| File name: | W-1553916722.xlsb |
| Full analysis: | https://app.any.run/tasks/a3f96805-9c83-44ec-ad9b-9c1c6bc613a9 |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 12:45:05 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.spreadsheetml.sheet |
| File info: | Microsoft Excel 2007+ |
| MD5: | 82C18CBD86F03A752314840A80DEEB80 |
| SHA1: | AA35464F8770F8BCC8F77C528E1328A7C24B8D77 |
| SHA256: | 508E823895C2DBC8FC72B35FC1A888B81A0509EE4856566FA236A7AD70396BC3 |
| SSDEEP: | 49152:ZY5kCFkptNCiwqQo8wn5p4i1jDJZSObw+8p8rfY5kCFkptNCiwgY5kCFkptNCiwO:ZYGS4tNNLQUai1jDbf8p8bYGS4tNNPY2 |
MALICIOUS
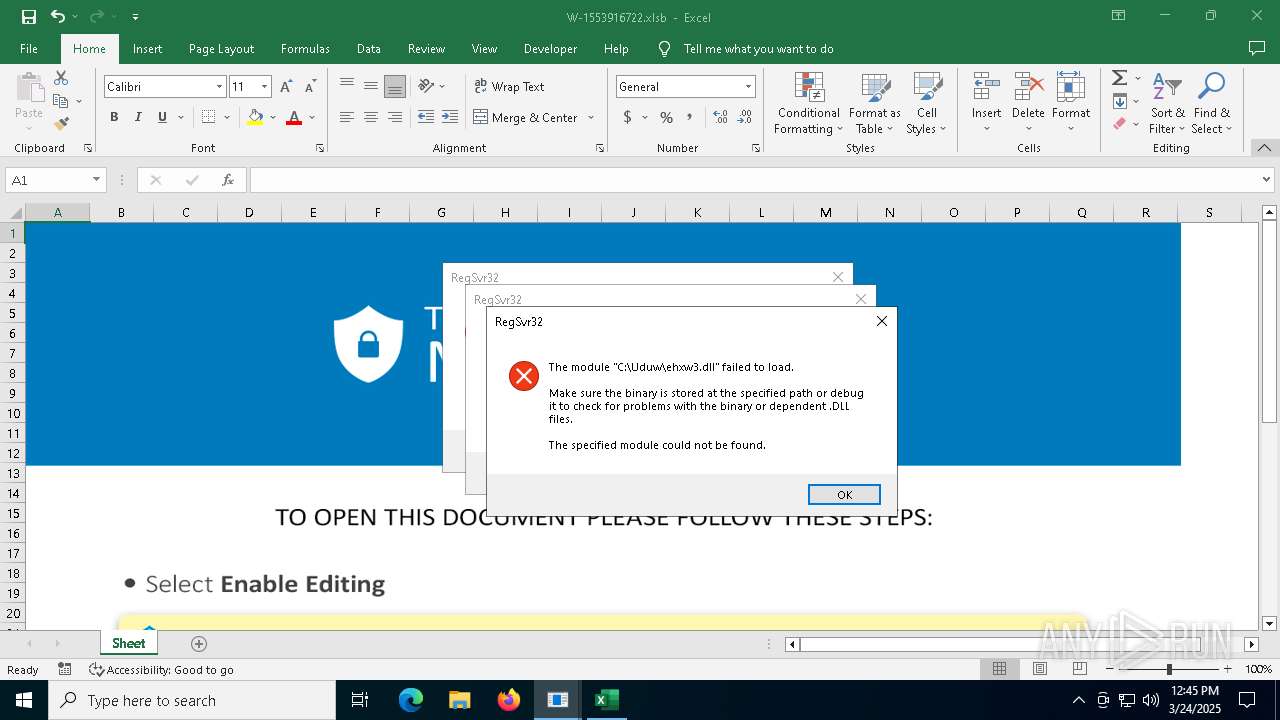
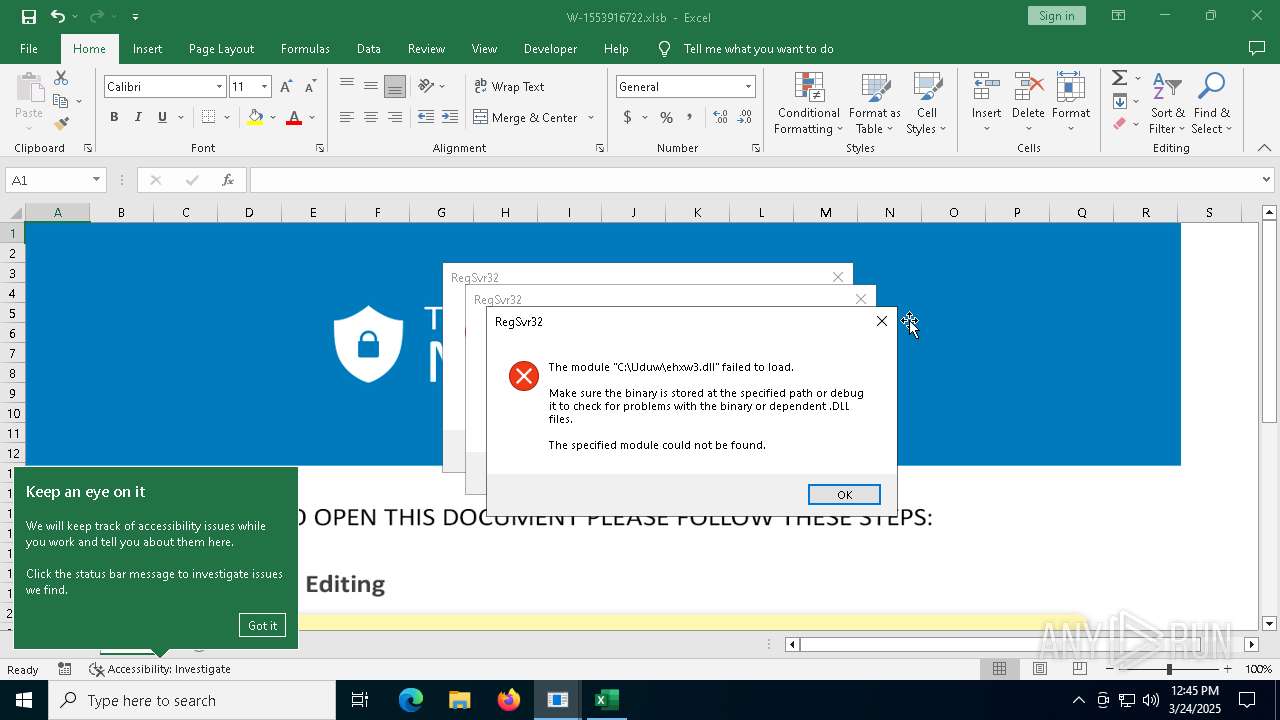
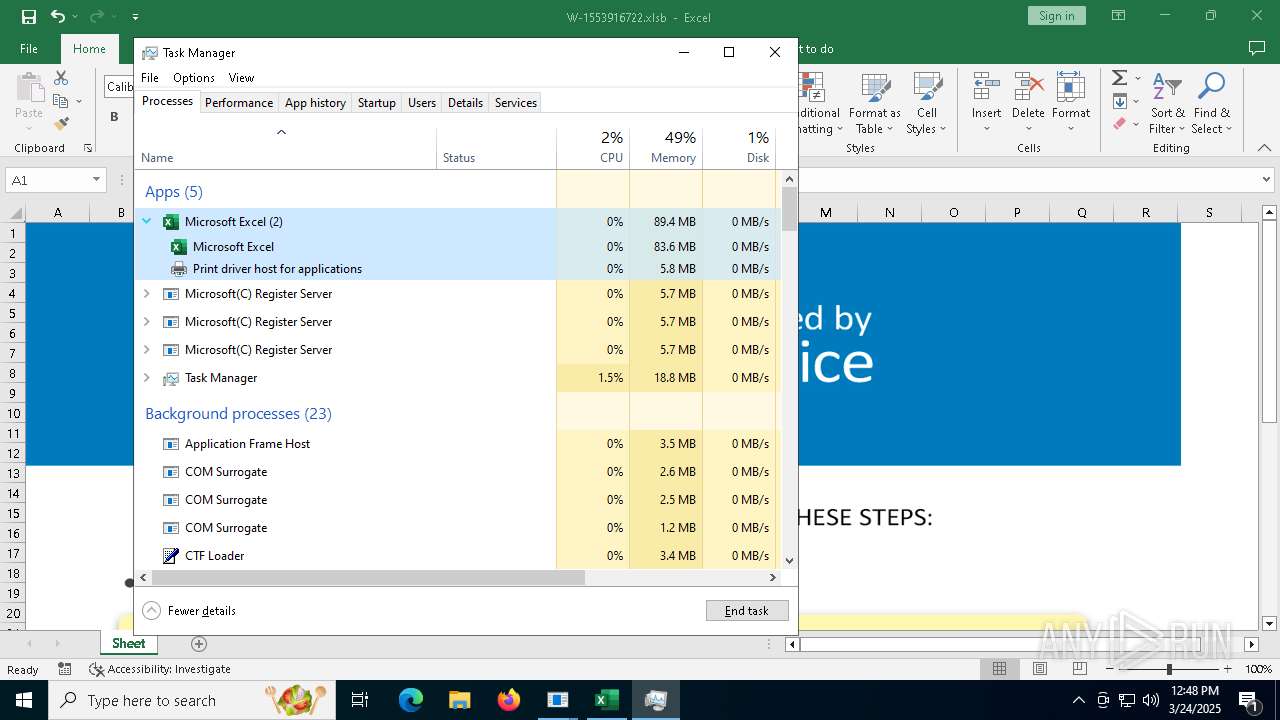
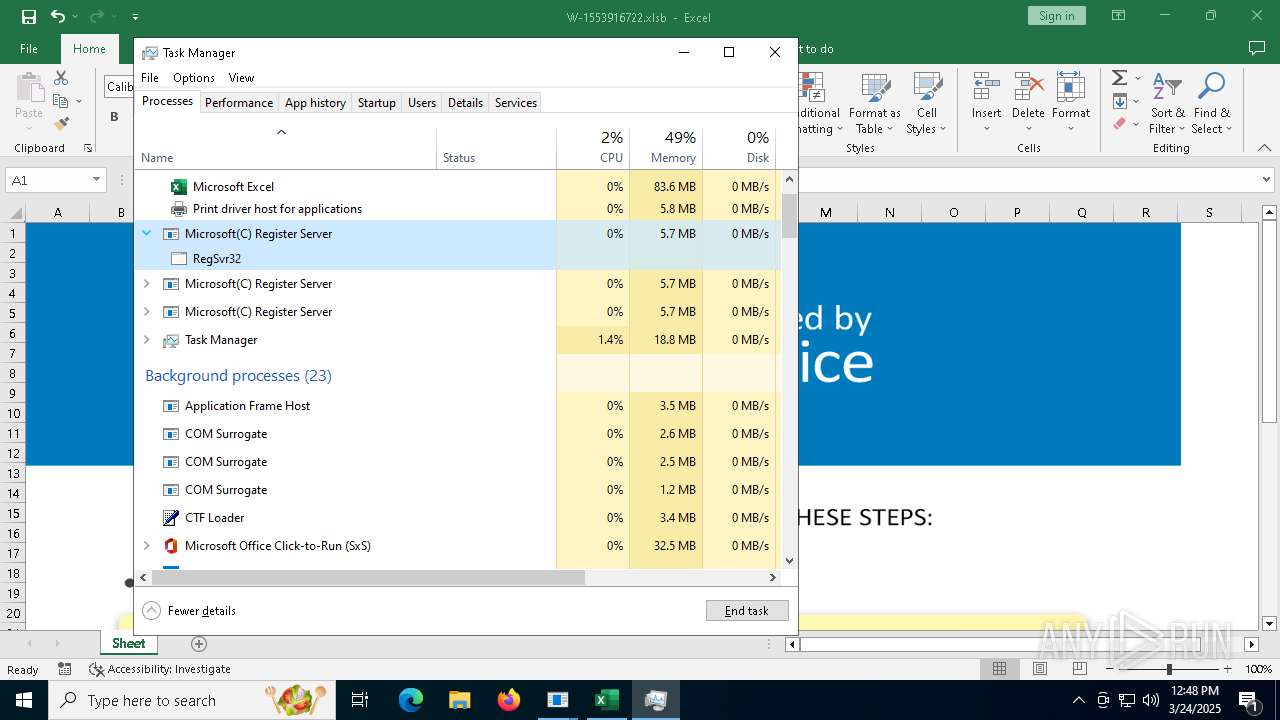
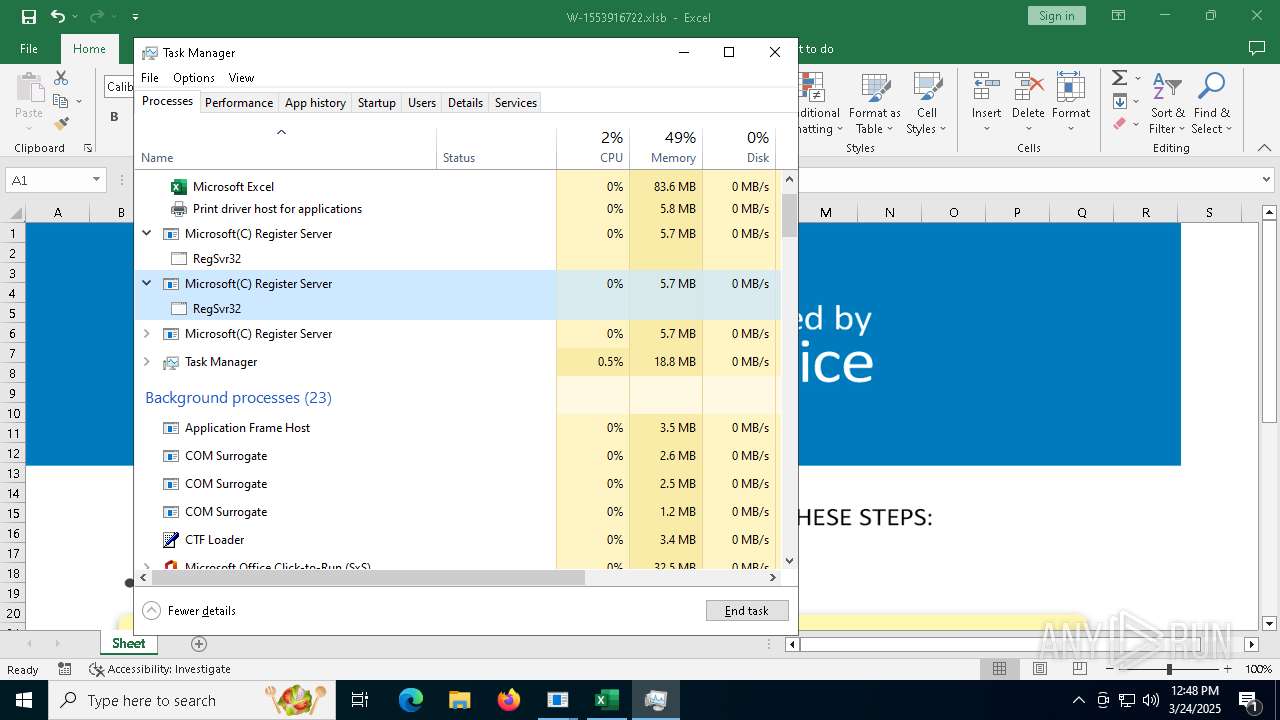
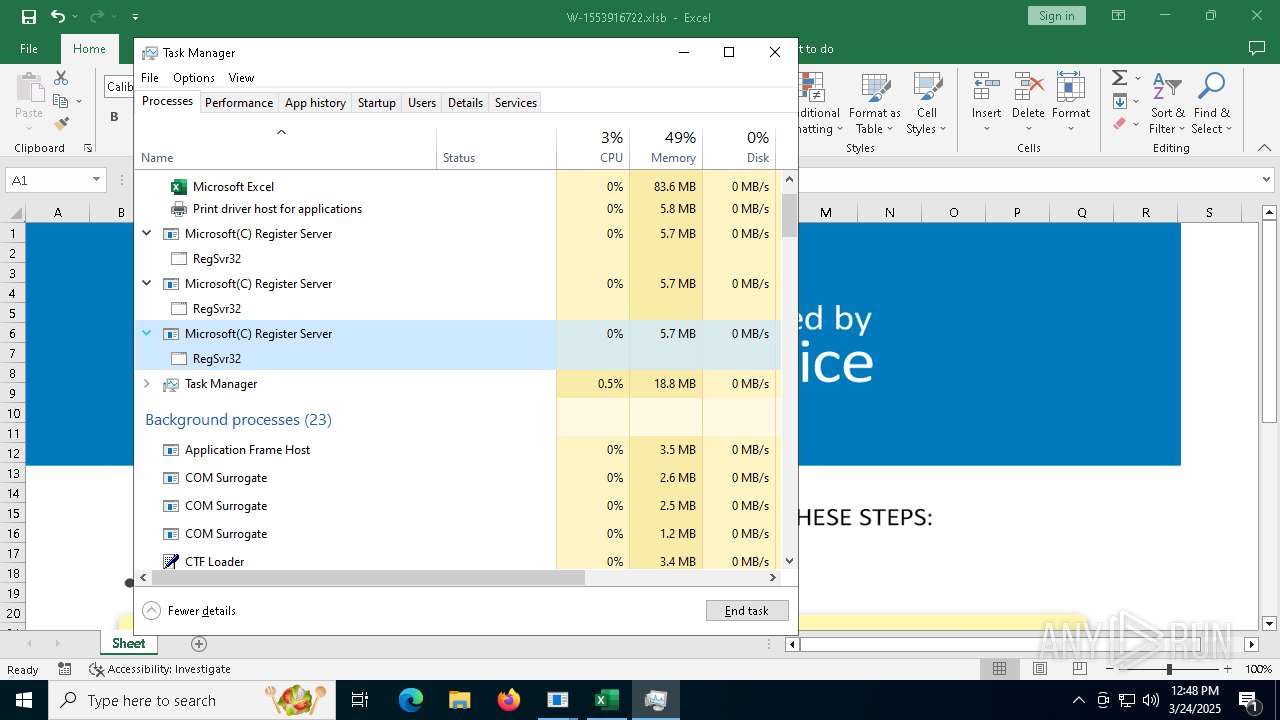
Calls Win API functions (MACROS)
- EXCEL.EXE (PID: 7472)
Unusual execution from MS Office
- EXCEL.EXE (PID: 7472)
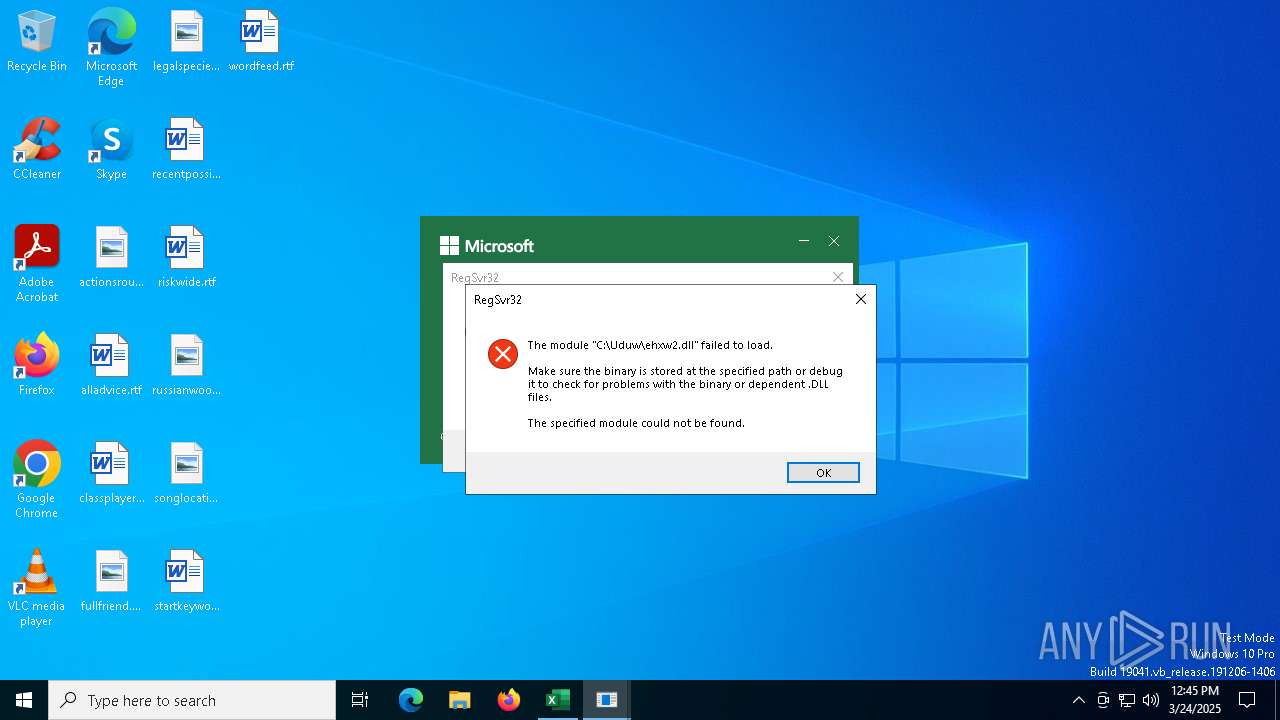
Registers / Runs the DLL via REGSVR32.EXE
- EXCEL.EXE (PID: 7472)
SUSPICIOUS
Detected use of alternative data streams (AltDS)
- EXCEL.EXE (PID: 7472)
Sets XML DOM element text (SCRIPT)
- splwow64.exe (PID: 5776)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 4176)
INFO
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 2108)
- slui.exe (PID: 7652)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 2108)
- slui.exe (PID: 6644)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 2108)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 4180)
- BackgroundTransferHost.exe (PID: 2108)
- BackgroundTransferHost.exe (PID: 8060)
- BackgroundTransferHost.exe (PID: 8184)
- BackgroundTransferHost.exe (PID: 7408)
- Taskmgr.exe (PID: 1676)
- splwow64.exe (PID: 5776)
Checks supported languages
- ShellExperienceHost.exe (PID: 7872)
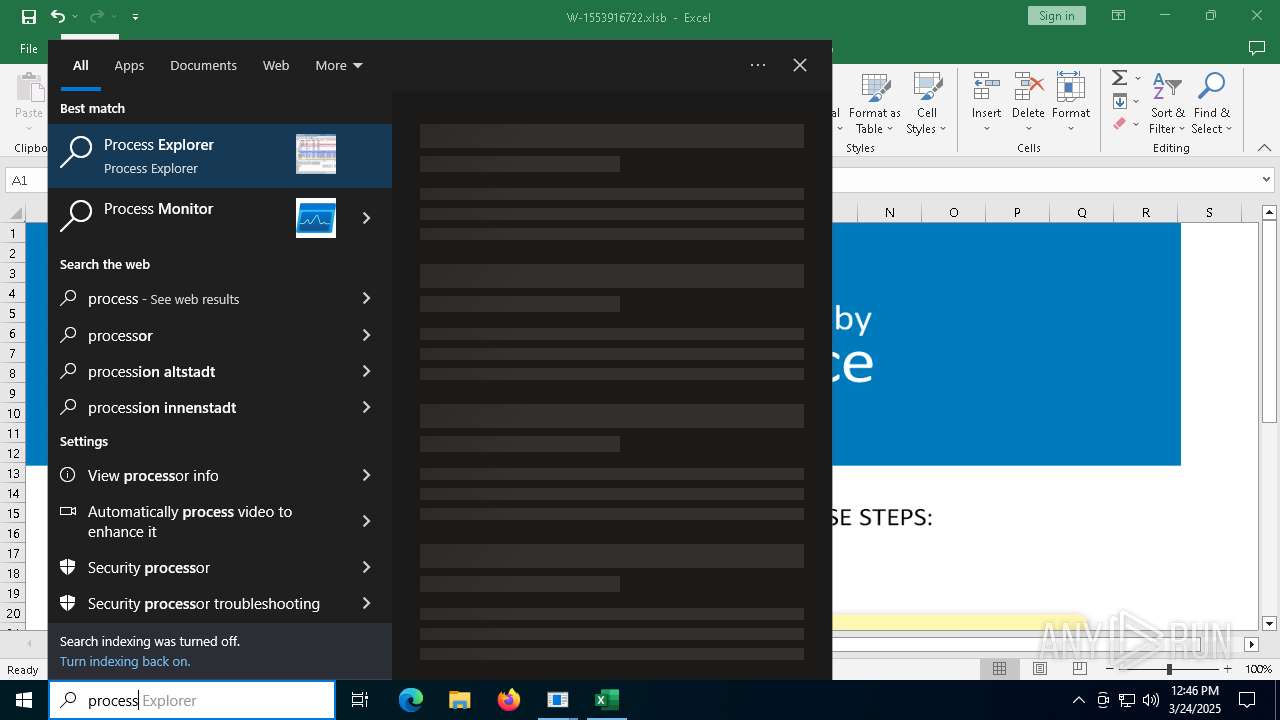
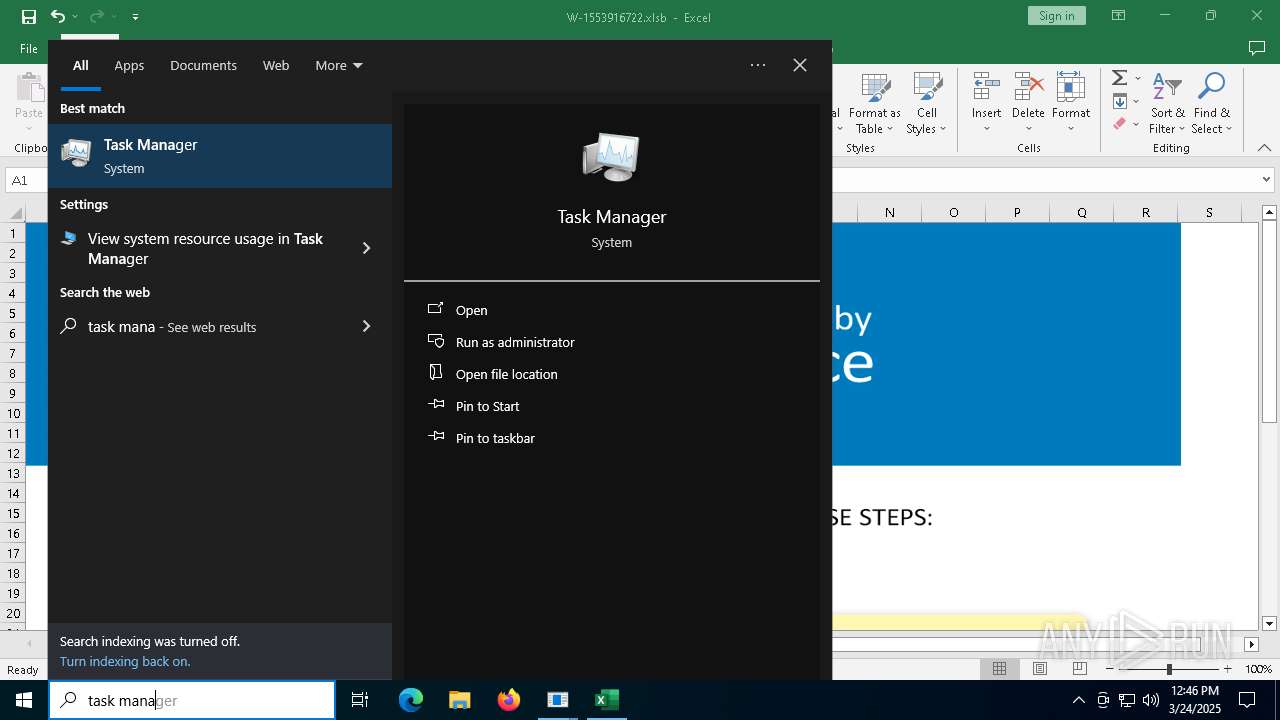
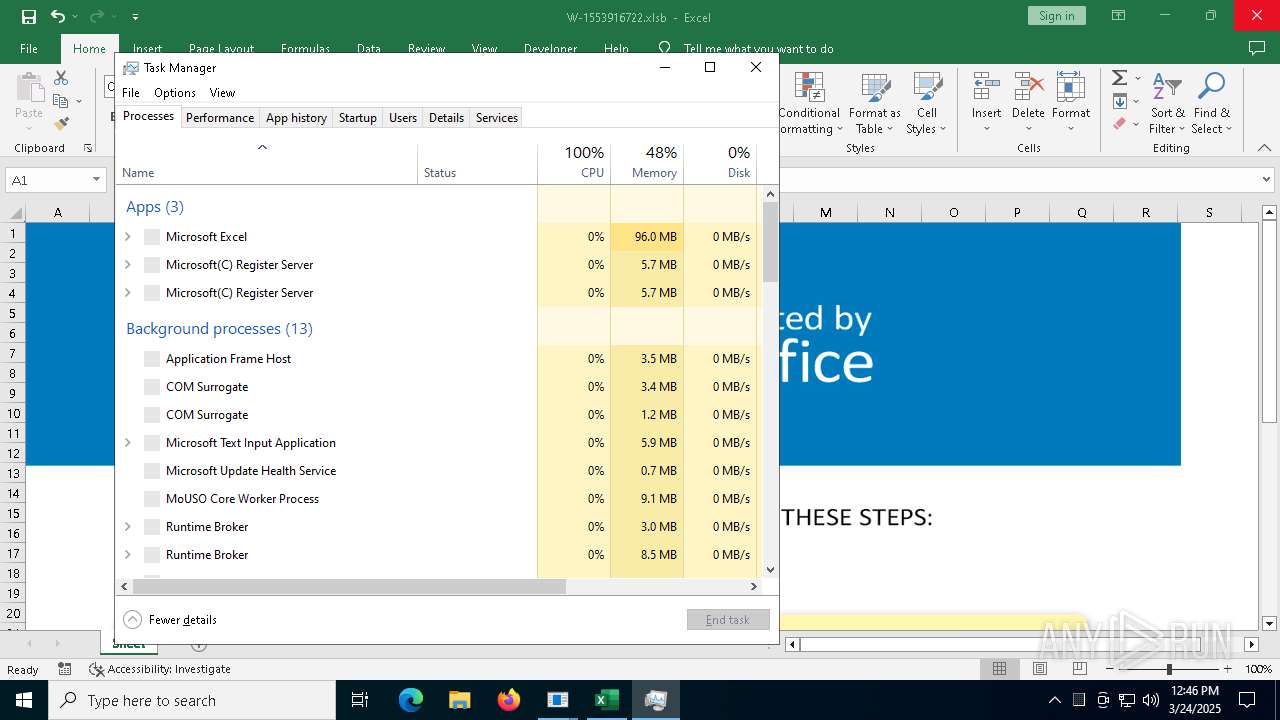
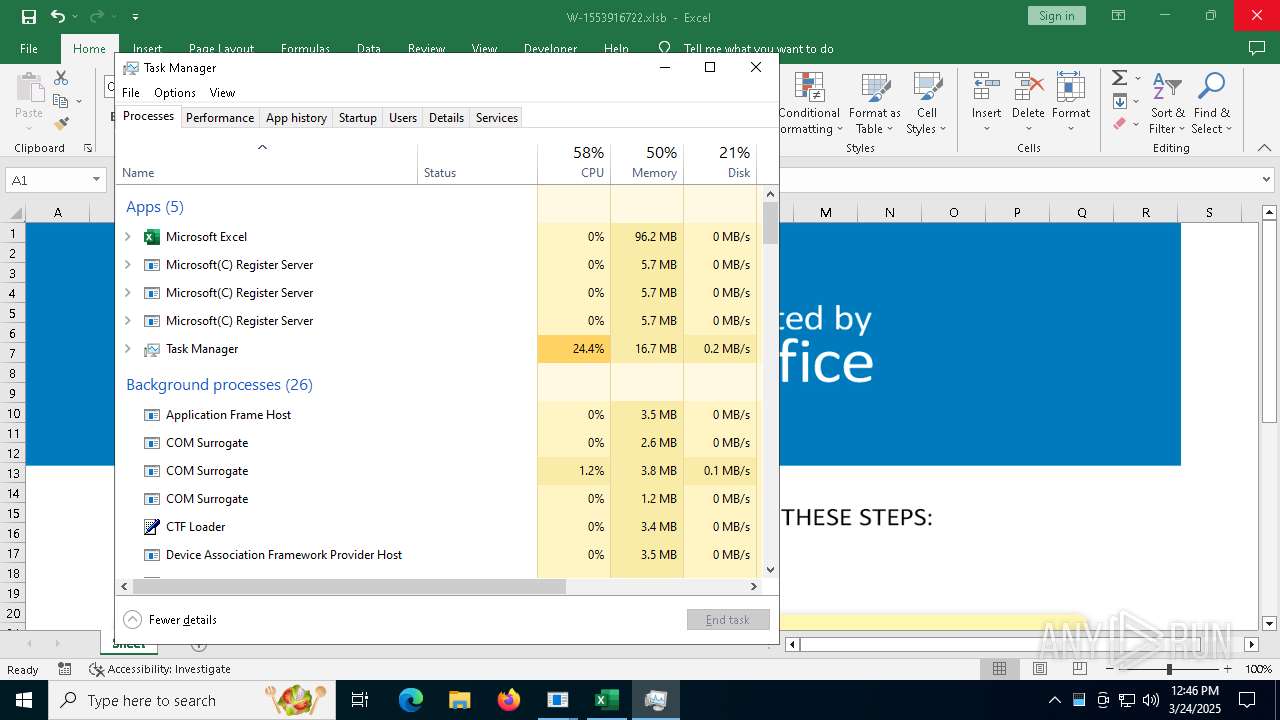
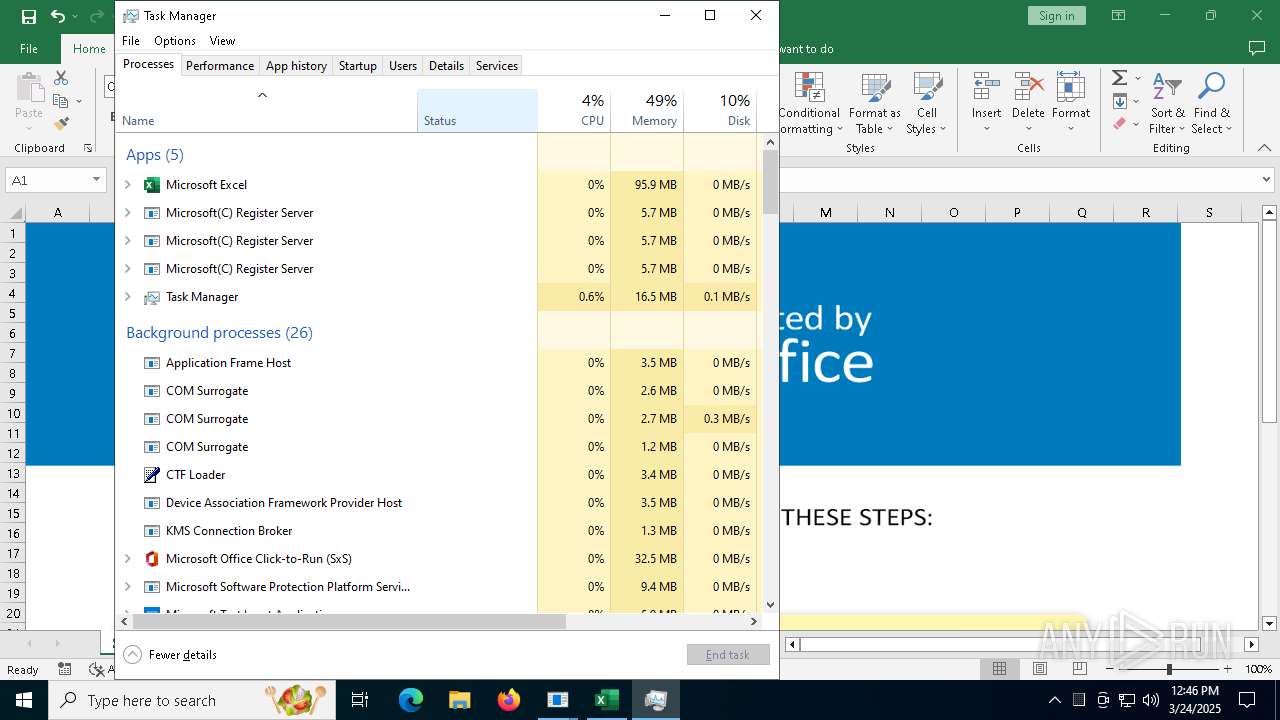
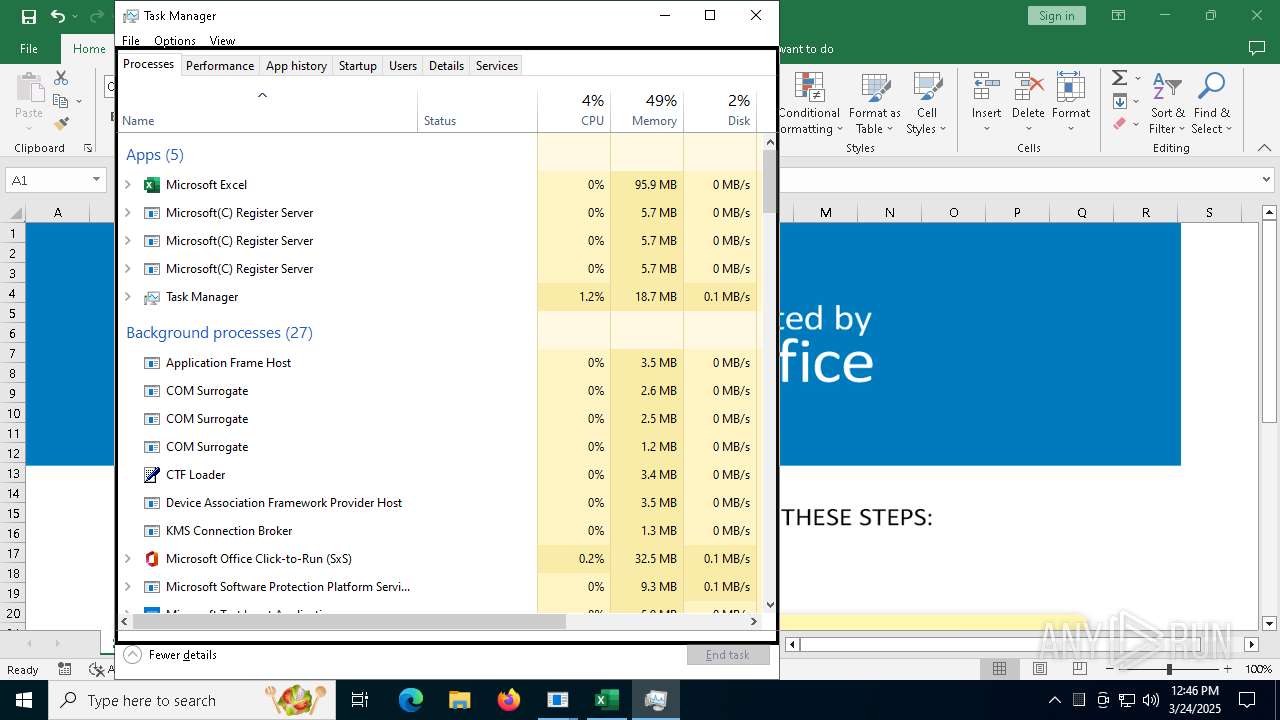
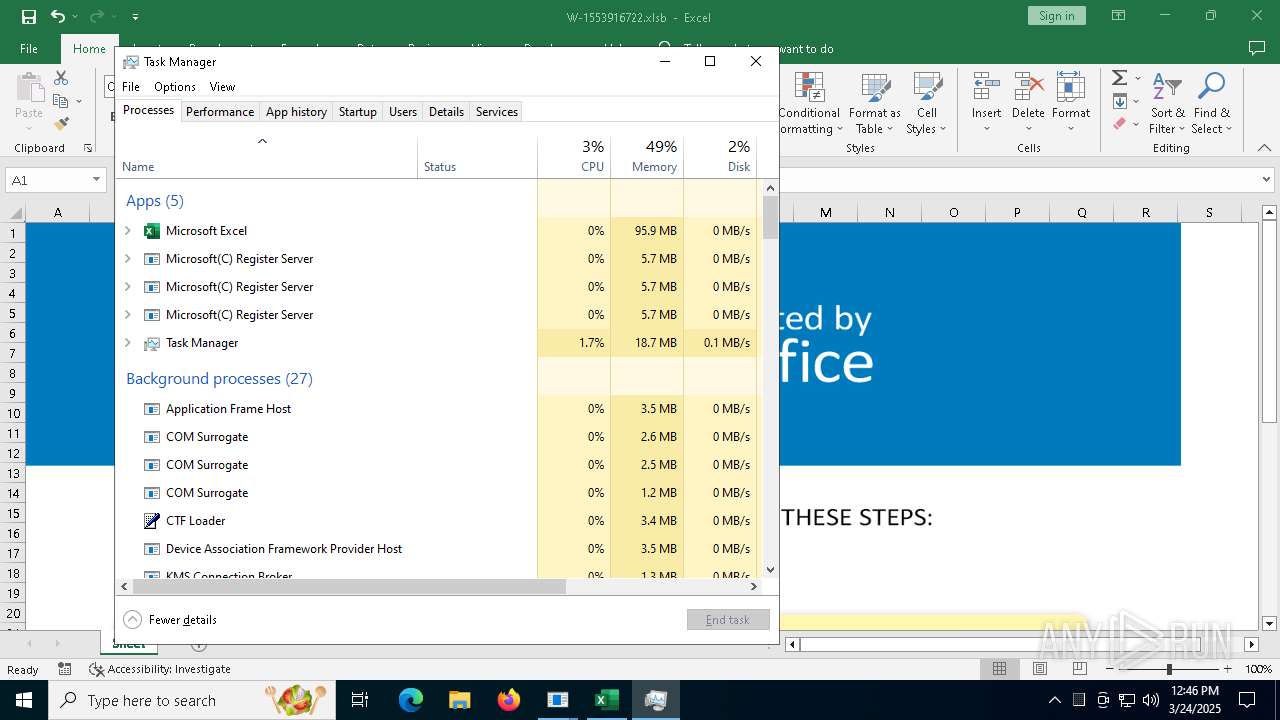
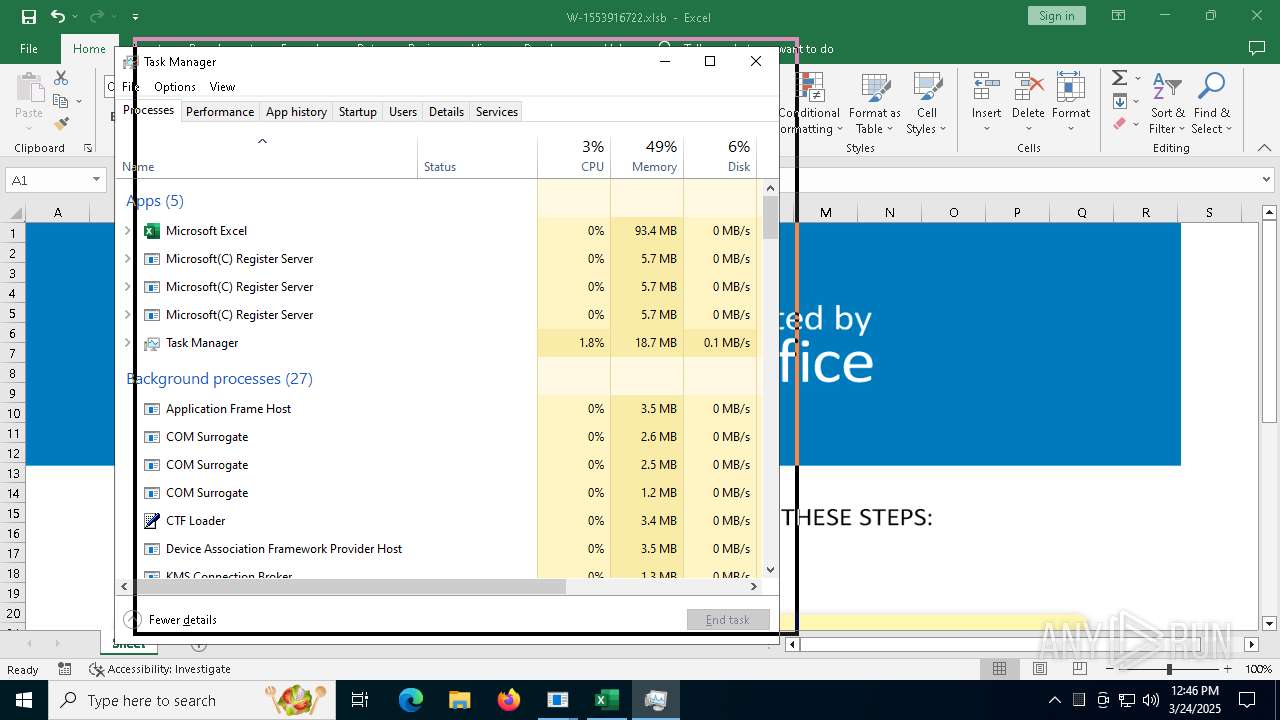
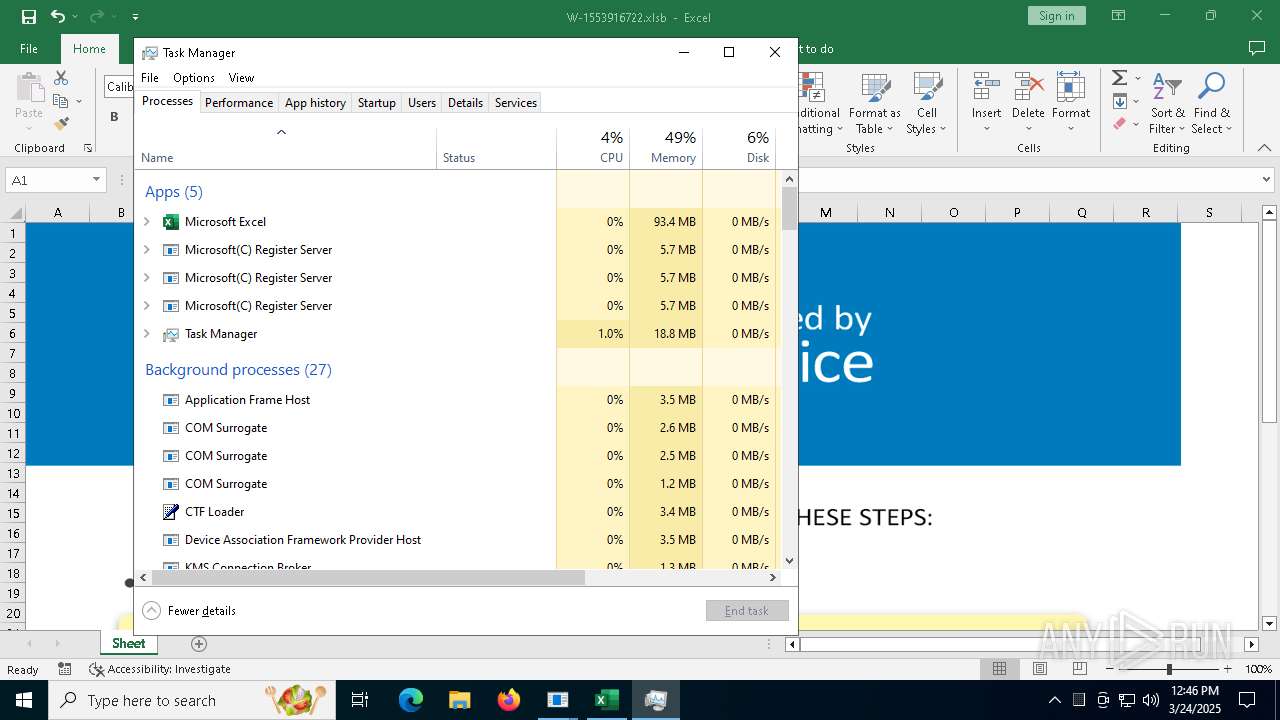
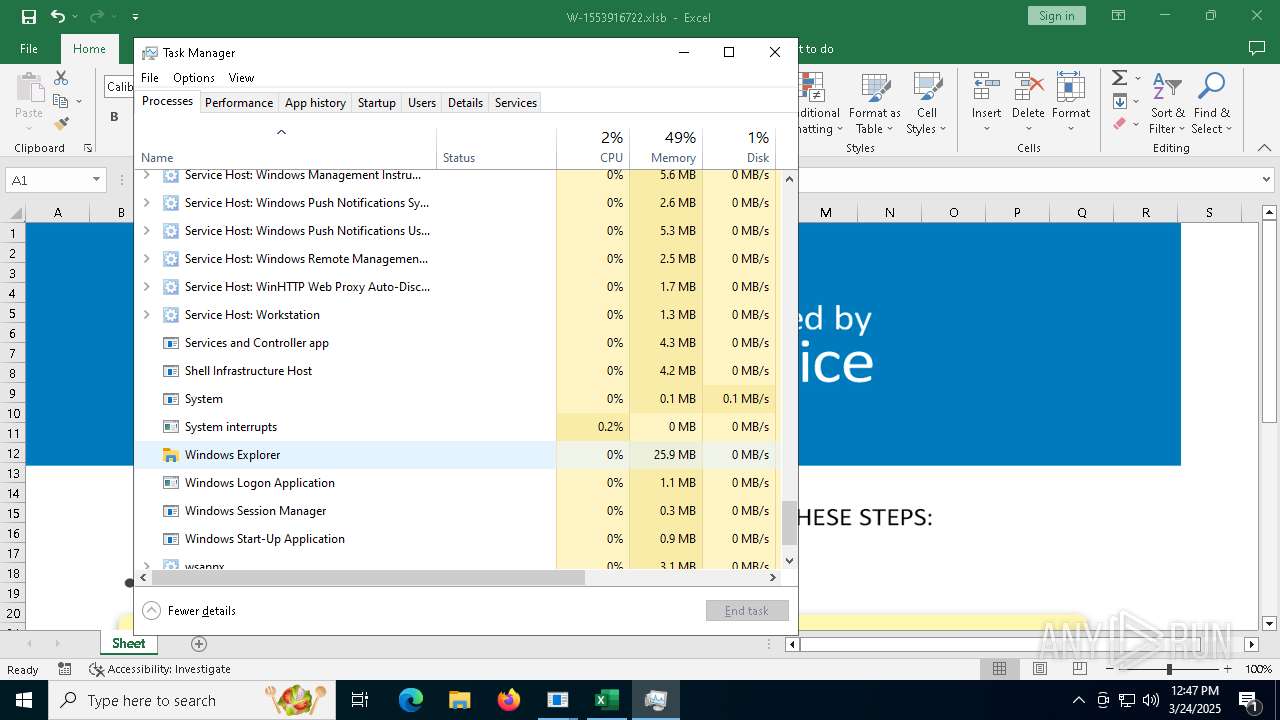
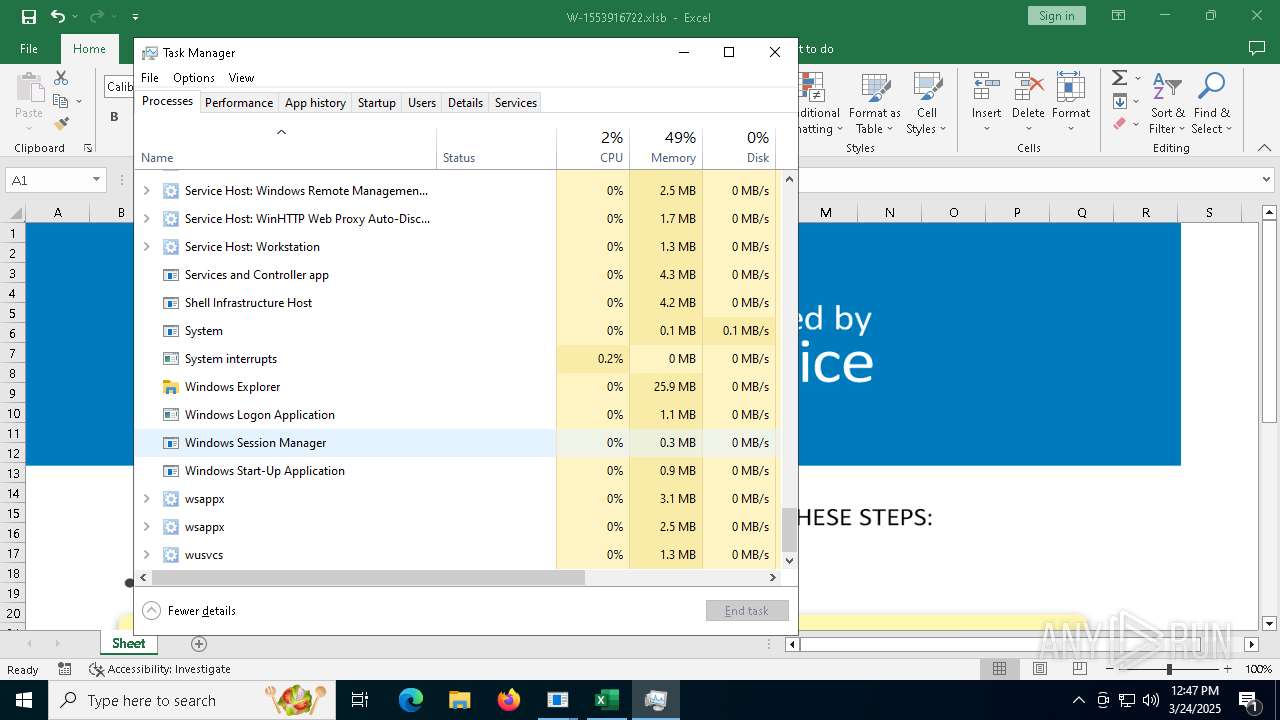
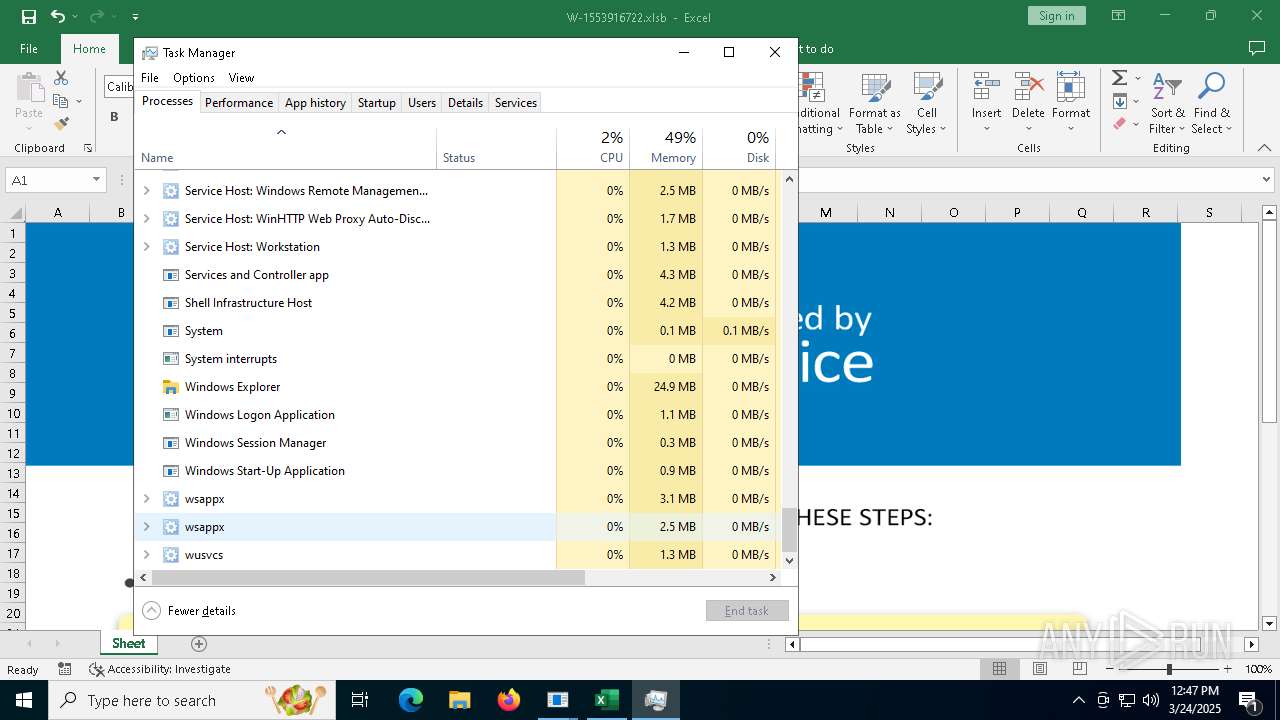
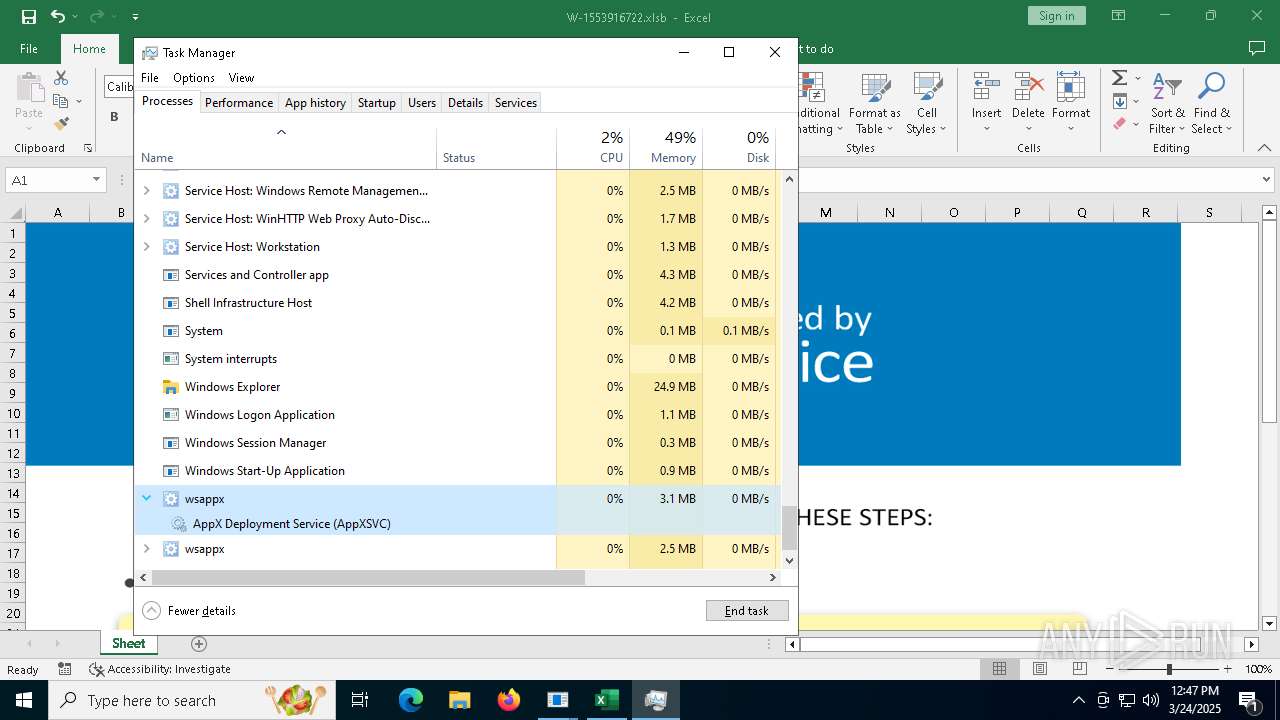
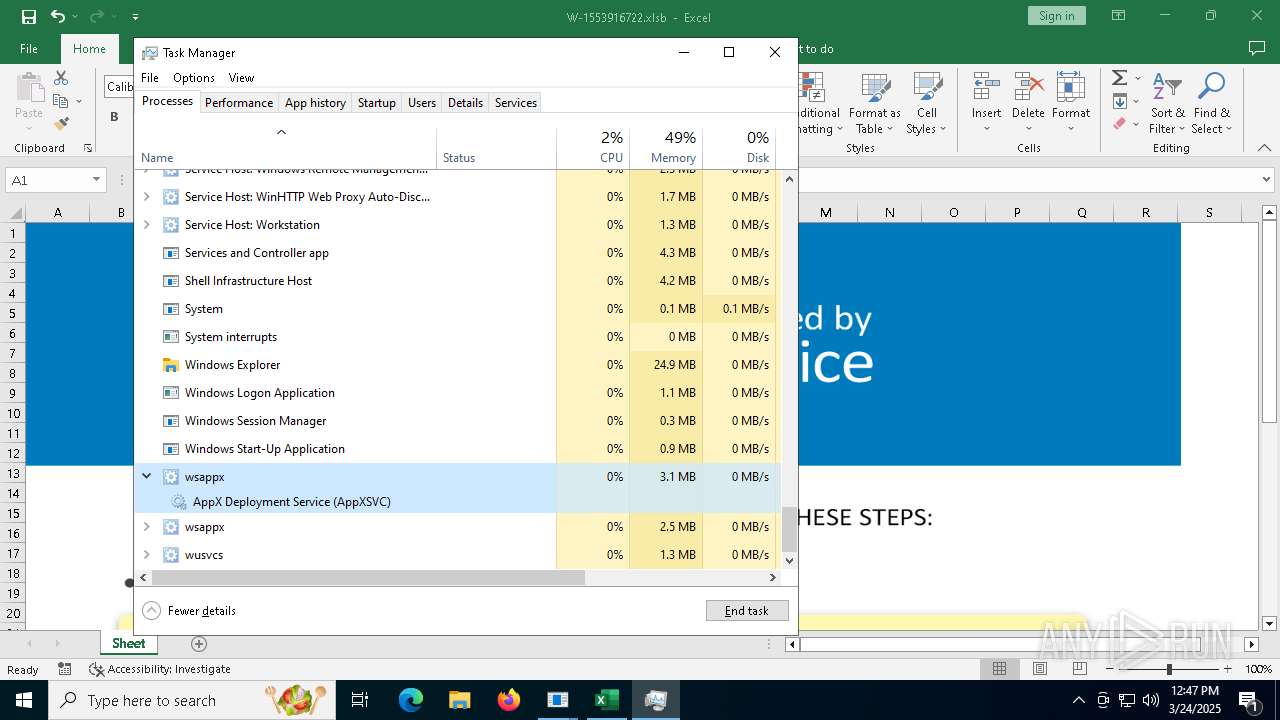
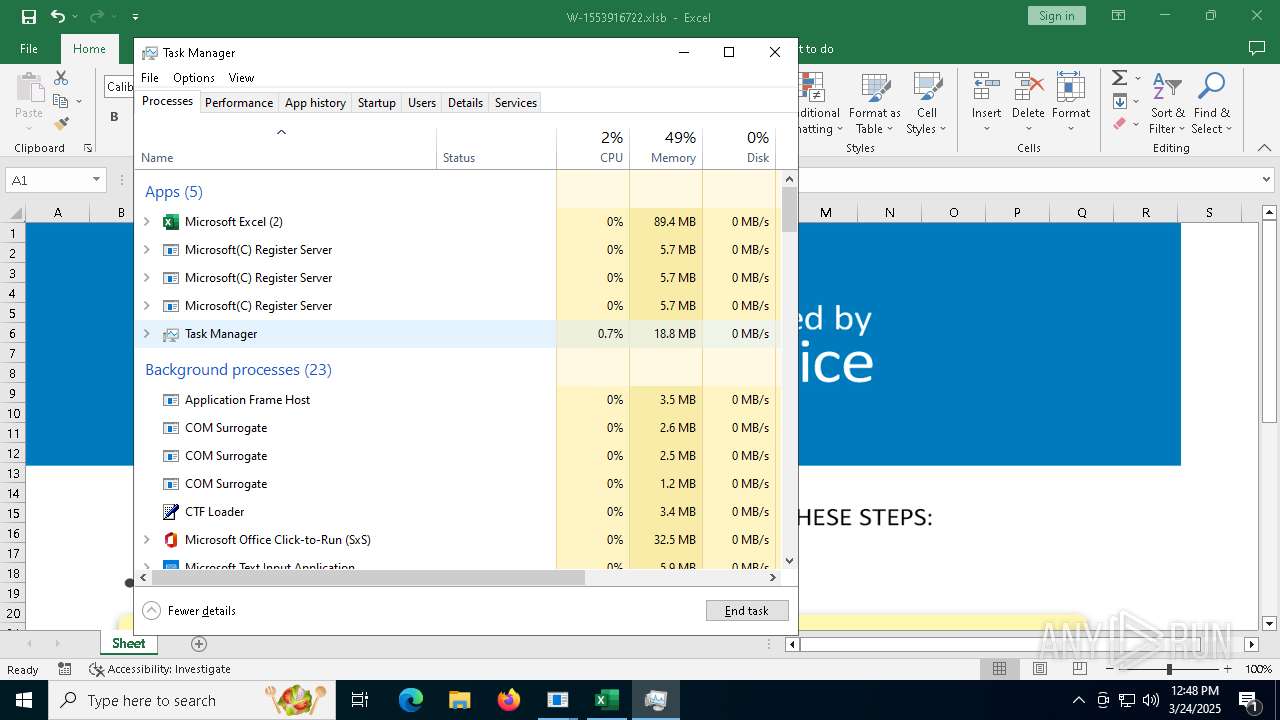
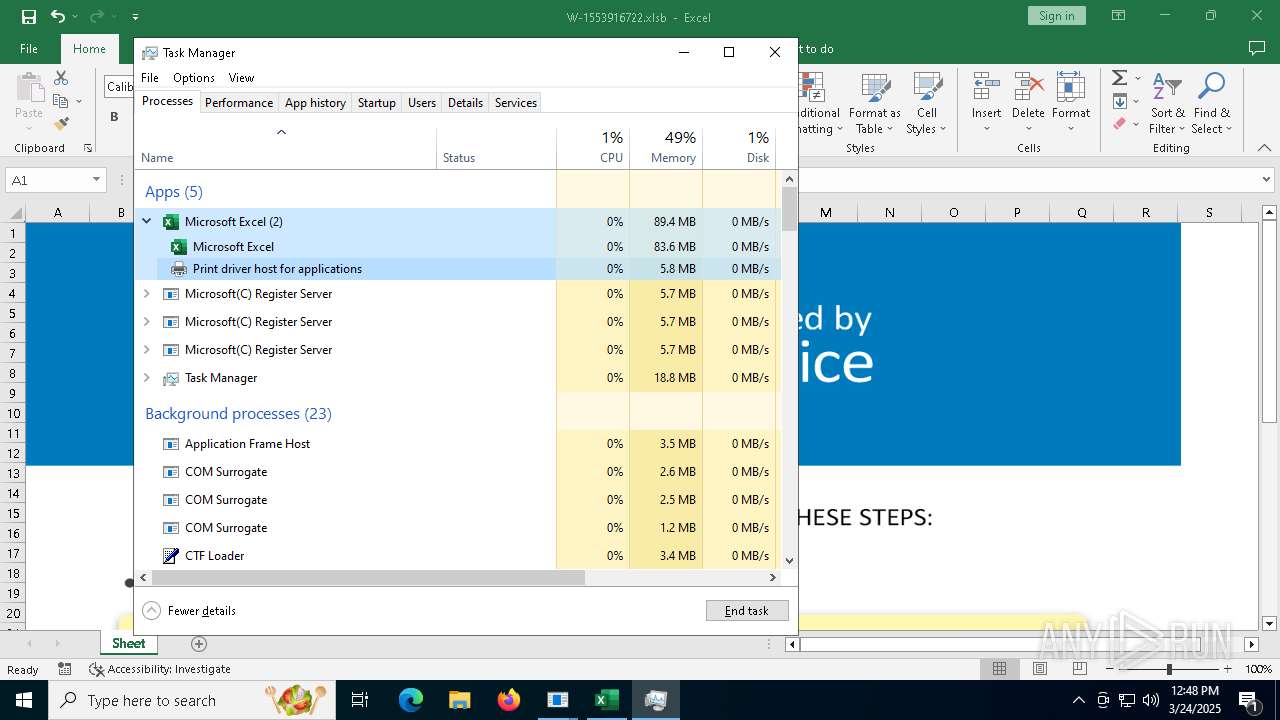
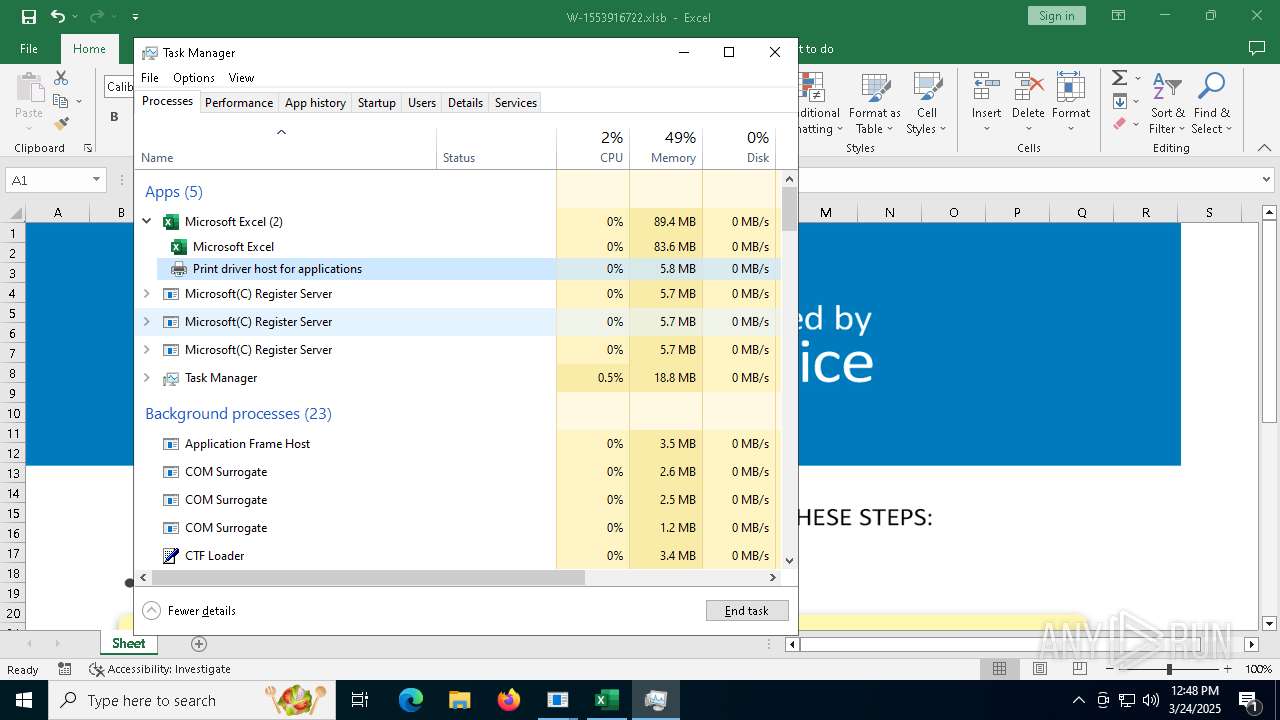
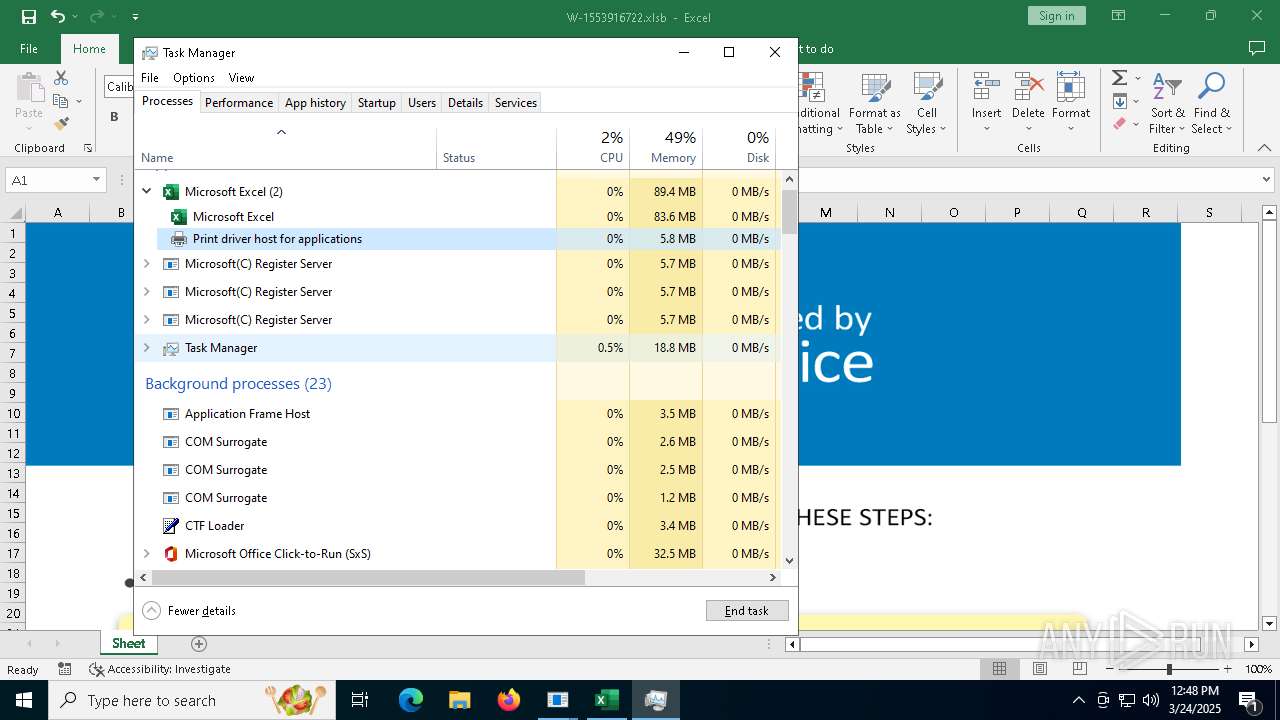
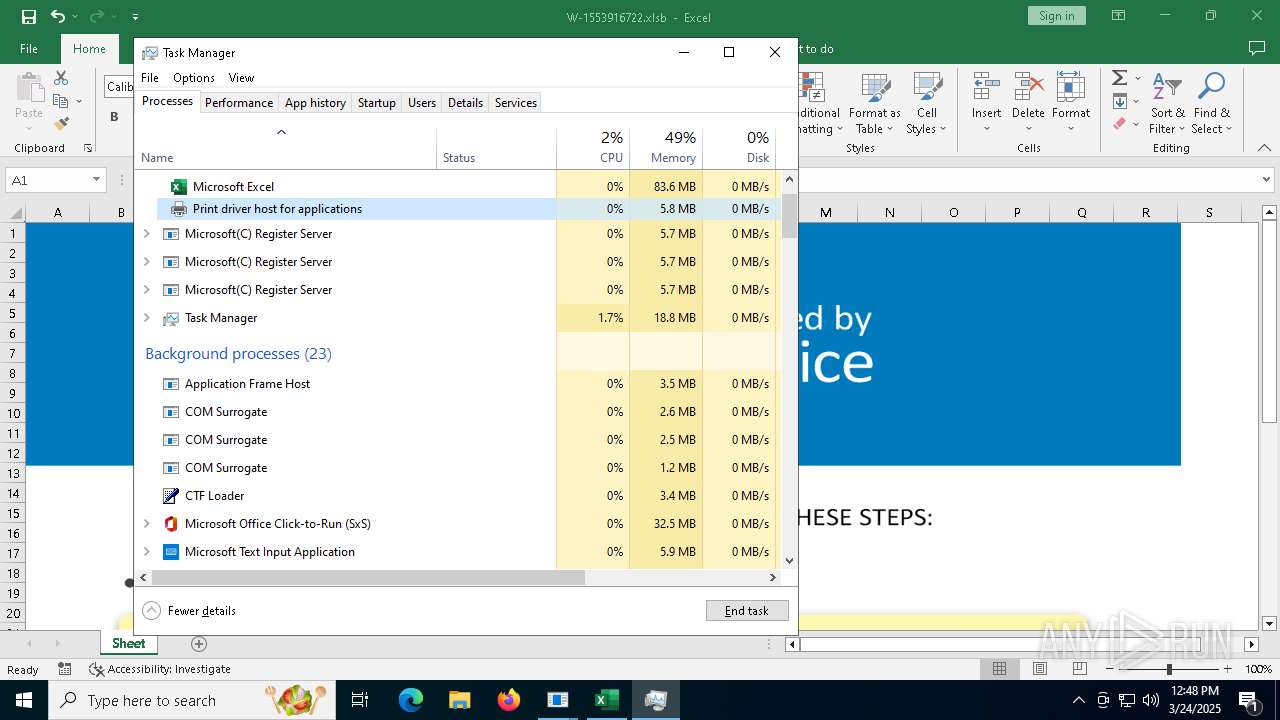
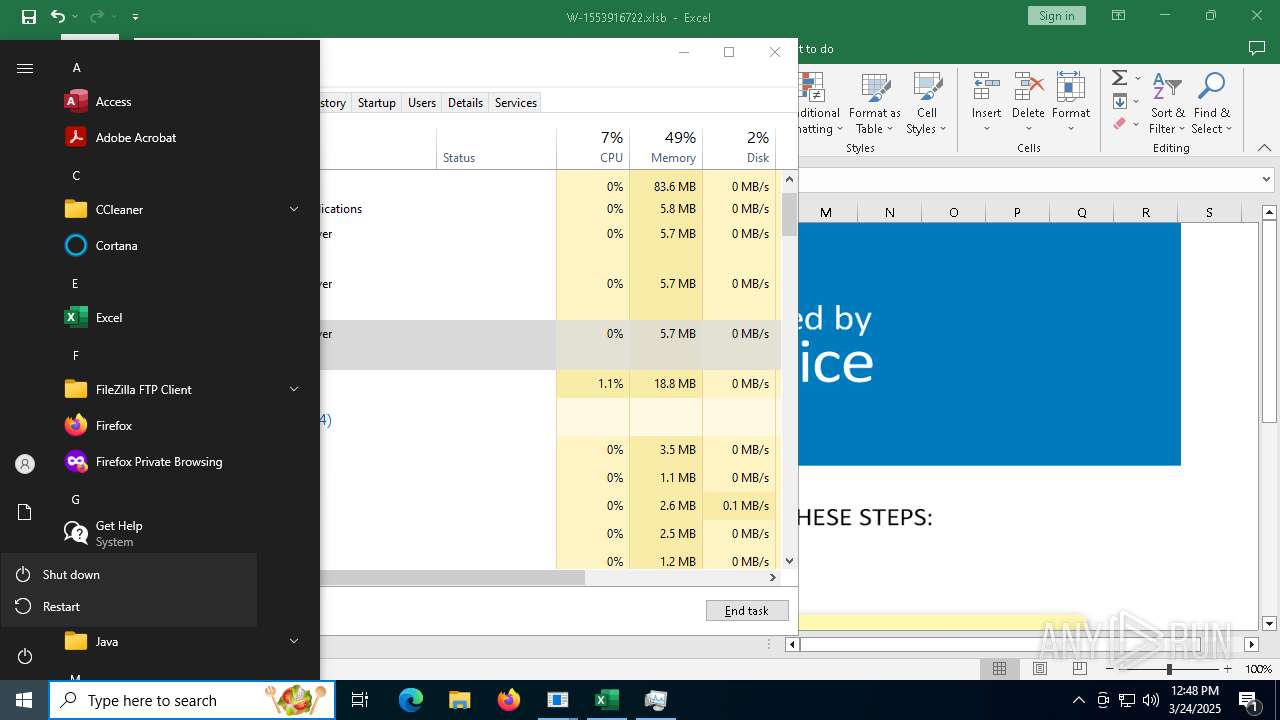
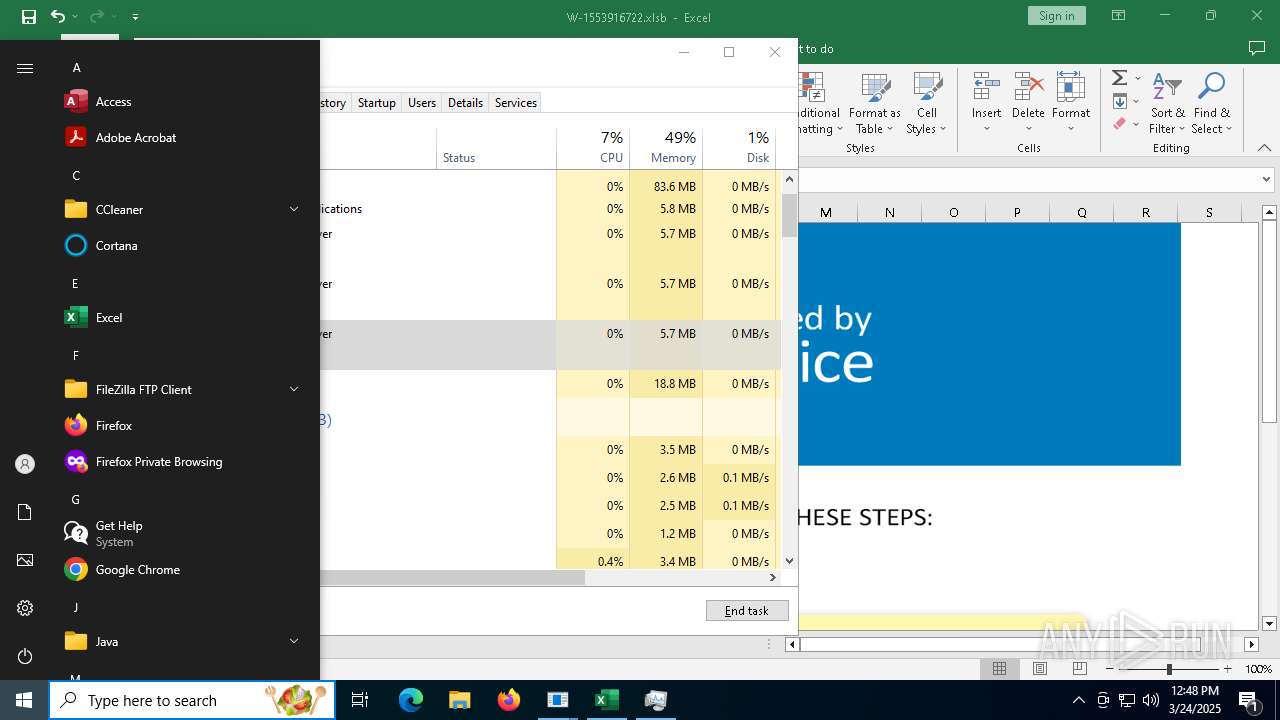
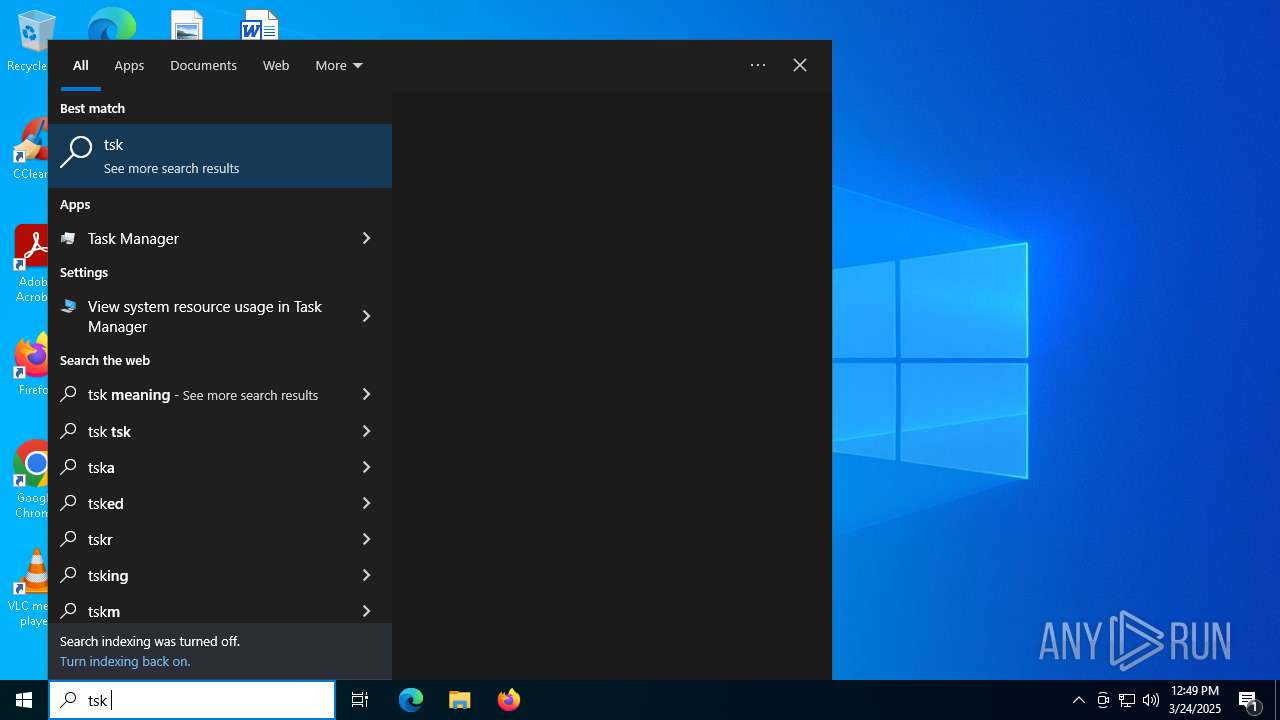
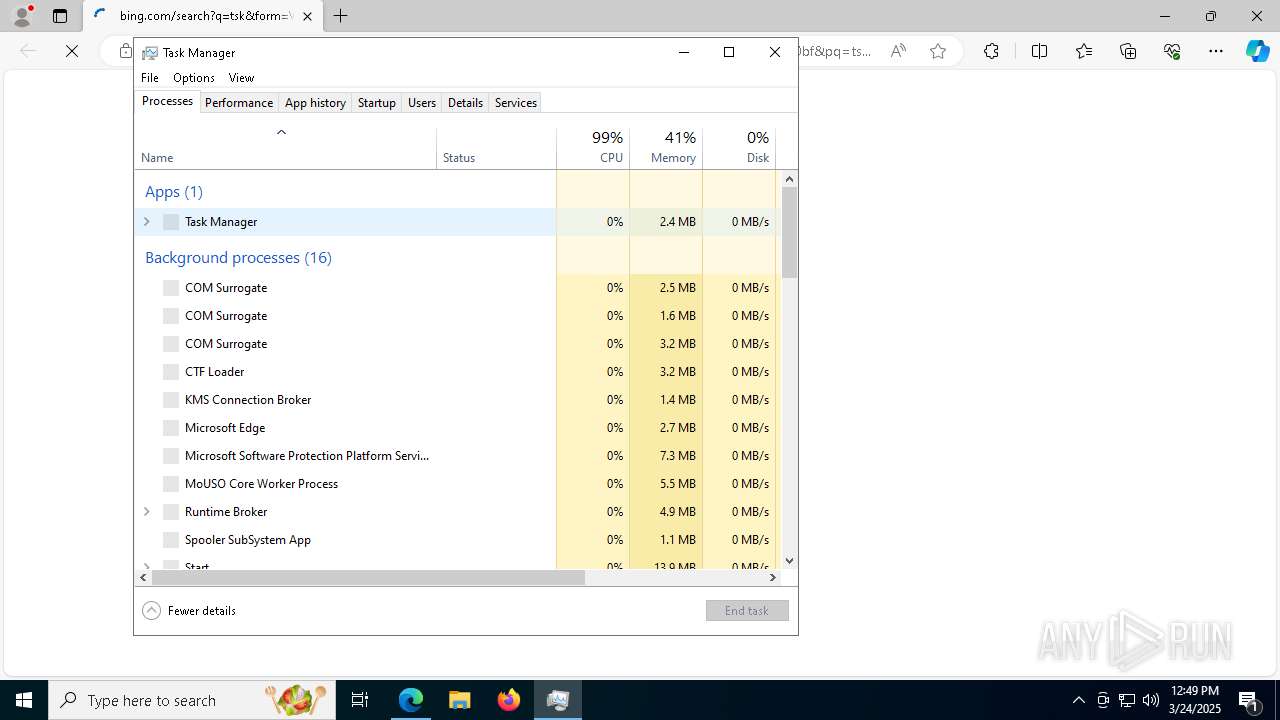
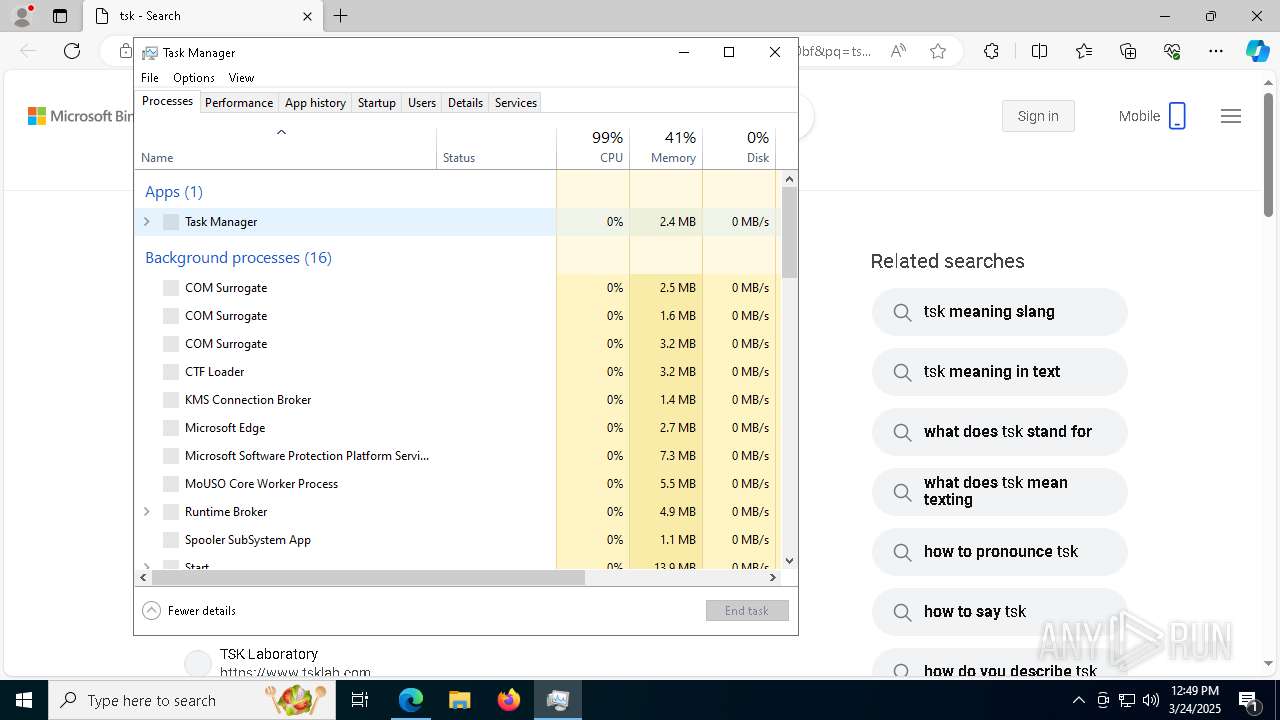
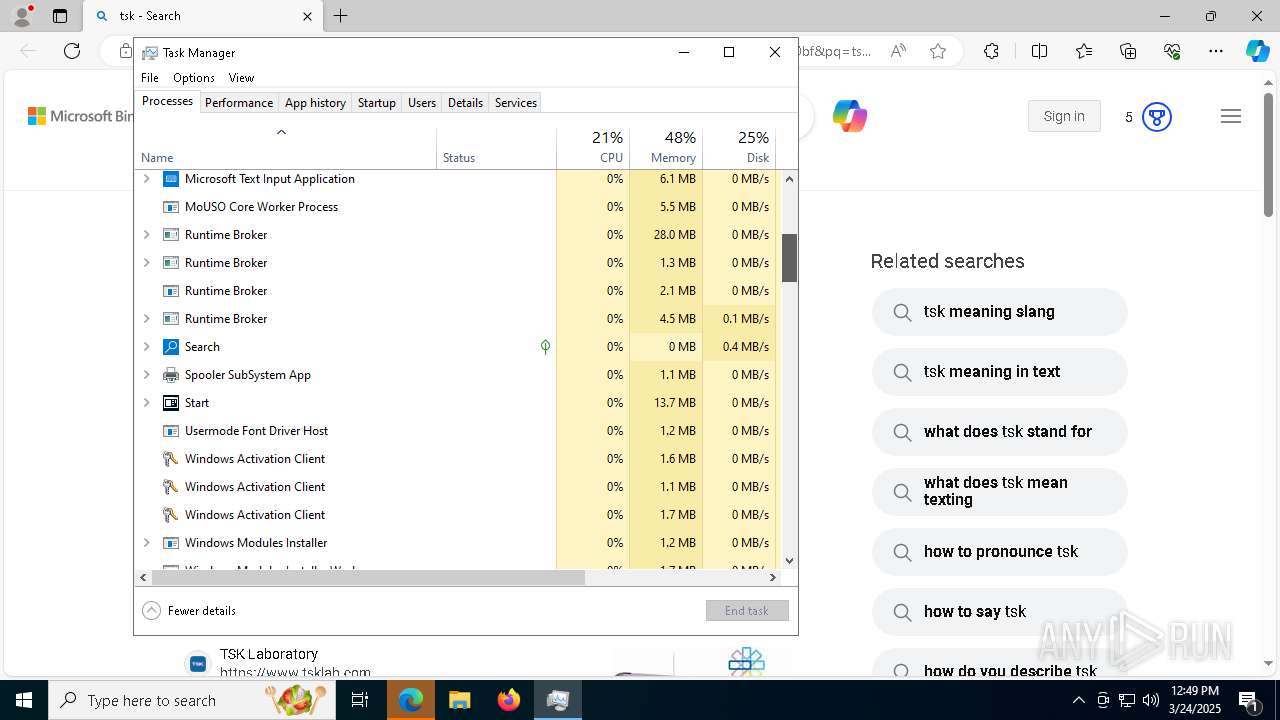
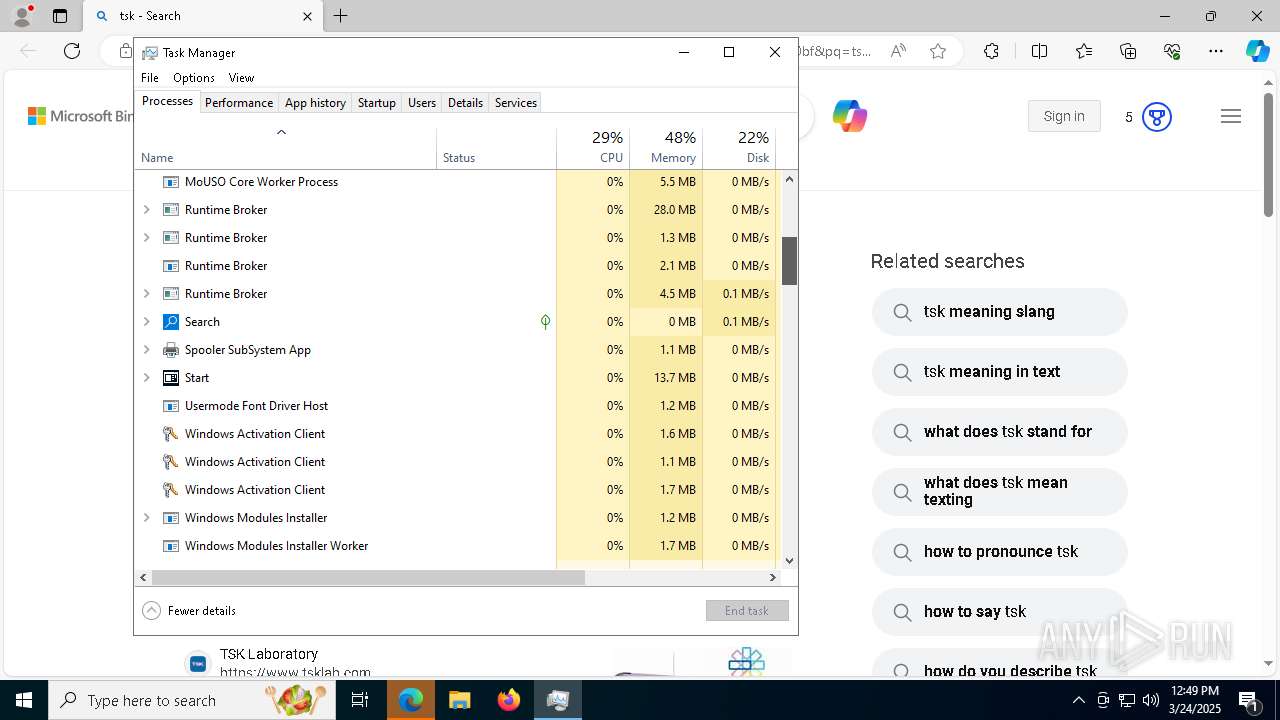
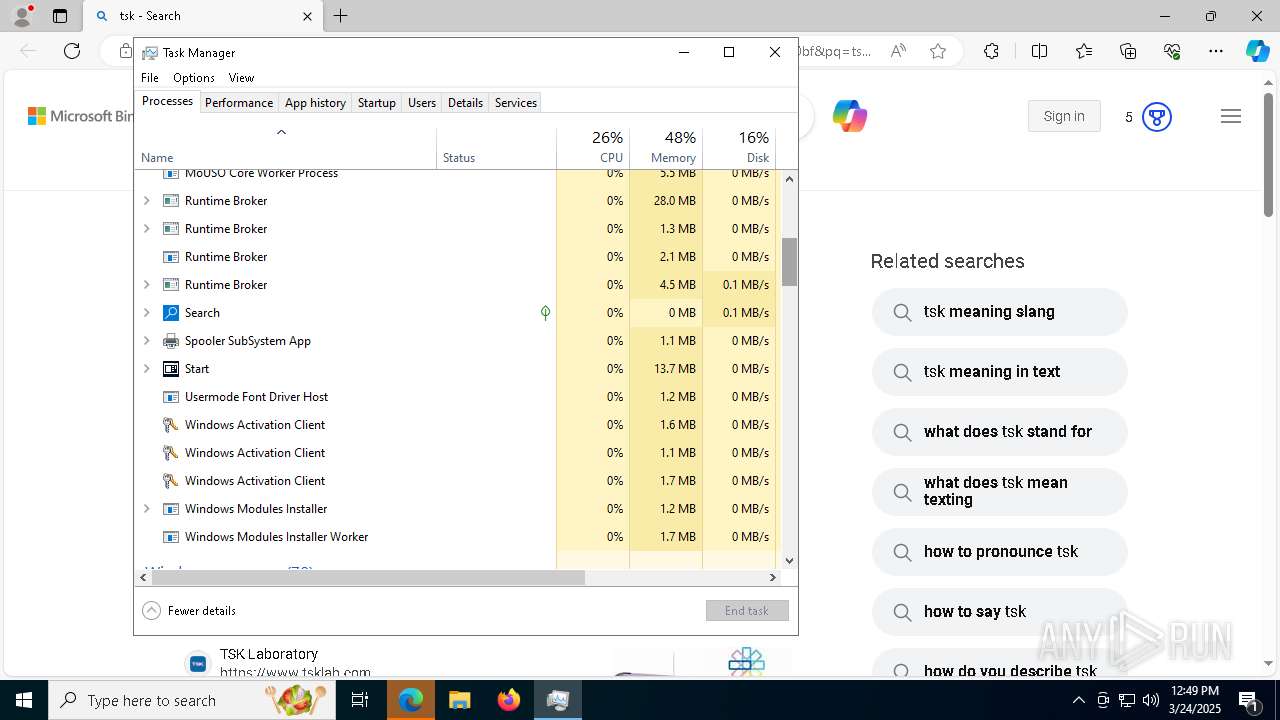
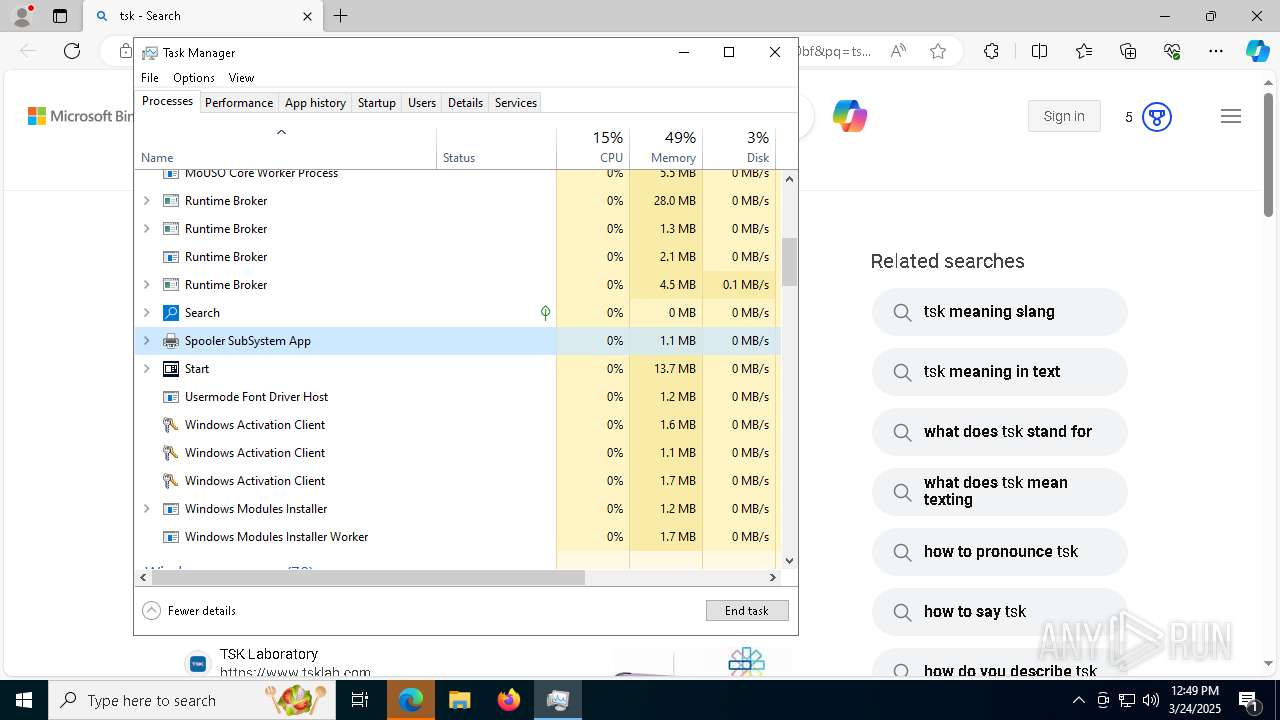
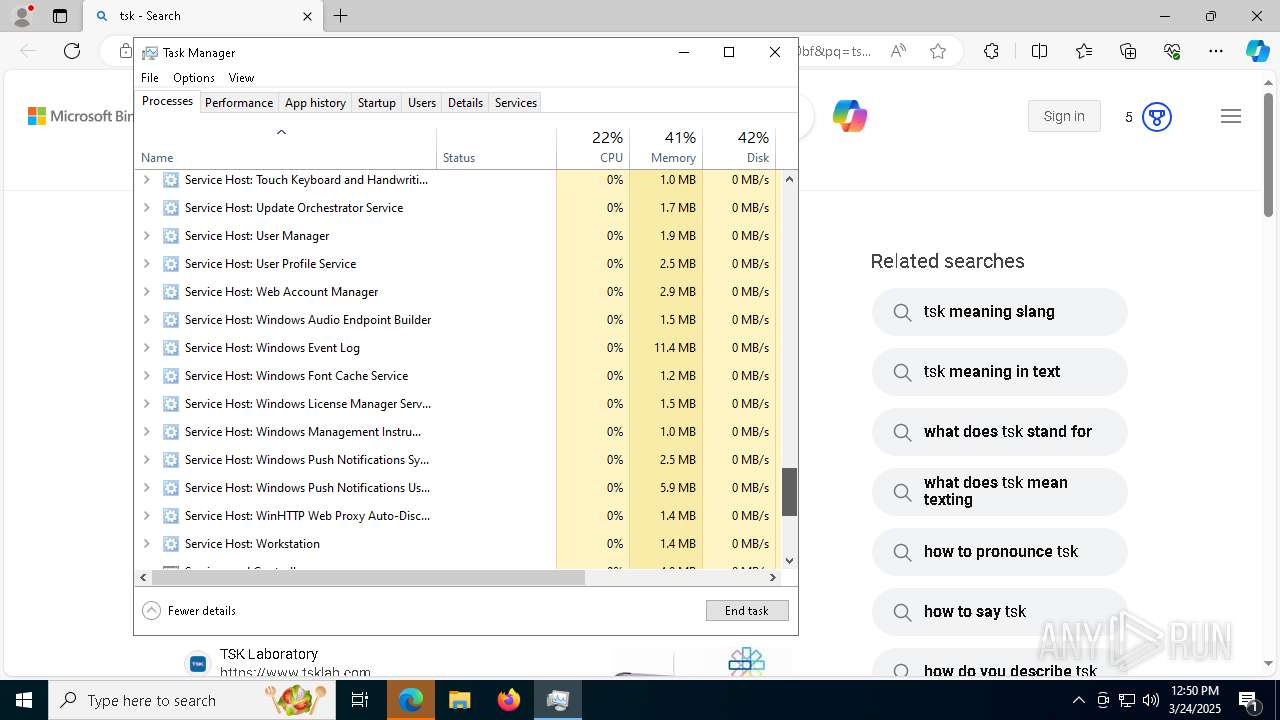
Manual execution by a user
- Taskmgr.exe (PID: 6868)
- Taskmgr.exe (PID: 6688)
- Taskmgr.exe (PID: 4880)
- Taskmgr.exe (PID: 1676)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlsx | | | Excel Microsoft Office Open XML Format document (61.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (31.5) |
| .zip | | | ZIP compressed archive (7.2) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x2a5ef837 |
| ZipCompressedSize: | 702 |
| ZipUncompressedSize: | 5214 |
| ZipFileName: | [Content_Types].xml |
XML
| Application: | Microsoft Excel |
|---|---|
| DocSecurity: | None |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: |
|
| Company: | - |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16.03 |
| LastModifiedBy: | RHfdh |
| CreateDate: | 2015:06:05 18:19:34Z |
| ModifyDate: | 2022:04:13 08:02:18Z |
XMP
| Creator: | Posik |
|---|
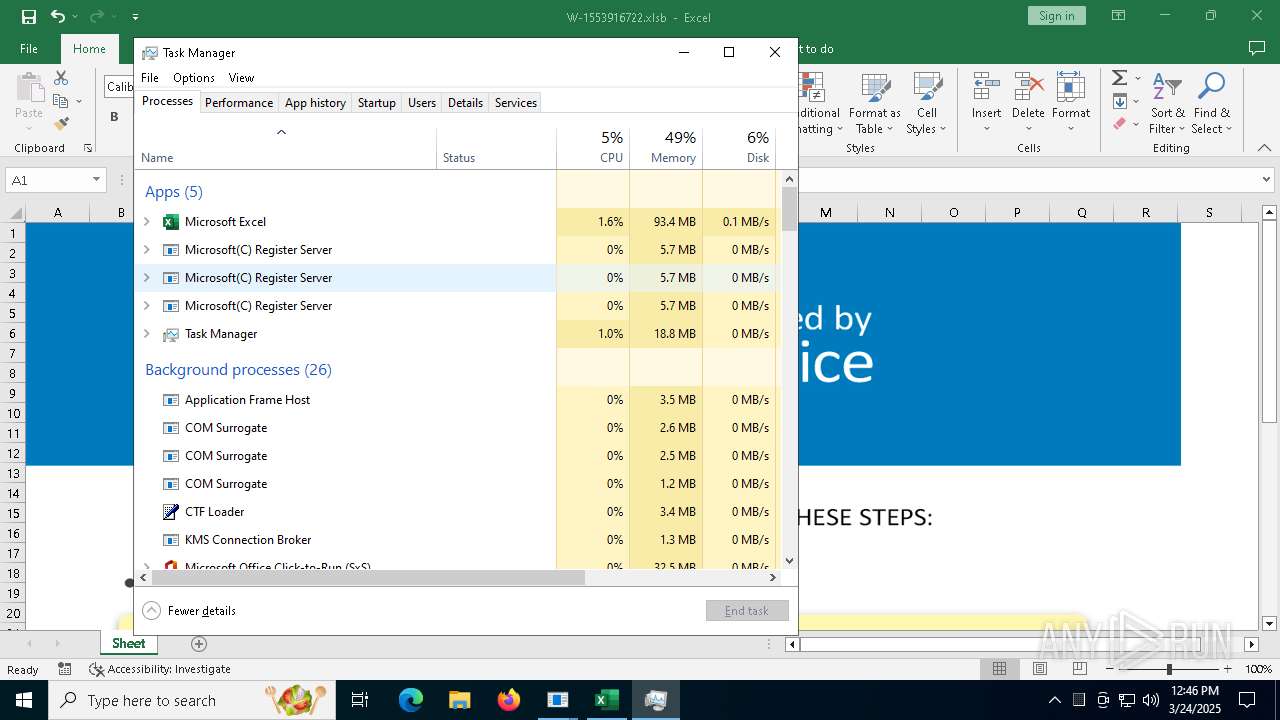
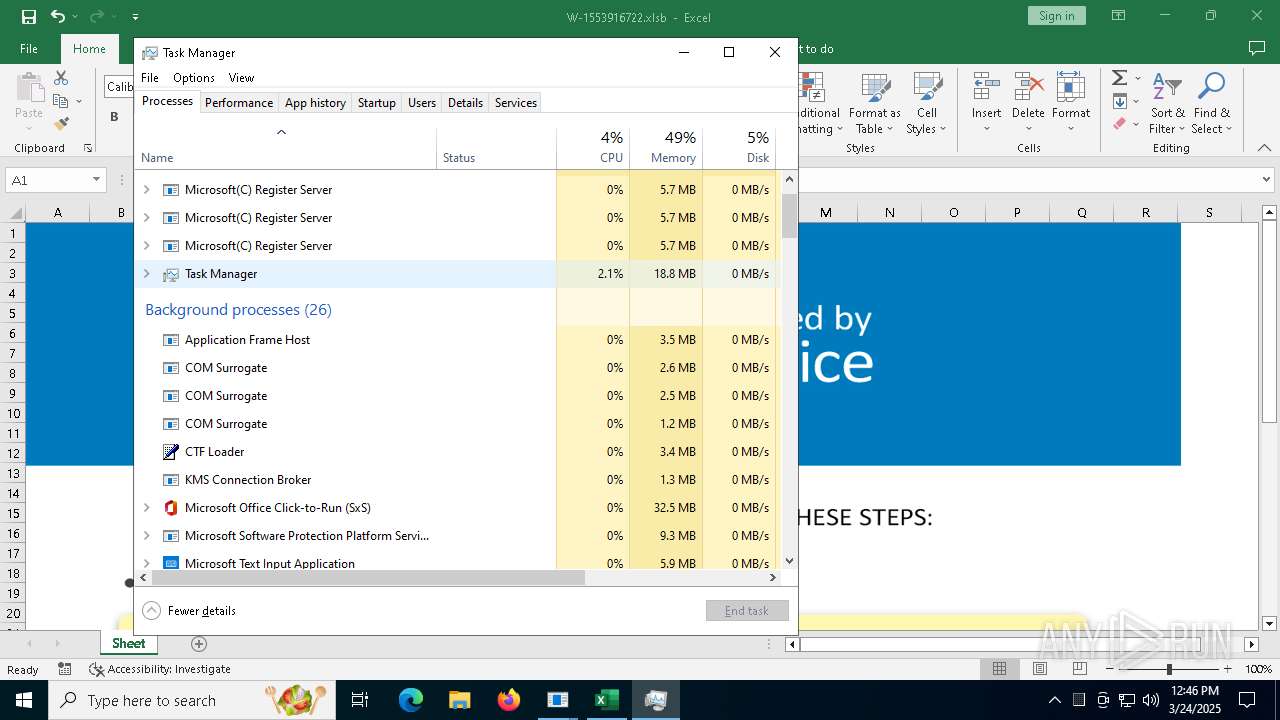
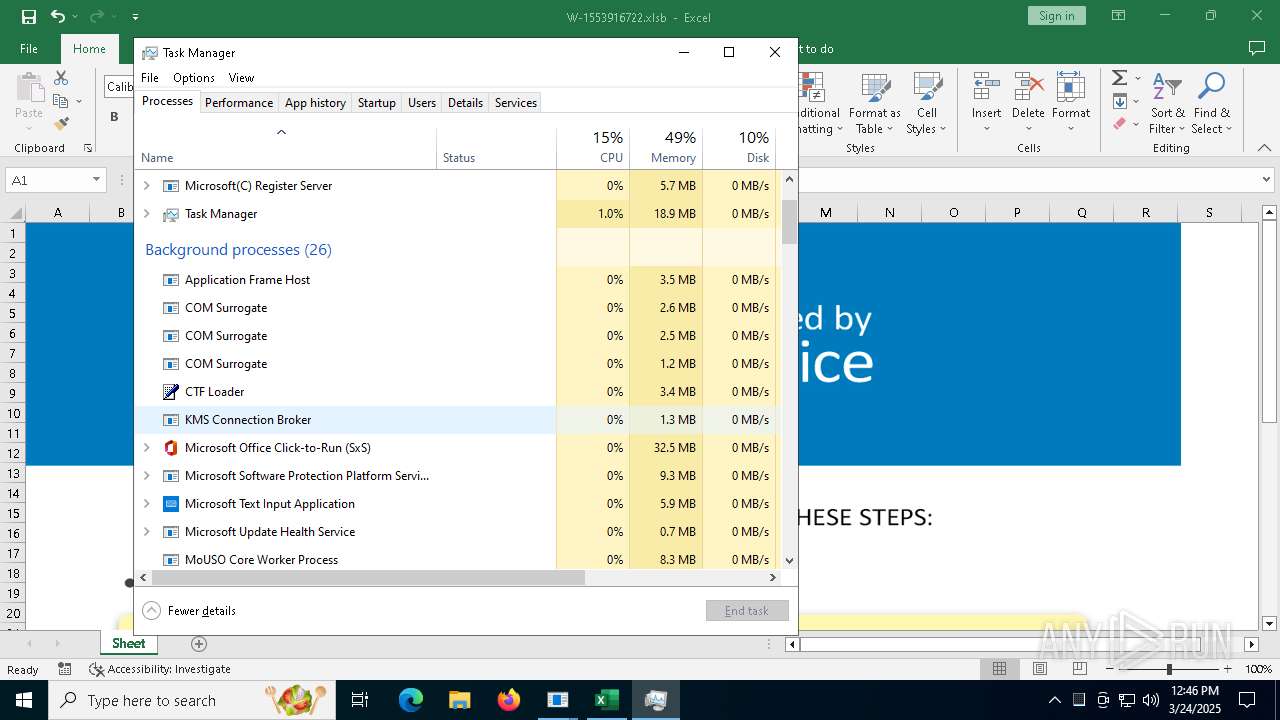
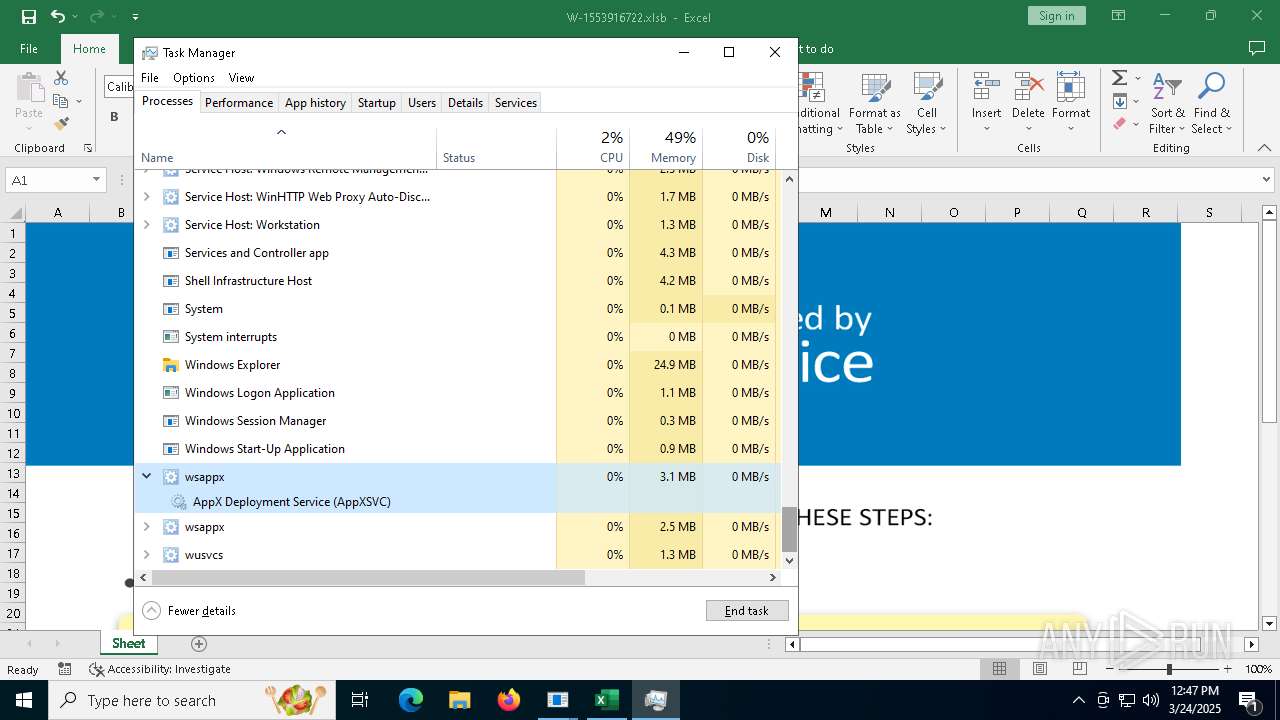
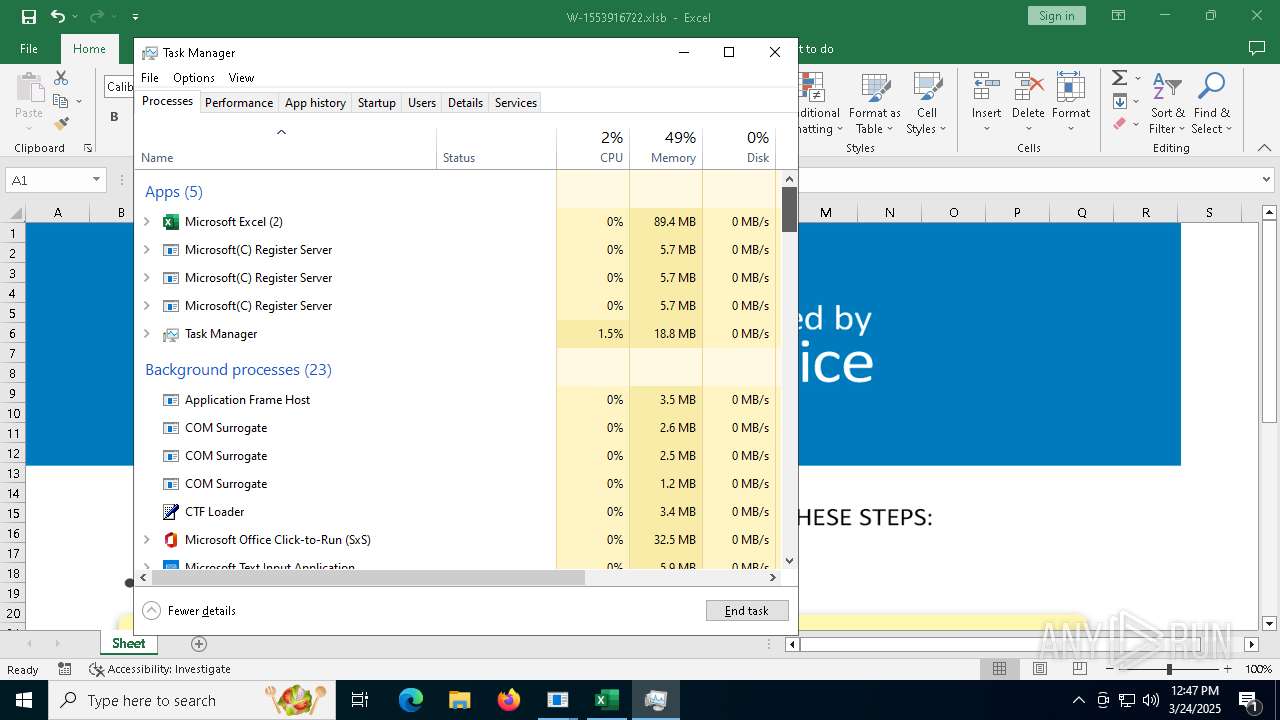
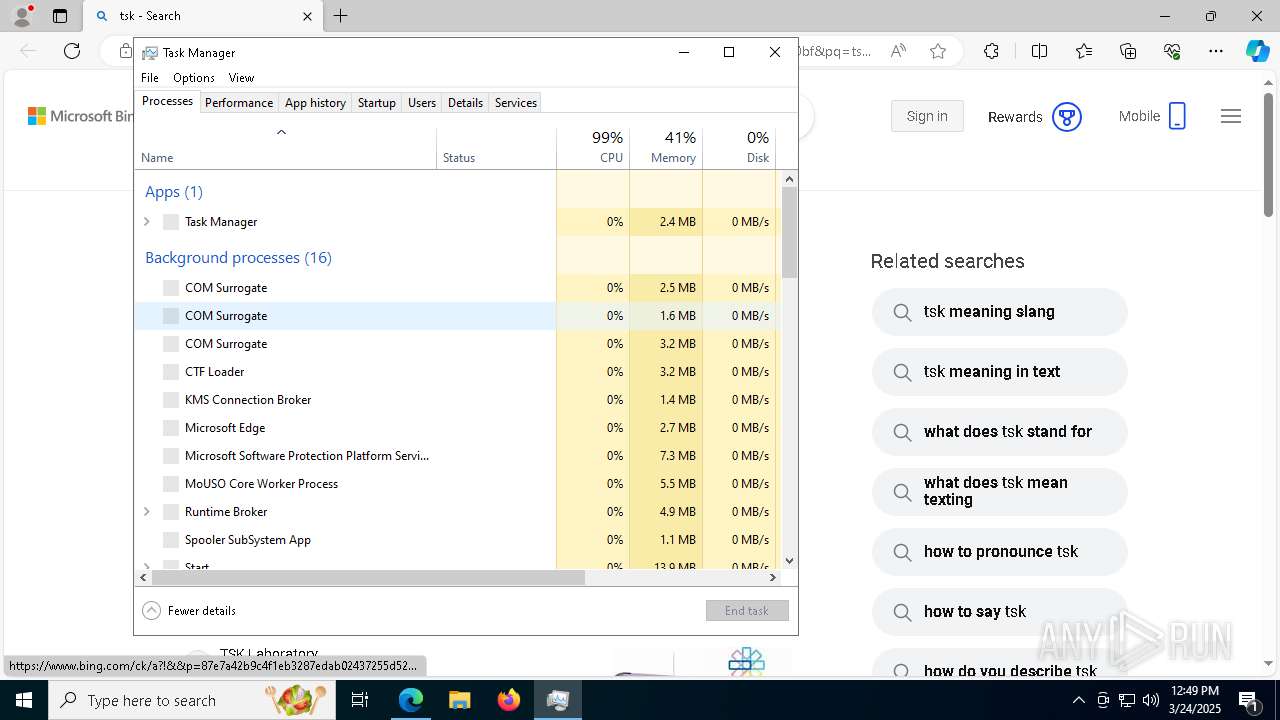
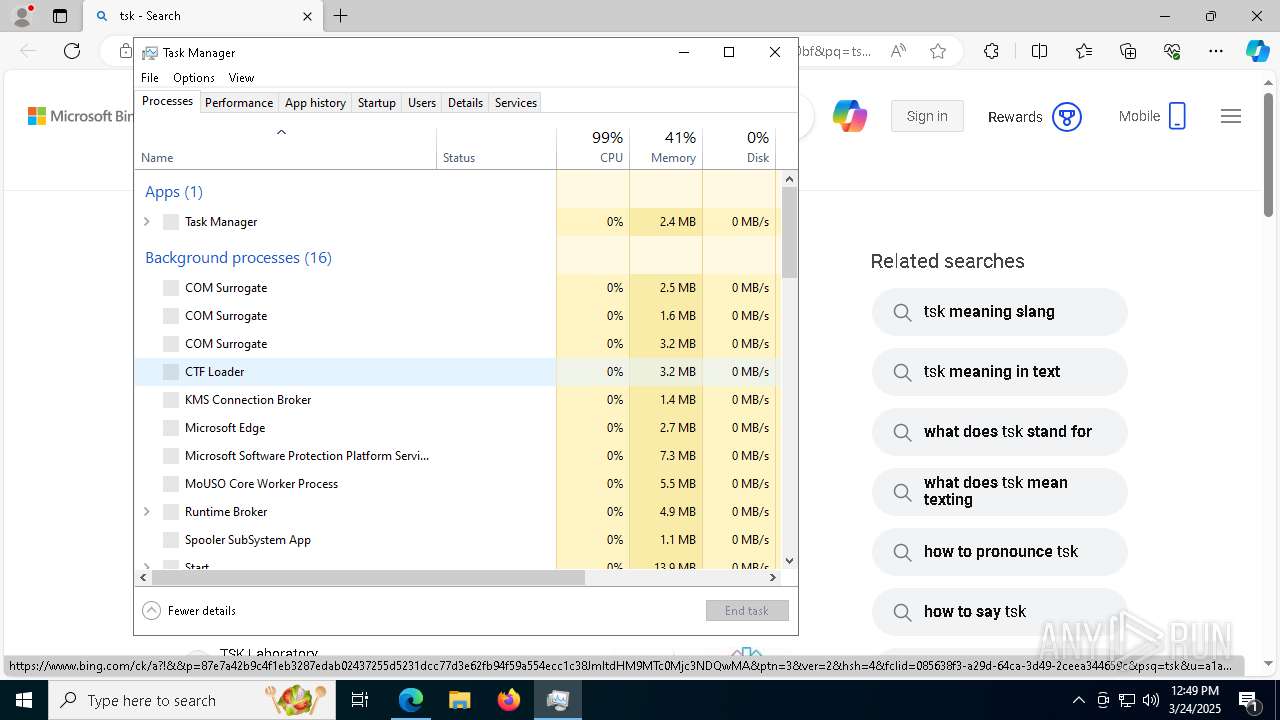
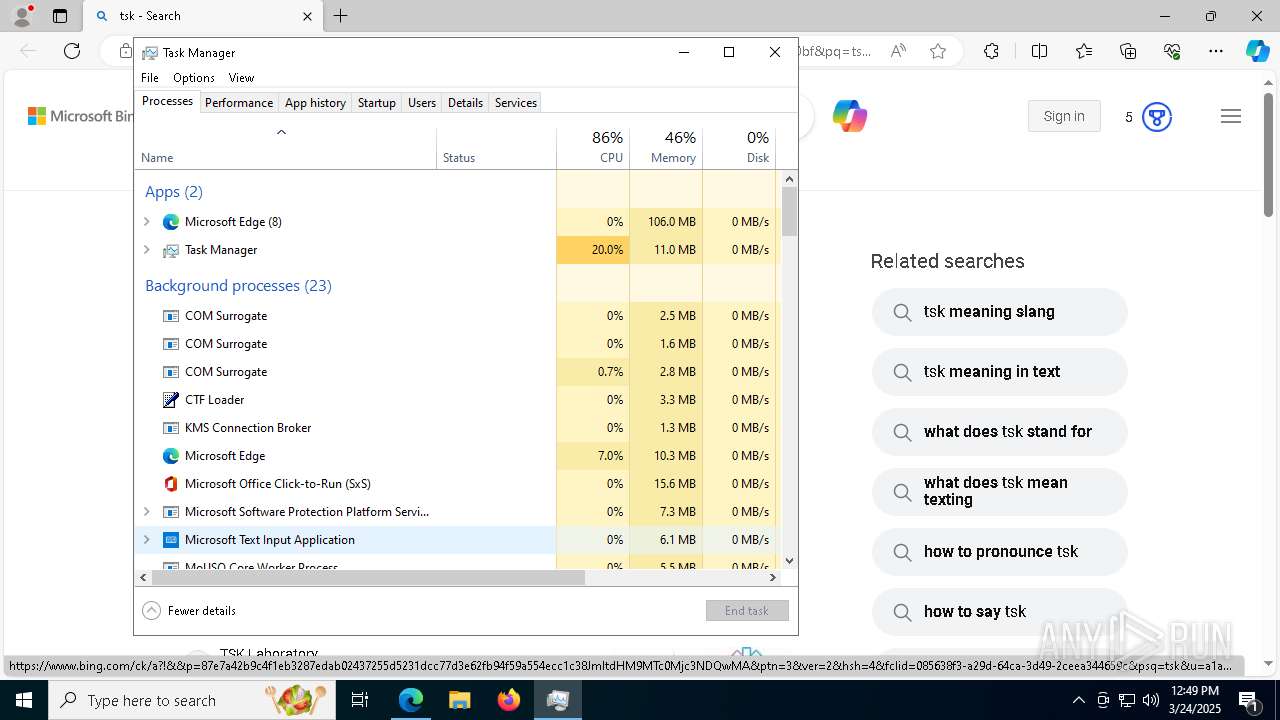
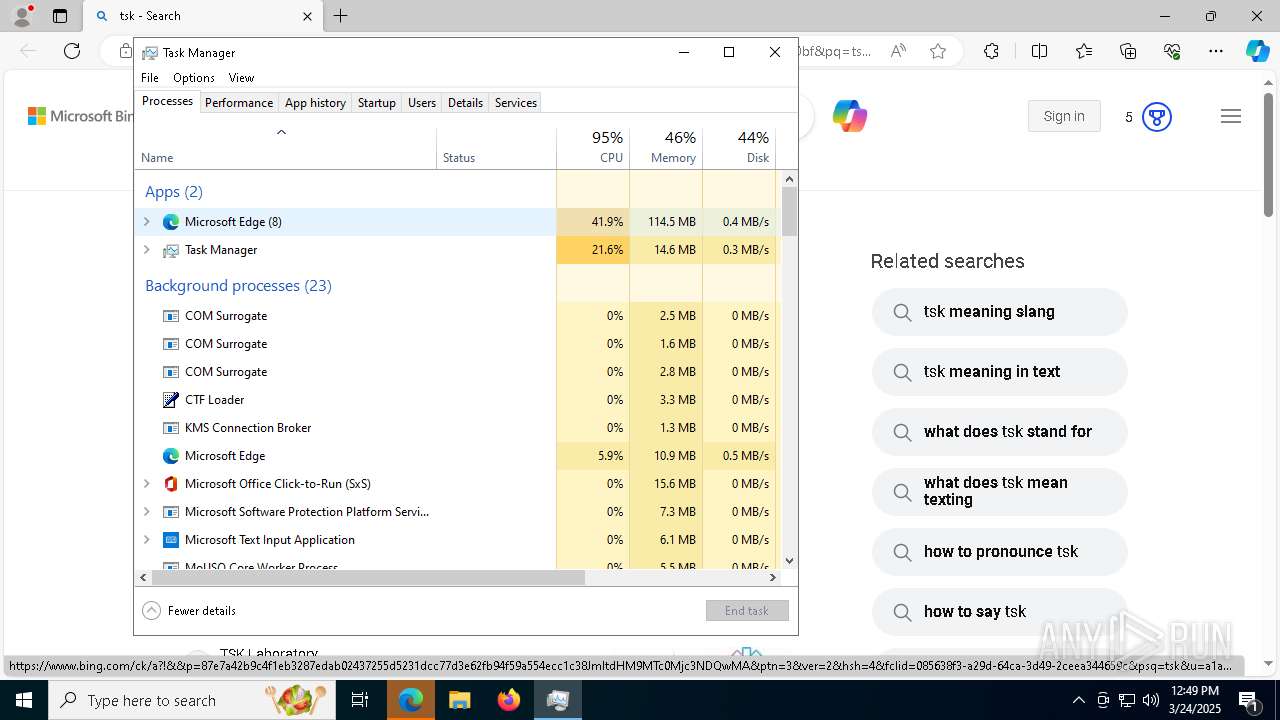
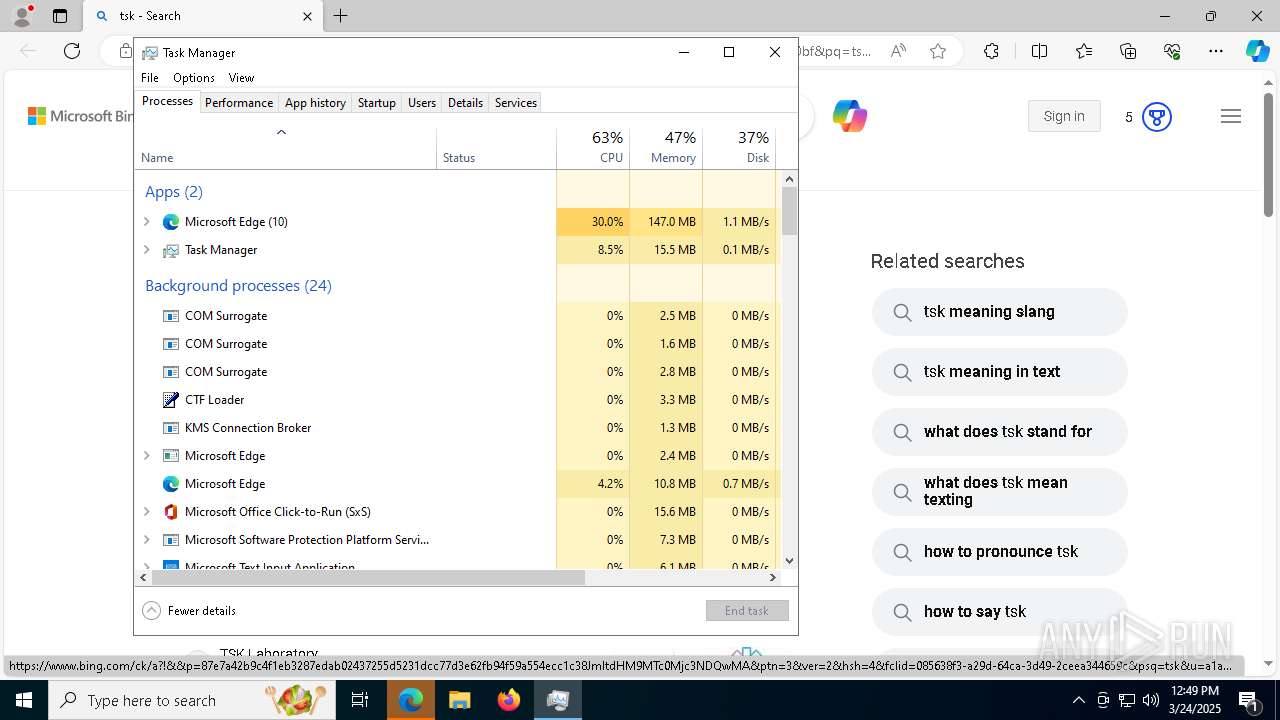
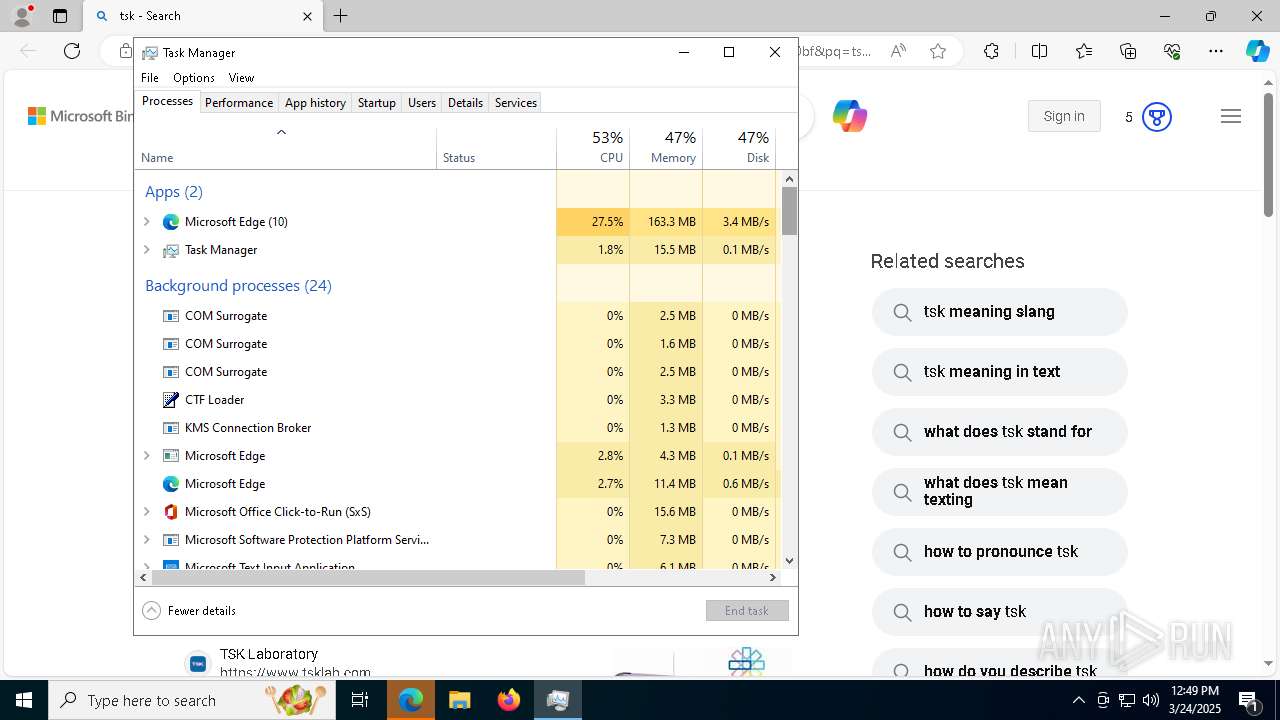
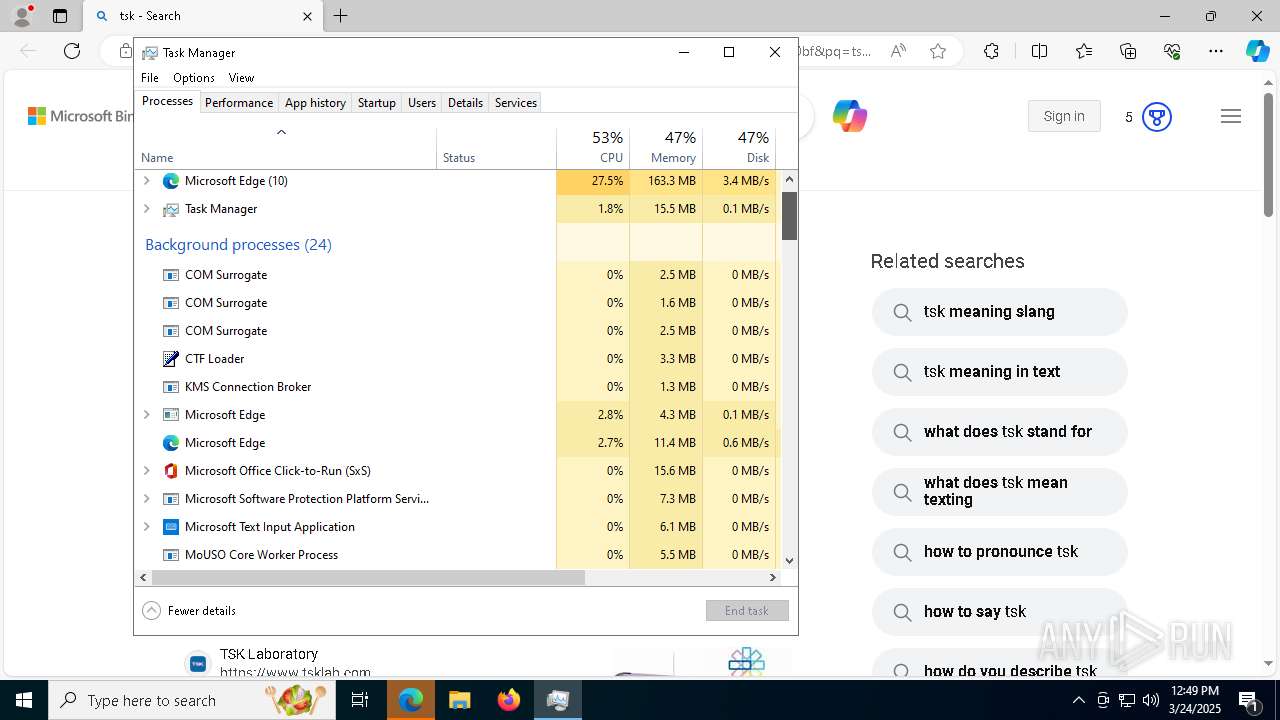
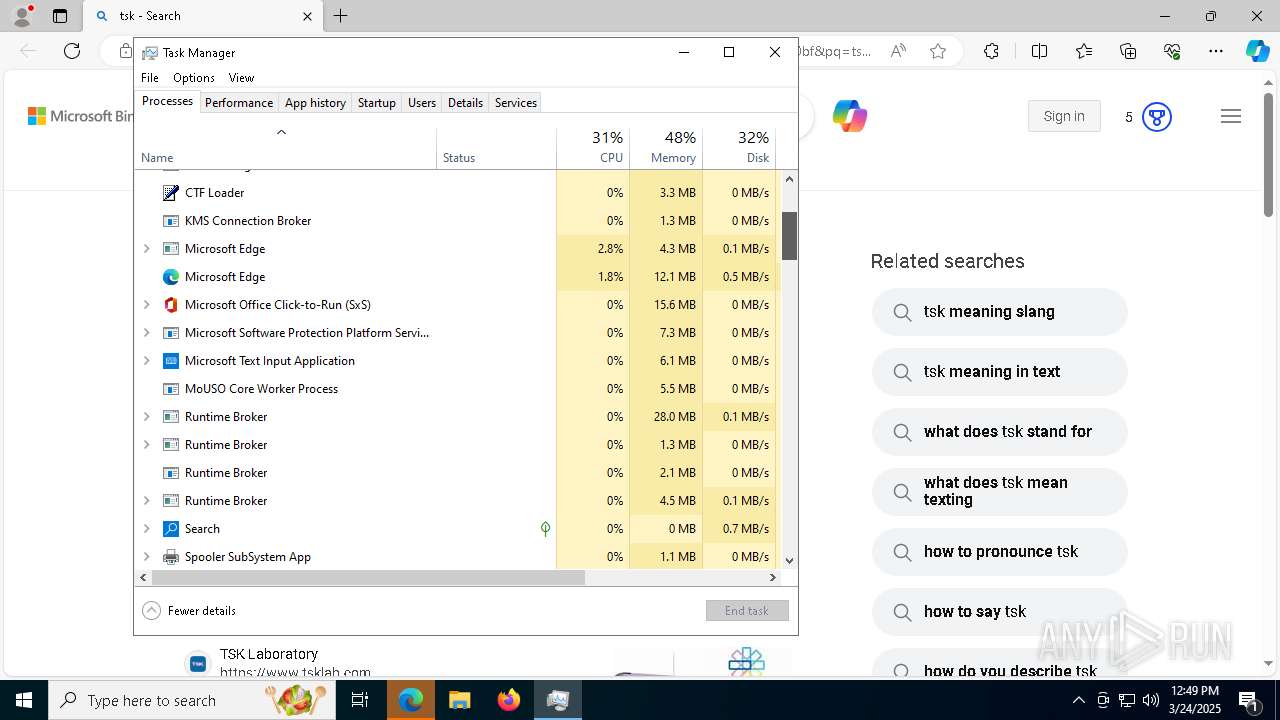
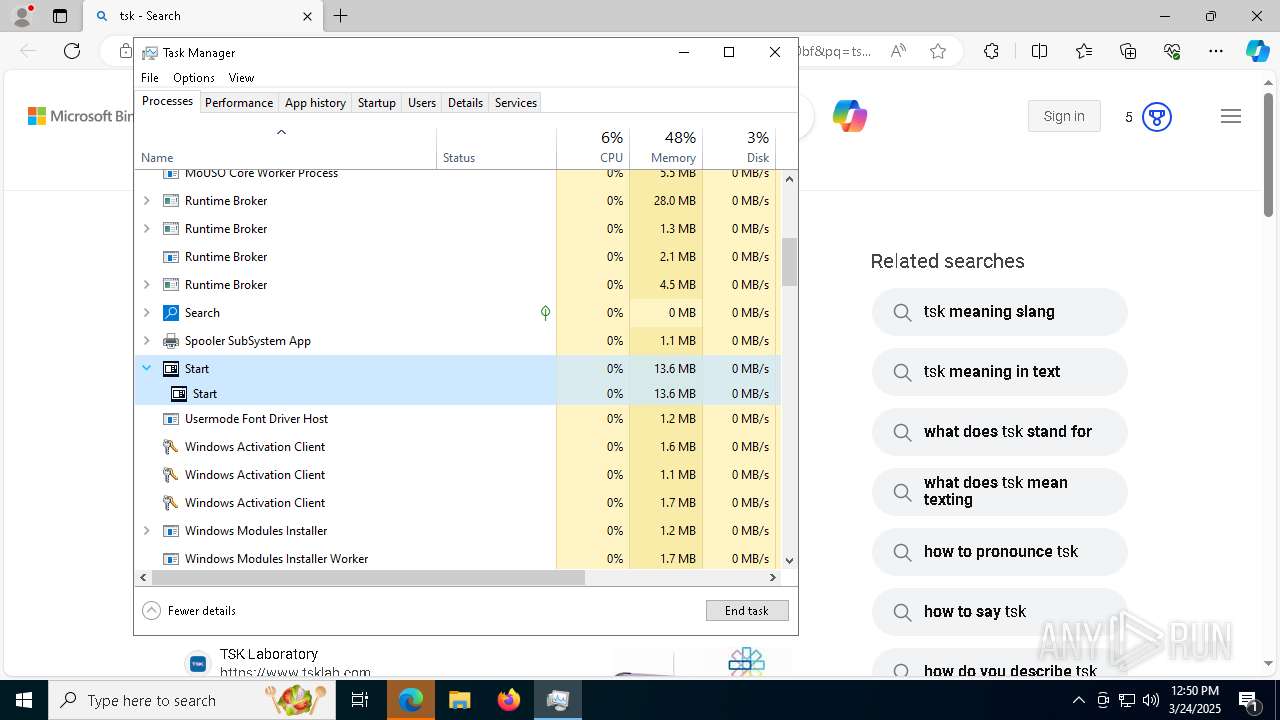
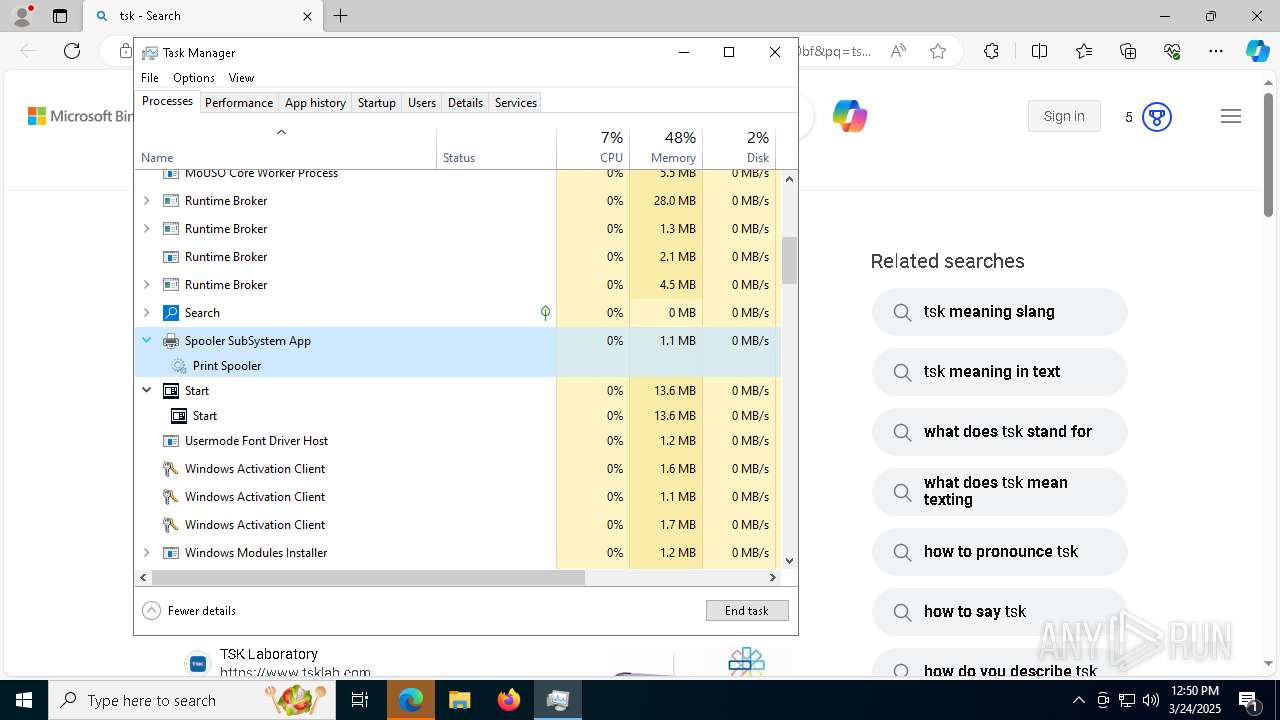
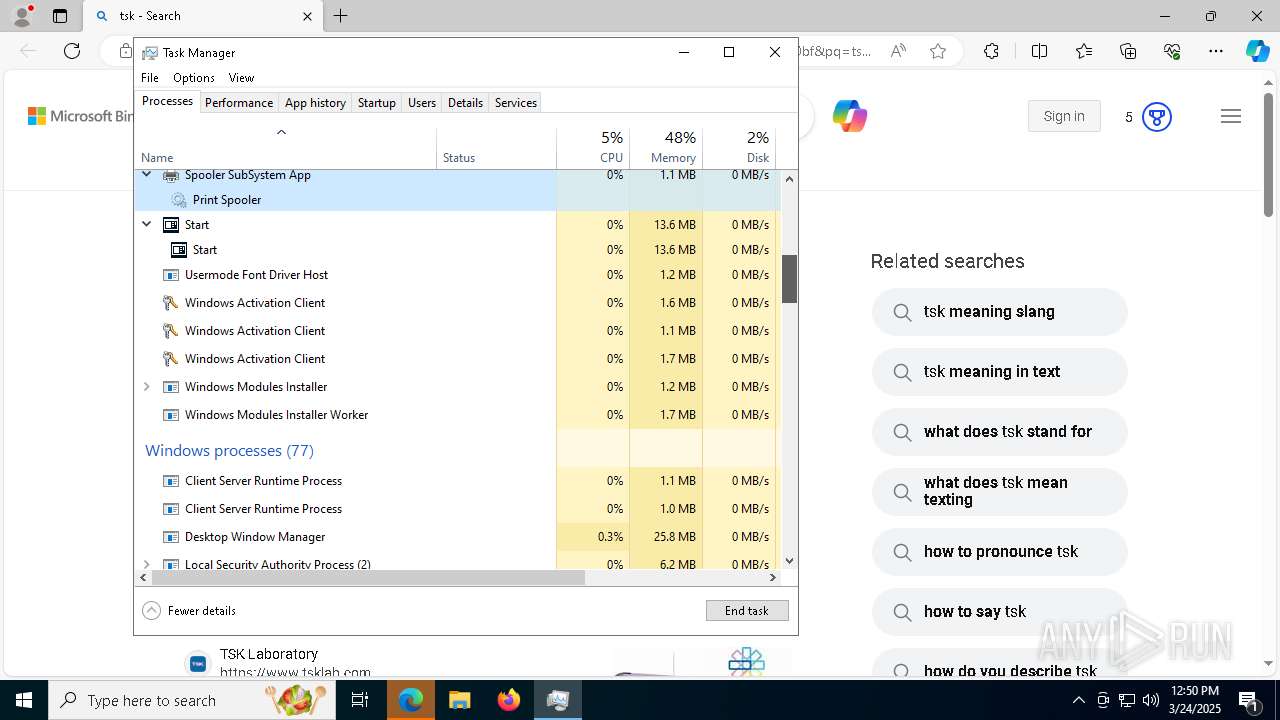
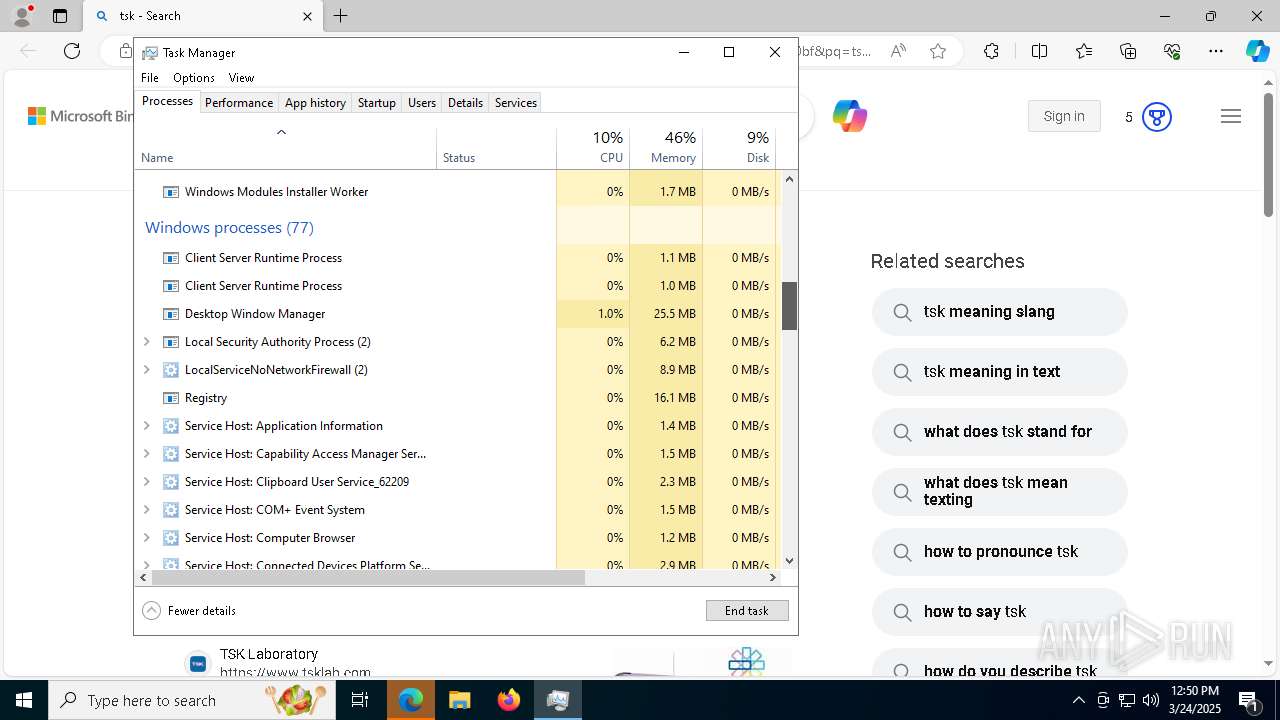
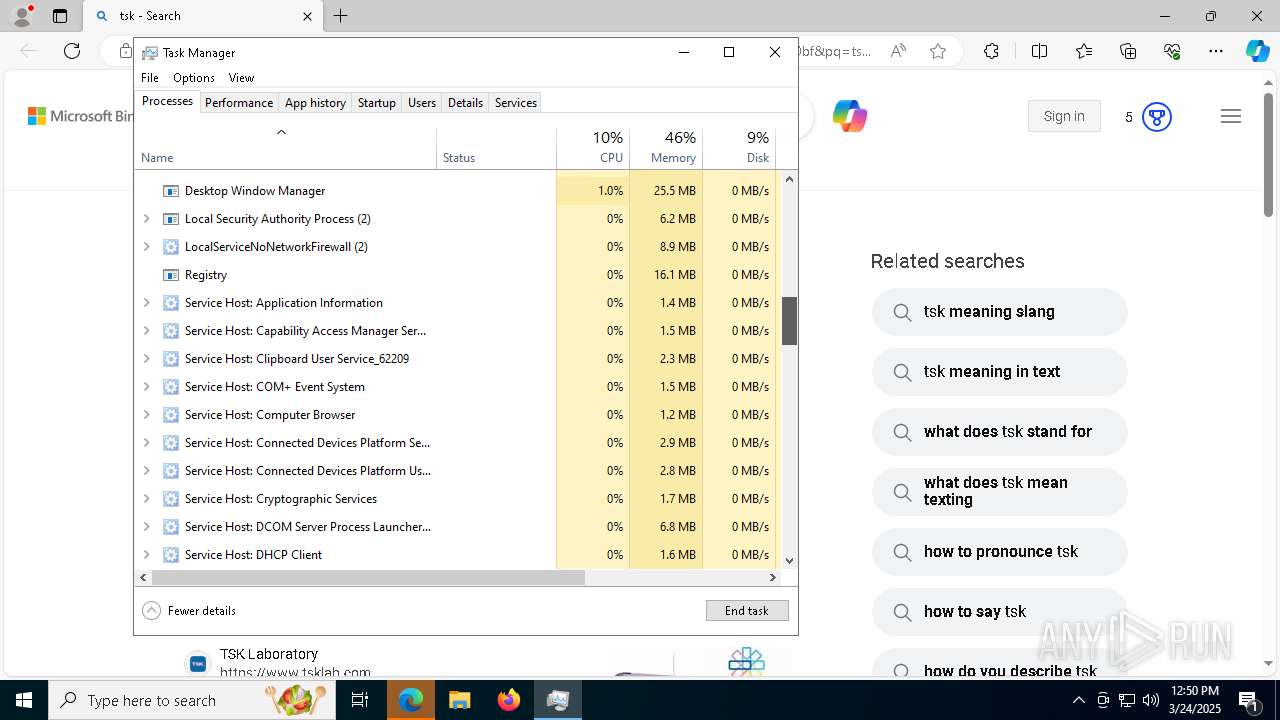
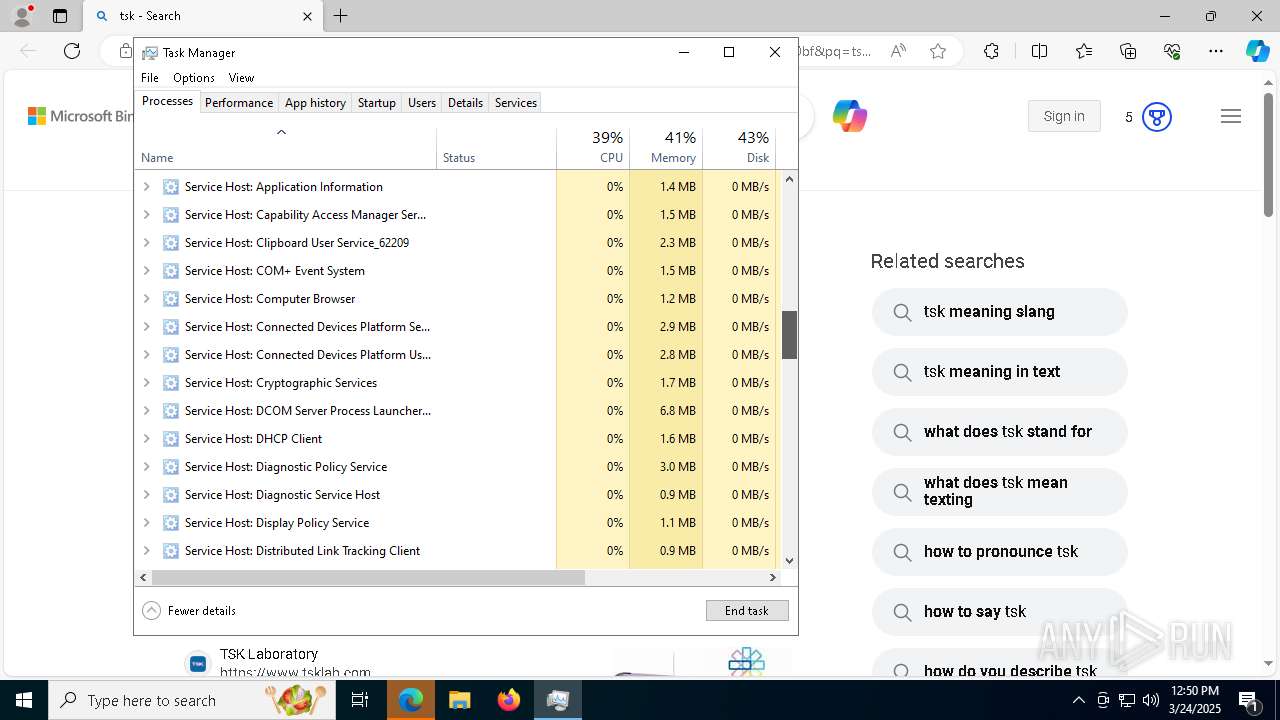
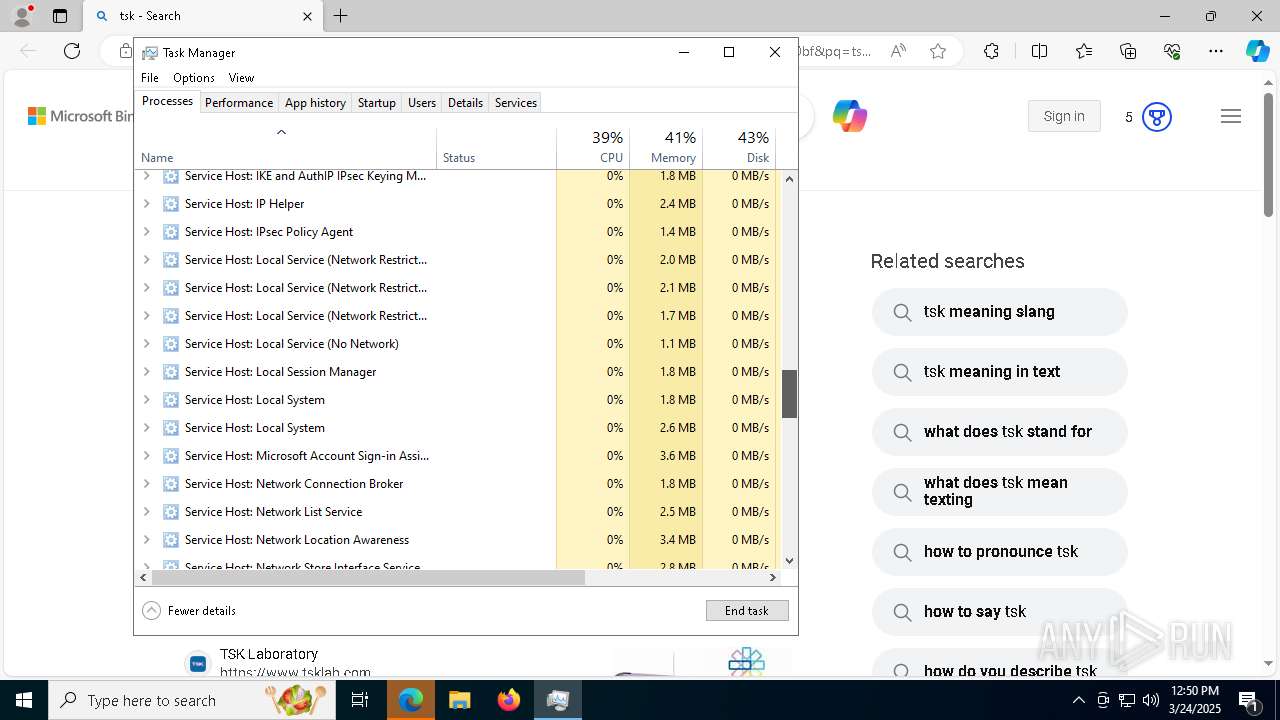
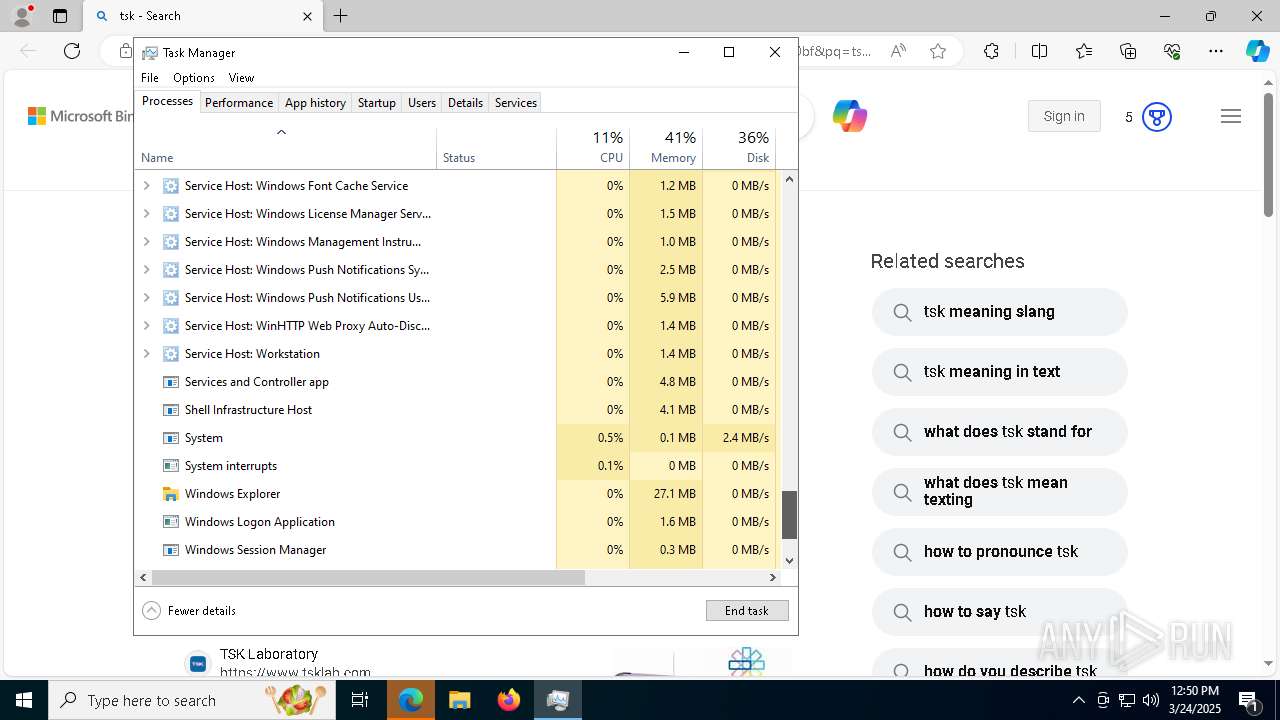
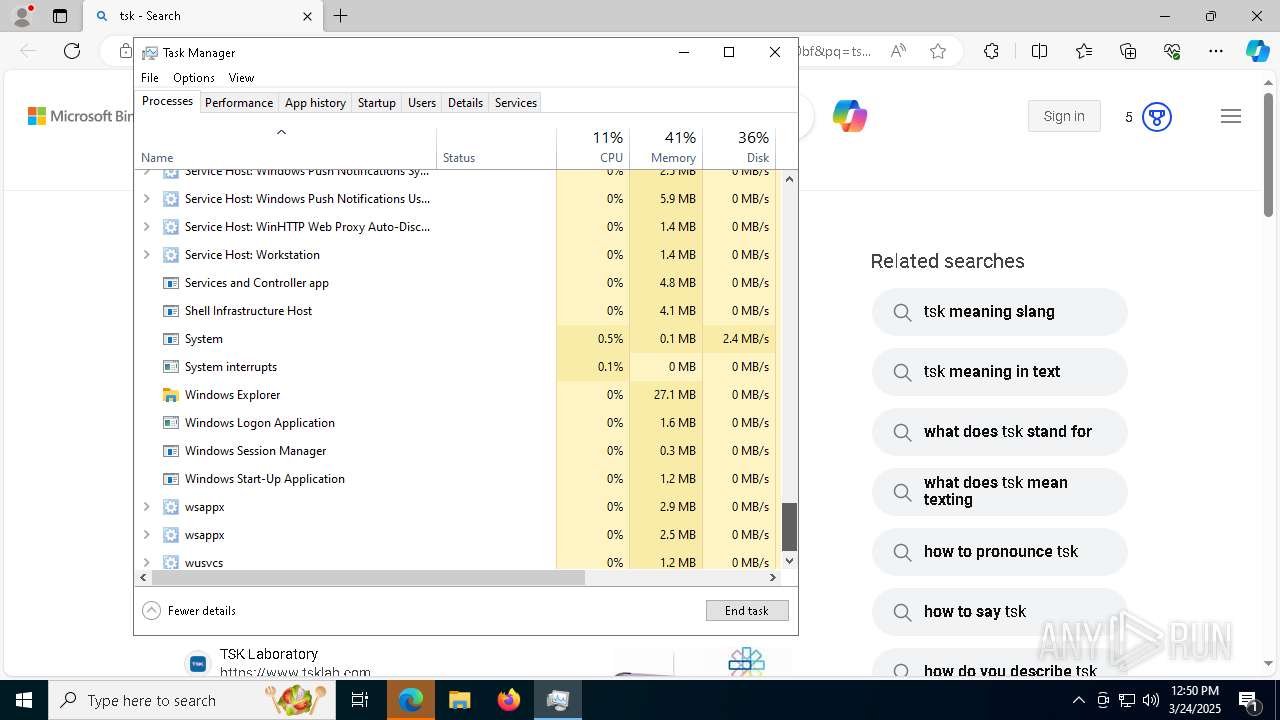
Total processes
322
Monitored processes
19
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1676 | "C:\WINDOWS\system32\taskmgr.exe" /7 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2108 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4176 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4180 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4880 | "C:\WINDOWS\system32\taskmgr.exe" /7 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5776 | C:\WINDOWS\splwow64.exe 8192 | C:\Windows\splwow64.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Print driver host for applications Exit code: 1073807364 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6644 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6688 | "C:\WINDOWS\system32\taskmgr.exe" /7 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6868 | "C:\WINDOWS\system32\taskmgr.exe" /7 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7408 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 268
Read events
13 973
Write events
265
Delete events
30
Modification events
| (PID) Process: | (7472) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | f5. |
Value: 66352E00301D000001000000000000009816CF9DBA9CDB0100000000 | |||
| (PID) Process: | (7472) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Excel |
| Operation: | write | Name: | ImmersiveWorkbookDirtySentinel |
Value: 0 | |||
| (PID) Process: | (7472) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Excel |
| Operation: | write | Name: | ExcelPreviousSessionId |
Value: {575B9DAF-E222-4A3C-BA44-4615E48D9023} | |||
| (PID) Process: | (7472) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Excel |
| Operation: | write | Name: | FontInfoCache |
Value: 6000000060000000F5FFFFFF0000000000000000000000009001000000000000000000205400610068006F006D00610000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000050000001B000000000000000D0000000B000000020000000200000000000000330000000000000000000000F5FFFFFF0000000000000000000000009001000000000000000000205300650067006F006500200055004900000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000060000001C000000000000000D0000000B000000020000000200000000000000330000000000000000000000F5FFFFFF000000000000000000000000BC02000000000000000000205400610068006F006D006100000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000600000020000000000000000D0000000B000000020000000200000000000000330000000000000000000000F3FFFFFF0000000000000000000000009001000000000000000000005400610068006F006D00610000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000060000002000000000000000100000000D000000030000000300000000000000330000000000000000000000F3FFFFFF000000000000000000000000E803000000000000000000005400610068006F006D00610000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000070000002600000000000000100000000D000000030000000300000000000000330000000000000000000000F1FFFFFF000000000000000000000000900100000000000000000000430061006C0069006200720069000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000080000001A00000000000000120000000E000000040000000300000000000000330000000000000000000000F3FFFFFF0000000000000000000000009001000000000000000000005300650067006F006500200055004900000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000070000002100000000000000110000000E000000030000000400000000000000330000000000000000000000F3FFFFFF000000000000000000000000BC02000000000000000000005300650067006F006500200055004900000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000080000002100000000000000110000000E000000030000000400000000000000330000000000000000000000F3FFFFFF0000000000000000000000009001000000000000000000205300650067006F006500200055004900000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000070000002100000000000000110000000E000000030000000400000000000000330000000000000000000000F3FFFFFF000000000000000000000000BC02000000000000000000205300650067006F006500200055004900000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000080000002100000000000000110000000E000000030000000400000000000000330000000000000000000000F5FFFFFF0000000000000000000000009001000000000000000000205300650067006F006500200055004900000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000060000001C000000000000000D0000000B000000020000000200000000000000330000000000000000000000F1FFFFFF000000000000000000000000900100000000000000000000430061006C0069006200720069000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000080000001A00000000000000120000000E000000040000000300000000000000330000000000000000000000F5FFFFFF0000000000000000000000009001000000000000000000205300650067006F006500200055004900000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000060000001C000000000000000D0000000B000000020000000200000000000000330000000000000000000000F5FFFFFF0000000000000000000000009001000000000000000000205400610068006F006D00610000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000050000001B000000000000000D0000000B000000020000000200000000000000330000000000000000000000F5FFFFFF000000000000000000000000BC02000000000000000000205300650067006F006500200055004900000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000060000001C000000000000000D0000000B000000020000000200000000000000330000000000000000000000F1FFFFFF000000000000000000000000900100000000000000000000430061006C0069006200720069000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000080000001A00000000000000120000000E000000040000000300000000000000330000000000000000000000F3FFFFFF000000000000000000000000BC02000000000000000000005300650067006F006500200055004900000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000080000002100000000000000110000000E000000030000000400000000000000330000000000000000000000 | |||
| (PID) Process: | (7472) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\Internet\WebServiceCache\AllUsers\officeclient.microsoft.com\config16--lcid=1033&syslcid=1033&uilcid=1033&build=16.0.16026&crev=3\0 |
| Operation: | write | Name: | FilePath |
Value: officeclient.microsoft.com\00C829D3-8DC3-4E6D-B9F4-5876E6BAEA5D | |||
| (PID) Process: | (7472) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\Internet\WebServiceCache\AllUsers\officeclient.microsoft.com\config16--lcid=1033&syslcid=1033&uilcid=1033&build=16.0.16026&crev=3\0 |
| Operation: | write | Name: | StartDate |
Value: F0E5249EBA9CDB01 | |||
| (PID) Process: | (7472) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\Internet\WebServiceCache\AllUsers\officeclient.microsoft.com\config16--lcid=1033&syslcid=1033&uilcid=1033&build=16.0.16026&crev=3\0 |
| Operation: | write | Name: | EndDate |
Value: F0A58EC8839DDB01 | |||
| (PID) Process: | (7472) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | f5. |
Value: 㕦.ᴰ | |||
| (PID) Process: | (7472) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7472) EXCEL.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Excel\Resiliency |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
0
Suspicious files
69
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7472 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.MSO\74F71703.emf | — | |
MD5:— | SHA256:— | |||
| 2108 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\a690b190-994b-4120-ac92-b2cb0314be39.down_data | — | |
MD5:— | SHA256:— | |||
| 2108 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:C07FC686D4286404DFF59DA900C8C666 | SHA256:A696111E3F5AA7F62AA968E67314E96A51CEFD31A2E53F419188FDEB5E435B99 | |||
| 7472 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\00C829D3-8DC3-4E6D-B9F4-5876E6BAEA5D | xml | |
MD5:3C7FB069593F42588F9278F615EB9787 | SHA256:554ADEB166A95DED83237D33C2D4D403A0F44505CA1EEAFC330761E49A159187 | |||
| 7472 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\excel.exe_Rules.xml | xml | |
MD5:13AF026BB17E87B1A24C00E8295447B0 | SHA256:4695B860F6568E9EDDC220E4C80C848D5B6BE780C9A4A31FAD4D878E098FF8DB | |||
| 2108 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:4872BABAF39AA62B8D32695EBB7E9173 | SHA256:2EE85DF86EE29BBEB3DCA81AA29B6DE204F605A2769B84C728A329178A2D0999 | |||
| 7472 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_CBDCCBFE4F7A916411C1E69BDD97BB04 | binary | |
MD5:2596CB236EBCA768CA81740AA9B81B59 | SHA256:73FDE9934B086CF0956B22493F9AB7B094D144B48A3B06E995FD3E644B6BAA0C | |||
| 2108 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\da1ac65b-2f74-498e-a4c3-a6c973dbbc4b.up_meta_secure | binary | |
MD5:698E2D8A07C79CE3705F8C92D156F088 | SHA256:13017D7BC2A798DD0A4889BE6B005781F2D43DB3F480331BAEC240EB6E3AEDA6 | |||
| 7472 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:70BBCCC3C97E9D4F916D1520785400D0 | SHA256:C11675EF62438EE9E03290BC96760652026D50893EB700B88CEF3F0BE3CFC34C | |||
| 7472 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_CBDCCBFE4F7A916411C1E69BDD97BB04 | binary | |
MD5:54F6521C654AC8594BE7AC12F5077FF2 | SHA256:91FB71650A1C93BFD8619E4933B95775DC52ED5DD9FDBF07893F49E8BDA9C83C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
109
DNS requests
96
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7472 | EXCEL.EXE | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
7592 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7472 | EXCEL.EXE | GET | 200 | 92.123.17.129:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
2108 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7472 | EXCEL.EXE | GET | 200 | 95.101.54.123:80 | http://r11.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBQaUrm0WeTDM5ghfoZtS72KO9ZnzgQUCLkRO6XQhRi06g%2BgrZ%2BGHo78OCcCEgMByhMs4ZBgwiQmBdVFWSXirw%3D%3D | unknown | — | — | whitelisted |
7472 | EXCEL.EXE | GET | 200 | 95.101.54.123:80 | http://r11.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBQaUrm0WeTDM5ghfoZtS72KO9ZnzgQUCLkRO6XQhRi06g%2BgrZ%2BGHo78OCcCEgPnk8CpOGL%2B%2BeqnJHiwkPOG%2BQ%3D%3D | unknown | — | — | whitelisted |
7472 | EXCEL.EXE | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
7288 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7288 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7592 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7592 | backgroundTaskHost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
roaming.officeapps.live.com |
| whitelisted |
maramaabroo.com |
| unknown |
x1.c.lencr.org |
| whitelisted |