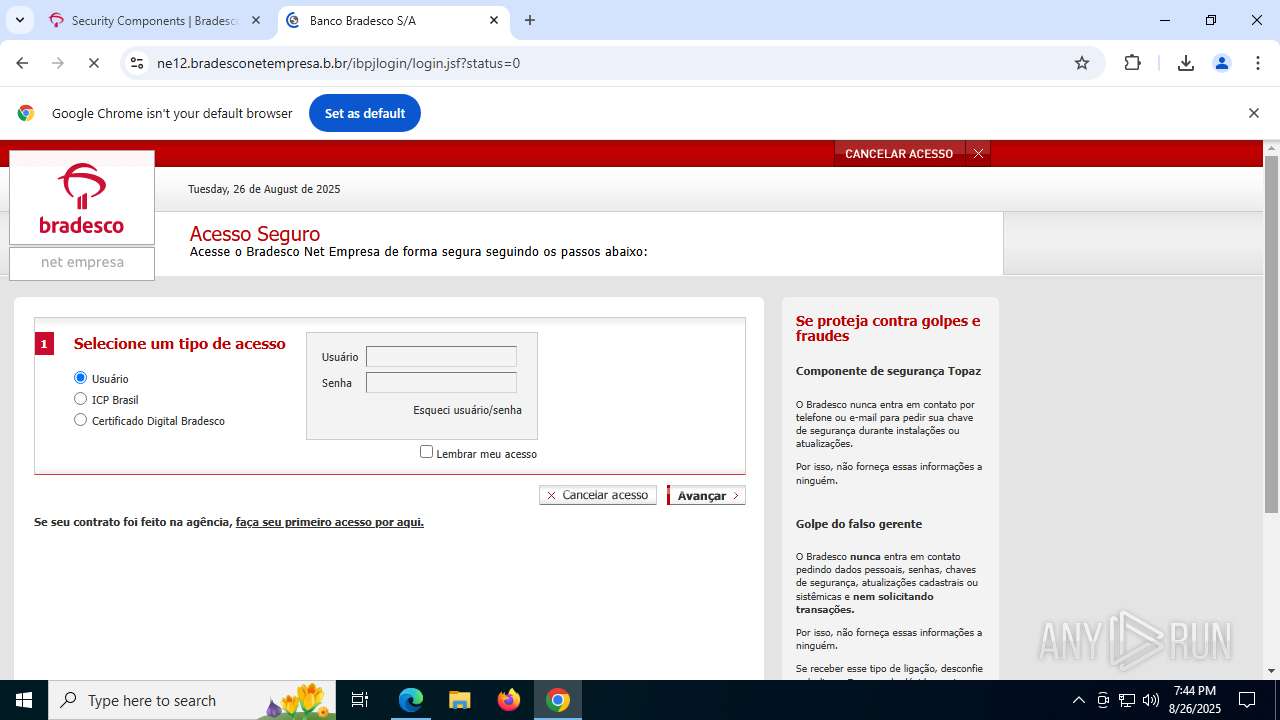
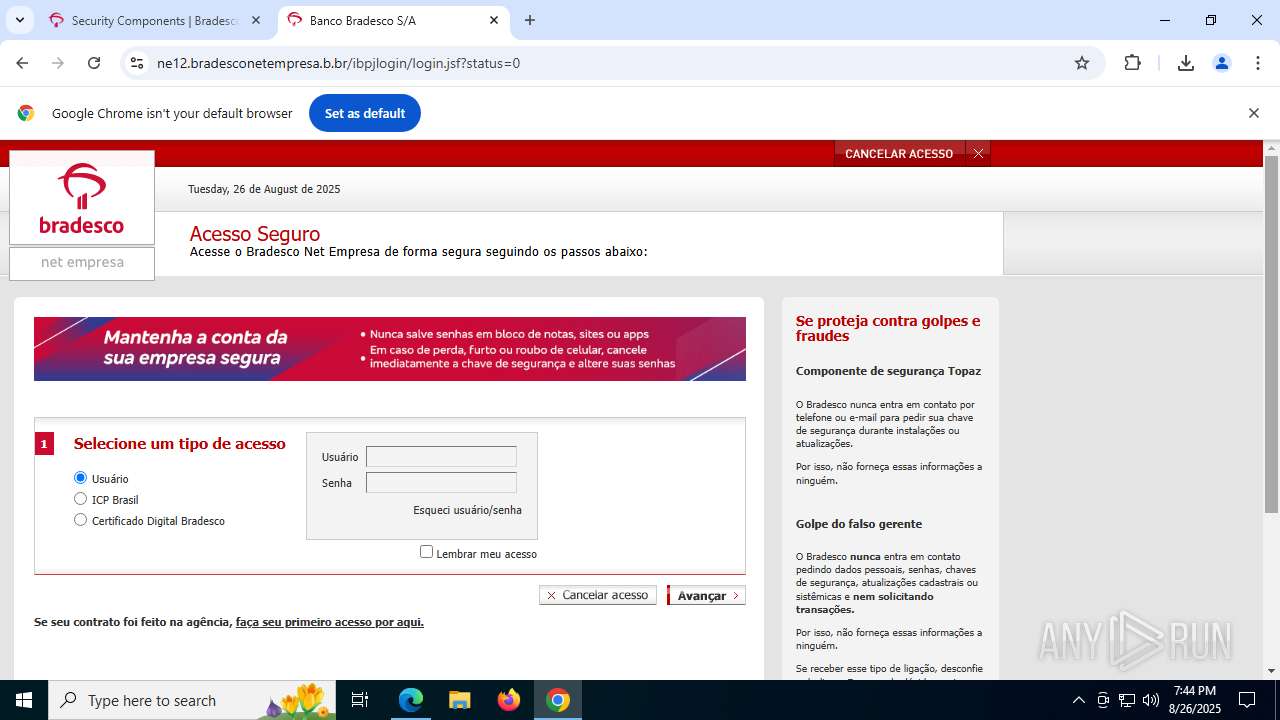
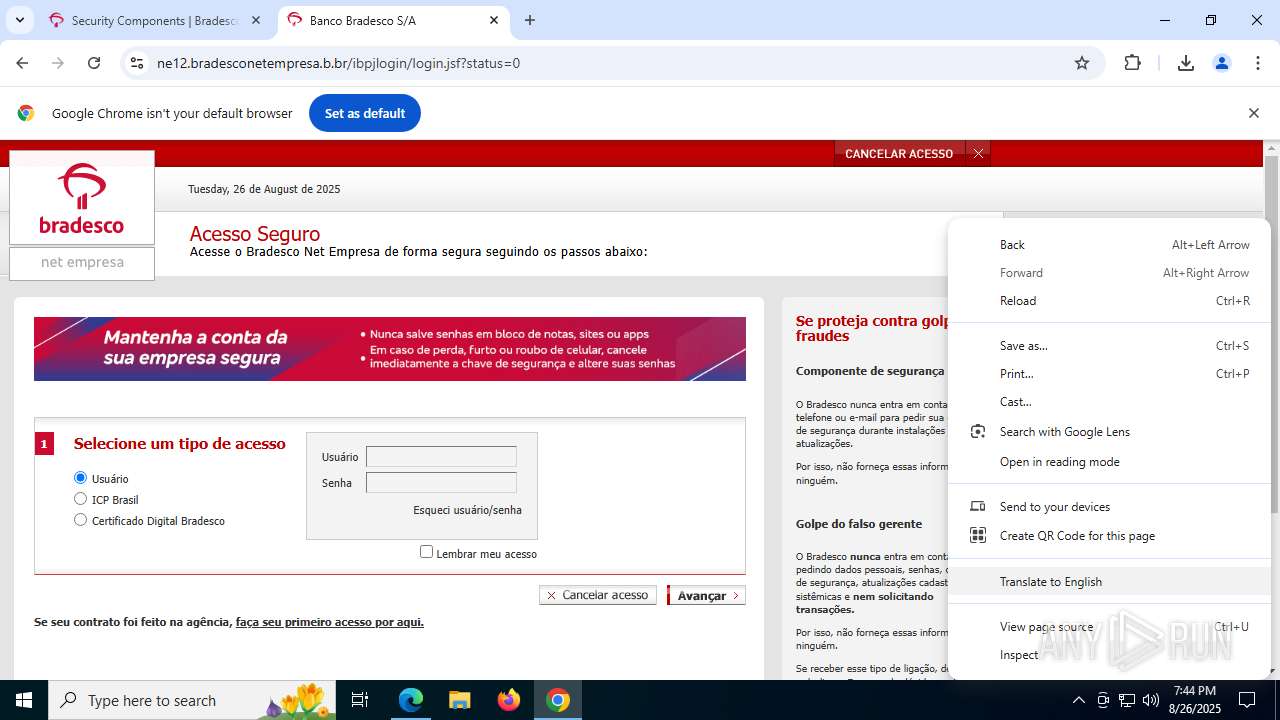
| 236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://www.ne12.bradesconetempresa.b.br/ibpjlogin/login.jsf?status=0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | DiagnosticoBradesco.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=2268,i,2757692285445536167,12362239646385734406,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2284 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1612 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=16 --field-trial-handle=5496,i,2757692285445536167,12362239646385734406,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=6752 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1652 | "C:\Program Files\Topaz OFD\Warsaw\core.exe" --install-service | C:\Program Files\Topaz OFD\Warsaw\core.exe | — | warsaw_setup_64.tmp | |||||||||||
User: SYSTEM Company: Topaz OFD Integrity Level: SYSTEM Description: Topaz OFD - Protection Module Exit code: 0 Version: 2.12.0.265 Modules
| |||||||||||||||
| 1828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=2052,i,2757692285445536167,12362239646385734406,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2148 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2192 | find /C "core.exe" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5240,i,2757692285445536167,12362239646385734406,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=5256 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2356 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4248,i,8214667939061964678,10064060370461353908,262144 --variations-seed-version --mojo-platform-channel-handle=4268 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2484 | C:\WINDOWS\system32\DllHost.exe /Processid:{973D20D7-562D-44B9-B70B-5A0F49CCDF3F} | C:\Windows\System32\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
94 351
Read events
94 064
Write events
237
Delete events
50
Modification events
| (PID) Process: | (5952) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5952) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5952) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5952) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4468) ctfmon.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Input\TypingInsights |
| Operation: | write | Name: | Insights |
Value: 02000000071DE8C131CC8360A3D6D9C1330A686B165ABA2E235F5A5C | |||
| (PID) Process: | (5952) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5952) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en-US |
Value: | |||
| (PID) Process: | (5952) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en |
Value: | |||
| (PID) Process: | (5952) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | _Global_ |
Value: | |||
| (PID) Process: | (7884) DiagnosticoBradesco.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | AutoHelpDesk |
Value: | |||
Executable files
857
Suspicious files
614
Text files
107
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF18d973.TMP | — | |
MD5:— | SHA256:— | |||
| 5952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF18d973.TMP | — | |
MD5:— | SHA256:— | |||
| 5952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF18d982.TMP | — | |
MD5:— | SHA256:— | |||
| 5952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF18d982.TMP | — | |
MD5:— | SHA256:— | |||
| 5952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF18d9a2.TMP | — | |
MD5:— | SHA256:— | |||
| 5952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF18d9a2.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
341
DNS requests
320
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1828 | chrome.exe | GET | 200 | 142.250.186.174:80 | http://clients2.google.com/time/1/current?cup2key=8:LhrWMIT4zp33QS-A7-fBb9fbvW6bTCH1edVnG56Stek&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
4880 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.164.43:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5952 | chrome.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5952 | chrome.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEA0Ruro8uz8DirQGINxgFlQ%3D | unknown | — | — | whitelisted |
7784 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5952 | chrome.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
7784 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1472 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5348 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1828 | chrome.exe | 142.250.186.174:80 | clients2.google.com | GOOGLE | US | whitelisted |
1828 | chrome.exe | 216.58.206.74:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
1828 | chrome.exe | 23.50.131.136:443 | banco.bradesco | Akamai International B.V. | DE | whitelisted |
1828 | chrome.exe | 66.102.1.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
1828 | chrome.exe | 69.192.160.133:443 | s.go-mpulse.net | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
banco.bradesco |
| whitelisted |
accounts.google.com |
| whitelisted |
s.go-mpulse.net |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
c.go-mpulse.net |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1828 | chrome.exe | Misc activity | INFO [ANY.RUN] Possible short link service (t .co) |
1828 | chrome.exe | Misc activity | INFO [ANY.RUN] Possible short link service (t .co) |
1828 | chrome.exe | Misc activity | INFO [ANY.RUN] Possible short link service (t .co) |
1828 | chrome.exe | Misc activity | INFO [ANY.RUN] Possible short link service (t .co) |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Potentially Bad Traffic | ET INFO Executable served from Amazon S3 |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |