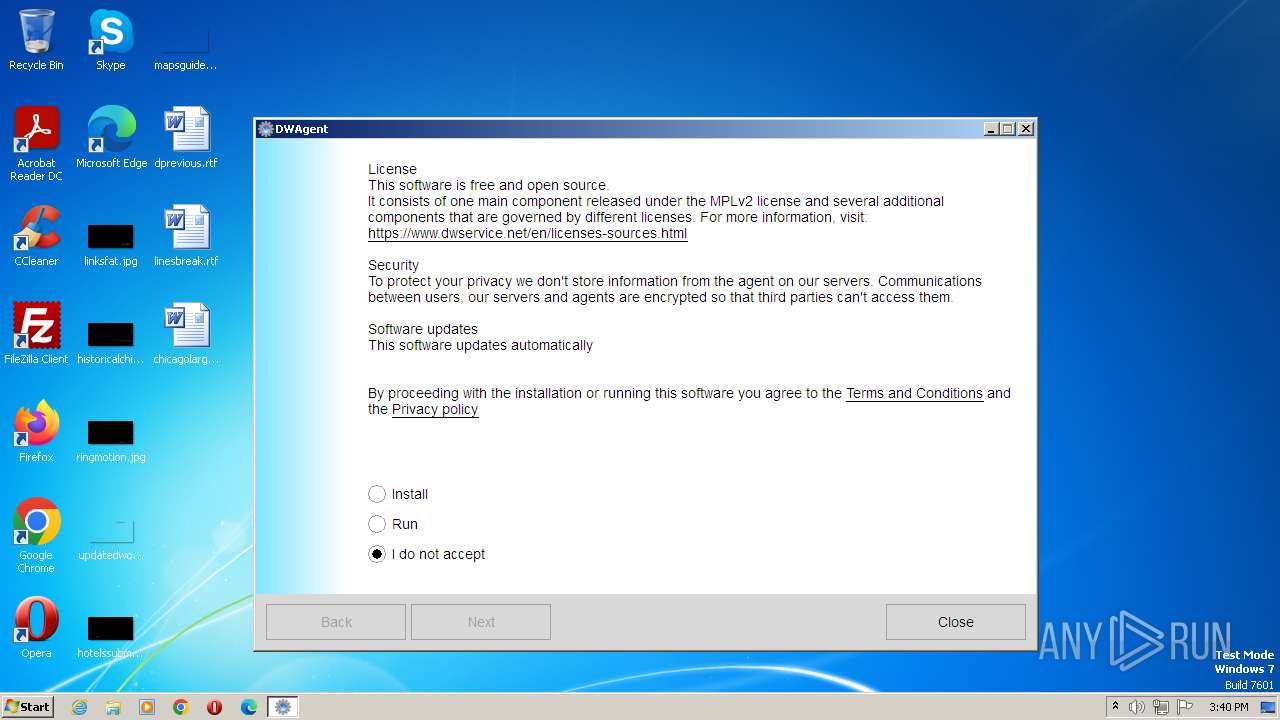
| File name: | dwagent.exe |
| Full analysis: | https://app.any.run/tasks/6f7d75d1-f77c-4d7b-9f7f-161a8c43a8ed |
| Verdict: | Malicious activity |
| Analysis date: | July 27, 2023, 14:39:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | DE9F6A0056655DA1E52BDA92AAC6B584 |
| SHA1: | 03D0CBE3F4BEECF468EE738C0A9B7C47529FDB75 |
| SHA256: | 50350BCE3908539A15A51D661A698E52937348F18FFFBFA525DC8BAA80315220 |
| SSDEEP: | 393216:ItrUgfPqghy78YSBp3fndAY6q5SU4SvdOJ:SFho8nBpPEGSdSi |
MALICIOUS
Loads dropped or rewritten executable
- dwagent.exe (PID: 2596)
Application was dropped or rewritten from another process
- dwagent.exe (PID: 2596)
SUSPICIOUS
Reads the Internet Settings
- dwagent.exe (PID: 1964)
Loads Python modules
- dwagent.exe (PID: 2596)
Executable content was dropped or overwritten
- dwagent.exe (PID: 1964)
INFO
Checks supported languages
- dwagent.exe (PID: 1964)
- dwagent.exe (PID: 2596)
Create files in a temporary directory
- dwagent.exe (PID: 1964)
- dwagent.exe (PID: 2596)
Reads the computer name
- dwagent.exe (PID: 1964)
- dwagent.exe (PID: 2596)
The process checks LSA protection
- dwagent.exe (PID: 1964)
- dwagent.exe (PID: 2596)
Reads the machine GUID from the registry
- dwagent.exe (PID: 2596)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | 1 |
| OSVersion: | 4 |
| EntryPoint: | 0x1490 |
| UninitializedDataSize: | 26624 |
| InitializedDataSize: | 355328 |
| CodeSize: | 291328 |
| LinkerVersion: | 2.3 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit, No debug |
| TimeStamp: | 2021:11:18 12:45:44+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Nov-2021 12:45:44 |
| Detected languages: |
|
| TLS Callbacks: | 2 callback(s) detected. |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 18-Nov-2021 12:45:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000471F8 | 0x00047200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.17403 |
.data | 0x00049000 | 0x000000AC | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.18374 |
.rdata | 0x0004A000 | 0x00004260 | 0x00004400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.49302 |
.bss | 0x0004F000 | 0x00006668 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00056000 | 0x00001484 | 0x00001600 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.07908 |
.CRT | 0x00058000 | 0x00000034 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.282833 |
.tls | 0x00059000 | 0x00000008 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0005A000 | 0x000098AC | 0x00009A00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.54339 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.79673 | 1625 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.07571 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 6.10549 | 872 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.74743 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 6.23414 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.96389 | 3240 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 3.28585 | 1640 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.35345 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 4.94859 | 7336 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 5.55446 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
msvcrt.dll |
Total processes
35
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1964 | "C:\Users\admin\AppData\Local\Temp\dwagent.exe" | C:\Users\admin\AppData\Local\Temp\dwagent.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2596 | "C:\Users\admin\AppData\Local\Temp\dwagent20230727144013\runtime\dwagent.exe" -S -m installer | C:\Users\admin\AppData\Local\Temp\dwagent20230727144013\runtime\dwagent.exe | — | dwagent.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
882
Read events
874
Write events
8
Delete events
0
Modification events
| (PID) Process: | (1964) dwagent.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1964) dwagent.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1964) dwagent.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1964) dwagent.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
43
Suspicious files
170
Text files
65
Unknown types
343
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1964 | dwagent.exe | C:\Users\admin\AppData\Local\Temp\dwagent20230727144013\win.7z | — | |
MD5:— | SHA256:— | |||
| 1964 | dwagent.exe | C:\Users\admin\AppData\Local\Temp\dwagent20230727144013\runtimepy2.7z | — | |
MD5:— | SHA256:— | |||
| 1964 | dwagent.exe | C:\Users\admin\AppData\Local\Temp\dwagent20230727144013\runtimepy3.7z | — | |
MD5:— | SHA256:— | |||
| 1964 | dwagent.exe | C:\Users\admin\AppData\Local\Temp\dwagent20230727144013\detectinfo.py | text | |
MD5:401F48BE24D349632A2438B5EC3B606E | SHA256:184A44033F071547A6077630458303A2729784AB10208ECC95F6F7F59906835F | |||
| 1964 | dwagent.exe | C:\Users\admin\AppData\Local\Temp\dwagent20230727144013\native.py | text | |
MD5:CA4D0231BE63091F5BFA1E25B479C36E | SHA256:FFB87E22348273AA6C4B007837535FAB5AE0BE57AC202DA3752ADF1455F8F07A | |||
| 1964 | dwagent.exe | C:\Users\admin\AppData\Local\Temp\dwagent20230727144013\ipc.py | text | |
MD5:C5D804450DEA060F85CC586990F70AC3 | SHA256:7F5BC8D46F41A874AE5D4975DDC732482413020D498E80AE5465AC4B1C8806AE | |||
| 1964 | dwagent.exe | C:\Users\admin\AppData\Local\Temp\dwagent20230727144013\communication.py | text | |
MD5:ACCA5D712EE28A5677AB6E3C85590D03 | SHA256:4CDC84CFBFA834C611F21A59D424D3019206A7D7CED6D845CDBDA5E0FFABF541 | |||
| 1964 | dwagent.exe | C:\Users\admin\AppData\Local\Temp\dwagent20230727144013\listener.py | text | |
MD5:6209D6BDF53DB8684B95436C4F4812B8 | SHA256:884EC2BD1F2899A33C3DCD214E716074A3C27C3B325D3D197A80BE2D17420F3C | |||
| 1964 | dwagent.exe | C:\Users\admin\AppData\Local\Temp\dwagent20230727144013\LICENSES\ui | text | |
MD5:CFD7D66D2864C38232EC1EF20B27C13A | SHA256:CDE215E5B42363EB28CA2462C4558FF4807B38F383C537624C31E44657AC58F4 | |||
| 1964 | dwagent.exe | C:\Users\admin\AppData\Local\Temp\dwagent20230727144013\ui\images\activities_logo.bmp | image | |
MD5:C96F5BCF310AE61596F5571BF9EDC16F | SHA256:15B89F3DAB535AE859274864511ACEA1163A12C7AB1D6D7E9EB6008993AF31B3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2720 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |