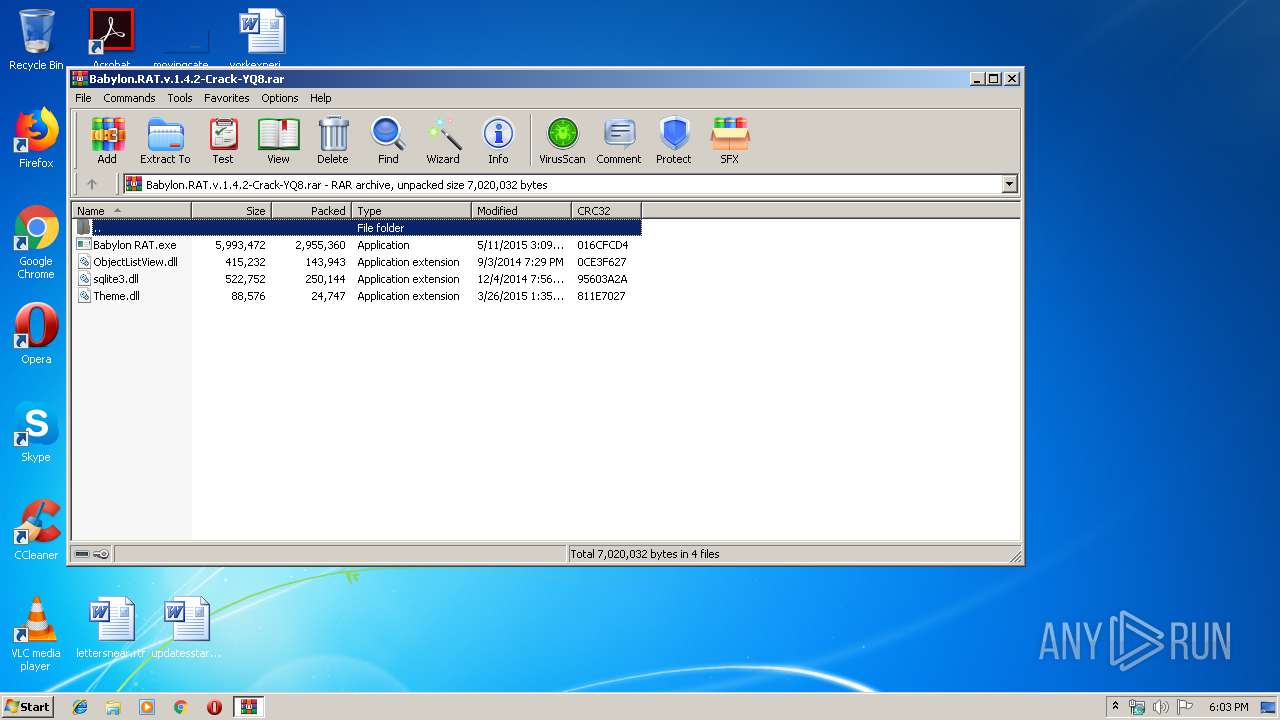
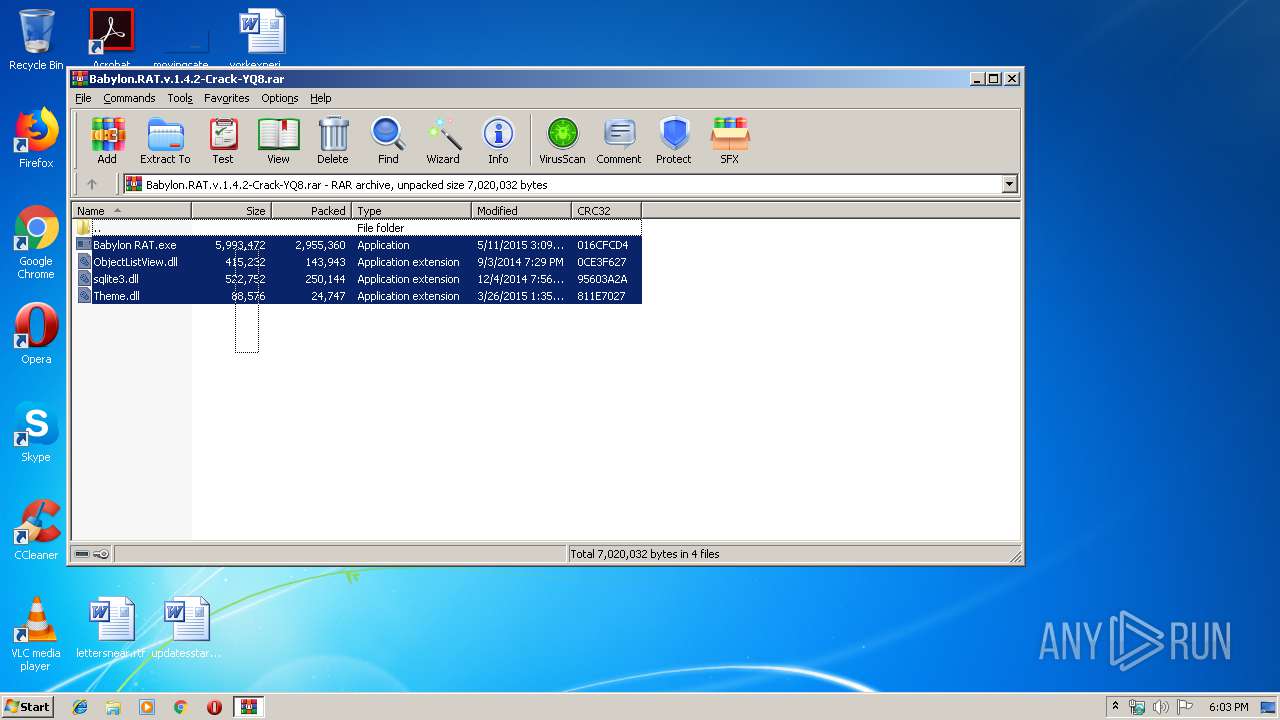
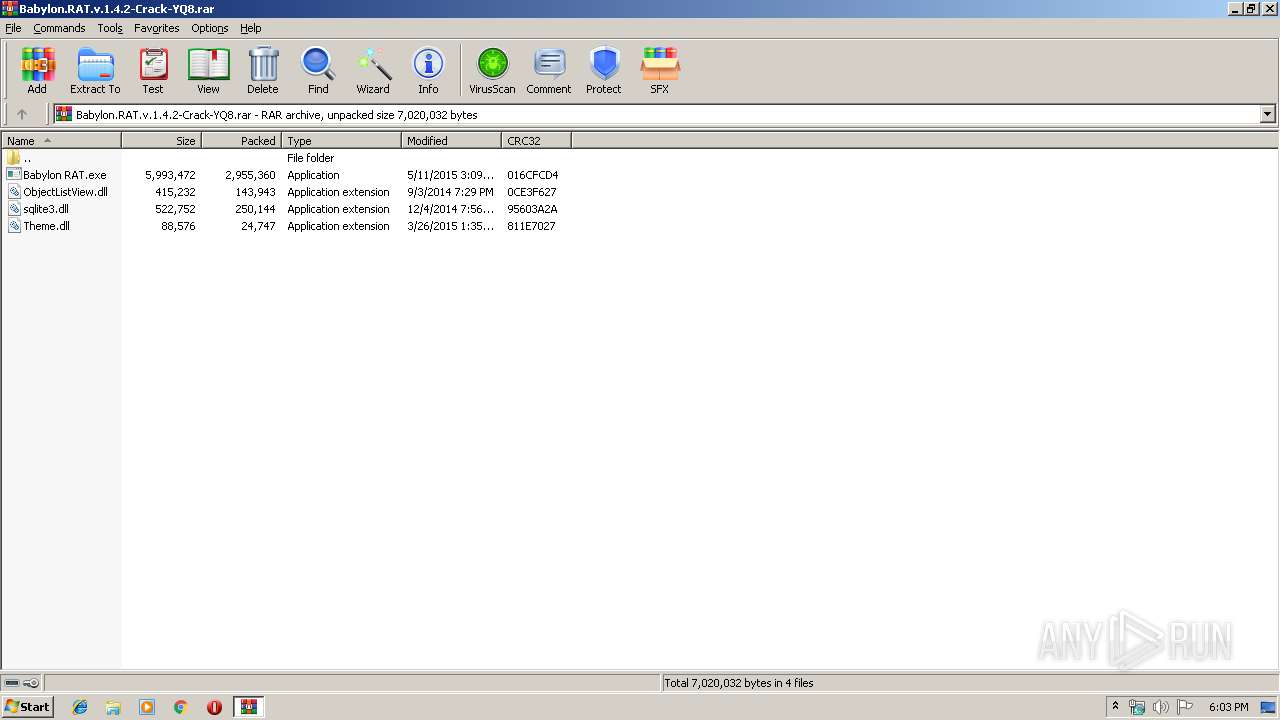
| File name: | Babylon.RAT.v.1.4.2-Crack-YQ8.rar |
| Full analysis: | https://app.any.run/tasks/16248e51-4901-41cb-98da-8635dd9e6140 |
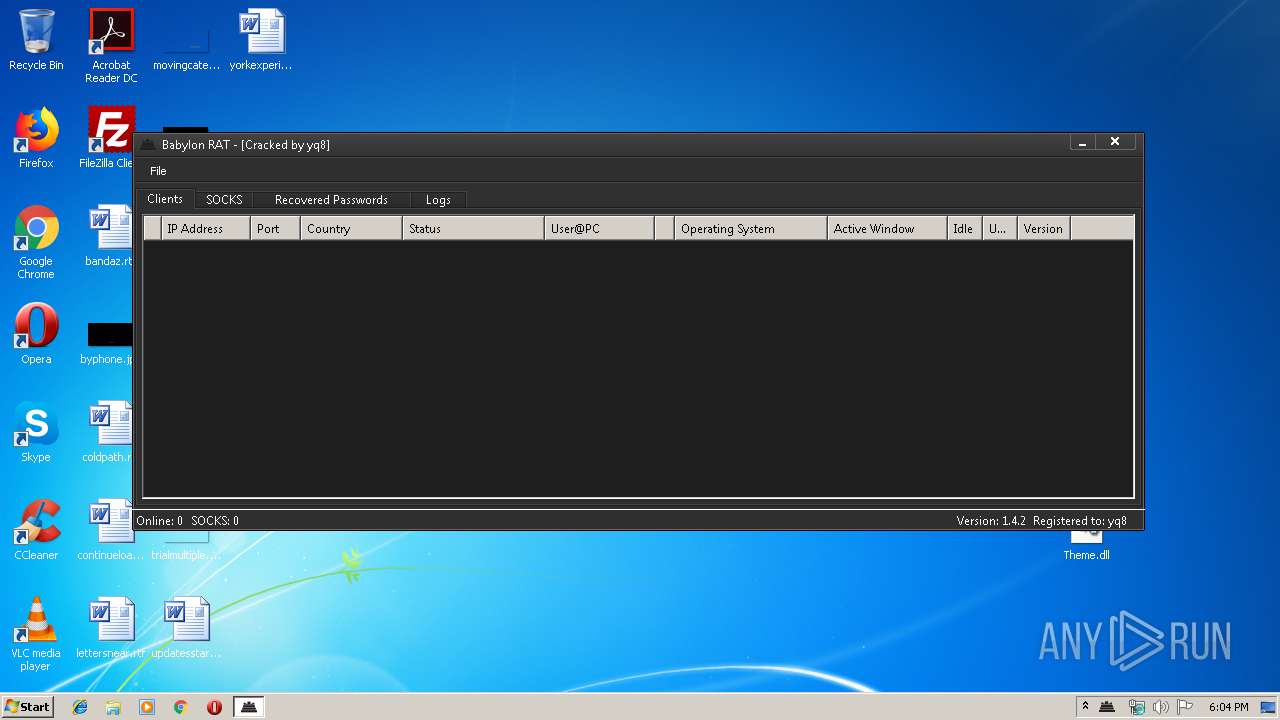
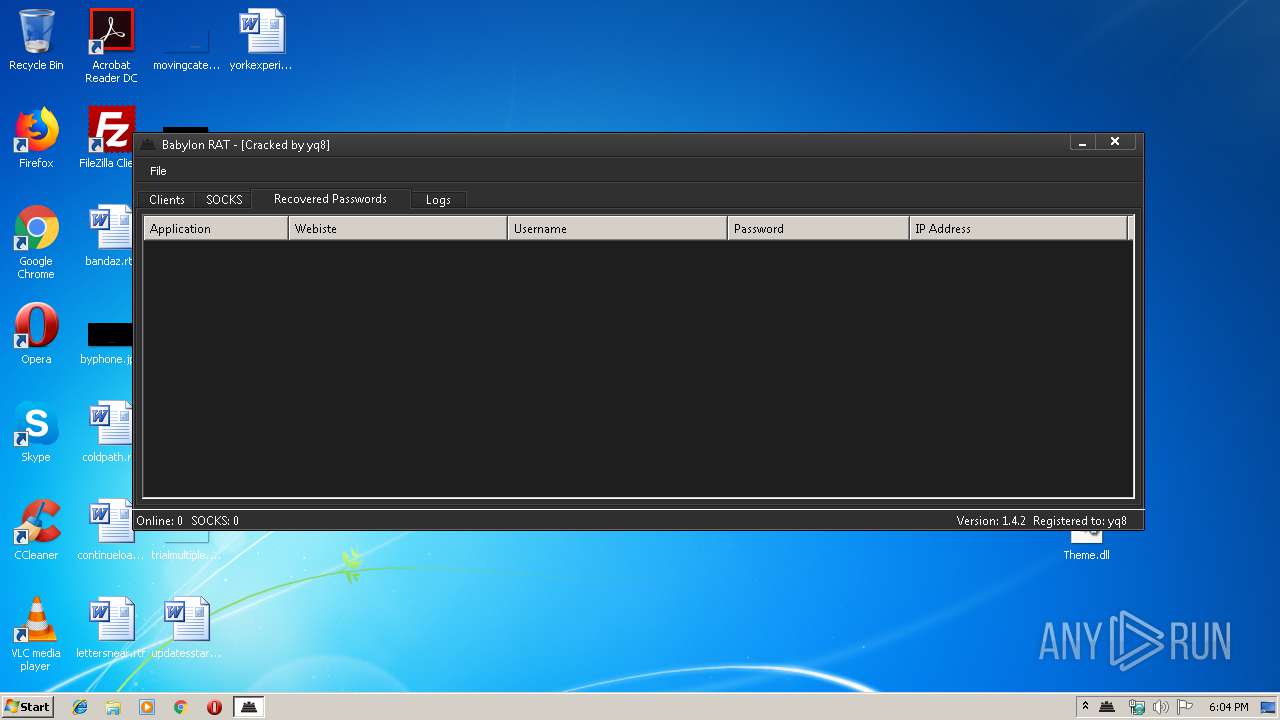
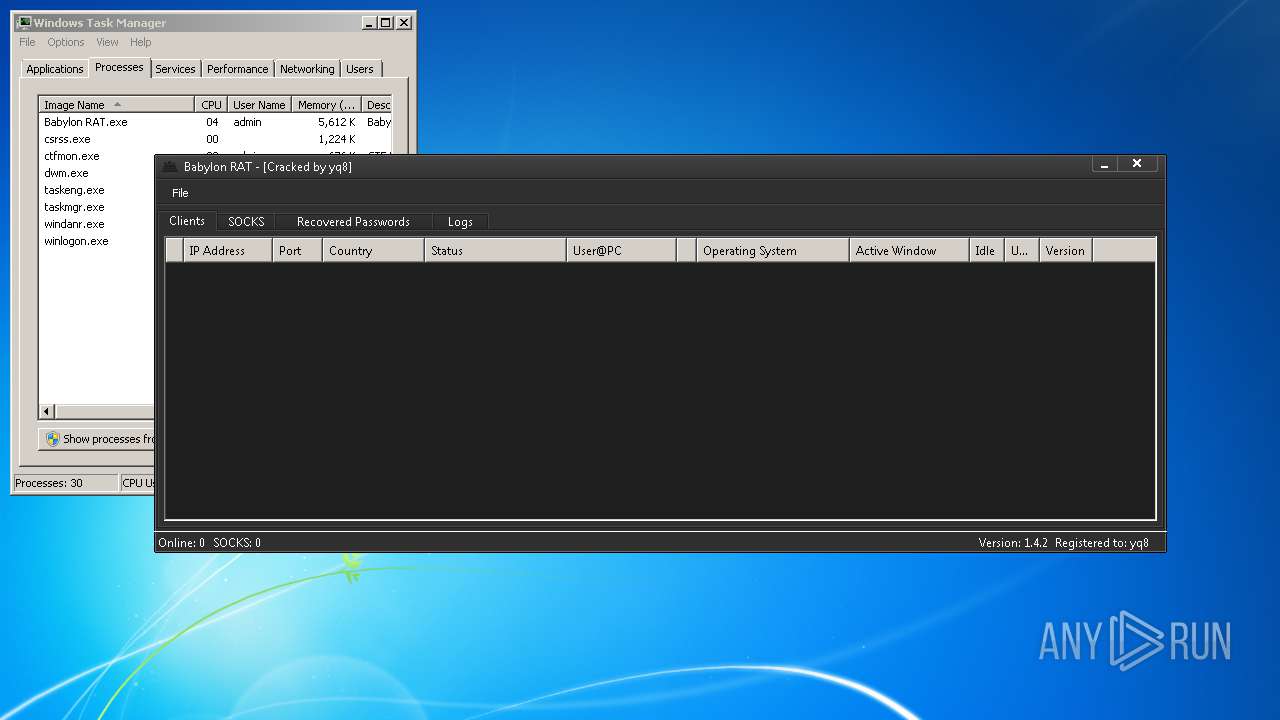
| Verdict: | Malicious activity |
| Analysis date: | September 07, 2019, 17:03:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | A1B6FB67D16A6F5559BF5D9CB50AC719 |
| SHA1: | 79E3066F27E36398257A630C10B83C0F13090DE7 |
| SHA256: | 509FFCFB35F47435892B1E1989D5C25A5FF49820098B3568495ED739D8696FAB |
| SSDEEP: | 49152:KmLK1s9XCQqG3mFTQBogjN7n2KacTPkzFkTQ8O6wGnZ4zmm+oUGWCE6xmqJ2t/UP:KcXCoeT6hKMTBc16wGnZBoUGXzSUR12E |
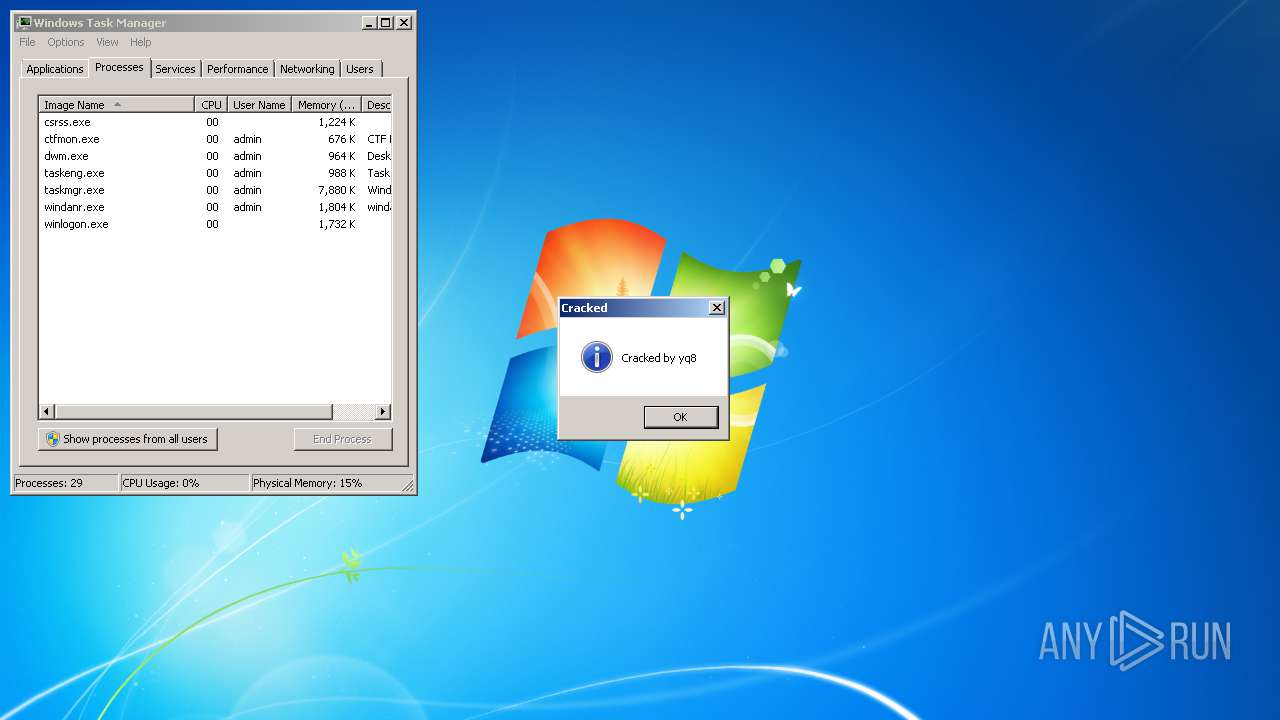
MALICIOUS
Loads dropped or rewritten executable
- Babylon RAT.exe (PID: 2416)
- SearchProtocolHost.exe (PID: 1000)
- Babylon RAT.exe (PID: 1016)
Application was dropped or rewritten from another process
- Babylon RAT.exe (PID: 2416)
- Babylon RAT.exe (PID: 1016)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3080)
INFO
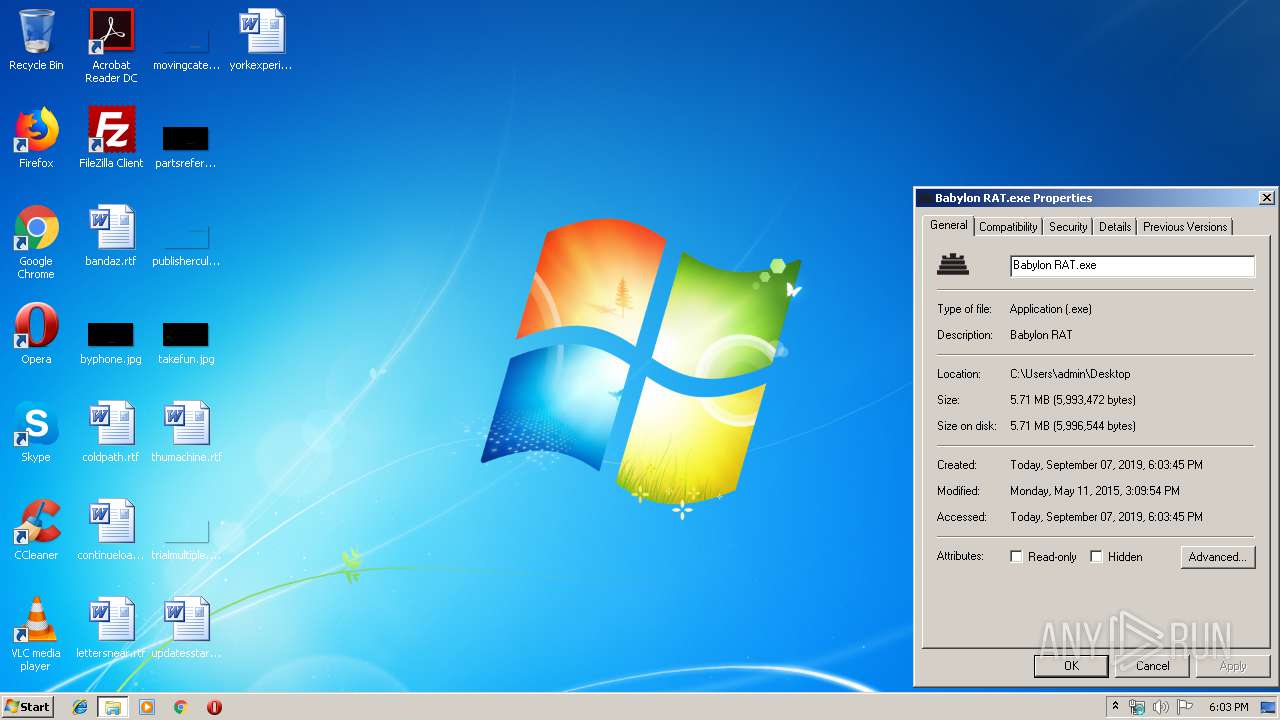
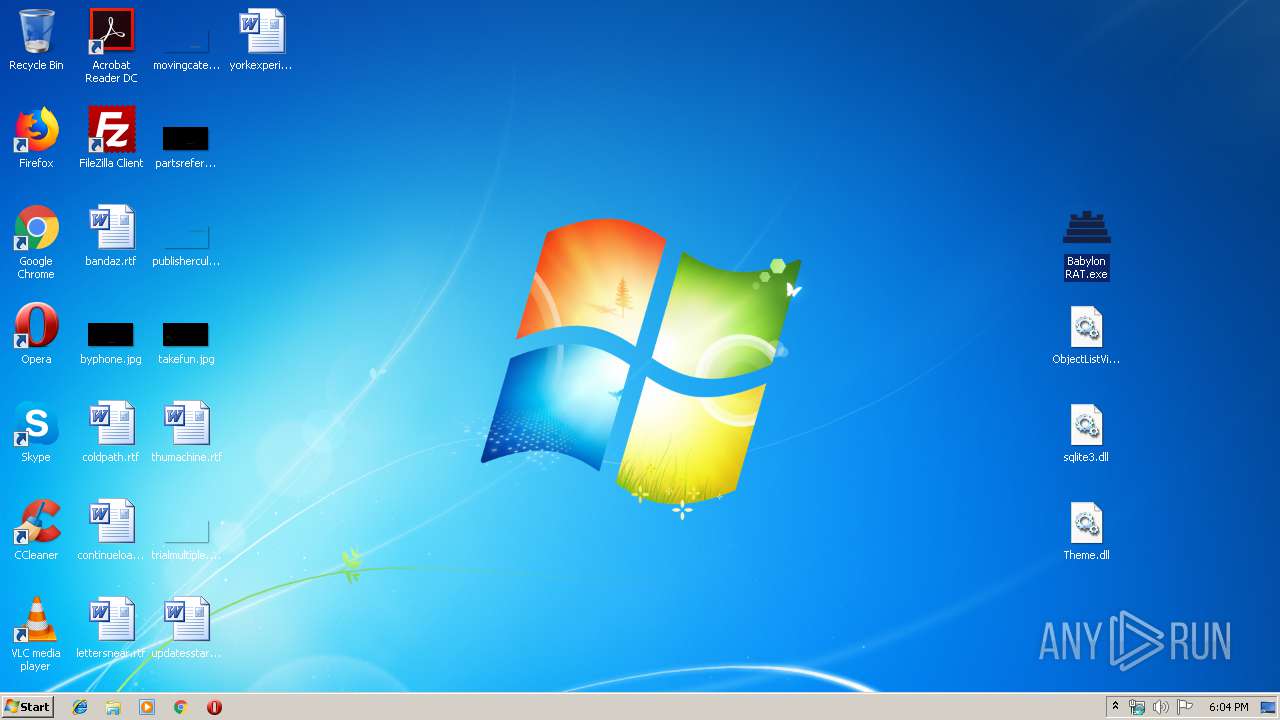
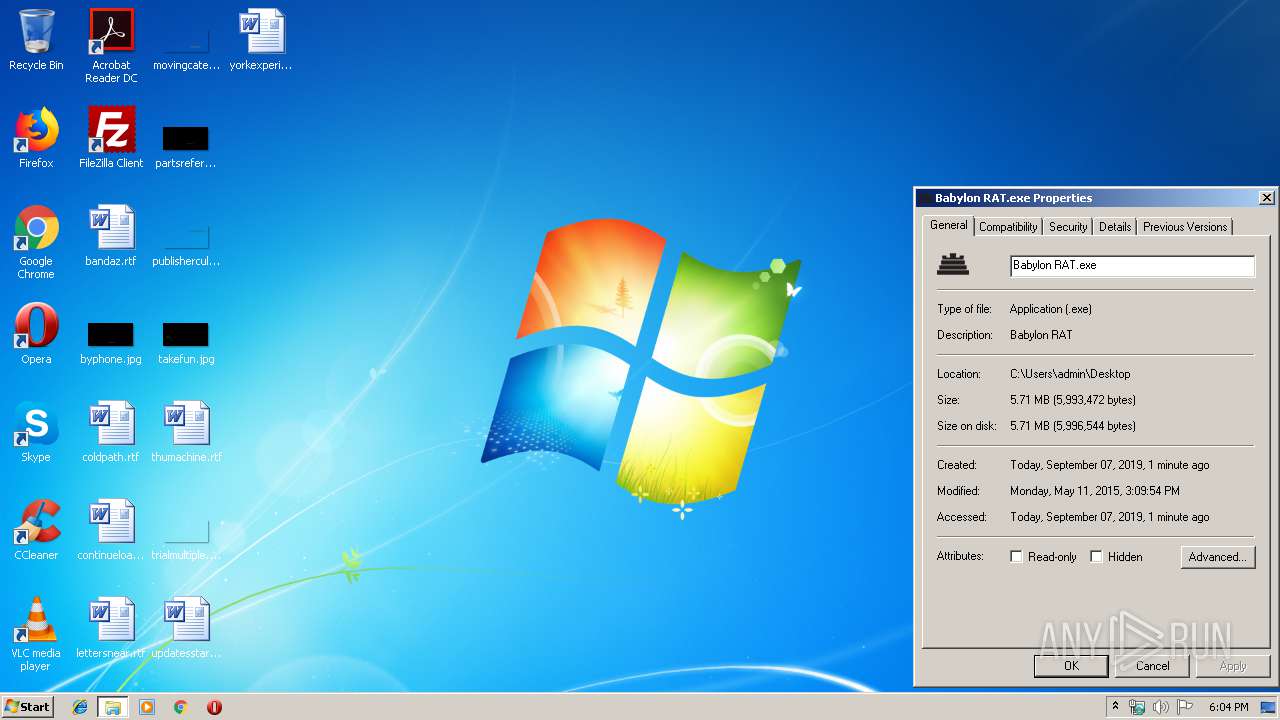
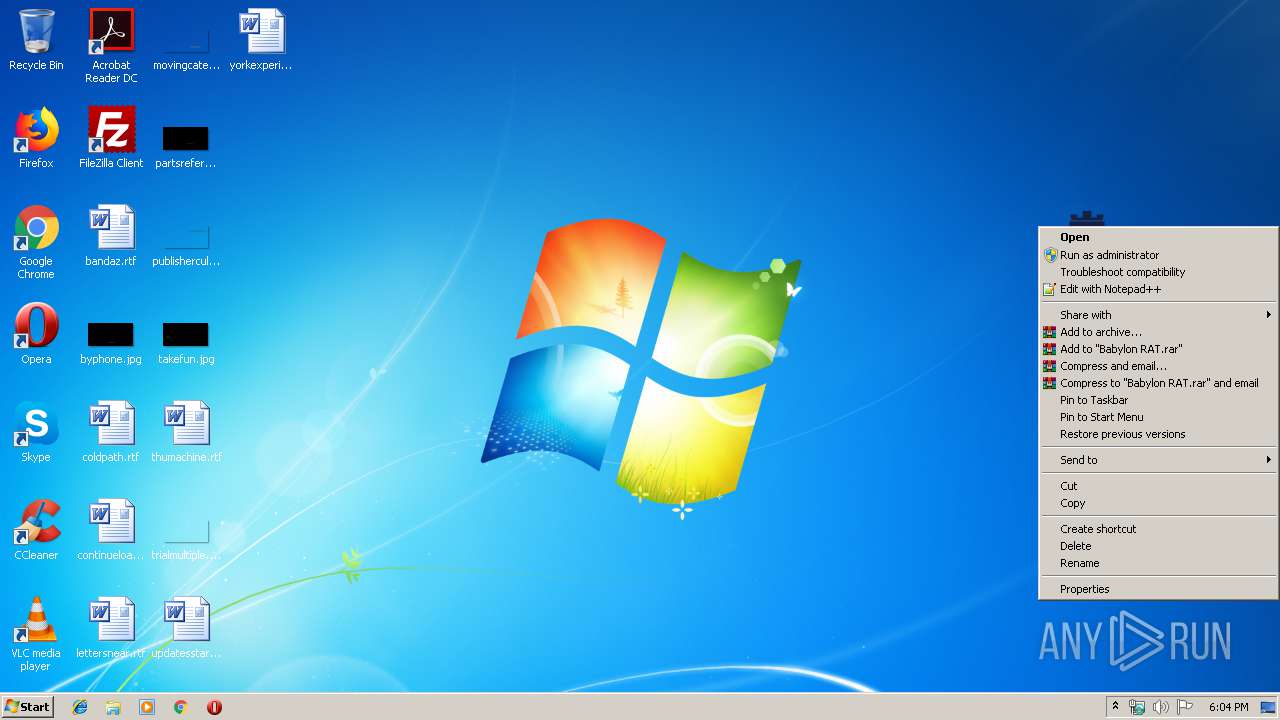
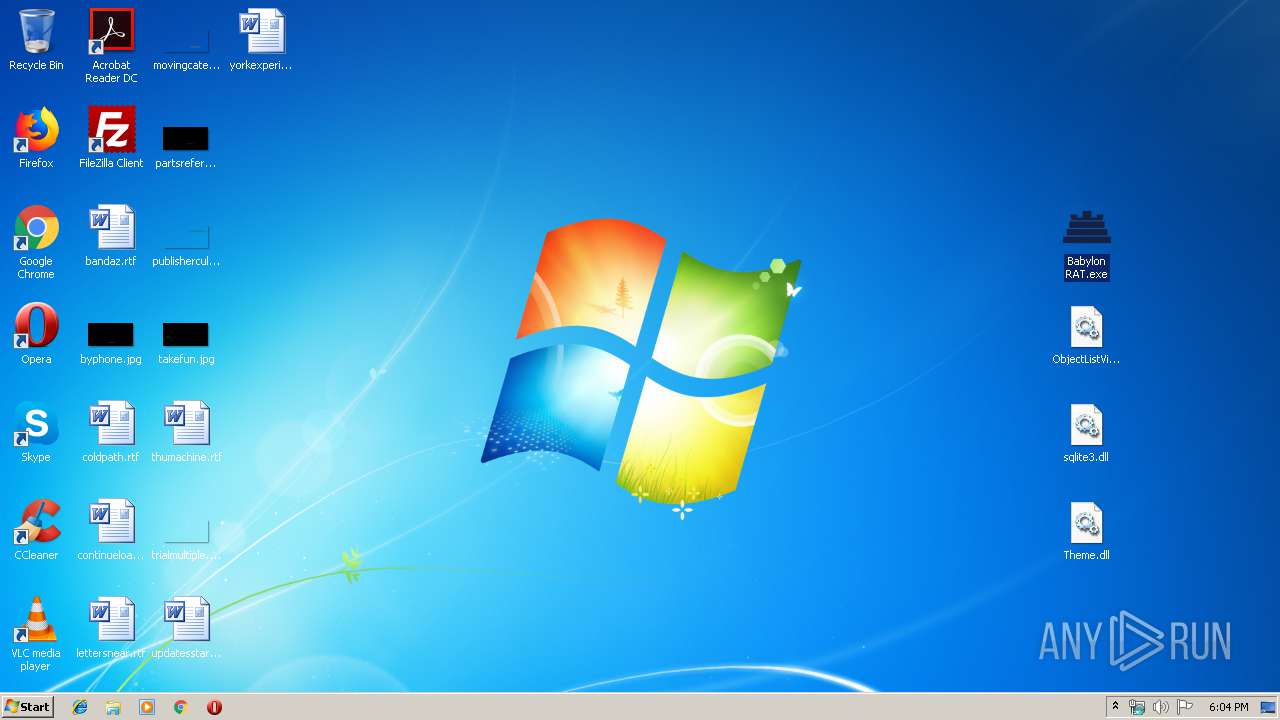
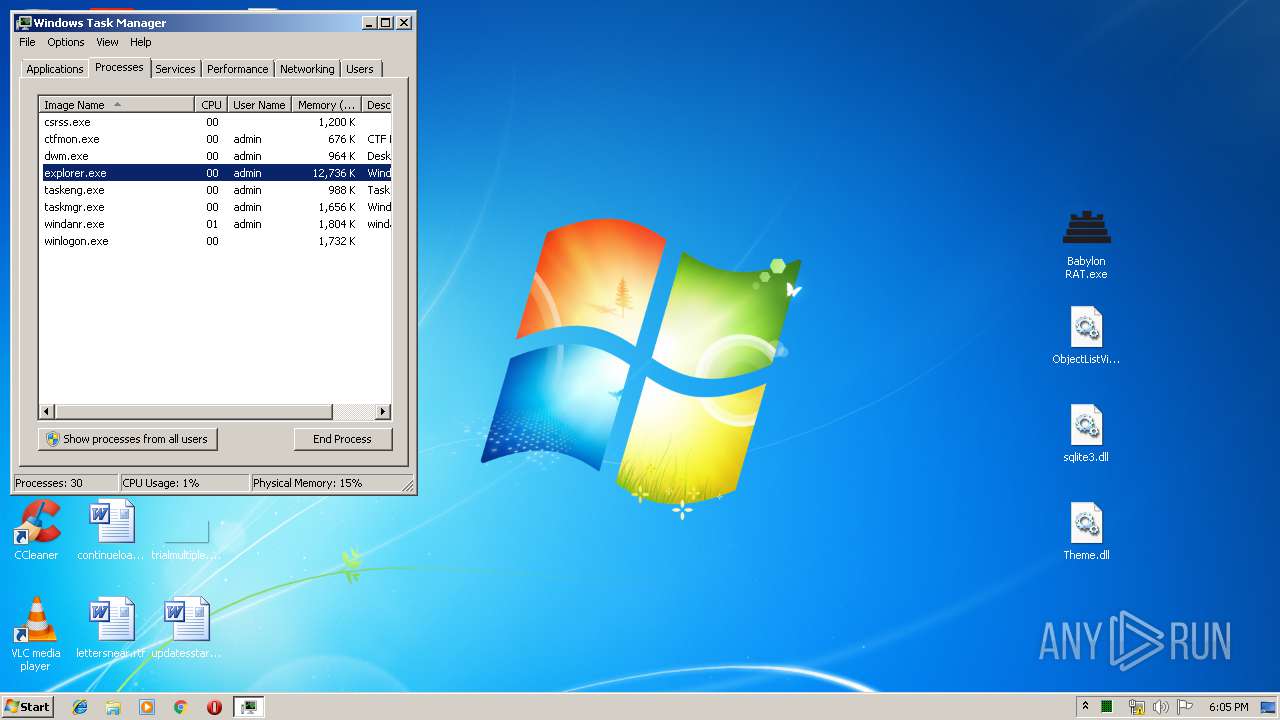
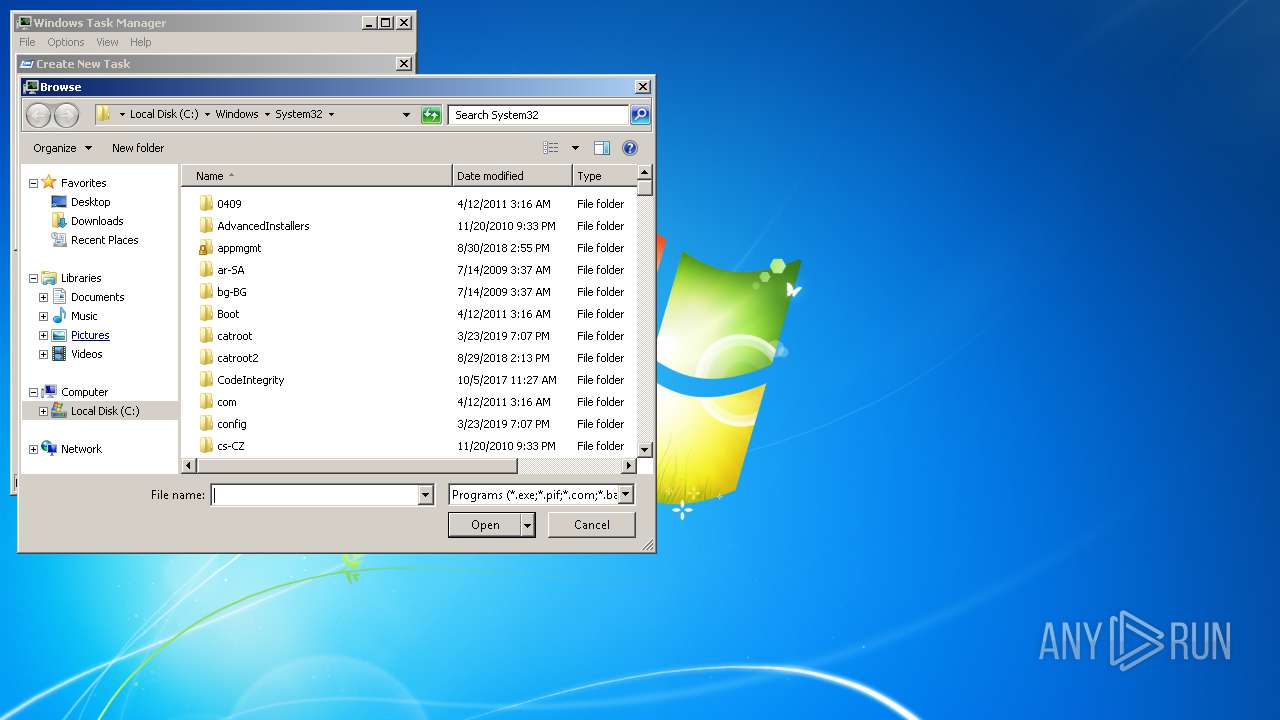
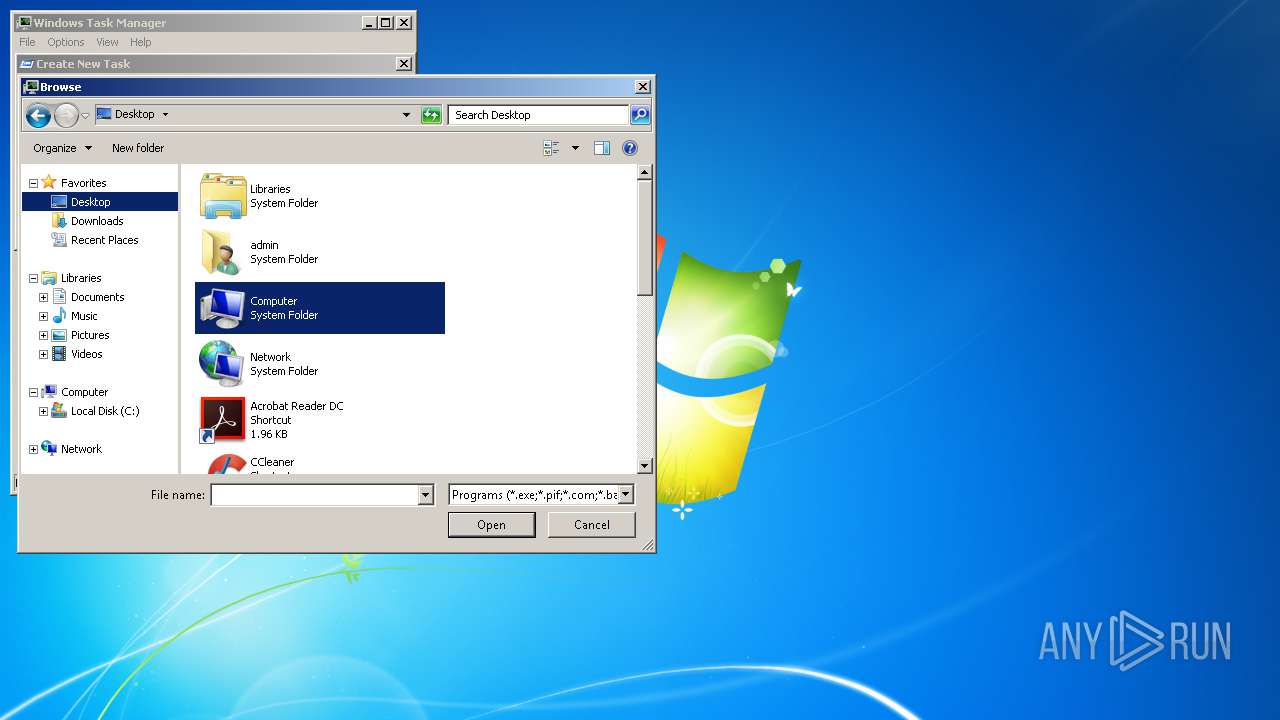
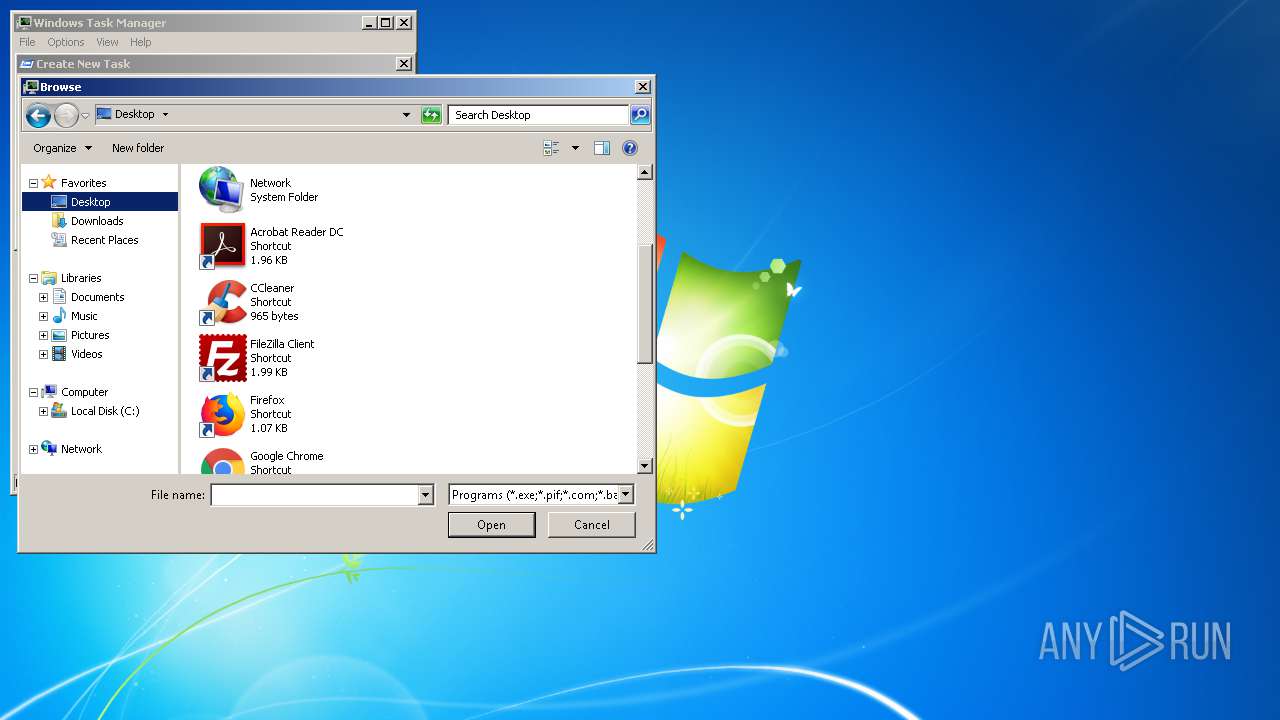
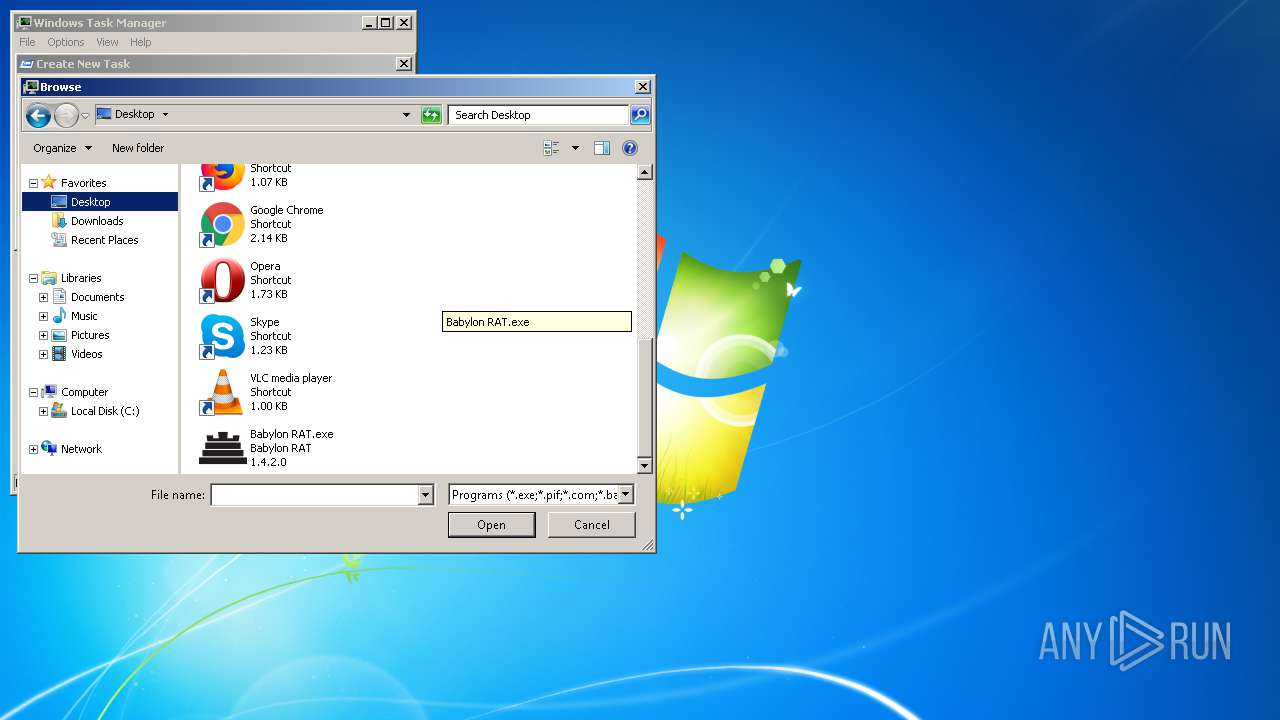
Manual execution by user
- Babylon RAT.exe (PID: 2416)
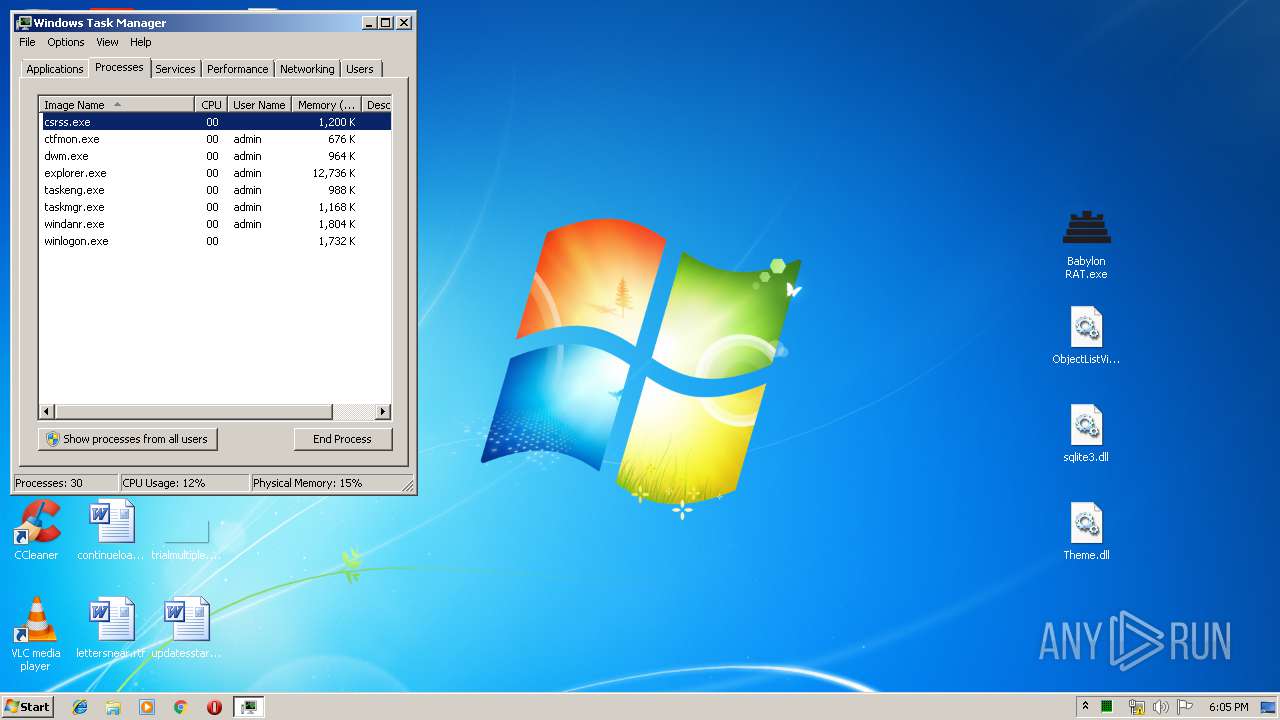
- taskmgr.exe (PID: 3660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
41
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1000 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
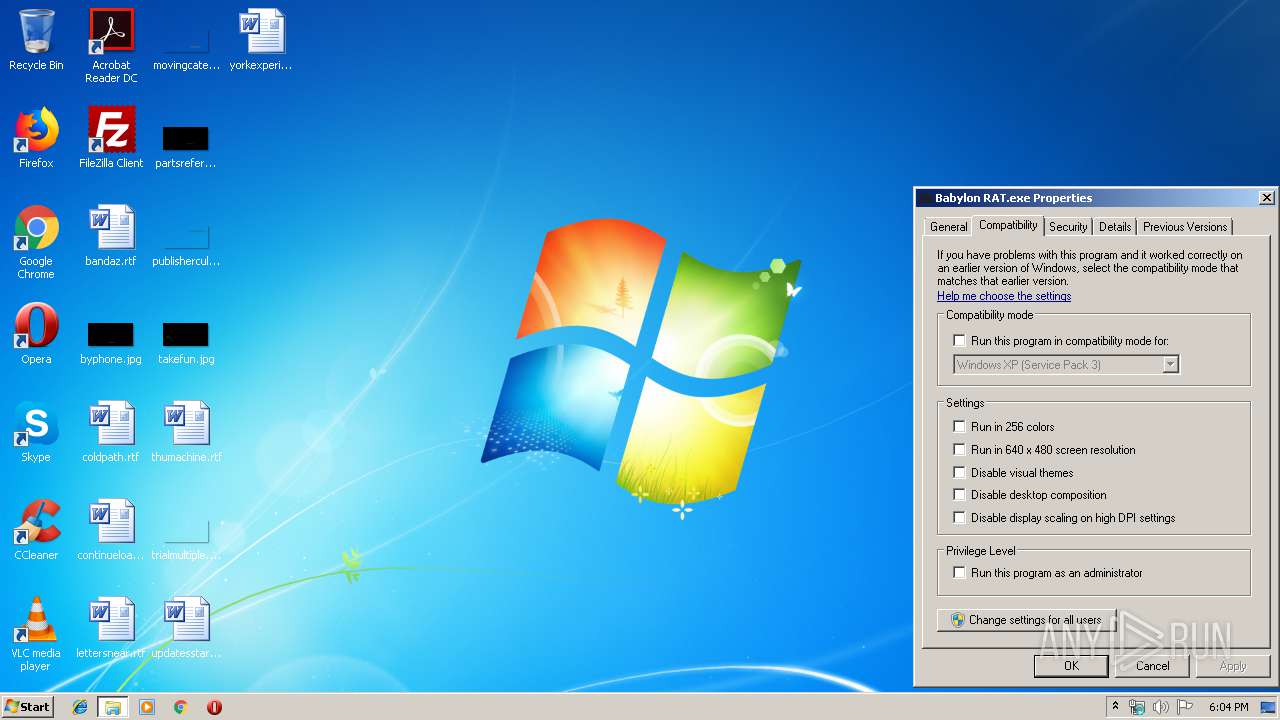
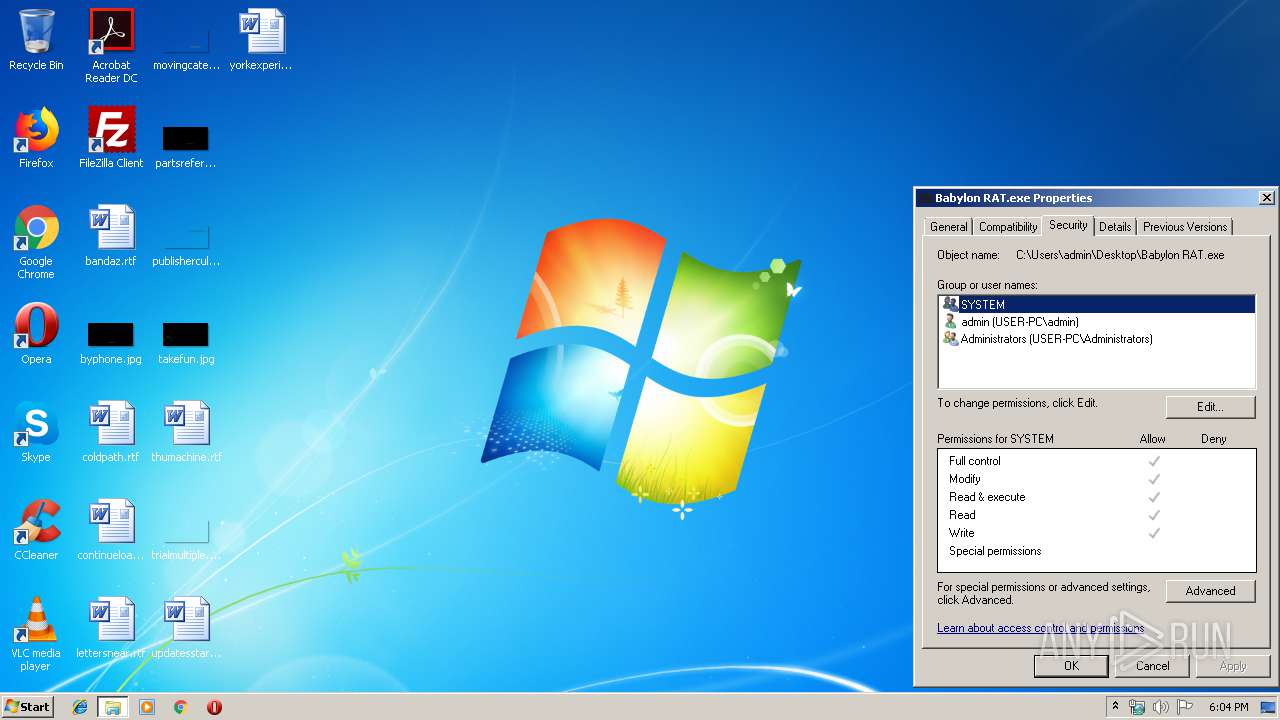
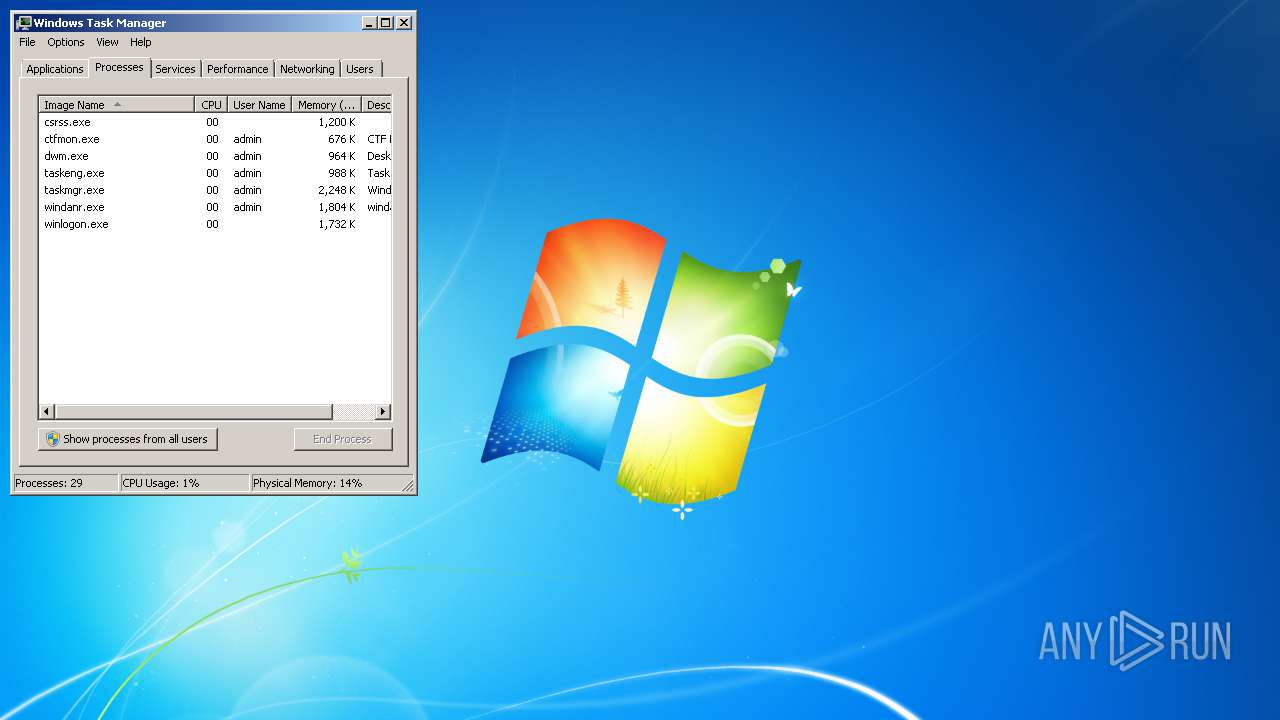
| 1016 | "C:\Users\admin\Desktop\Babylon RAT.exe" | C:\Users\admin\Desktop\Babylon RAT.exe | — | taskmgr.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Babylon RAT Exit code: 0 Version: 1.4.2 Modules
| |||||||||||||||
| 2416 | "C:\Users\admin\Desktop\Babylon RAT.exe" | C:\Users\admin\Desktop\Babylon RAT.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Babylon RAT Exit code: 0 Version: 1.4.2 Modules
| |||||||||||||||
| 3080 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Babylon.RAT.v.1.4.2-Crack-YQ8.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
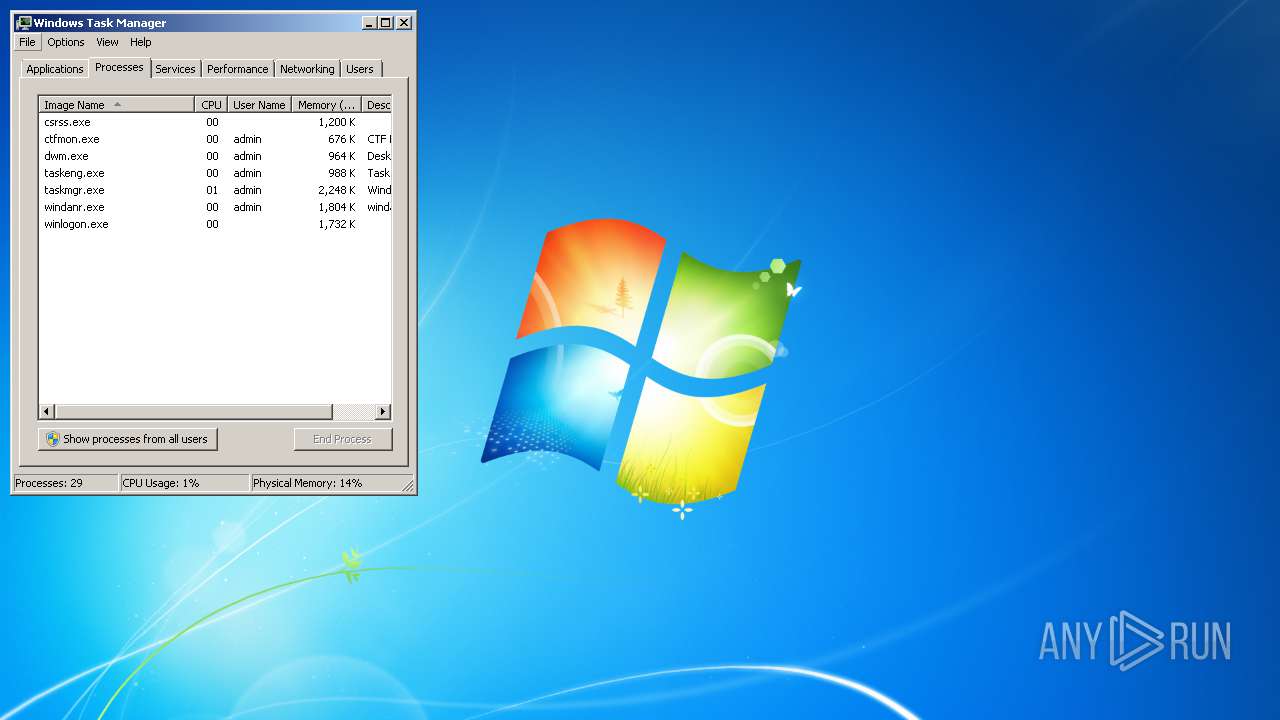
| 3660 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 191
Read events
1 046
Write events
144
Delete events
1
Modification events
| (PID) Process: | (3080) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3080) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3080) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3080) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Babylon.RAT.v.1.4.2-Crack-YQ8.rar | |||
| (PID) Process: | (3080) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3080) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3080) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3080) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3080) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (3080) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
4
Suspicious files
0
Text files
0
Unknown types
0
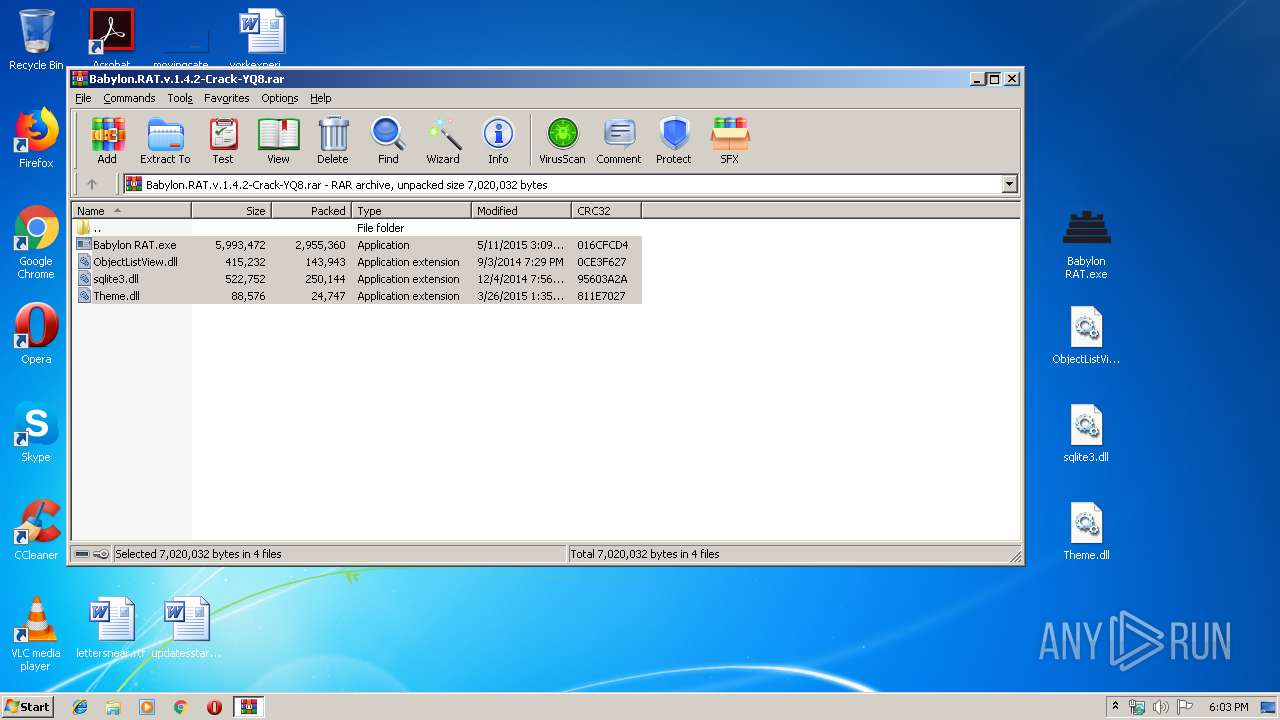
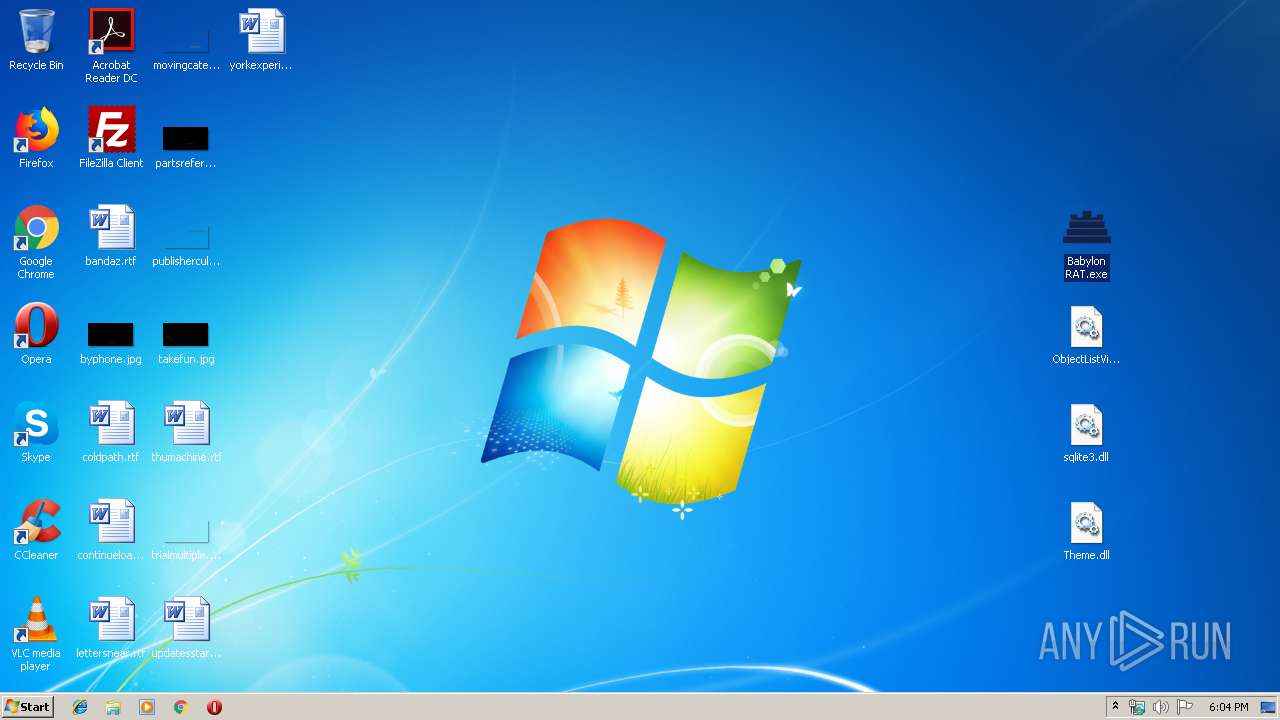
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3080 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3080.32626\Babylon RAT.exe | executable | |
MD5:— | SHA256:— | |||
| 3080 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3080.32626\sqlite3.dll | executable | |
MD5:D3979DB259F55D59B4EDB327673C1905 | SHA256:043E5570299C6099756C1809C5632EABEAB95ED3C1A55C86843C0EC218940E5A | |||
| 3080 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3080.32626\Theme.dll | executable | |
MD5:44C4FFF764E71051FAED99BA7A18F608 | SHA256:49400F97281D4D3F084333DB0E976520F95EF2B2D797E1F8FE3E795617B1FFD3 | |||
| 3080 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3080.32626\ObjectListView.dll | executable | |
MD5:DE9F71635FB8532BD5202086097C2083 | SHA256:1FA030CDD98F653FCAA109AF5C48F3D58F624AA671A980628397C6C6BC6433BE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report