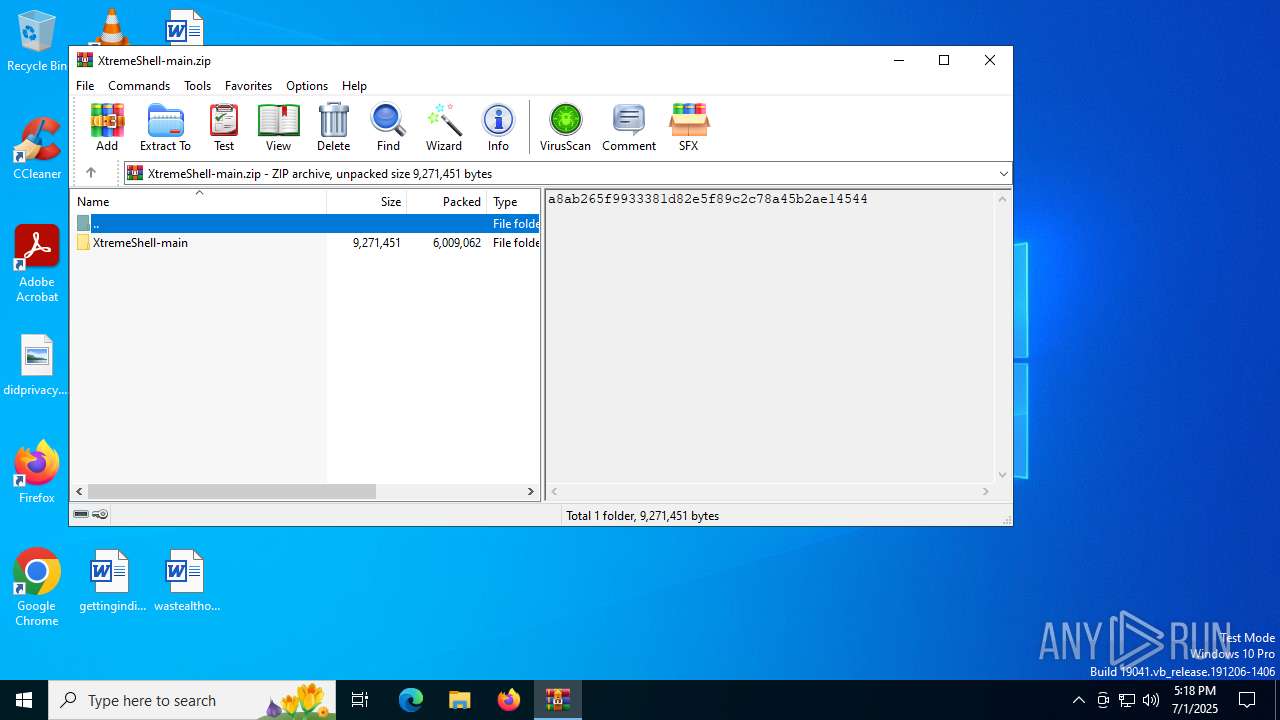
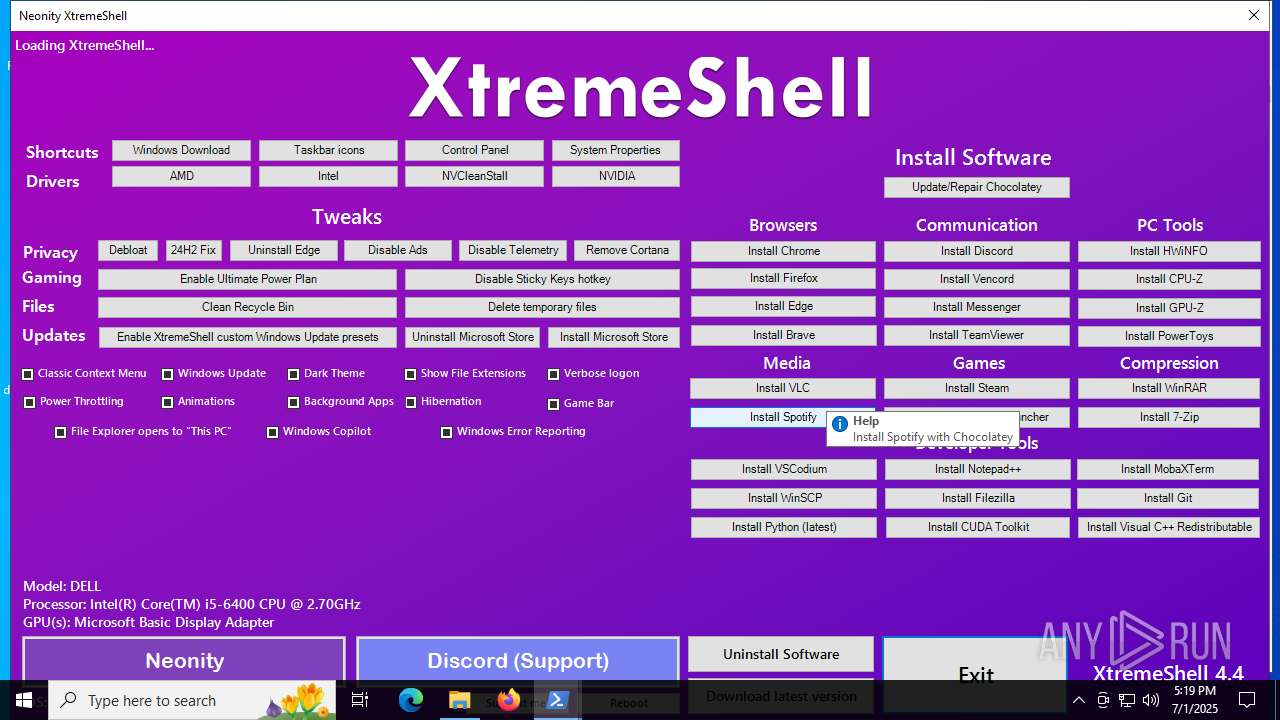
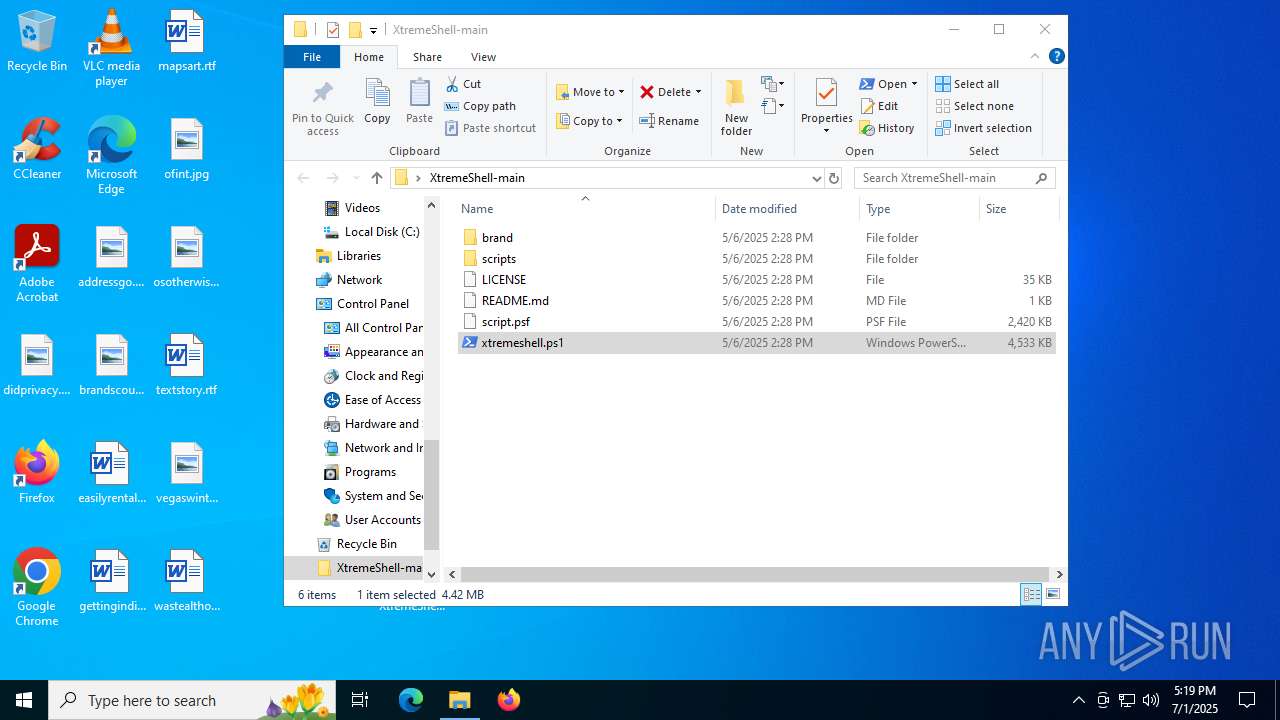
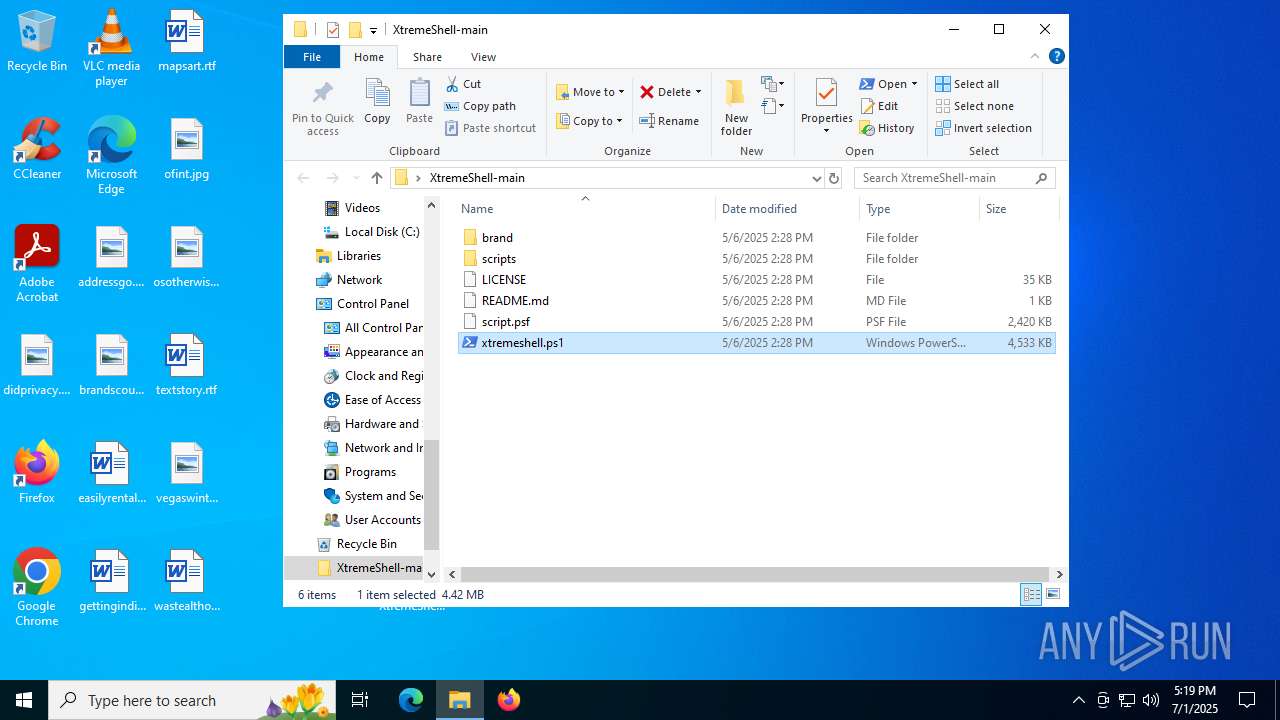
| File name: | XtremeShell-main.zip |
| Full analysis: | https://app.any.run/tasks/f6aff901-bec9-4de0-bd05-2a7e77e79177 |
| Verdict: | Malicious activity |
| Analysis date: | July 01, 2025, 17:18:39 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 6ECF0E0D5AB7D64B820B263896D17CCB |
| SHA1: | A6860CA66AD1C9E1981647F486E80691CAC4E762 |
| SHA256: | 5071589165B65D73ABE2C864127086C3C43CD0EAADE158C990111B4AB8C0AE17 |
| SSDEEP: | 98304:3zXAxyUAcip/DCOJv76r74Zg8IWBNBrBMAZA5C3ctwVQ1fNJqH5dE5aWdL/IKY3v:3KMR8or7pevwwsdmOX |
MALICIOUS
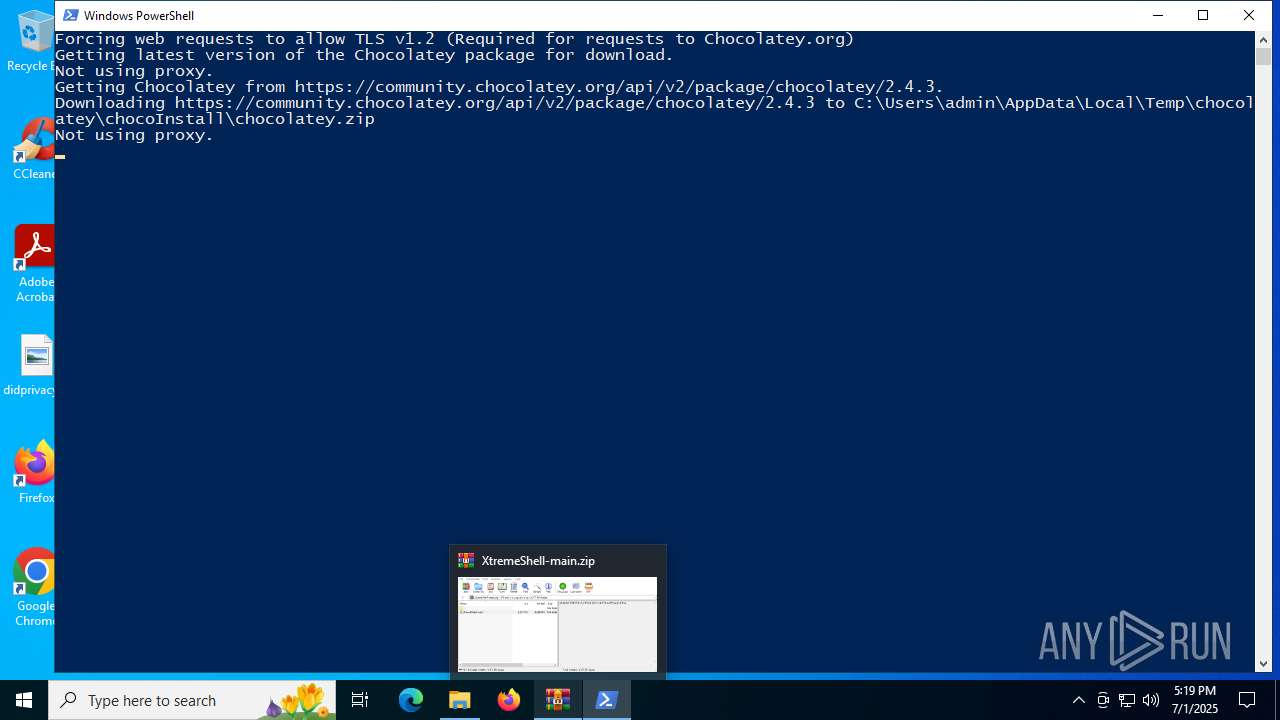
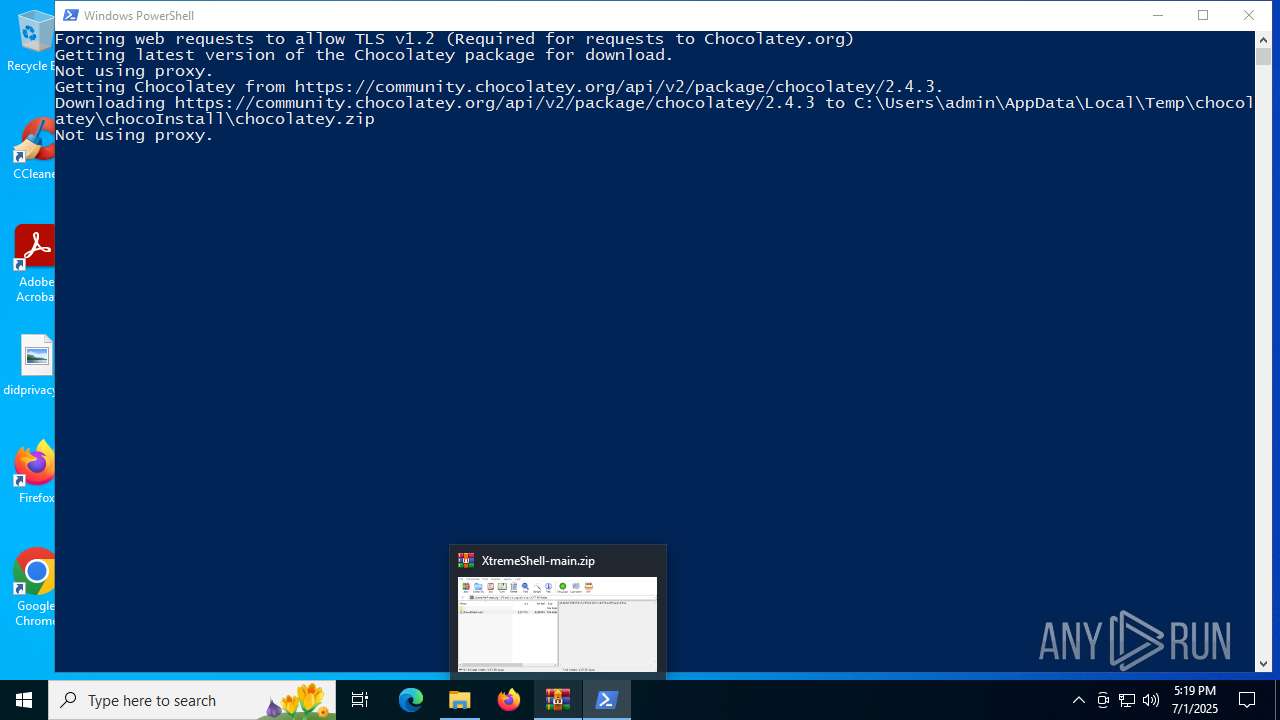
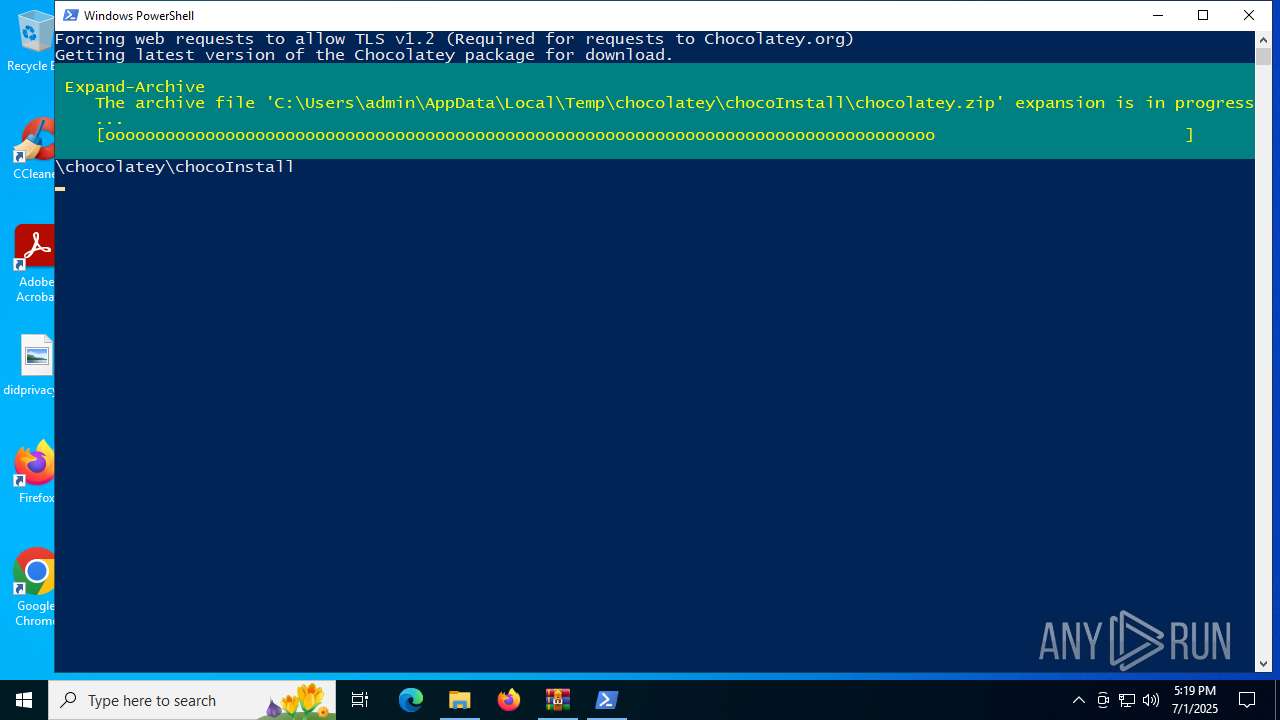
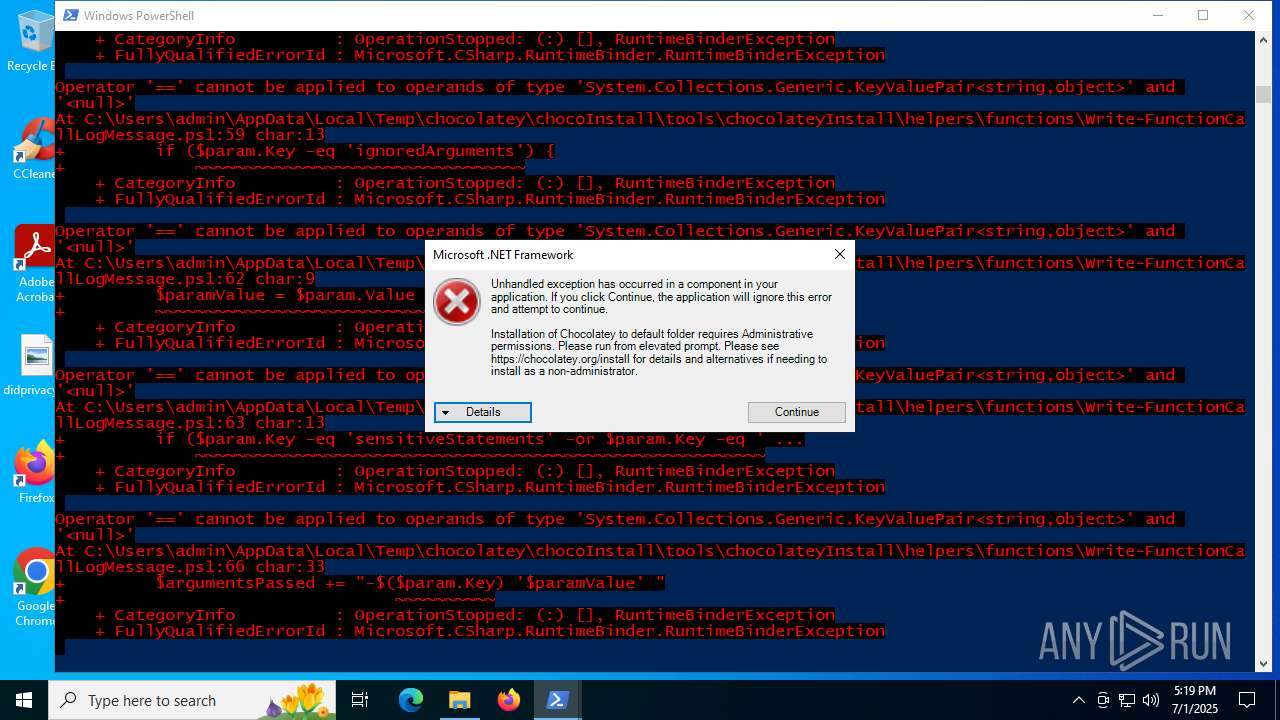
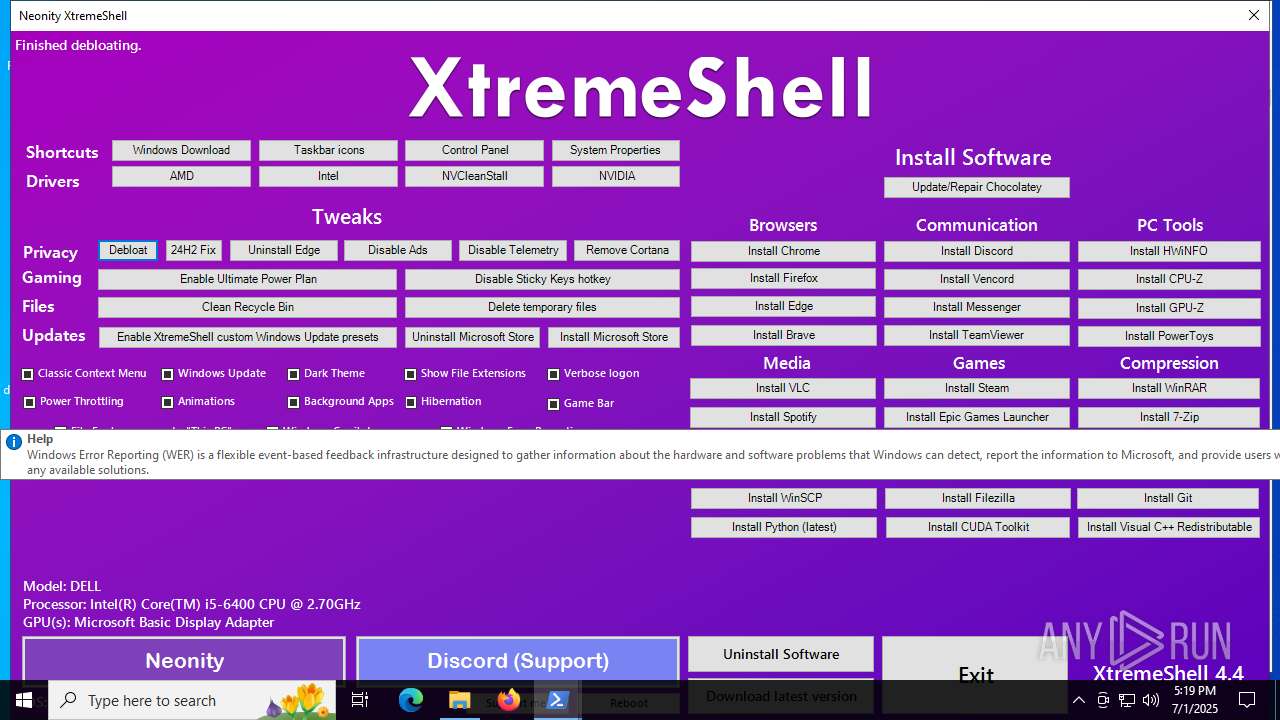
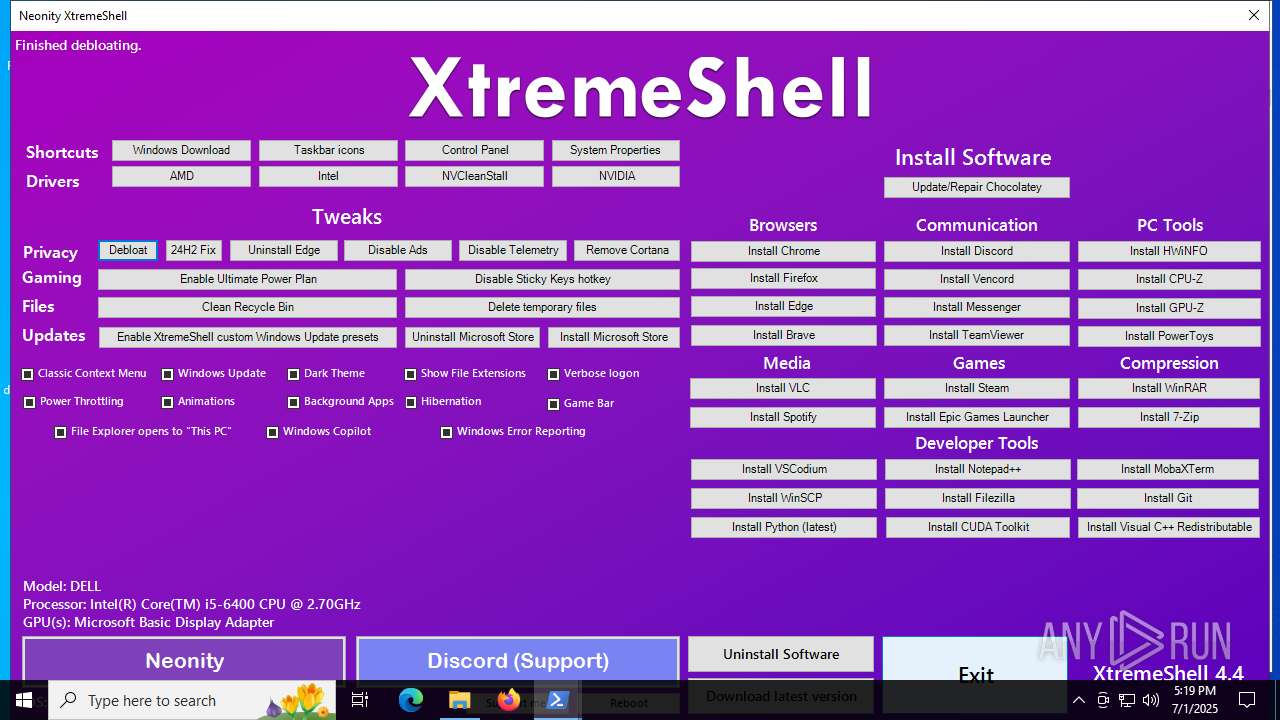
Bypass execution policy to execute commands
- powershell.exe (PID: 4916)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 4916)
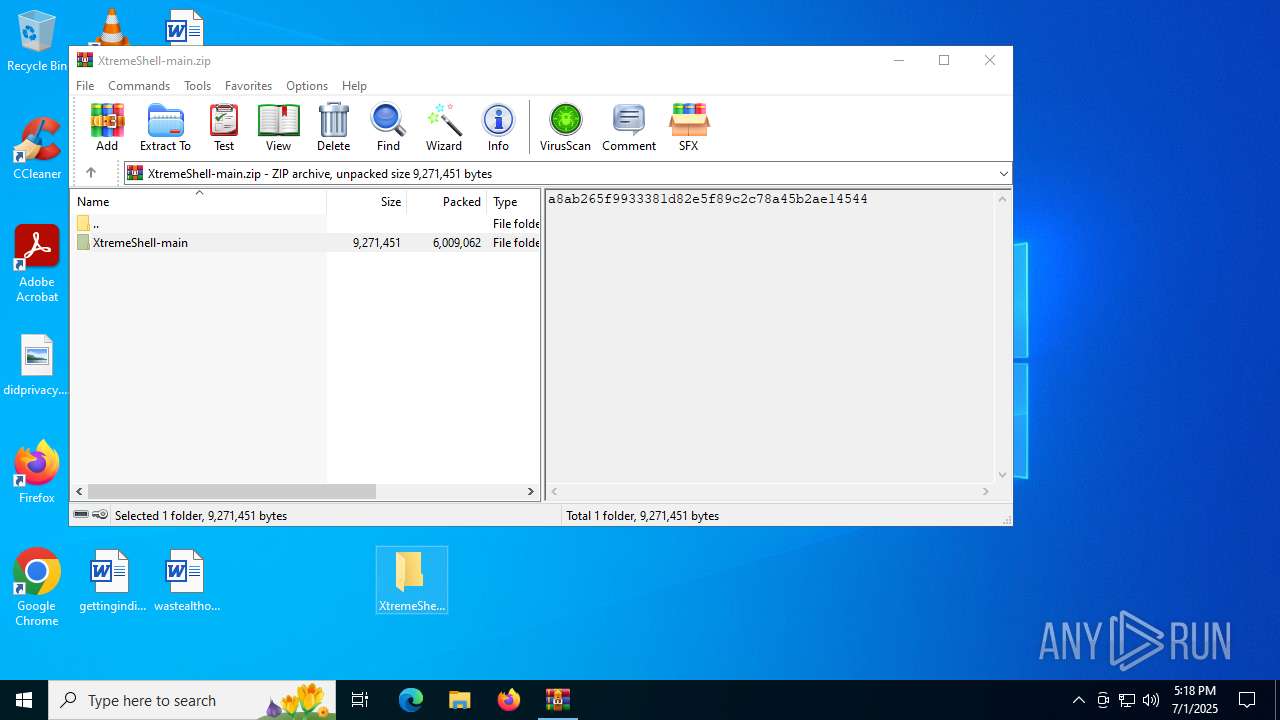
Generic archive extractor
- WinRAR.exe (PID: 2976)
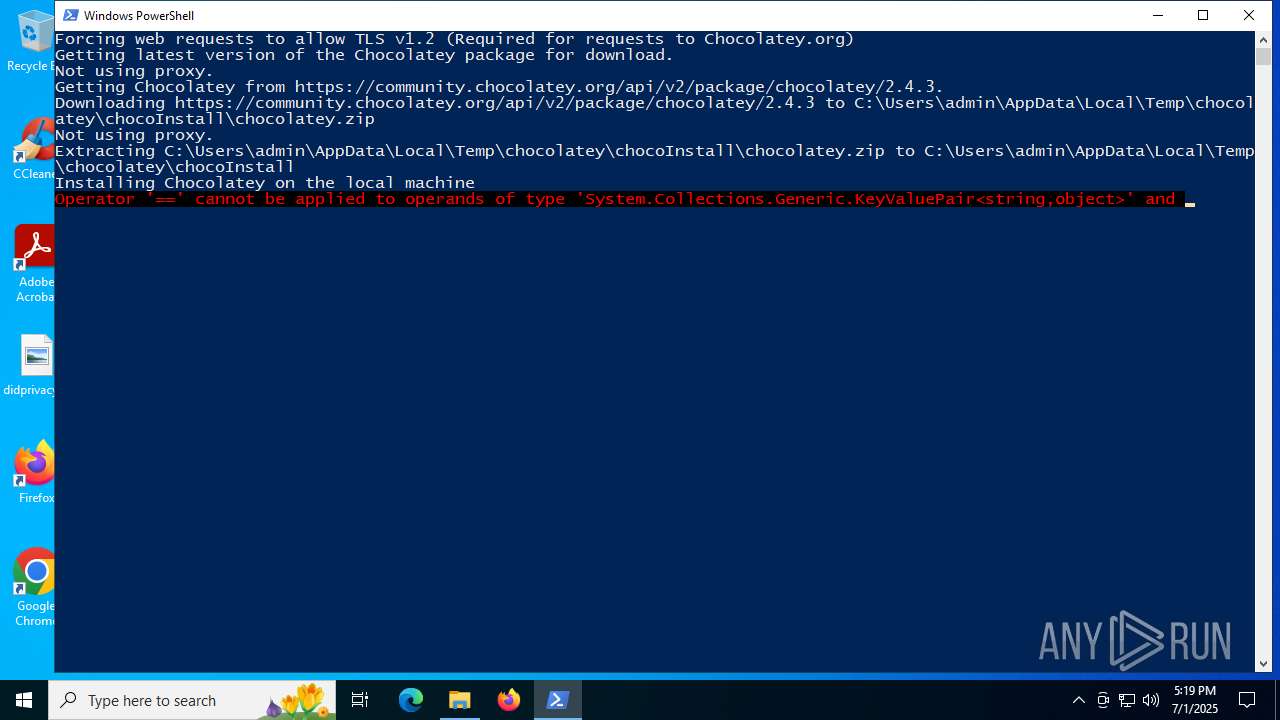
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 4916)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 4916)
SUSPICIOUS
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 4916)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 4916)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 4916)
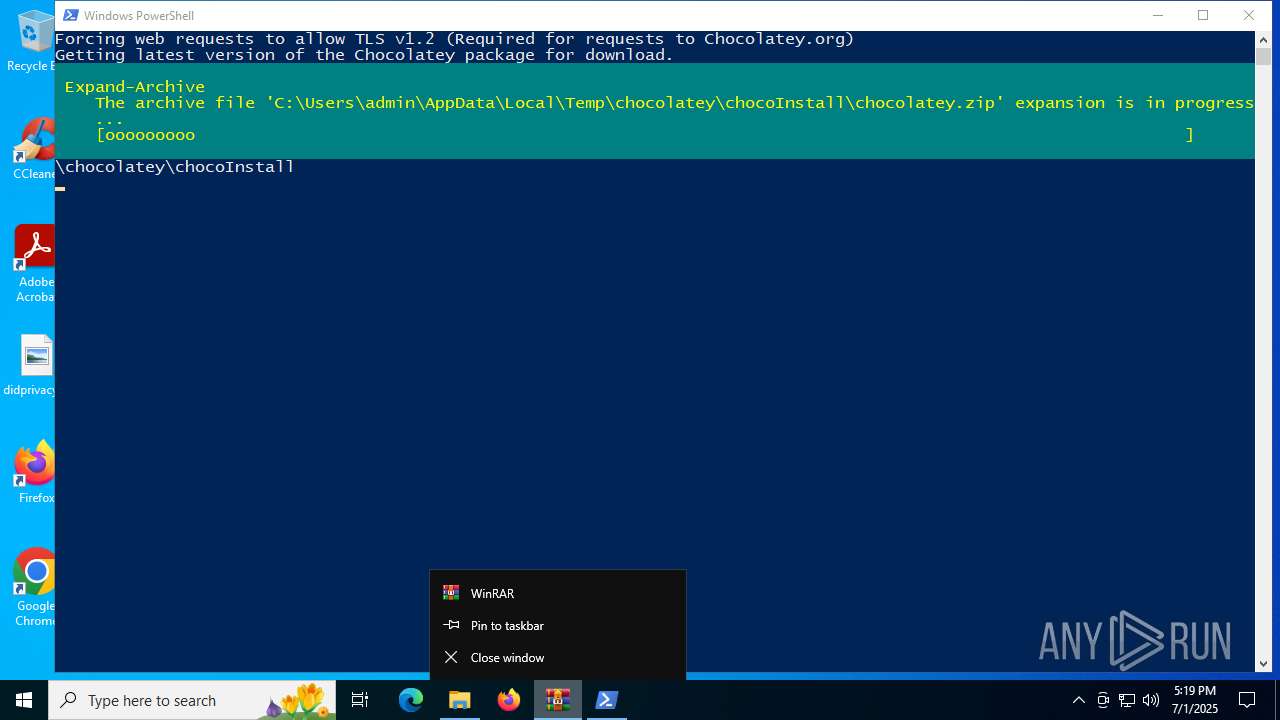
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 4916)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 1976)
Drops 7-zip archiver for unpacking
- powershell.exe (PID: 4916)
Gets path to any of the special folders (POWERSHELL)
- powershell.exe (PID: 4916)
Creates a directory (POWERSHELL)
- powershell.exe (PID: 4916)
The process creates files with name similar to system file names
- powershell.exe (PID: 4916)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 4916)
Executable content was dropped or overwritten
- powershell.exe (PID: 4916)
INFO
Manual execution by a user
- powershell.exe (PID: 4916)
Disables trace logs
- powershell.exe (PID: 4916)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 4916)
Checks proxy server information
- powershell.exe (PID: 4916)
Checks supported languages
- ShellExperienceHost.exe (PID: 1976)
Reads the computer name
- ShellExperienceHost.exe (PID: 1976)
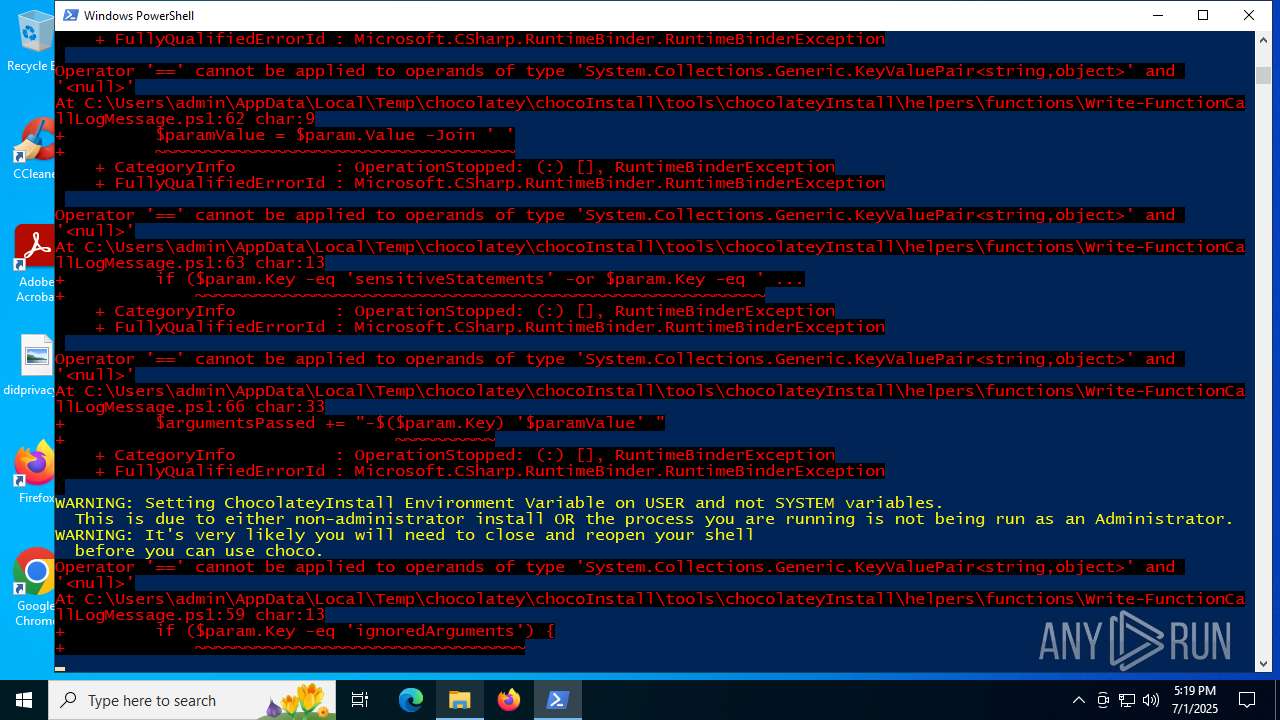
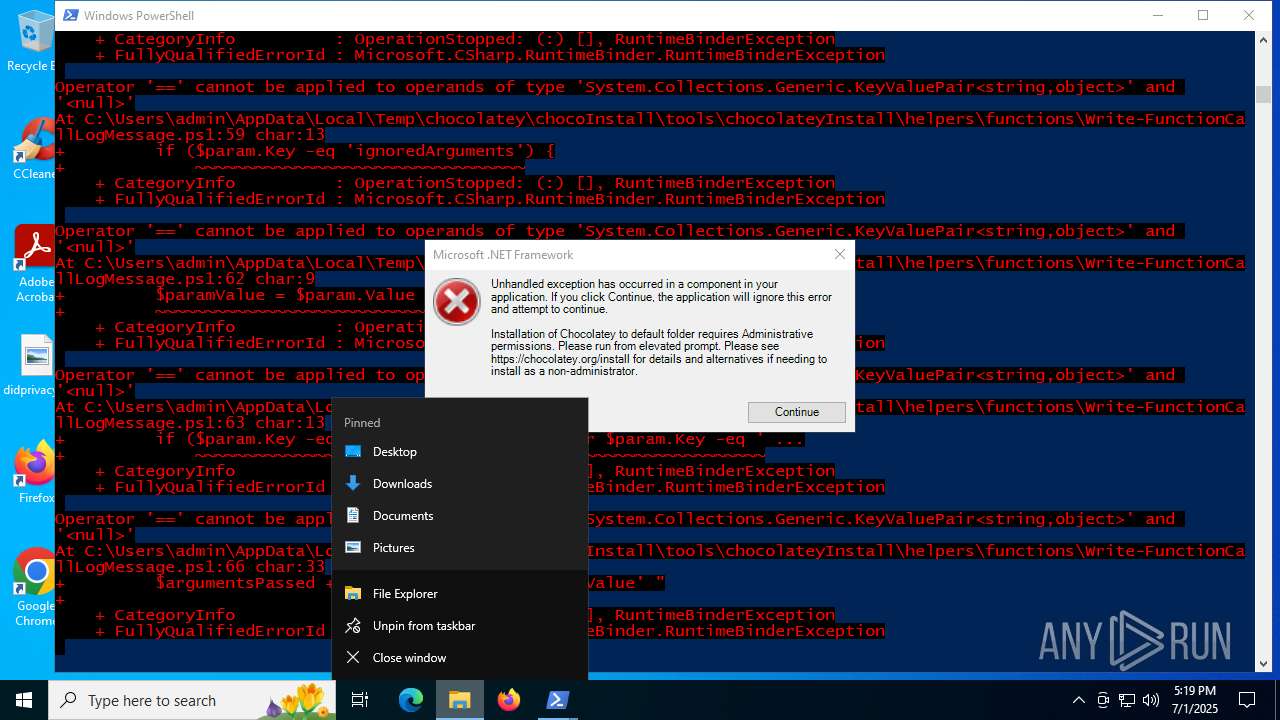
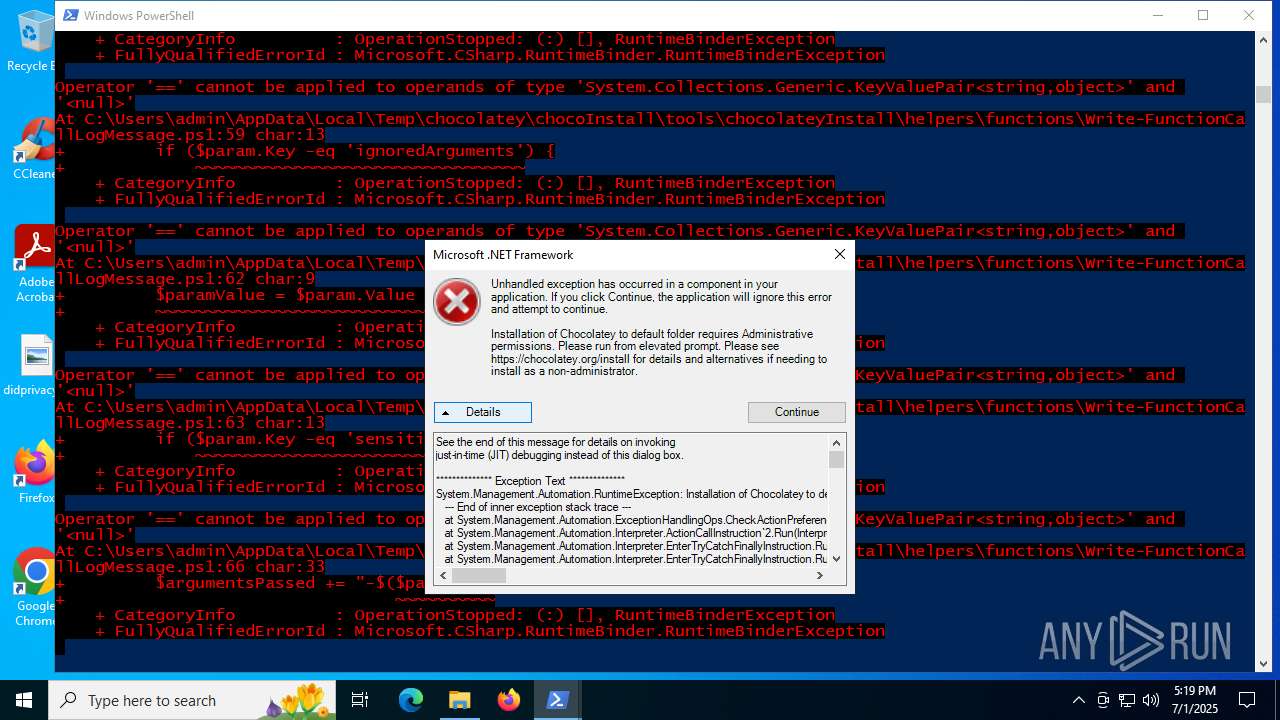
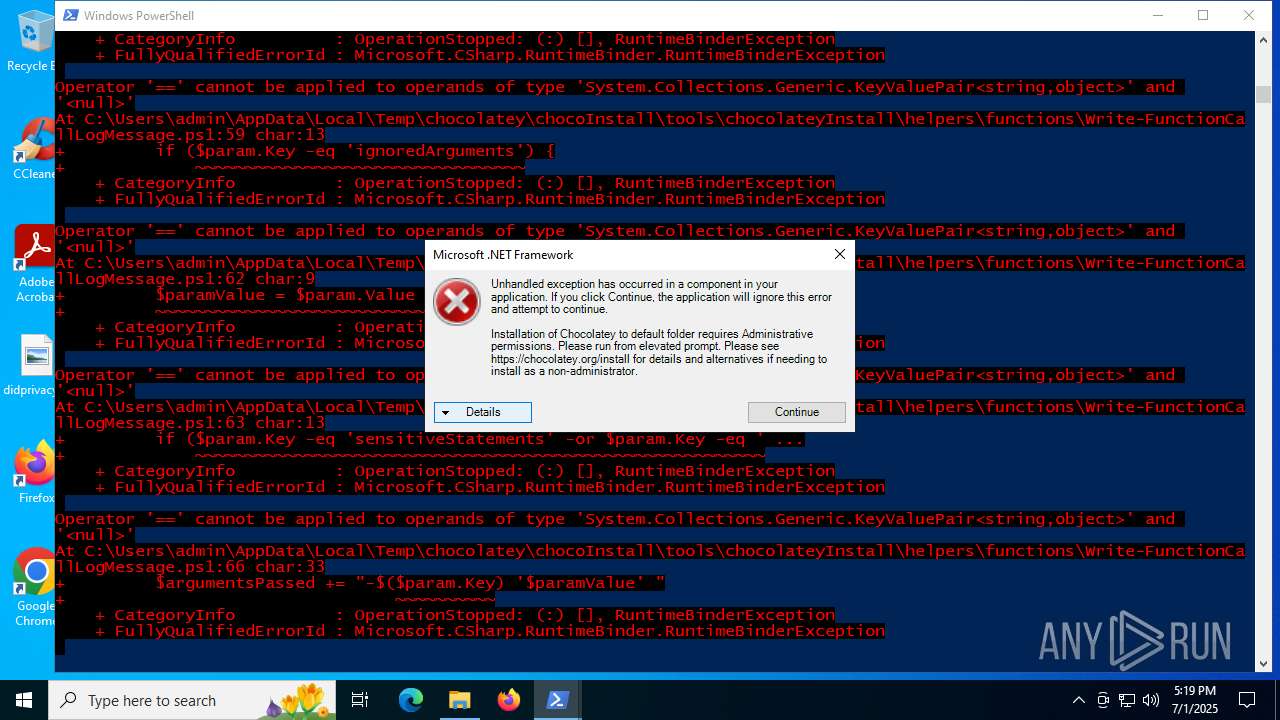
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4916)
Creates files in the program directory
- powershell.exe (PID: 4916)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 4916)
The sample compiled with english language support
- powershell.exe (PID: 4916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:05:06 07:28:36 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | XtremeShell-main/ |
Total processes
148
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 424 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1976 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2464 | "C:\WINDOWS\System32\setx.exe" ChocolateyLastPathUpdate 133958639543030993 | C:\Windows\System32\setx.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Setx - Sets environment variables Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2976 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\XtremeShell-main.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3608 | "C:\WINDOWS\System32\setx.exe" ChocolateyLastPathUpdate 133958639549903911 | C:\Windows\System32\setx.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Setx - Sets environment variables Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
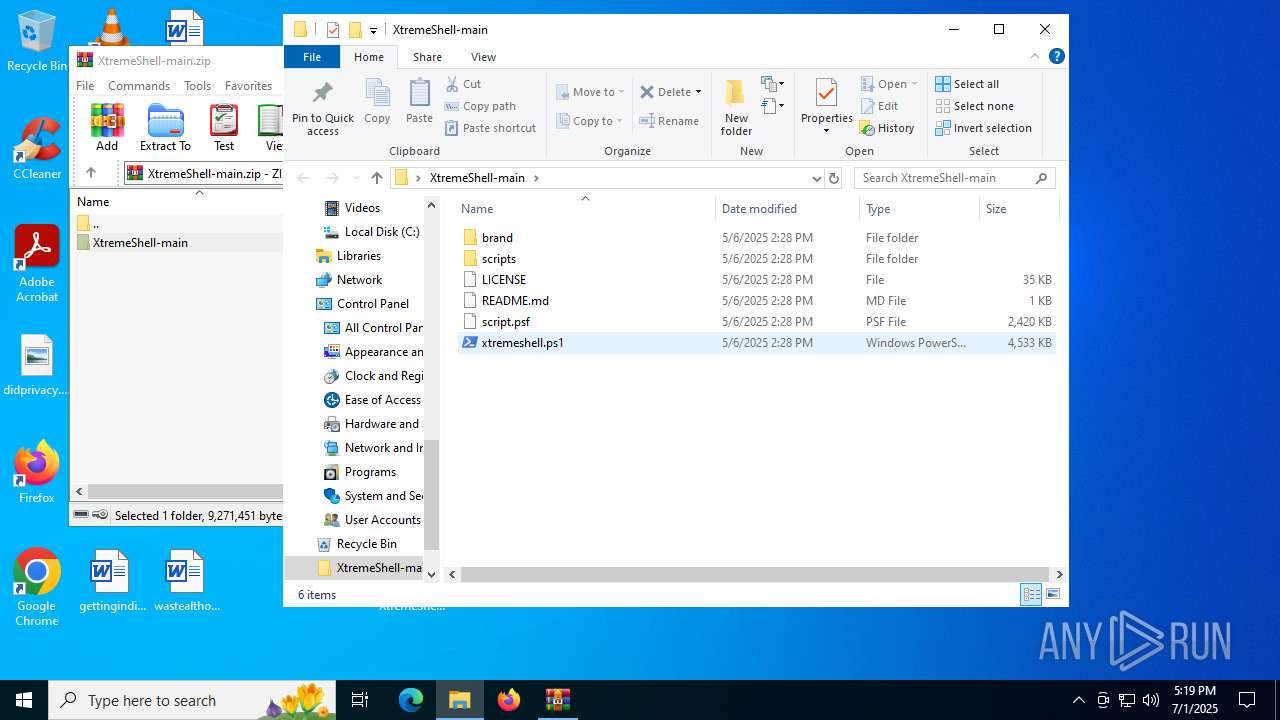
| 4916 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass "C:\Users\admin\Desktop\XtremeShell-main\xtremeshell.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6472 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7080 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 483
Read events
13 460
Write events
22
Delete events
1
Modification events
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\XtremeShell-main.zip | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (4916) powershell.exe | Key: | HKEY_CURRENT_USER\Environment |
| Operation: | delete value | Name: | ChocolateyInstall |
Value: | |||
Executable files
7
Suspicious files
6
Text files
71
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
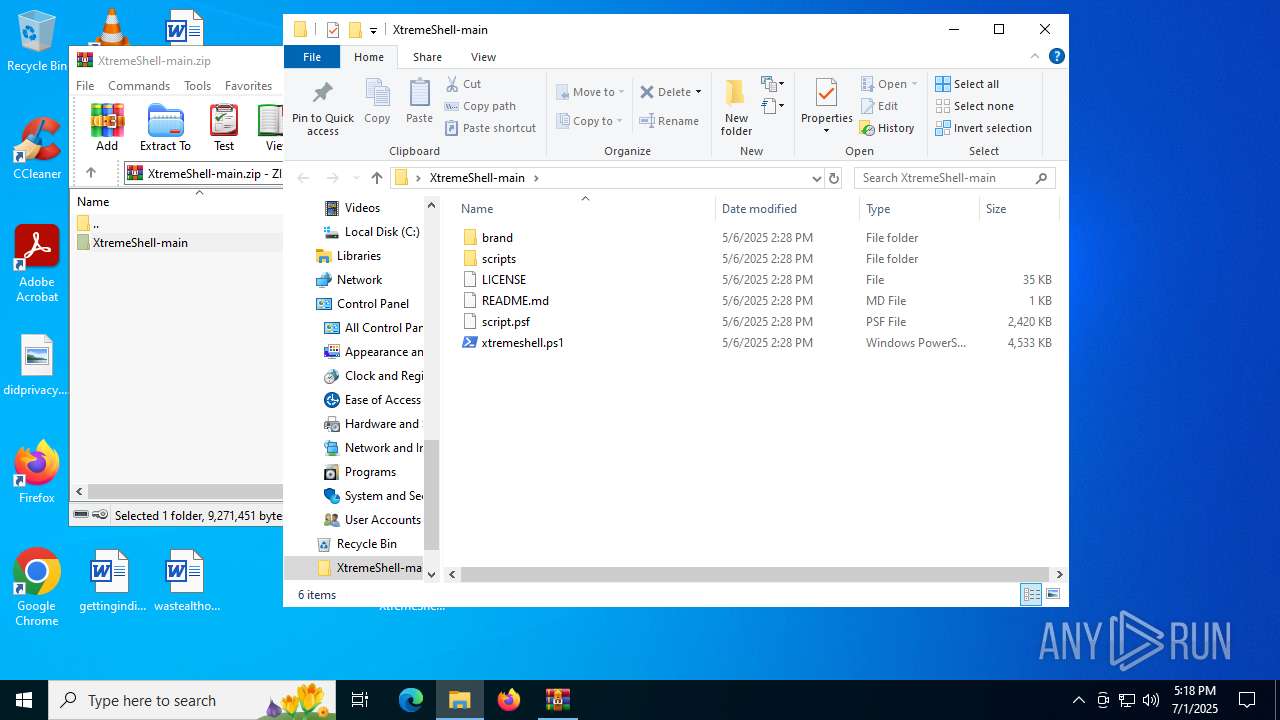
| 2976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2976.14354\XtremeShell-main\xtremeshell.ps1 | — | |
MD5:— | SHA256:— | |||
| 2976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2976.14354\XtremeShell-main\LICENSE | text | |
MD5:1EBBD3E34237AF26DA5DC08A4E440464 | SHA256:3972DC9744F6499F0F9B2DBF76696F2AE7AD8AF9B23DDE66D6AF86C9DFB36986 | |||
| 2976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2976.14354\XtremeShell-main\brand\logo2.ico | image | |
MD5:824C96ED08412EE7D3757A21CD80FEE4 | SHA256:E9F7B3C0CCE66F7EB18A8DC0494931C6C9147155490406D59EAD0FCDA516CC78 | |||
| 2976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2976.14354\XtremeShell-main\brand\background.png | image | |
MD5:9CB41D81D097E77E839D300B1A020DC8 | SHA256:70A5CF0F5F23B5C47043602878EFD713D46D22281111C6944ADE6AD40DFC50CE | |||
| 4916 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:F1813D23F957B668E1641CFAE229C3A3 | SHA256:1633719016EB603F5E267E48AE7DF2EC9036A837C1E119B18B6FF35EFAE3665B | |||
| 4916 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_cflvjtb3.bca.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2976.14354\XtremeShell-main\scripts\EdgeUninstall.bat | text | |
MD5:3F7AC52CEA97B7386E25F3AFEC4823AD | SHA256:26414B12D023D09184027521BE13E8DECE829015D60EAB92849D4AC125F49361 | |||
| 2976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2976.14354\XtremeShell-main\scripts\Debloat.ps1 | text | |
MD5:04756225A57438F83504A56DEE1FC8D2 | SHA256:43E185D8265299B7587F9272B04FFAE4A14E16E54E1DCA7679F5BDF9ECE3B65F | |||
| 4916 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF17924d.TMP | binary | |
MD5:00A03B286E6E0EBFF8D9C492365D5EC2 | SHA256:4DBFC417D053BA6867308671F1C61F4DCAFC61F058D4044DB532DA6D3BDE3615 | |||
| 4916 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_204so50w.s2r.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
22
DNS requests
18
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.20.245.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2524 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4788 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4788 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6828 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 2.20.245.137:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2524 | svchost.exe | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2524 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
community.chocolatey.org |
| whitelisted |
packages.chocolatey.org |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
4916 | powershell.exe | Potentially Bad Traffic | ET INFO Observed Chocolatey Windows Package Management Domain (chocolatey .org in TLS SNI) |
— | — | Potentially Bad Traffic | ET INFO Chocolatey Windows Package Management Installation File Retrieval |
— | — | Potentially Bad Traffic | ET INFO PS1 Powershell File Request |
— | — | Potentially Bad Traffic | ET HUNTING Generic Powershell DownloadString Command |
— | — | Potentially Bad Traffic | ET HUNTING Generic Powershell DownloadFile Command |
— | — | Potentially Bad Traffic | ET HUNTING PowerShell DownloadString Command Common In Powershell Stagers |
— | — | Potentially Bad Traffic | ET HUNTING PowerShell DownloadFile Command Common In Powershell Stagers |
Process | Message |
|---|---|
powershell.exe | PID=4916 TID=5708 DISM API requires elevation - DismInitializeInternal(hr:0x800702e4)
|
powershell.exe | PID=4916 TID=5708 Leave DismInitializeInternal - DismInitializeInternal
|
powershell.exe | PID=4916 TID=5708 DISM API requires elevation - DismInitializeInternal(hr:0x800702e4)
|
powershell.exe | PID=4916 TID=5708 Leave DismInitializeInternal - DismInitializeInternal
|