| File name: | 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.exe |
| Full analysis: | https://app.any.run/tasks/2418cb8d-7e80-468e-9fd9-838c993b8d1e |
| Verdict: | Malicious activity |
| Analysis date: | June 01, 2024, 19:23:10 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C74AC8E2372D7FFBF59DF8E5D50F81CF |
| SHA1: | 095E3EF202ED82C48A07899B5B876ED2963B8228 |
| SHA256: | 506A508B6A6F236185FD9C2689F548C7085948CEB0E99CC8D5C7C2B81BBE80F9 |
| SSDEEP: | 786432:6P3j/7GNt9FXVY5cBIadVRAqJOSiZYeKoK:gD7GNvFXVY51aHRABZYQK |
MALICIOUS
Drops the executable file immediately after the start
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.exe (PID: 7036)
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.exe (PID: 5932)
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp (PID: 6192)
Registers / Runs the DLL via REGSVR32.EXE
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp (PID: 6192)
Changes the autorun value in the registry
- vidnotifier.exe (PID: 1864)
SUSPICIOUS
Reads security settings of Internet Explorer
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp (PID: 7148)
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp (PID: 6192)
Reads the date of Windows installation
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp (PID: 7148)
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp (PID: 6192)
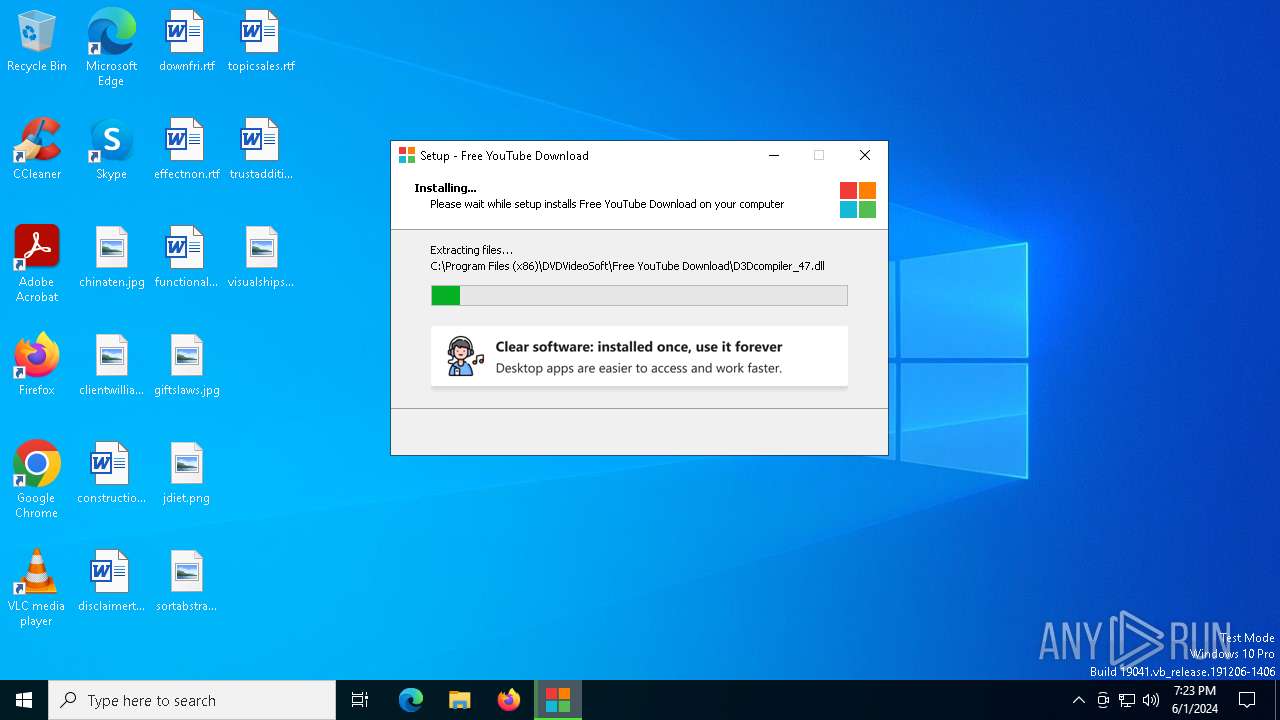
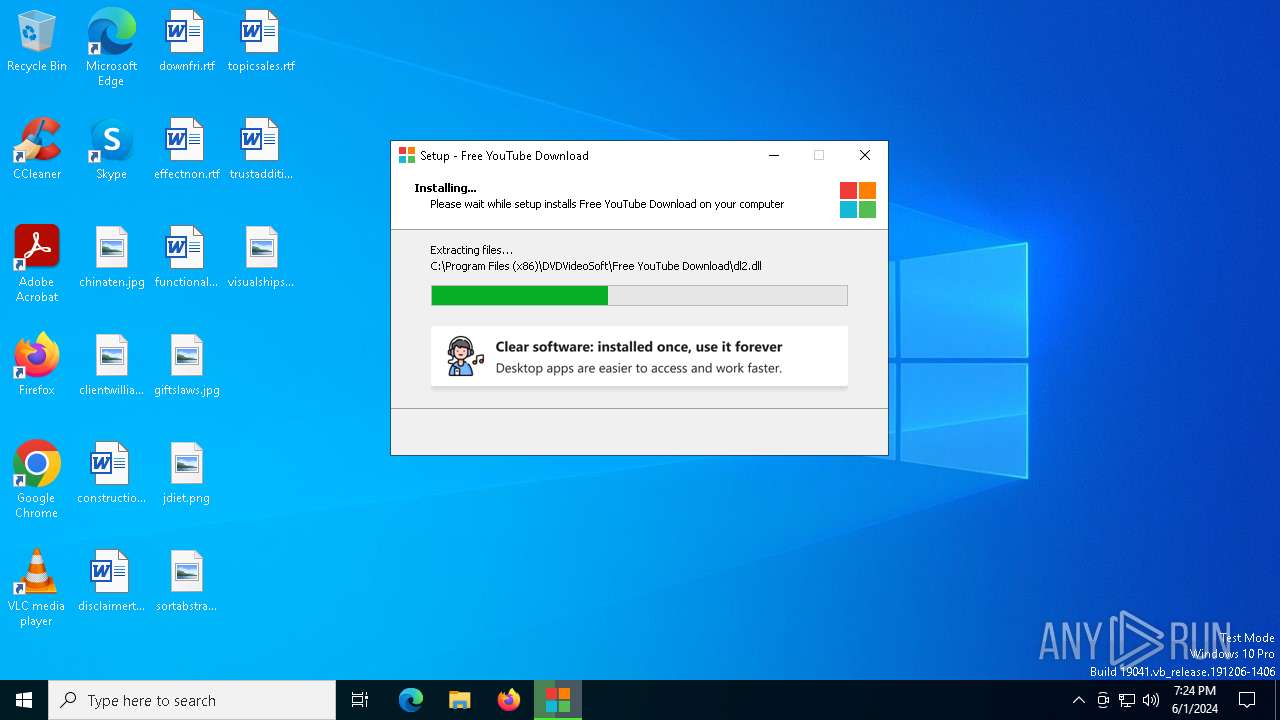
Executable content was dropped or overwritten
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.exe (PID: 5932)
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp (PID: 6192)
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.exe (PID: 7036)
Process drops legitimate windows executable
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp (PID: 6192)
Reads the Windows owner or organization settings
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp (PID: 6192)
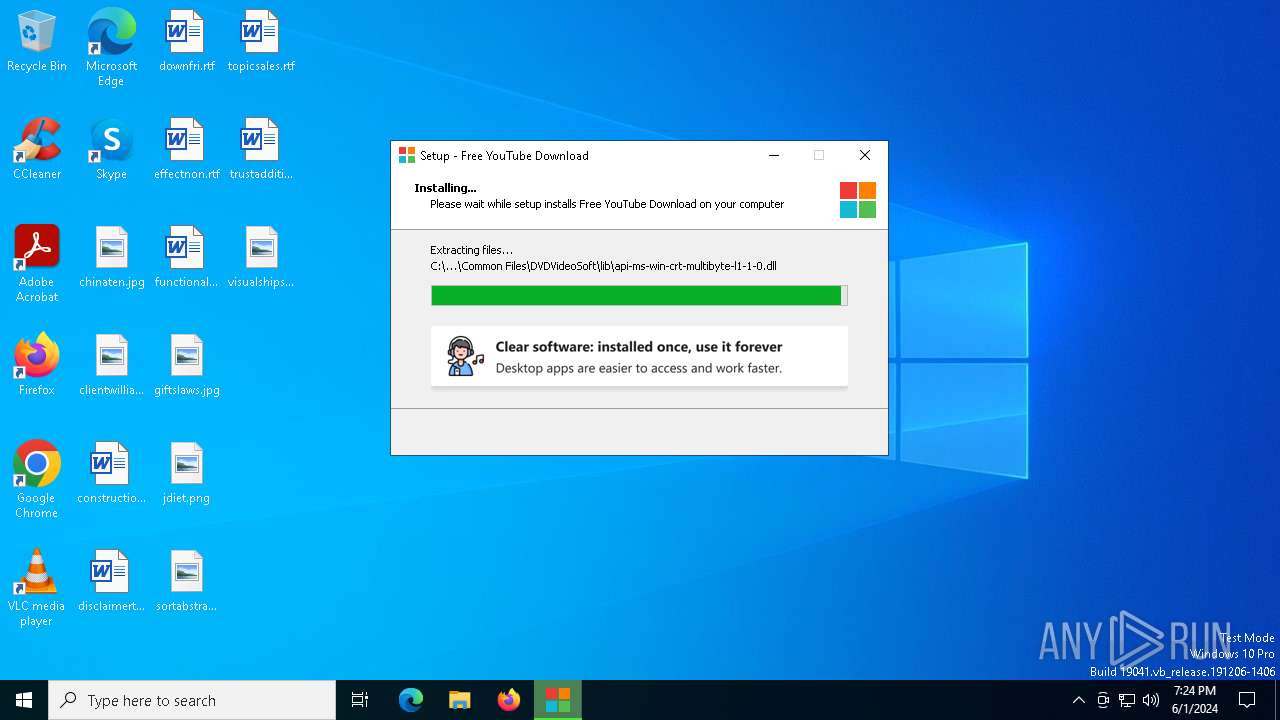
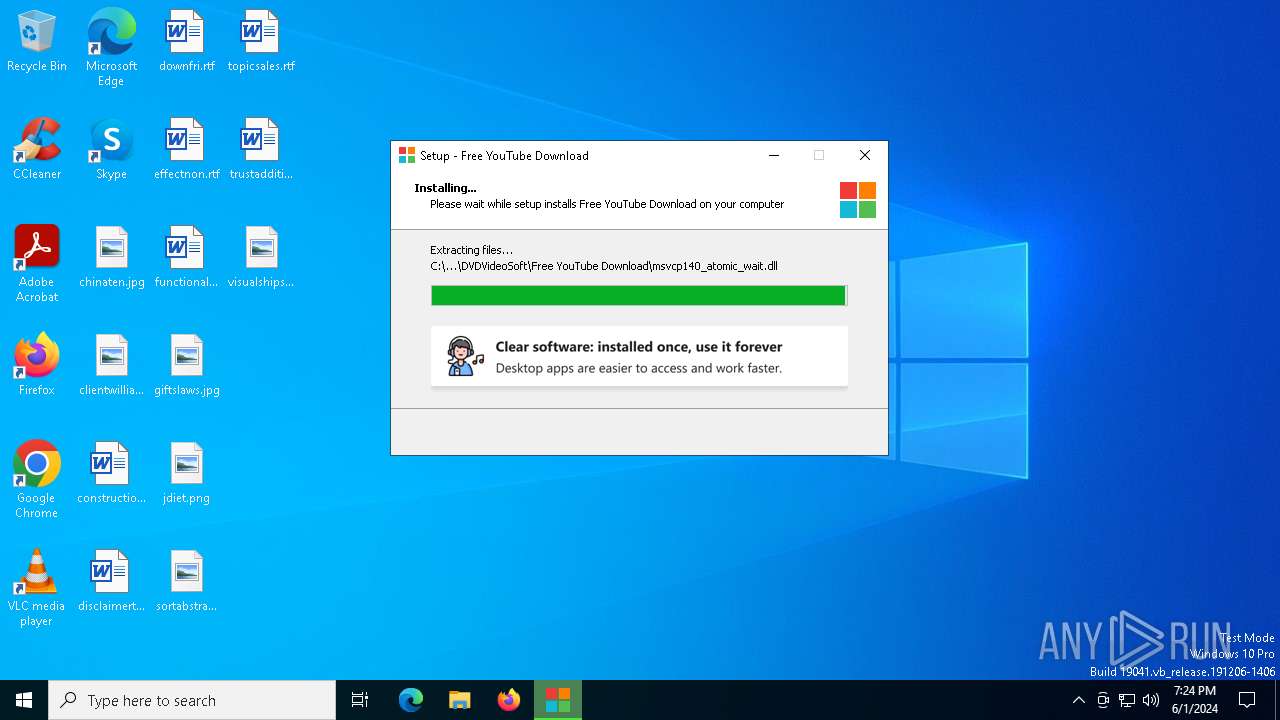
The process drops C-runtime libraries
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp (PID: 6192)
Process drops SQLite DLL files
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp (PID: 6192)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 6608)
