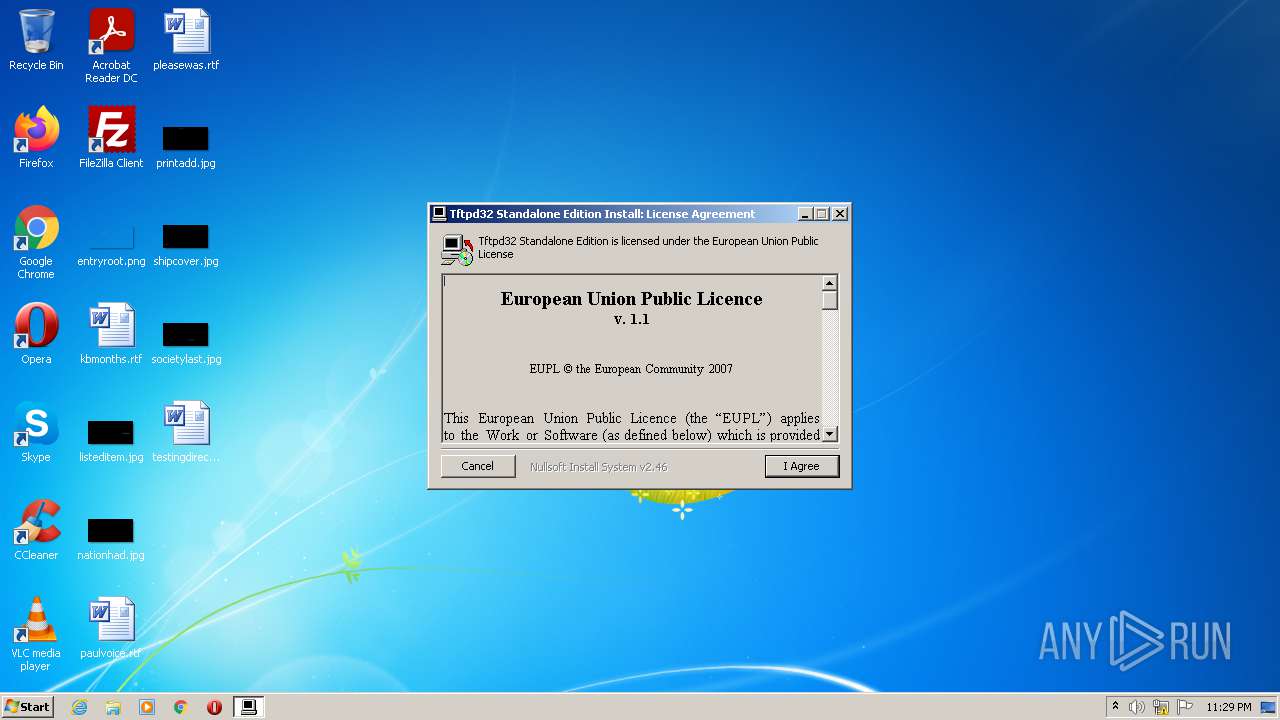
| File name: | Tftpd32-4.60-setup.exe |
| Full analysis: | https://app.any.run/tasks/ce57a10e-7dd5-4cb5-a03e-2347b1219952 |
| Verdict: | Malicious activity |
| Analysis date: | September 24, 2021, 22:29:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 049B11FE3AD4C8E4F36AEE4148F420DC |
| SHA1: | D87138CDF840BE0CBCB6C7D6068A4C0EC3196F09 |
| SHA256: | 50691B9081C9A706B7A806AD5CA16C7D3194FC06CC9402BCBA8DF148894E6BFF |
| SSDEEP: | 12288:vYPfJc0uNKLzmjXofmInufKDAn8M9gideJZiTO4B:vYnzz4XHfdkJYq4B |
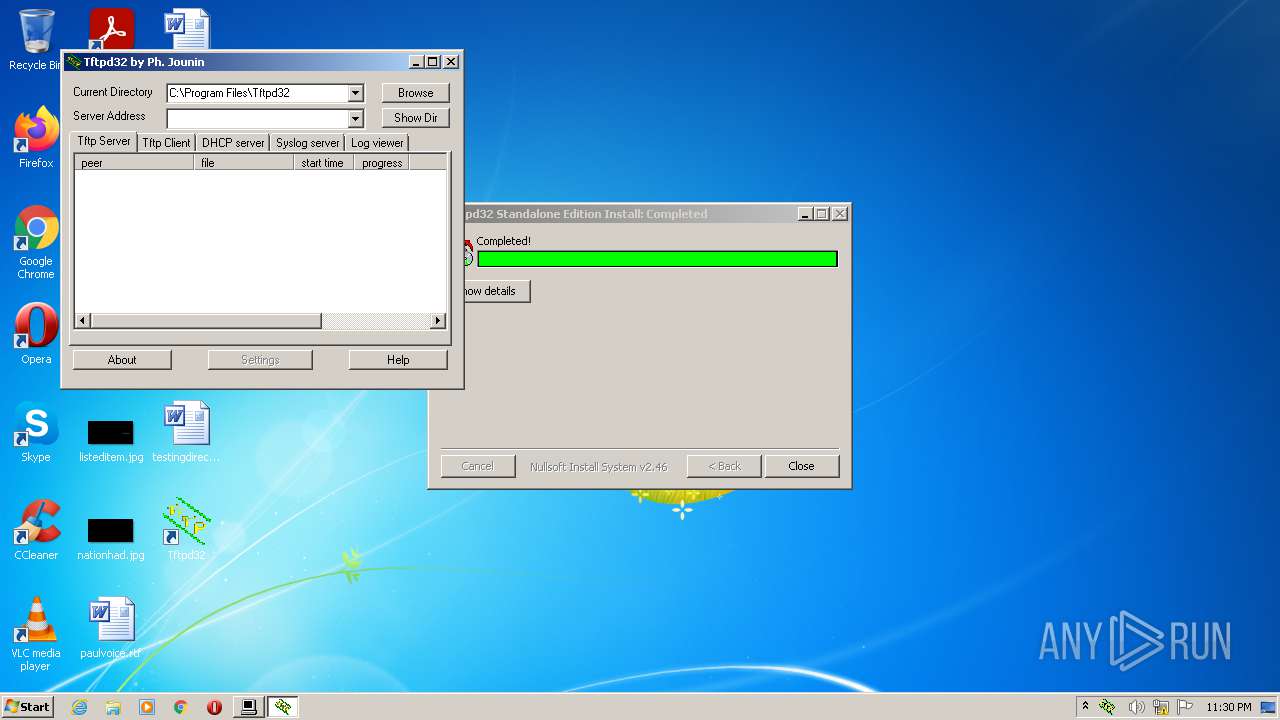
MALICIOUS
Application was dropped or rewritten from another process
- Tftpd32.exe (PID: 1868)
SUSPICIOUS
Checks supported languages
- Tftpd32-4.60-setup.exe (PID: 1456)
- Tftpd32.exe (PID: 1868)
Reads the computer name
- Tftpd32-4.60-setup.exe (PID: 1456)
- Tftpd32.exe (PID: 1868)
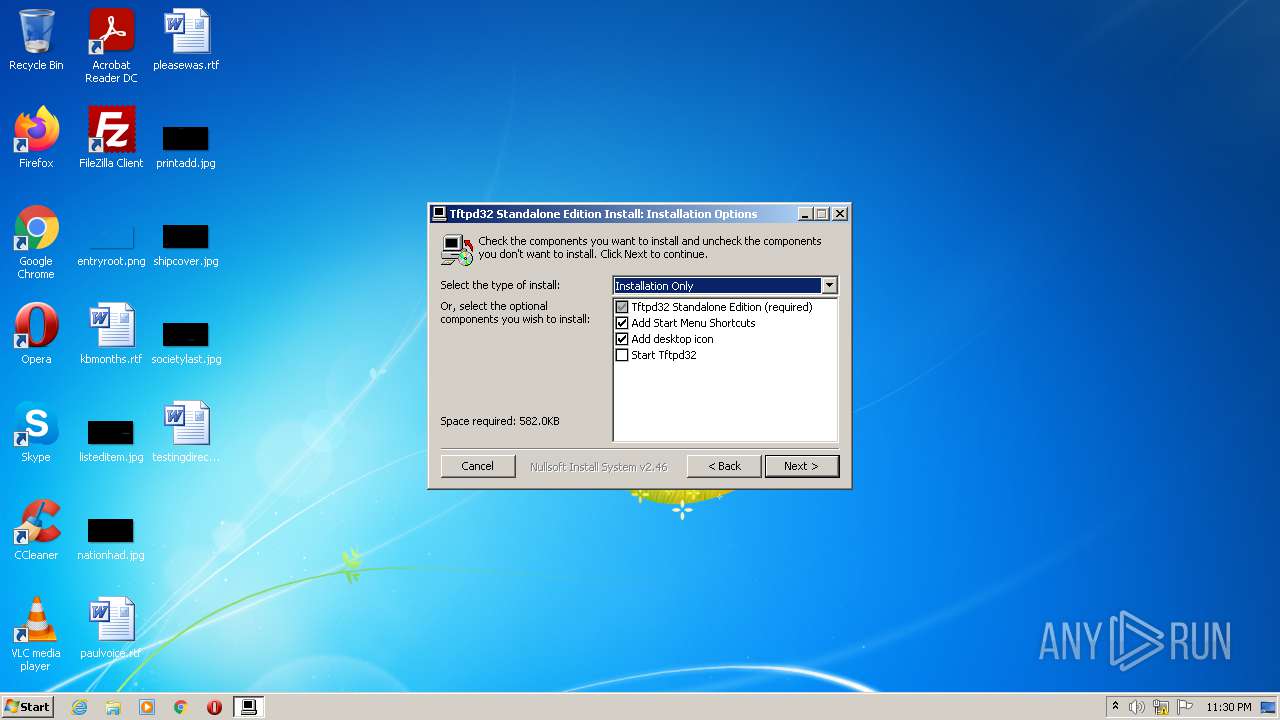
Creates files in the program directory
- Tftpd32-4.60-setup.exe (PID: 1456)
Creates a directory in Program Files
- Tftpd32-4.60-setup.exe (PID: 1456)
Executable content was dropped or overwritten
- Tftpd32-4.60-setup.exe (PID: 1456)
Creates a software uninstall entry
- Tftpd32-4.60-setup.exe (PID: 1456)
Drops a file with too old compile date
- Tftpd32-4.60-setup.exe (PID: 1456)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x30fa |
| UninitializedDataSize: | 1024 |
| InitializedDataSize: | 164864 |
| CodeSize: | 24064 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2009:12:05 23:50:52+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:52 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005C4C | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44011 |
.rdata | 0x00007000 | 0x0000129C | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04684 |
.data | 0x00009000 | 0x00025C58 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.801 |
.ndata | 0x0002F000 | 0x00008000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00037000 | 0x000010A8 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.42529 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.52631 | 744 | UNKNOWN | English - United States | RT_ICON |
2 | 2.76386 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.74309 | 184 | UNKNOWN | English - United States | RT_DIALOG |
103 | 1.97134 | 34 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.6935 | 316 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.89971 | 284 | UNKNOWN | English - United States | RT_DIALOG |
107 | 2.62276 | 196 | UNKNOWN | English - United States | RT_DIALOG |
110 | 3.22336 | 872 | UNKNOWN | English - United States | RT_BITMAP |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
40
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1456 | "C:\Users\admin\AppData\Local\Temp\Tftpd32-4.60-setup.exe" | C:\Users\admin\AppData\Local\Temp\Tftpd32-4.60-setup.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
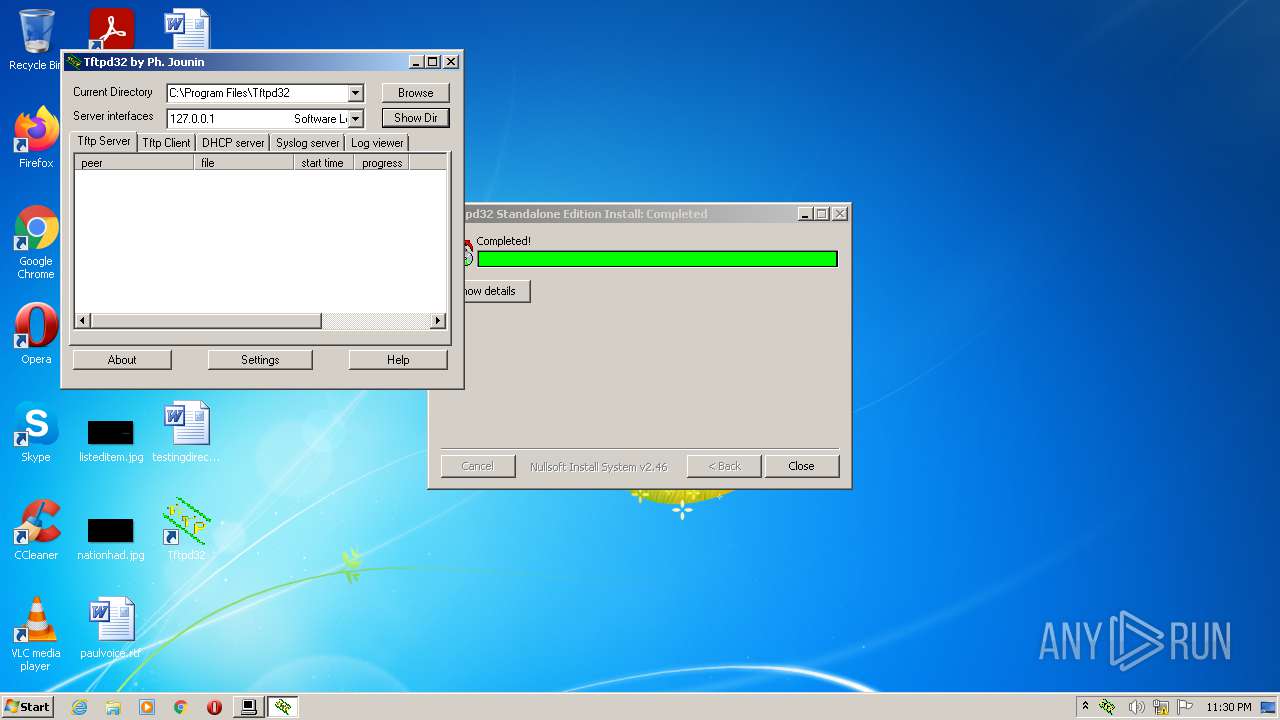
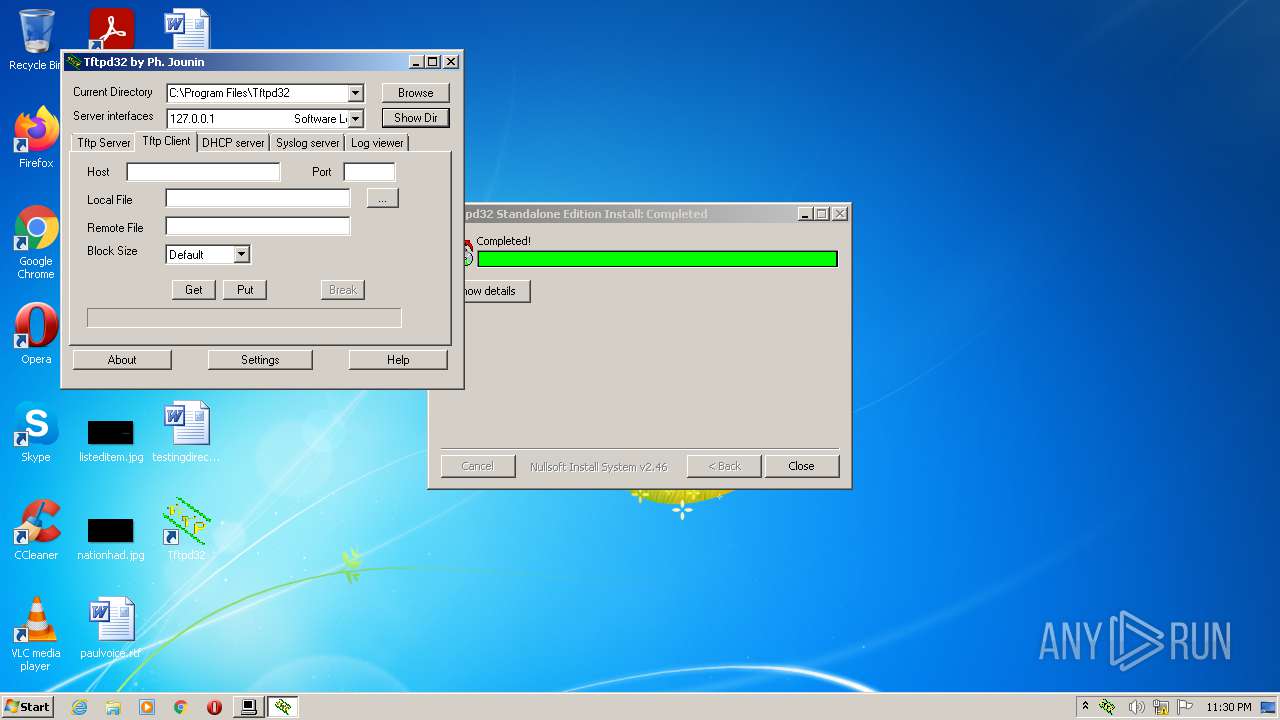
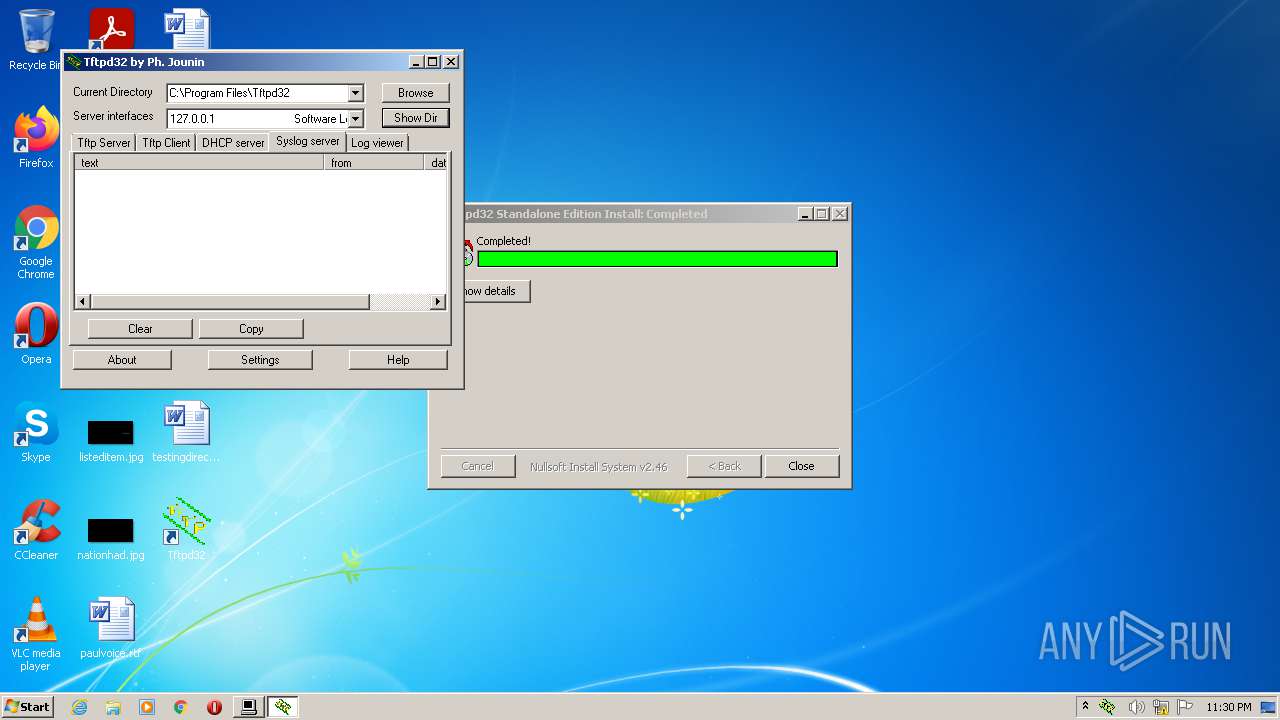
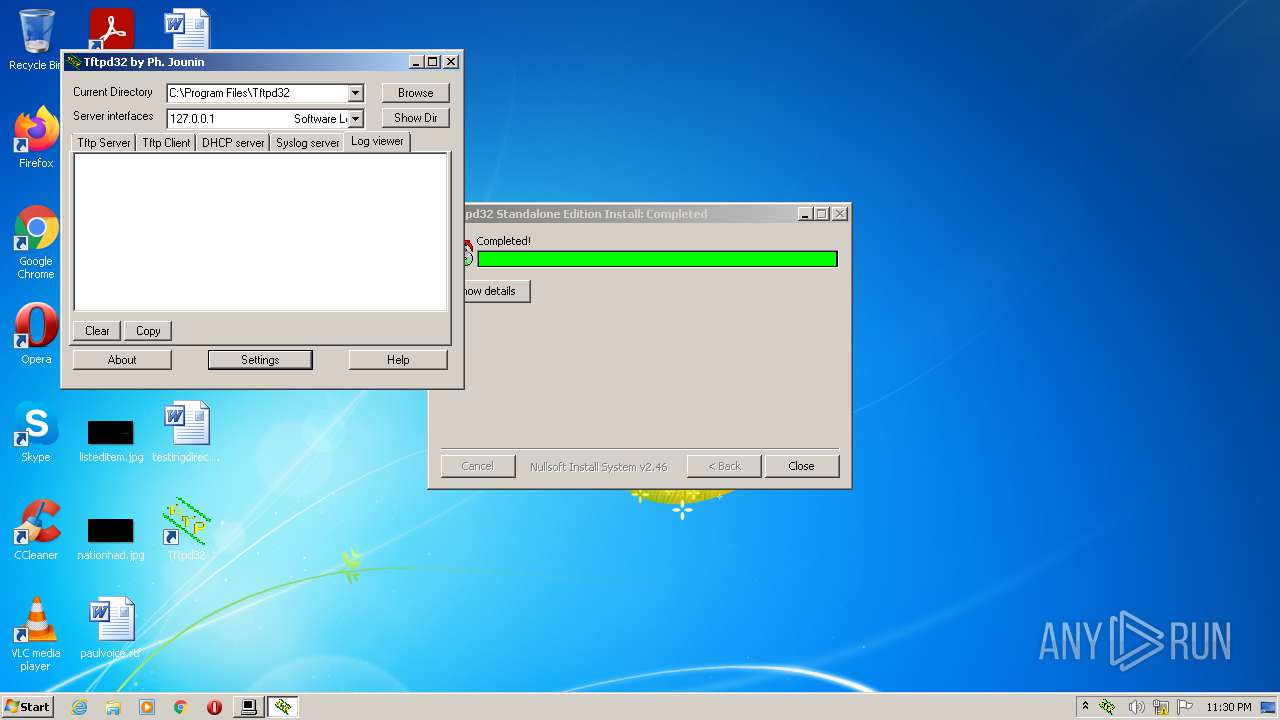
| 1868 | "C:\Program Files\Tftpd32\Tftpd32.exe" | C:\Program Files\Tftpd32\Tftpd32.exe | Tftpd32-4.60-setup.exe | ||||||||||||
User: admin Company: Ph. Jounin Integrity Level: HIGH Description: TFTP server Exit code: 0 Modules
| |||||||||||||||
| 3584 | "C:\Users\admin\AppData\Local\Temp\Tftpd32-4.60-setup.exe" | C:\Users\admin\AppData\Local\Temp\Tftpd32-4.60-setup.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
1 154
Read events
1 149
Write events
5
Delete events
0
Modification events
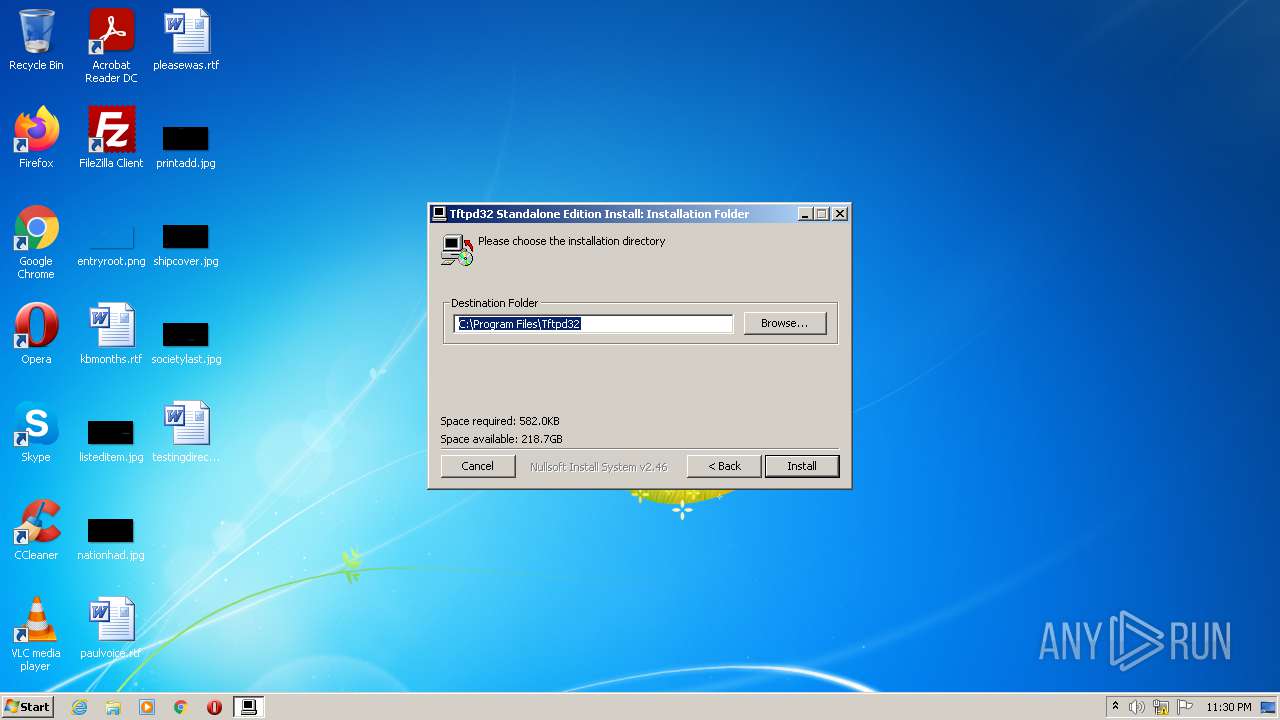
| (PID) Process: | (1456) Tftpd32-4.60-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Tftpd32 |
| Operation: | write | Name: | Install_Dir |
Value: C:\Program Files\Tftpd32 | |||
| (PID) Process: | (1456) Tftpd32-4.60-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Tftpd32 |
| Operation: | write | Name: | DisplayName |
Value: Tftpd32 Standalone Edition (remove only) | |||
| (PID) Process: | (1456) Tftpd32-4.60-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Tftpd32 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\Tftpd32\uninstall.exe" | |||
| (PID) Process: | (1456) Tftpd32-4.60-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Tftpd32 |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (1456) Tftpd32-4.60-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Tftpd32 |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
Executable files
2
Suspicious files
1
Text files
1
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1456 | Tftpd32-4.60-setup.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Tftpd32\Uninstall.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1456 | Tftpd32-4.60-setup.exe | C:\Users\admin\Desktop\Tftpd32.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1456 | Tftpd32-4.60-setup.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Tftpd32\Tftpd32 Settings.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1456 | Tftpd32-4.60-setup.exe | C:\Users\Administrator\Desktop\Tftpd32.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1456 | Tftpd32-4.60-setup.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Tftpd32\Tftpd32.lnk | lnk | |
MD5:— | SHA256:— | |||
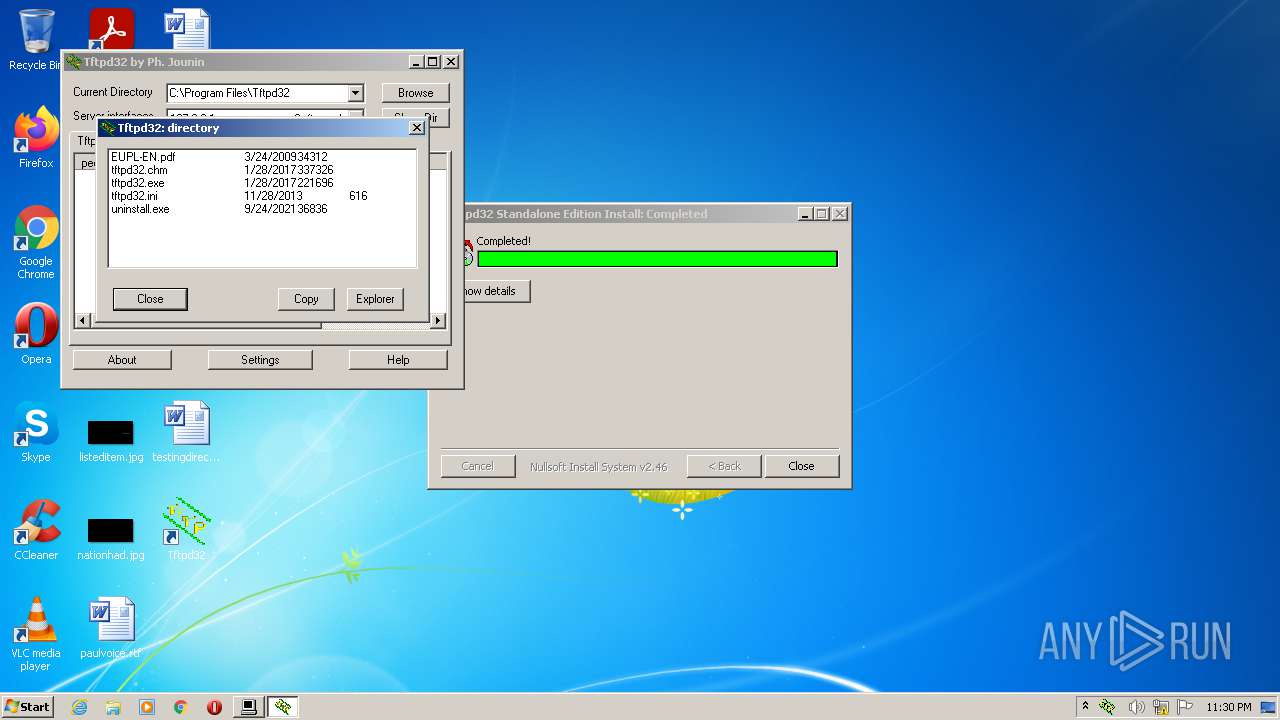
| 1456 | Tftpd32-4.60-setup.exe | C:\Program Files\Tftpd32\tftpd32.chm | chm | |
MD5:3578AFF8A6DADED8C4774C8E4053232A | SHA256:7E825CF03246CA285470D3B37E527BF053157B968880CB3E85E06FBB730B622E | |||
| 1456 | Tftpd32-4.60-setup.exe | C:\Program Files\Tftpd32\tftpd32.exe | executable | |
MD5:EFAB0F310705A21F8861A6F472358EF7 | SHA256:1E96B335BF6F20E05F0BBB62160C63ECC1FDC6711E393E6BB3893ABAED4CFAF6 | |||
| 1456 | Tftpd32-4.60-setup.exe | C:\Program Files\Tftpd32\tftpd32.ini | text | |
MD5:C973075D00B0BF2D5C4CB18155AD92FB | SHA256:0C00CBDAE4E3F2F430CA803E2E08BB3CBBA4E83CF9024DBB64DA212B8034E60D | |||
| 1456 | Tftpd32-4.60-setup.exe | C:\Program Files\Tftpd32\uninstall.exe | executable | |
MD5:E5433AF12383078C9F091E67A8793E82 | SHA256:7EEB001D20B13368E4EC895222087444CA3A5705D798C654B027AFF2C7A3BA13 | |||
| 1456 | Tftpd32-4.60-setup.exe | C:\Program Files\Tftpd32\EUPL-EN.pdf | ||
MD5:254B5DDBC15269E72BA3A0508681A70C | SHA256:CD5D9E2A925D8DAA92D083FD8C1CEA48DF1BCFFFD857F4F93E2148FDDC5001EC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
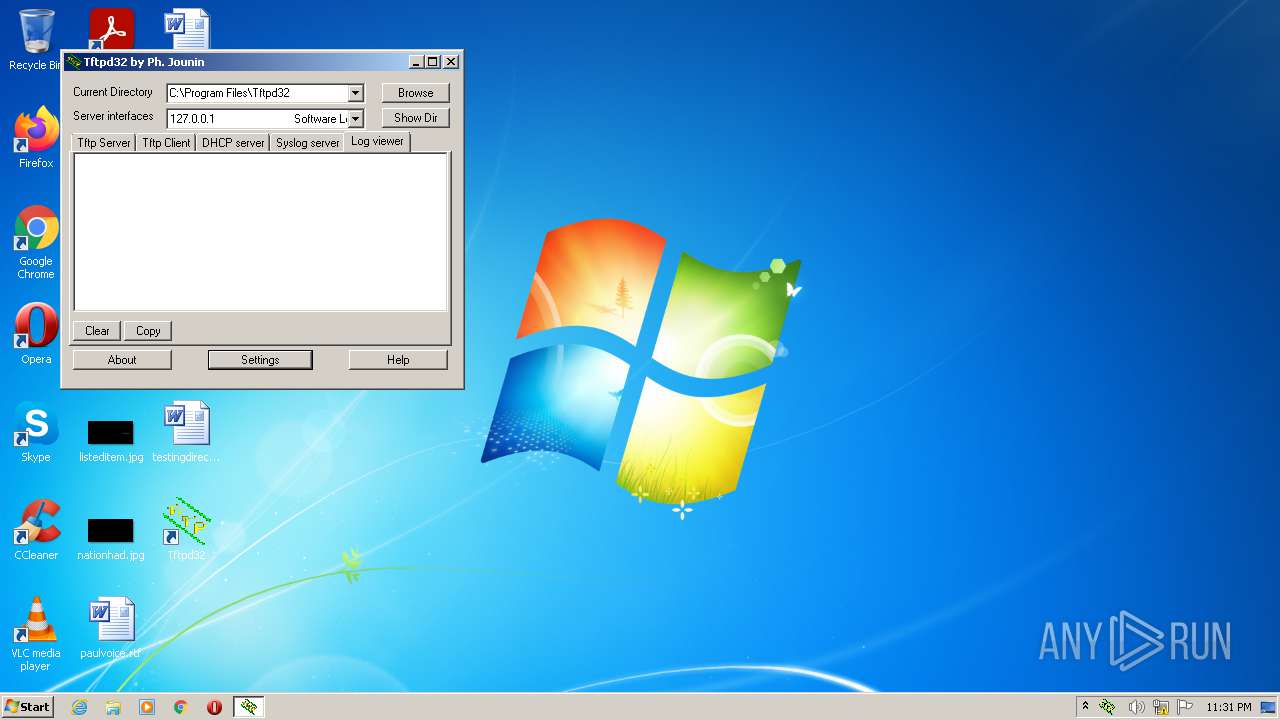
Tftpd32.exe | Th 2572 :opening comm socket
|
Tftpd32.exe | Th 2572 :Console disconnected |
Tftpd32.exe | Th 2476 :Port 17152 may be reused
|
Tftpd32.exe | Th 1836 :connected to console
|
Tftpd32.exe | Th 2572 :Verify Console/GUI parameters
|
Tftpd32.exe | Th 2572 :Version check OK
|
Tftpd32.exe | Th 1836 :GUI Version check OK
|
Tftpd32.exe | Th 2572 :Console connected |
Tftpd32.exe | Th 2436 :Scheduler signal received |
Tftpd32.exe | Th 1836 :GUI: new service 4 status 4
|