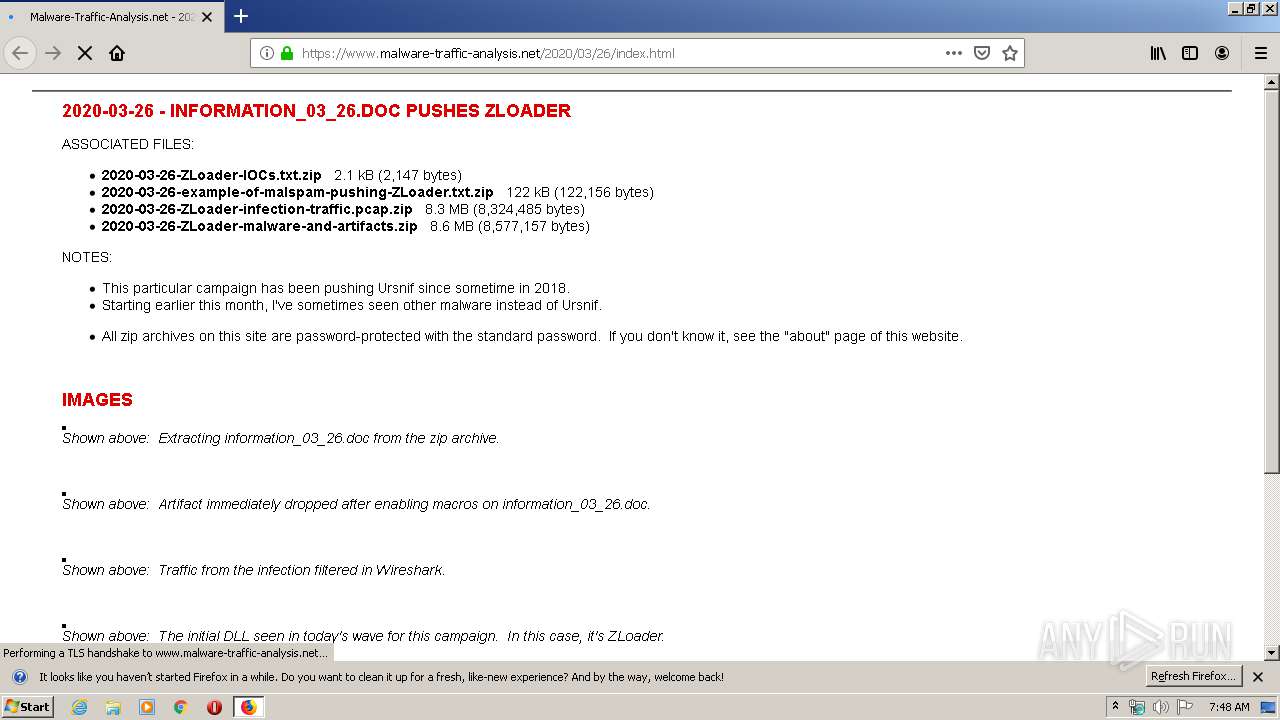
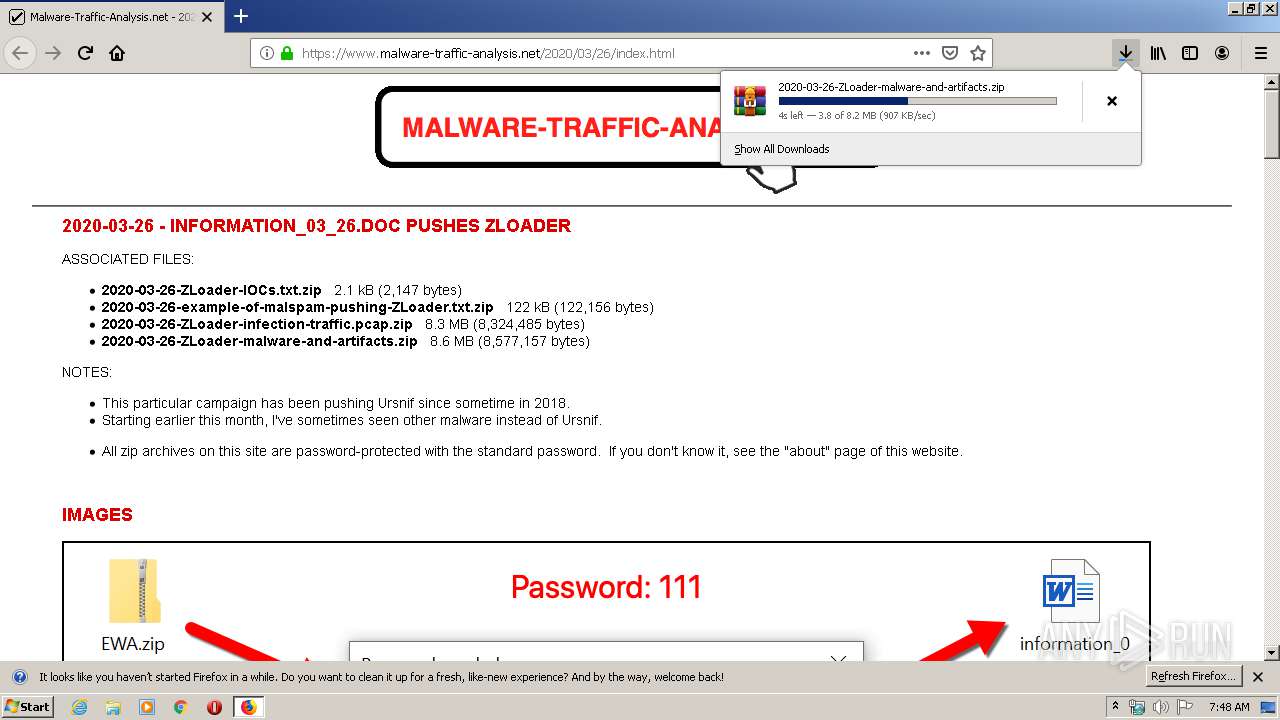
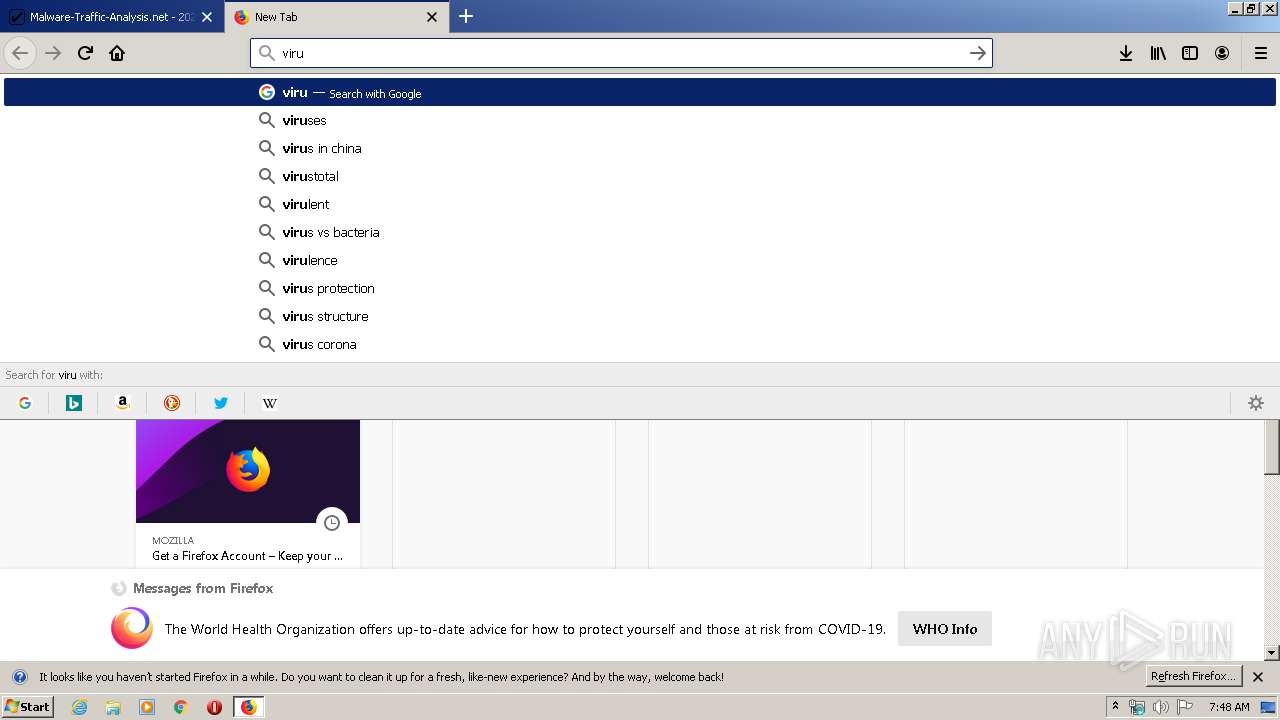
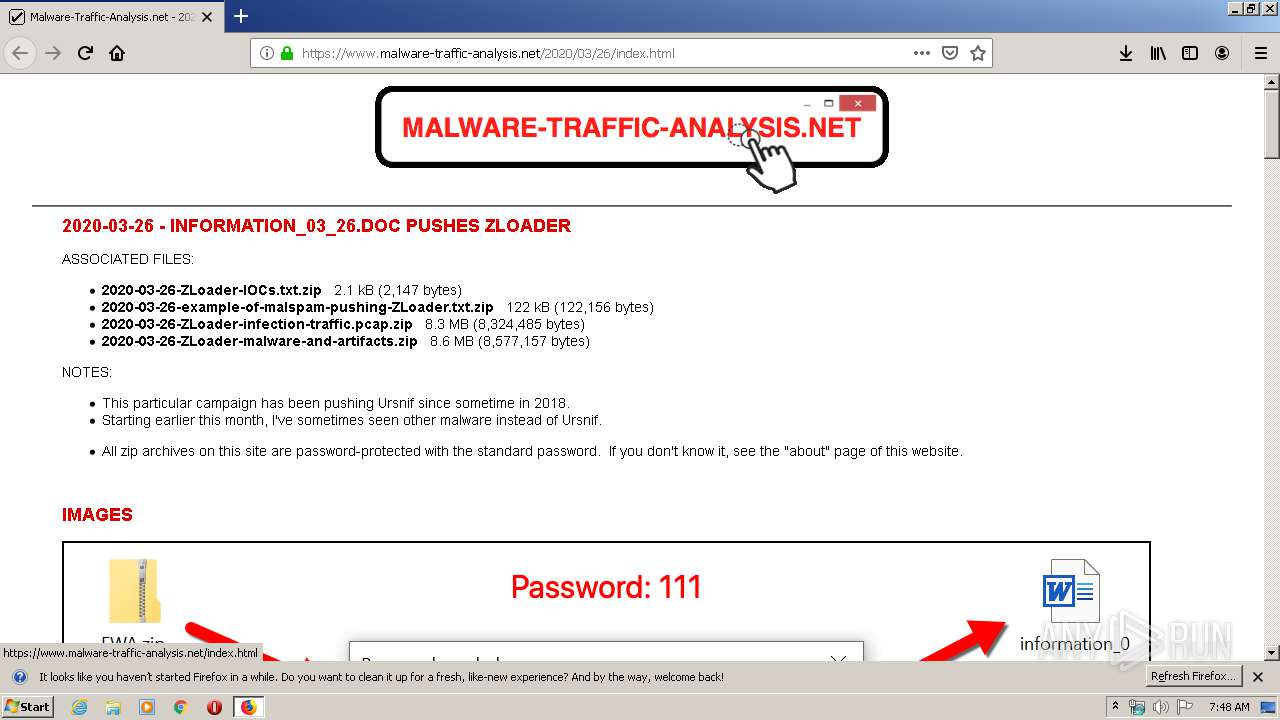
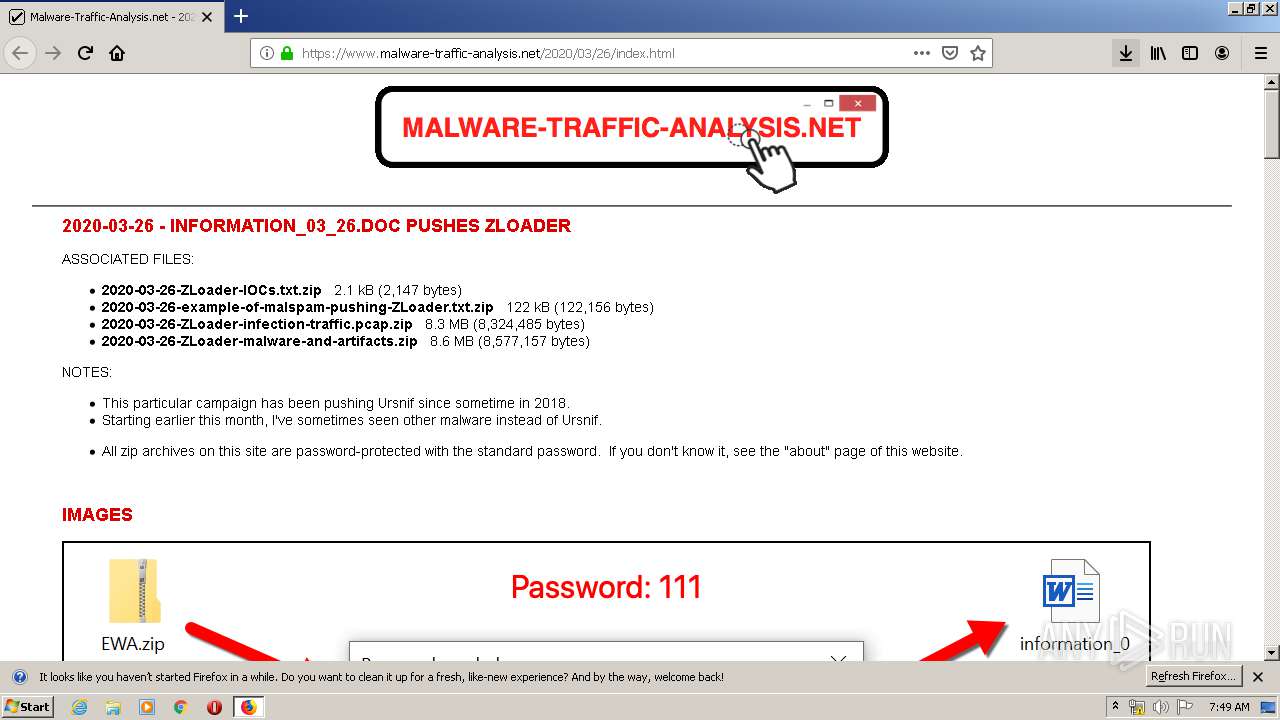
| URL: | https://www.malware-traffic-analysis.net/2020/03/26/index.html |
| Full analysis: | https://app.any.run/tasks/2da5ca1c-70fd-4272-ba5a-f58119dc35e0 |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 06:48:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | BE7C019A6D1B7DA438E6BD530C1D34EF |
| SHA1: | BF27FA8B8DFF7522725E00B8724B0831BFF85A9B |
| SHA256: | 503A5EDA855C37D087AFCF157F43A1E7E6999DD0BD952B6C4CB2C8DA648A755E |
| SSDEEP: | 3:N8DSLHXWQfigcWMMLA23OTMG:2OLHpJY/QG |
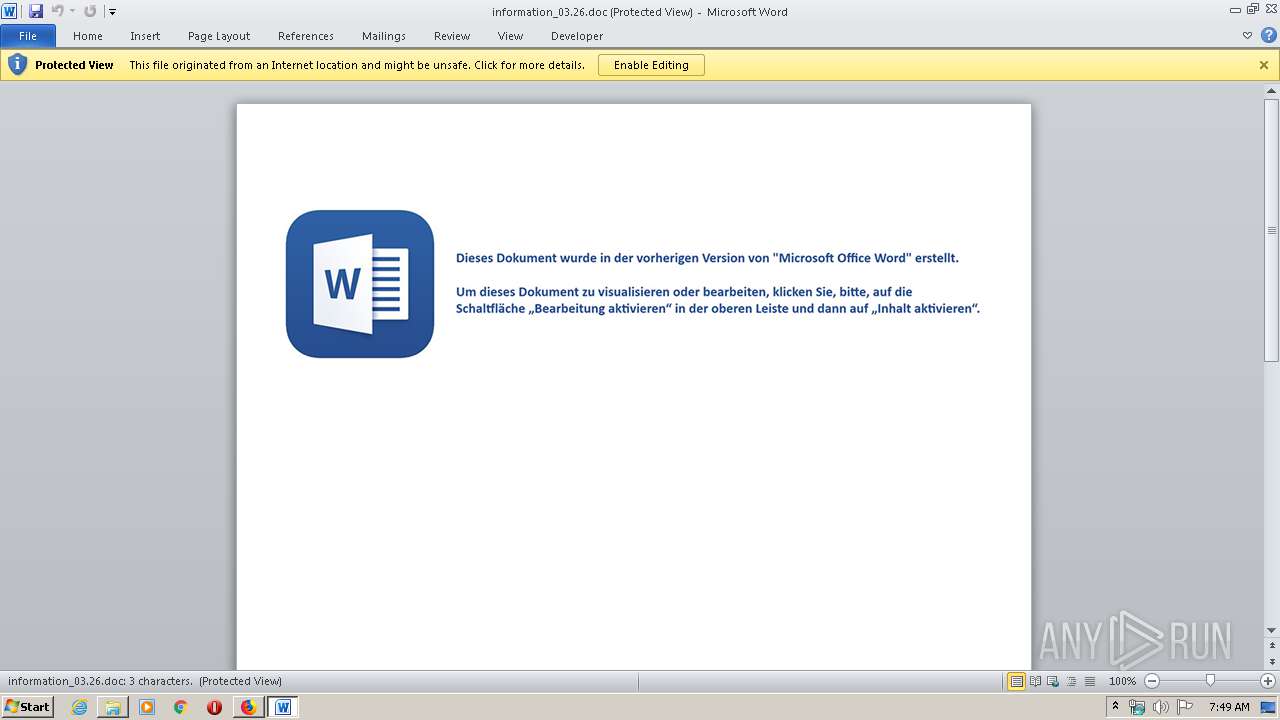
MALICIOUS
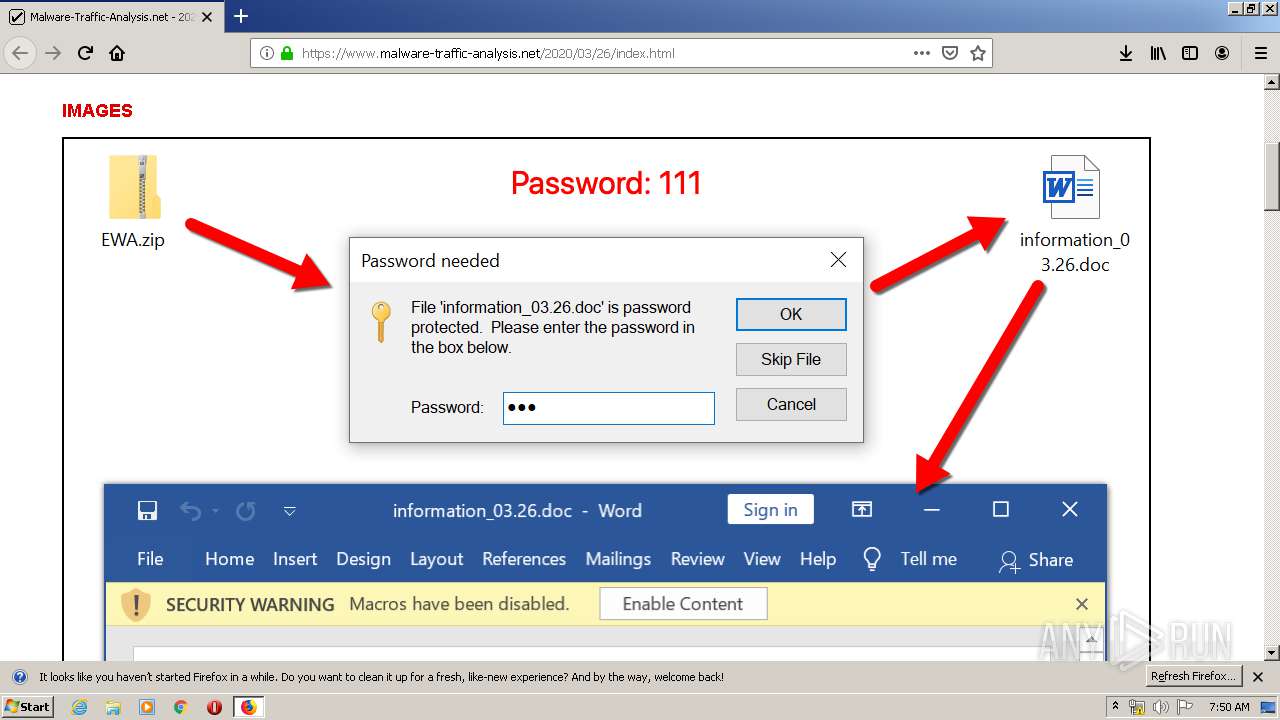
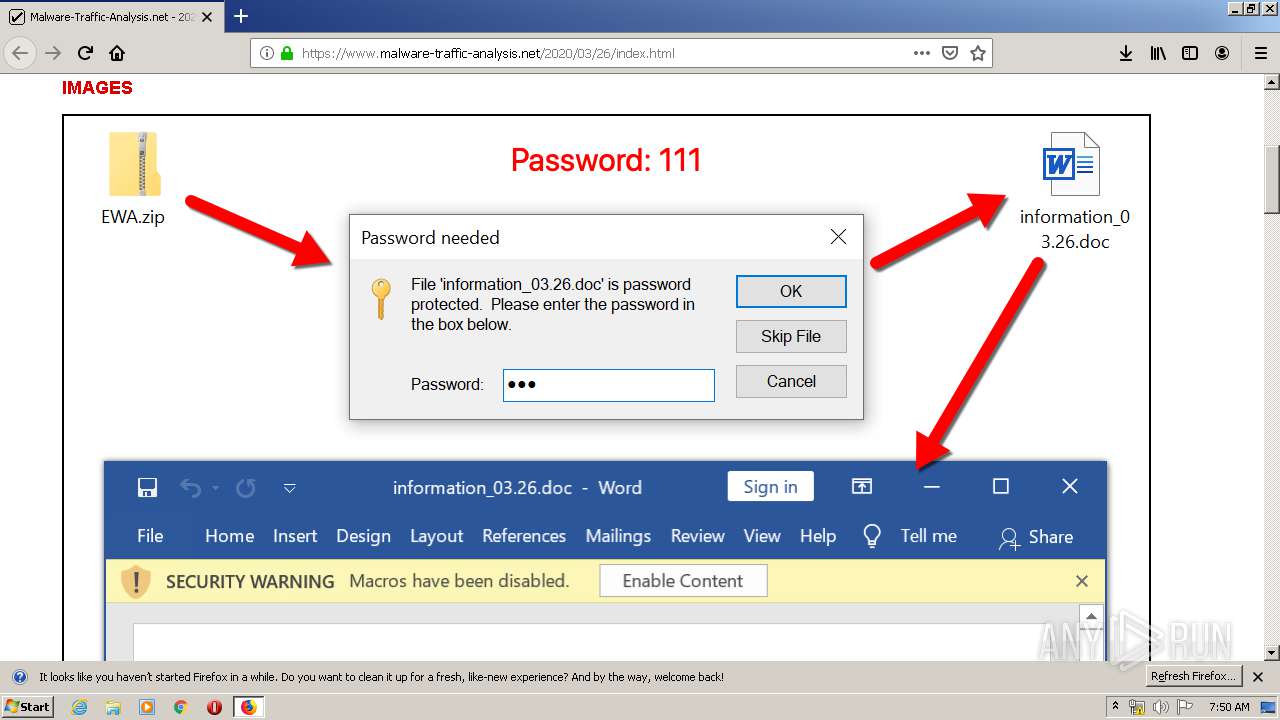
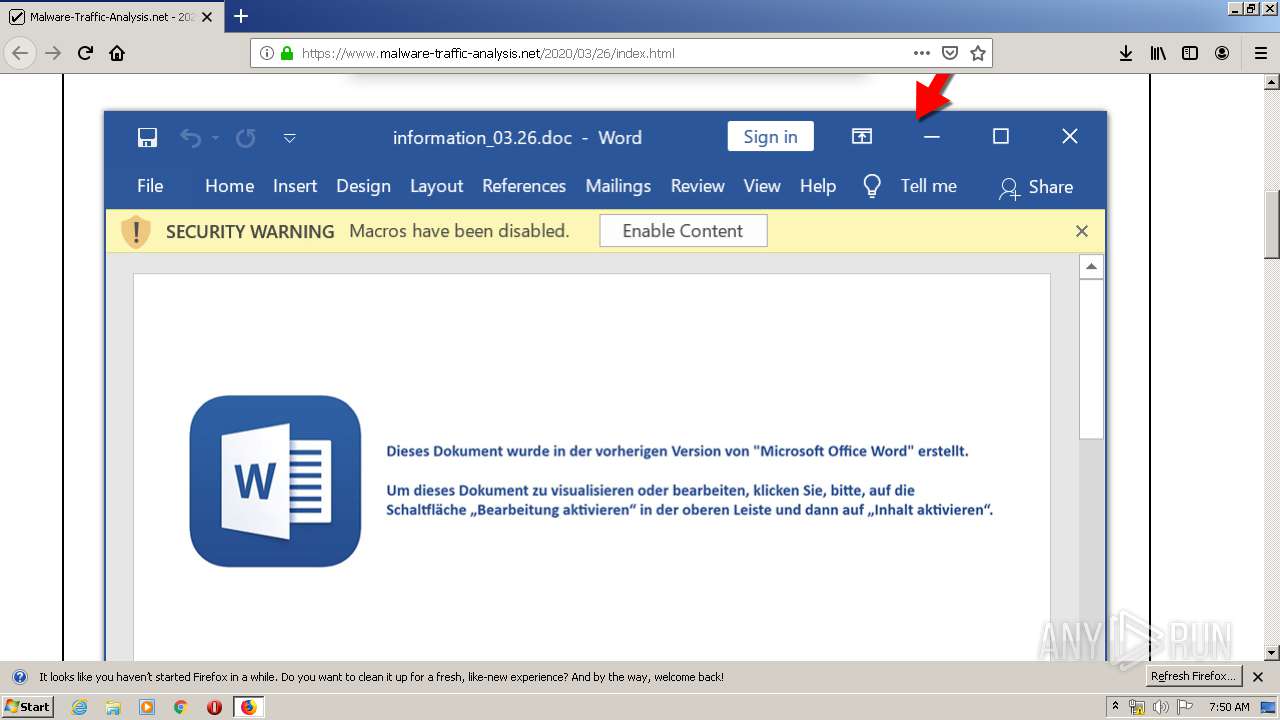
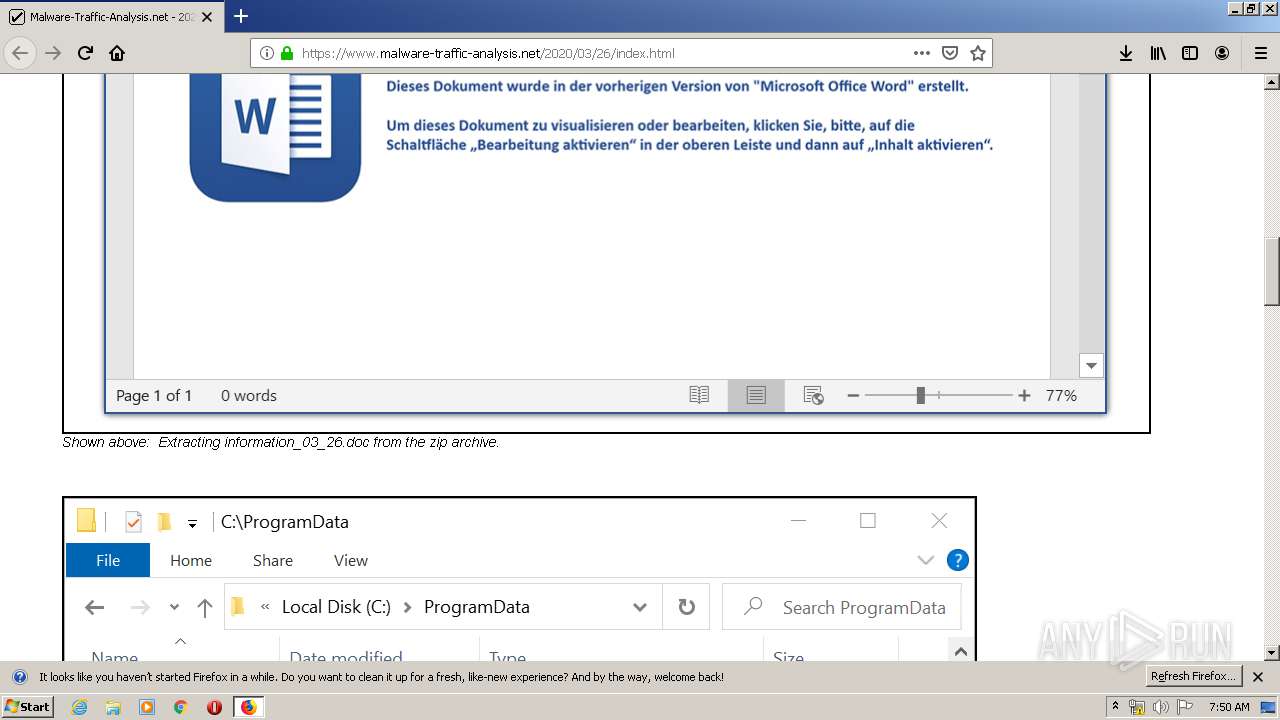
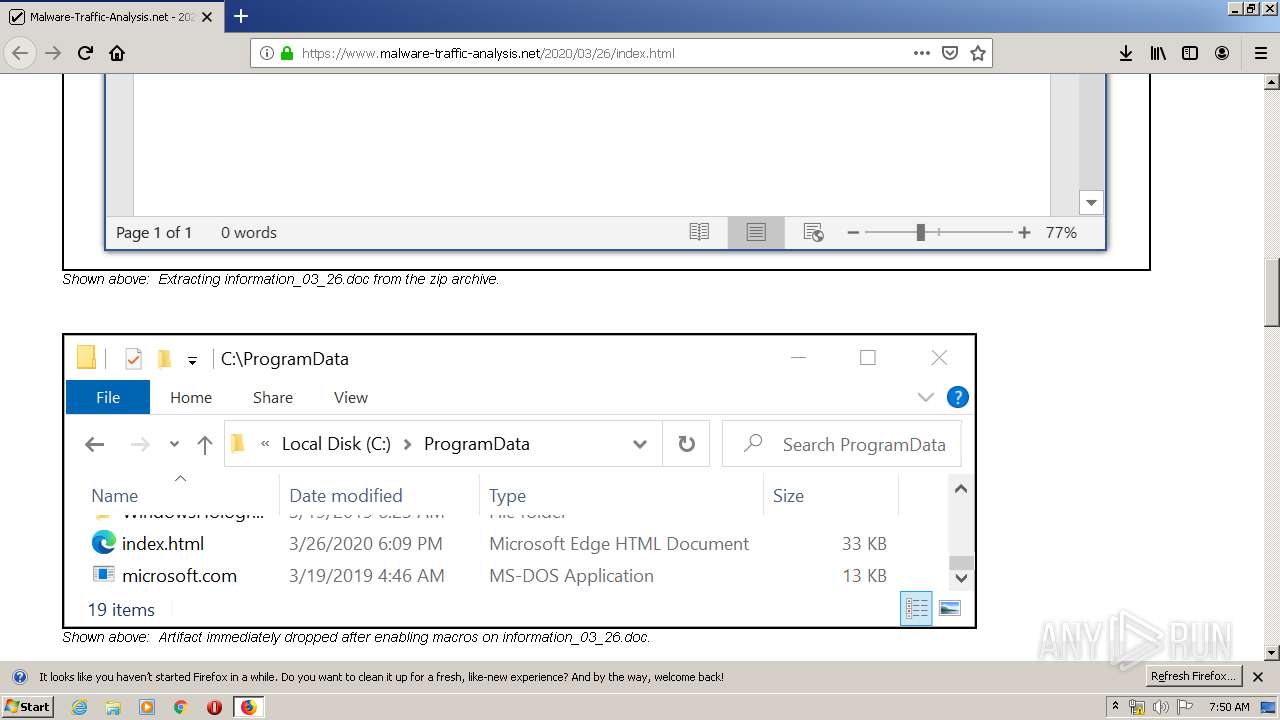
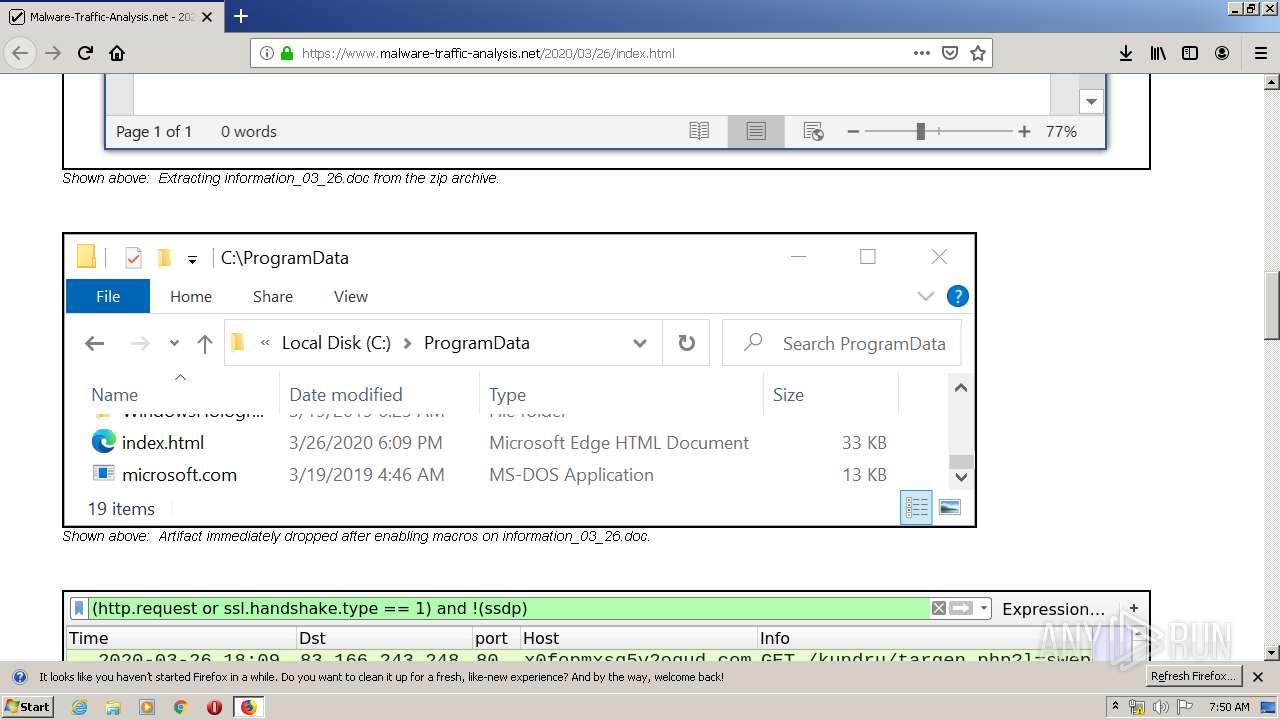
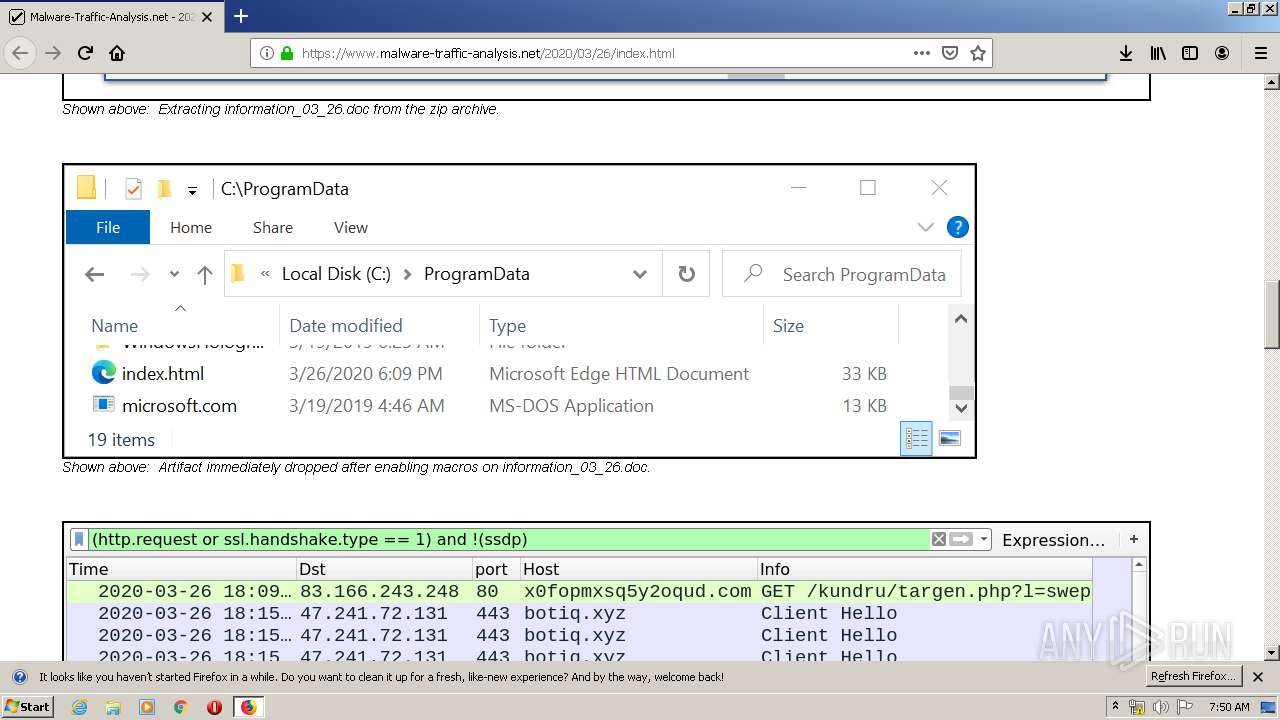
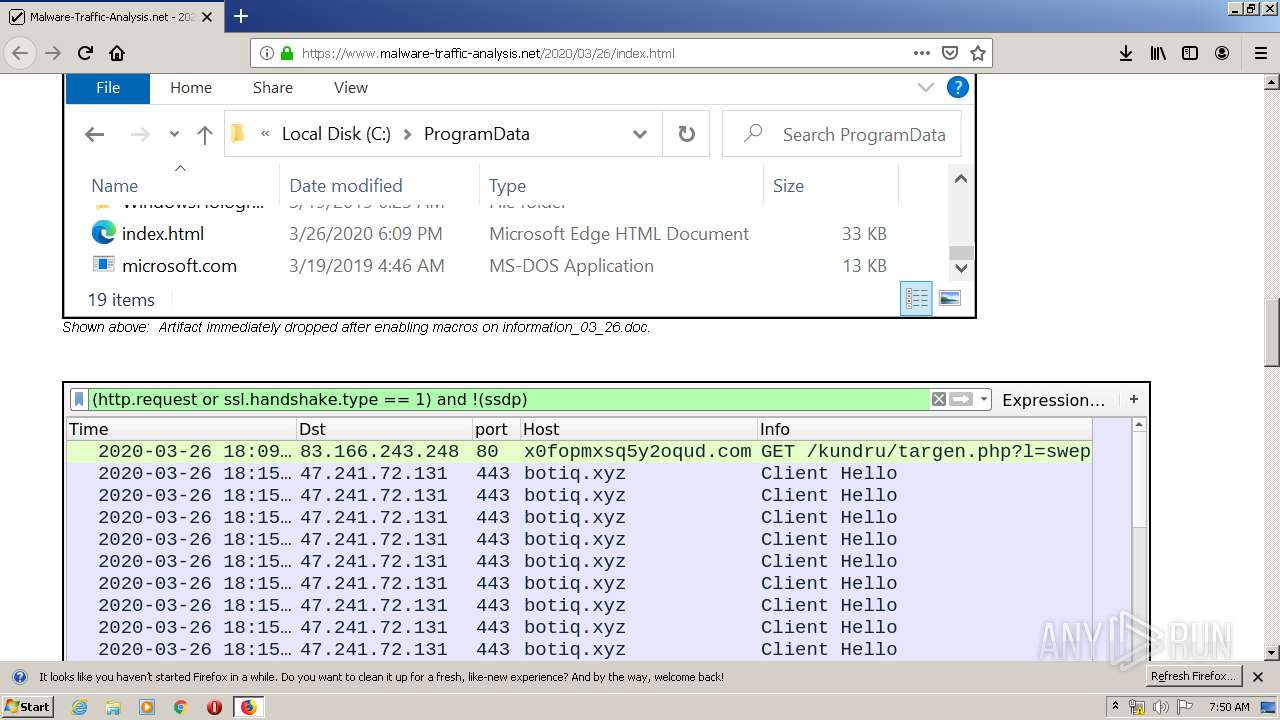
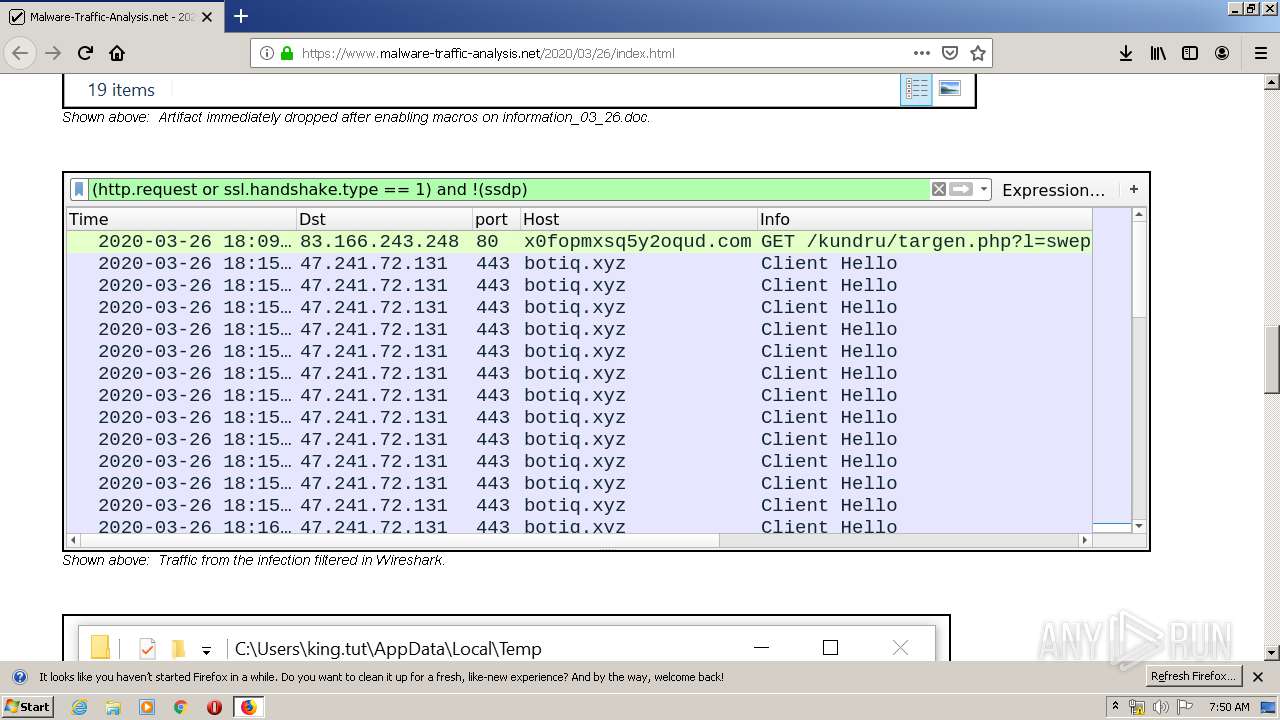
Drops known malicious document
- WinRAR.exe (PID: 2380)
