| File name: | 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn |
| Full analysis: | https://app.any.run/tasks/b4d166ea-3bea-4f67-8755-a9a4560cffa9 |
| Verdict: | Malicious activity |
| Analysis date: | April 06, 2025, 05:29:39 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | 19457E39C266A4E7CED4B9D8E39F24DE |
| SHA1: | 1440DF91466366AF603FAF06A466AC82A219A5F5 |
| SHA256: | 50955988ADDE2D55E09BF4D773596CC9C3FA5CA6DE09A082D6424C51383B777D |
| SSDEEP: | 98304:5c928pqN1GsLCgGdZNvExjz1H9DH6wIRFm5WUlXFnqKHQuAxiu8fWWIZ9NypOsCj:2xIJOi00lcjicDEA |
MALICIOUS
JEEFO has been detected
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 4696)
- icsys.icn.exe (PID: 960)
- svchost.exe (PID: 7020)
- explorer.exe (PID: 6872)
Changes the autorun value in the registry
- explorer.exe (PID: 6872)
- svchost.exe (PID: 7020)
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 900)
SUSPICIOUS
Starts a Microsoft application from unusual location
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 900)
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 744)
Executable content was dropped or overwritten
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 744)
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 4696)
- icsys.icn.exe (PID: 960)
- explorer.exe (PID: 6872)
- spoolsv.exe (PID: 6572)
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 900)
Starts application with an unusual extension
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 4696)
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 900)
Application launched itself
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 900)
Starts itself from another location
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 4696)
- explorer.exe (PID: 6872)
- icsys.icn.exe (PID: 960)
- svchost.exe (PID: 7020)
- spoolsv.exe (PID: 6572)
The process creates files with name similar to system file names
- icsys.icn.exe (PID: 960)
- spoolsv.exe (PID: 6572)
Searches for installed software
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 744)
- dllhost.exe (PID: 7148)
Process drops legitimate windows executable
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 4696)
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 744)
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 900)
- msiexec.exe (PID: 7232)
Executes as Windows Service
- VSSVC.exe (PID: 7000)
Creates a software uninstall entry
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 900)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7232)
Creates or modifies Windows services
- svchost.exe (PID: 7020)
Reads security settings of Internet Explorer
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 900)
INFO
The sample compiled with english language support
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 4696)
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 744)
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 900)
- msiexec.exe (PID: 7232)
Checks supported languages
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 900)
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 744)
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 4696)
- icsys.icn.exe (PID: 960)
- explorer.exe (PID: 6872)
- spoolsv.exe (PID: 6572)
- svchost.exe (PID: 7020)
- spoolsv.exe (PID: 1188)
- msiexec.exe (PID: 7232)
Create files in a temporary directory
- icsys.icn.exe (PID: 960)
- explorer.exe (PID: 6872)
- spoolsv.exe (PID: 6572)
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 4696)
- spoolsv.exe (PID: 1188)
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 744)
- svchost.exe (PID: 7020)
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 900)
Reads the computer name
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 744)
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 900)
- svchost.exe (PID: 7020)
- msiexec.exe (PID: 7232)
Manages system restore points
- SrTasks.exe (PID: 3096)
Reads the machine GUID from the registry
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 900)
- msiexec.exe (PID: 7232)
Creates files or folders in the user directory
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 900)
Reads the software policy settings
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 900)
- msiexec.exe (PID: 7232)
- slui.exe (PID: 7504)
Creates files in the program directory
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 900)
The sample compiled with german language support
- msiexec.exe (PID: 7232)
The sample compiled with chinese language support
- msiexec.exe (PID: 7232)
Creates a software uninstall entry
- msiexec.exe (PID: 7232)
The sample compiled with spanish language support
- msiexec.exe (PID: 7232)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7232)
The sample compiled with japanese language support
- msiexec.exe (PID: 7232)
The sample compiled with Italian language support
- msiexec.exe (PID: 7232)
The sample compiled with russian language support
- msiexec.exe (PID: 7232)
The sample compiled with french language support
- msiexec.exe (PID: 7232)
The sample compiled with korean language support
- msiexec.exe (PID: 7232)
Checks proxy server information
- slui.exe (PID: 7504)
- 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe (PID: 900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:04:01 07:08:22+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 106496 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x290c |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| ProductName: | Project1 |
| FileVersion: | 1 |
| ProductVersion: | 1 |
| InternalName: | TJprojMain |
| OriginalFileName: | TJprojMain.exe |
Total processes
143
Monitored processes
15
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 744 | "c:\users\admin\desktop\2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe " -burn.unelevated BurnPipe.{CC4F444C-961C-4633-B4EC-0F2B82321696} {BDA5AA8E-ED9D-4A1C-96BF-437D8A628A0F} 900 | C:\Users\admin\Desktop\2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe | 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe | ||||||||||||
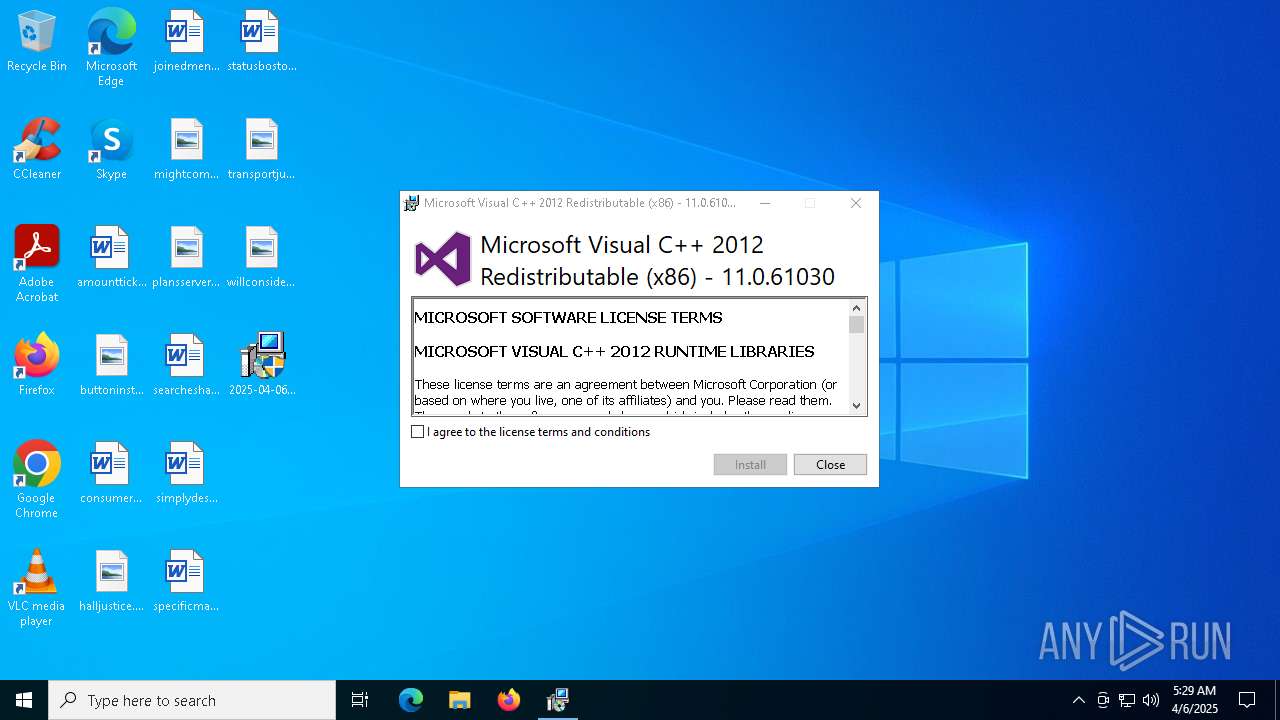
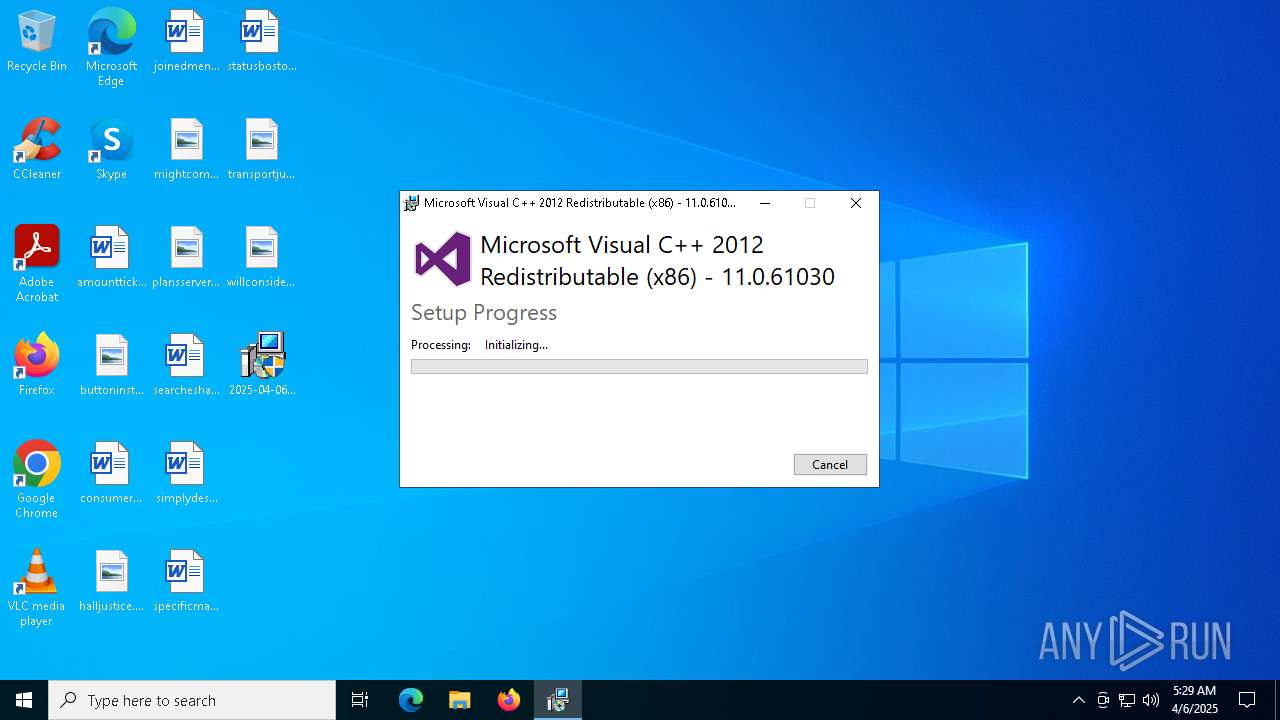
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2012 Redistributable (x86) - 11.0.61030 Exit code: 0 Version: 11.0.61030.0 Modules
| |||||||||||||||
| 900 | c:\users\admin\desktop\2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe | C:\Users\admin\Desktop\2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe | 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2012 Redistributable (x86) - 11.0.61030 Exit code: 0 Version: 11.0.61030.0 Modules
| |||||||||||||||
| 960 | C:\Windows\Resources\Themes\icsys.icn.exe | C:\Windows\Resources\Themes\icsys.icn.exe | 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 1188 | c:\windows\resources\spoolsv.exe PR | C:\Windows\Resources\spoolsv.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3096 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Windows System Protection background tasks. Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4696 | "C:\Users\admin\Desktop\2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe" | C:\Users\admin\Desktop\2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 5364 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6272 | "C:\Users\admin\Desktop\2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe" | C:\Users\admin\Desktop\2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.00 Modules
| |||||||||||||||
| 6572 | c:\windows\resources\spoolsv.exe SE | C:\Windows\Resources\spoolsv.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 6872 | c:\windows\resources\themes\explorer.exe | C:\Windows\Resources\Themes\explorer.exe | icsys.icn.exe | ||||||||||||
User: admin Integrity Level: HIGH Version: 1.00 Modules
| |||||||||||||||
Total events
14 688
Read events
14 056
Write events
593
Delete events
39
Modification events
| (PID) Process: | (4696) 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (960) icsys.icn.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (6872) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Explorer |
Value: c:\windows\resources\themes\explorer.exe RO | |||
| (PID) Process: | (6872) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Svchost |
Value: c:\windows\resources\svchost.exe RO | |||
| (PID) Process: | (6872) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Explorer |
Value: | |||
| (PID) Process: | (6872) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Svchost |
Value: | |||
| (PID) Process: | (7020) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Explorer |
Value: c:\windows\resources\themes\explorer.exe RO | |||
| (PID) Process: | (7020) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Svchost |
Value: c:\windows\resources\svchost.exe RO | |||
| (PID) Process: | (7020) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Explorer |
Value: | |||
| (PID) Process: | (7020) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Svchost |
Value: | |||
Executable files
30
Suspicious files
50
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7148 | dllhost.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 6872 | explorer.exe | C:\Windows\Resources\spoolsv.exe | executable | |
MD5:83BA6D49AC1EAE9F02737C7B308B3B30 | SHA256:3287F4F2AB2BF2D4EAF18BF3F2EBA813E9B58A4A7954AF3FABE3F6E56E0106FE | |||
| 744 | 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe | C:\Users\admin\AppData\Local\Temp\{33d1fd90-4274-48a1-9bc1-97e33d9c2d6f}\.ba1\wixstdba.dll | executable | |
MD5:D7BF29763354EDA154AAD637017B5483 | SHA256:7F5F8FCFD84132579F07E395E65B44E1B031FE01A299BCE0E3DD590131C5CB93 | |||
| 1188 | spoolsv.exe | C:\Users\admin\AppData\Local\Temp\~DF418C1EC0F391E7A3.TMP | binary | |
MD5:BAE8C122B3CEAD242A5FDC56B013DC2C | SHA256:0C2D2F12AA02DBE69679E78D81DD4974FB5EFB5E116BC3E8E4B921B31CB4A8AC | |||
| 4696 | 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe | C:\Users\admin\AppData\Local\Temp\~DFC4CE57CD21B12E87.TMP | binary | |
MD5:423A78CD2ADCCC8F5625F42578113FAC | SHA256:7A0439E80EBF4CBF0929C94F504D3341036E2026A75610DC7CD4683F51F94E6C | |||
| 744 | 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe | C:\Users\admin\AppData\Local\Temp\{33d1fd90-4274-48a1-9bc1-97e33d9c2d6f}\cabB3E1576D1FEFBB979E13B1A5379E0B16 | — | |
MD5:— | SHA256:— | |||
| 744 | 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe | C:\Users\admin\AppData\Local\Temp\{33d1fd90-4274-48a1-9bc1-97e33d9c2d6f}\.be\vcredist_x86.exe | executable | |
MD5:1191BA2A9908EE79C0220221233E850A | SHA256:4670E1ECB4B136D81148401CD71737CCF1376C772FA513A3E176B8CE8B8F982D | |||
| 744 | 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe | C:\Users\admin\AppData\Local\Temp\{33d1fd90-4274-48a1-9bc1-97e33d9c2d6f}\.ba1\license.rtf | text | |
MD5:E9F84E5EF16D918FAA9A5425B4B041CF | SHA256:5B7BD9AD76C8DF8E2C496B3DCEFC9FE3750DCCC48FB416126605ED3FB208F55A | |||
| 744 | 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe | C:\Users\admin\AppData\Local\Temp\{33d1fd90-4274-48a1-9bc1-97e33d9c2d6f}\.ba1\BootstrapperApplicationData.xml | xml | |
MD5:6182F3BB2D861DC04D0EA55F3BA4FFED | SHA256:EF0085C0476FBE4D6D170C6909F4AD35762FB05E125E9ED707B3C413AE6BBC74 | |||
| 900 | 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe | C:\ProgramData\Package Cache\{33d1fd90-4274-48a1-9bc1-97e33d9c2d6f}\vcredist_x86.exe | executable | |
MD5:1191BA2A9908EE79C0220221233E850A | SHA256:4670E1ECB4B136D81148401CD71737CCF1376C772FA513A3E176B8CE8B8F982D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
52
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
900 | 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | — | — | whitelisted |
— | — | GET | 304 | 20.12.23.50:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
900 | 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | — | — | whitelisted |
5084 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
900 | 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | — | — | whitelisted |
5084 | SIHClient.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5084 | SIHClient.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
5084 | SIHClient.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
5084 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5084 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.7.1.246:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3216 | svchost.exe | 20.7.1.246:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5452 | svchost.exe | 95.100.186.9:443 | go.microsoft.com | AKAMAI-AS | FR | whitelisted |
900 | 2025-04-06_19457e39c266a4e7ced4b9d8e39f24de_amadey_rhadamanthys_smoke-loader_swisyn.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5084 | SIHClient.exe | 172.202.163.200:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
5084 | SIHClient.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5084 | SIHClient.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |