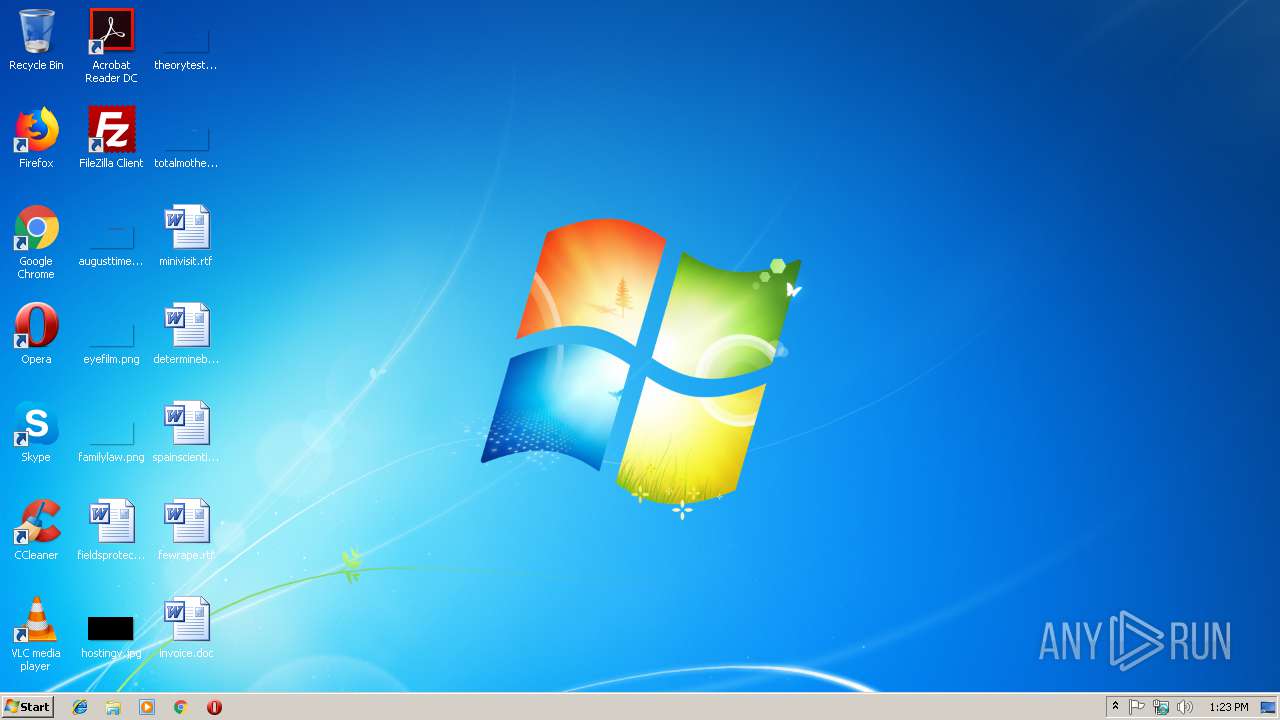
| File name: | invoice.doc |
| Full analysis: | https://app.any.run/tasks/9030ffc1-bdd0-4c7e-9bb6-c16fc21dfc05 |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2018, 13:23:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
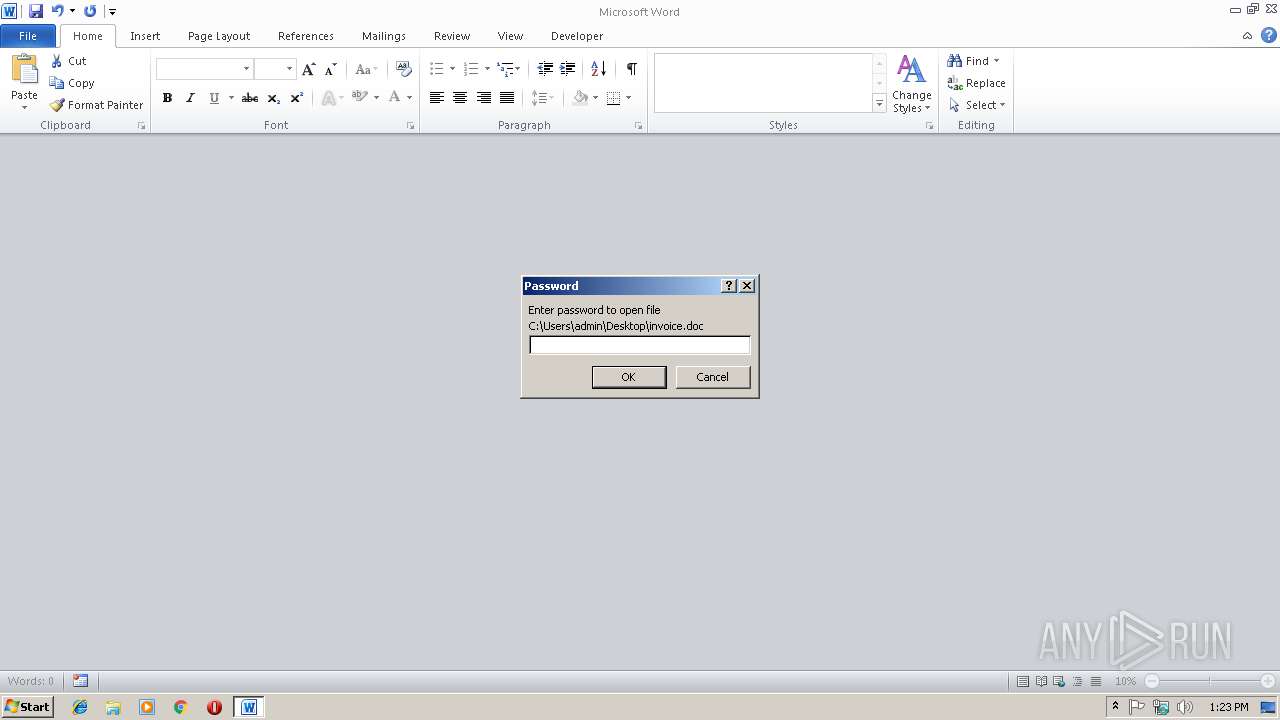
| MIME: | application/encrypted |
| File info: | CDFV2 Encrypted |
| MD5: | EC6DDB1160F848F1E6AA1C9AD6B941B3 |
| SHA1: | 7CB90D8F87E279AC695E8B7A9740BB000FCA1A0E |
| SHA256: | 50928F8E527C4737FABB8DC6E435CC18CD4291AD370A345DF1F657C724B7B8C7 |
| SSDEEP: | 768:a7ACy1kz5f6e3uqdPJrGf4eIq9XeyuZRft/59i:UA1UDu+hGf4eISXsFK |
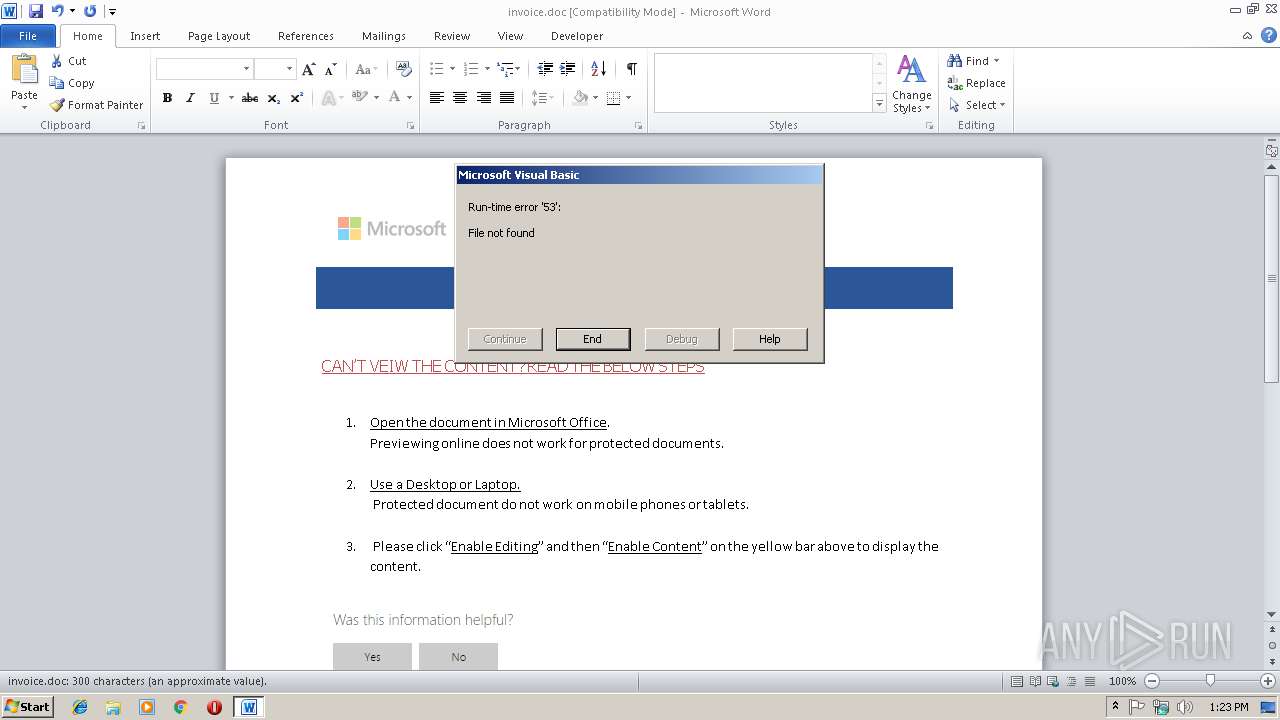
MALICIOUS
Requests a remote executable file from MS Office
- WINWORD.EXE (PID: 2692)
SUSPICIOUS
Unusual connect from Microsoft Office
- WINWORD.EXE (PID: 2692)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2692)
Creates files in the user directory
- WINWORD.EXE (PID: 2692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
32
Monitored processes
1
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2692 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\invoice.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 084
Read events
677
Write events
400
Delete events
7
Modification events
| (PID) Process: | (2692) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | d2$ |
Value: 64322400840A0000010000000000000000000000 | |||
| (PID) Process: | (2692) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2692) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2692) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1301151774 | |||
| (PID) Process: | (2692) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1301151888 | |||
| (PID) Process: | (2692) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1301151889 | |||
| (PID) Process: | (2692) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 840A000050B32D32B093D40100000000 | |||
| (PID) Process: | (2692) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | a5$ |
Value: 61352400840A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2692) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | a5$ |
Value: 61352400840A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2692) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
3
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2692 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8A64.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2692 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFDD375E47C4B9181D.TMP | — | |
MD5:— | SHA256:— | |||
| 2692 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF751F80BA840E50D6.TMP | — | |
MD5:— | SHA256:— | |||
| 2692 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFBD3373AE9847FE53.TMP | — | |
MD5:— | SHA256:— | |||
| 2692 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFB1EFDDC8E47D96E7.TMP | — | |
MD5:— | SHA256:— | |||
| 2692 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\msoB0B9.tmp | — | |
MD5:— | SHA256:— | |||
| 2692 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFF77FFBB45436F5C9.TMP | — | |
MD5:— | SHA256:— | |||
| 2692 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF26B84B2EB2F9E461.TMP | — | |
MD5:— | SHA256:— | |||
| 2692 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\3968BBC4.png | — | |
MD5:— | SHA256:— | |||
| 2692 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\FB45A0F5.png | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
0
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2692 | WINWORD.EXE | GET | 404 | 209.141.61.249:80 | http://209.141.61.249/516.exe | US | html | 205 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2692 | WINWORD.EXE | 209.141.61.249:80 | — | FranTech Solutions | US | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
2692 | WINWORD.EXE | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
2692 | WINWORD.EXE | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious downloader - 404 Not Found for .exe |