- WINWORD.EXE (PID: 3852)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3548)
- explorer.exe (PID: 372)
SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 2936)
Creates files in the user directory
- explorer.exe (PID: 372)
Executable content was dropped or overwritten
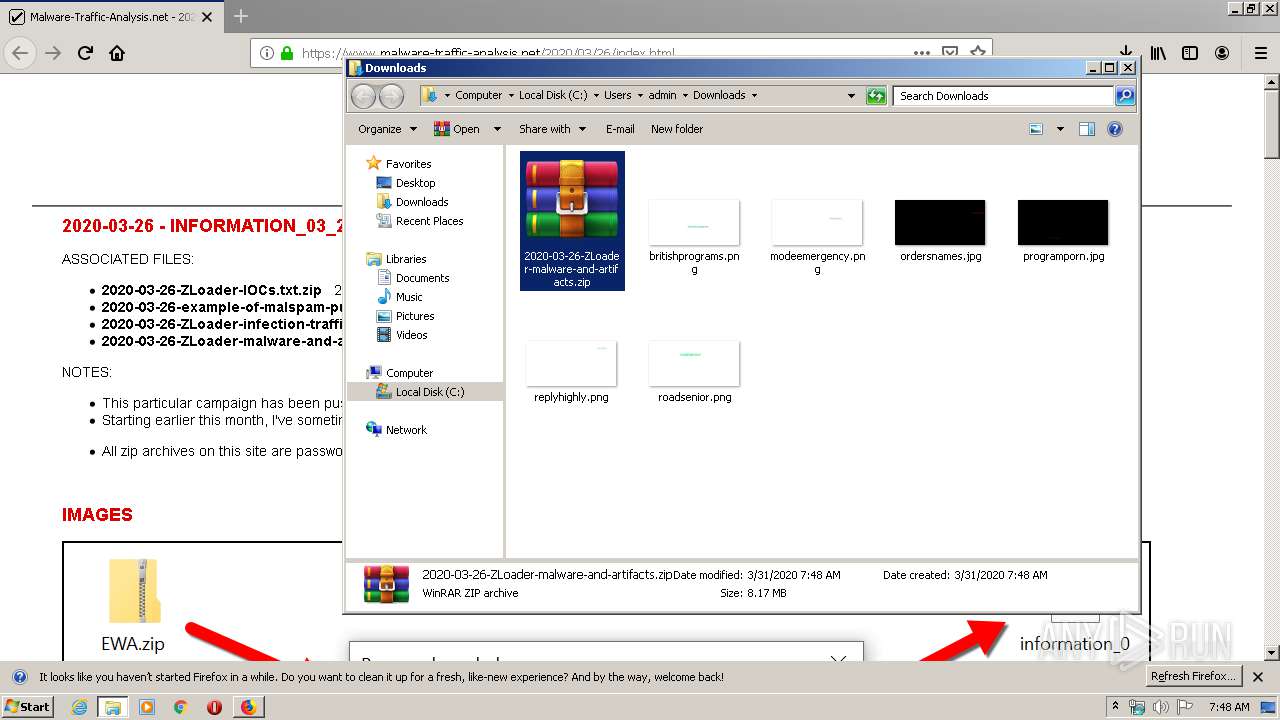
- WinRAR.exe (PID: 2380)
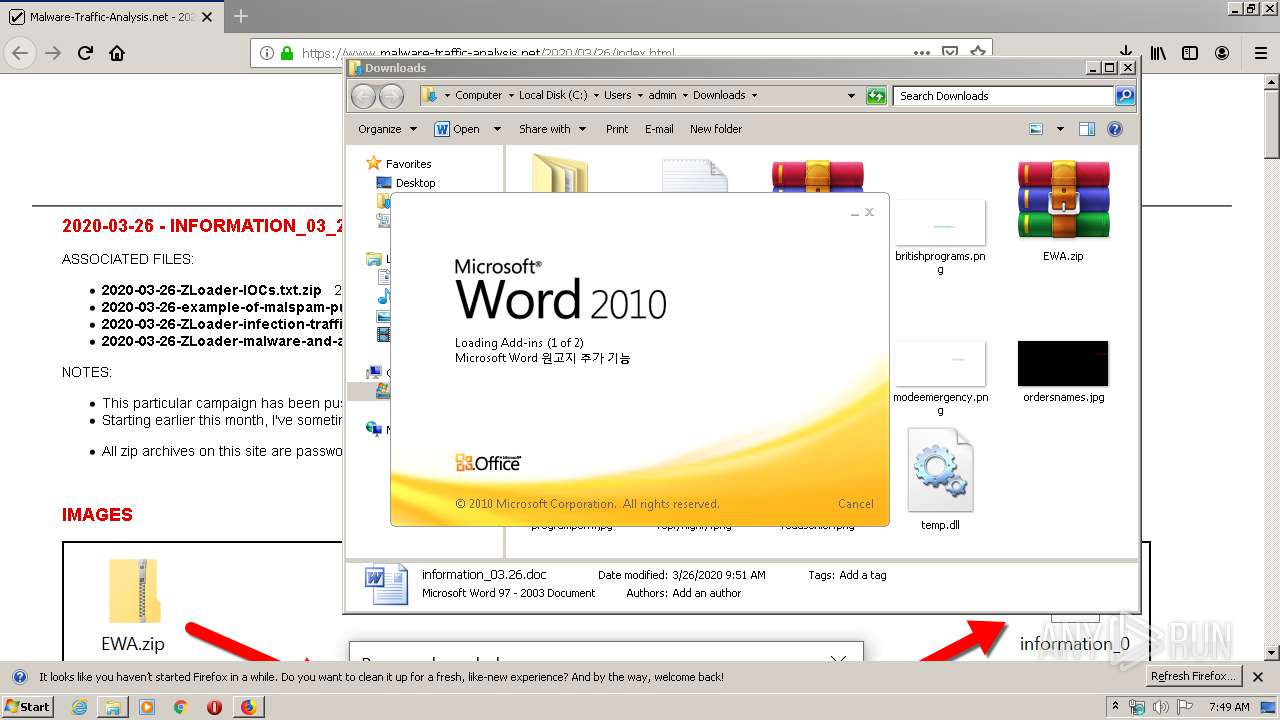
Application launched itself
- WINWORD.EXE (PID: 3852)
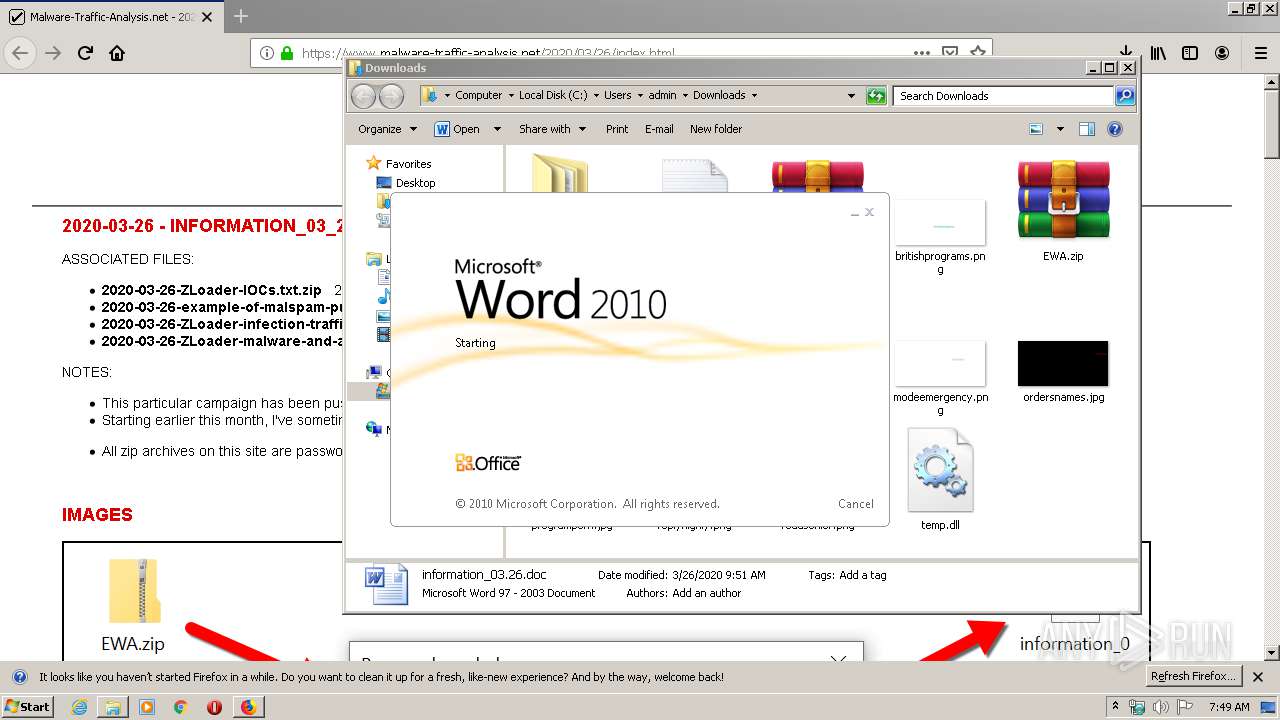
Starts Microsoft Office Application
- WINWORD.EXE (PID: 3852)
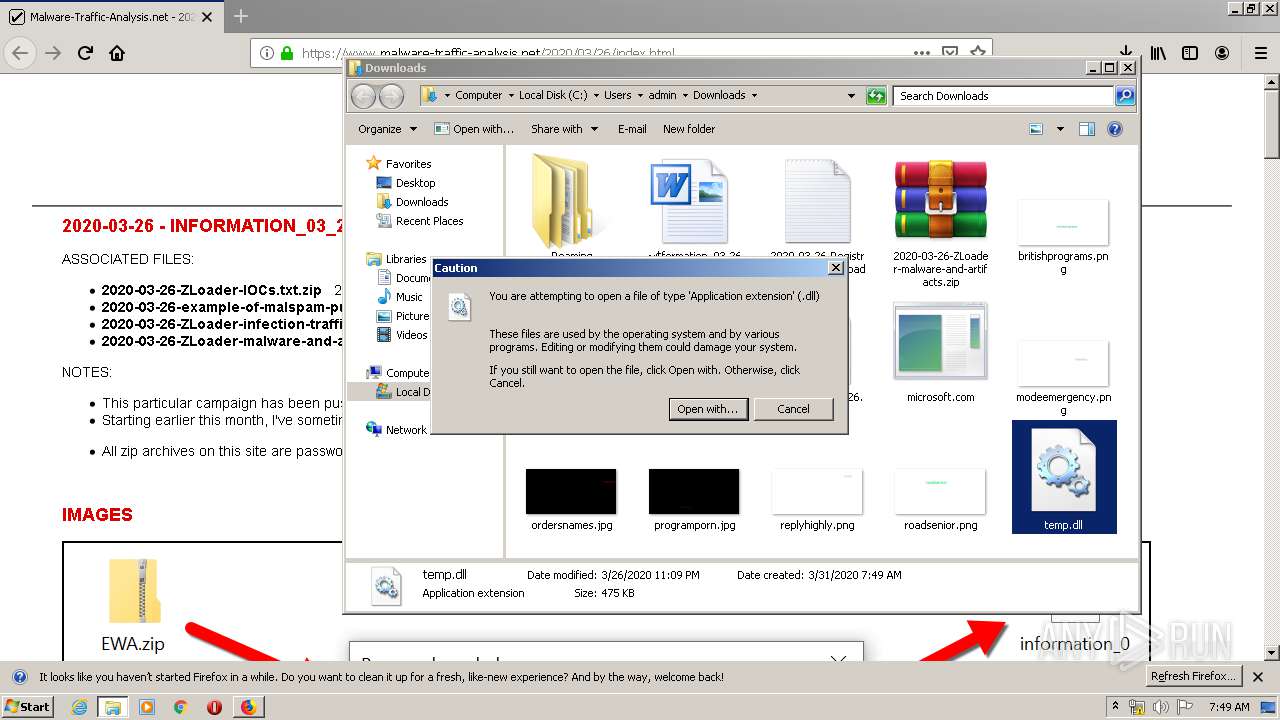
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 372)
INFO
Application launched itself
- firefox.exe (PID: 2936)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 2936)
Reads Internet Cache Settings
- firefox.exe (PID: 2936)
Reads CPU info
- firefox.exe (PID: 2936)
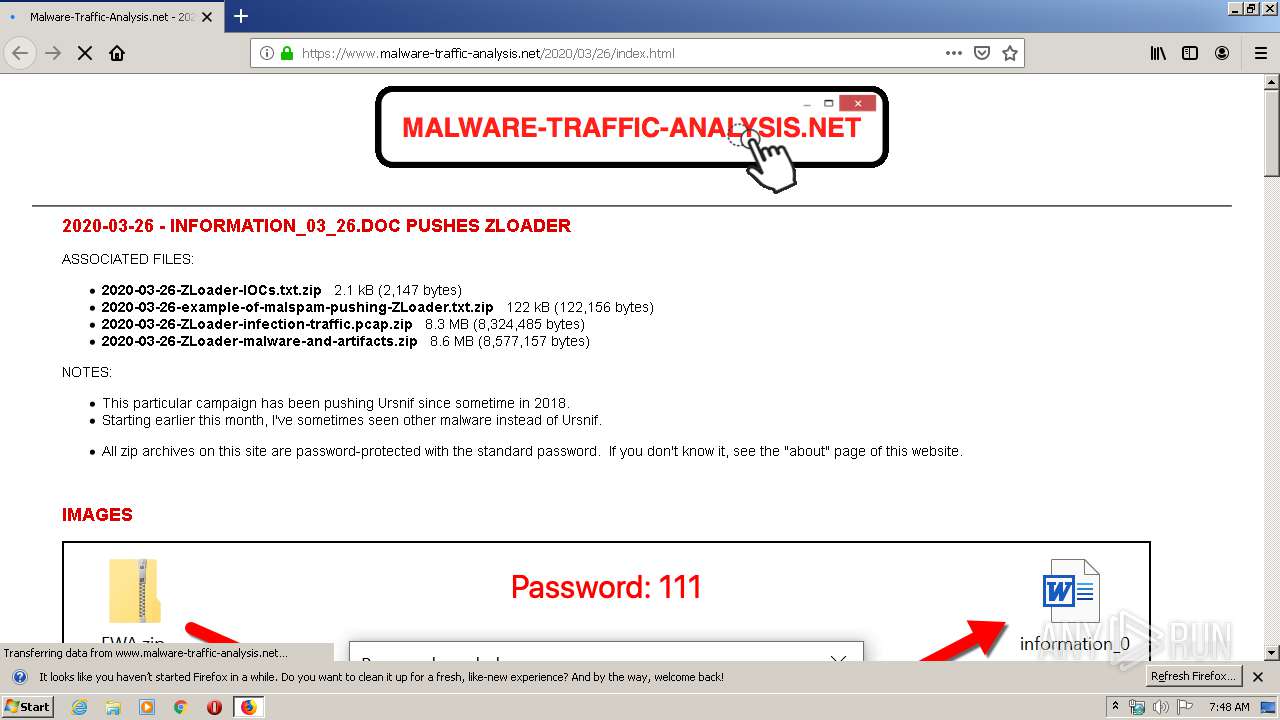
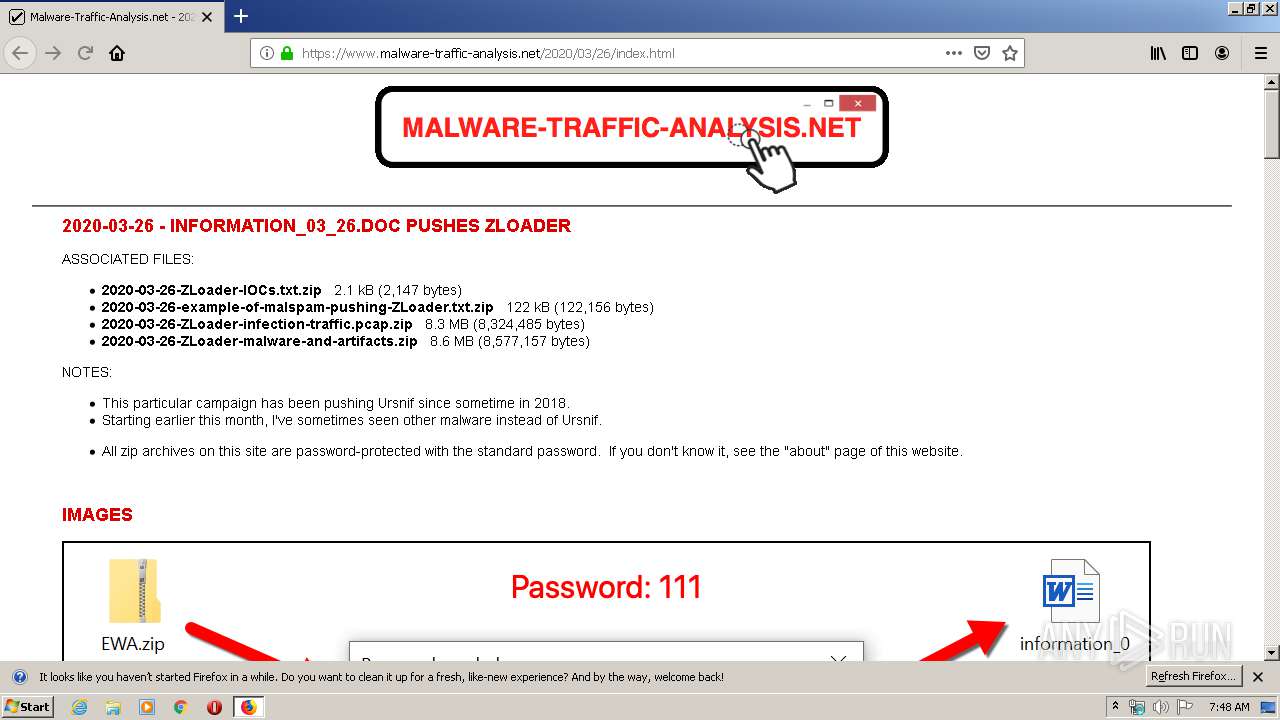
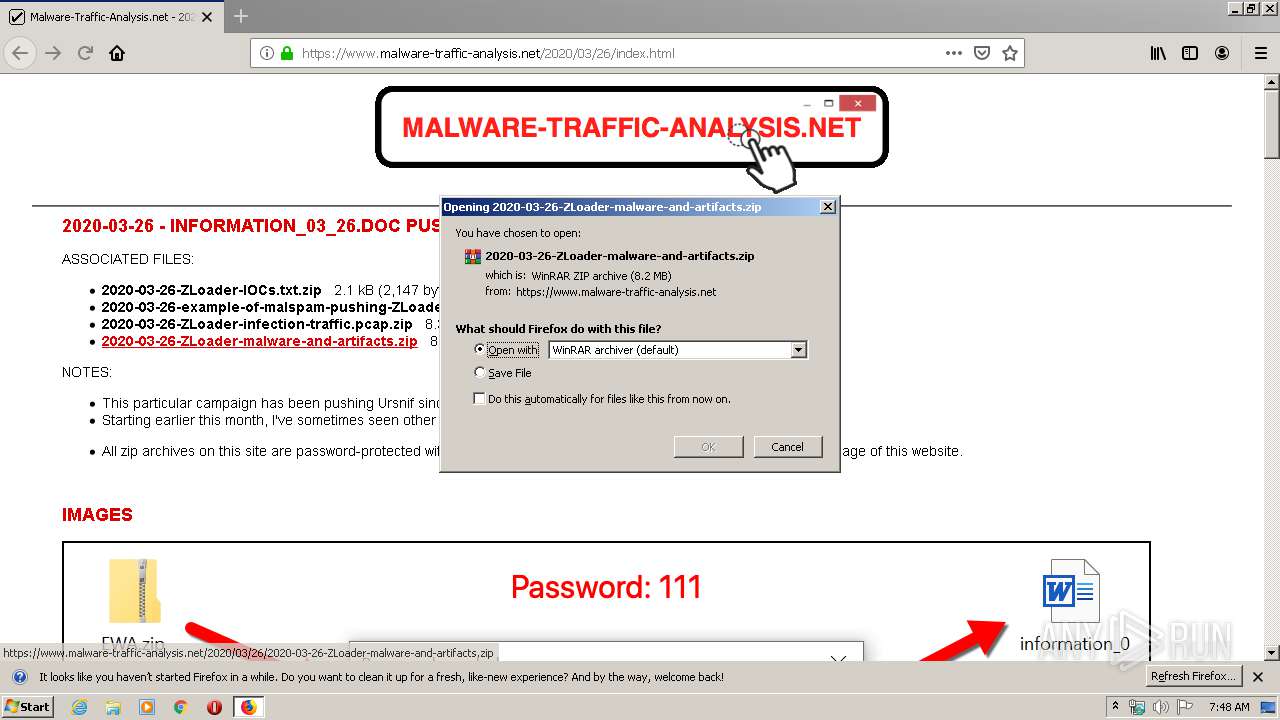
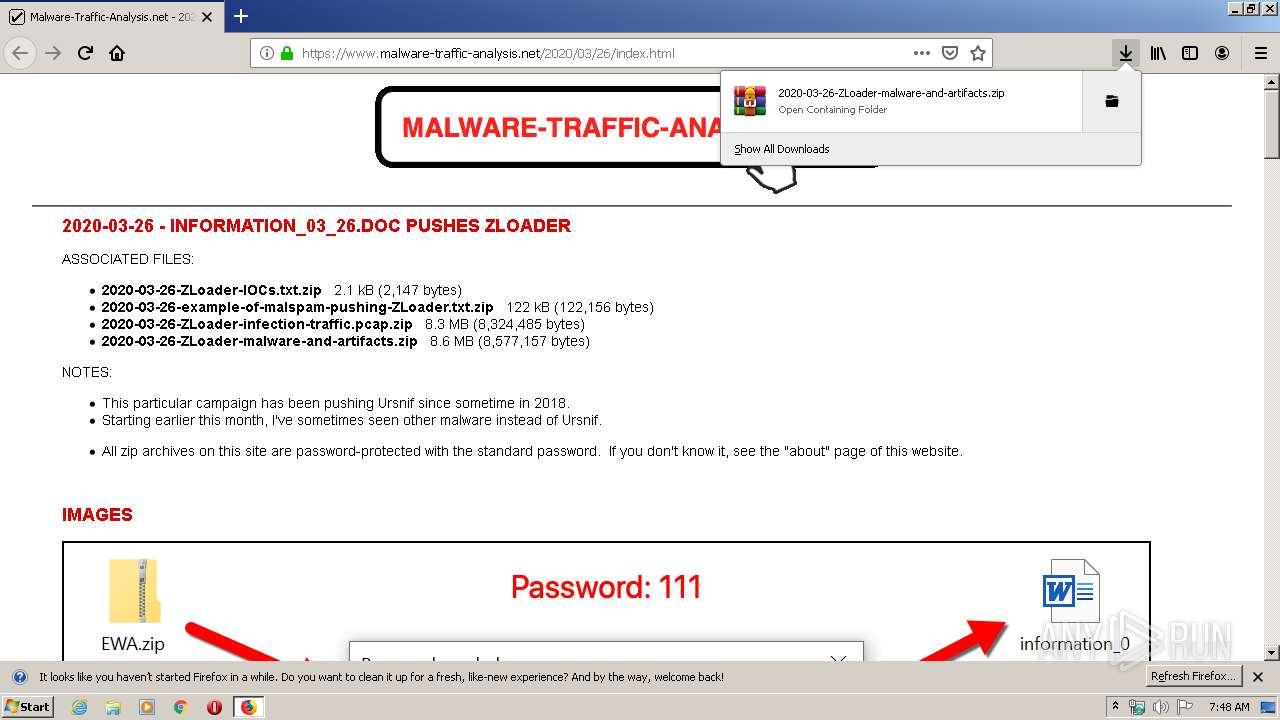
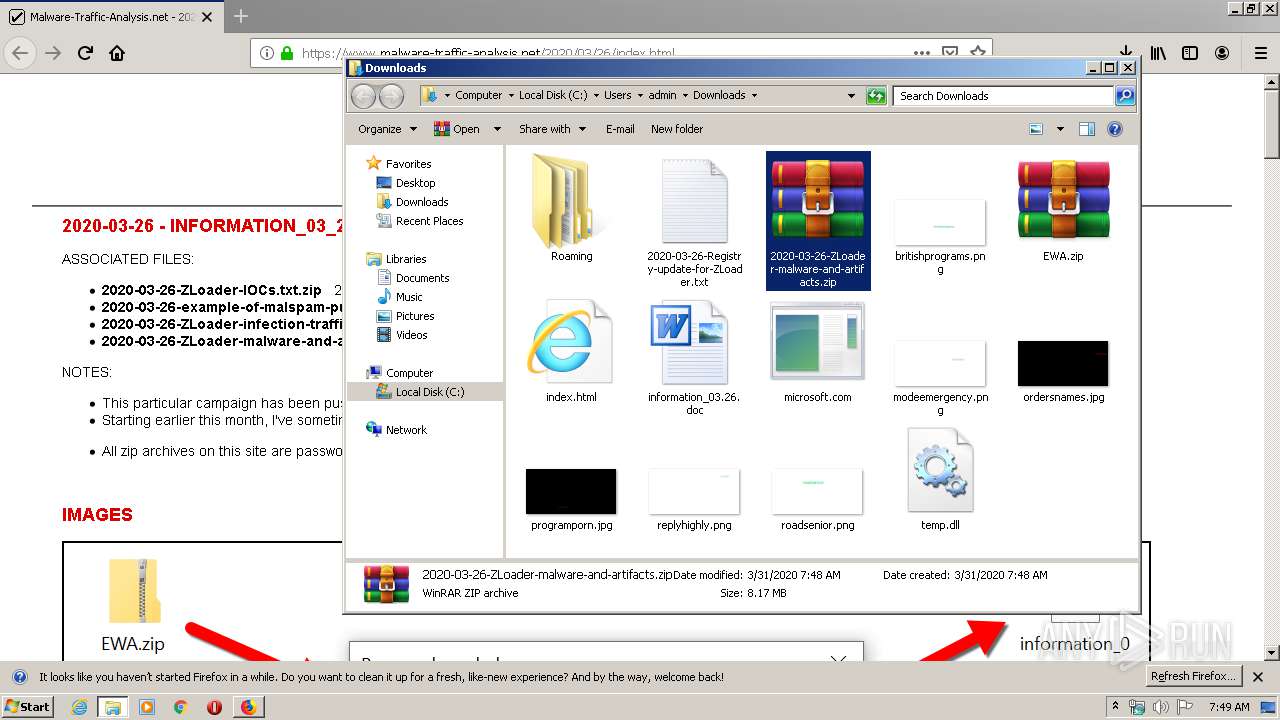
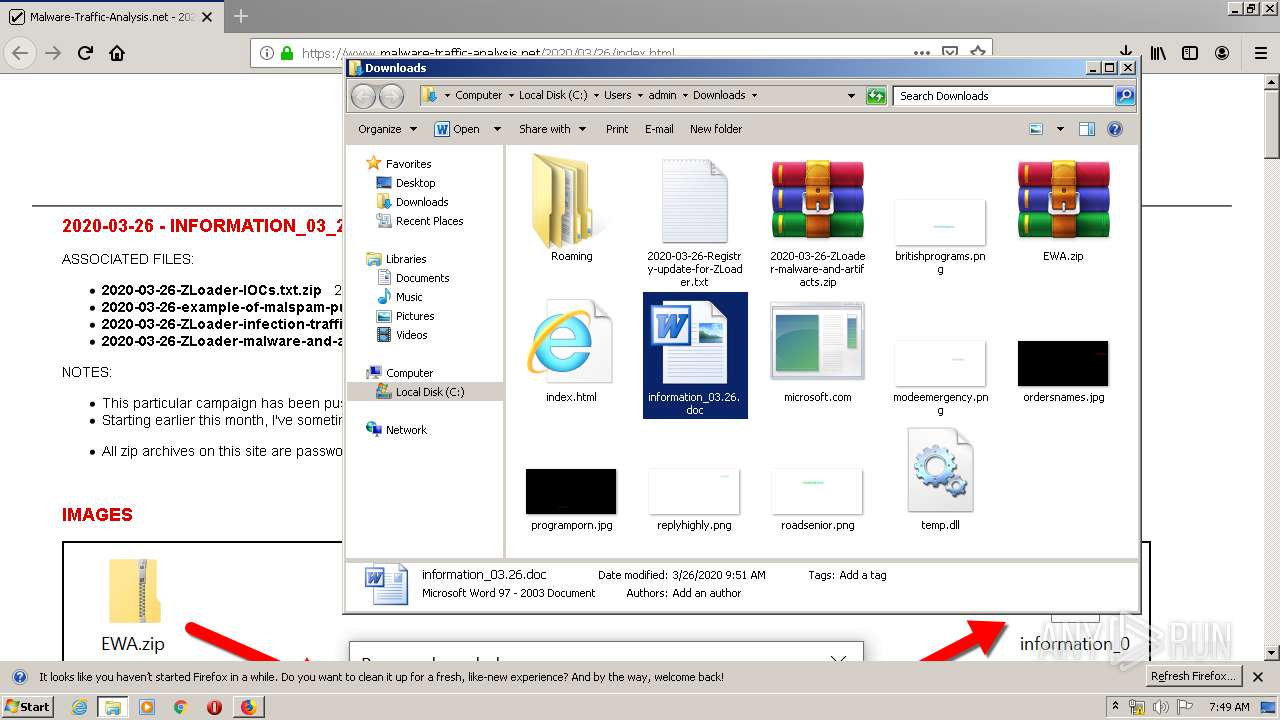
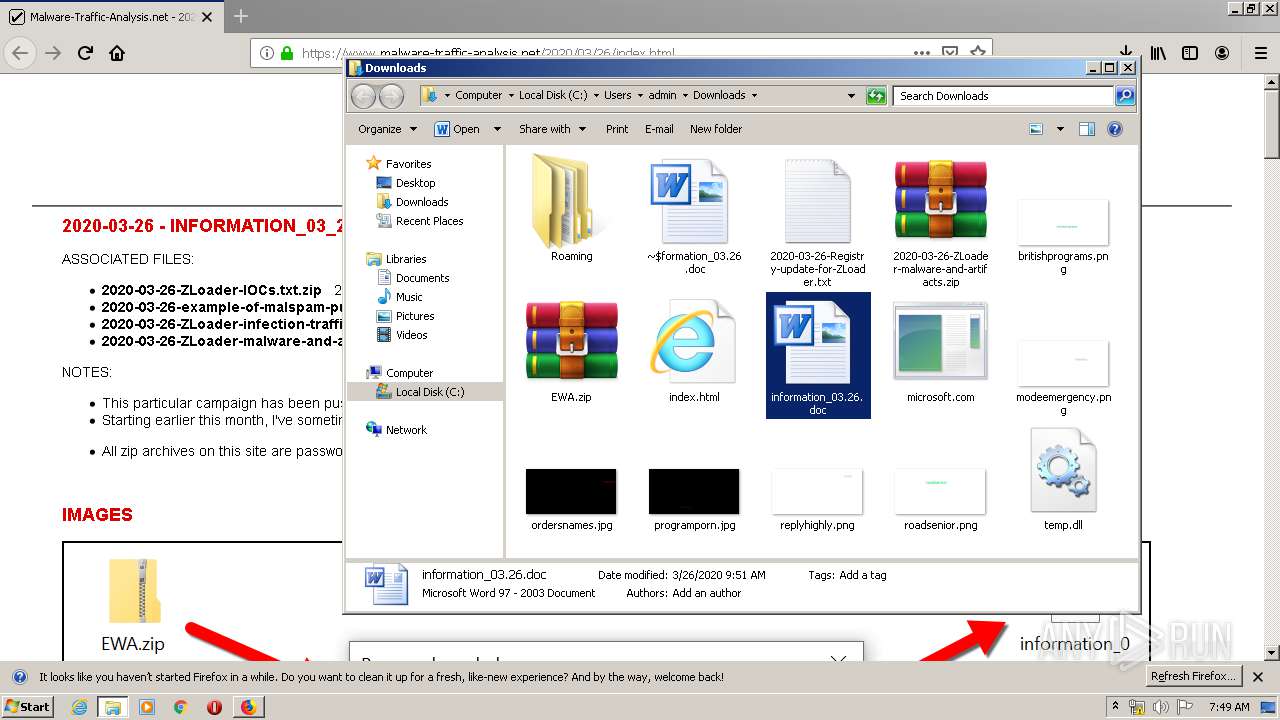
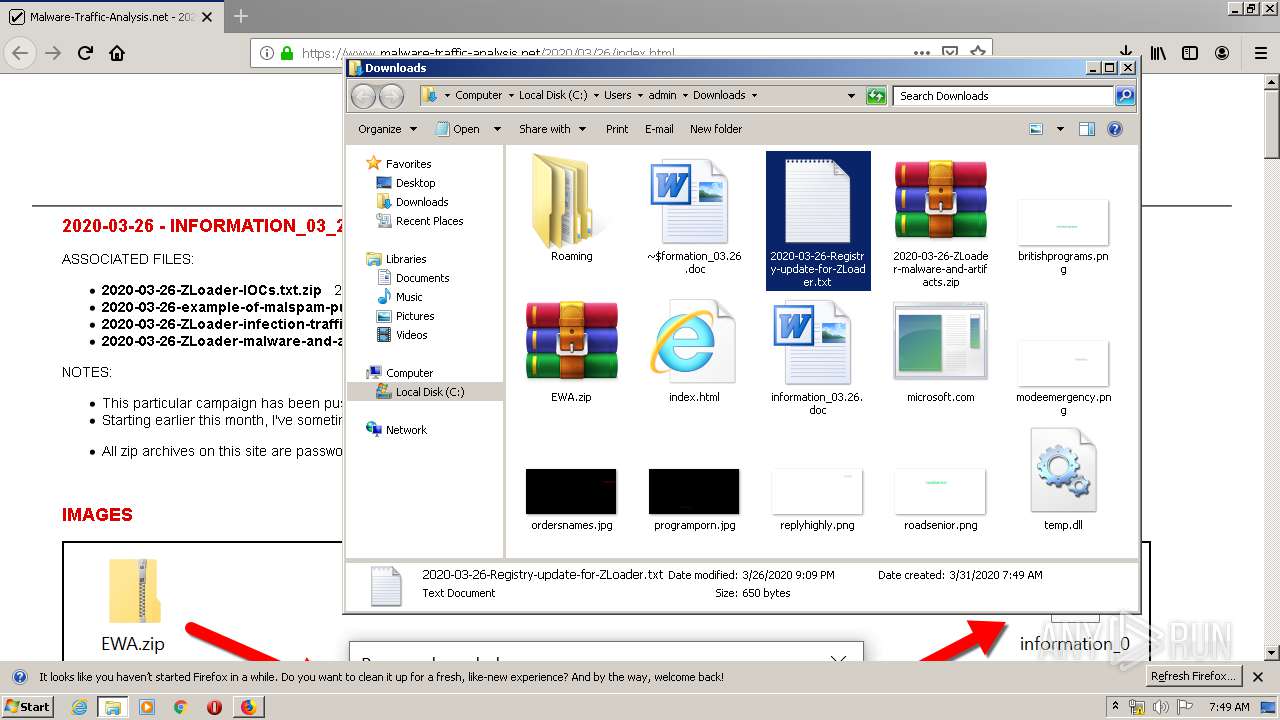
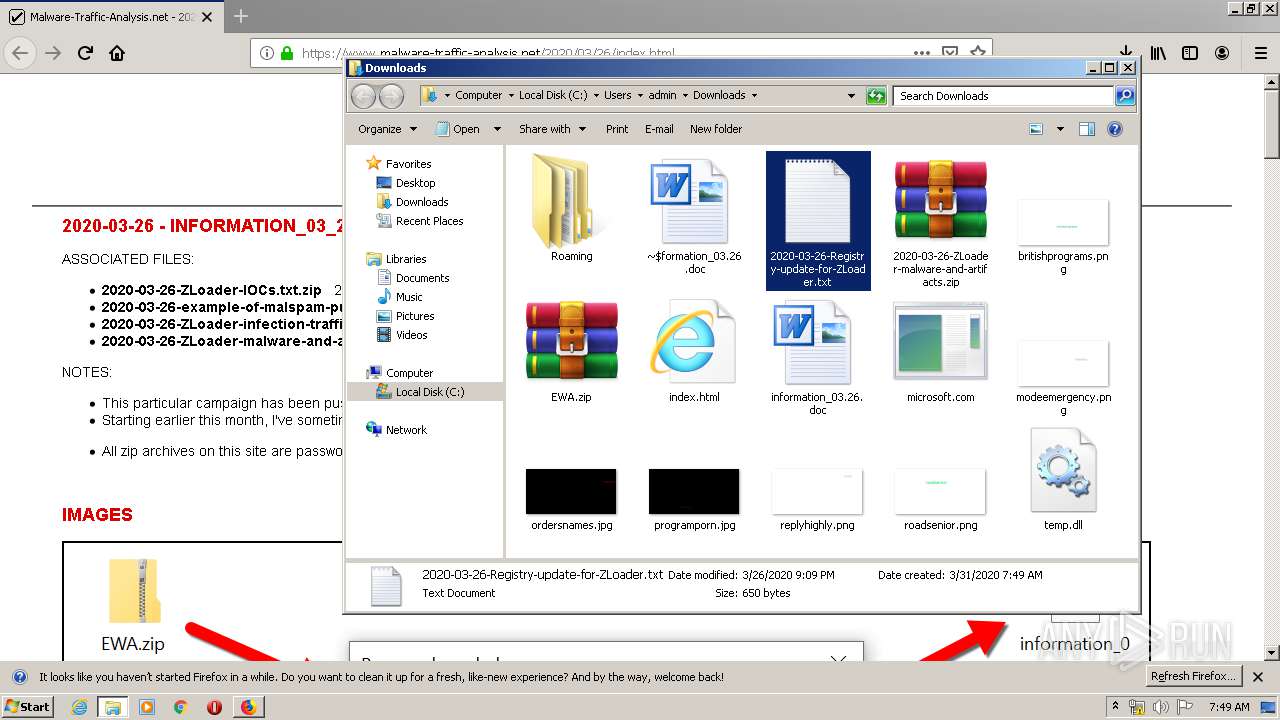
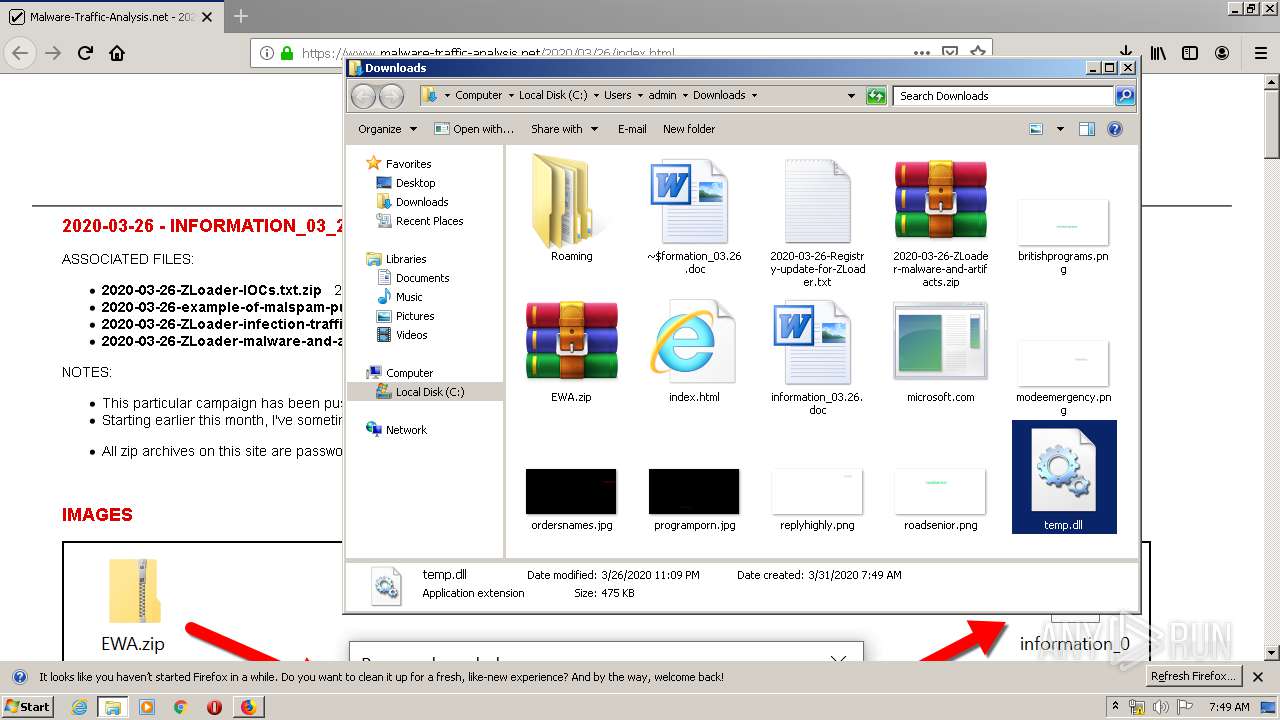
Manual execution by user
- WinRAR.exe (PID: 2380)
- WINWORD.EXE (PID: 3852)
- NOTEPAD.EXE (PID: 2736)
- rundll32.exe (PID: 1712)
Creates files in the user directory
- firefox.exe (PID: 2936)
- WINWORD.EXE (PID: 3852)
Starts Microsoft Office Application
- explorer.exe (PID: 372)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3852)
- WINWORD.EXE (PID: 2668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
13
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 916 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2936.3.702834255\710548357" -childID 1 -isForBrowser -prefsHandle 1716 -prefMapHandle 1320 -prefsLen 1 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2936 "\\.\pipe\gecko-crash-server-pipe.2936" 1632 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1712 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Downloads\temp.dll | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2936.0.1341437325\876402343" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2936 "\\.\pipe\gecko-crash-server-pipe.2936" 1168 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
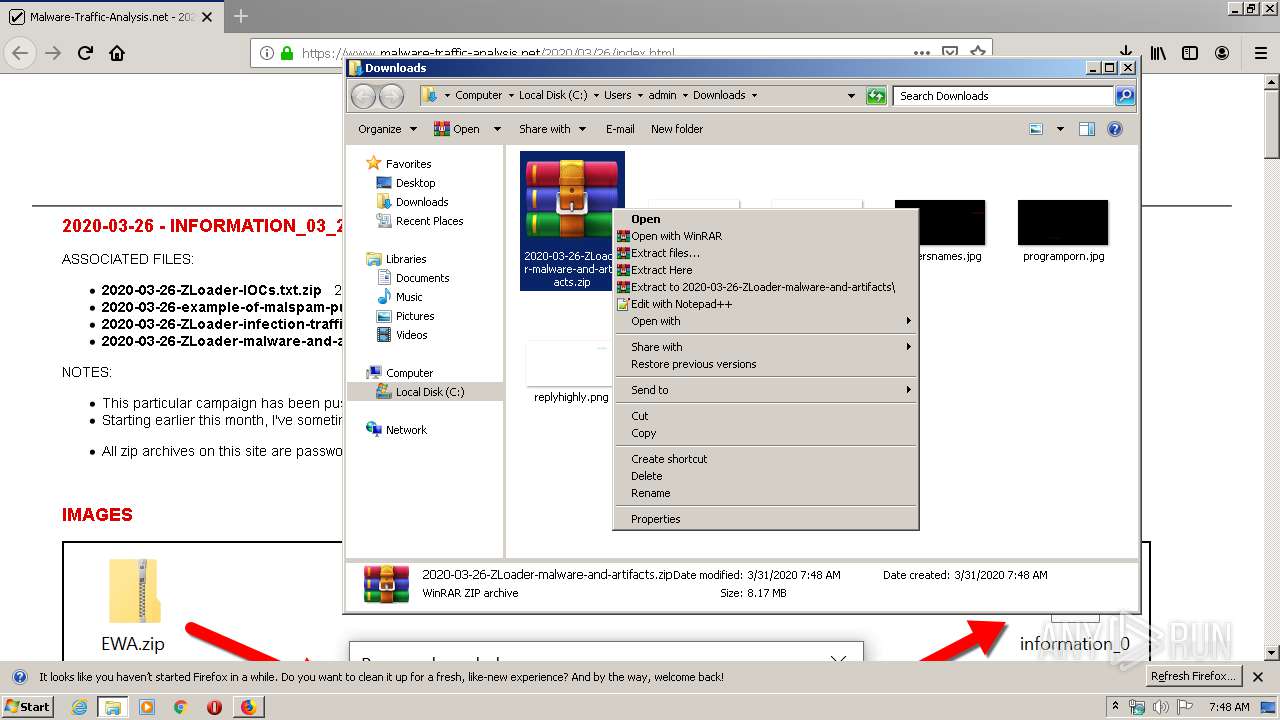
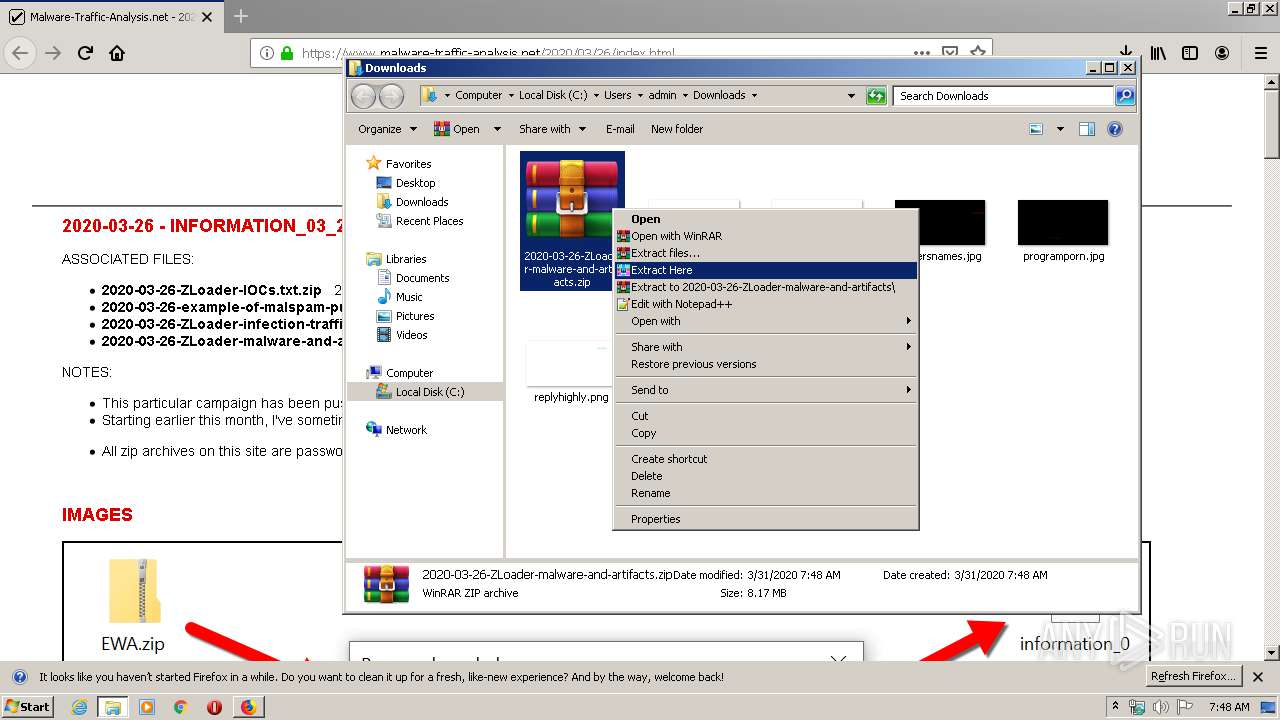
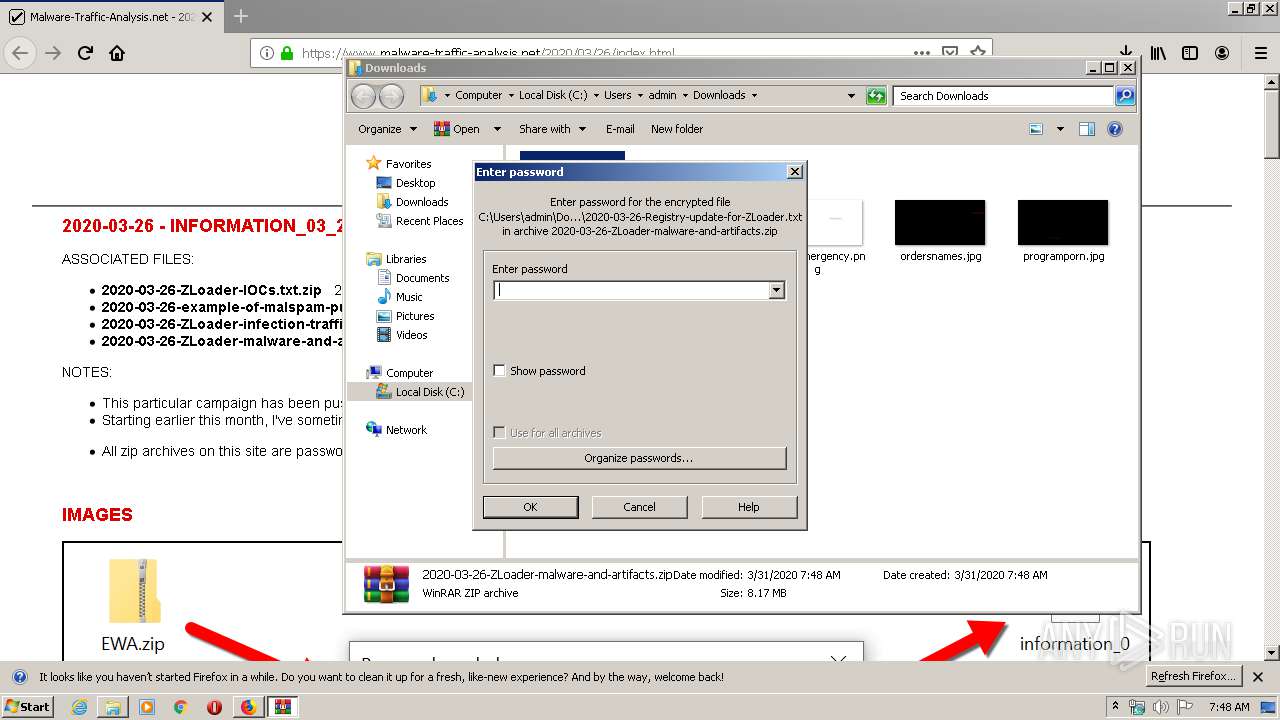
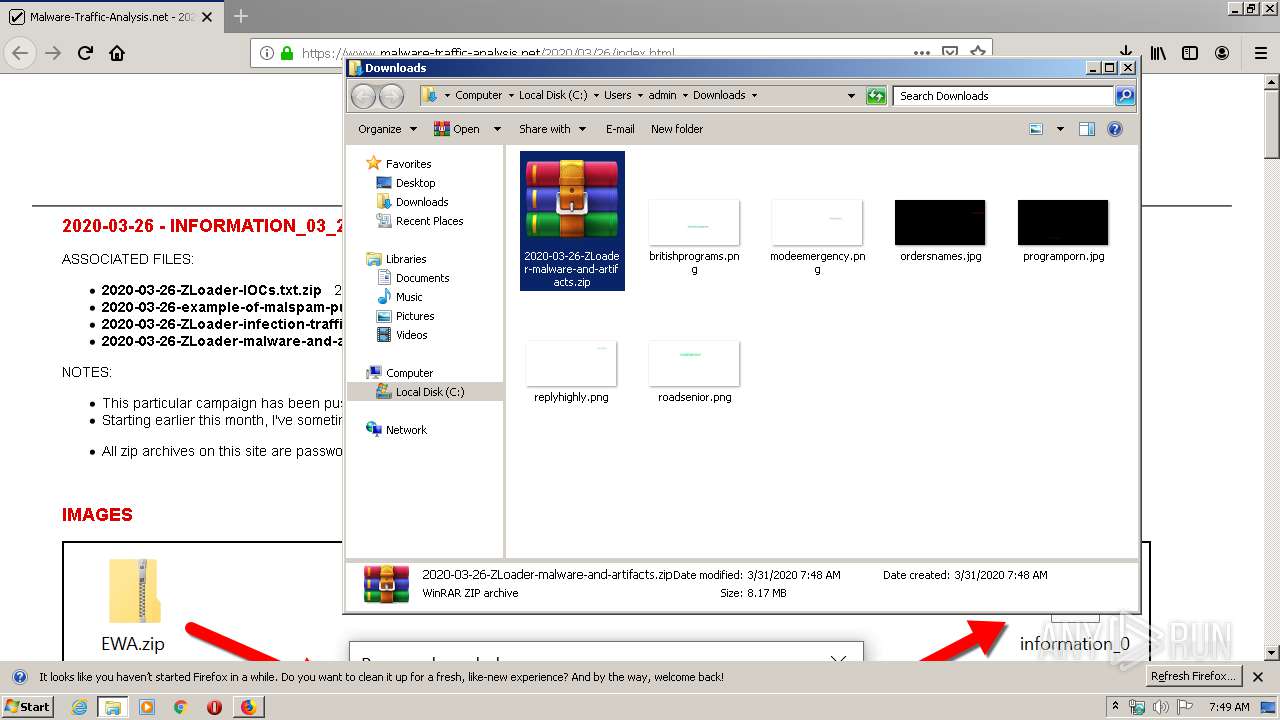
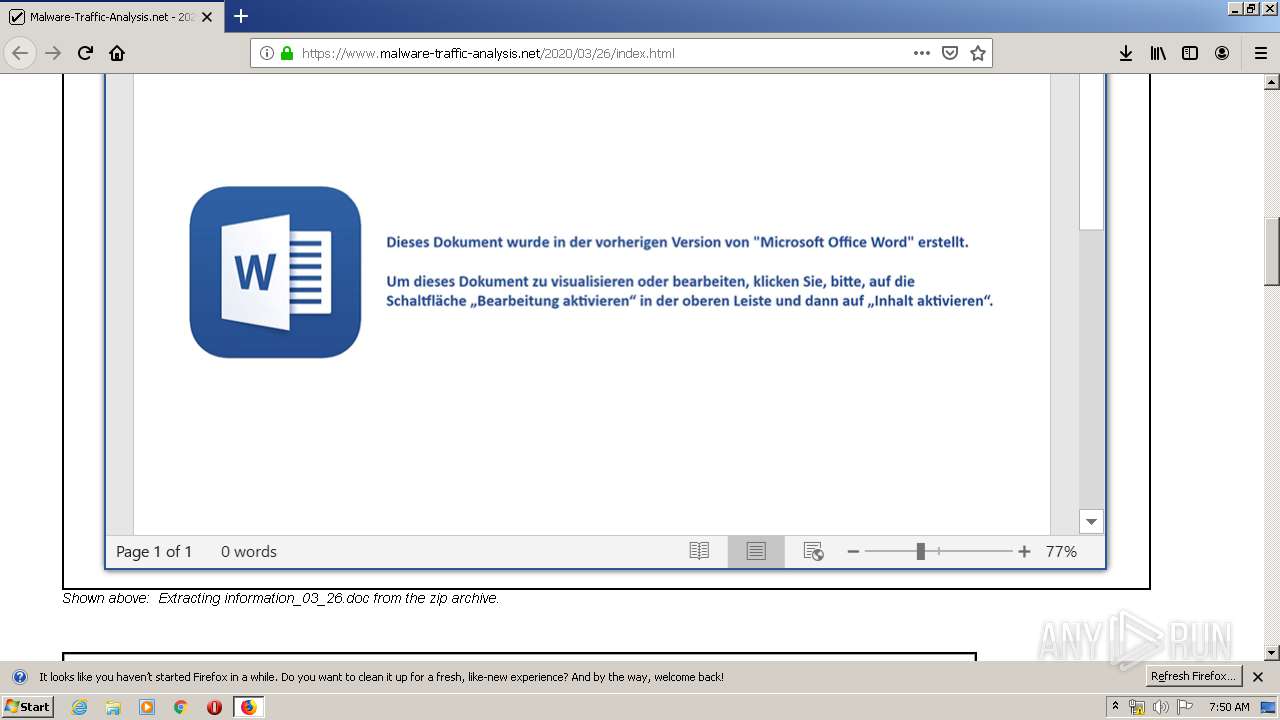
| 2380 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\2020-03-26-ZLoader-malware-and-artifacts.zip" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2556 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2936.20.703282185\1653837285" -childID 3 -isForBrowser -prefsHandle 3736 -prefMapHandle 3740 -prefsLen 7195 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2936 "\\.\pipe\gecko-crash-server-pipe.2936" 3752 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2668 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
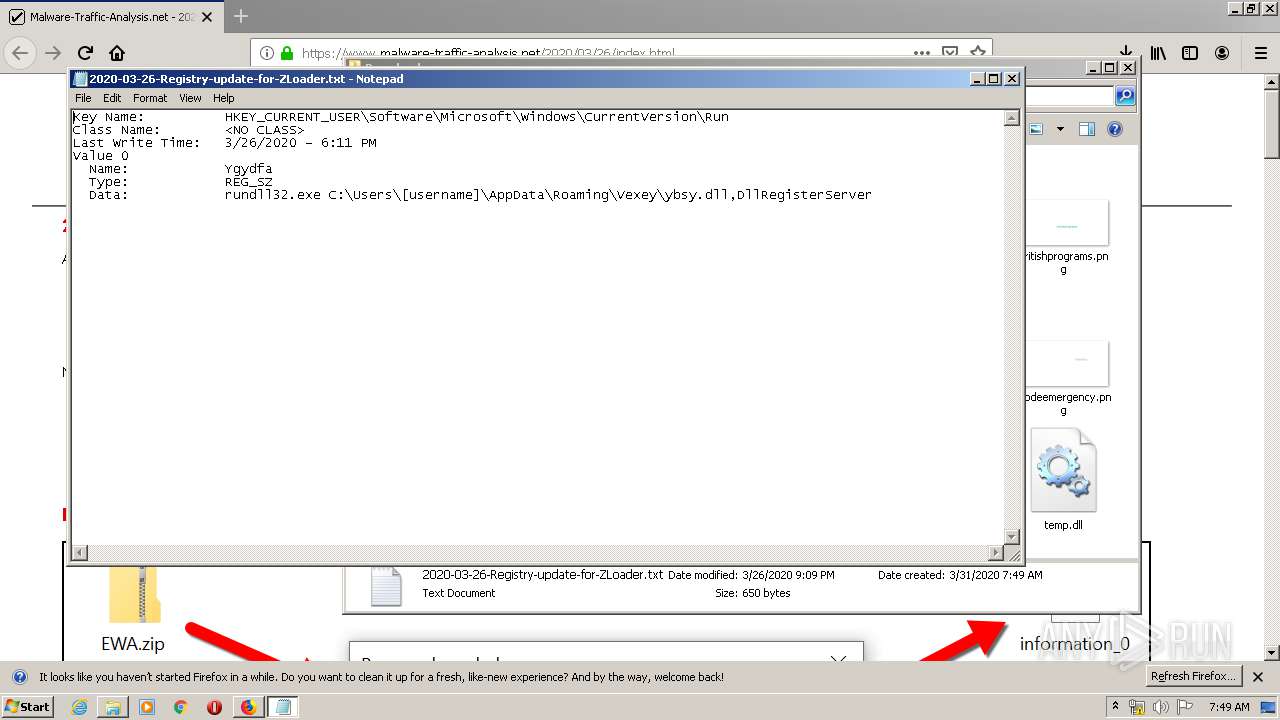
| 2736 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Downloads\2020-03-26-Registry-update-for-ZLoader.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2936 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://www.malware-traffic-analysis.net/2020/03/26/index.html | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3084 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://www.malware-traffic-analysis.net/2020/03/26/index.html" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
Total events
4 406
Read events
3 623
Write events
744
Delete events
39
Modification events
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3084) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 3363BAED08000000 | |||
| (PID) Process: | (2936) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 1C49BDED08000000 | |||
| (PID) Process: | (2936) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (2936) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2936) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | 308046O0NS4N39PO |
Value: 00000000090000000D000000CC190500000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF605D425CD146D50100000000 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000003F0000004F000000F9A625000A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED010A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED010A00000018000000868F0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000005CE9ED0100000000000000000000000000000000480B20020000000005000000D80B200200000000340C200270E9ED01C0E9ED010000000000000000C0DB2002050000002000000000000000000000000100000064666C7464666C7400000000400000000459A377AD0501A70000000000000000010000000000000000000000B02D0C08A82C0C08A4E9ED013DA9D27600000000FBFFFF7FC8E9ED01987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000371054065310540637105406000000000000000000000000080000002E006C006E006B0000006E006400200011000000483D3200403D32002E006C006E006B0000002F0080EA0000C85704AB34EAED018291D27680EAED01EC430000E45704AB48EAED01B69CD276F04311024C06000060EAED01603F11026CEAED0111000000483D3200403D320060EAED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED01 | |||
| (PID) Process: | (2936) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2936) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
3
Suspicious files
82
Text files
47
Unknown types
77
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2936 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2936 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 2936 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 2936 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2936 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2936 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2936 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 2936 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
| 2936 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 2936 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4 | jsonlz4 | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
39
DNS requests
79
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2936 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://status.rapidssl.com/ | US | der | 471 b | shared |
2936 | firefox.exe | POST | 200 | 172.217.23.131:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
2936 | firefox.exe | POST | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2936 | firefox.exe | POST | 200 | 172.217.23.131:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
2936 | firefox.exe | POST | 200 | 172.217.23.131:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
2936 | firefox.exe | POST | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2936 | firefox.exe | POST | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2936 | firefox.exe | GET | 200 | 23.55.110.80:80 | http://detectportal.firefox.com/success.txt | US | text | 8 b | whitelisted |
2936 | firefox.exe | POST | 200 | 172.217.23.131:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
2936 | firefox.exe | POST | 200 | 172.217.23.131:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2936 | firefox.exe | 23.55.110.80:80 | detectportal.firefox.com | NTT America, Inc. | US | unknown |
2936 | firefox.exe | 52.11.143.45:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2936 | firefox.exe | 166.78.135.34:443 | www.malware-traffic-analysis.net | Rackspace Ltd. | US | unknown |
2936 | firefox.exe | 52.33.116.145:443 | push.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2936 | firefox.exe | 72.21.91.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2936 | firefox.exe | 52.222.158.80:443 | snippets.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
2936 | firefox.exe | 93.184.220.29:80 | status.rapidssl.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2936 | firefox.exe | 172.217.23.106:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2936 | firefox.exe | 172.217.23.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2936 | firefox.exe | 52.222.158.46:443 | firefox.settings.services.mozilla.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
www.malware-traffic-analysis.net |
| malicious |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
d228z91au11ukj.cloudfront.net |
| whitelisted |
status.rapidssl.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |