| File name: | Microsoft Visual C++ 2013.exe |
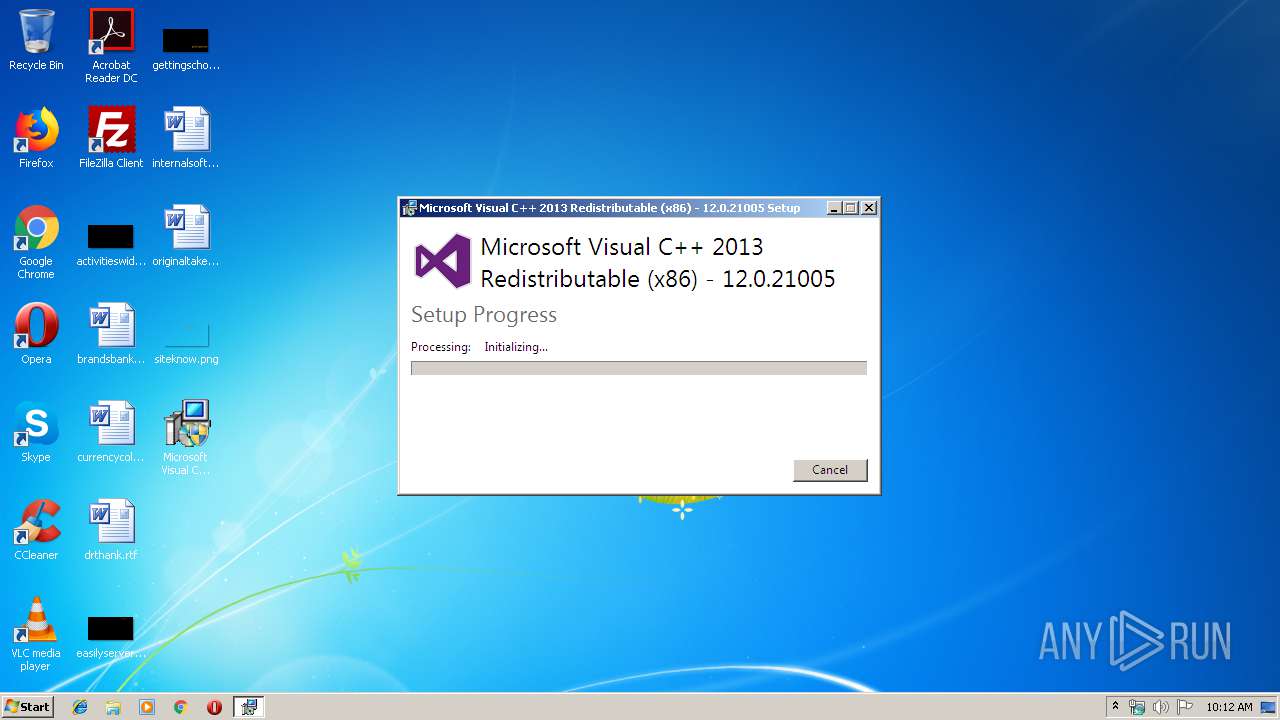
| Full analysis: | https://app.any.run/tasks/9d8396c3-bdb4-4d45-8ab4-edb821ff8f3d |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2019, 09:12:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 4F1ADCA105186D04B4613A41381C8701 |
| SHA1: | BD24D540BC17629A0C0A260F4E4F1EFA7A005E17 |
| SHA256: | 502EBDDD0FBF15696E7AA4E7D55D7308C5FF8E318F9A23DBD3C617868DFA3DE5 |
| SSDEEP: | 196608:r/LRDnuBotjJh2emr8L/YIsG7MOgqHG64O:rzRDOotj+eBLJ7XFH |
MALICIOUS
Loads dropped or rewritten executable
- Microsoft Visual C++ 2013.exe (PID: 1140)
- ASMicrosoft Visual C++ 2013.exe (PID: 3116)
Application was dropped or rewritten from another process
- ASMicrosoft Visual C++ 2013.exe (PID: 2244)
- ASMicrosoft Visual C++ 2013.exe (PID: 3116)
Changes the autorun value in the registry
- ASMicrosoft Visual C++ 2013.exe (PID: 2244)
SUSPICIOUS
Searches for installed software
- ASMicrosoft Visual C++ 2013.exe (PID: 3116)
- ASMicrosoft Visual C++ 2013.exe (PID: 2244)
Executable content was dropped or overwritten
- Microsoft Visual C++ 2013.exe (PID: 1140)
- ASMicrosoft Visual C++ 2013.exe (PID: 3116)
- ASMicrosoft Visual C++ 2013.exe (PID: 2244)
Application launched itself
- ASMicrosoft Visual C++ 2013.exe (PID: 2244)
Executed via COM
- DrvInst.exe (PID: 3940)
Executed as Windows Service
- vssvc.exe (PID: 3172)
Creates files in the program directory
- ASMicrosoft Visual C++ 2013.exe (PID: 2244)
Creates a software uninstall entry
- ASMicrosoft Visual C++ 2013.exe (PID: 2244)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 3172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (93.4) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .scr | | | Windows screen saver (1.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:52+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 164864 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30fa |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:52 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005C4C | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44011 |
.rdata | 0x00007000 | 0x0000129C | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04684 |
.data | 0x00009000 | 0x00025C58 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.801 |
.ndata | 0x0002F000 | 0x00008000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00037000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.88133 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.27817 | 2216 | UNKNOWN | English - United States | RT_ICON |
103 | 1.81924 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
42
Monitored processes
6
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1140 | "C:\Users\admin\Desktop\Microsoft Visual C++ 2013.exe" | C:\Users\admin\Desktop\Microsoft Visual C++ 2013.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
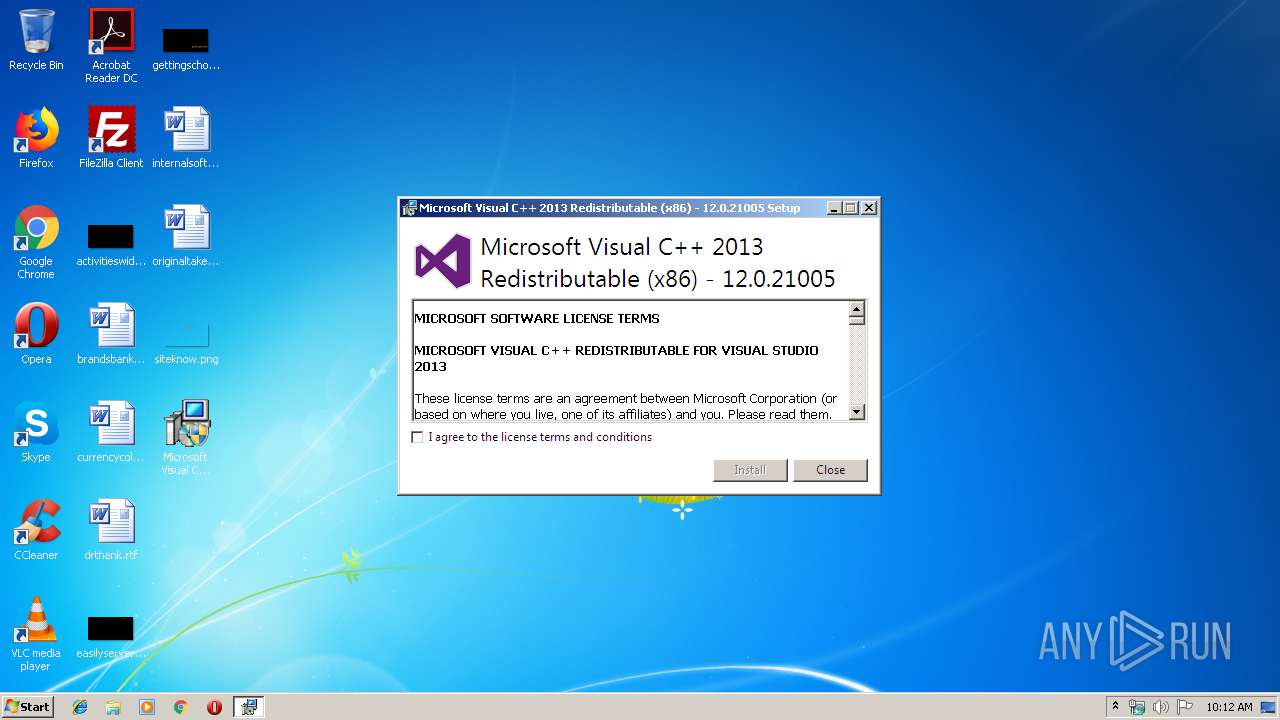
| 2244 | "C:\Users\admin\AppData\Local\Temp\Install\ASMicrosoft Visual C++ 2013.exe" | C:\Users\admin\AppData\Local\Temp\Install\ASMicrosoft Visual C++ 2013.exe | Microsoft Visual C++ 2013.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2013 Redistributable (x86) - 12.0.21005 Exit code: 0 Version: 12.0.21005.1 Modules
| |||||||||||||||
| 3116 | "C:\Users\admin\AppData\Local\Temp\Install\ASMicrosoft Visual C++ 2013.exe" -burn.unelevated BurnPipe.{8E6500EE-ED84-4657-9B3A-922DEA7B1B01} {A9F18C00-FD81-4F60-BF17-CC67C1ACFF76} 2244 | C:\Users\admin\AppData\Local\Temp\Install\ASMicrosoft Visual C++ 2013.exe | ASMicrosoft Visual C++ 2013.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2013 Redistributable (x86) - 12.0.21005 Exit code: 0 Version: 12.0.21005.1 Modules
| |||||||||||||||
| 3172 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3828 | "C:\Users\admin\Desktop\Microsoft Visual C++ 2013.exe" | C:\Users\admin\Desktop\Microsoft Visual C++ 2013.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3940 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot22" "" "" "695c3f483" "00000000" "000005BC" "000005C4" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
370
Read events
190
Write events
179
Delete events
1
Modification events
| (PID) Process: | (1140) Microsoft Visual C++ 2013.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1140) Microsoft Visual C++ 2013.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2244) ASMicrosoft Visual C++ 2013.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000000CB0CE2F6F77D501C4080000C8080000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2244) ASMicrosoft Visual C++ 2013.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000000CB0CE2F6F77D501C4080000C8080000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2244) ASMicrosoft Visual C++ 2013.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 24 | |||
| (PID) Process: | (2244) ASMicrosoft Visual C++ 2013.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000005A2222306F77D501C4080000C8080000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2244) ASMicrosoft Visual C++ 2013.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000B48424306F77D501C4080000380E0000E803000001000000000000000000000001B9B322CDE81F4597F89461BB8857AF0000000000000000 | |||
| (PID) Process: | (3172) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000001C0E2E306F77D501640C00009C0E0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3172) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000001C0E2E306F77D501640C0000940E0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3172) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000001C0E2E306F77D501640C00004C0B0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
5
Suspicious files
4
Text files
67
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2244 | ASMicrosoft Visual C++ 2013.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3172 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 1140 | Microsoft Visual C++ 2013.exe | C:\Users\admin\AppData\Local\Temp\~DF855AE806E6134321.TMP | — | |
MD5:— | SHA256:— | |||
| 2244 | ASMicrosoft Visual C++ 2013.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
| 1140 | Microsoft Visual C++ 2013.exe | C:\Users\admin\AppData\Local\Temp\Splash.jpg | image | |
MD5:— | SHA256:— | |||
| 3116 | ASMicrosoft Visual C++ 2013.exe | C:\Users\admin\AppData\Local\Temp\{ce085a78-074e-4823-8dc1-8a721b94b76d}\.ba1\logo.png | image | |
MD5:D6BD210F227442B3362493D046CEA233 | SHA256:335A256D4779EC5DCF283D007FB56FD8211BBCAF47DCD70FE60DED6A112744EF | |||
| 1140 | Microsoft Visual C++ 2013.exe | C:\Users\admin\AppData\Local\Temp\nsv4F28.tmp\newadvsplash.dll | executable | |
MD5:7EE14DFF57FB6E6C644B318D16768F4C | SHA256:53377D0710F551182EDBAB4150935425948535D11B92BF08A1C2DCF989723BD7 | |||
| 3116 | ASMicrosoft Visual C++ 2013.exe | C:\Users\admin\AppData\Local\Temp\{ce085a78-074e-4823-8dc1-8a721b94b76d}\.ba1\license.rtf | text | |
MD5:1E47EE7B71B22488068343DF4CE30534 | SHA256:8518F0420972C1DBE8A323FFC6F57863AF0B80C6A3B27FD0C6FC9BDABB7E2D13 | |||
| 3116 | ASMicrosoft Visual C++ 2013.exe | C:\Users\admin\AppData\Local\Temp\{ce085a78-074e-4823-8dc1-8a721b94b76d}\.ba1\thm.xml | xml | |
MD5:0056F10A42638EA8B4BEFC614741DDD6 | SHA256:6B1BA0DEA830E556A58C883290FAA5D49C064E546CBFCD0451596A10CC693F87 | |||
| 2244 | ASMicrosoft Visual C++ 2013.exe | C:\ProgramData\Package Cache\{ce085a78-074e-4823-8dc1-8a721b94b76d}\state.rsm | smt | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report