| File name: | b01bd6db1fc0e7276cc38647d147a9b6 |
| Full analysis: | https://app.any.run/tasks/35d88af1-7f37-4064-9a35-9d0c0669173b |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 04:22:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, unknown character set |
| MD5: | B01BD6DB1FC0E7276CC38647D147A9B6 |
| SHA1: | 24C9B94FDA8C6B5D8026083FB0178ABFEF6FAAD6 |
| SHA256: | 50160B68A3545070CA6BBD6CC900F70CA34278965CC8E4F140A5C52843481F60 |
| SSDEEP: | 3072:qfuZK0lDZK0laZK0lpZK0lXZK0l7ZK0lIZK0l6ZK0lrZK0l6ZK0lqZK0l6ZK0lmD:O+0+5+G+4+s+7+Z+8+Z+p+Z+F+R+by9 |
MALICIOUS
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 3336)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 300)
- cmd.exe (PID: 2948)
- cmd.exe (PID: 2932)
- cmd.exe (PID: 2868)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 3336)
SUSPICIOUS
Executed via COM
- EXCEL.EXE (PID: 3336)
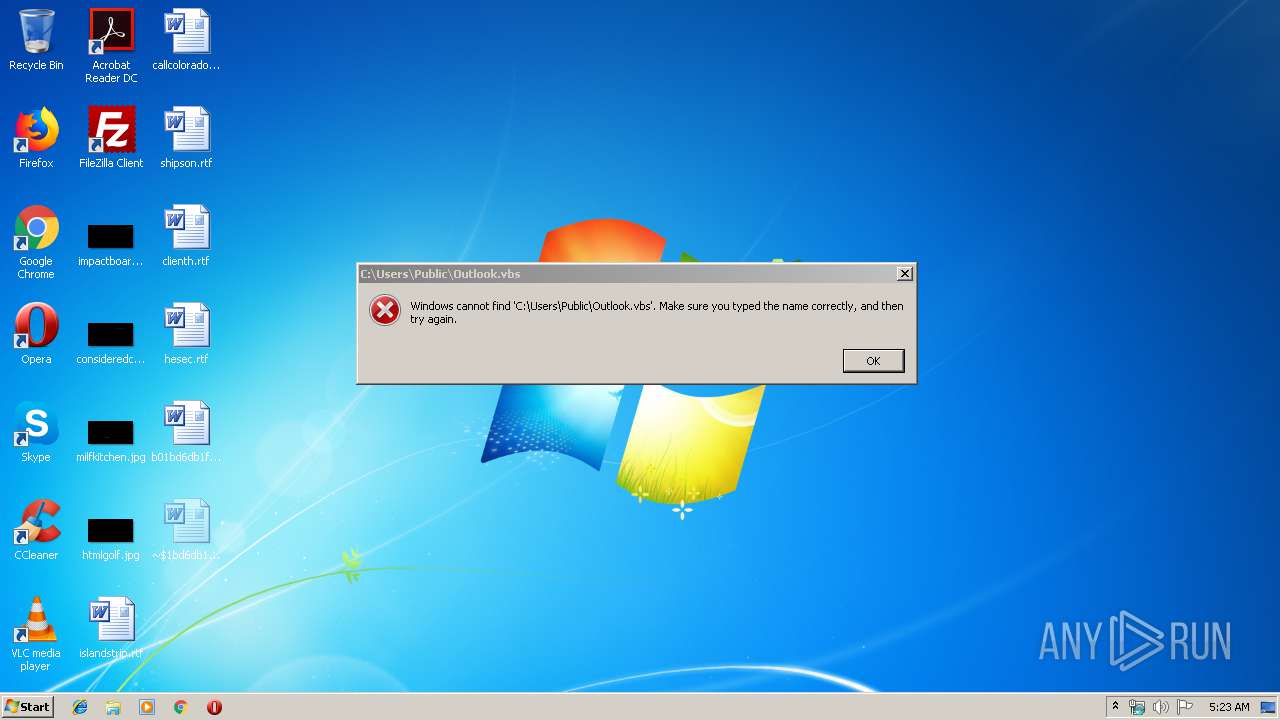
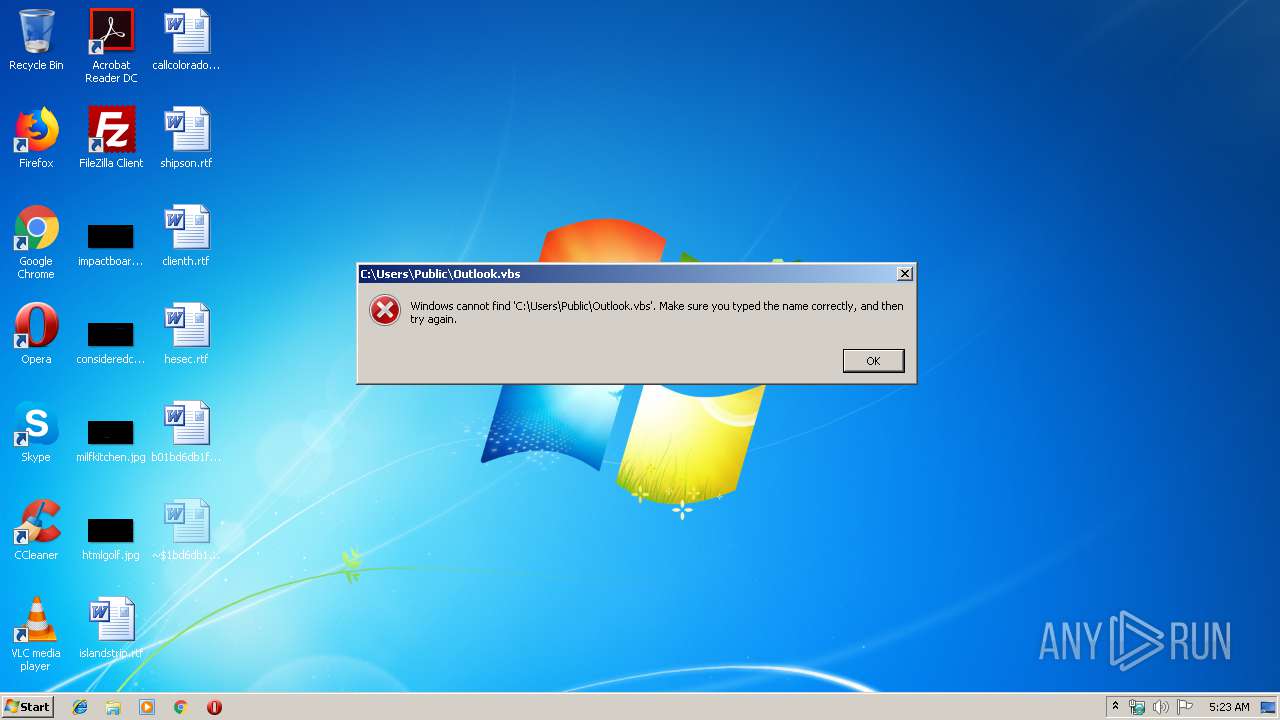
Uses TASKKILL.EXE to kill Office Apps
- cmd.exe (PID: 2772)
- cmd.exe (PID: 3168)
- cmd.exe (PID: 3784)
- cmd.exe (PID: 2972)
Application launched itself
- cmd.exe (PID: 2772)
- cmd.exe (PID: 3168)
- cmd.exe (PID: 2972)
- cmd.exe (PID: 3784)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2972)
- cmd.exe (PID: 3784)
- cmd.exe (PID: 2772)
- cmd.exe (PID: 3168)
INFO
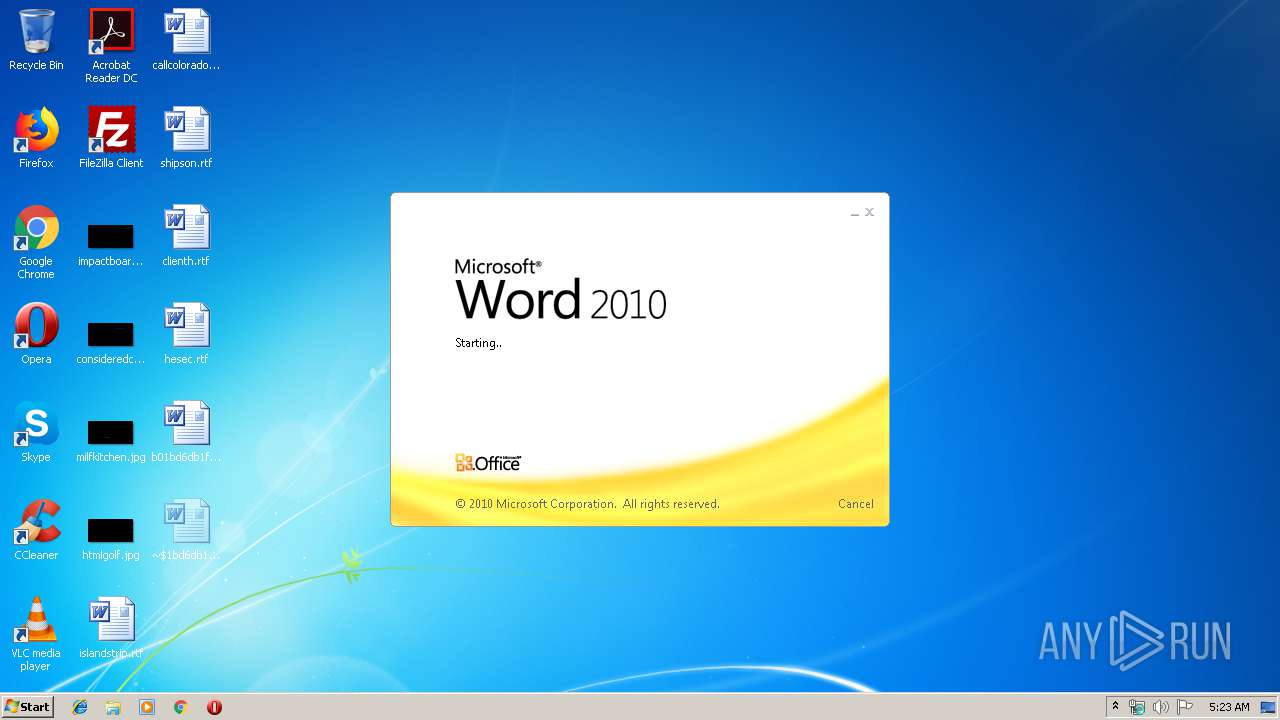
Creates files in the user directory
- WINWORD.EXE (PID: 3568)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3568)
- EXCEL.EXE (PID: 3336)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
EXIF
RTF
| Author: | Karla |
|---|---|
| LastModifiedBy: | Karla |
| CreateDate: | 2019:07:09 10:17:00 |
| ModifyDate: | 2019:07:09 10:19:00 |
| RevisionNumber: | 1 |
| TotalEditTime: | 2 minutes |
| Pages: | 1 |
| Words: | 85 |
| Characters: | 462 |
| CharactersWithSpaces: | 546 |
| InternalVersionNumber: | 57433 |
Total processes
55
Monitored processes
18
Malicious processes
1
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | cmd.exe /c ping 127.0.0.1 -n 5 | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 700 | ping 127.0.0.1 -n 5 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 972 | taskkill /f /im winword.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1476 | taskkill /f /im winword.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1748 | ping 127.0.0.1 -n 5 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1816 | ping 127.0.0.1 -n 5 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
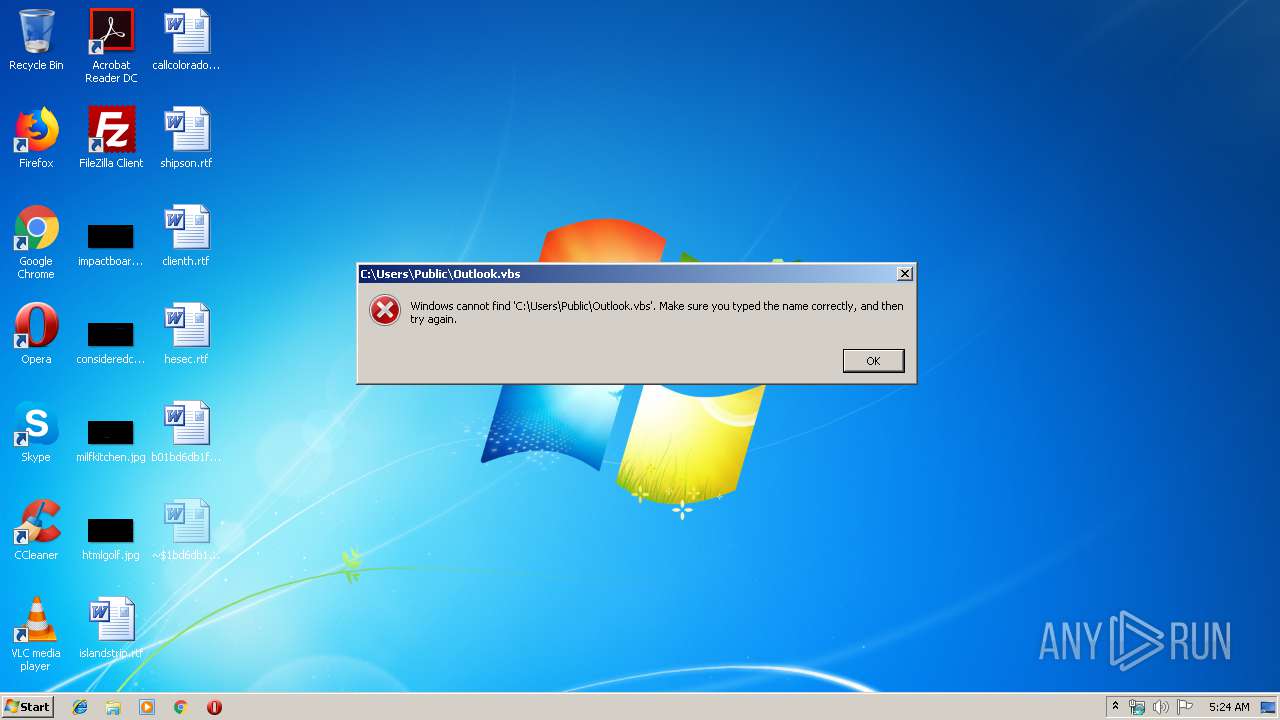
| 2772 | "C:\Windows\System32\cmd.exe" /c cd "%CDT%\" & taskkill /f /im winword.exe & cmd.exe /c ping 127.0.0.1 -n 5 > nul & start C:\Users\Public\Outlook.vbs | C:\Windows\System32\cmd.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2868 | cmd.exe /c ping 127.0.0.1 -n 5 | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2932 | cmd.exe /c ping 127.0.0.1 -n 5 | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2948 | cmd.exe /c ping 127.0.0.1 -n 5 | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
559
Read events
519
Write events
36
Delete events
4
Modification events
| (PID) Process: | (3568) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ~m& |
Value: 7E6D2600F00D0000010000000000000000000000 | |||
| (PID) Process: | (3568) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3568) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3568) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1324482590 | |||
| (PID) Process: | (3568) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1324482704 | |||
| (PID) Process: | (3568) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1324482705 | |||
| (PID) Process: | (3568) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: F00D00005E2E8E83203DD50100000000 | |||
| (PID) Process: | (3568) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | -p& |
Value: 2D702600F00D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3568) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | -p& |
Value: 2D702600F00D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3568) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3568 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRD5DE.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3336 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRDFC1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3568 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3336 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\SystemCertificates\My\Certificates\E02357FC7708441D4B0BE5F371F4B28961870F70 | binary | |
MD5:— | SHA256:— | |||
| 3568 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{755A8195-351C-47B9-A791-F40C76263E6E}.tmp | binary | |
MD5:— | SHA256:— | |||
| 3568 | WINWORD.EXE | C:\Users\admin\Desktop\~$1bd6db1fc0e7276cc38647d147a9b6.rtf | pgc | |
MD5:— | SHA256:— | |||
| 3568 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{C44EFD22-0F32-40D9-9A34-58DC735D8FD1}.tmp | smt | |
MD5:5D4D94EE7E06BBB0AF9584119797B23A | SHA256:4826C0D860AF884D3343CA6460B0006A7A2CE7DBCCC4D743208585D997CC5FD1 | |||
| 3568 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\DCB1E0DC.emf | emf | |
MD5:D2F4DCA5A3F6A962C07D9F02B1FC3B46 | SHA256:7213805F4C566EA9F382050E9AB2FB0D2A7BFCE2FBD43F6A055E692325076F27 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3336 | EXCEL.EXE | GET | 200 | 104.20.208.21:443 | https://pastebin.com/raw/5cYnj5vL | US | text | 4.21 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3336 | EXCEL.EXE | 104.20.208.21:443 | pastebin.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |