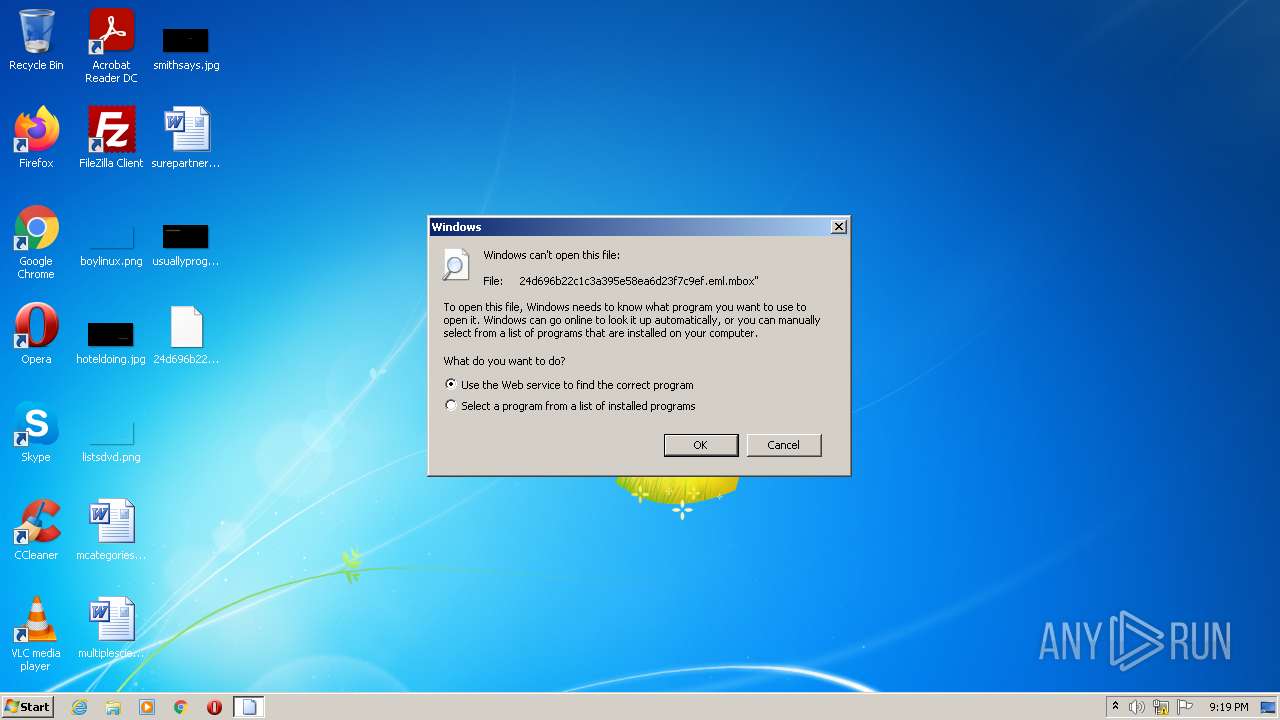
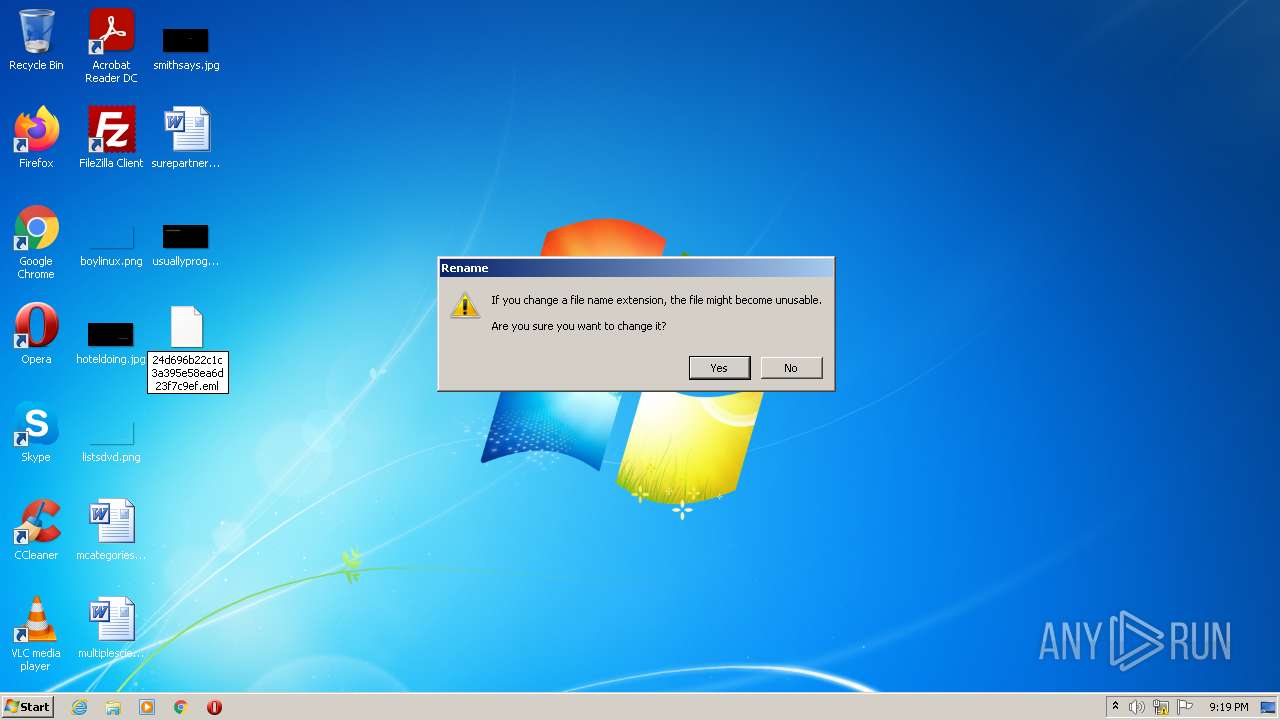
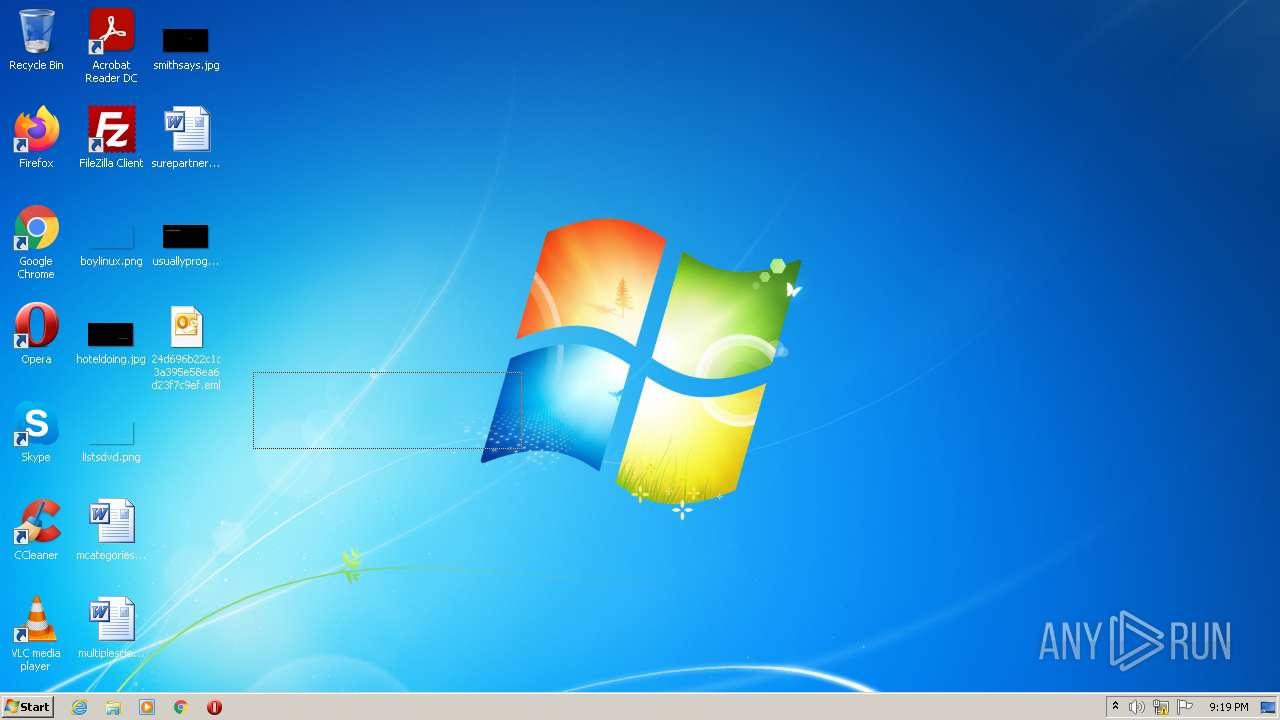
| File name: | 24d696b22c1c3a395e58ea6d23f7c9ef.eml |
| Full analysis: | https://app.any.run/tasks/8a858729-c63d-45f9-9e2f-efe4f00dd010 |
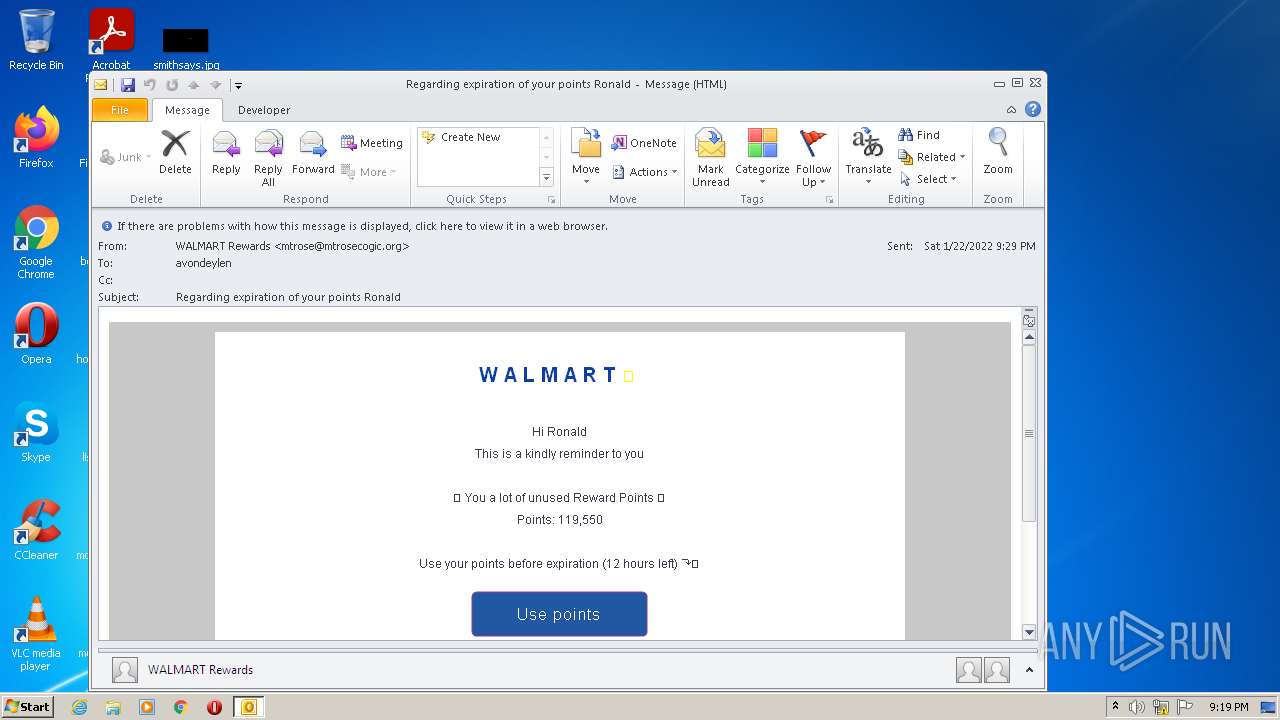
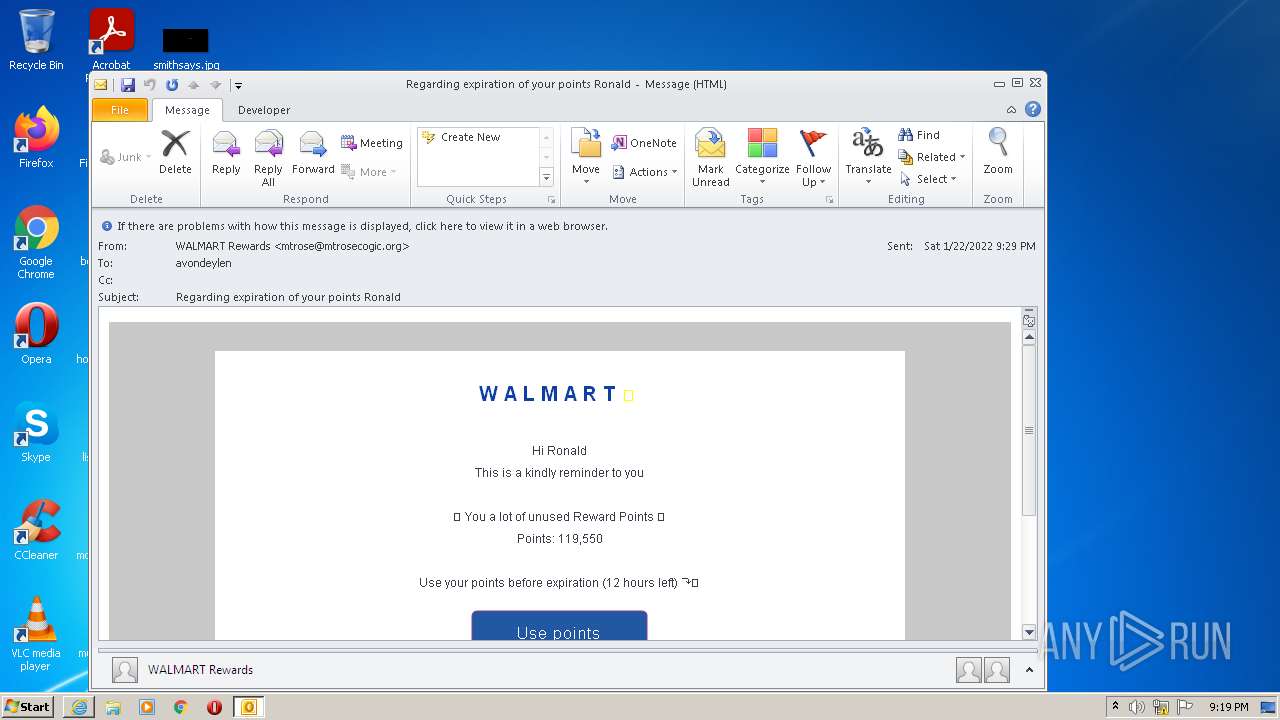
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 21:18:56 |
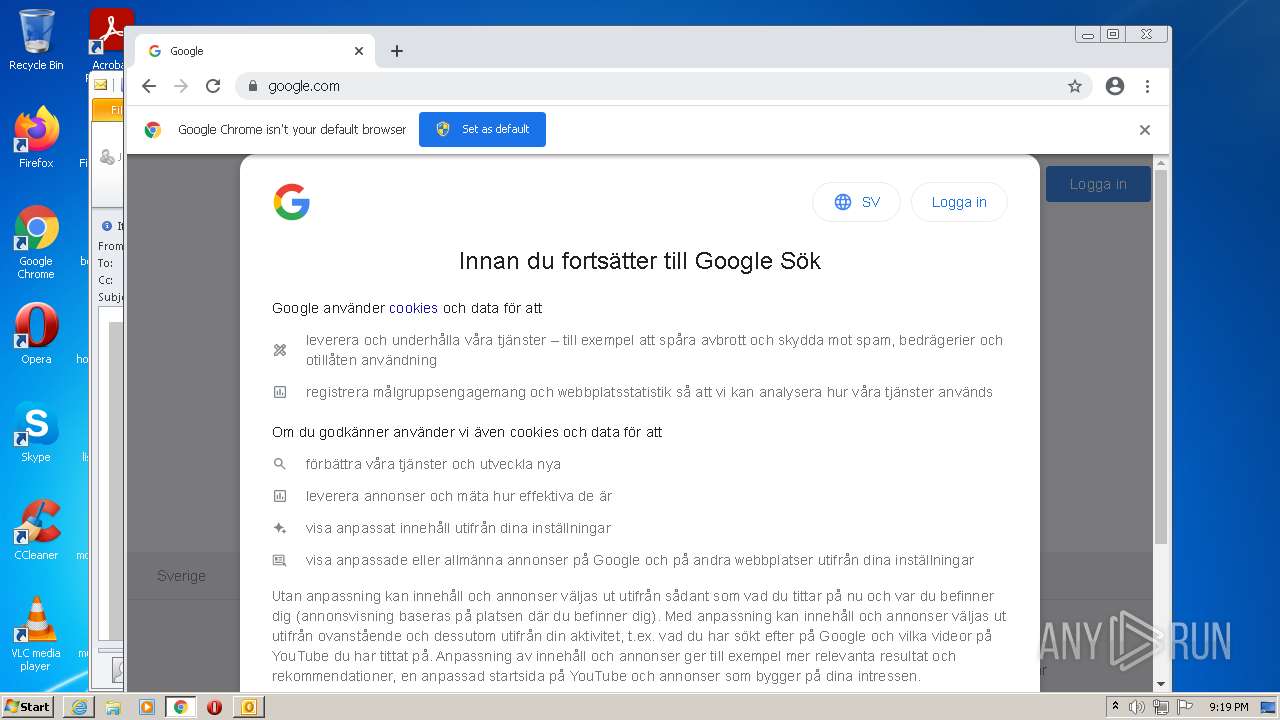
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF, LF line terminators |
| MD5: | FC41C8AF46349BD6F032466D25703119 |
| SHA1: | A13FBAB0DCF7C5DE7DFD1482B2864857B8CE0079 |
| SHA256: | 5052D04CE49FA31FA35EBD55D5CB66313FC93745E6288663C1A8CF37DBA5017F |
| SSDEEP: | 768:WWR/0ARGHOiOYiNoce3V7g0IiAw+kGHbiWsCDC46m71umWXQuTpxIM02ex0:WWR/0ARCOHYL3VWtsqfnsXPxIx6 |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 4008)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2300)
Checks supported languages
- OUTLOOK.EXE (PID: 2300)
Searches for installed software
- OUTLOOK.EXE (PID: 2300)
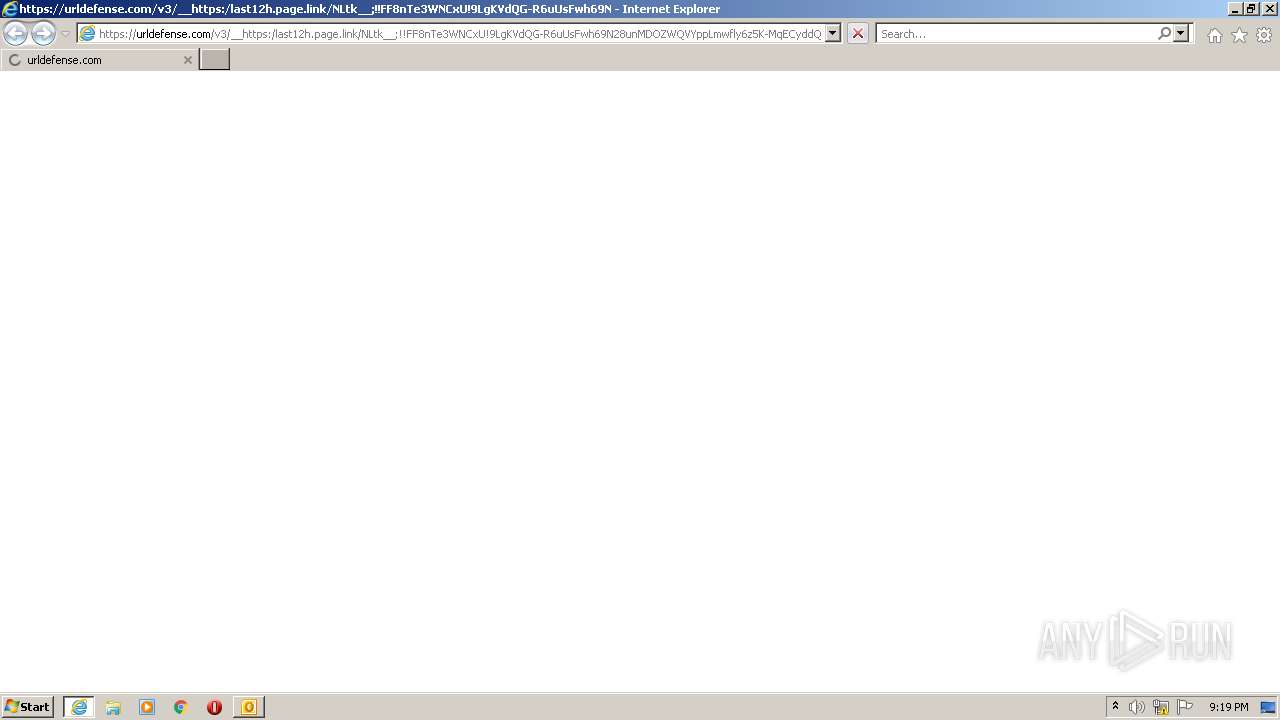
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2368)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2300)
Reads the computer name
- OUTLOOK.EXE (PID: 2300)
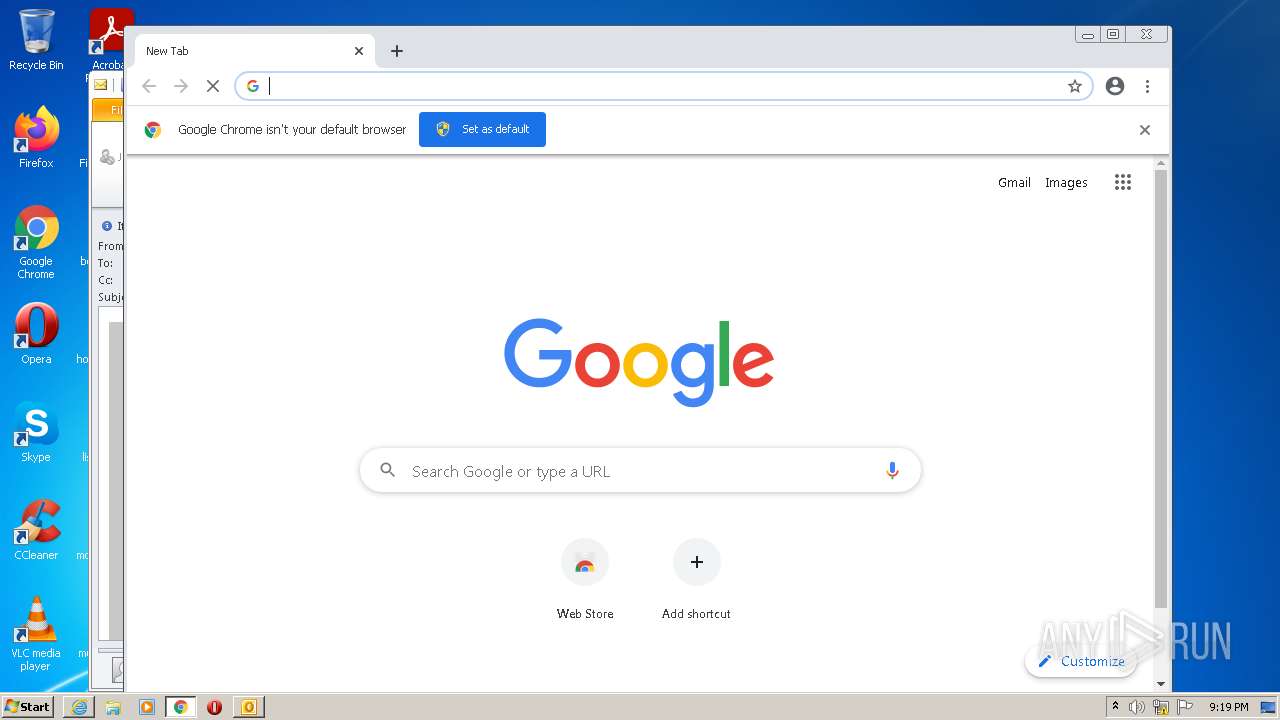
Modifies files in Chrome extension folder
- chrome.exe (PID: 2024)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 4008)
Executable content was dropped or overwritten
- chrome.exe (PID: 4008)
INFO
Manual execution by user
- OUTLOOK.EXE (PID: 2300)
- chrome.exe (PID: 2024)
Checks supported languages
- iexplore.exe (PID: 1864)
- rundll32.exe (PID: 3980)
- iexplore.exe (PID: 2368)
- chrome.exe (PID: 3136)
- chrome.exe (PID: 2024)
- chrome.exe (PID: 3464)
- chrome.exe (PID: 3000)
- chrome.exe (PID: 1500)
- chrome.exe (PID: 3720)
- chrome.exe (PID: 2544)
- chrome.exe (PID: 2372)
- chrome.exe (PID: 1024)
- chrome.exe (PID: 2708)
- chrome.exe (PID: 2848)
- chrome.exe (PID: 2896)
- chrome.exe (PID: 2540)
- chrome.exe (PID: 3028)
- chrome.exe (PID: 3128)
- chrome.exe (PID: 3240)
- chrome.exe (PID: 2844)
- chrome.exe (PID: 2912)
- chrome.exe (PID: 3736)
- chrome.exe (PID: 508)
- chrome.exe (PID: 3612)
- chrome.exe (PID: 3696)
- chrome.exe (PID: 1472)
- chrome.exe (PID: 1044)
- chrome.exe (PID: 636)
- chrome.exe (PID: 1936)
- chrome.exe (PID: 3588)
- chrome.exe (PID: 2408)
- chrome.exe (PID: 2808)
- chrome.exe (PID: 1228)
- chrome.exe (PID: 3256)
- chrome.exe (PID: 3568)
- chrome.exe (PID: 4008)
- chrome.exe (PID: 968)
- chrome.exe (PID: 2468)
- chrome.exe (PID: 1076)
- chrome.exe (PID: 3412)
Reads the computer name
- iexplore.exe (PID: 1864)
- iexplore.exe (PID: 2368)
- chrome.exe (PID: 2024)
- chrome.exe (PID: 1500)
- chrome.exe (PID: 2372)
- chrome.exe (PID: 2708)
- chrome.exe (PID: 2896)
- chrome.exe (PID: 3696)
- chrome.exe (PID: 1472)
- chrome.exe (PID: 2808)
Application launched itself
- iexplore.exe (PID: 1864)
- chrome.exe (PID: 2024)
Checks Windows Trust Settings
- iexplore.exe (PID: 1864)
- iexplore.exe (PID: 2368)
Changes internet zones settings
- iexplore.exe (PID: 1864)
Reads settings of System Certificates
- iexplore.exe (PID: 2368)
- iexplore.exe (PID: 1864)
- chrome.exe (PID: 2372)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2300)
Reads the hosts file
- chrome.exe (PID: 2024)
- chrome.exe (PID: 2372)
Creates files in the user directory
- iexplore.exe (PID: 2368)
- iexplore.exe (PID: 1864)
Changes settings of System certificates
- iexplore.exe (PID: 1864)
Reads internet explorer settings
- iexplore.exe (PID: 2368)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1864)
Reads the date of Windows installation
- chrome.exe (PID: 1472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .mbox | | | Standard Unix Mailbox (74.3) |
|---|---|---|
| .eml | | | E-Mail message (Var. 2) (25.6) |
Total processes
82
Monitored processes
41
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1056,9077042438051377523,17643804645747287854,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3352 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1056,9077042438051377523,17643804645747287854,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2624 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1056,9077042438051377523,17643804645747287854,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3052 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1056,9077042438051377523,17643804645747287854,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2852 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,9077042438051377523,17643804645747287854,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1040 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1056,9077042438051377523,17643804645747287854,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2932 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,9077042438051377523,17643804645747287854,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=932 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1472 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1056,9077042438051377523,17643804645747287854,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=608 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1056,9077042438051377523,17643804645747287854,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1024 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
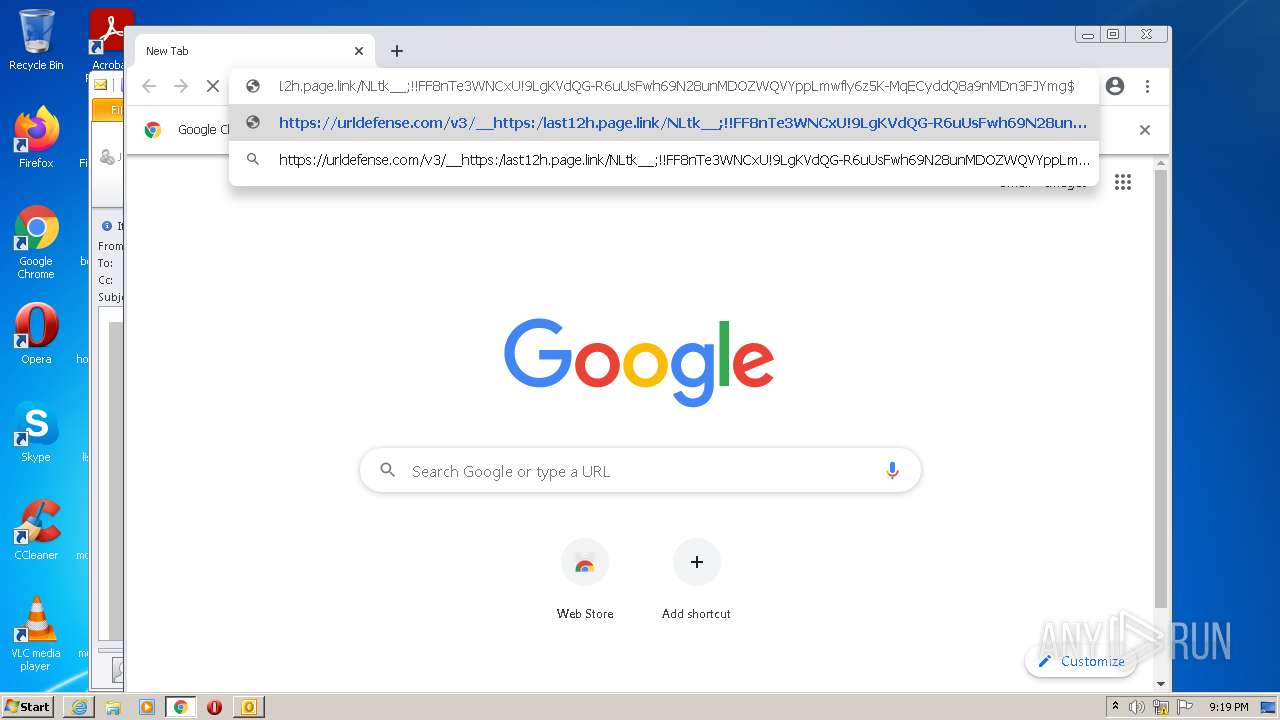
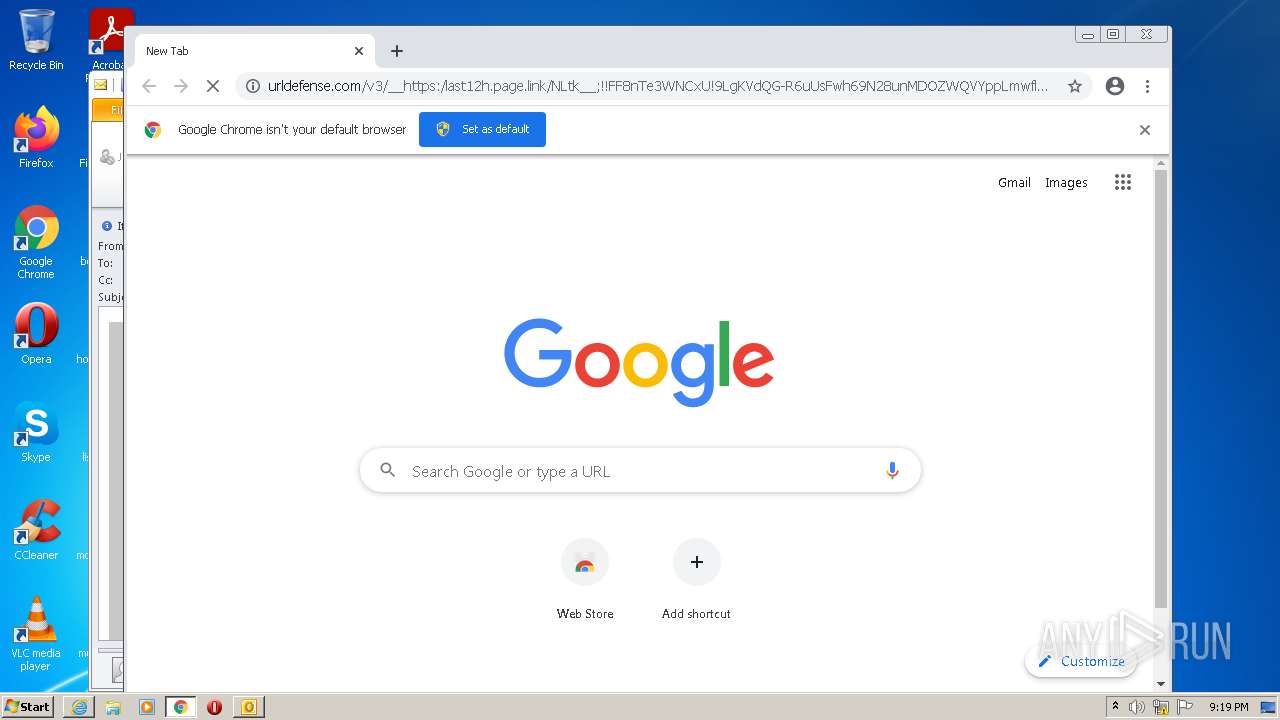
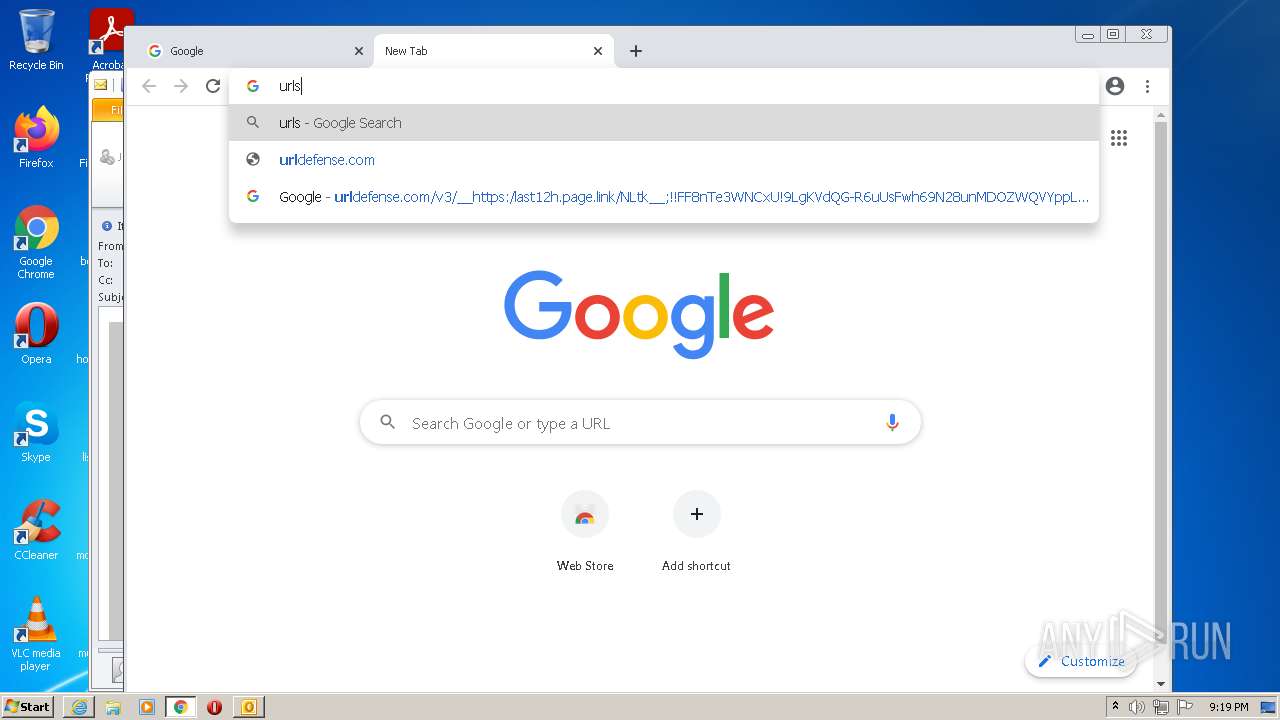
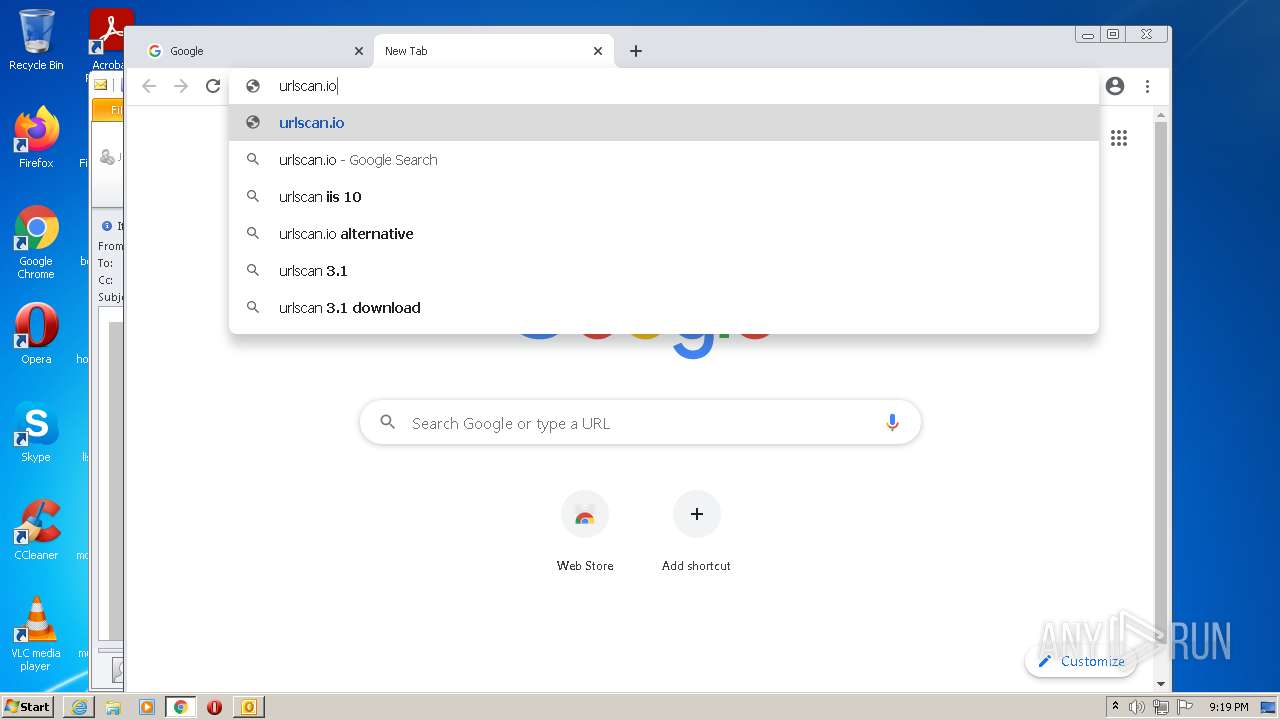
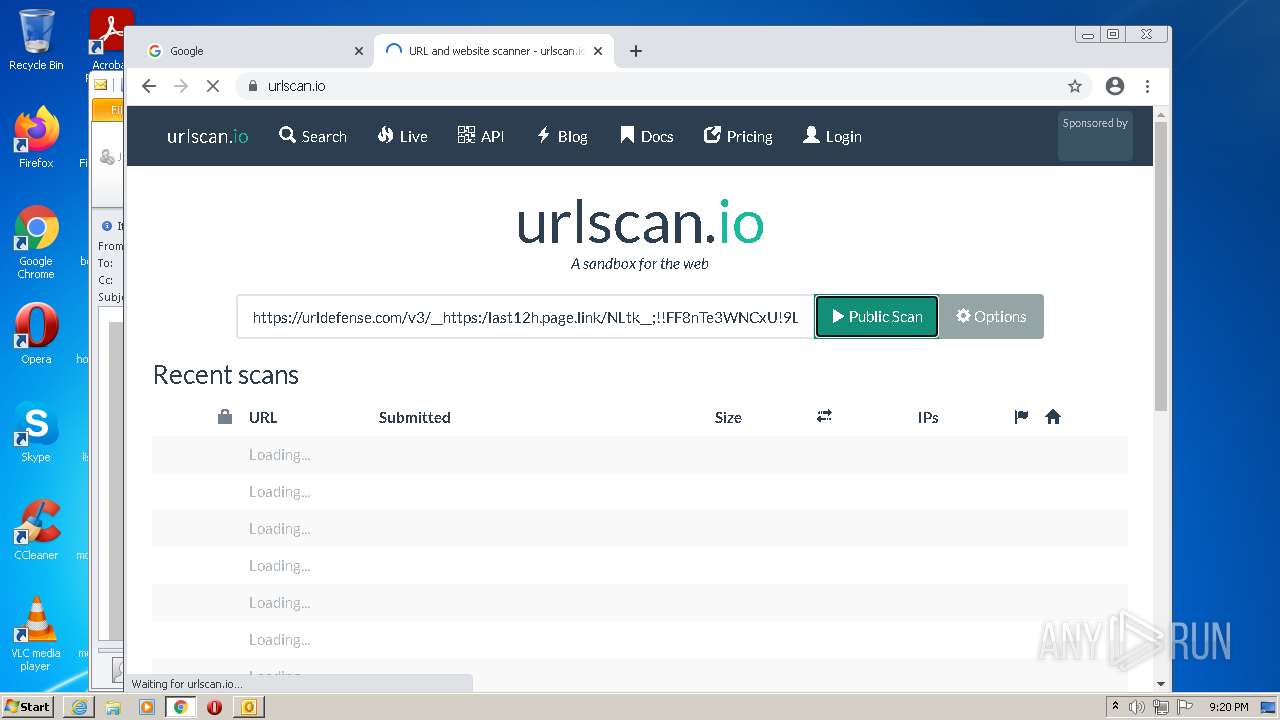
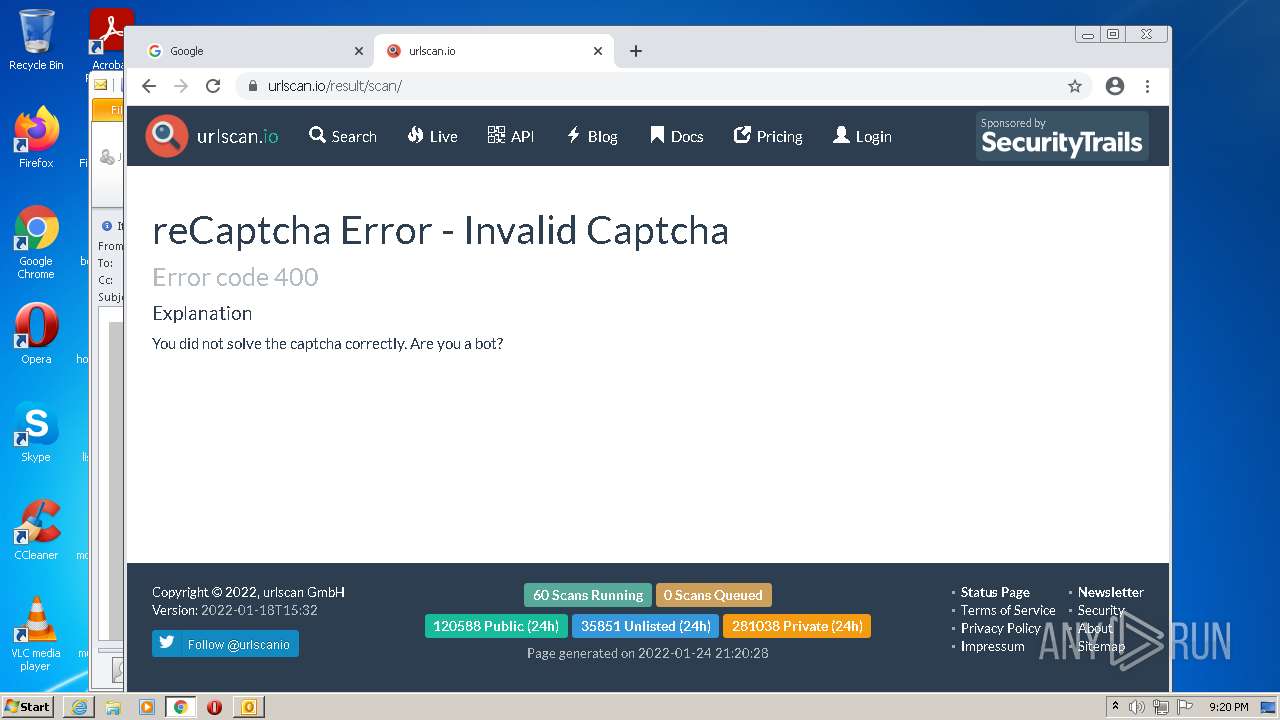
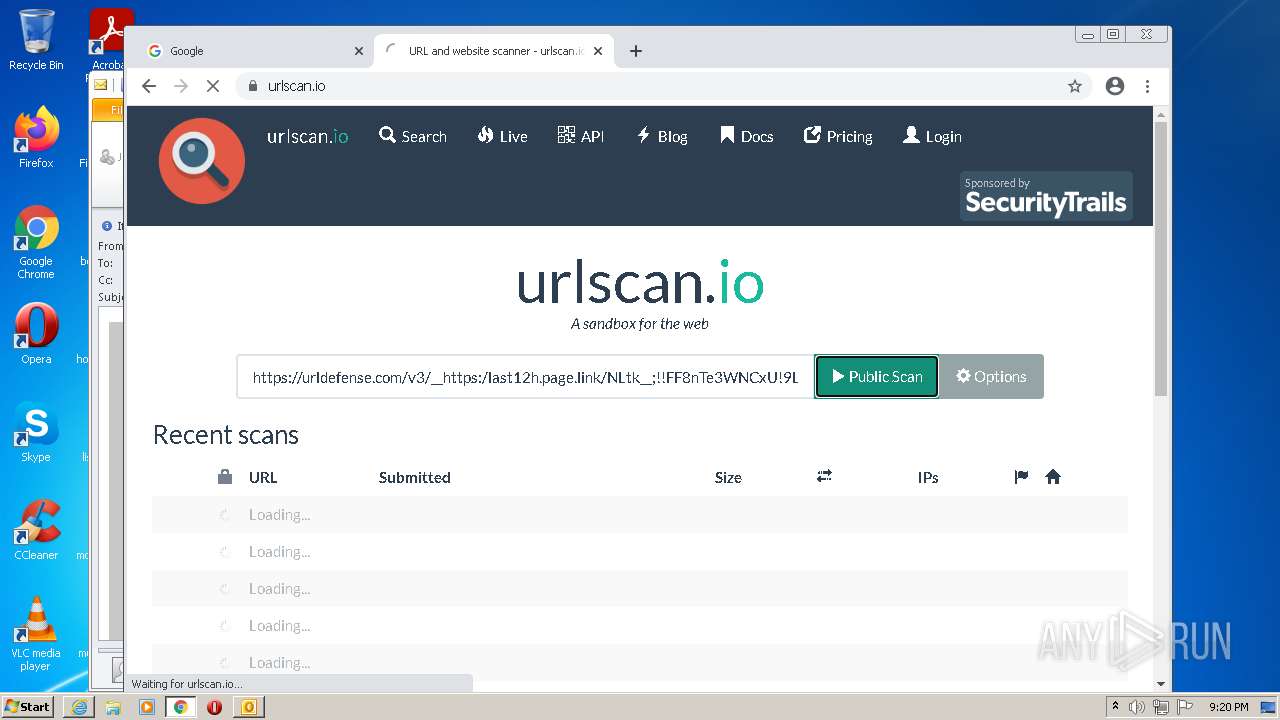
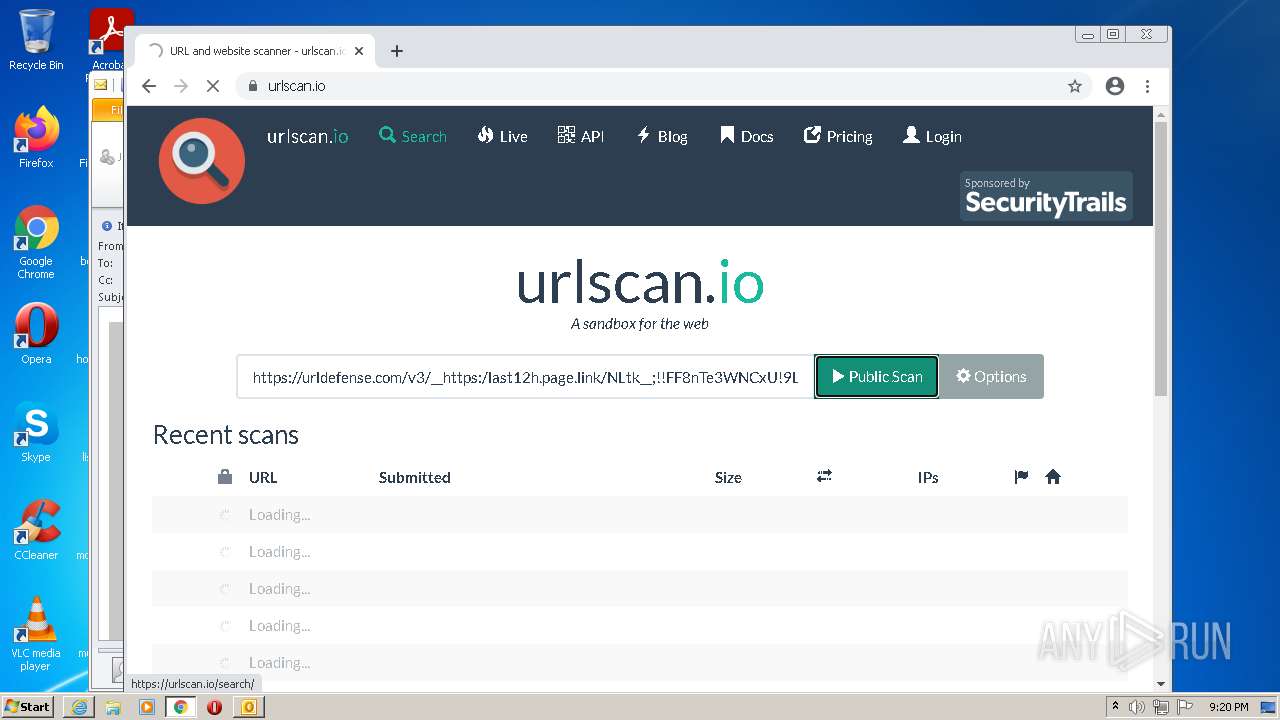
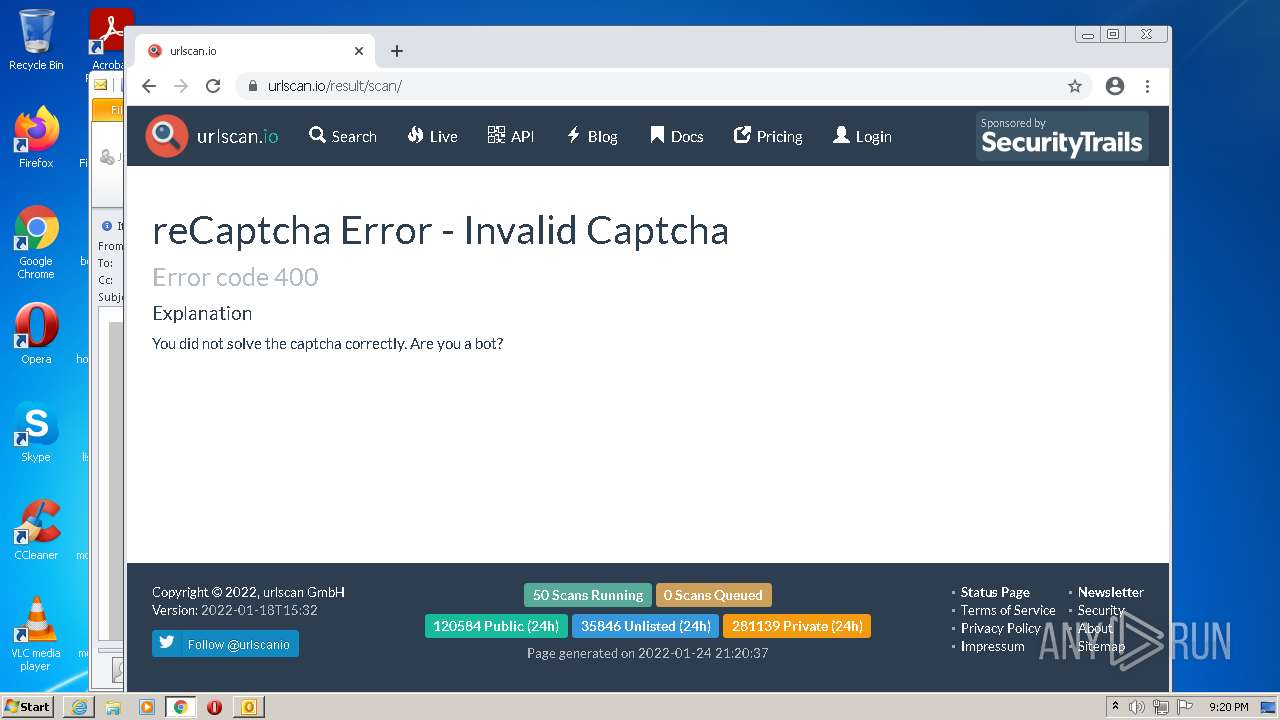
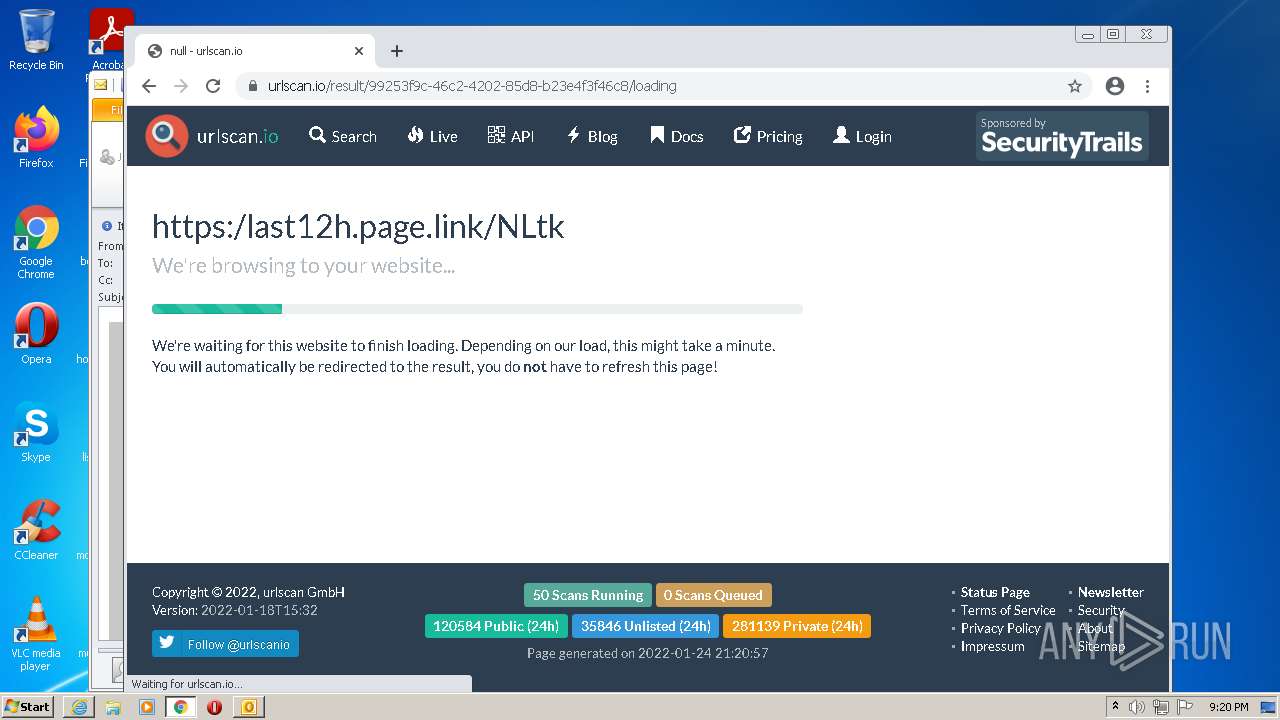
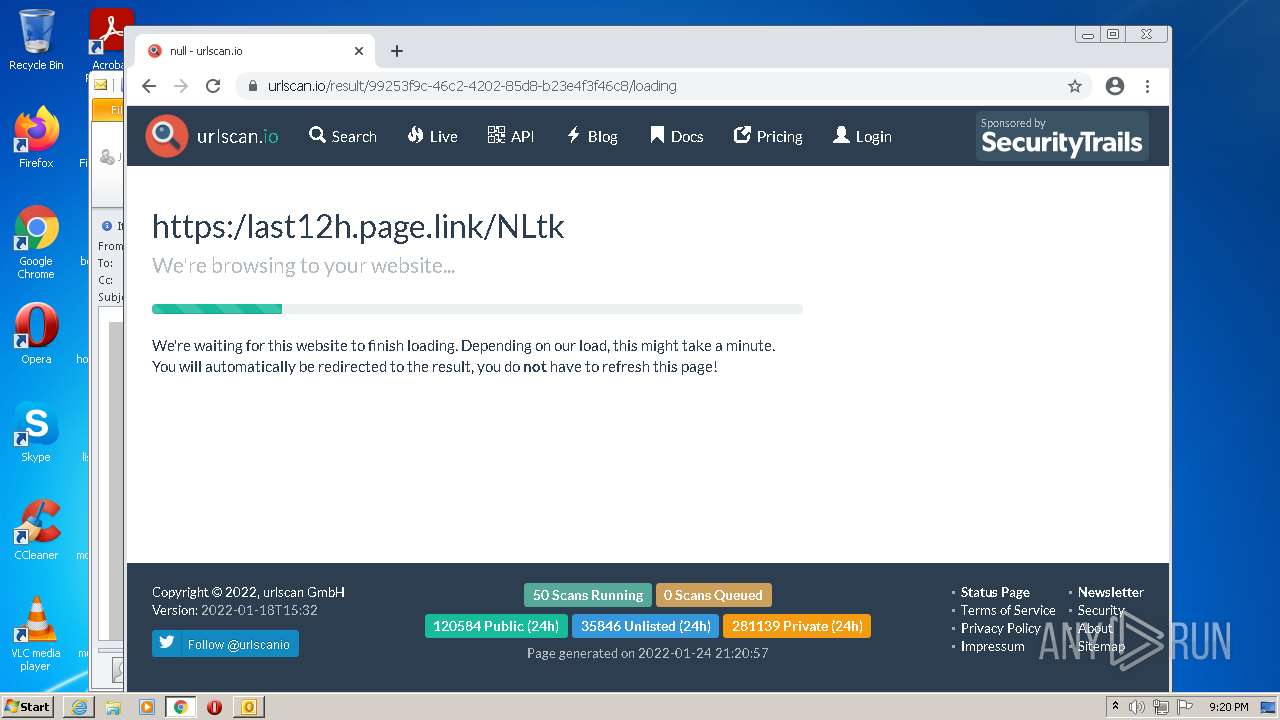
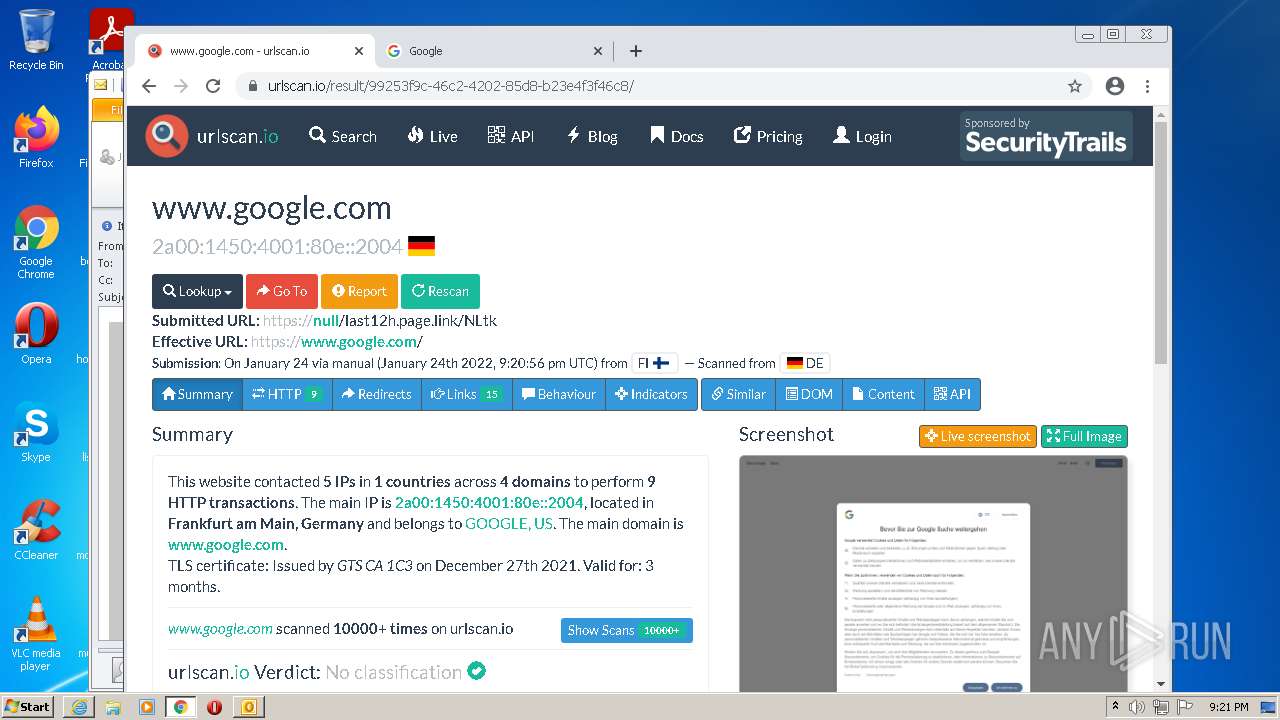
| 1864 | "C:\Program Files\Internet Explorer\iexplore.exe" https://urldefense.com/v3/__https:/last12h.page.link/NLtk__;!!FF8nTe3WNCxU!9LgKVdQG-R6uUsFwh69N28unMDOZWQVYppLmwfly6z5K-MqECyddQ8a9nMDn3FJYmg$ | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
30 740
Read events
29 879
Write events
829
Delete events
32
Modification events
| (PID) Process: | (2300) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2300) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2300) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2300) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2300) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2300) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2300) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2300) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2300) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2300) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
1
Suspicious files
206
Text files
240
Unknown types
25
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2300 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR1F9C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2300 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 2300 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2368 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:— | SHA256:— | |||
| 2300 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2368 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\72BA427A91F50409B9EAC87F2B59B951_DAD45A86502C05AF671CDFB147052D91 | binary | |
MD5:— | SHA256:— | |||
| 2368 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:— | SHA256:— | |||
| 2368 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 1864 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 2024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61EF17DE-7E8.pma | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
64
TCP/UDP connections
91
DNS requests
63
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2300 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
924 | svchost.exe | HEAD | 302 | 142.250.186.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/czka5fc33qq67ao7g67evi5jte_9.32.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.32.0_all_hkbbg5yepfmg4tn57zz6rpfdiy.crx3 | US | — | — | whitelisted |
2368 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQh80WaEMqmyEvaHjlisSfVM4p8SAQUF9nWJSdn%2BTHCSUPZMDZEjGypT%2BsCEBBsbMdZKid6hcZfT6LpnsI%3D | US | der | 471 b | whitelisted |
2368 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2368 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2368 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEBN9U5yqfDGppDNwGWiEeo0%3D | US | der | 727 b | whitelisted |
2368 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQC04WHG3wyS9QoAAAABK3x8 | US | der | 472 b | whitelisted |
1864 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2368 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDgAde1VeKYIQoAAAABK4GI | US | der | 472 b | whitelisted |
1864 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2300 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2368 | iexplore.exe | 52.6.56.188:443 | urldefense.com | Amazon.com, Inc. | US | suspicious |
2368 | iexplore.exe | 67.27.235.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
2368 | iexplore.exe | 104.18.30.182:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
1864 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
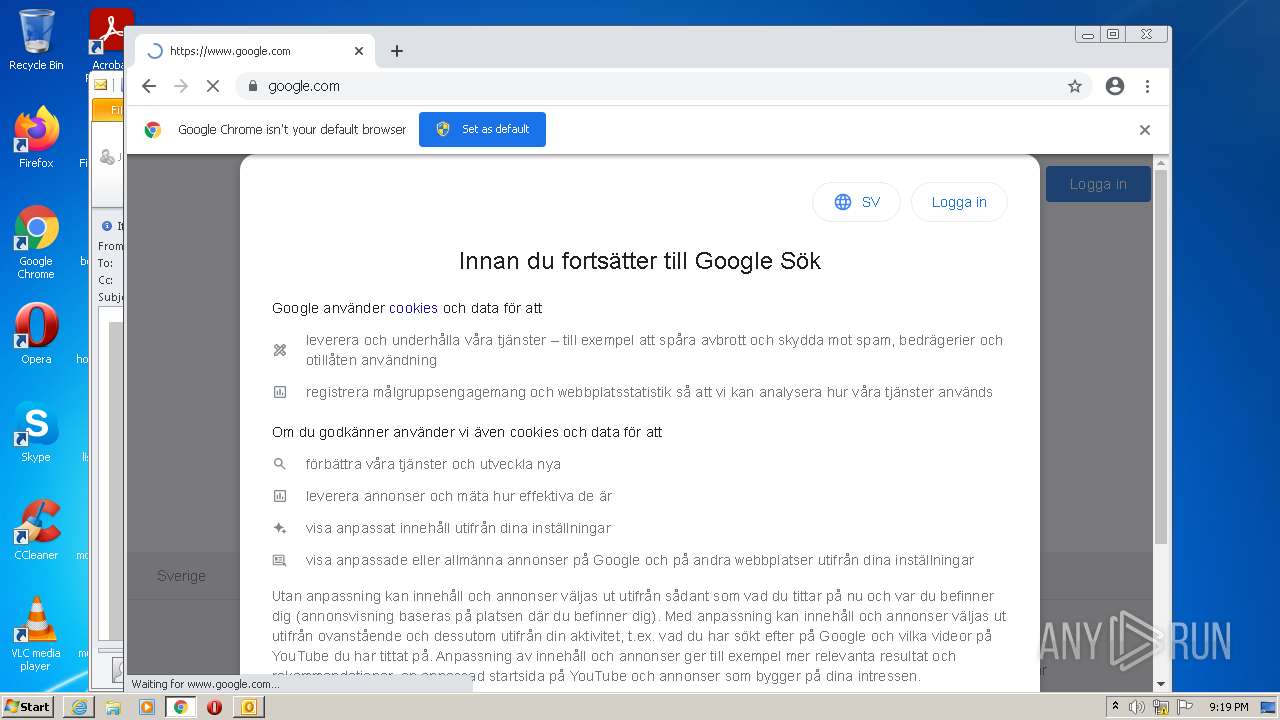
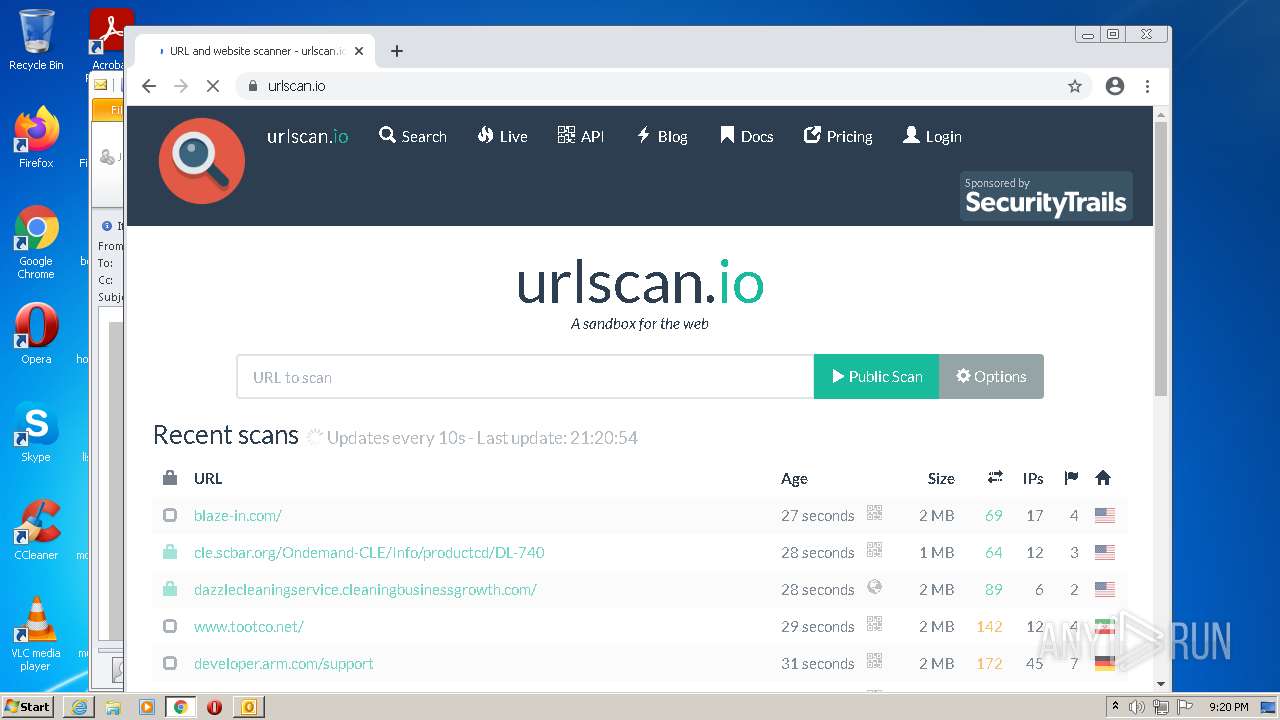
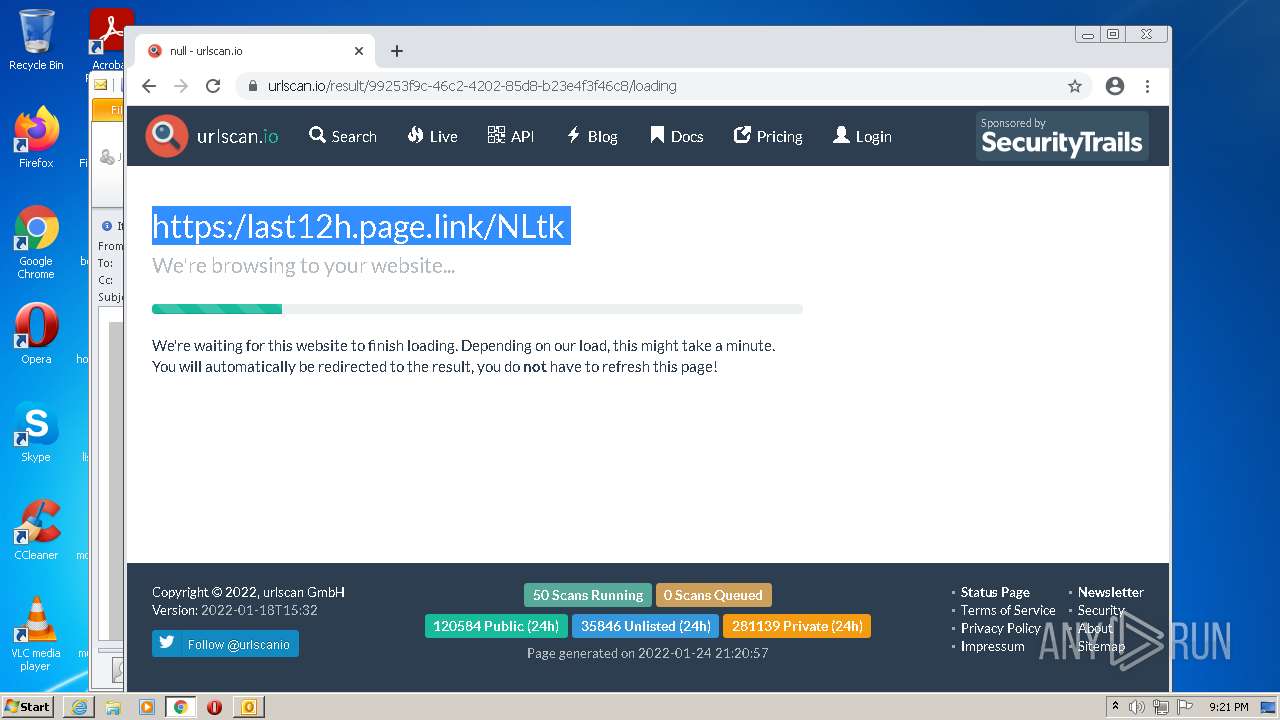
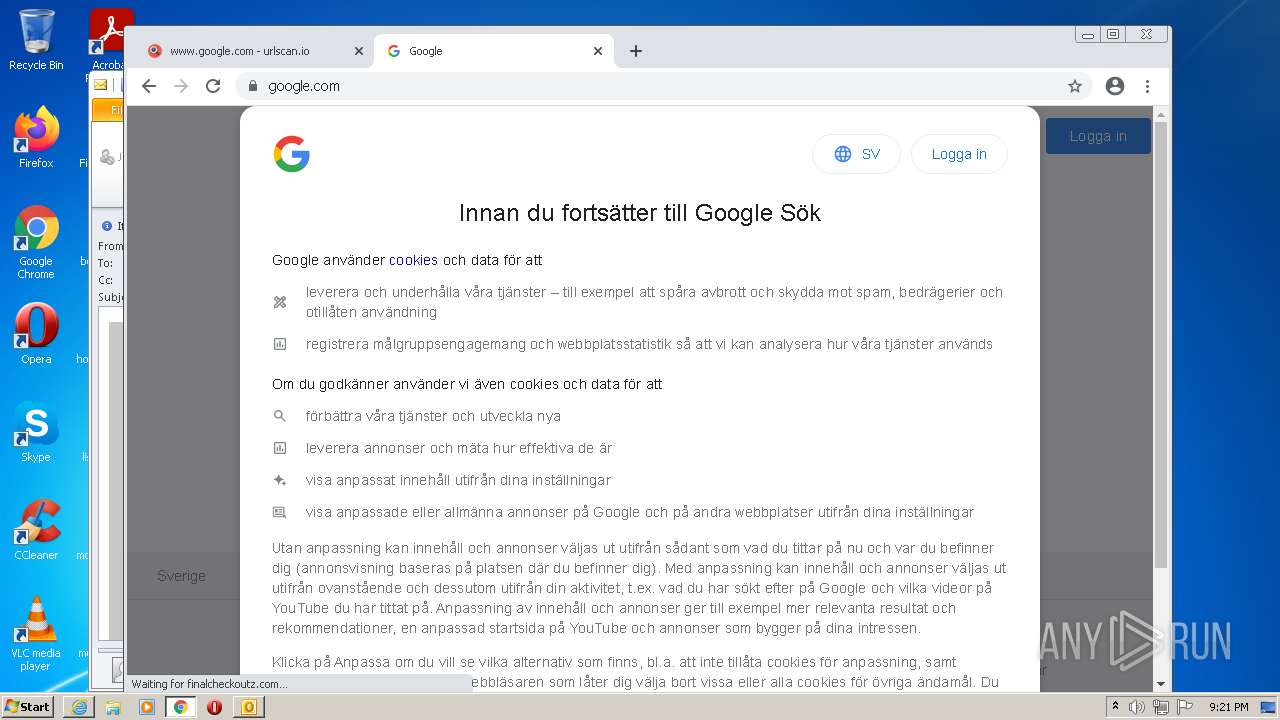
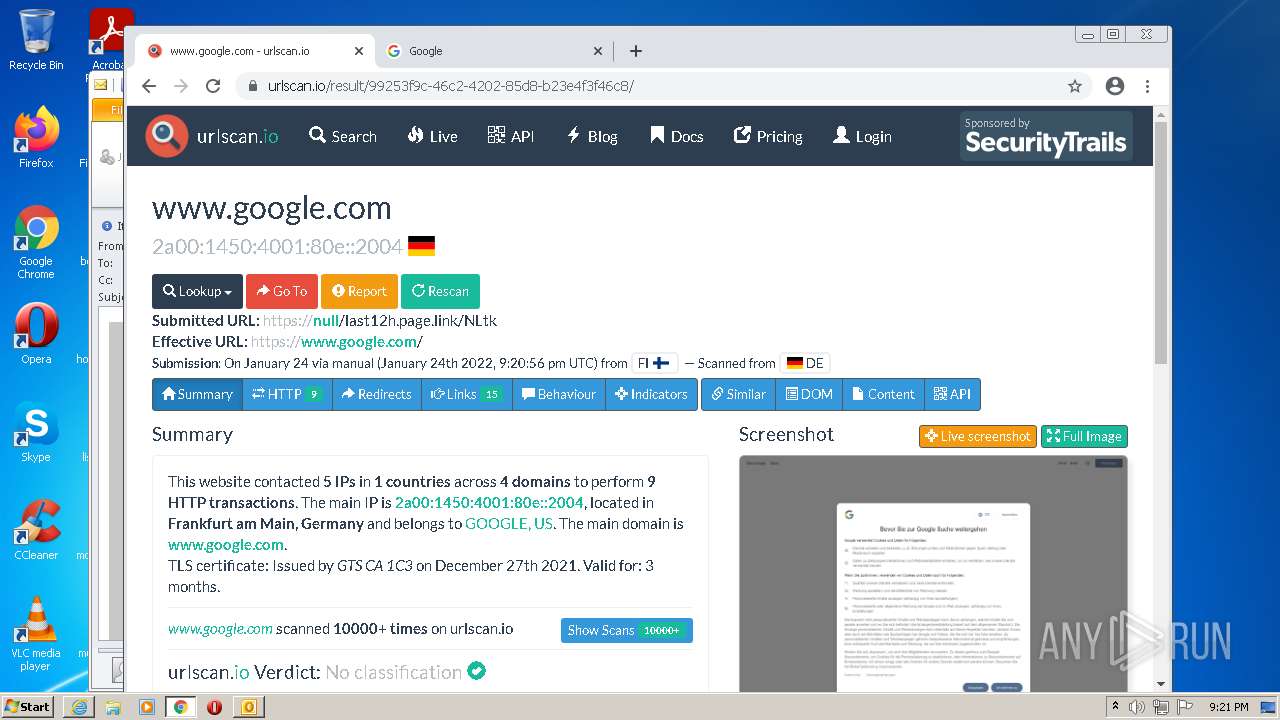
2368 | iexplore.exe | 142.250.185.78:443 | last12h.page.link | Google Inc. | US | whitelisted |
2368 | iexplore.exe | 142.250.184.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
— | — | 142.250.185.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2372 | chrome.exe | 142.250.186.100:443 | www.google.com | Google Inc. | US | whitelisted |
2372 | chrome.exe | 142.250.186.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
urldefense.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
last12h.page.link |
| whitelisted |