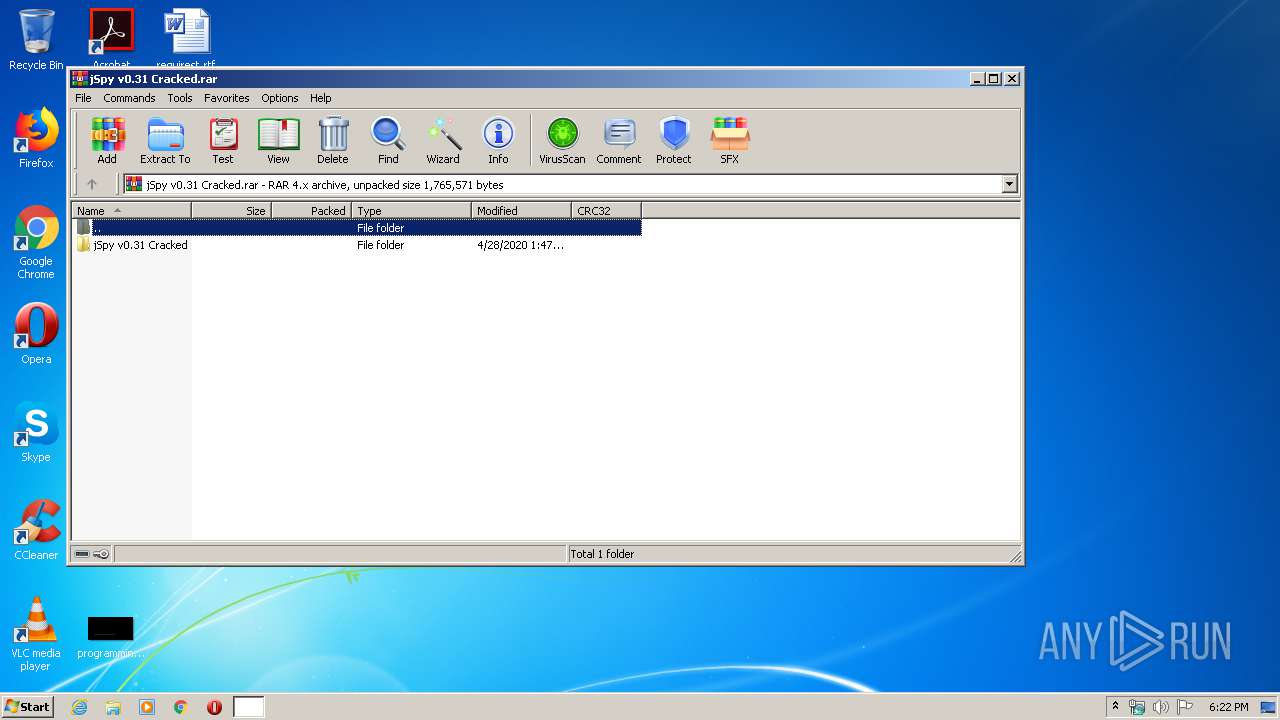
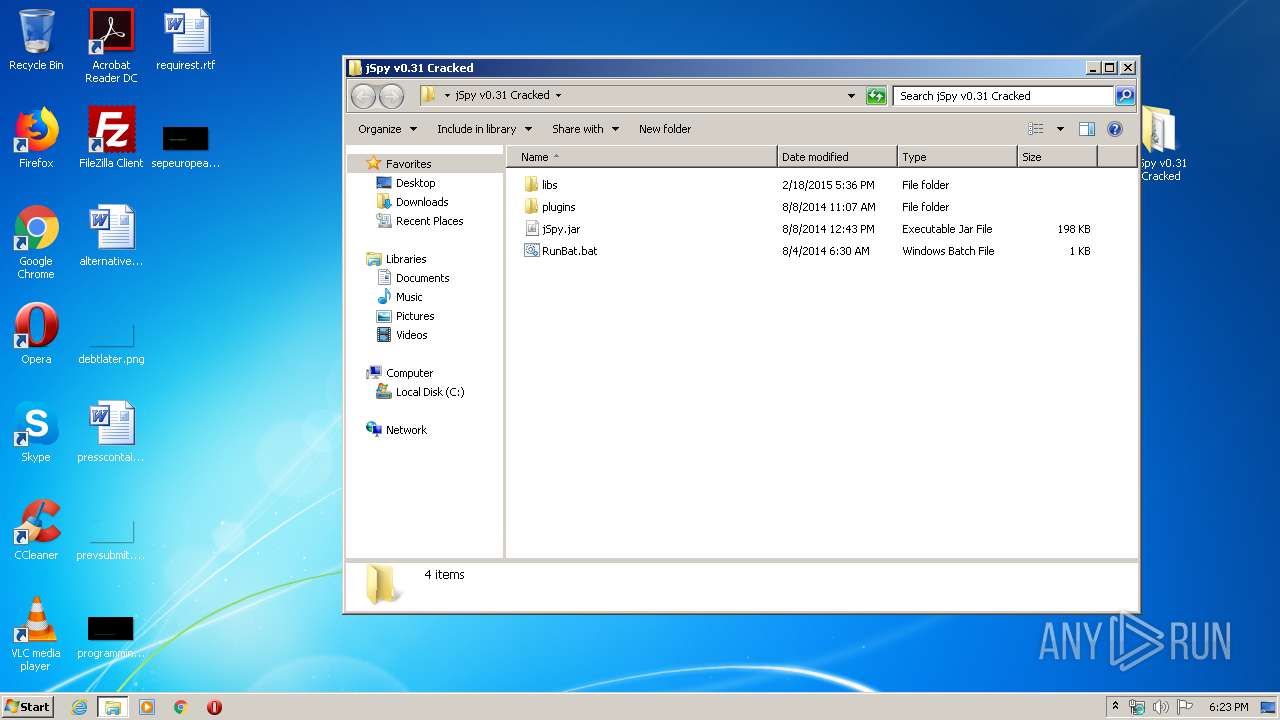
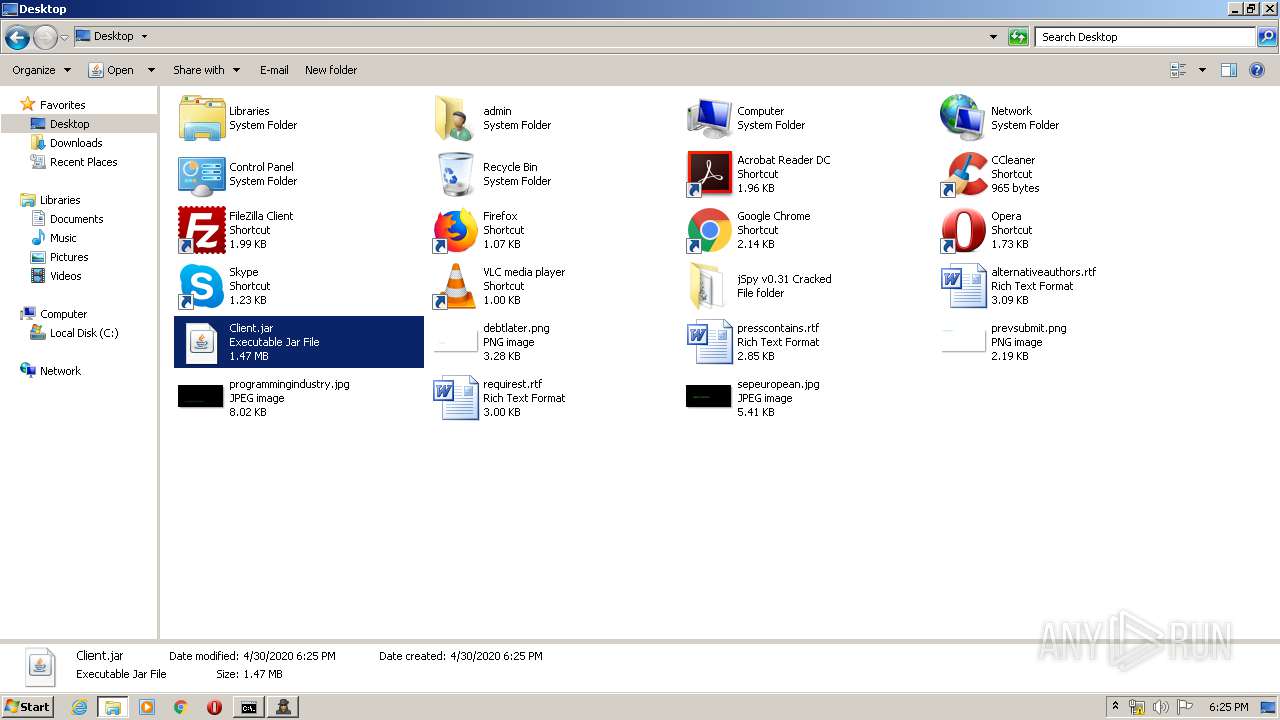
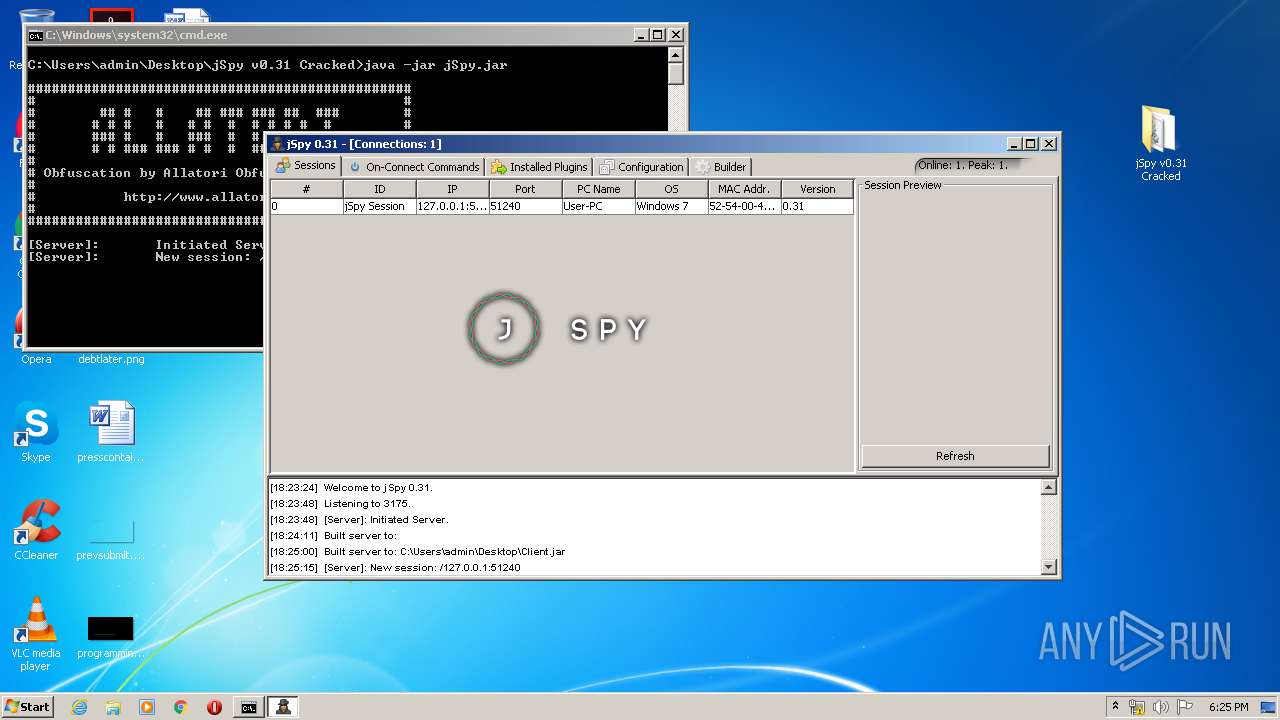
| File name: | jSpy v0.31 Cracked.rar |
| Full analysis: | https://app.any.run/tasks/a2b43b59-d406-42b7-99d2-94f07e42882a |
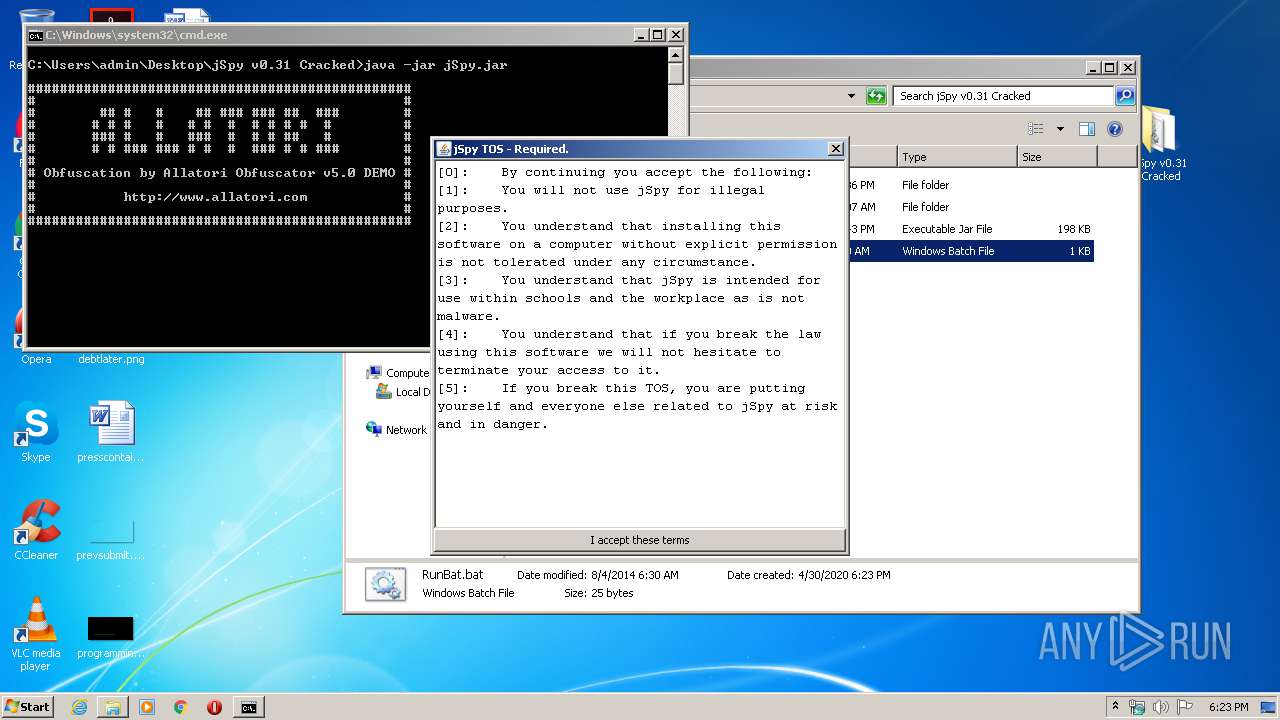
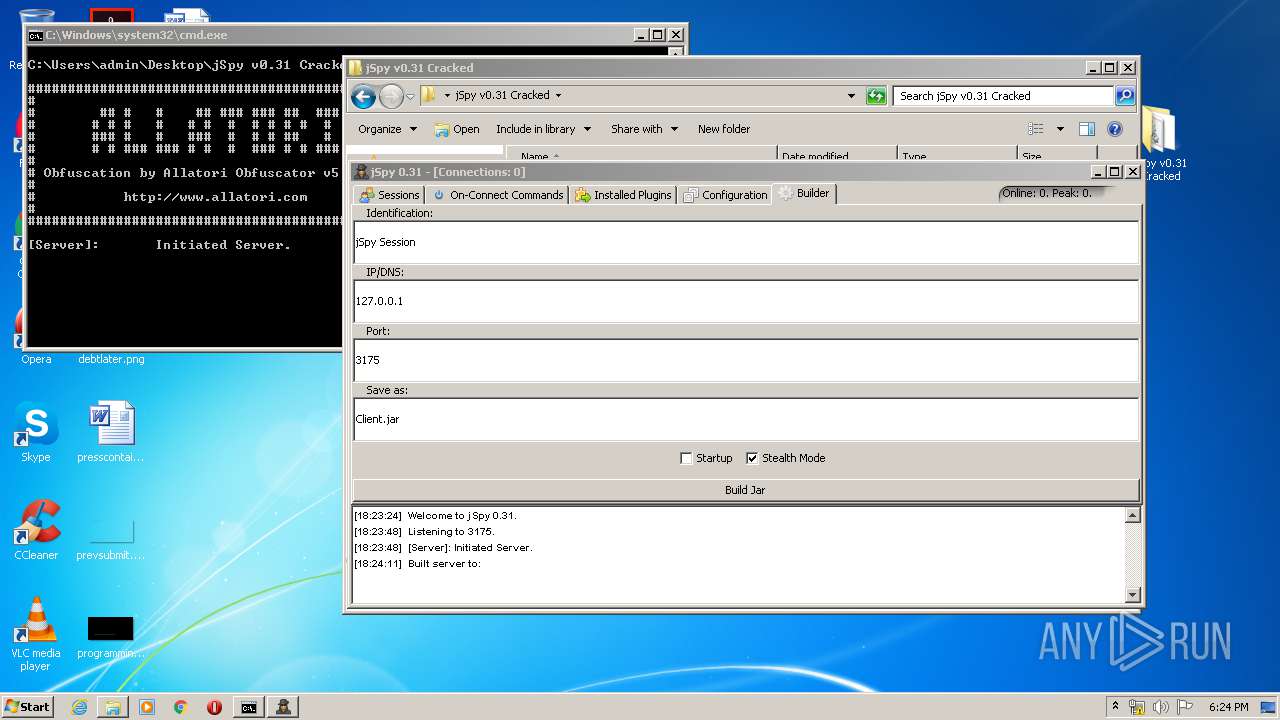
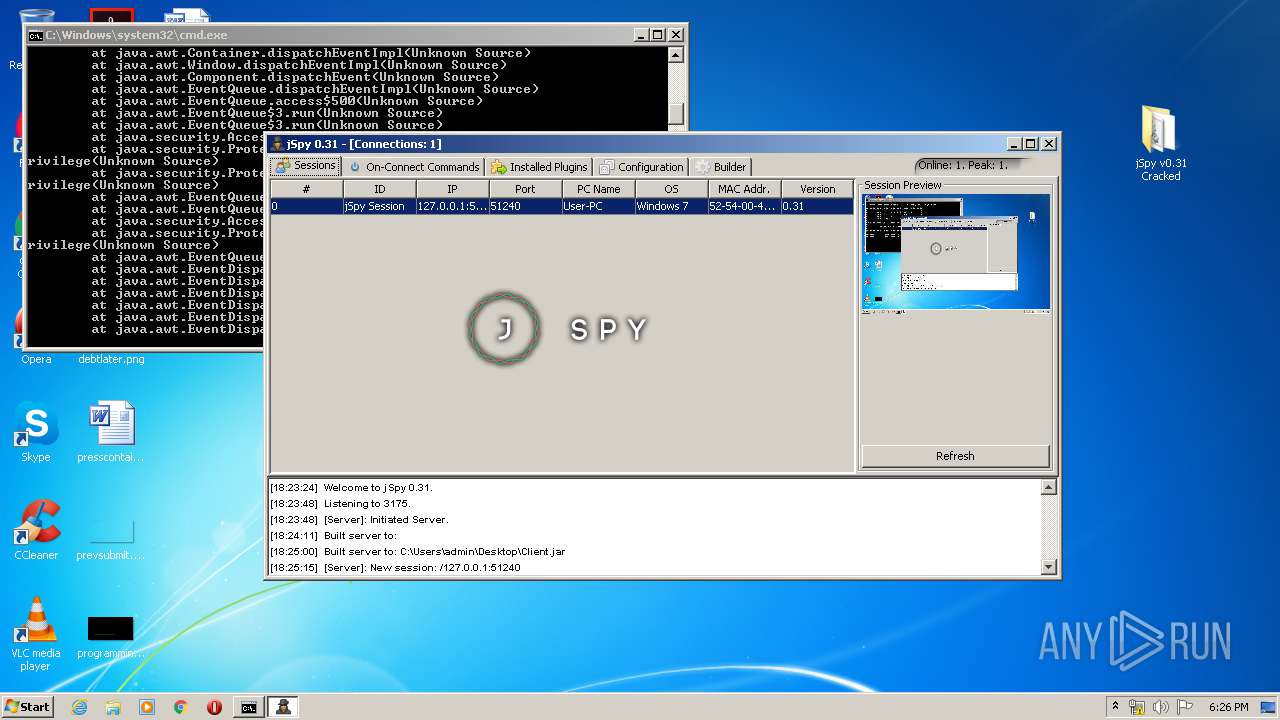
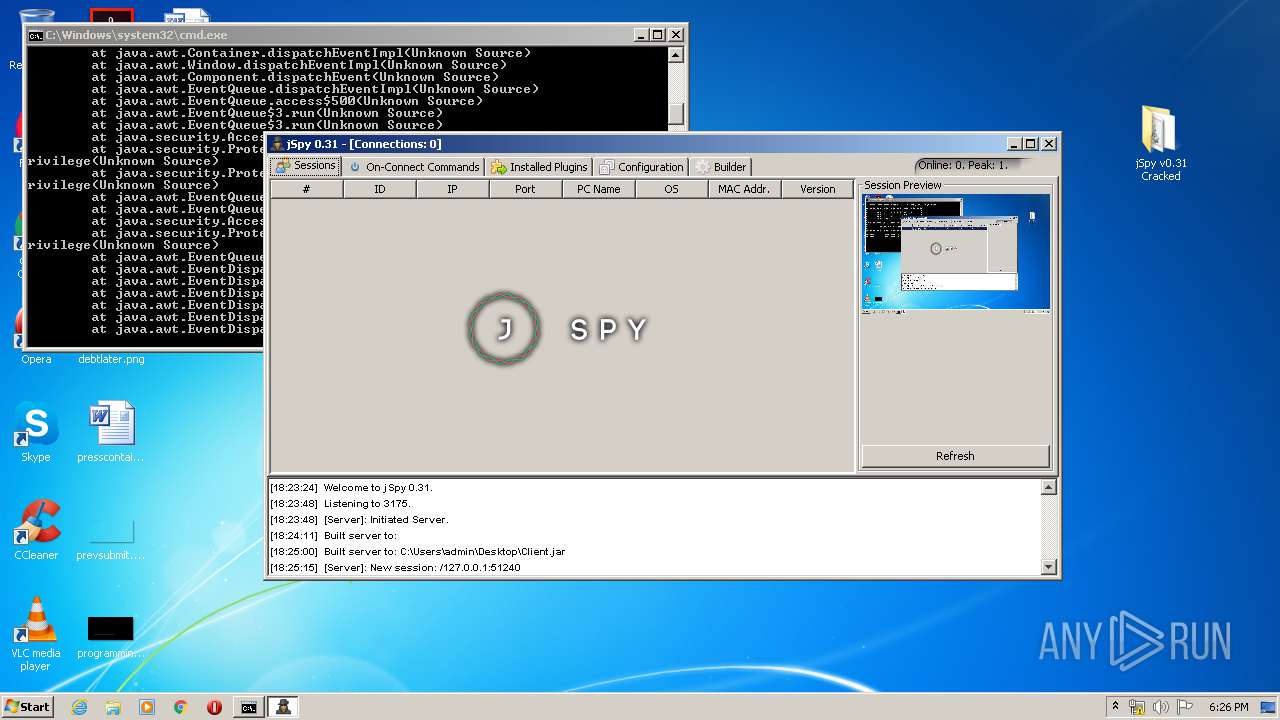
| Verdict: | Malicious activity |
| Analysis date: | April 30, 2020, 17:22:41 |
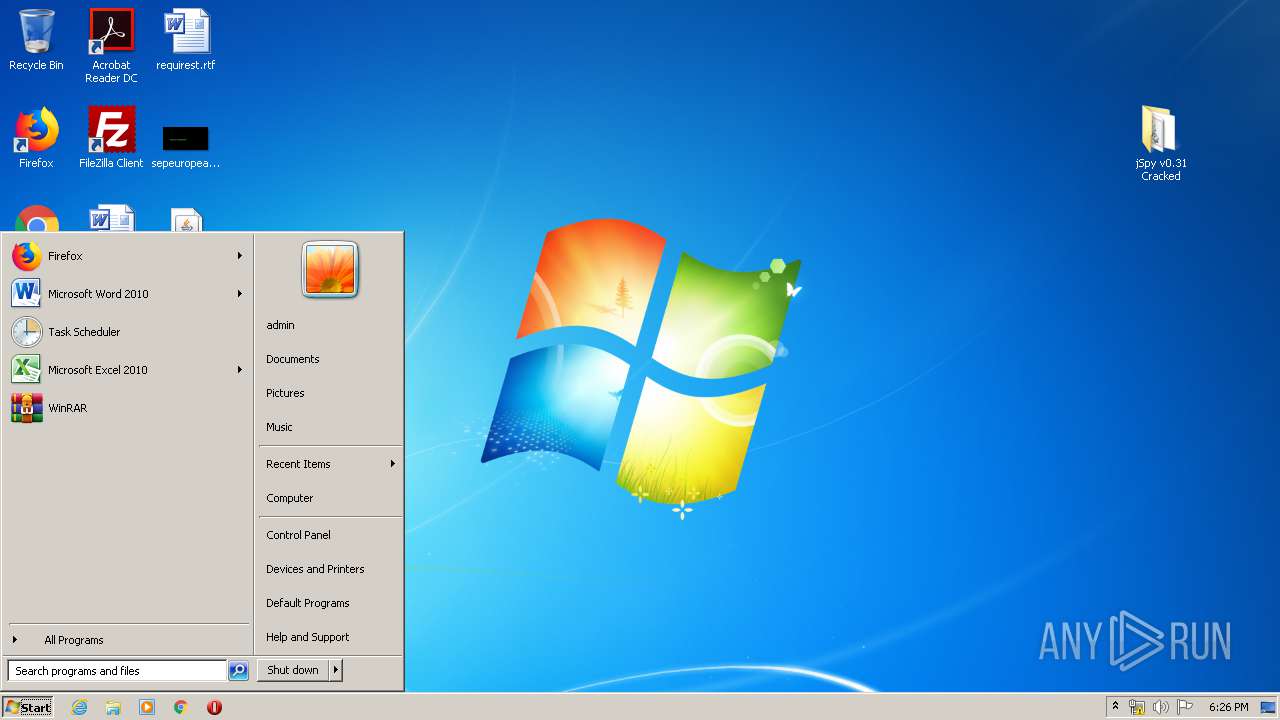
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 7B4E5DA617AC1E61566A7F48E8504E5D |
| SHA1: | 2A371BB28BCE13DEB56EE4684EFE397B01FEC836 |
| SHA256: | 500E5CA4E4609016CEB1191B2EB55DAFBB1F1F6A6272395C6603A52589D96141 |
| SSDEEP: | 49152:2IF/j3liSRrG4a53sknXynmVokTBBLePTz:2CRizv5nCmVok3o3 |
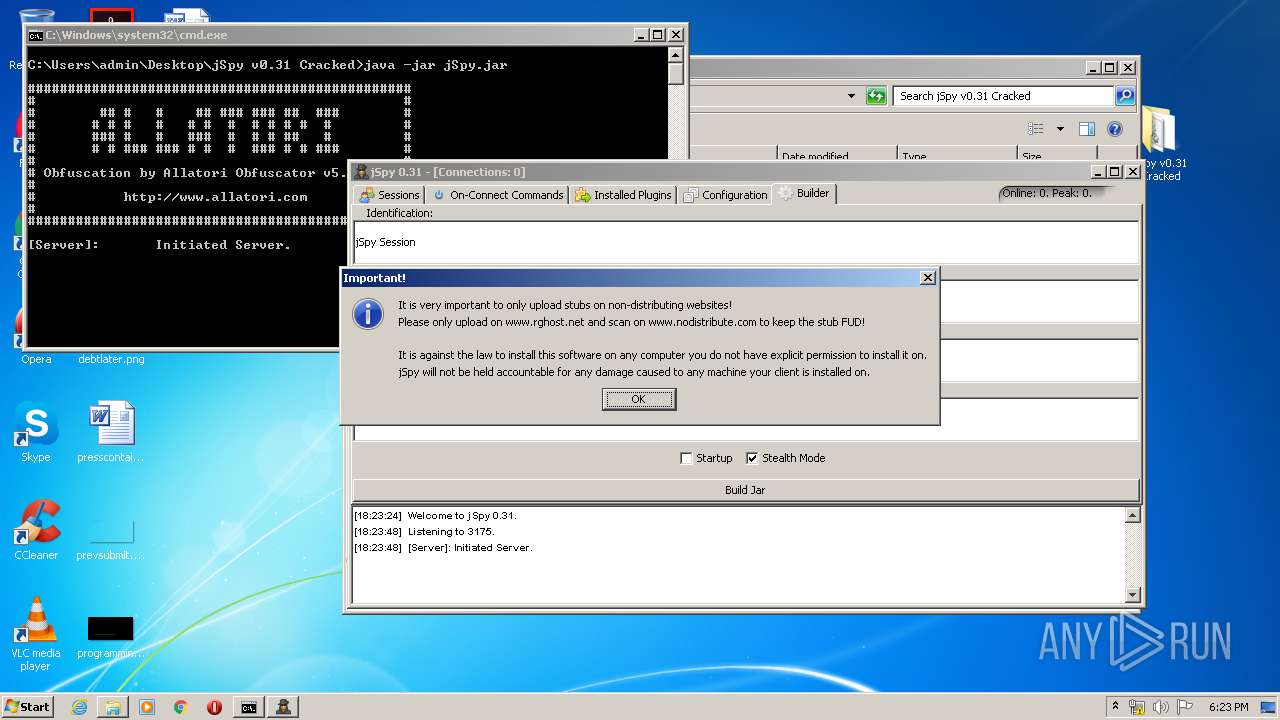
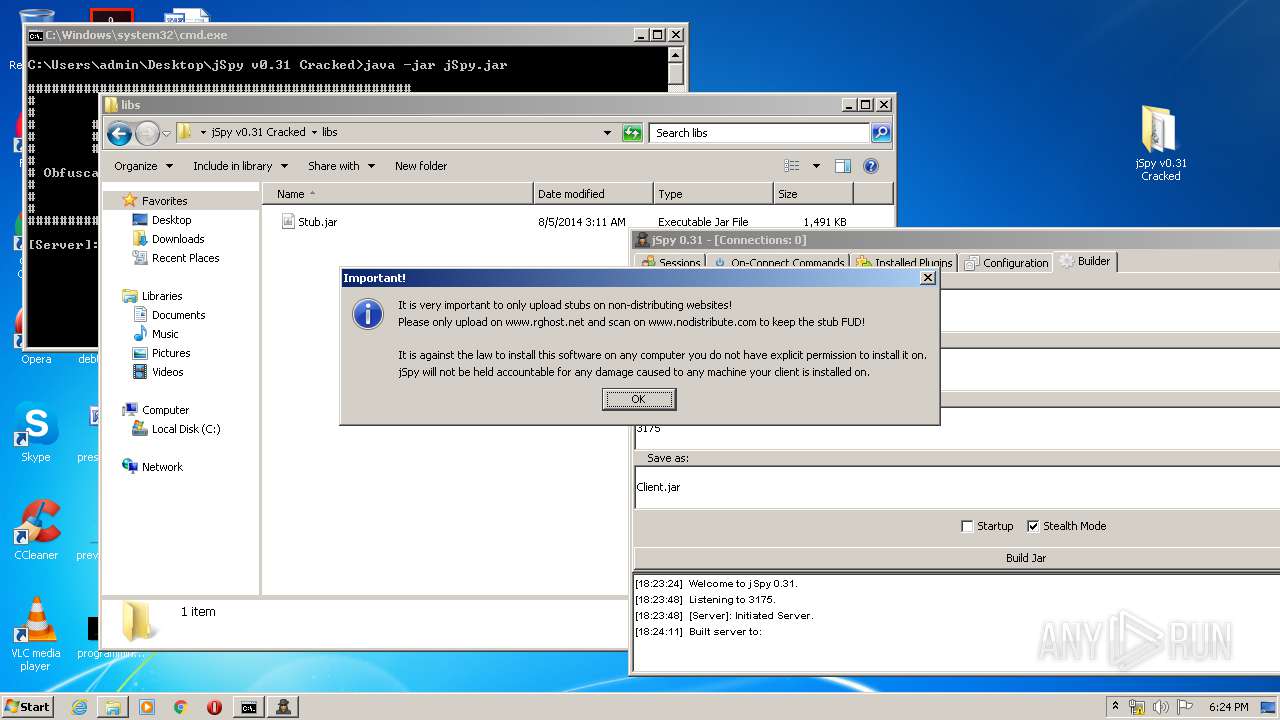
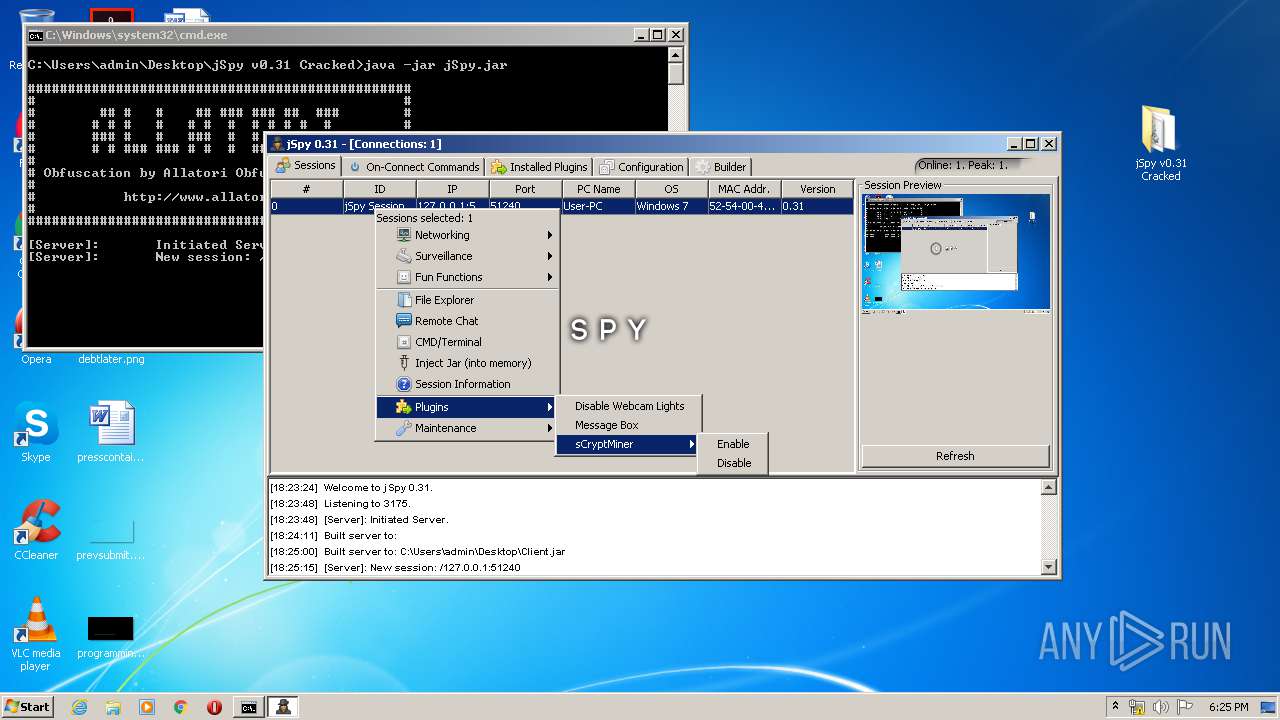
MALICIOUS
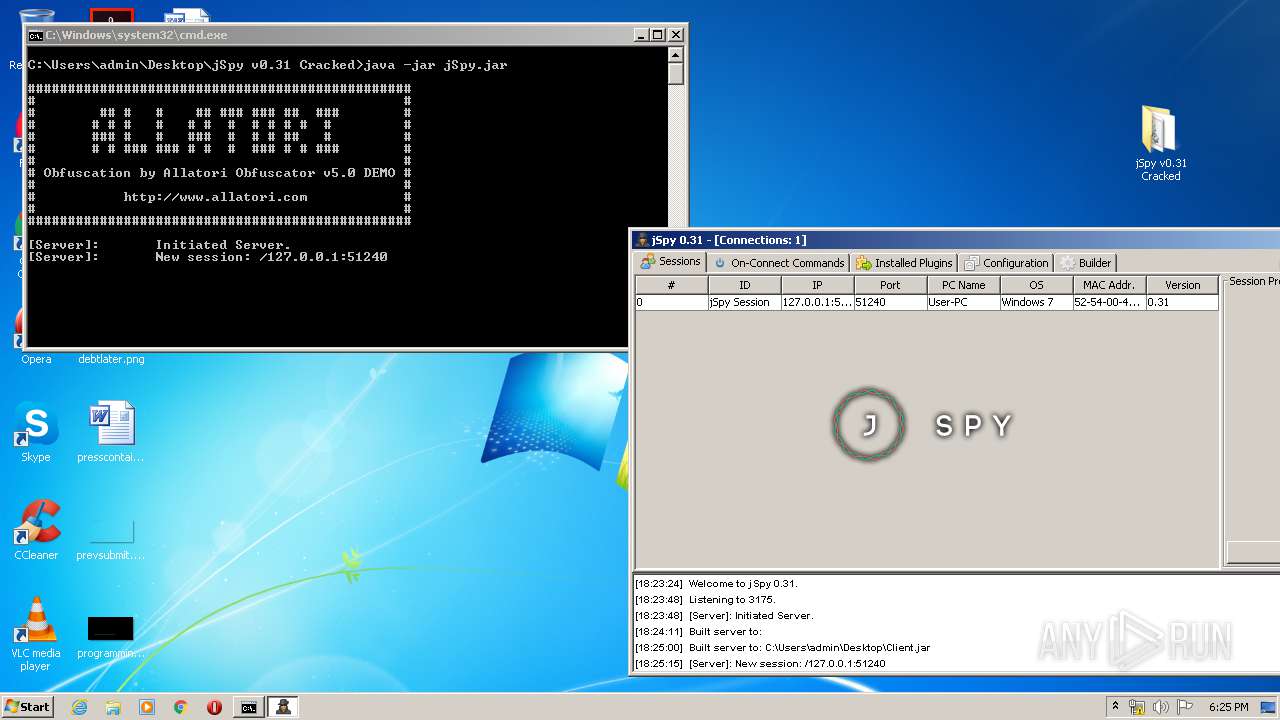
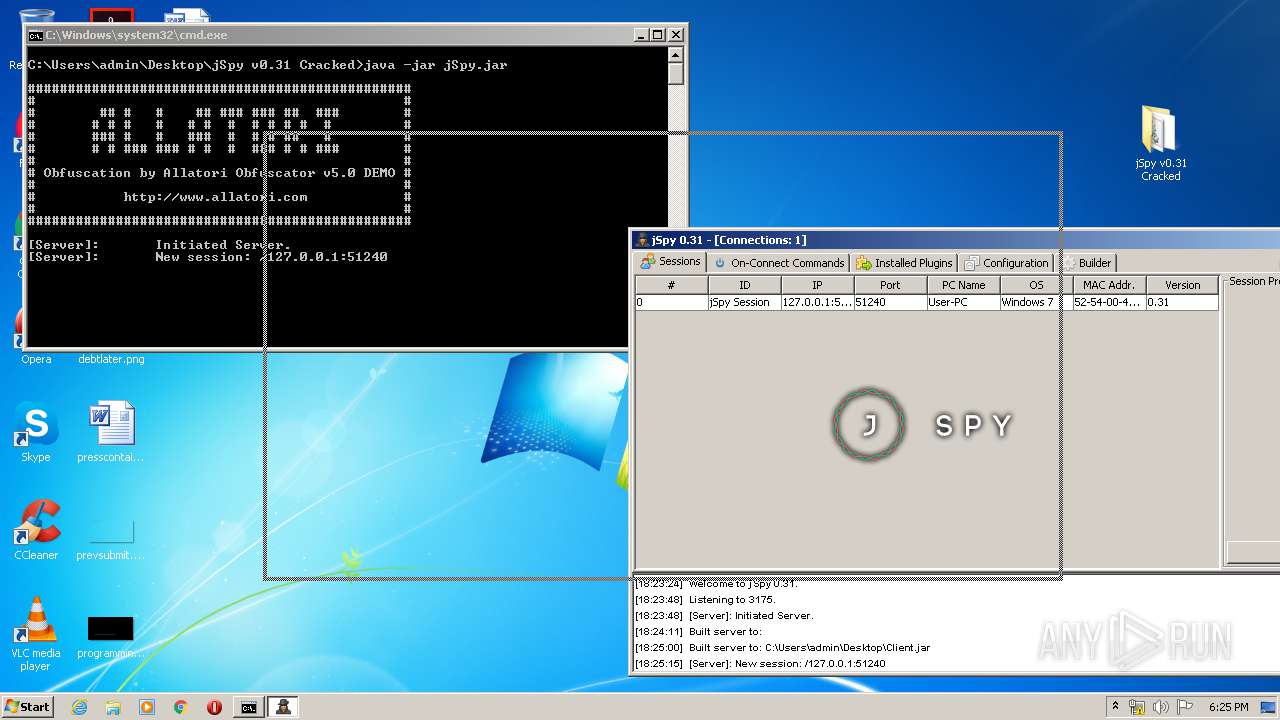
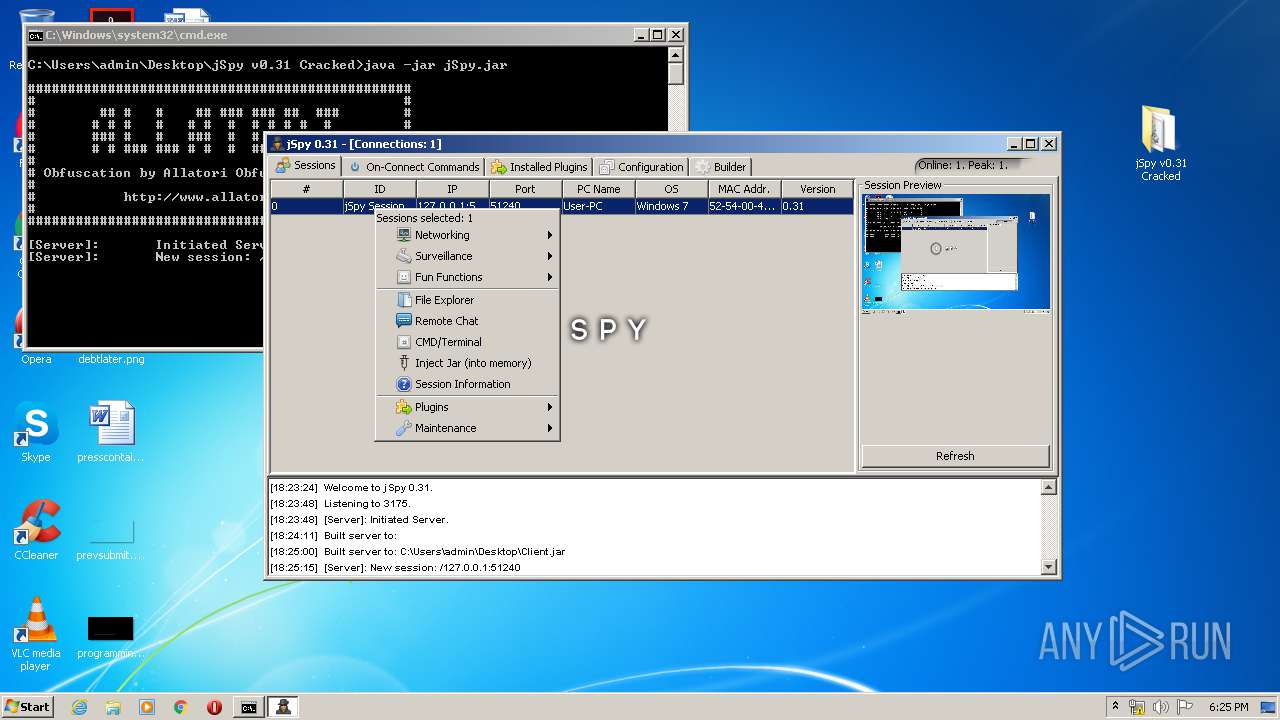
Loads dropped or rewritten executable
- javaw.exe (PID: 3180)
Actions looks like stealing of personal data
- java.exe (PID: 1828)
SUSPICIOUS
Executable content was dropped or overwritten
- javaw.exe (PID: 3180)
- java.exe (PID: 1828)
Creates files in the user directory
- java.exe (PID: 1828)
INFO
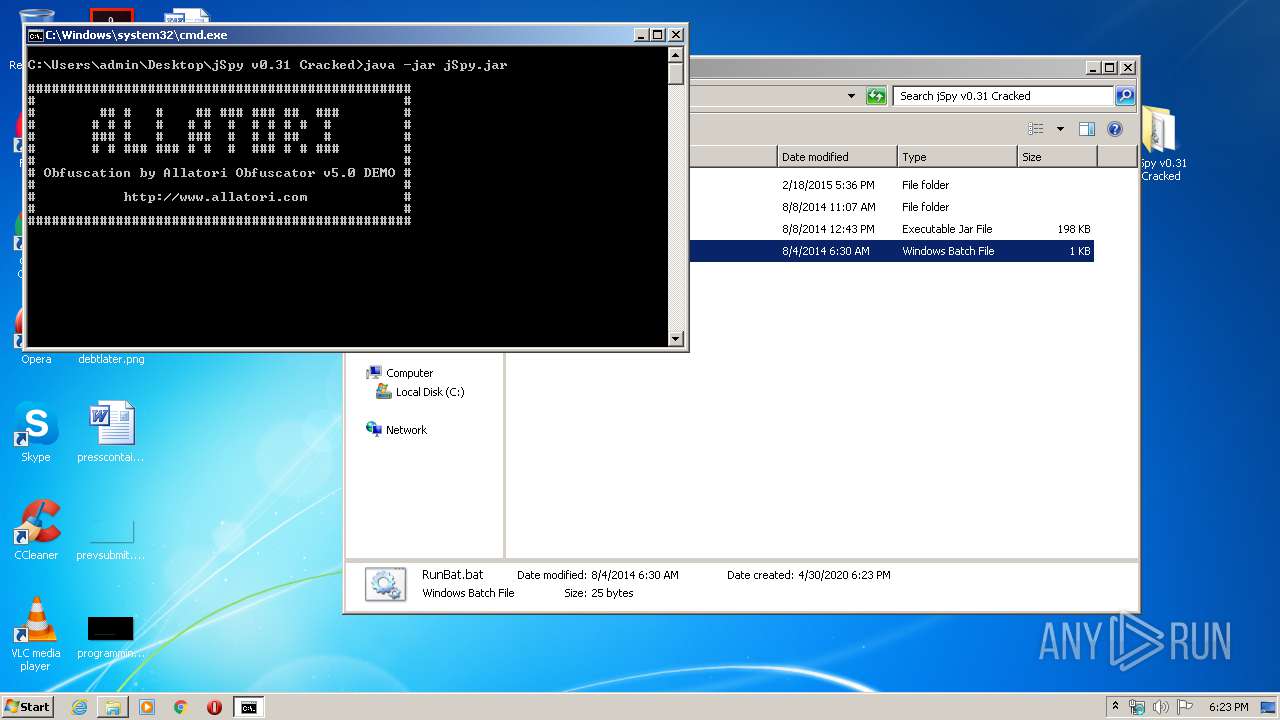
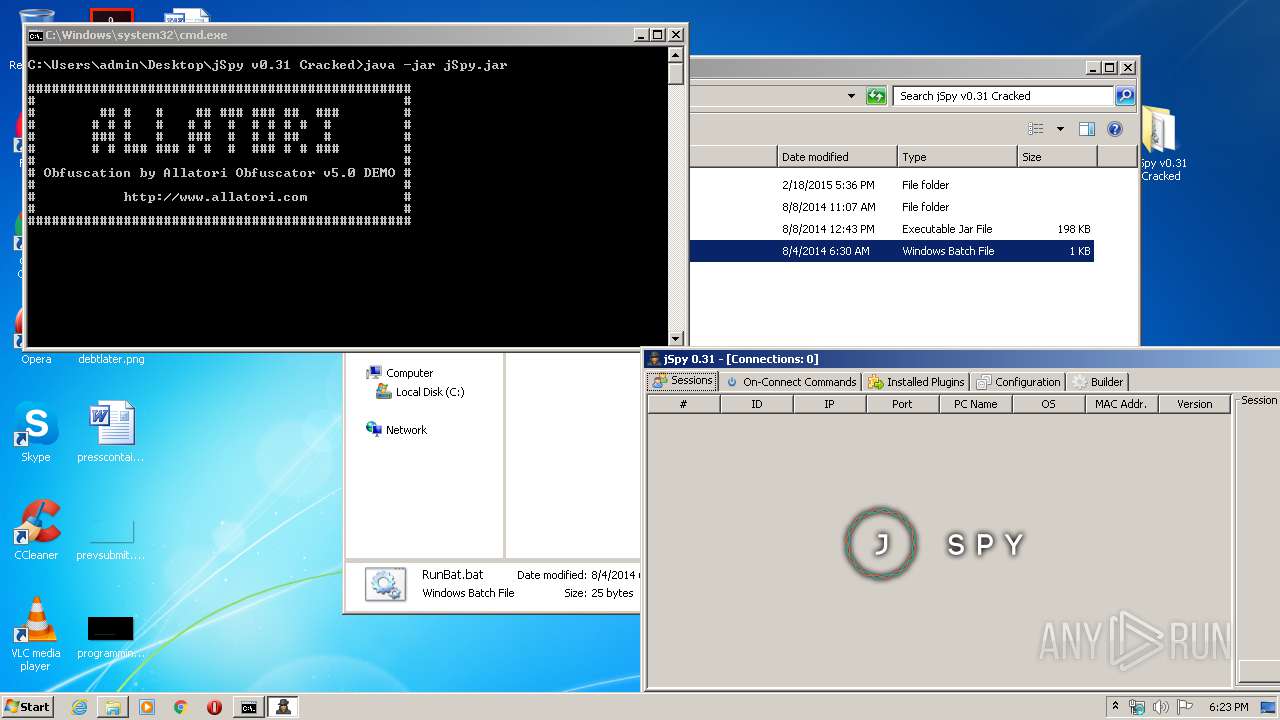
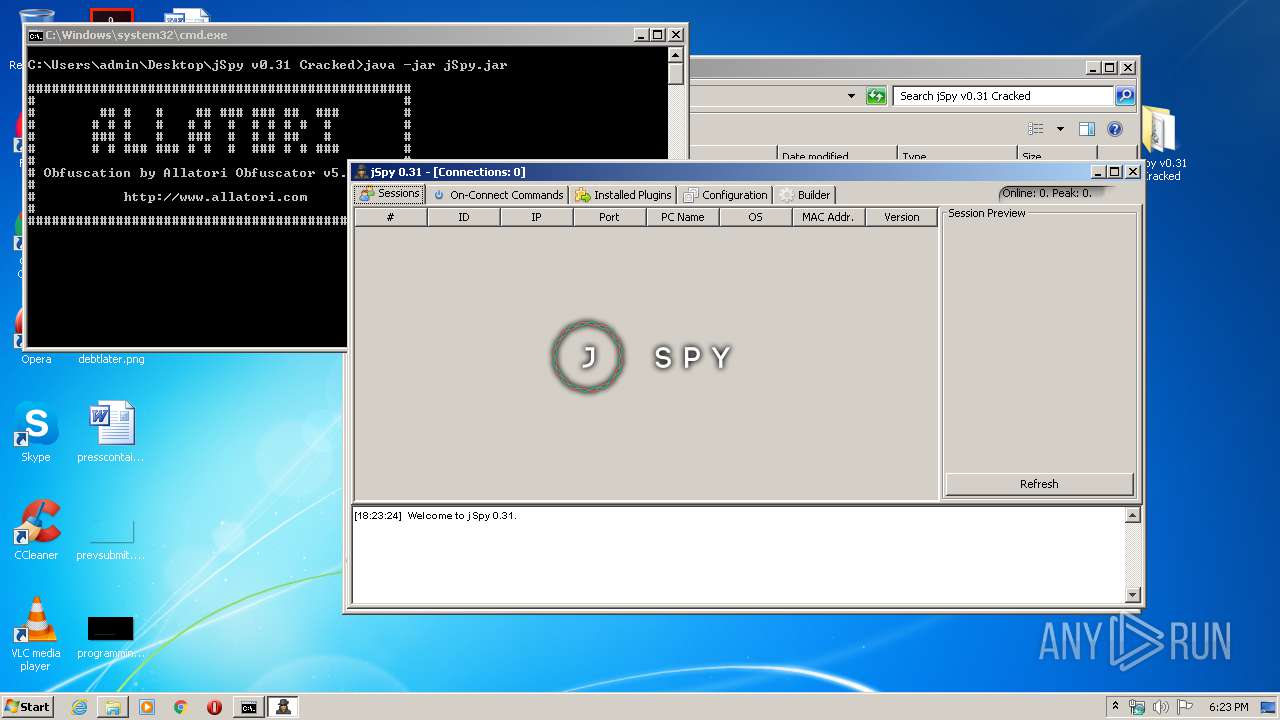
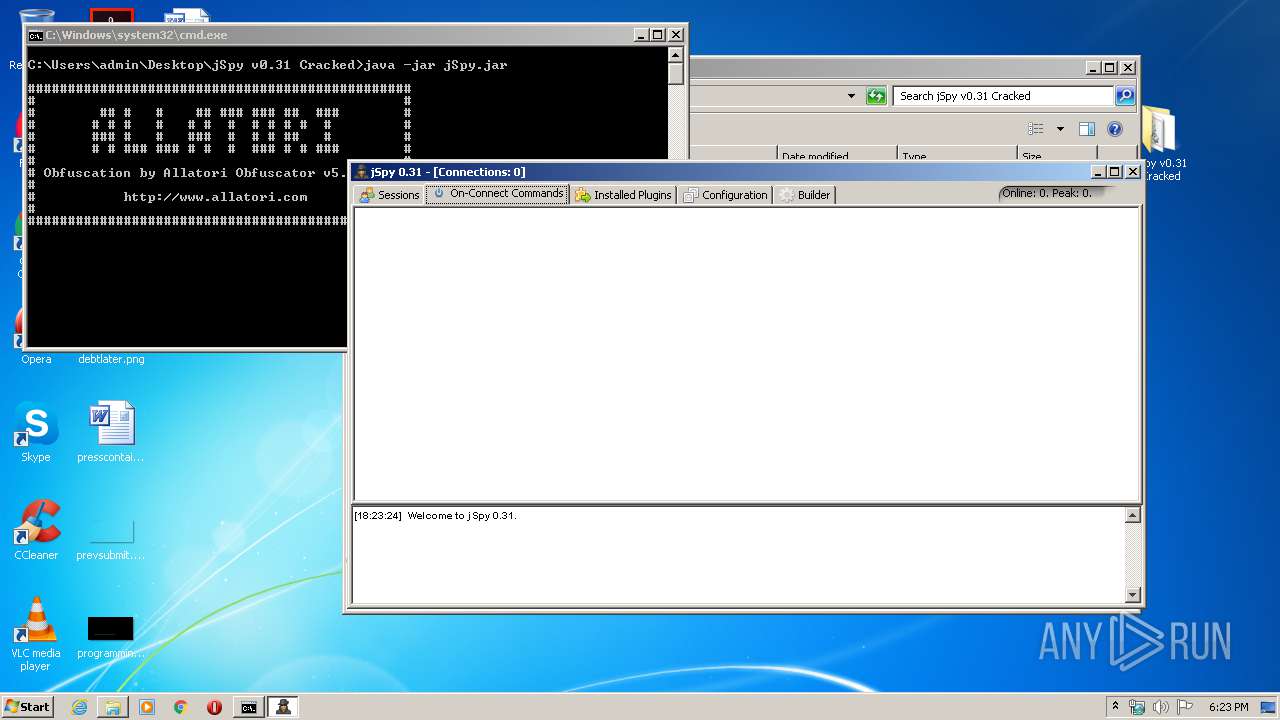
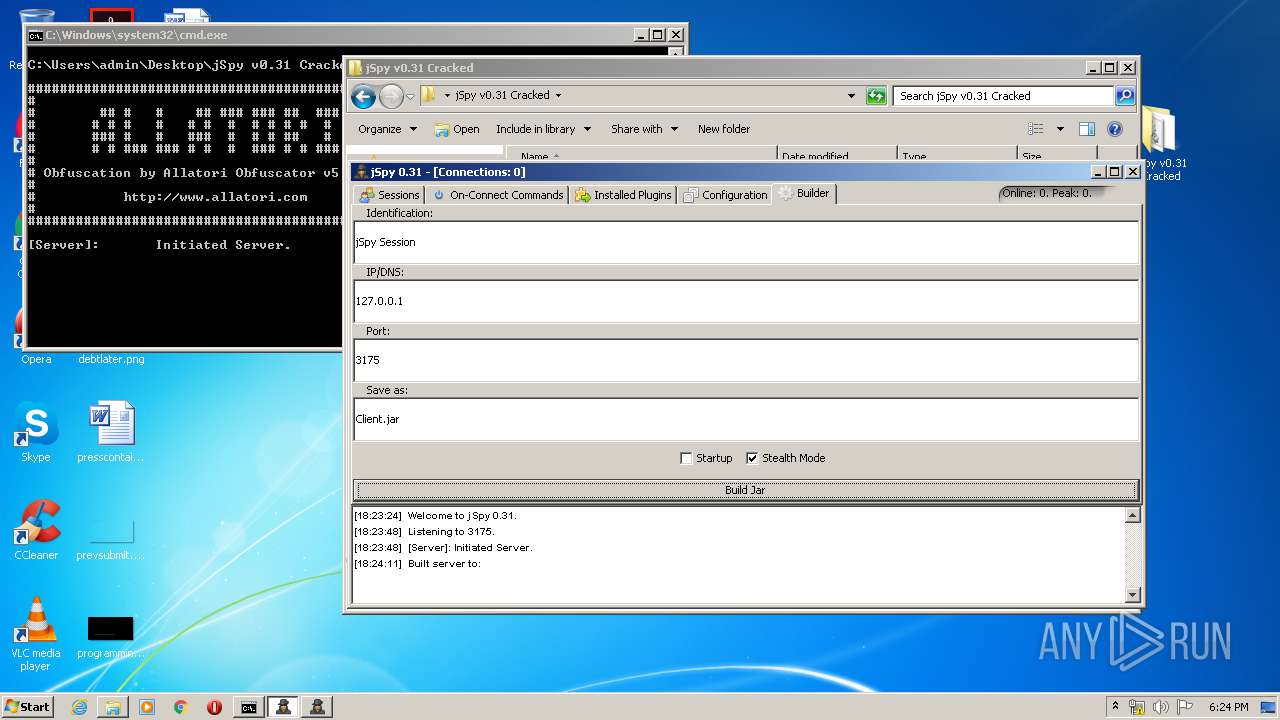
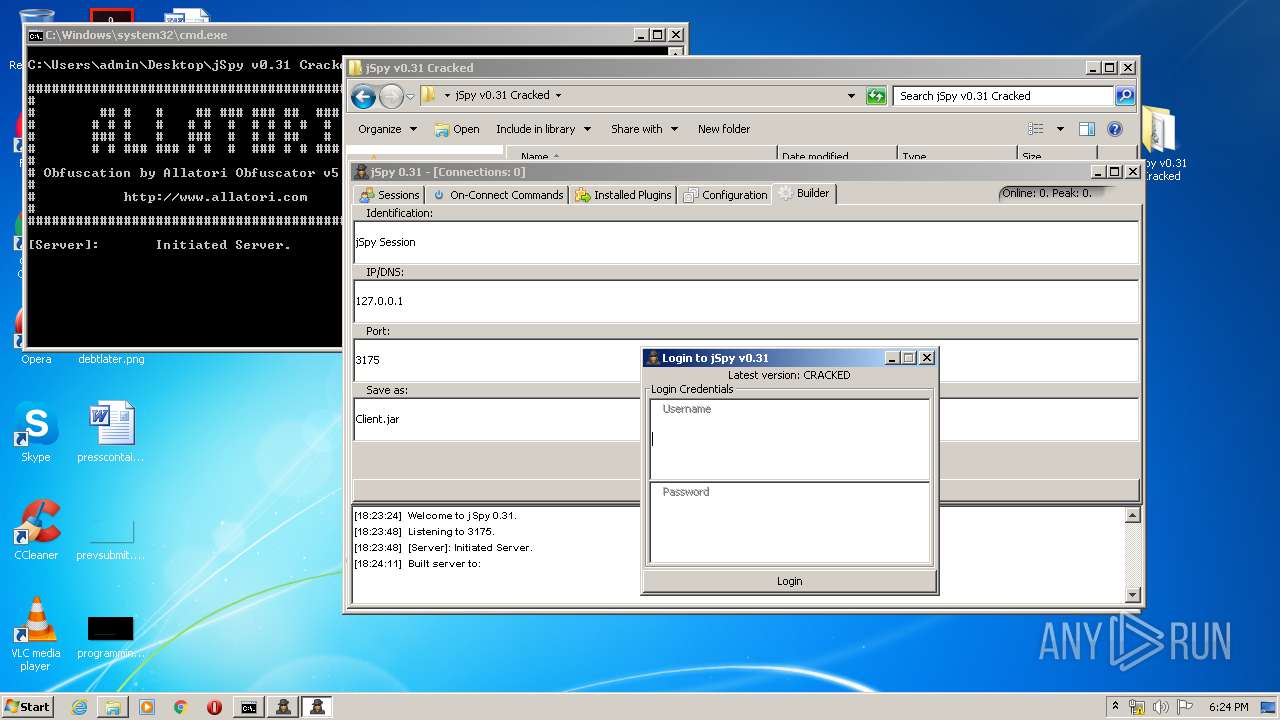
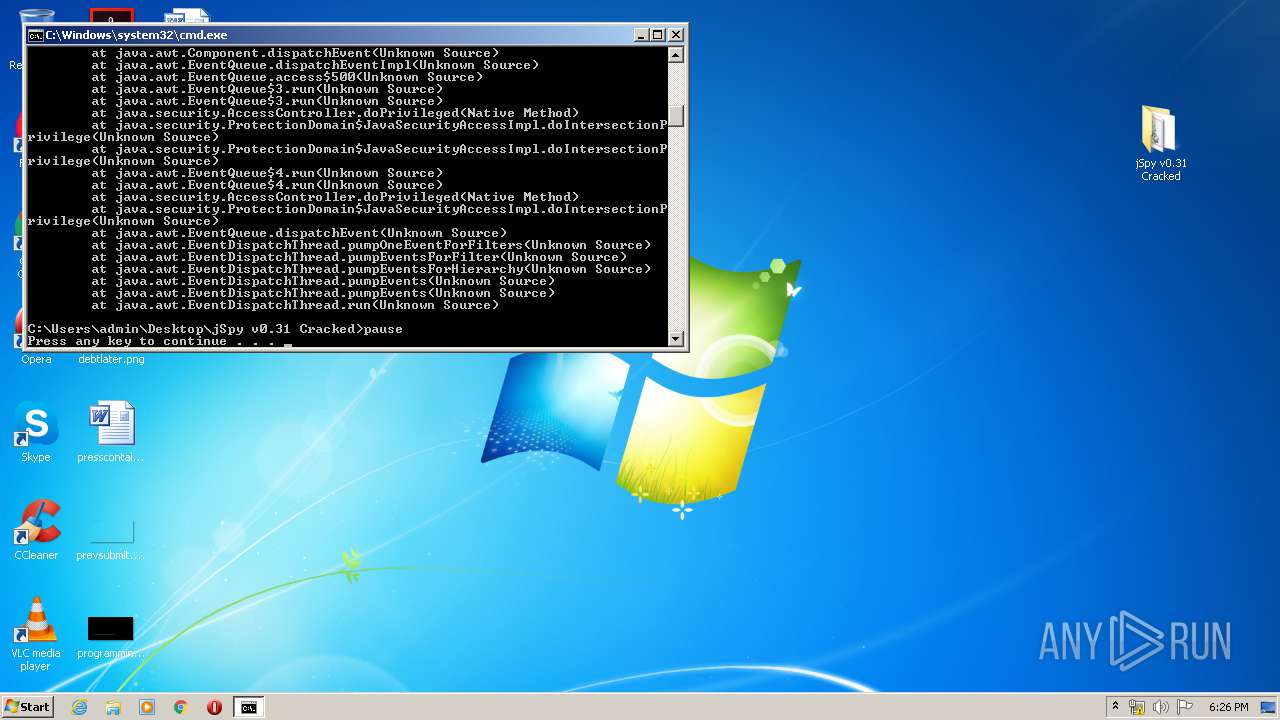
Manual execution by user
- cmd.exe (PID: 1632)
- javaw.exe (PID: 3180)
- javaw.exe (PID: 3512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 164370 |
|---|---|
| UncompressedSize: | 202060 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2014:08:08 12:43:06 |
| PackingMethod: | Normal |
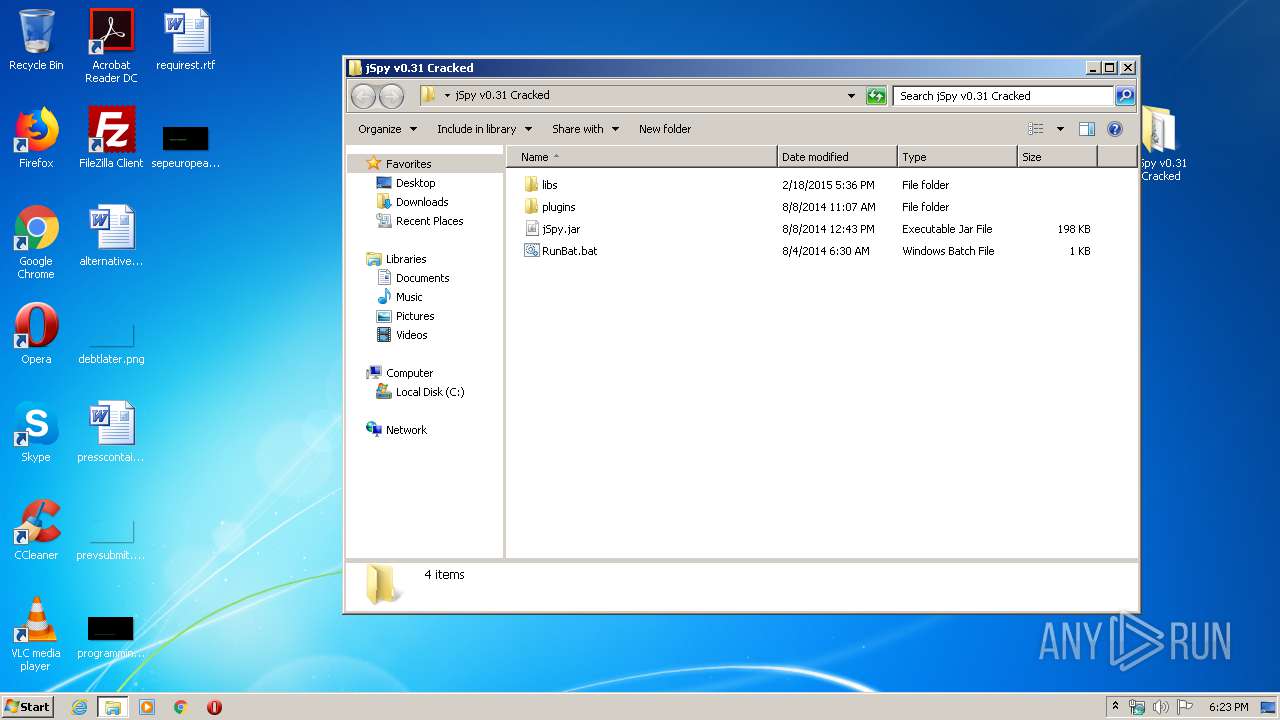
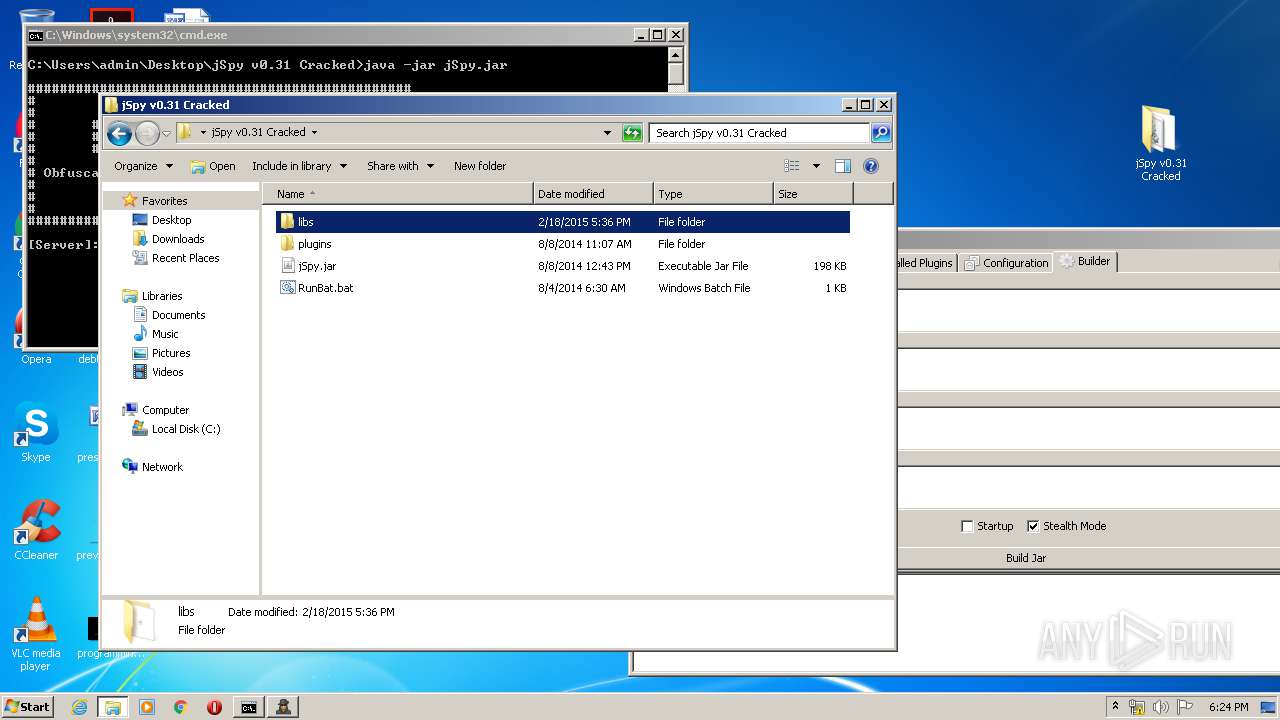
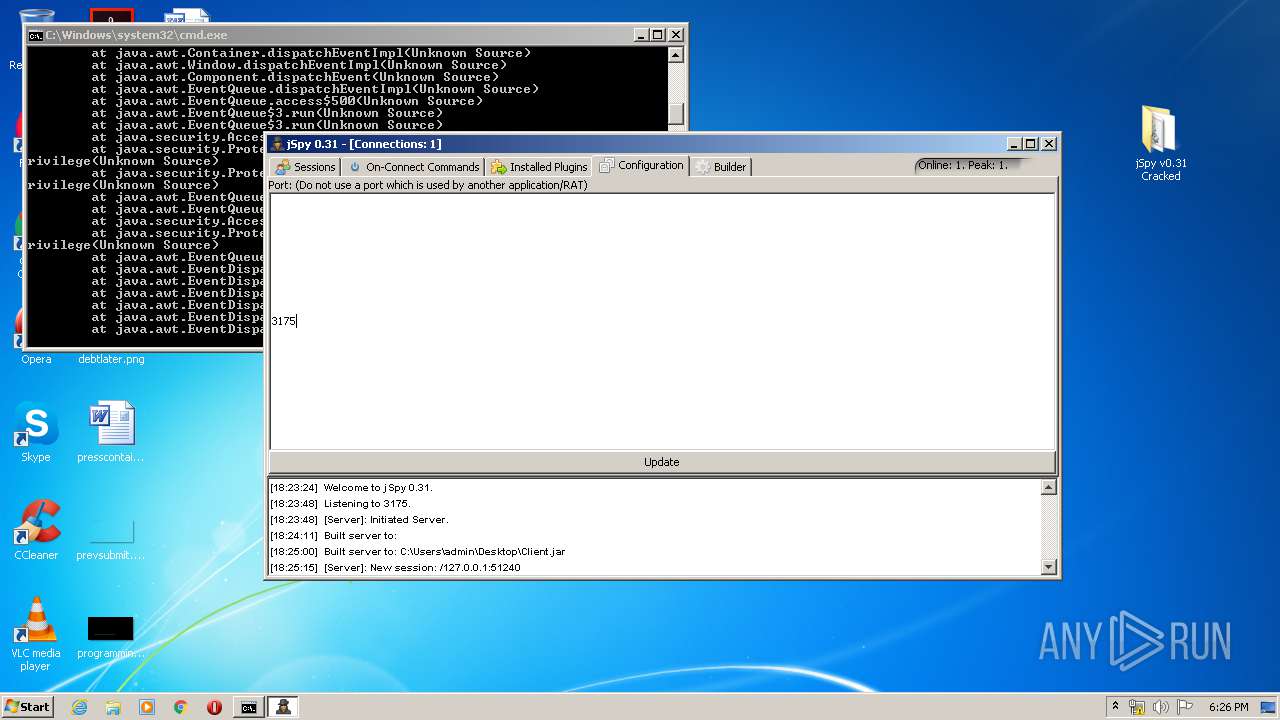
| ArchivedFileName: | jSpy v0.31 Cracked\jSpy.jar |
Total processes
53
Monitored processes
5
Malicious processes
2
Suspicious processes
0
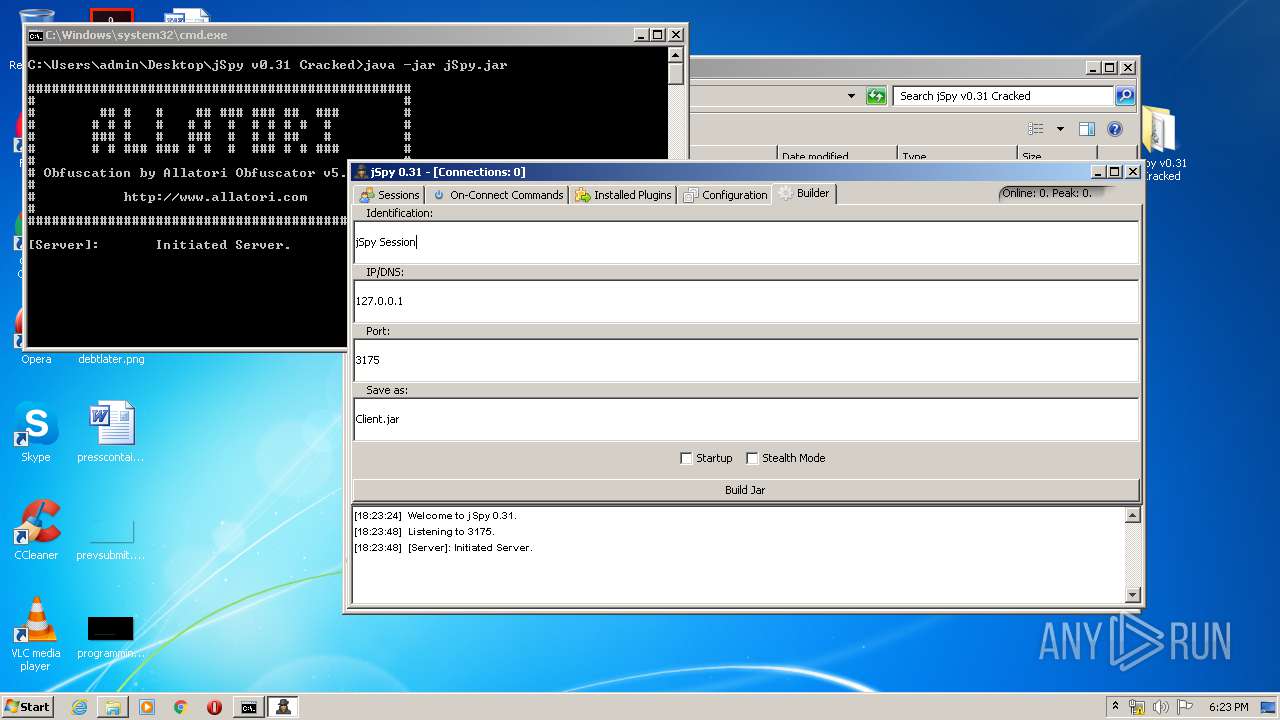
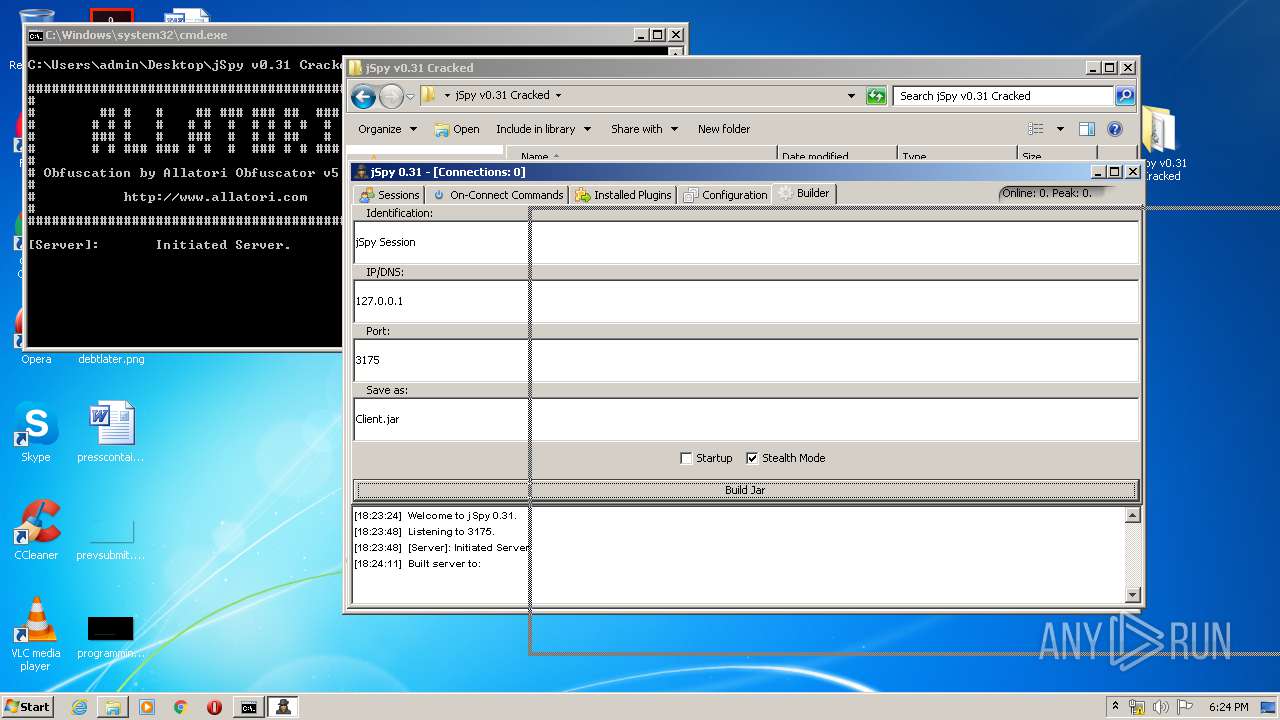
Behavior graph
Click at the process to see the details
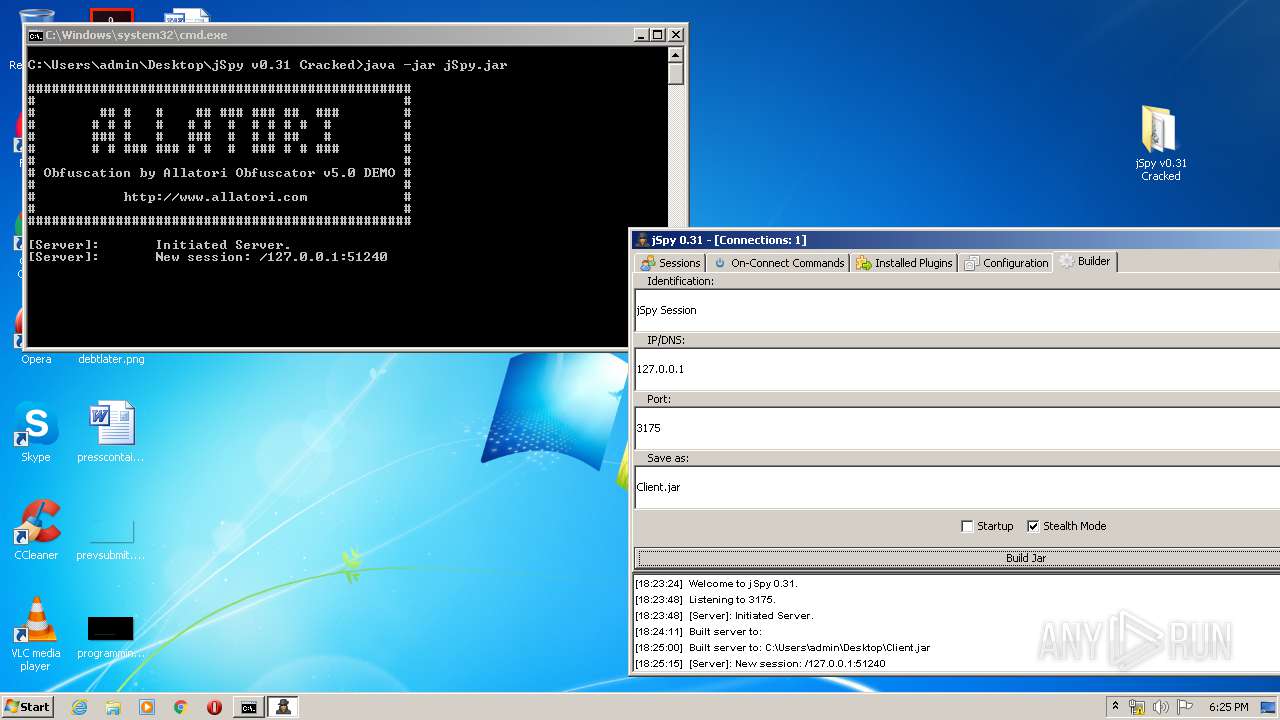
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
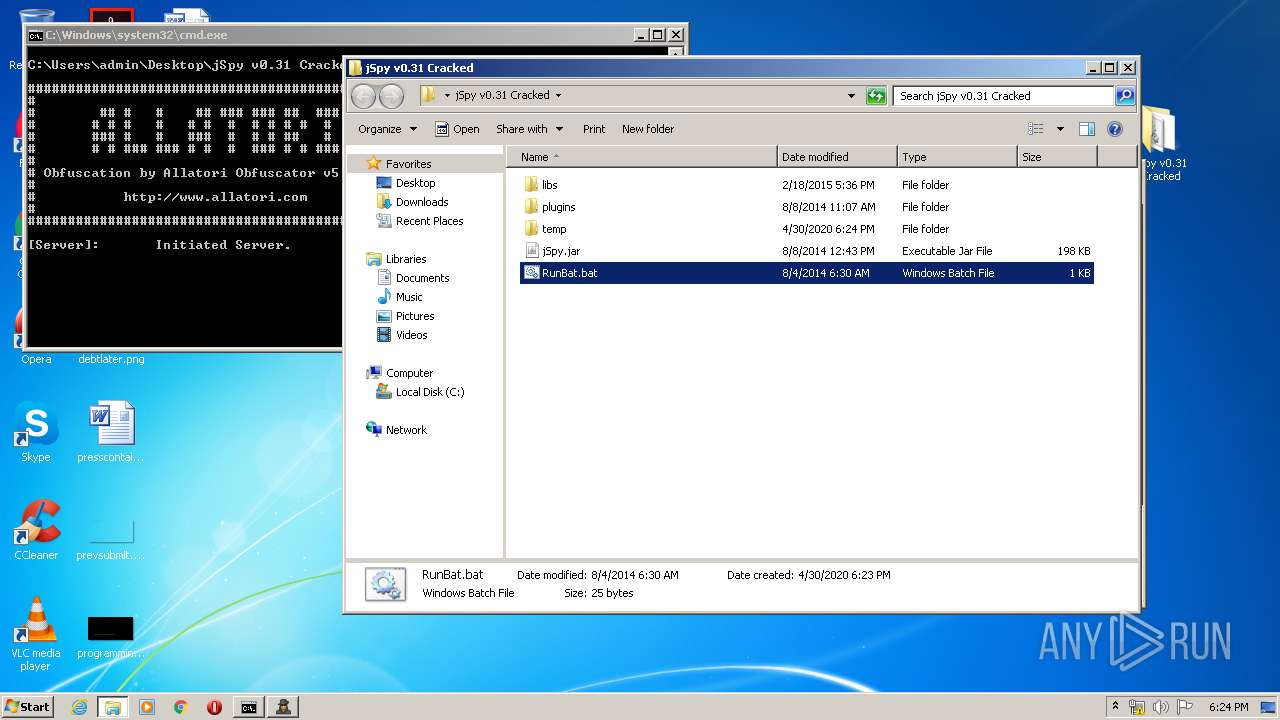
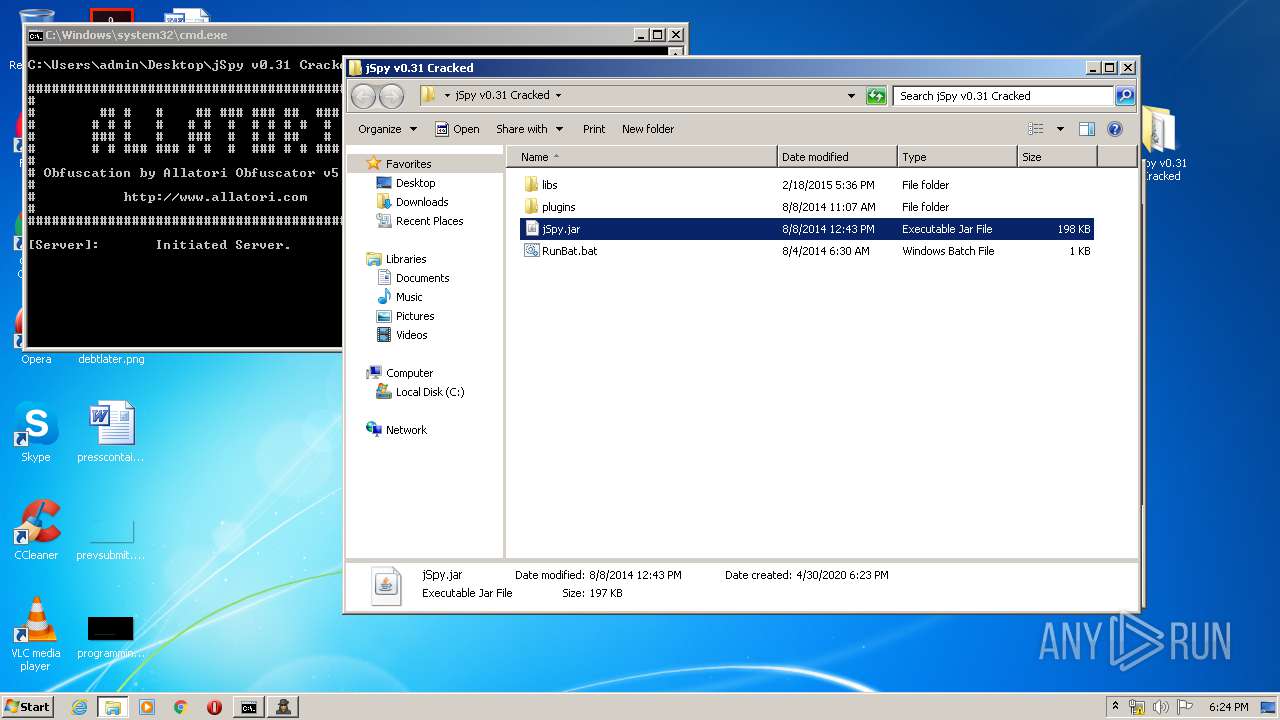
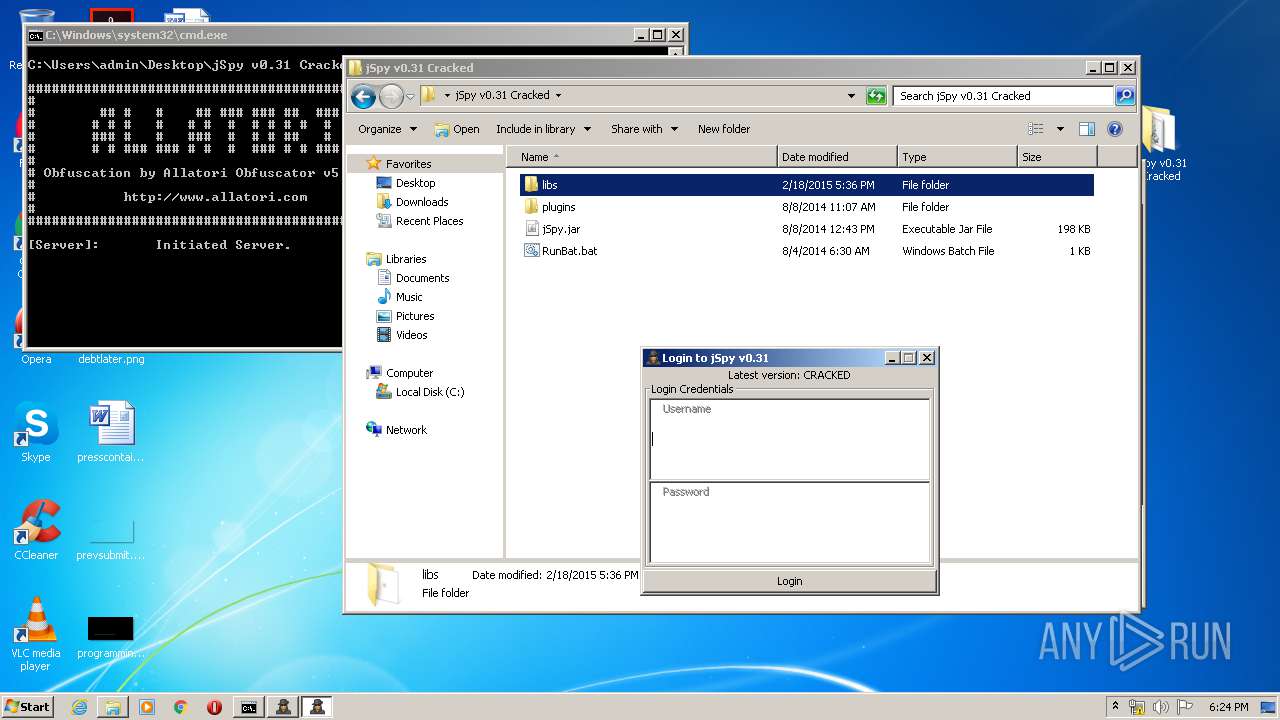
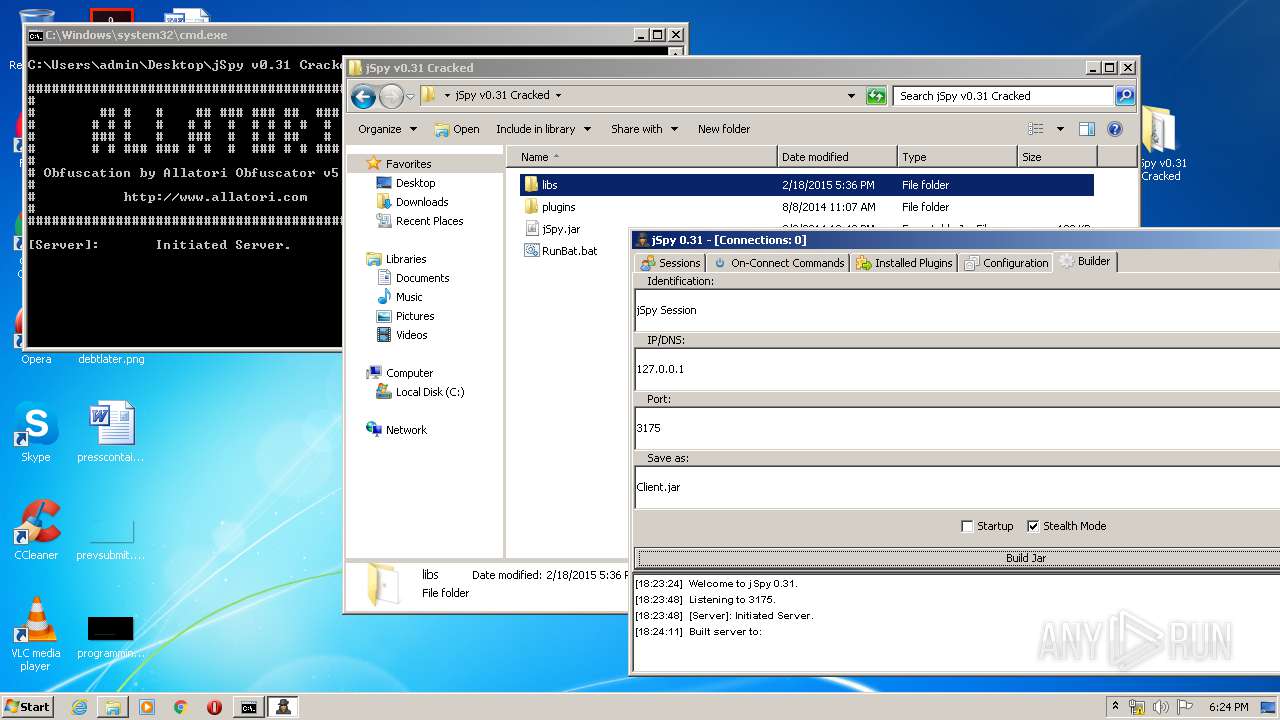
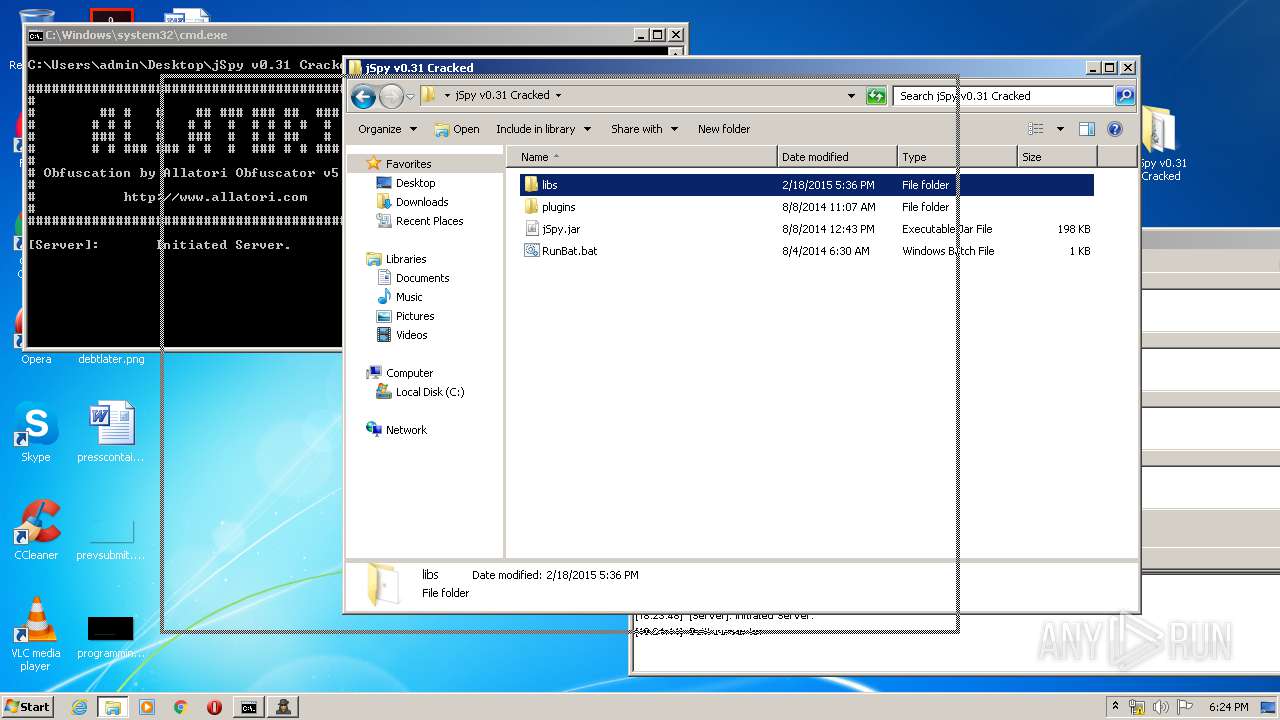
| 1632 | cmd /c ""C:\Users\admin\Desktop\jSpy v0.31 Cracked\RunBat.bat" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
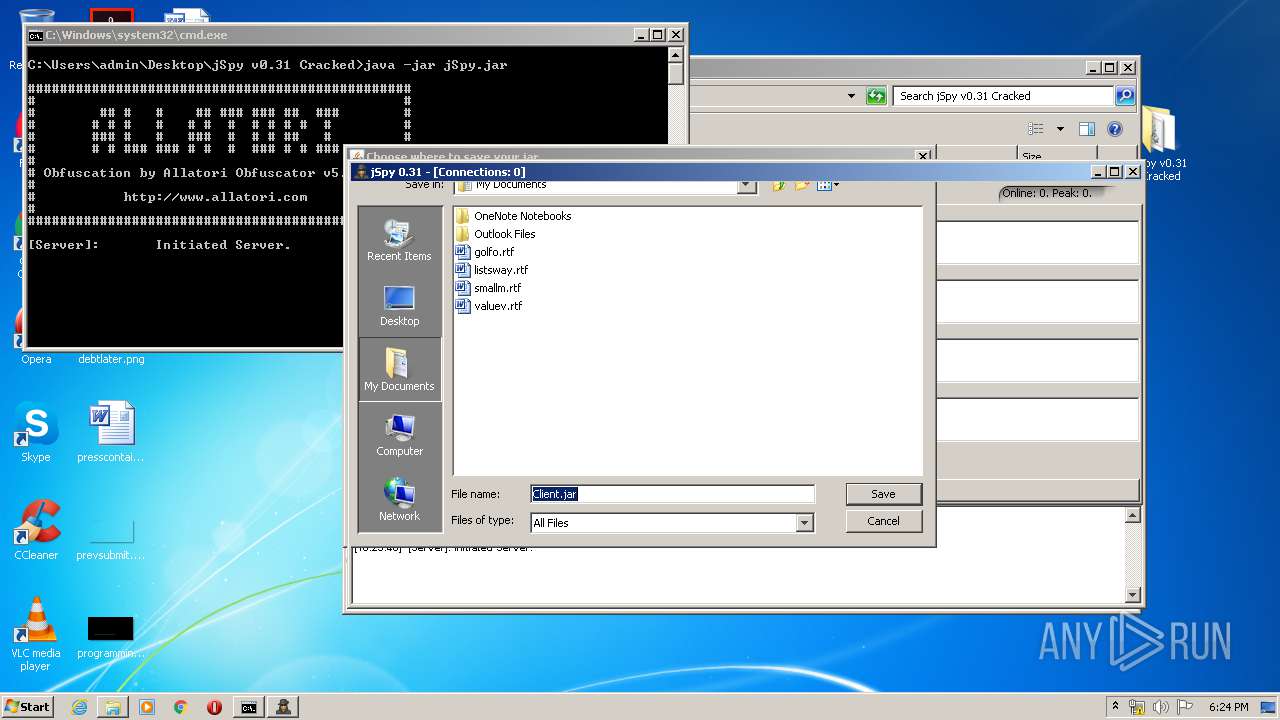
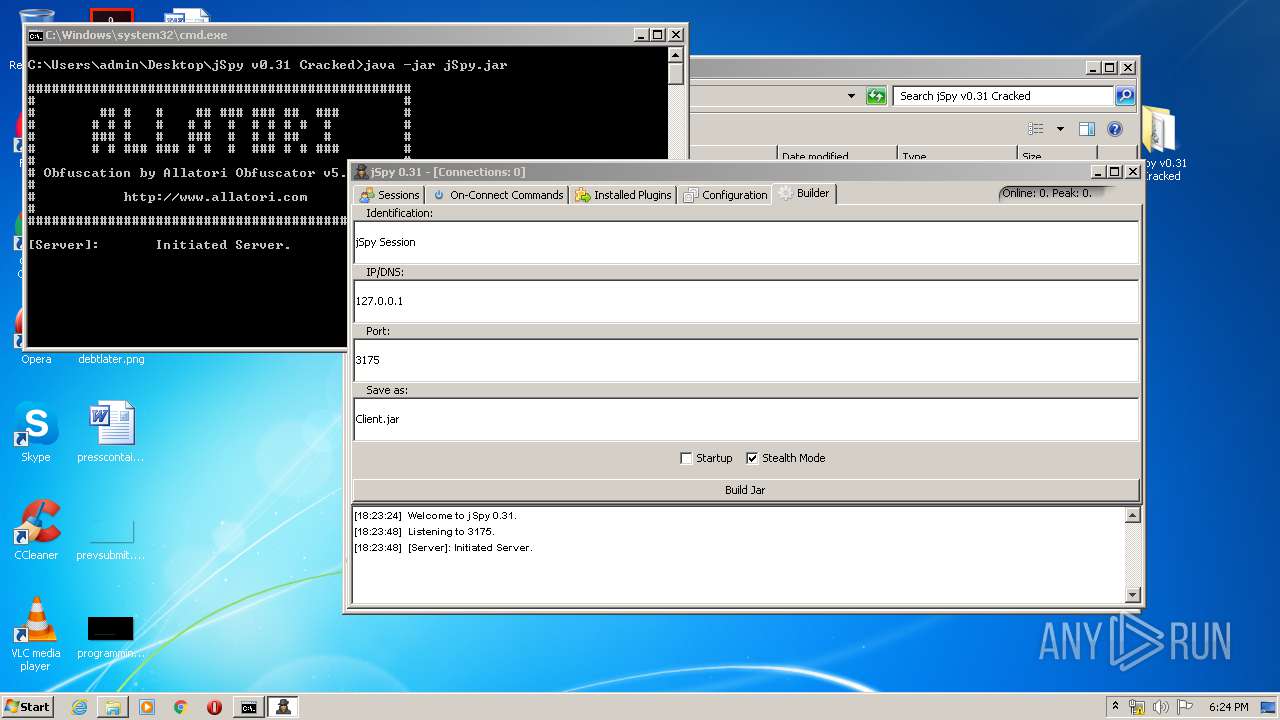
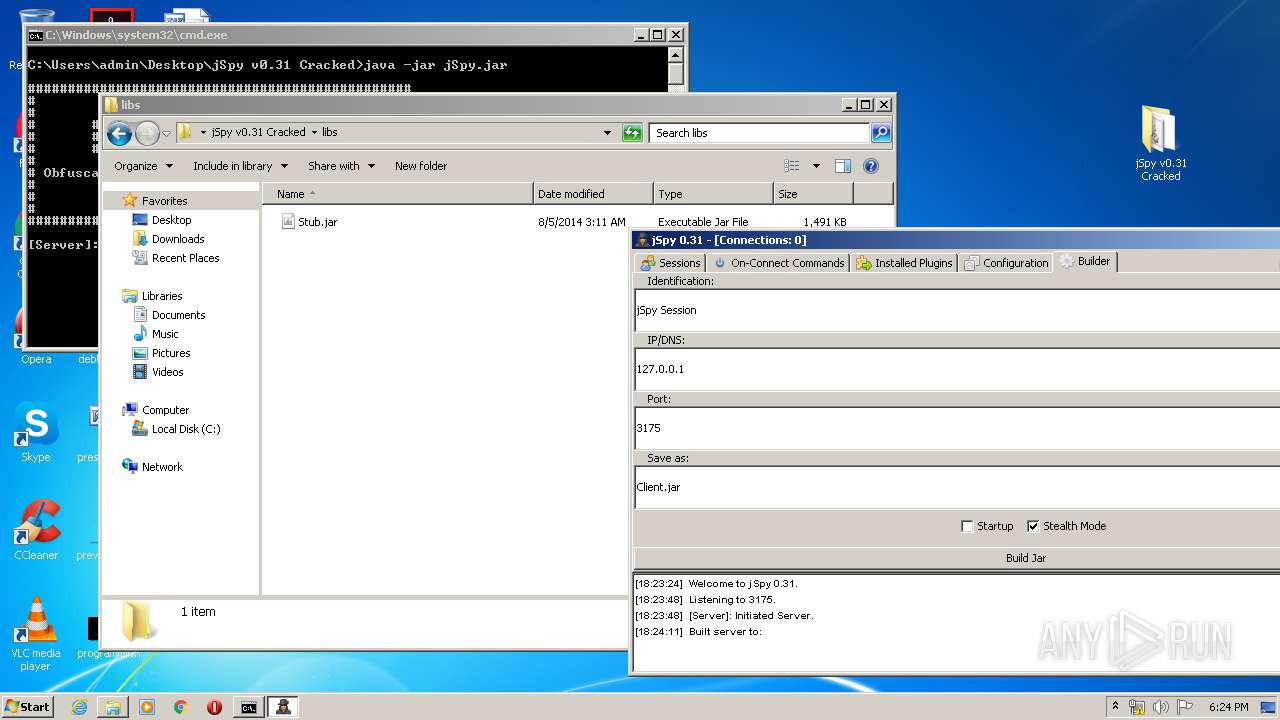
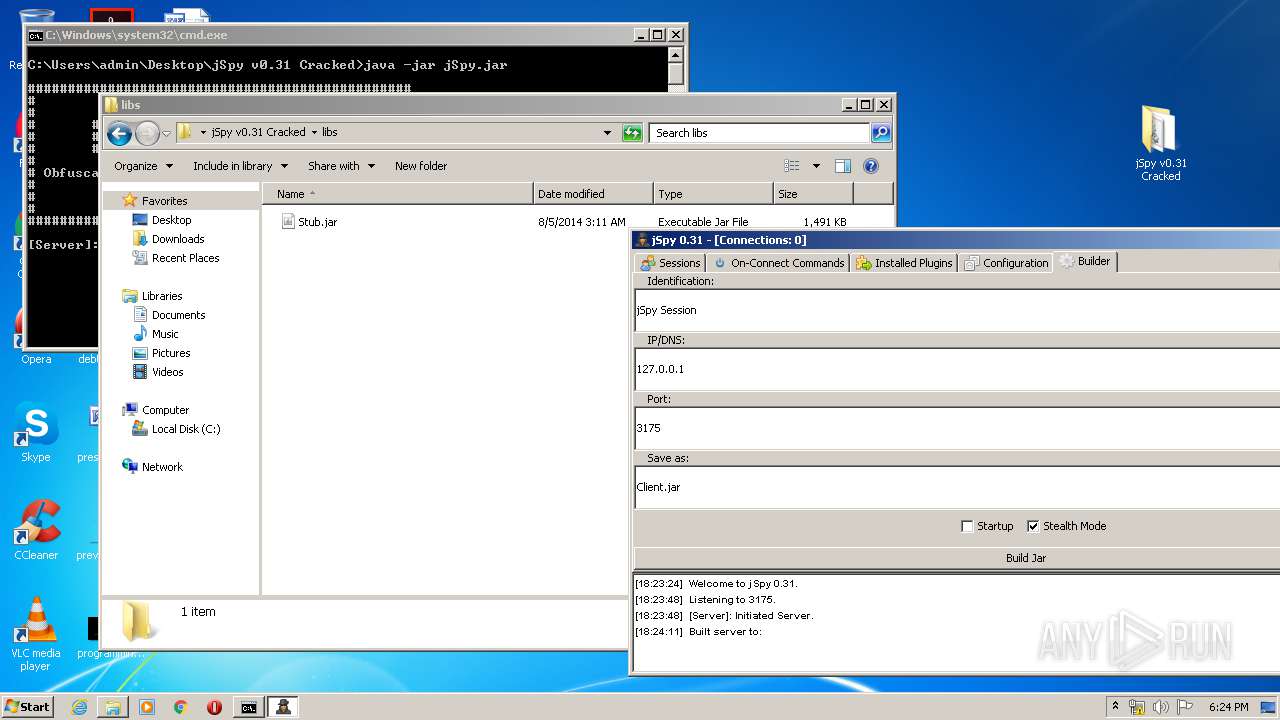
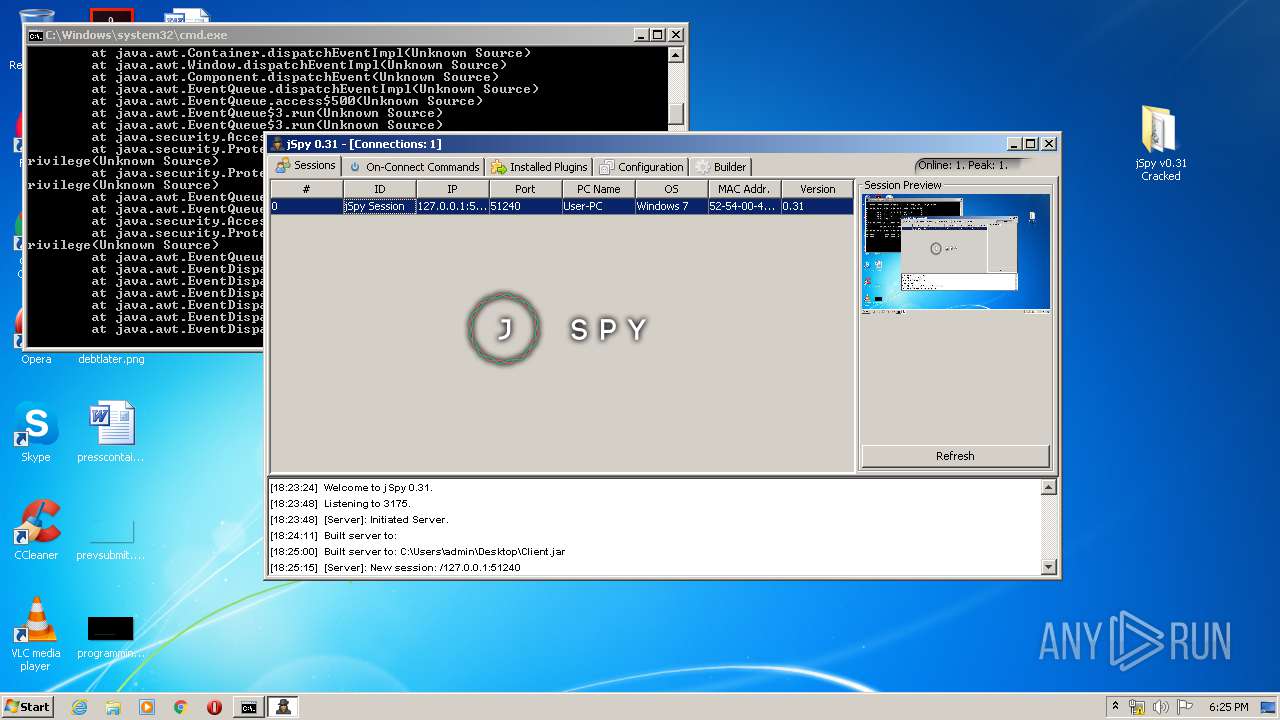
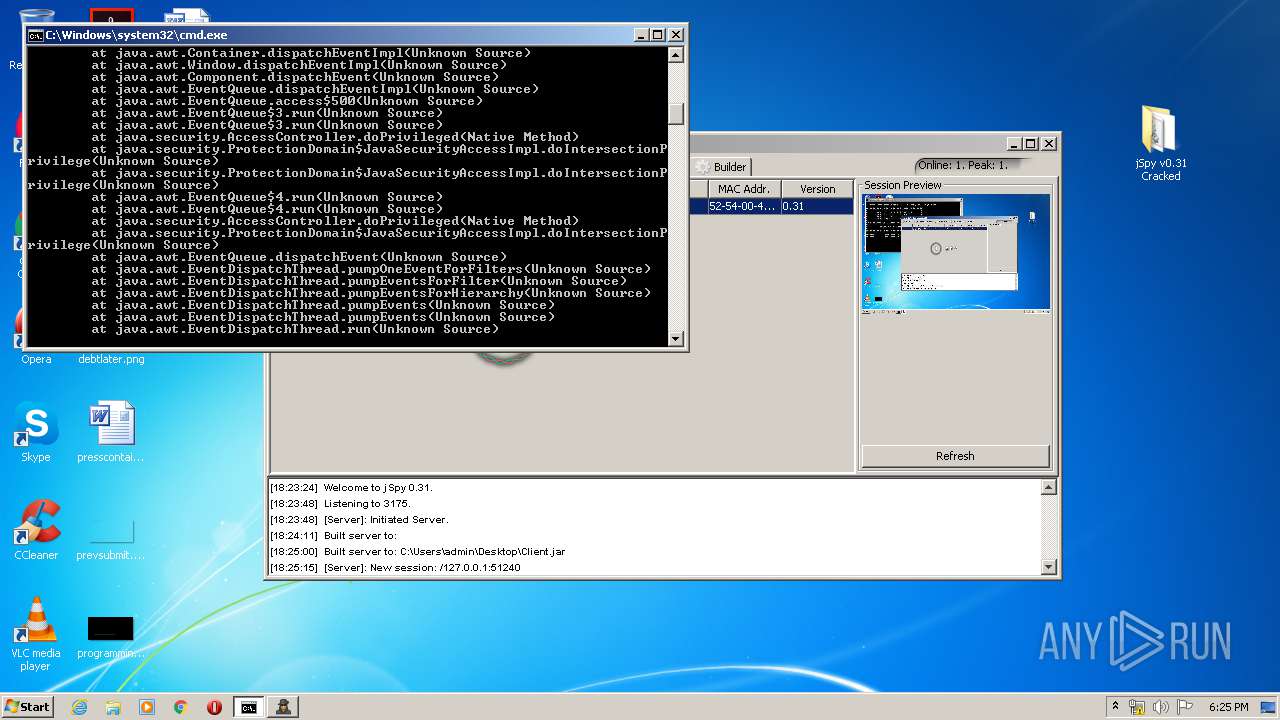
| 1828 | java -jar jSpy.jar | C:\ProgramData\Oracle\Java\javapath\java.exe | cmd.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
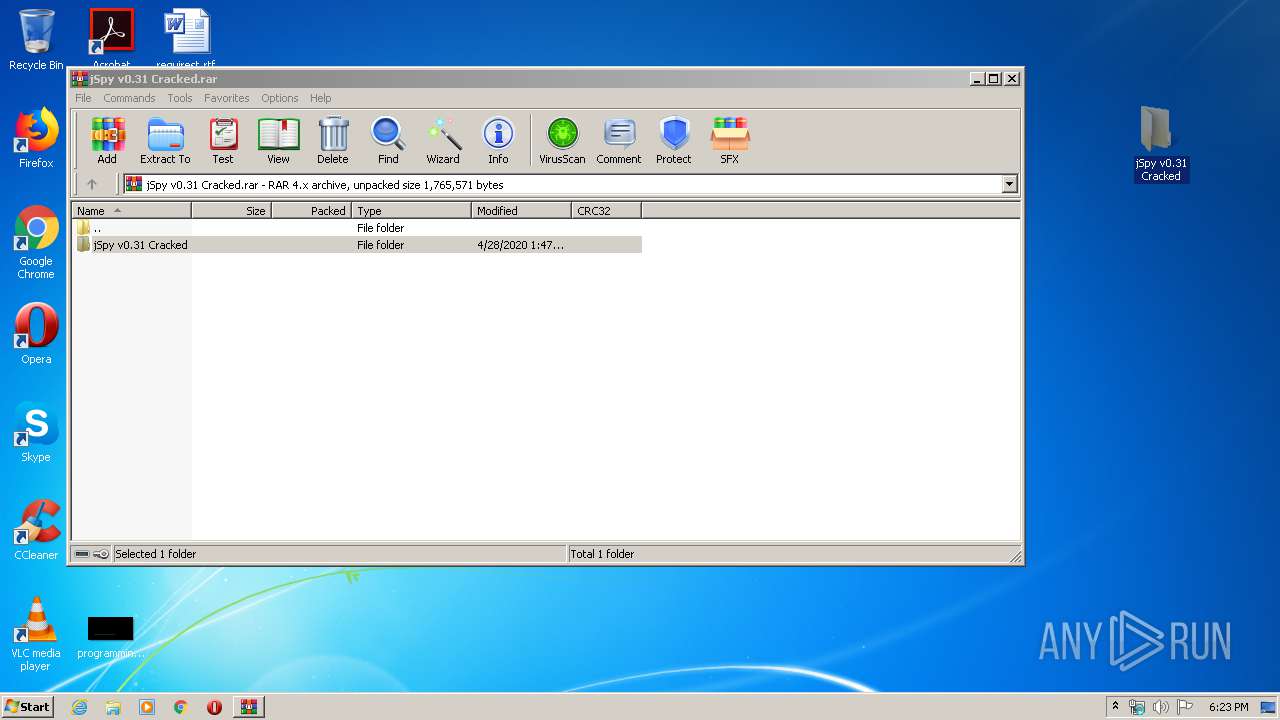
| 3168 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\jSpy v0.31 Cracked.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
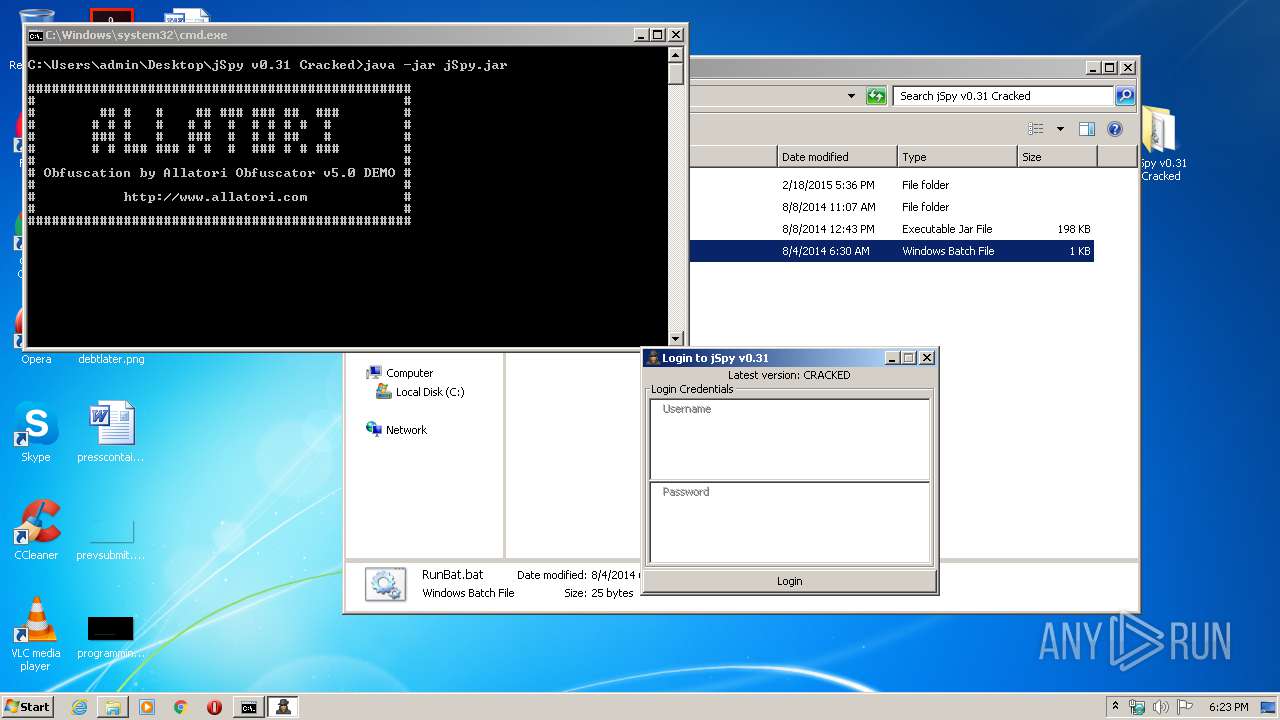
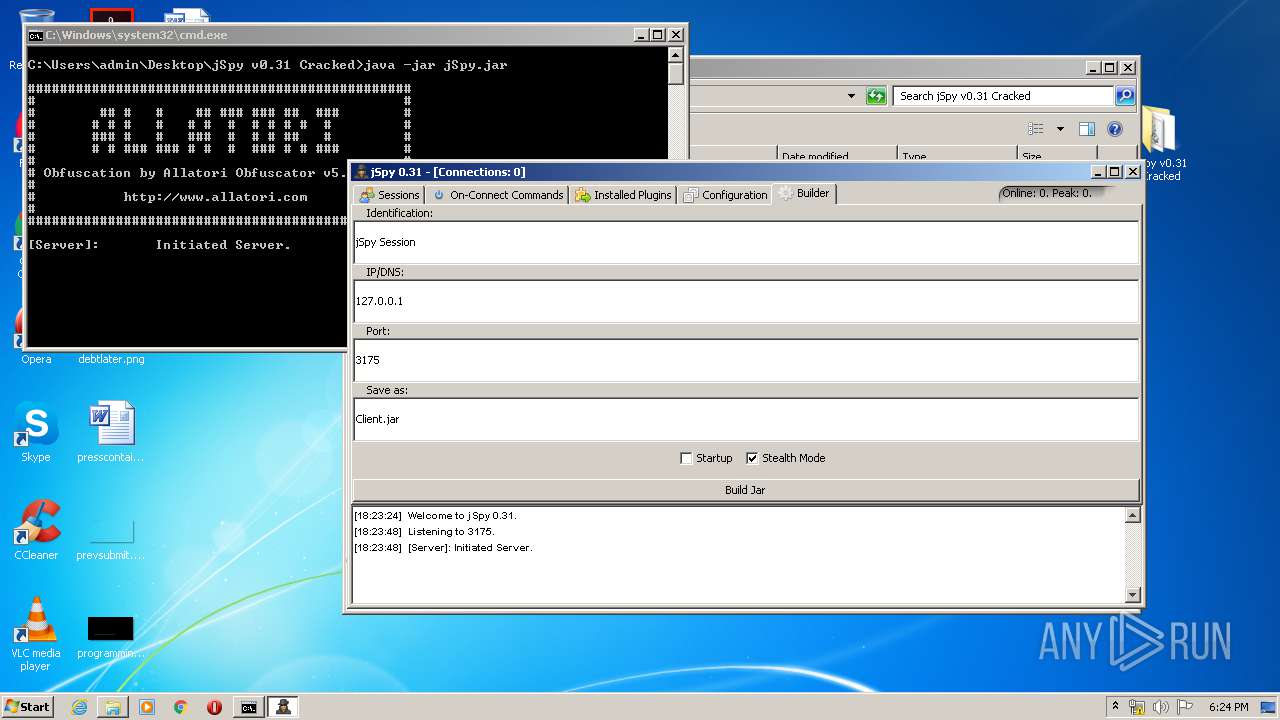
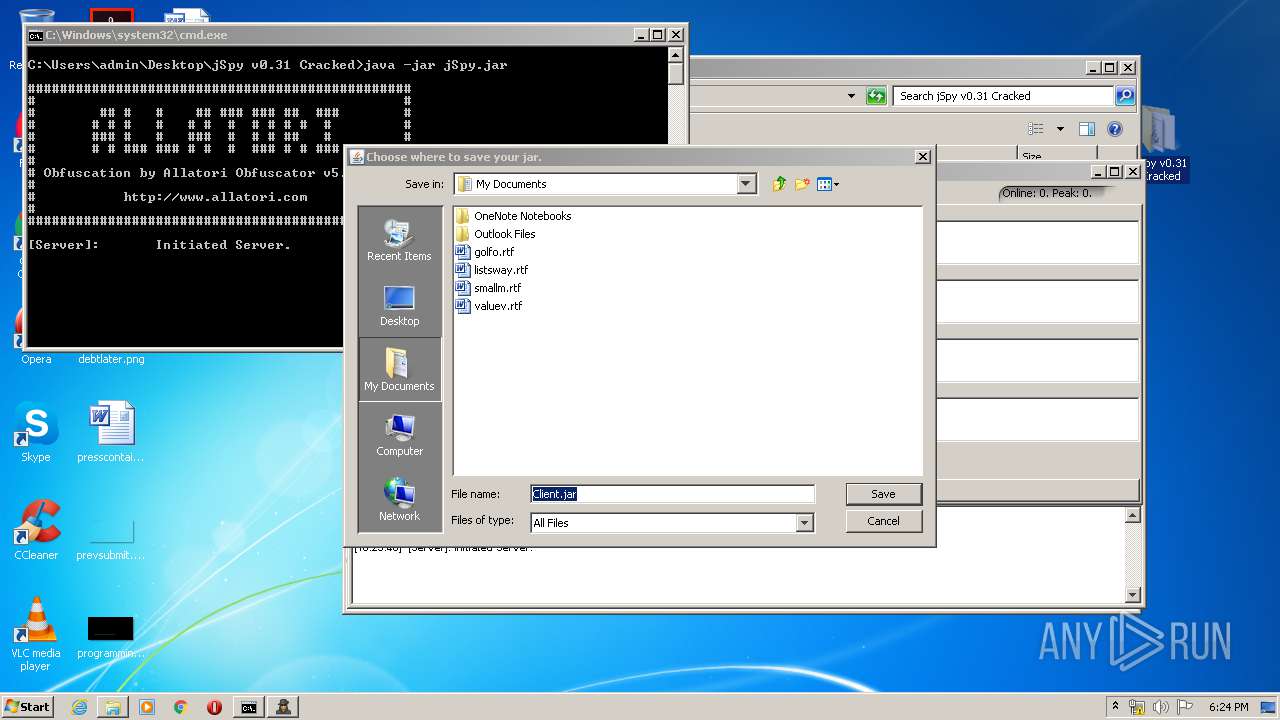
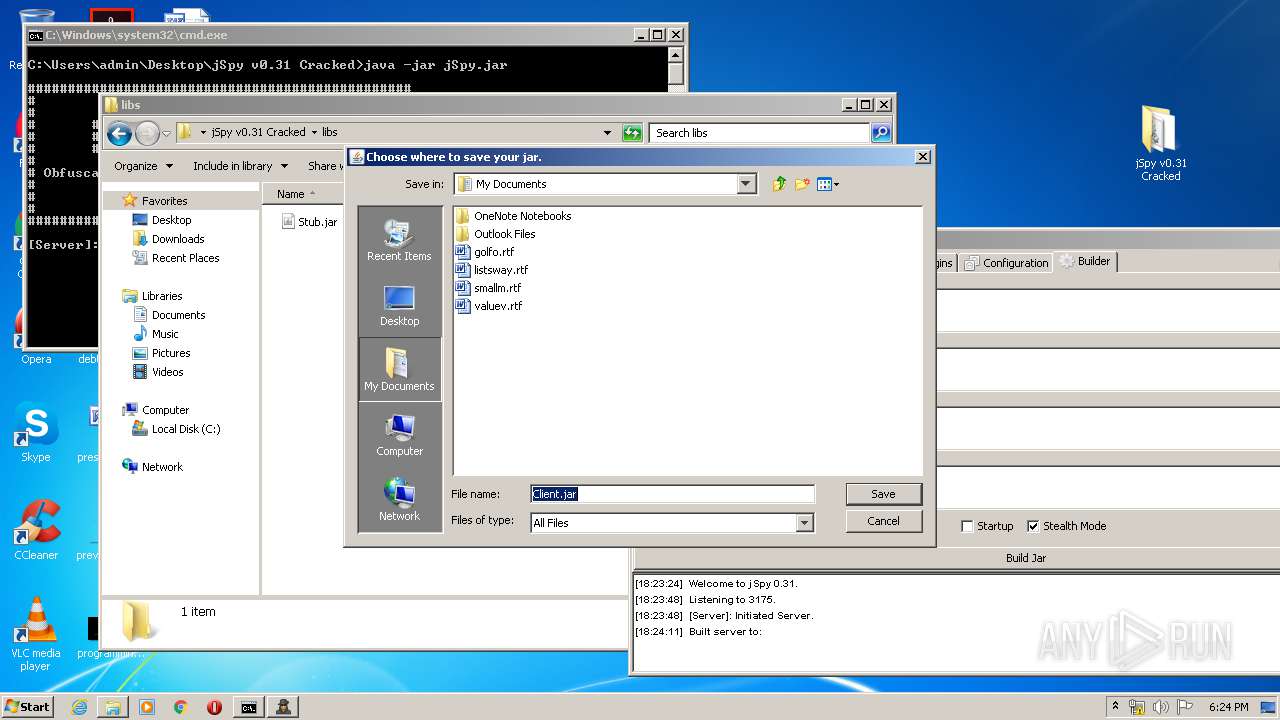
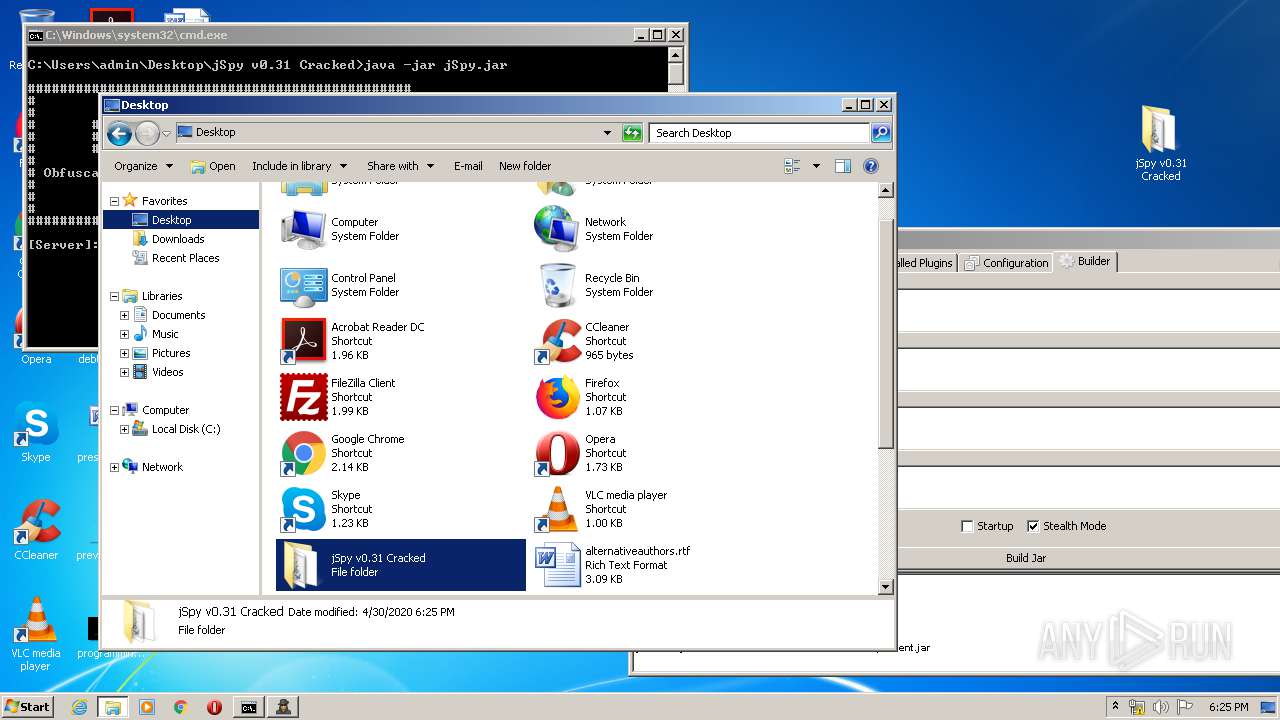
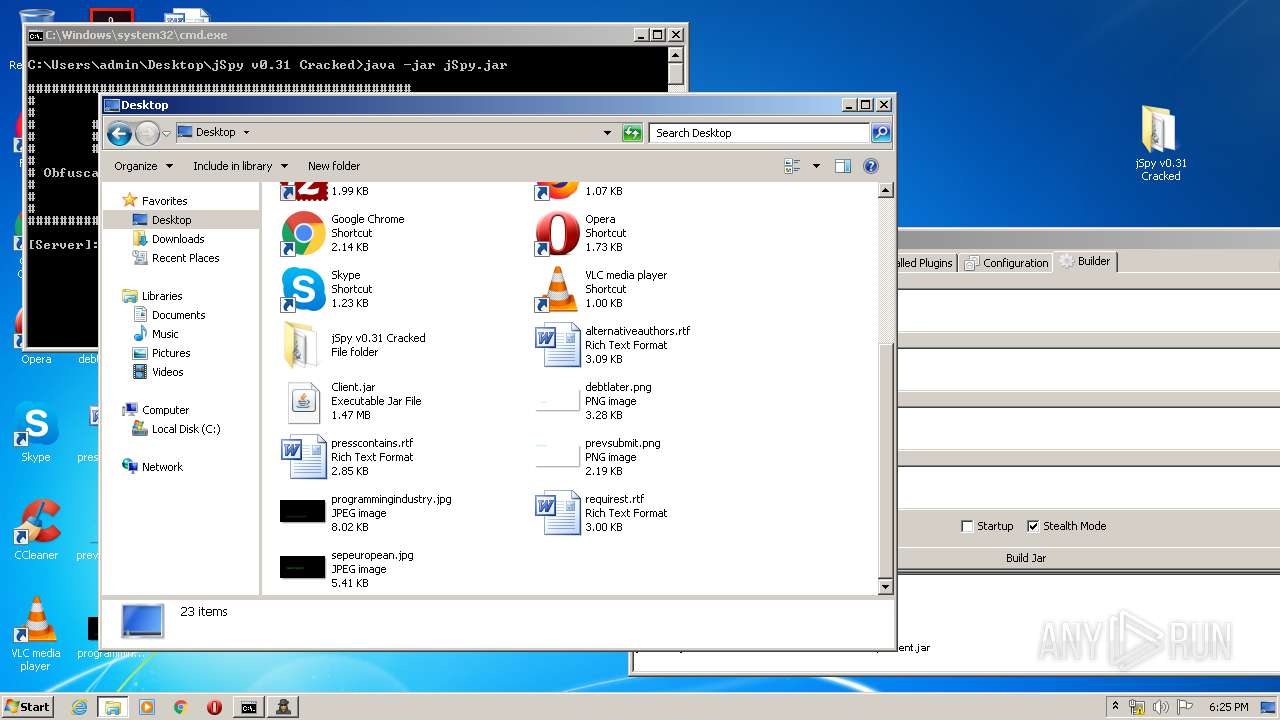
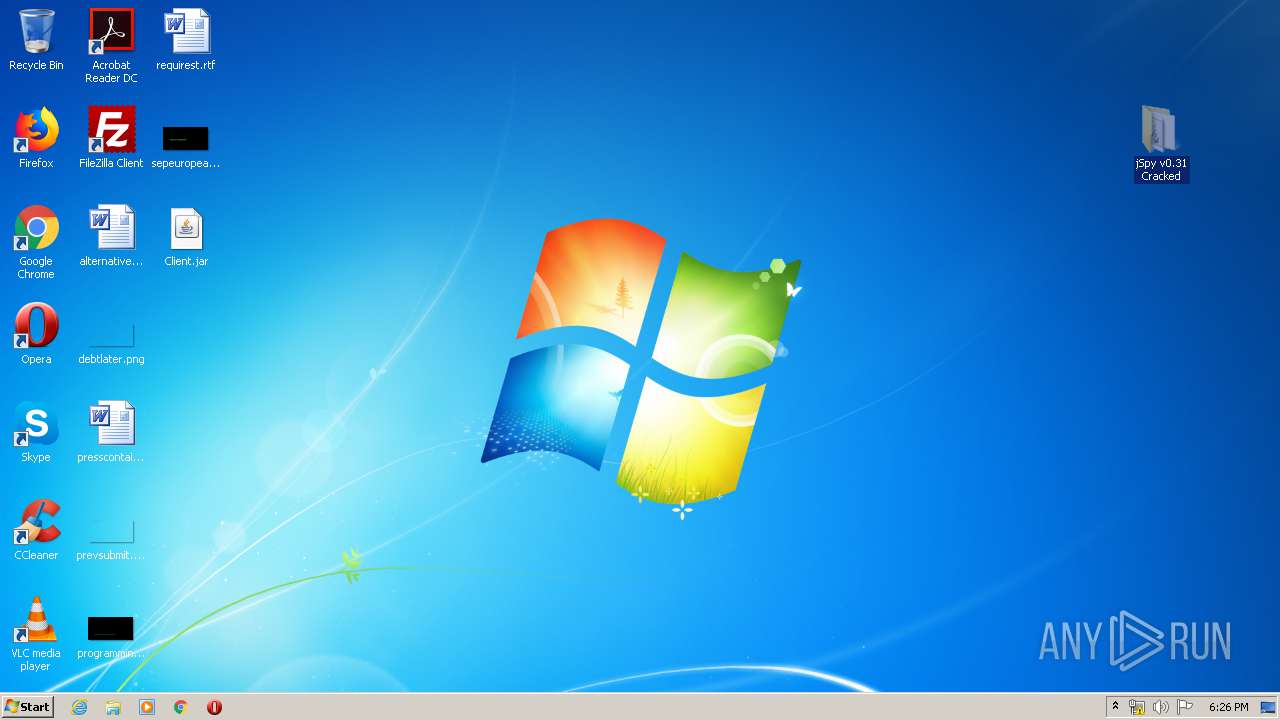
| 3180 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\Desktop\Client.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | explorer.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 3512 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\Desktop\jSpy v0.31 Cracked\jSpy.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | explorer.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
Total events
895
Read events
868
Write events
27
Delete events
0
Modification events
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\jSpy v0.31 Cracked.rar | |||
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
11
Suspicious files
8
Text files
23
Unknown types
499
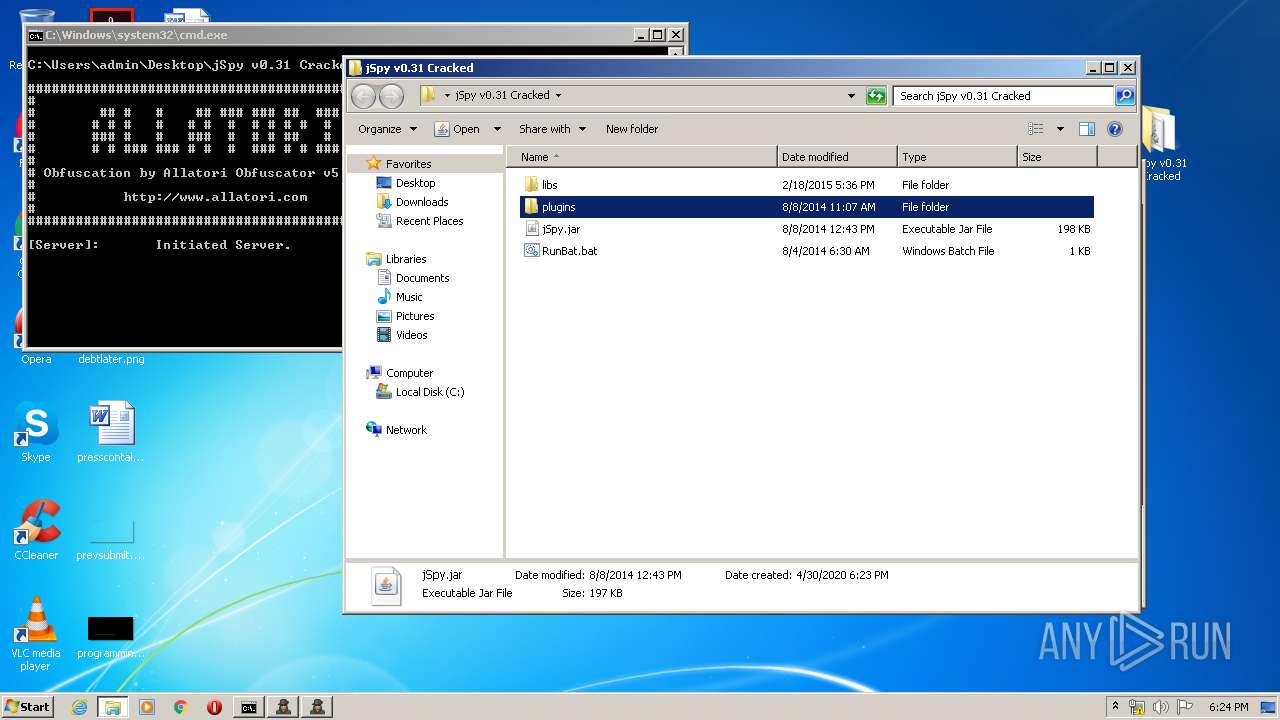
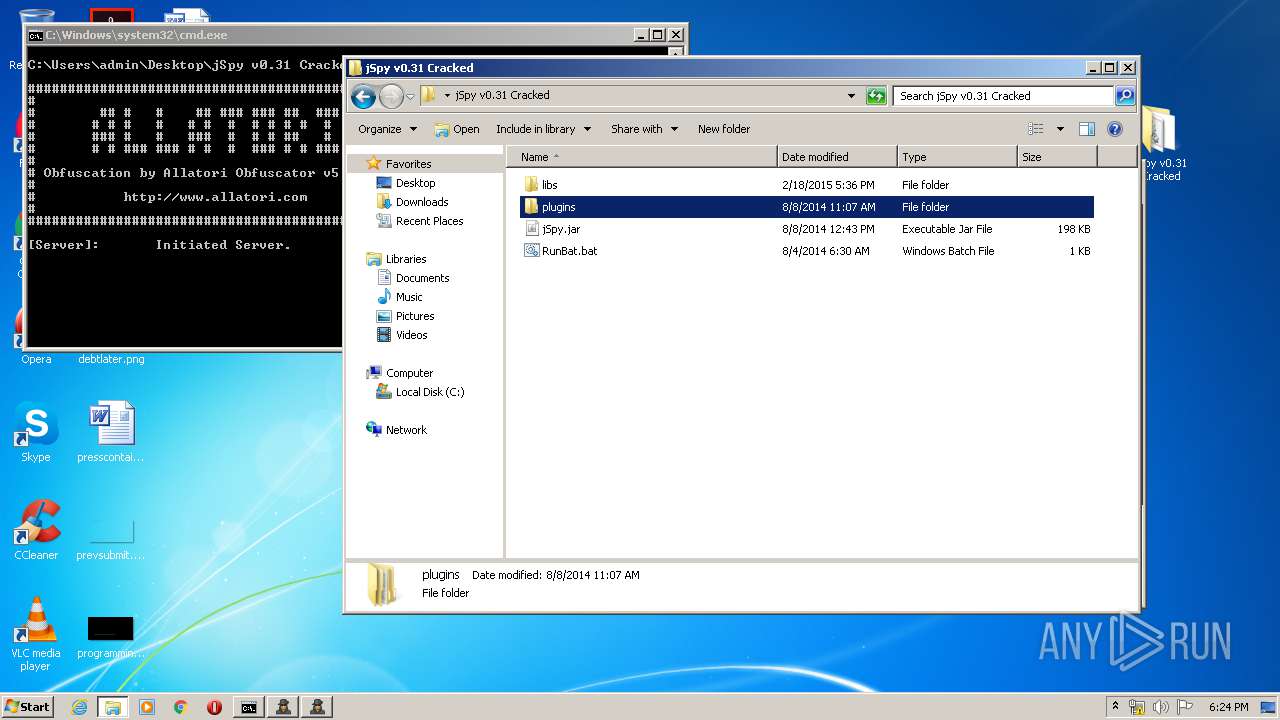
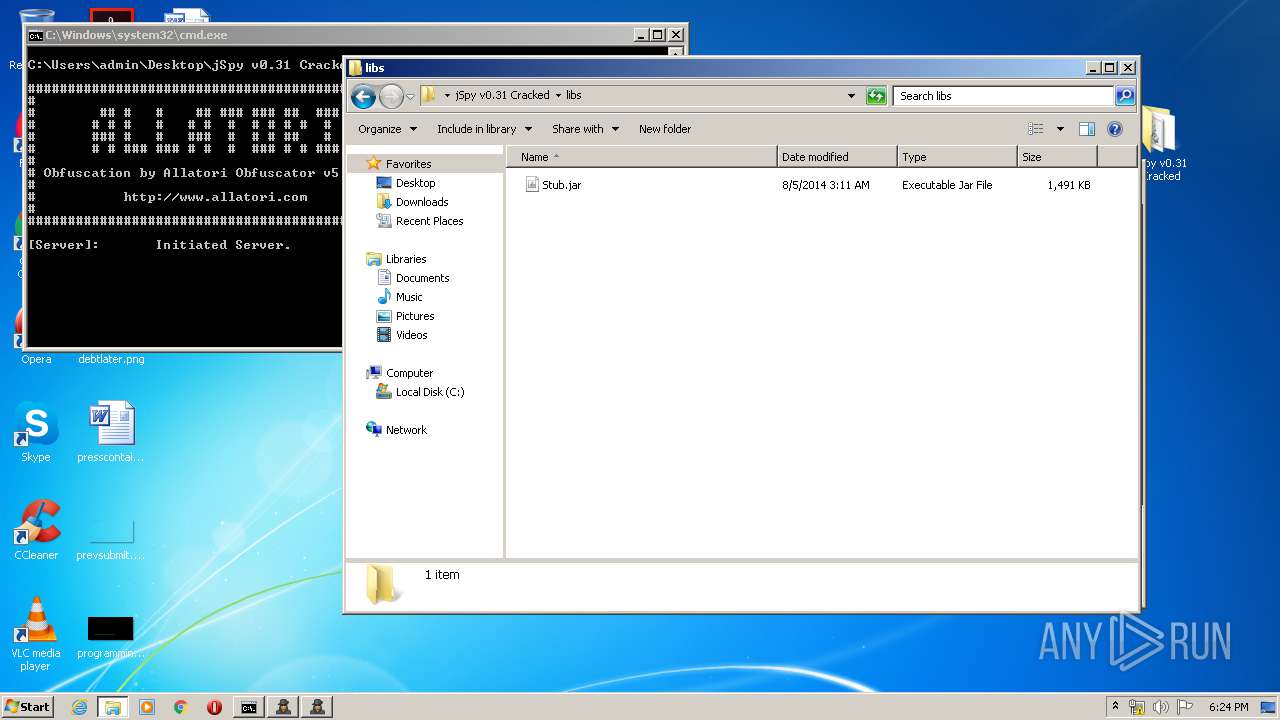
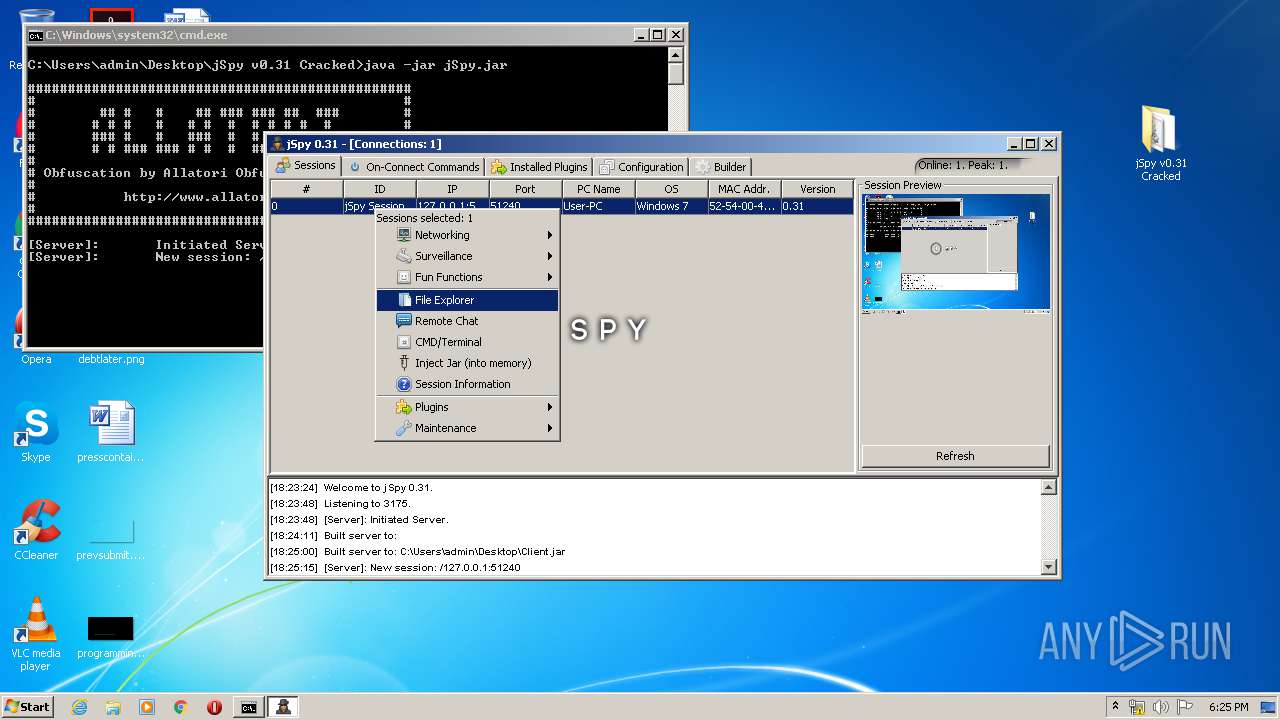
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3168.21473\jSpy v0.31 Cracked\jSpy.jar | — | |
MD5:— | SHA256:— | |||
| 3168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3168.21473\jSpy v0.31 Cracked\libs\Stub.jar | — | |
MD5:— | SHA256:— | |||
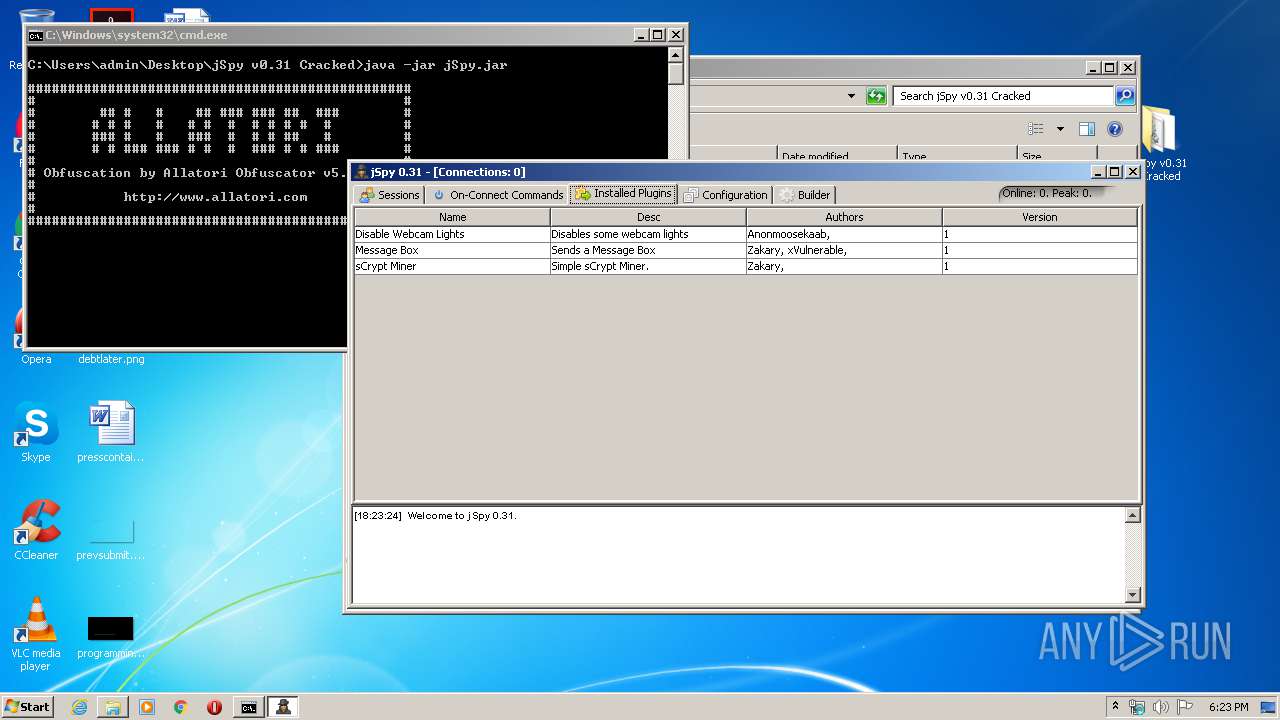
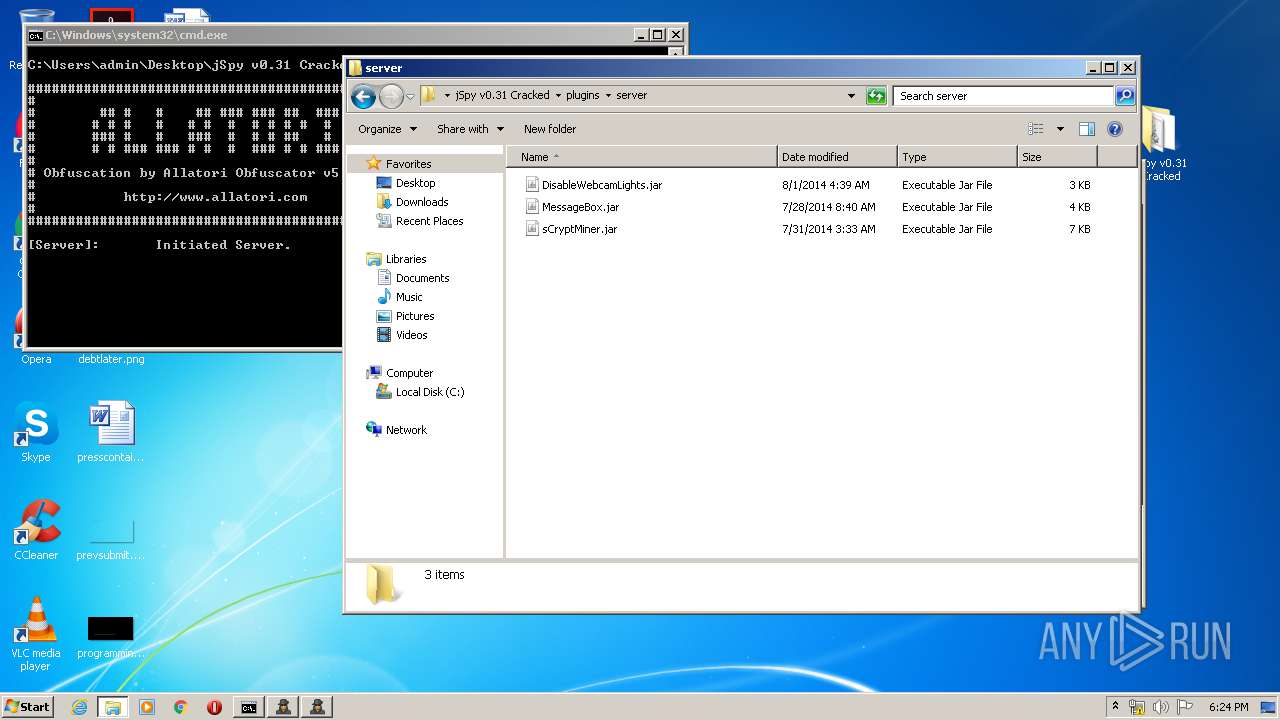
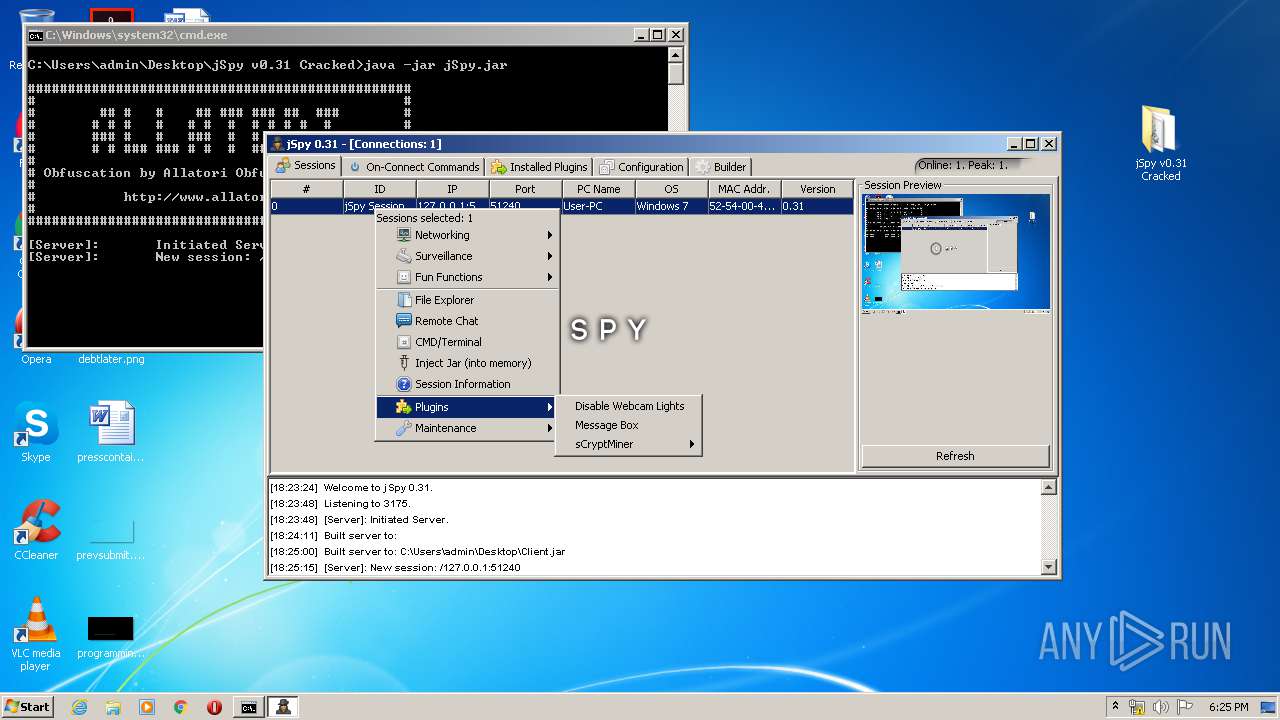
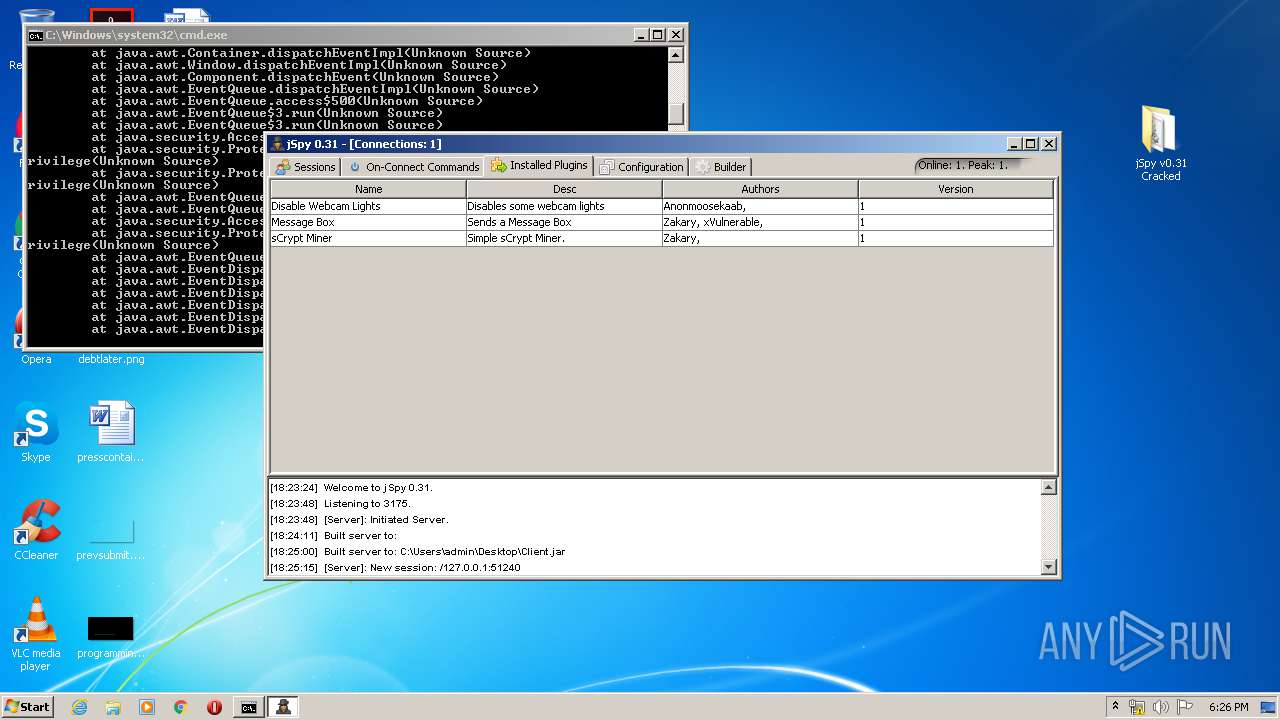
| 3168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3168.21473\jSpy v0.31 Cracked\plugins\server\DisableWebcamLights.jar | — | |
MD5:— | SHA256:— | |||
| 3168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3168.21473\jSpy v0.31 Cracked\plugins\server\MessageBox.jar | — | |
MD5:— | SHA256:— | |||
| 3168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3168.21473\jSpy v0.31 Cracked\plugins\server\sCryptMiner.jar | — | |
MD5:— | SHA256:— | |||
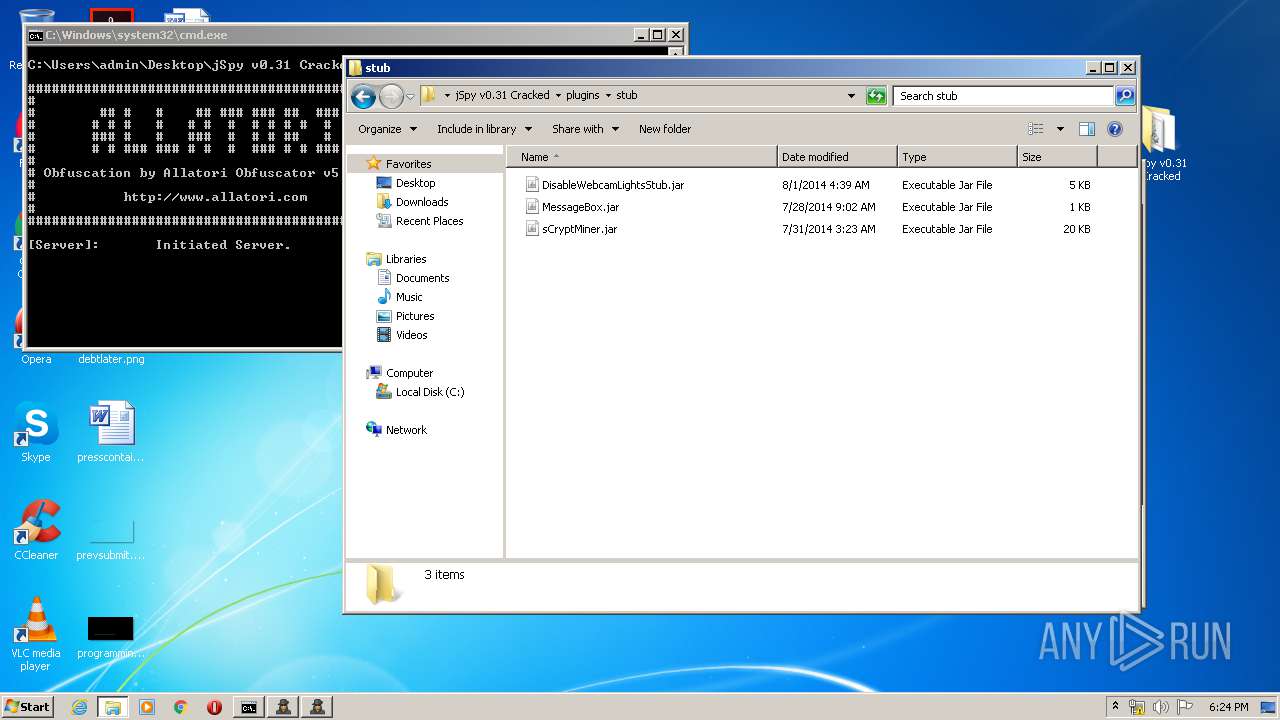
| 3168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3168.21473\jSpy v0.31 Cracked\plugins\stub\DisableWebcamLightsStub.jar | — | |
MD5:— | SHA256:— | |||
| 3168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3168.21473\jSpy v0.31 Cracked\plugins\stub\MessageBox.jar | — | |
MD5:— | SHA256:— | |||
| 3168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3168.21473\jSpy v0.31 Cracked\plugins\stub\sCryptMiner.jar | — | |
MD5:— | SHA256:— | |||
| 3168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3168.21473\jSpy v0.31 Cracked\RunBat.bat | — | |
MD5:— | SHA256:— | |||
| 1828 | java.exe | C:\Users\admin\AppData\Local\Temp\imageio7698422717578967928.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
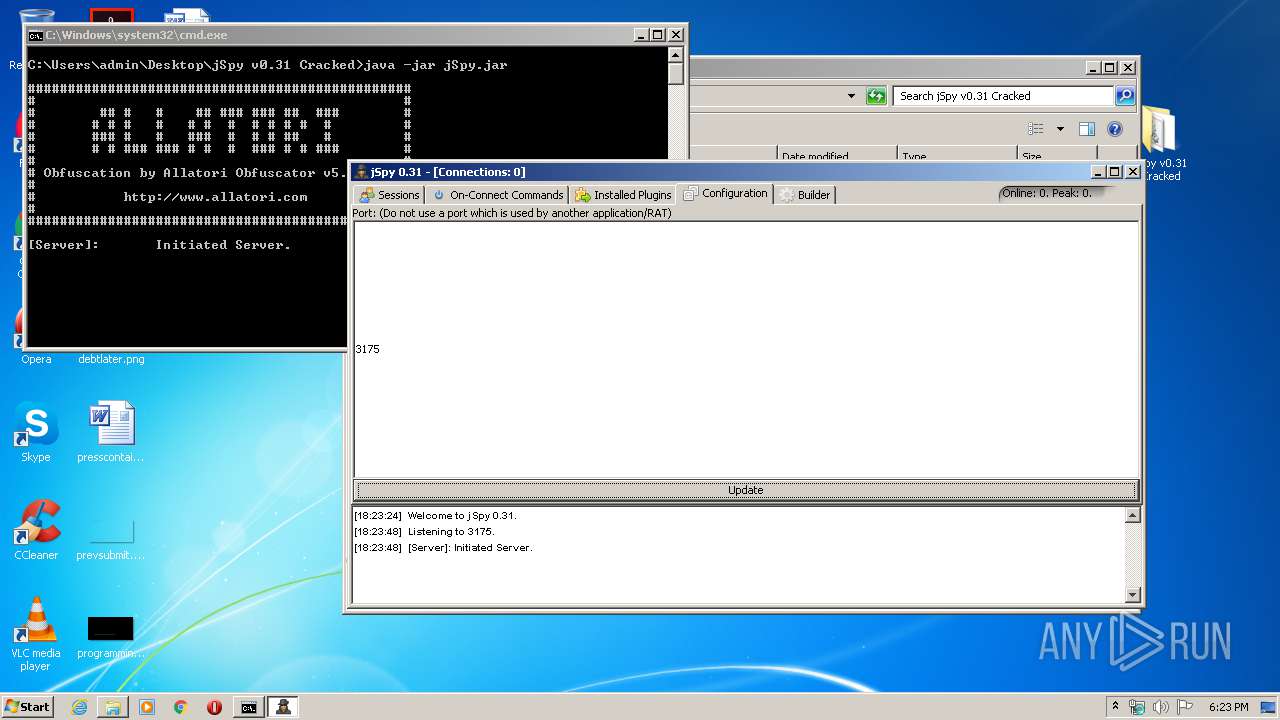
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
jstealth.co.uk |
| unknown |