- regsvr32.exe (PID: 2116)
- regsvr32.exe (PID: 6604)
- regsvr32.exe (PID: 5828)
- regsvr32.exe (PID: 7052)
- regsvr32.exe (PID: 7044)
- regsvr32.exe (PID: 5712)
- regsvr32.exe (PID: 2592)
- regsvr32.exe (PID: 1016)
- regsvr32.exe (PID: 3244)
- regsvr32.exe (PID: 4936)
- regsvr32.exe (PID: 1204)
- regsvr32.exe (PID: 4920)
- regsvr32.exe (PID: 1720)
- regsvr32.exe (PID: 6976)
Searches for installed software
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp (PID: 6192)
Adds/modifies Windows certificates
- FreeYTVDownloader.exe (PID: 5920)
INFO
Create files in a temporary directory
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.exe (PID: 7036)
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.exe (PID: 5932)
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp (PID: 6192)
- FreeYTVDownloader.exe (PID: 5920)
Checks supported languages
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.exe (PID: 7036)
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp (PID: 7148)
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.exe (PID: 5932)
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp (PID: 6192)
- FreeYTVDownloader.exe (PID: 5920)
- vidnotifier.exe (PID: 1864)
- QtWebEngineProcess.exe (PID: 3396)
- QtWebEngineProcess.exe (PID: 1728)
- QtWebEngineProcess.exe (PID: 6864)
- QtWebEngineProcess.exe (PID: 3116)
- QtWebEngineProcess.exe (PID: 3628)
- QtWebEngineProcess.exe (PID: 3704)
- identity_helper.exe (PID: 6788)
- QtWebEngineProcess.exe (PID: 3904)
- pwahelper.exe (PID: 7652)
Reads the computer name
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp (PID: 7148)
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp (PID: 6192)
- vidnotifier.exe (PID: 1864)
- FreeYTVDownloader.exe (PID: 5920)
- identity_helper.exe (PID: 6788)
- pwahelper.exe (PID: 7652)
Process checks computer location settings
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp (PID: 7148)
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp (PID: 6192)
- QtWebEngineProcess.exe (PID: 1728)
- QtWebEngineProcess.exe (PID: 3628)
- QtWebEngineProcess.exe (PID: 3704)
- QtWebEngineProcess.exe (PID: 3116)
- QtWebEngineProcess.exe (PID: 3396)
- QtWebEngineProcess.exe (PID: 6864)
- QtWebEngineProcess.exe (PID: 3904)
Reads the software policy settings
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp (PID: 6192)
- slui.exe (PID: 5632)
- FreeYTVDownloader.exe (PID: 5920)
Reads product name
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp (PID: 6192)
- vidnotifier.exe (PID: 1864)
- FreeYTVDownloader.exe (PID: 5920)
Reads Environment values
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp (PID: 6192)
- vidnotifier.exe (PID: 1864)
- FreeYTVDownloader.exe (PID: 5920)
Creates files in the program directory
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp (PID: 6192)
Creates a software uninstall entry
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp (PID: 6192)
Creates files or folders in the user directory
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp (PID: 6192)
- vidnotifier.exe (PID: 1864)
- FreeYTVDownloader.exe (PID: 5920)
Reads the machine GUID from the registry
- FreeYTVDownloader.exe (PID: 5920)
Reads Microsoft Office registry keys
- 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp (PID: 6192)
- msedge.exe (PID: 6944)
- msedge.exe (PID: 1036)
Application launched itself
- msedge.exe (PID: 6944)
- msedge.exe (PID: 1036)
Manual execution by a user
- msedge.exe (PID: 1036)
Checks proxy server information
- FreeYTVDownloader.exe (PID: 5920)
Reads the time zone
- QtWebEngineProcess.exe (PID: 1728)
- QtWebEngineProcess.exe (PID: 3628)
- QtWebEngineProcess.exe (PID: 3704)
- QtWebEngineProcess.exe (PID: 3116)
- QtWebEngineProcess.exe (PID: 3396)
- QtWebEngineProcess.exe (PID: 6864)
- QtWebEngineProcess.exe (PID: 3904)
Drops the executable file immediately after the start
- msedge.exe (PID: 6580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:04:14 16:10:23+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741888 |
| InitializedDataSize: | 157696 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
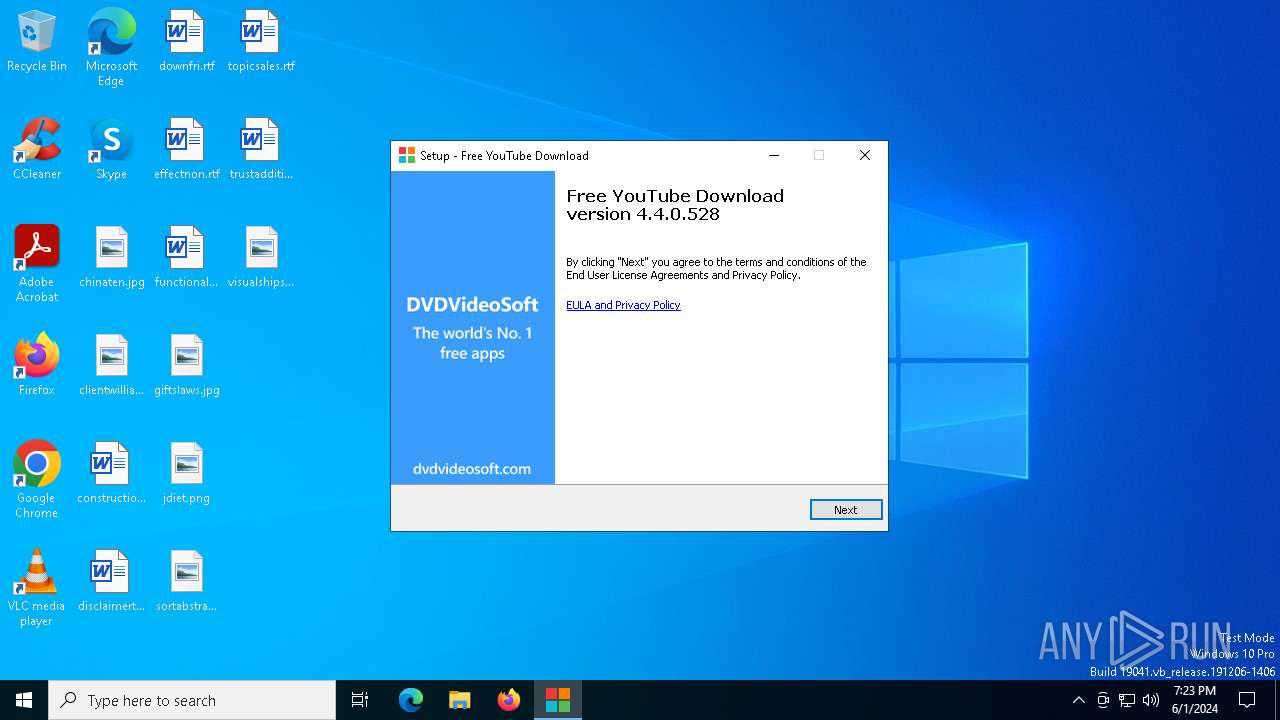
| FileVersionNumber: | 4.4.0.528 |
| ProductVersionNumber: | 4.4.0.528 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Digital Wave Ltd |
| FileDescription: | Free YouTube Download Setup |
| FileVersion: | 4.4.0.528 |
| LegalCopyright: | (c) 2006-2024 Digital Wave Ltd |
| OriginalFileName: | |
| ProductName: | Free YouTube Download (sc) |
| ProductVersion: | 4.4.0.528 |
Total processes
211
Monitored processes
81
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3832 --field-trial-handle=2340,i,8088250231643606532,1823178109503829562,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 628 | "C:\WINDOWS\system32\regsvr32.exe" /s "C:\Program Files (x86)\FreeCodecPack\Haali\Splitter.x64.ax" | C:\Windows\SysWOW64\regsvr32.exe | — | 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5388 --field-trial-handle=2340,i,8088250231643606532,1823178109503829562,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1016 | /s "C:\Program Files (x86)\FreeCodecPack\Haali\ogm.x64.dll" | C:\Windows\System32\regsvr32.exe | — | regsvr32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1036 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --flag-switches-begin --flag-switches-end --do-not-de-elevate --single-argument http://www.dvdvideosoft.com/r/AfterInstall.aspx?ProgramName=FreeYTVDownloader | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1204 | /s "C:\Program Files (x86)\FreeCodecPack\Haali\ts.x64.dll" | C:\Windows\System32\regsvr32.exe | — | regsvr32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1208 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7004 --field-trial-handle=2340,i,8088250231643606532,1823178109503829562,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1676 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x2fc,0x300,0x304,0x2f8,0x30c,0x7ffcf3175fd8,0x7ffcf3175fe4,0x7ffcf3175ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1720 | "C:\WINDOWS\system32\regsvr32.exe" /s "C:\Program Files (x86)\FreeCodecPack\vsfilter.dll" | C:\Windows\SysWOW64\regsvr32.exe | — | 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1728 | "C:\Program Files (x86)\DVDVideoSoft\Free YouTube Download\QtWebEngineProcess.exe" --type=renderer --no-sandbox --disable-gpu-memory-buffer-video-frames --enable-threaded-compositing --enable-features=AllowContentInitiatedDataUrlNavigations --disable-features=MojoVideoCapture,SurfaceSynchronization,UseModernMediaControls,UseVideoCaptureApiForDevToolsSnapshots --disable-gpu-compositing --service-pipe-token=14346560307427040055 --lang=en-US --webengine-schemes=qrc:sLV --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14346560307427040055 --renderer-client-id=3 --mojo-platform-channel-handle=3616 /prefetch:1 | C:\Program Files (x86)\DVDVideoSoft\Free YouTube Download\QtWebEngineProcess.exe | — | FreeYTVDownloader.exe | |||||||||||
User: admin Company: The Qt Company Ltd. Integrity Level: HIGH Description: Qt Qtwebengineprocess Version: 5.12.10.0 Modules
| |||||||||||||||
Total events
32 243
Read events
31 486
Write events
752
Delete events
5
Modification events
| (PID) Process: | (6192) 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\DVDVideoSoft\Manager |
| Operation: | write | Name: | CurrentCulture |
Value: en-US | |||
| (PID) Process: | (6192) 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\DVDVideoSoft\FreeStudio |
| Operation: | write | Name: | CurrentCulture |
Value: en-US | |||
| (PID) Process: | (6192) 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\DVDVideoSoft\FreeStudio |
| Operation: | write | Name: | CurrentCultureFromInstaller |
Value: en-US | |||
| (PID) Process: | (6192) 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\SharedDlls |
| Operation: | write | Name: | C:\Program Files (x86)\Common Files\DVDVideoSoft\unihelp.dll |
Value: 1 | |||
| (PID) Process: | (6192) 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Program Files (x86)\Common Files\DVDVideoSoft\bin\Assistant64.exe |
Value: 1 | |||
| (PID) Process: | (6192) 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\SharedDlls |
| Operation: | write | Name: | C:\Program Files (x86)\Common Files\DVDVideoSoft\lib\vidnotifier\api-ms-win-core-console-l1-1-0.dll |
Value: 1 | |||
| (PID) Process: | (6192) 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\SharedDlls |
| Operation: | write | Name: | C:\Program Files (x86)\Common Files\DVDVideoSoft\lib\vidnotifier\api-ms-win-core-console-l1-2-0.dll |
Value: 1 | |||
| (PID) Process: | (6192) 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\SharedDlls |
| Operation: | write | Name: | C:\Program Files (x86)\Common Files\DVDVideoSoft\lib\vidnotifier\api-ms-win-core-datetime-l1-1-0.dll |
Value: 1 | |||
| (PID) Process: | (6192) 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\SharedDlls |
| Operation: | write | Name: | C:\Program Files (x86)\Common Files\DVDVideoSoft\lib\vidnotifier\api-ms-win-core-debug-l1-1-0.dll |
Value: 1 | |||
| (PID) Process: | (6192) 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\SharedDlls |
| Operation: | write | Name: | C:\Program Files (x86)\Common Files\DVDVideoSoft\lib\vidnotifier\api-ms-win-core-errorhandling-l1-1-0.dll |
Value: 1 | |||
Executable files
822
Suspicious files
643
Text files
227
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6192 | 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | C:\Users\admin\AppData\Local\Temp\is-64N20.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 7036 | 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.exe | C:\Users\admin\AppData\Local\Temp\is-4SUP8.tmp\506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | executable | |
MD5:FAC8132CAA0CB6C2D3E39CBD998F06FB | SHA256:7BF4F7E44C6CA207555034B4C869C638D8CC6B198A46A4875F4C64F2877C77D8 | |||
| 6192 | 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | C:\Users\admin\AppData\Local\Temp\is-64N20.tmp\dvssyshelper.dll | executable | |
MD5:6CBB8DD7C6D931A0AA47684BA70501F6 | SHA256:F3B4F343049A363B0F0055580F7091D43A89DCBFFEEC1CB7B65DF2C2BF7BD3C4 | |||
| 6192 | 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | C:\Users\admin\AppData\Local\Temp\is-64N20.tmp\jansson.dll | executable | |
MD5:BD85AE31F57E240DD145A0B1B3A23D1D | SHA256:E80BB21D45FF59DA6CB22B0FB63267E025BE3B11F89006661D077D852FB0A110 | |||
| 6192 | 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | C:\Users\admin\AppData\Local\Temp\is-64N20.tmp\libssl-1_1.dll | executable | |
MD5:3503885267B930C992CF2FBE028C3B4B | SHA256:BA5084C0C44317D42FCDB2FD76CE07B73C5048B66F932242945095C5E2E2668B | |||
| 6192 | 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | C:\Users\admin\AppData\Local\Temp\is-64N20.tmp\libcrypto-1_1.dll | executable | |
MD5:D525D6132163A1CCC8BBA68892452A64 | SHA256:375639FFB9EFDBC5D978D020BE5867C3E6FE29CFF9CE54BE3E584D262673569F | |||
| 6192 | 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | C:\Users\admin\AppData\Local\Temp\is-64N20.tmp\dlmgr.dll | executable | |
MD5:C41A84EAD571651D3F54472E2534B590 | SHA256:DA9FB4B2BDEC84D4B6EE6602666B55D762A0F925863B97BA9F4134E26E5BE370 | |||
| 6192 | 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | C:\Users\admin\AppData\Local\Temp\is-64N20.tmp\libcurl.dll | executable | |
MD5:D5E314B1856826ED2C729996718DDE82 | SHA256:A3E8DFA038824DA6F56AAD2921B12F383E318E1DBDFAD603D8DF16EBC5A02AD2 | |||
| 6192 | 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | C:\Users\admin\AppData\Local\Temp\is-64N20.tmp\zlib.dll | executable | |
MD5:42EAD533D902C09AC7C6B78EAAFBC76B | SHA256:BD33974EACF309CDCD0BC081286FE777D95F7A97F0BFCA873A4255427EAC7EA1 | |||
| 6192 | 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | C:\Users\admin\AppData\Local\Temp\is-64N20.tmp\tier0.dll | executable | |
MD5:DB894E877AA91484EC5B7075F6DFDE2A | SHA256:B318FB7D1CC6763C0C21684A3949B46A9316045AFAA3BB6959F37678CF661F1B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
274
DNS requests
192
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5952 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
5952 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
4000 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
6724 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | unknown |
6192 | 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | GET | 200 | 95.179.240.76:80 | http://geo.dvdvideosoft.com/?instType=country | unknown | — | — | unknown |
6192 | 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | POST | 200 | 45.76.84.8:80 | http://stats.dvdvideosoft.com/AddEventJSONString.php | unknown | — | — | unknown |
6192 | 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | GET | 200 | 95.179.240.76:80 | http://geo.dvdvideosoft.com/?instType=country | unknown | — | — | unknown |
6192 | 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | POST | 200 | 45.76.84.8:80 | http://stats.dvdvideosoft.com/AddEventJSONString.php | unknown | — | — | unknown |
6192 | 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | POST | 200 | 142.250.185.174:80 | http://www.google-analytics.com/collect?v=1&tid=UA-72940219-1&cid=064FC2CA-3124-459B-BB9F-98156511D7F6&ds=app&an=Free%20YouTube%20Download&aid=FreeYTVDownloader&av=4.4.0.528&ua=FreeYTVDownloader/4.4.0.528%20(Windows%20NT%2010.0.SP0%20)&ul=en&sc=start&t=event&ec=source&ea=undefined&cd4=(unknown)&el=4.4.0.528&sc=end | unknown | — | — | unknown |
6192 | 506a508b6a6f236185fd9c2689f548c7085948ceb0e99cc8d5c7c2b81bbe80f9.tmp | POST | 200 | 142.250.185.174:80 | http://www.google-analytics.com/collect?v=1&tid=UA-72940219-1&cid=064FC2CA-3124-459B-BB9F-98156511D7F6&ds=app&an=Free%20YouTube%20Download&aid=FreeYTVDownloader&av=4.4.0.528&ua=FreeYTVDownloader/4.4.0.528%20(Windows%20NT%2010.0.SP0%20)&ul=en&sc=start&t=event&ec=start_offline&ea=sc&el=4.4.0.528&sc=end | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | unknown |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
— | — | 239.255.255.250:1900 | — | — | — | unknown |
5952 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
5952 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
— | — | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
4000 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | unknown |
4680 | SearchApp.exe | 95.100.146.27:443 | — | Akamai International B.V. | CZ | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
tools.dvdvideosoft.net |
| unknown |
arc.msn.com |
| whitelisted |
geo.dvdvideosoft.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
Process | Message |
|---|---|
vidnotifier.exe | Timeout in secs: 1800
|
FreeYTVDownloader.exe | libpng warning: iCCP: cHRM chunk does not match sRGB
|
FreeYTVDownloader.exe | libpng warning: iCCP: known incorrect sRGB profile
|
FreeYTVDownloader.exe | libpng warning: iCCP: cHRM chunk does not match sRGB
|
FreeYTVDownloader.exe | libpng warning: iCCP: known incorrect sRGB profile
|
FreeYTVDownloader.exe | libpng warning: iCCP: known incorrect sRGB profile
|
FreeYTVDownloader.exe | libpng warning: iCCP: cHRM chunk does not match sRGB
|
FreeYTVDownloader.exe | libpng warning: iCCP: known incorrect sRGB profile
|
FreeYTVDownloader.exe | libpng warning: iCCP: cHRM chunk does not match sRGB
|
FreeYTVDownloader.exe | libpng warning: iCCP: cHRM chunk does not match sRGB
|