| File name: | 502ea40b18677aae31abd50b9c645760a204c4a92b661541631fe6e215df88bf.bat |
| Full analysis: | https://app.any.run/tasks/6dd327ba-6e42-4834-82fc-e8d23bb914d8 |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 10:19:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with CRLF line terminators |
| MD5: | 4DEB12AA307D26A2B941F1688D9E89CE |
| SHA1: | A08B98377D441CF93DA444244B9664292456024E |
| SHA256: | 502EA40B18677AAE31ABD50B9C645760A204C4A92B661541631FE6E215DF88BF |
| SSDEEP: | 96:ODu18Rs02/MYb6vGq9D3858hioVdrEFvZX13Xw1LHLwp5ehLUs:k6/CIG932ZXRwZ |
MALICIOUS
Executing a file with an untrusted certificate
- curl.exe (PID: 2656)
- curl.exe (PID: 2988)
- curl.exe (PID: 3160)
- curl.exe (PID: 3824)
- curl.exe (PID: 2464)
- curl.exe (PID: 3816)
- curl.exe (PID: 3112)
- curl.exe (PID: 4044)
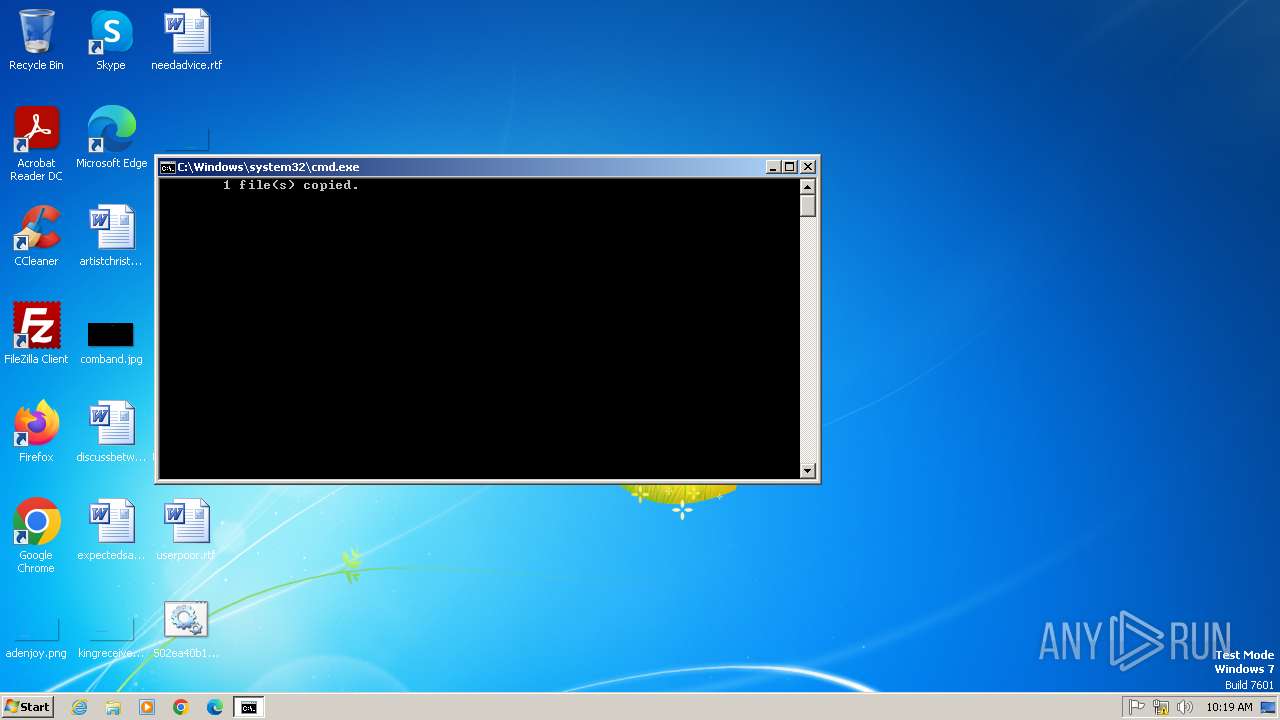
Create files in the Startup directory
- cmd.exe (PID: 2840)
Changes the autorun value in the registry
- reg.exe (PID: 2516)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 2840)
Starts NET.EXE for service management
- net.exe (PID: 2788)
- cmd.exe (PID: 2840)
Antivirus name has been found in the command line (generic signature)
- taskkill.exe (PID: 2888)
Uses TASKKILL.EXE to kill antiviruses
- cmd.exe (PID: 2840)
SUSPICIOUS
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2840)
Application launched itself
- cmd.exe (PID: 2840)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2840)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1484)
- cmd.exe (PID: 2916)
- cmd.exe (PID: 268)
- cmd.exe (PID: 328)
- cmd.exe (PID: 3688)
- cmd.exe (PID: 2764)
- cmd.exe (PID: 3212)
- cmd.exe (PID: 4080)
- cmd.exe (PID: 2616)
- cmd.exe (PID: 2840)
Likely accesses (executes) a file from the Public directory
- attrib.exe (PID: 3104)
- cmd.exe (PID: 2916)
- powershell.exe (PID: 2016)
Executing commands from a ".bat" file
- cmd.exe (PID: 2840)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 1324)
- powershell.exe (PID: 1784)
- powershell.exe (PID: 2016)
- powershell.exe (PID: 2432)
- powershell.exe (PID: 2860)
- powershell.exe (PID: 2728)
- powershell.exe (PID: 3752)
- powershell.exe (PID: 2808)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2840)
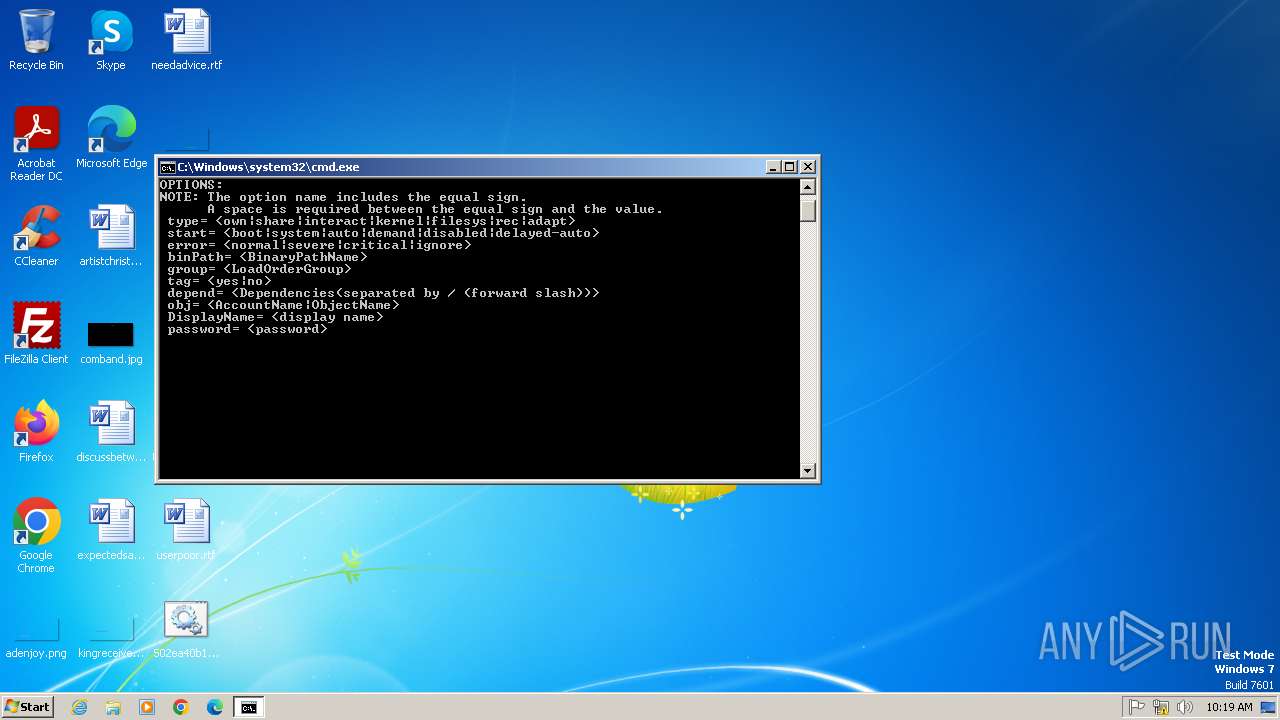
Windows service management via SC.EXE
- sc.exe (PID: 3232)
Starts SC.EXE for service management
- cmd.exe (PID: 2840)
Get information on the list of running processes
- cmd.exe (PID: 4080)
- cmd.exe (PID: 2840)
Uses WMIC.EXE to obtain physical disk drive information
- cmd.exe (PID: 2044)
Uses WMIC.EXE to obtain BIOS management information
- cmd.exe (PID: 4020)
Reads the Internet Settings
- WMIC.exe (PID: 4032)
- WMIC.exe (PID: 2876)
INFO
Checks supported languages
- curl.exe (PID: 2656)
- curl.exe (PID: 2988)
- curl.exe (PID: 3160)
- curl.exe (PID: 2464)
- curl.exe (PID: 3824)
- curl.exe (PID: 3816)
- curl.exe (PID: 3112)
- curl.exe (PID: 4044)
Autorun file from Startup directory
- cmd.exe (PID: 2840)
Execution of CURL command
- cmd.exe (PID: 2840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
79
Monitored processes
44
Malicious processes
1
Suspicious processes
9
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 268 | C:\Windows\system32\cmd.exe /c powershell -command "[Convert]::ToBase64String([Text.Encoding]::UTF8.GetBytes('Setup: C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\rtt.bat'))" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 328 | C:\Windows\system32\cmd.exe /c powershell -command "[Convert]::ToBase64String([Text.Encoding]::UTF8.GetBytes('Registry: Software\Microsoft\Windows\CurrentVersion\Run\RTT1'))" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1324 | powershell -command "[Convert]::ToBase64String([Text.Encoding]::UTF8.GetBytes('Setup: C:\Users\admin\AppData\Roaming\rtt.bat'))" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1460 | attrib +h +s "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\rtt.bat" | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1484 | C:\Windows\system32\cmd.exe /c powershell -command "[Convert]::ToBase64String([Text.Encoding]::UTF8.GetBytes('Setup: C:\Users\admin\AppData\Roaming\rtt.bat'))" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1784 | powershell -command "[Convert]::ToBase64String([Text.Encoding]::UTF8.GetBytes('Setup: C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\rtt.bat'))" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2016 | powershell -command "[Convert]::ToBase64String([Text.Encoding]::UTF8.GetBytes('Setup: C:\Users\Public\rtt_1193425260.bat'))" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2044 | C:\Windows\system32\cmd.exe /c wmic diskdrive get model | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2068 | powershell -command "(Get-Process | Where-Object {$_.Path -like '*vbox*'}).Count" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2360 | attrib +h +s "C:\Users\admin\AppData\Roaming\rtt.bat" | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
11 634
Read events
11 632
Write events
2
Delete events
0
Modification events
| (PID) Process: | (2516) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | RTT1 |
Value: C:\Users\admin\AppData\Roaming\rtt.bat | |||
| (PID) Process: | (2420) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\StartupApproved\Run |
| Operation: | write | Name: | RTT2 |
Value: C:\Users\admin\AppData\Roaming\rtt.bat | |||
Executable files
0
Suspicious files
21
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2728 | powershell.exe | C:\Users\admin\AppData\Local\Temp\kktu2ccw.him.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2840 | cmd.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\rtt.bat | text | |
MD5:4DEB12AA307D26A2B941F1688D9E89CE | SHA256:502EA40B18677AAE31ABD50B9C645760A204C4A92B661541631FE6E215DF88BF | |||
| 2432 | powershell.exe | C:\Users\admin\AppData\Local\Temp\2ggigfxs.5av.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1784 | powershell.exe | C:\Users\admin\AppData\Local\Temp\rqfoaiao.owc.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2016 | powershell.exe | C:\Users\admin\AppData\Local\Temp\vrqoqdoc.pla.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3752 | powershell.exe | C:\Users\admin\AppData\Local\Temp\o31mecsy.xvc.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2840 | cmd.exe | C:\Users\Public\rtt_1193425260.bat | text | |
MD5:4DEB12AA307D26A2B941F1688D9E89CE | SHA256:502EA40B18677AAE31ABD50B9C645760A204C4A92B661541631FE6E215DF88BF | |||
| 2432 | powershell.exe | C:\Users\admin\AppData\Local\Temp\izztftlo.zqk.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2860 | powershell.exe | C:\Users\admin\AppData\Local\Temp\215o1wm3.k4c.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1324 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |