| File name: | Activation Patch.exe |
| Full analysis: | https://app.any.run/tasks/e888ffbb-5529-413f-aefa-e0f441398ea9 |
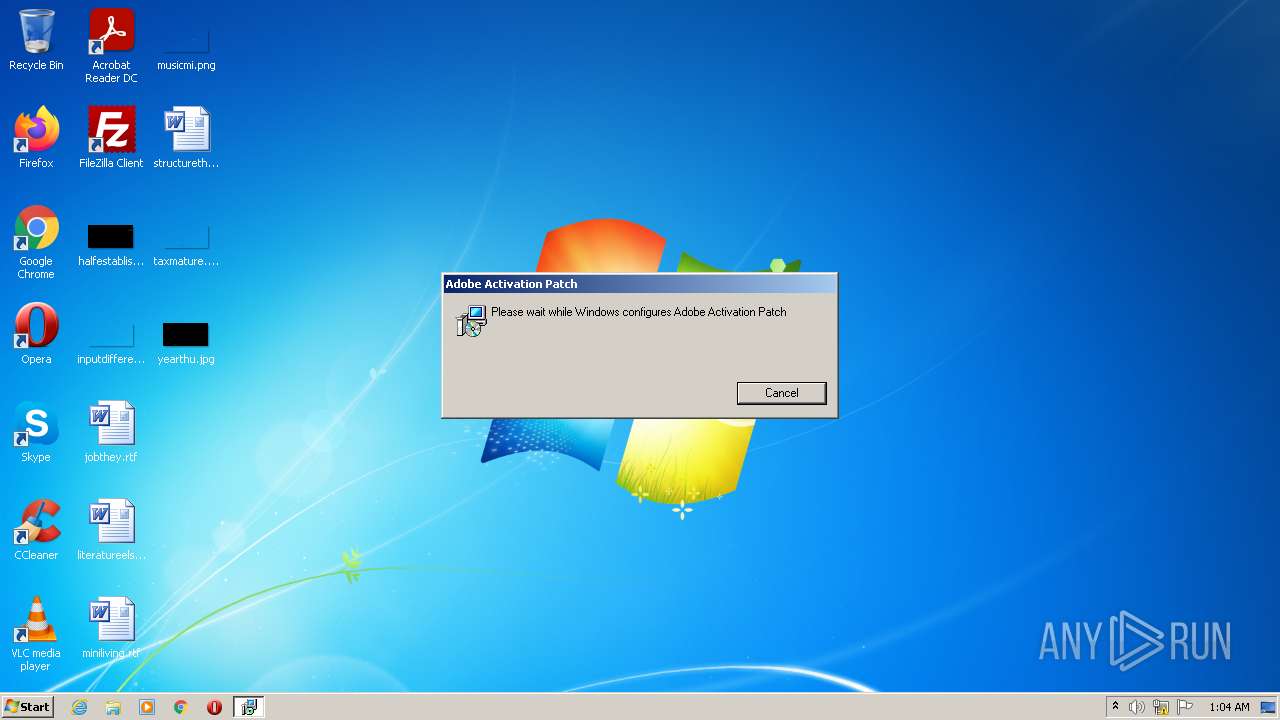
| Verdict: | Malicious activity |
| Analysis date: | July 23, 2022, 00:04:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2F6649730FE0C6DAF60AC91CBCC2273B |
| SHA1: | C22D69A2ED74A088237EF1A3DF4C36726A771213 |
| SHA256: | 5043171432237C4D824278C60010F33ACC58D79F51AE1D4ACD59CCC3CB44AE35 |
| SSDEEP: | 98304:h35E+vGaiDnXGtwcmoQvoTn0iMYexBA7YnkPOYnqGGse:/vGacofn05WYnk5qGGse |
MALICIOUS
Drops executable file immediately after starts
- Activation Patch.exe (PID: 2556)
- msiexec.exe (PID: 2932)
Application was dropped or rewritten from another process
- Active-Services.exe (PID: 2052)
SUSPICIOUS
Creates files in the user directory
- Activation Patch.exe (PID: 2556)
- msiexec.exe (PID: 2932)
Reads Environment values
- Activation Patch.exe (PID: 2556)
- vssvc.exe (PID: 2080)
- Active-Services.exe (PID: 2052)
Checks supported languages
- msiexec.exe (PID: 2932)
- Activation Patch.exe (PID: 2556)
- MsiExec.exe (PID: 3536)
- MsiExec.exe (PID: 1092)
- Active-Services.exe (PID: 2052)
- cmd.exe (PID: 2008)
Reads the computer name
- Activation Patch.exe (PID: 2556)
- msiexec.exe (PID: 2932)
- MsiExec.exe (PID: 3536)
- MsiExec.exe (PID: 1092)
- Active-Services.exe (PID: 2052)
Reads the Windows organization settings
- Activation Patch.exe (PID: 2556)
- msiexec.exe (PID: 3616)
- msiexec.exe (PID: 2932)
Reads Windows owner or organization settings
- Activation Patch.exe (PID: 2556)
- msiexec.exe (PID: 3616)
- msiexec.exe (PID: 2932)
Executable content was dropped or overwritten
- Activation Patch.exe (PID: 2556)
- msiexec.exe (PID: 2932)
Drops a file with a compile date too recent
- Activation Patch.exe (PID: 2556)
- msiexec.exe (PID: 2932)
Starts Microsoft Installer
- Activation Patch.exe (PID: 2556)
Executed as Windows Service
- vssvc.exe (PID: 2080)
Creates a directory in Program Files
- msiexec.exe (PID: 2932)
Starts CMD.EXE for commands execution
- Active-Services.exe (PID: 2052)
INFO
Application launched itself
- msiexec.exe (PID: 2932)
Dropped object may contain Bitcoin addresses
- Activation Patch.exe (PID: 2556)
Checks supported languages
- msiexec.exe (PID: 3616)
- vssvc.exe (PID: 2080)
- timeout.exe (PID: 2624)
Reads the computer name
- msiexec.exe (PID: 3616)
- vssvc.exe (PID: 2080)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3536)
- MsiExec.exe (PID: 1092)
Creates a software uninstall entry
- msiexec.exe (PID: 2932)
Reads settings of System Certificates
- Active-Services.exe (PID: 2052)
Searches for installed software
- msiexec.exe (PID: 2932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (18) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (2.9) |
| .exe | | | Generic Win/DOS Executable (1.3) |
| .exe | | | DOS Executable Generic (1.3) |
EXIF
EXE
| ProductVersion: | 1.0.0 |
|---|---|
| ProductName: | Adobe Activation Patch |
| OriginalFileName: | Adobe Activation Patch.exe |
| LegalCopyright: | Copyright (C) 2022 Adobe Activation Patch |
| InternalName: | Adobe Activation Patch |
| FileVersion: | 1.0.0 |
| FileDescription: | Adobe Activation Patch Installer |
| CompanyName: | Adobe Activation Patch |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Dynamic link library |
| FileOS: | Win32 |
| FileFlags: | Debug |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x1260c8 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 656384 |
| CodeSize: | 1559040 |
| LinkerVersion: | 14.28 |
| PEType: | PE32 |
| TimeStamp: | 2021:04:23 09:52:46+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Apr-2021 07:52:46 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Adobe Activation Patch |
| FileDescription: | Adobe Activation Patch Installer |
| FileVersion: | 1.0.0 |
| InternalName: | Adobe Activation Patch |
| LegalCopyright: | Copyright (C) 2022 Adobe Activation Patch |
| OriginalFileName: | Adobe Activation Patch.exe |
| ProductName: | Adobe Activation Patch |
| ProductVersion: | 1.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 23-Apr-2021 07:52:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0017C88F | 0x0017CA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44853 |
.rdata | 0x0017E000 | 0x0005EC74 | 0x0005EE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.57976 |
.data | 0x001DD000 | 0x00006E70 | 0x00005600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.03312 |
.rsrc | 0x001E4000 | 0x000227F0 | 0x00022800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.80578 |
.reloc | 0x00207000 | 0x00019678 | 0x00019800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.56628 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.221 | 1915 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.05305 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.29939 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 2.41709 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 2.63314 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 2.96629 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.37783 | 1116 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 3.34881 | 836 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.31743 | 760 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 3.23118 | 1432 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
msi.dll (delay-loaded) |
Total processes
44
Monitored processes
9
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1092 | C:\Windows\system32\MsiExec.exe -Embedding D98C00D04EC138EB27A576996EC9F8AD | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2008 | "C:\Windows\System32\cmd.exe" /C timeout 20 | C:\Windows\System32\cmd.exe | — | Active-Services.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2052 | "C:\Users\admin\AppData\Roaming\WindowsActiveServices\Active-Services.exe" | C:\Users\admin\AppData\Roaming\WindowsActiveServices\Active-Services.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Robocopy Exit code: 0 Version: 10.0.17763.1971 Modules
| |||||||||||||||
| 2080 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2556 | "C:\Users\admin\AppData\Local\Temp\Activation Patch.exe" | C:\Users\admin\AppData\Local\Temp\Activation Patch.exe | Explorer.EXE | ||||||||||||
User: admin Company: Adobe Activation Patch Integrity Level: MEDIUM Description: Adobe Activation Patch Installer Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
| 2624 | timeout 20 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2932 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3536 | C:\Windows\system32\MsiExec.exe -Embedding D034DB129F89FCA432711501F593DF85 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3616 | "C:\Windows\system32\msiexec.exe" /i "C:\Users\admin\AppData\Roaming\Adobe Activation Patch\Adobe Activation Patch 1.0.0\install\Adobe Activation Patch.msi" AI_SETUPEXEPATH="C:\Users\admin\AppData\Local\Temp\Activation Patch.exe" SETUPEXEDIR=C:\Users\admin\AppData\Local\Temp\ EXE_CMD_LINE="/exenoupdates /forcecleanup /wintime 1658533683 " | C:\Windows\system32\msiexec.exe | — | Activation Patch.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6 603
Read events
6 337
Write events
266
Delete events
0
Modification events
| (PID) Process: | (2932) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 400000000000000064FF17D5279ED801740B0000AC0F0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2932) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 400000000000000064FF17D5279ED801740B0000AC0F0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2932) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 69 | |||
| (PID) Process: | (2932) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000A44A64D5279ED801740B0000AC0F0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2932) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000A44A64D5279ED801740B0000AC040000E8030000010000000000000000000000E3EA757E42314C45AEAA2A6AC07FE2970000000000000000 | |||
| (PID) Process: | (2080) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000663670D5279ED801200800007C090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2080) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000663670D5279ED8012008000084090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2080) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000663670D5279ED8012008000074090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2080) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000663670D5279ED8012008000018060000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2080) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000745D77D5279ED8012008000084090000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
14
Suspicious files
5
Text files
14
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2556 | Activation Patch.exe | C:\Users\admin\AppData\Roaming\Adobe Activation Patch\Adobe Activation Patch 1.0.0\install\Adobe Activation Patch.msi | executable | |
MD5:CD4F2ECA11827900A8DE0F52636633BF | SHA256:814A26926B1E2715C0EFFD3BA6DD76E9BAFABB6D674642F946E5A621A7A78F21 | |||
| 2556 | Activation Patch.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_2556\completi | image | |
MD5:45B0E074F96A859ADAE198187AB9FA11 | SHA256:050282E679AC80F6A357FFF92F1E7A95D30A06B35247E25CBFD2DD8CEEE1A412 | |||
| 2556 | Activation Patch.exe | C:\Users\admin\AppData\Local\Temp\MSI61CE.tmp | executable | |
MD5:0981D5C068A9C33F4E8110F81FFBB92E | SHA256:B3F5E10FB1B7352A6DBBCBB10ED605A8FDA24F3F9C31F954835BD5A41EB6EA68 | |||
| 2932 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2556 | Activation Patch.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_2556\removico | image | |
MD5:20D25E871A244B94574C47726DE745D6 | SHA256:88DD7EE9FA22ECDBDC6B3D47DB83BC3D72360AEB43588E6A9A008B224389CB1C | |||
| 2556 | Activation Patch.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_2556\dialog | image | |
MD5:553DF955CB4B2E7BE5CEF99CB8EC9254 | SHA256:F1FCB09DF932AEF09B24EEA796286CEAEDCBCECCD4D8F4536345163C4D3D9FF7 | |||
| 2556 | Activation Patch.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_2556\exclamic | image | |
MD5:3DBA38E7A6085876E79F162F9985618C | SHA256:593F94EF1405422B3E453F4422B22C990D84303668D60344C6FD257318E92428 | |||
| 2556 | Activation Patch.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_2556\banner | image | |
MD5:CE1143E3563DE4E200BA7F4953B3807B | SHA256:A5EEFACA044B04460A1CED5FEC2229545EDF85F01E1D6673E6E14D06B3108C2D | |||
| 2556 | Activation Patch.exe | C:\Users\admin\AppData\Roaming\Adobe Activation Patch\Adobe Activation Patch 1.0.0\install\holder0.aiph | gmc | |
MD5:C2A7E2739788D68B47D1C012403D851A | SHA256:40A3ECCF86BFD01BF85F75E63CC209F56E551B83F7D6BA5DAE99D39F79DABDEE | |||
| 2556 | Activation Patch.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_2556\New | image | |
MD5:C23CBF002D82192481B61ED7EC0890F4 | SHA256:4F92E804A11453382EBFF7FB0958879BAE88FE3366306911DEC9D811CD306EED | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
12
DNS requests
9
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2052 | Active-Services.exe | GET | 301 | 142.250.185.174:80 | http://youtube.com/ | US | — | — | whitelisted |
2052 | Active-Services.exe | GET | 301 | 142.250.185.174:80 | http://youtube.com/ | US | — | — | whitelisted |
2052 | Active-Services.exe | GET | 301 | 13.107.21.200:80 | http://bing.com/ | US | — | — | whitelisted |
2052 | Active-Services.exe | GET | 301 | 13.107.21.200:80 | http://bing.com/ | US | — | — | whitelisted |
2052 | Active-Services.exe | GET | 301 | 142.250.185.174:80 | http://youtube.com/ | US | — | — | whitelisted |
2052 | Active-Services.exe | GET | 200 | 142.250.74.196:80 | http://www.google.com/ | US | html | 48.5 Kb | malicious |
2052 | Active-Services.exe | GET | 200 | 142.250.74.196:80 | http://www.google.com/ | US | html | 48.5 Kb | malicious |
2052 | Active-Services.exe | GET | 200 | 142.250.74.196:80 | http://www.google.com/ | US | html | 48.5 Kb | malicious |
2052 | Active-Services.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/ | US | html | 89.2 Kb | whitelisted |
2052 | Active-Services.exe | GET | 301 | 142.250.186.174:80 | http://google.com/ | US | html | 219 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2052 | Active-Services.exe | 142.250.186.174:80 | google.com | Google Inc. | US | whitelisted |
2052 | Active-Services.exe | 142.250.74.196:80 | www.google.com | Google Inc. | US | whitelisted |
2052 | Active-Services.exe | 204.79.197.200:80 | bing.com | Microsoft Corporation | US | whitelisted |
2052 | Active-Services.exe | 74.6.231.20:80 | yahoo.com | — | US | malicious |
2052 | Active-Services.exe | 74.6.231.20:443 | yahoo.com | — | US | malicious |
2052 | Active-Services.exe | 87.248.100.216:443 | www.yahoo.com | Yahoo! UK Services Limited | GB | malicious |
2052 | Active-Services.exe | 87.248.119.251:443 | au.yahoo.com | Yahoo! UK Services Limited | GB | malicious |
2052 | Active-Services.exe | 142.250.185.174:80 | youtube.com | Google Inc. | US | whitelisted |
2052 | Active-Services.exe | 142.250.184.206:443 | www.youtube.com | Google Inc. | US | whitelisted |
2052 | Active-Services.exe | 13.107.21.200:80 | bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| malicious |
www.google.com |
| malicious |
youtube.com |
| whitelisted |
www.youtube.com |
| whitelisted |
bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
yahoo.com |
| whitelisted |
www.yahoo.com |
| whitelisted |
au.yahoo.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2052 | Active-Services.exe | A Network Trojan was detected | ET INFO Terse Unencrypted Request for Google - Likely Connectivity Check |
2052 | Active-Services.exe | A Network Trojan was detected | ET INFO Terse Unencrypted Request for Google - Likely Connectivity Check |
2052 | Active-Services.exe | A Network Trojan was detected | ET INFO Terse Unencrypted Request for Google - Likely Connectivity Check |
2052 | Active-Services.exe | A Network Trojan was detected | ET INFO Terse Unencrypted Request for Google - Likely Connectivity Check |
2052 | Active-Services.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible automated connectivity check (www.bing.com) |
2052 | Active-Services.exe | A Network Trojan was detected | ET INFO Terse Unencrypted Request for Google - Likely Connectivity Check |
2052 | Active-Services.exe | A Network Trojan was detected | ET INFO Terse Unencrypted Request for Google - Likely Connectivity Check |
2052 | Active-Services.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible automated connectivity check (www.google.com) |
2052 | Active-Services.exe | A Network Trojan was detected | ET INFO Terse Unencrypted Request for Google - Likely Connectivity Check |
2052 | Active-Services.exe | A Network Trojan was detected | ET INFO Terse Unencrypted Request for Google - Likely Connectivity Check |