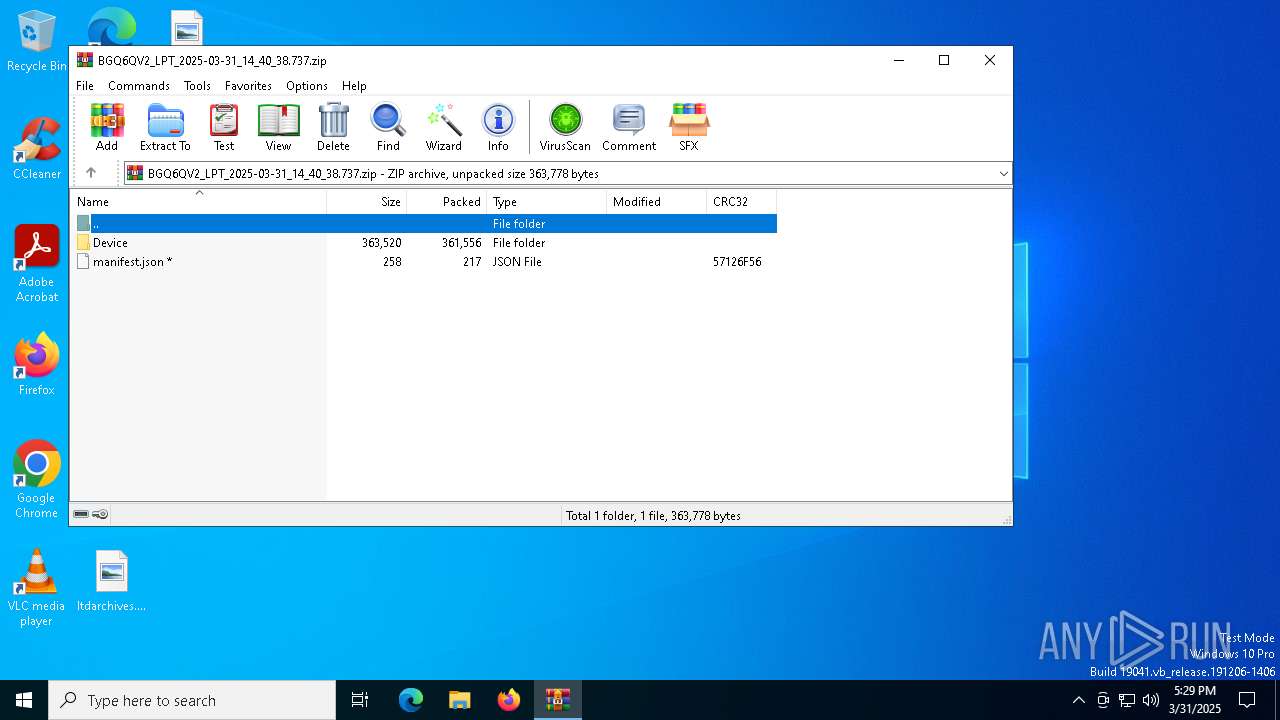
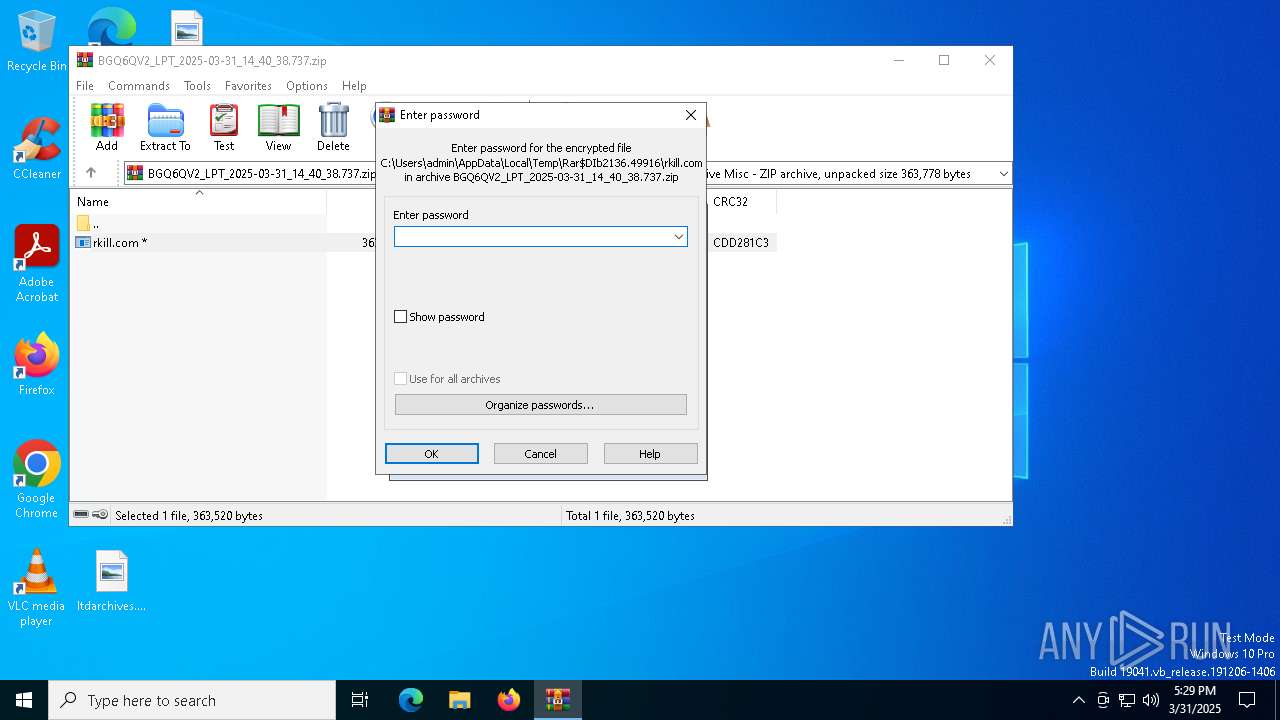
| File name: | BGQ6QV2_LPT_2025-03-31_14_40_38.737.zip |
| Full analysis: | https://app.any.run/tasks/b2ea6e9d-8c5b-4e27-9668-0f1973193961 |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2025, 17:29:37 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v4.5 to extract, compression method=deflate |
| MD5: | BF5162104050285AAC7238F61B6927D7 |
| SHA1: | C851D8314129C454158B4AE3544D02FDD0B1AFD9 |
| SHA256: | 505B1DC7E216C38C88610E659B75EDEC92C37F63665F1E94A0C8D7996EB17C5F |
| SSDEEP: | 12288:LB4xpSaD5OP1kOoWLDQhDKD4lMIATvFce7R:LWxpSaD5OP1kOoWLDkuD4lMdJce7R |
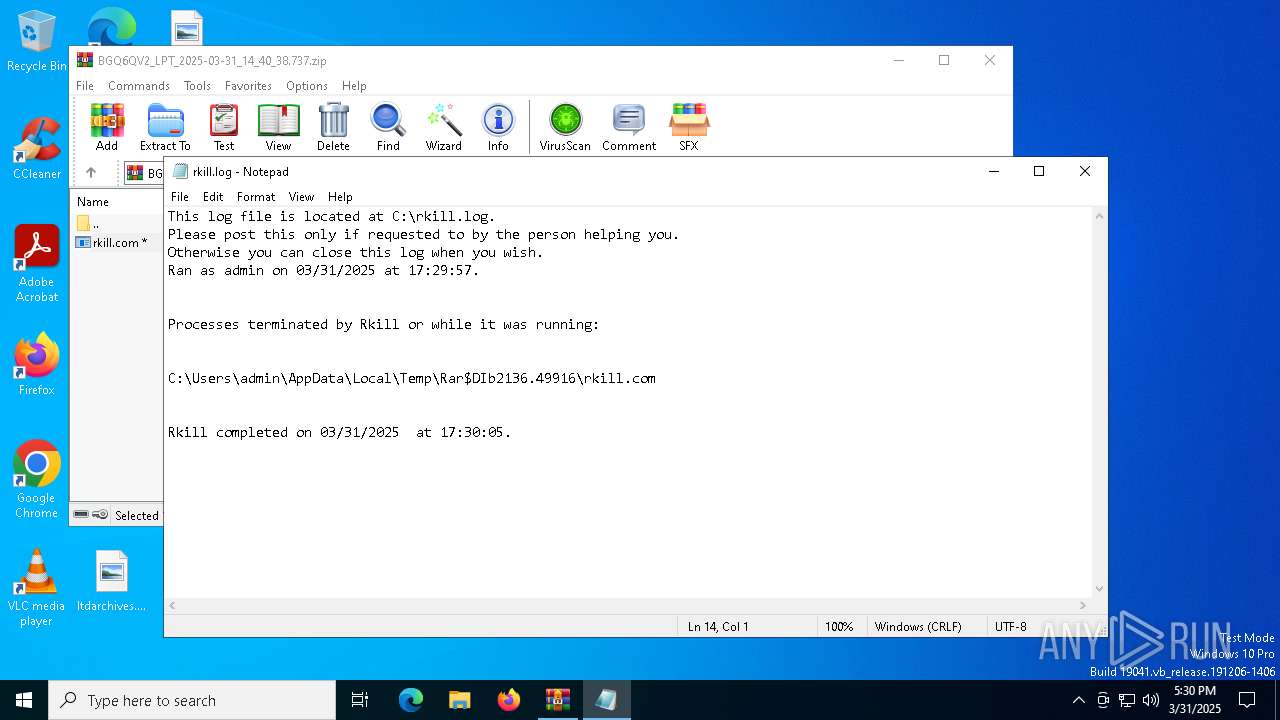
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2136)
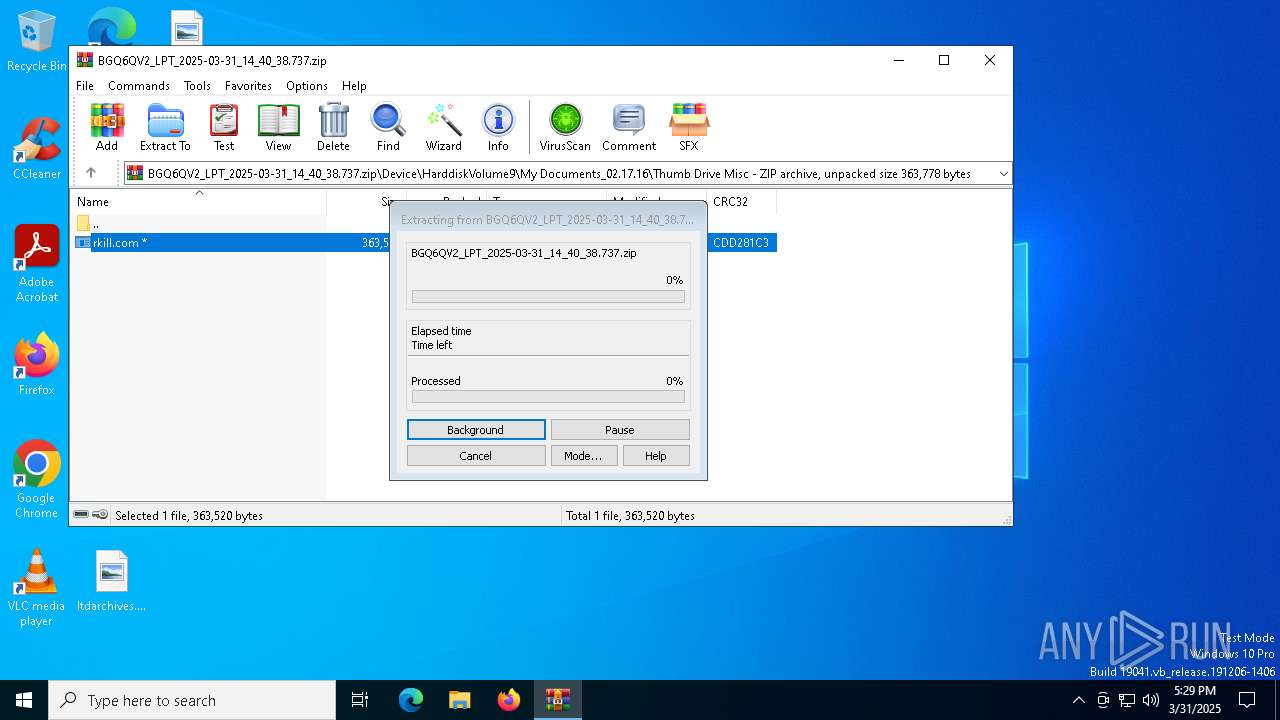
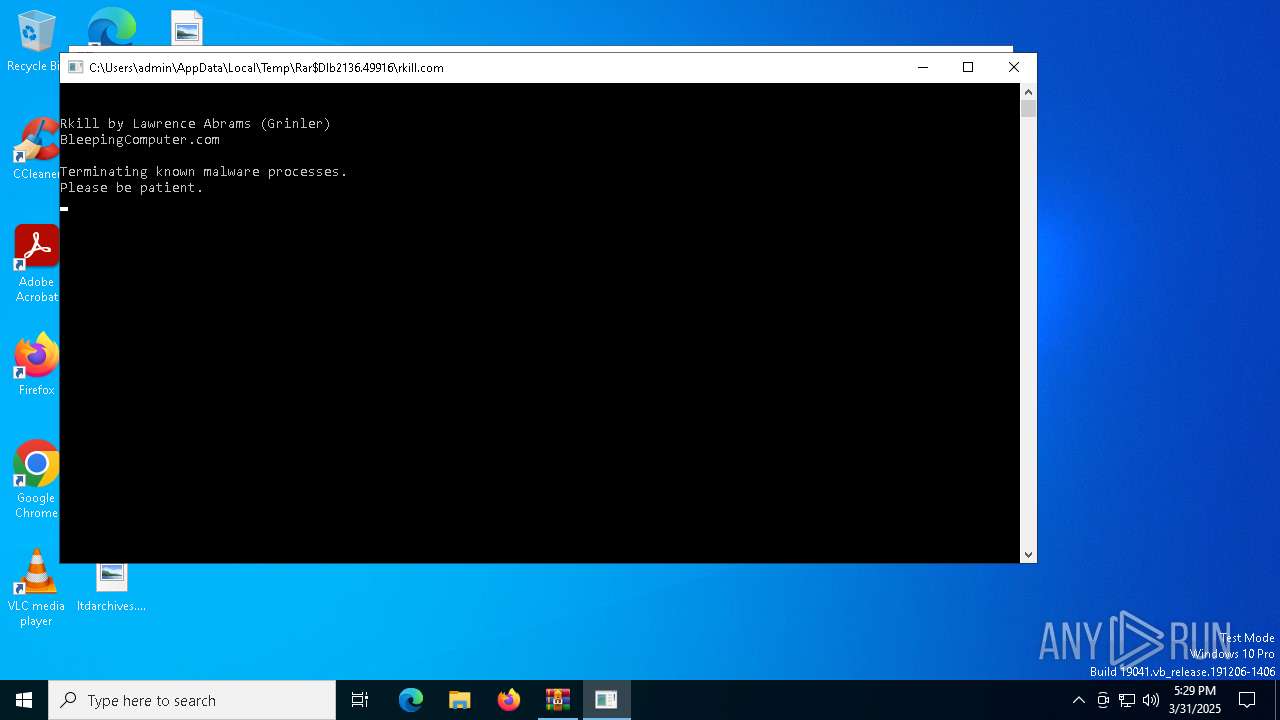
Starts application with an unusual extension
- WinRAR.exe (PID: 2136)
- cmd.exe (PID: 1164)
Executable content was dropped or overwritten
- rkill.com (PID: 4488)
Starts CMD.EXE for commands execution
- rkill.com (PID: 4488)
Executing commands from a ".bat" file
- rkill.com (PID: 4488)
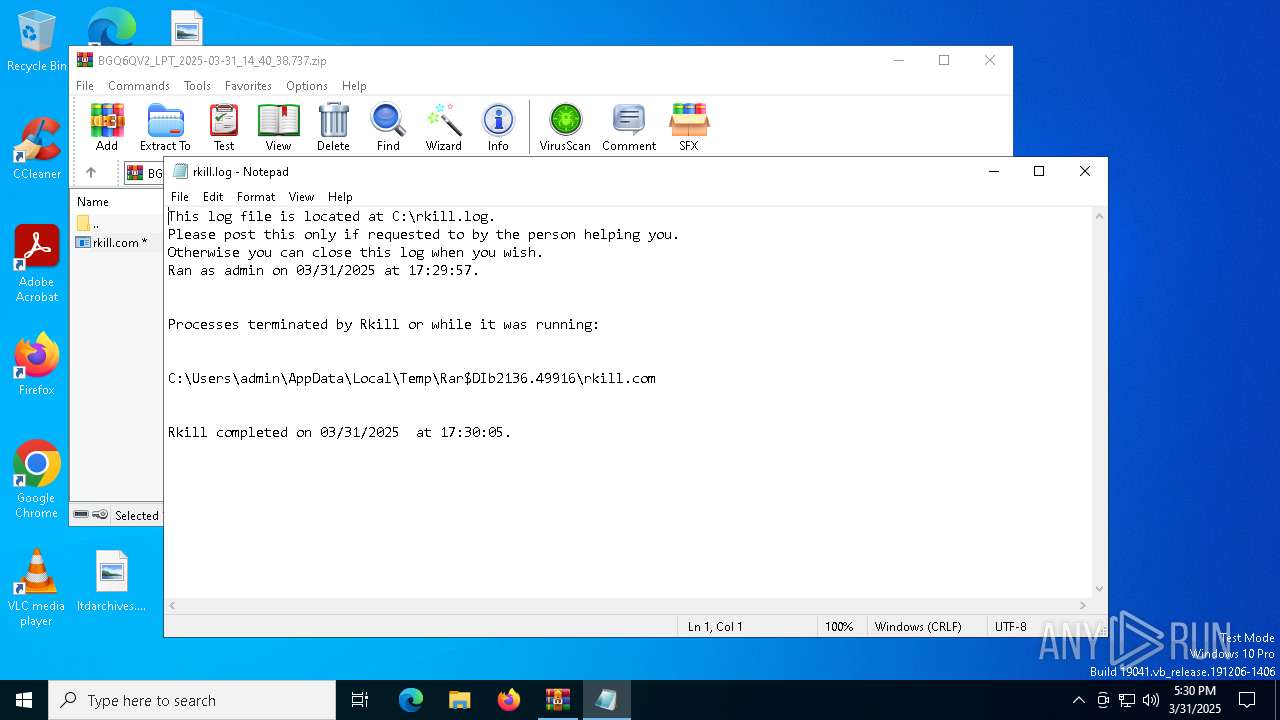
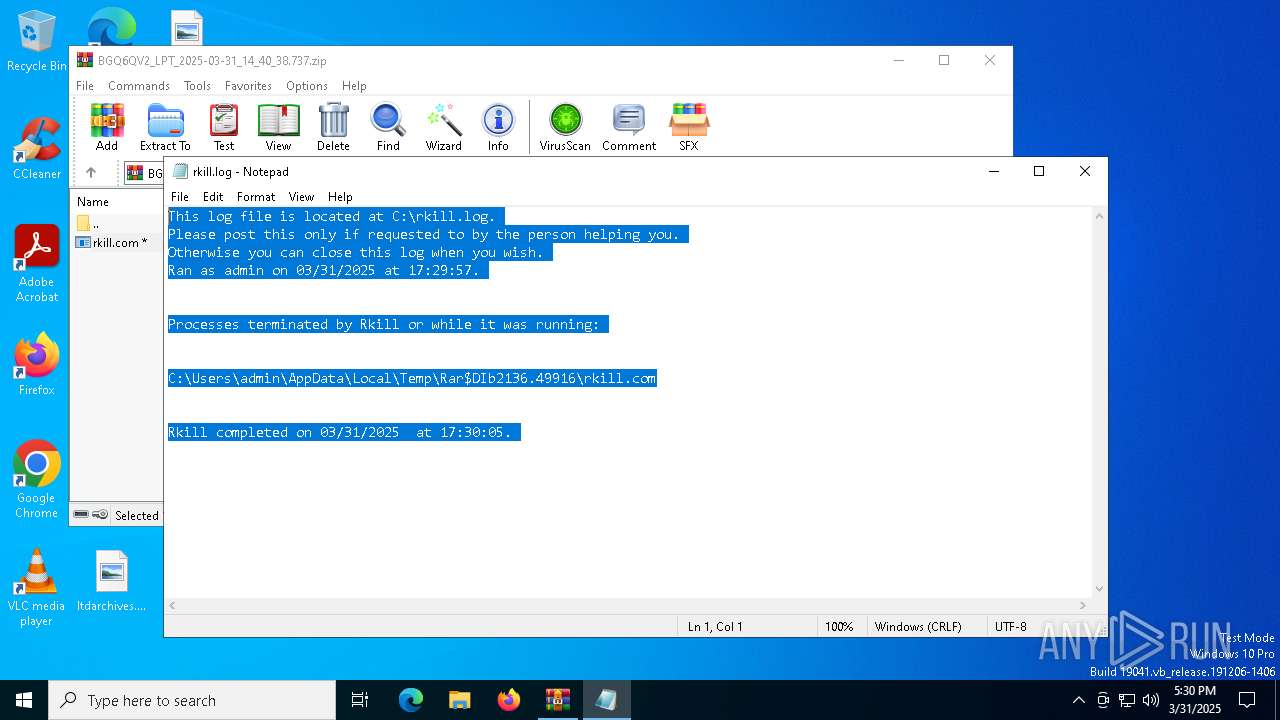
Creates file in the systems drive root
- cmd.exe (PID: 1164)
- notepad.exe (PID: 1012)
The executable file from the user directory is run by the CMD process
- pev.rkexe (PID: 5332)
- nircmdc.rkexe (PID: 864)
- nircmdc.rkexe (PID: 6156)
- nircmdc.rkexe (PID: 5008)
- nircmdc.rkexe (PID: 3884)
- nircmdc.rkexe (PID: 1348)
- nircmdc.rkexe (PID: 680)
- nircmdc.rkexe (PID: 516)
- pev.rkexe (PID: 4068)
- pev.rkexe (PID: 5384)
- pev.rkexe (PID: 1328)
- pev.rkexe (PID: 5964)
- nircmdc.rkexe (PID: 1324)
- pev.rkexe (PID: 960)
- pev.rkexe (PID: 2616)
- pev.rkexe (PID: 6032)
- pev.rkexe (PID: 2504)
- pev.rkexe (PID: 1096)
- pev.rkexe (PID: 1040)
- pev.rkexe (PID: 5408)
- pev.rkexe (PID: 4688)
- pev.rkexe (PID: 6708)
- pev.rkexe (PID: 6816)
- pev.rkexe (PID: 5772)
- pev.rkexe (PID: 7000)
- pev.rkexe (PID: 6560)
- pev.rkexe (PID: 4896)
- pev.rkexe (PID: 5256)
- pev.rkexe (PID: 2236)
- pev.rkexe (PID: 4724)
- sed.rkexe (PID: 5956)
- sed.rkexe (PID: 632)
- pev.rkexe (PID: 6676)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1164)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2136)
The sample compiled with english language support
- rkill.com (PID: 4488)
Create files in a temporary directory
- rkill.com (PID: 4488)
Checks supported languages
- rkill.com (PID: 4488)
- pev.rkexe (PID: 5332)
- nircmdc.rkexe (PID: 864)
- nircmdc.rkexe (PID: 6156)
- nircmdc.rkexe (PID: 1348)
- nircmdc.rkexe (PID: 5008)
- nircmdc.rkexe (PID: 516)
- nircmdc.rkexe (PID: 3884)
- nircmdc.rkexe (PID: 680)
- nircmdc.rkexe (PID: 1324)
- pev.rkexe (PID: 5384)
- pev.rkexe (PID: 1328)
- pev.rkexe (PID: 5964)
- pev.rkexe (PID: 4068)
- pev.rkexe (PID: 960)
- pev.rkexe (PID: 1040)
- pev.rkexe (PID: 2616)
- pev.rkexe (PID: 5408)
- pev.rkexe (PID: 6032)
- pev.rkexe (PID: 1096)
- pev.rkexe (PID: 2504)
- pev.rkexe (PID: 4688)
- pev.rkexe (PID: 6816)
- pev.rkexe (PID: 5772)
- pev.rkexe (PID: 7000)
- pev.rkexe (PID: 6708)
- pev.rkexe (PID: 4896)
- pev.rkexe (PID: 5256)
- pev.rkexe (PID: 2236)
- pev.rkexe (PID: 6560)
- pev.rkexe (PID: 4724)
- sed.rkexe (PID: 5956)
- sed.rkexe (PID: 632)
- pev.rkexe (PID: 6676)
Reads the computer name
- pev.rkexe (PID: 5332)
- pev.rkexe (PID: 5384)
- pev.rkexe (PID: 960)
- pev.rkexe (PID: 1328)
- pev.rkexe (PID: 4068)
- pev.rkexe (PID: 5964)
- pev.rkexe (PID: 1040)
- pev.rkexe (PID: 5408)
- pev.rkexe (PID: 2616)
- pev.rkexe (PID: 2504)
- pev.rkexe (PID: 1096)
- pev.rkexe (PID: 6708)
- pev.rkexe (PID: 6816)
- pev.rkexe (PID: 6032)
- pev.rkexe (PID: 7000)
- pev.rkexe (PID: 4688)
- pev.rkexe (PID: 2236)
- pev.rkexe (PID: 6560)
- pev.rkexe (PID: 5772)
- pev.rkexe (PID: 5256)
- pev.rkexe (PID: 4896)
- pev.rkexe (PID: 4724)
- pev.rkexe (PID: 6676)
NirSoft software is detected
- nircmdc.rkexe (PID: 864)
- nircmdc.rkexe (PID: 6156)
- nircmdc.rkexe (PID: 516)
- nircmdc.rkexe (PID: 5008)
- nircmdc.rkexe (PID: 3884)
- nircmdc.rkexe (PID: 1348)
- nircmdc.rkexe (PID: 680)
- nircmdc.rkexe (PID: 1324)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0801 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0xcdd281c3 |
| ZipCompressedSize: | 361556 |
| ZipUncompressedSize: | 363520 |
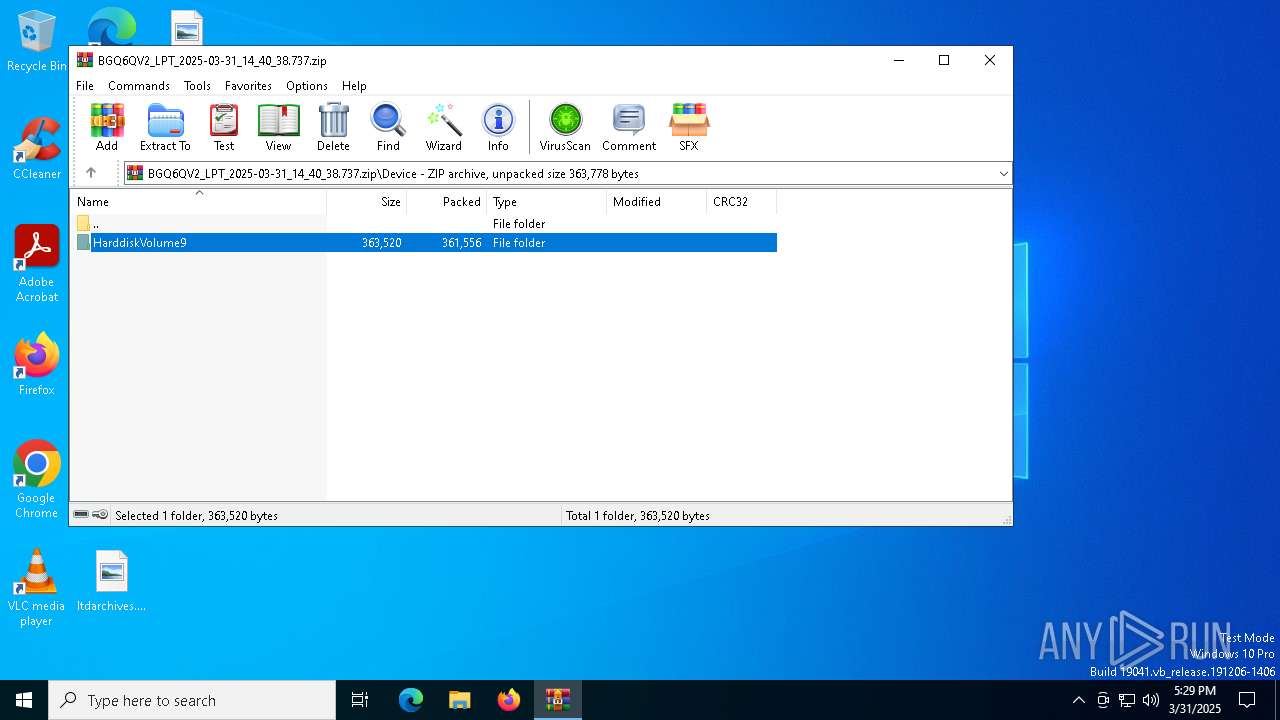
| ZipFileName: | Device/HarddiskVolume9/My Documents_02.17.16/Thumb Drive Misc/rkill.com |
Total processes
169
Monitored processes
42
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | nircmdc.rkexe win close stitle "Antivirus Soft" | C:\Users\admin\AppData\Local\Temp\F118.tmp\nircmdc.rkexe | — | cmd.exe | |||||||||||
User: admin Company: NirSoft Integrity Level: HIGH Description: NirCmd Exit code: 4206720 Version: 2.37 Modules
| |||||||||||||||
| 632 | sed.rkexe s/\\??\\// C:\Users\admin\AppData\Local\Temp\rke1.log | C:\Users\admin\AppData\Local\Temp\F118.tmp\sed.rkexe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 680 | nircmdc.rkexe win close stitle "Security Central" | C:\Users\admin\AppData\Local\Temp\F118.tmp\nircmdc.rkexe | — | cmd.exe | |||||||||||
User: admin Company: NirSoft Integrity Level: HIGH Description: NirCmd Exit code: 4206720 Version: 2.37 Modules
| |||||||||||||||
| 864 | nircmdc.rkexe win close stitle "Antivirus Suite" | C:\Users\admin\AppData\Local\Temp\F118.tmp\nircmdc.rkexe | — | cmd.exe | |||||||||||
User: admin Company: NirSoft Integrity Level: HIGH Description: NirCmd Exit code: 4206720 Version: 2.37 Modules
| |||||||||||||||
| 960 | PEV.rkexe -k "C:\Users\admin\local settings\application data\*.exe" | C:\Users\admin\AppData\Local\Temp\F118.tmp\pev.rkexe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 4 Modules
| |||||||||||||||
| 1012 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\rkill.log | C:\Windows\SysWOW64\notepad.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | PEV.rkexe -k "C:\ProgramData\*" | C:\Users\admin\AppData\Local\Temp\F118.tmp\pev.rkexe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 4 Modules
| |||||||||||||||
| 1096 | PEV.rkexe -k restore.exe | C:\Users\admin\AppData\Local\Temp\F118.tmp\pev.rkexe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 4 Modules
| |||||||||||||||
| 1164 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\F118.tmp\rkill.bat"" | C:\Windows\SysWOW64\cmd.exe | — | rkill.com | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | nircmdc.rkexe win close stitle "Security essentials" | C:\Users\admin\AppData\Local\Temp\F118.tmp\nircmdc.rkexe | — | cmd.exe | |||||||||||
User: admin Company: NirSoft Integrity Level: HIGH Description: NirCmd Exit code: 4206720 Version: 2.37 Modules
| |||||||||||||||
Total events
3 870
Read events
3 847
Write events
10
Delete events
13
Modification events
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\BGQ6QV2_LPT_2025-03-31_14_40_38.737.zip | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2136) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (1164) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.log\OpenWithProgids |
| Operation: | write | Name: | txtfile |
Value: | |||
Executable files
5
Suspicious files
1
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1164 | cmd.exe | C:\Users\admin\AppData\Local\Temp\rkstart.log | — | |
MD5:— | SHA256:— | |||
| 1164 | cmd.exe | C:\Users\admin\AppData\Local\Temp\rks1.log | text | |
MD5:— | SHA256:— | |||
| 4488 | rkill.com | C:\Users\admin\AppData\Local\Temp\F118.tmp\nircmdc.rkexe | executable | |
MD5:9CB3A38088807F54E7F89AC30E09C030 | SHA256:71579B7BB651004F9C2E3F8D62511F610443C7E8225001865415A4620BD04219 | |||
| 4488 | rkill.com | C:\Users\admin\AppData\Local\Temp\F118.tmp\proc.dat | text | |
MD5:3DCA7418EDC2C8D6D0858C4847719BBE | SHA256:8E70491202C2311A0C05C606E1024586ACE7C69554D24AF16C84CA7AE2A0D5B2 | |||
| 1164 | cmd.exe | C:\Users\admin\AppData\Local\Temp\F118.tmp\ncmd.cfxxe | text | |
MD5:3DCA7418EDC2C8D6D0858C4847719BBE | SHA256:8E70491202C2311A0C05C606E1024586ACE7C69554D24AF16C84CA7AE2A0D5B2 | |||
| 2136 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb2136.49916\rkill.com | executable | |
MD5:71CB69BC10E8B6CCCD15C4EF19B9F1EB | SHA256:398D375BB20BE08751A273E249DDFE0BD7A5235D5D201244E3B0FC88115FA3E1 | |||
| 4488 | rkill.com | C:\Users\admin\AppData\Local\Temp\F118.tmp\nircmd.rkexe | executable | |
MD5:AC6094297CD882B8626466CDEB64F19F | SHA256:27C7FFD8367AAA73155FBB287A7DF1F157F2D0C3323DBB176D02B36FF616FCA5 | |||
| 4488 | rkill.com | C:\Users\admin\AppData\Local\Temp\F118.tmp\sed.rkexe | executable | |
MD5:3A34D017AA4E5C11F2A329AB04DA17F4 | SHA256:21A9D5EEE6CA1B6D3AA1FC64B3B53D0846EDF8A698AD7924D1321857F708001F | |||
| 4488 | rkill.com | C:\Users\admin\AppData\Local\Temp\F118.tmp\pev.rkexe | executable | |
MD5:3B44E6B3653FABDF876BC2B13C434E62 | SHA256:21793F8B54906EBD1DADA5BC350BAE8399E49409C889BF6DC6294ACB13BAF797 | |||
| 1164 | cmd.exe | C:\Users\admin\AppData\Local\Temp\rkend.log | text | |
MD5:C21D6E318D0DDA2EECC367076504BA3B | SHA256:094F1330AA021827013B5A2EA5F79E93AB7E4CE74B28160569255A426251AAB5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
19
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6148 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6148 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.172.255.216:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6544 | svchost.exe | 40.126.31.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |