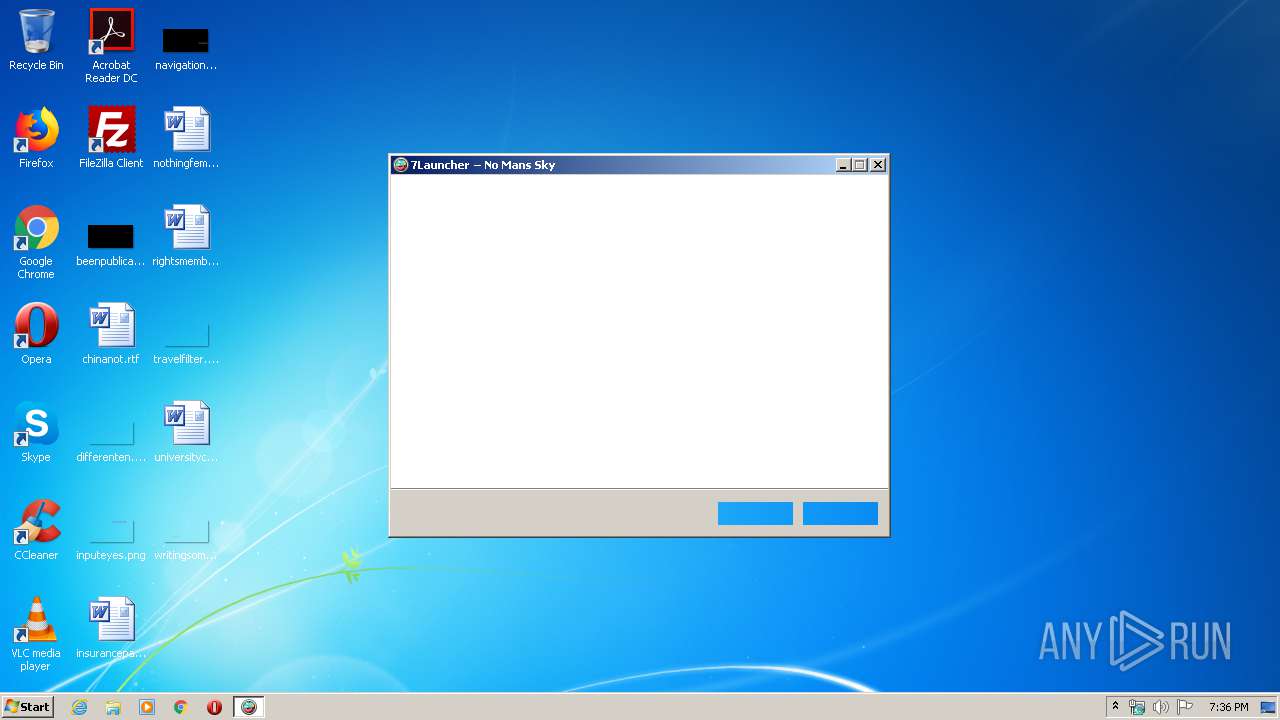
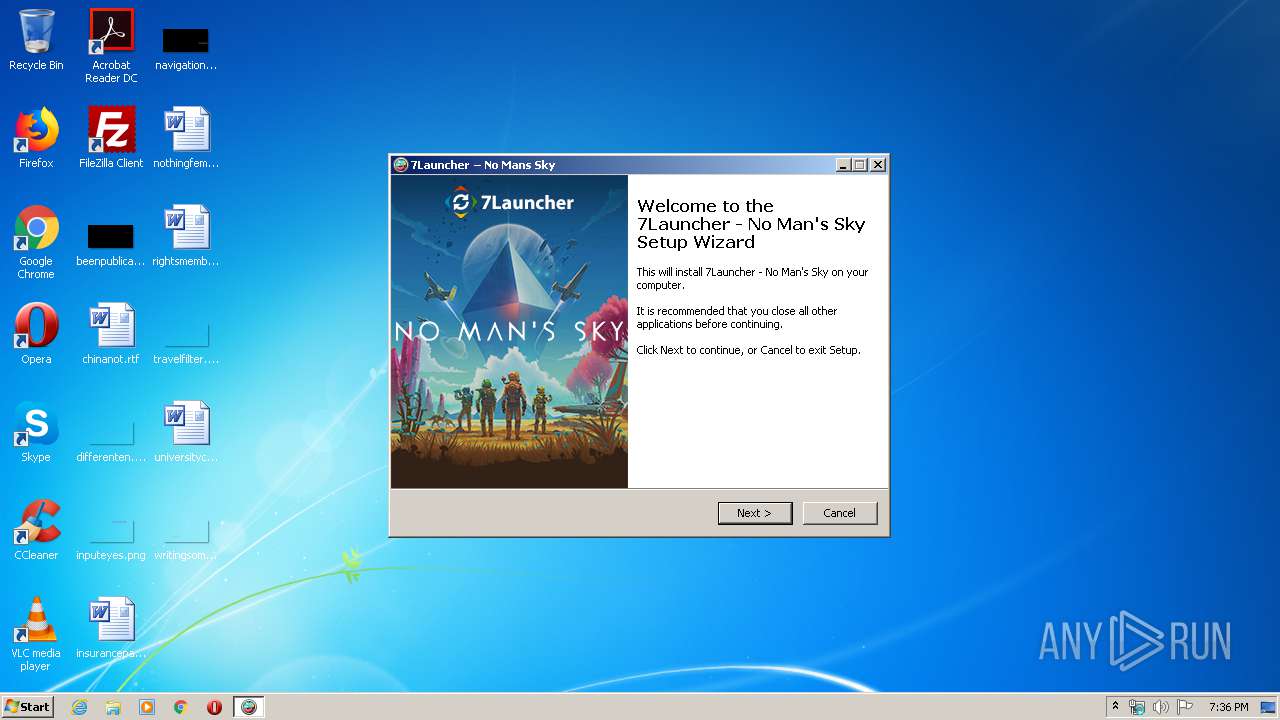
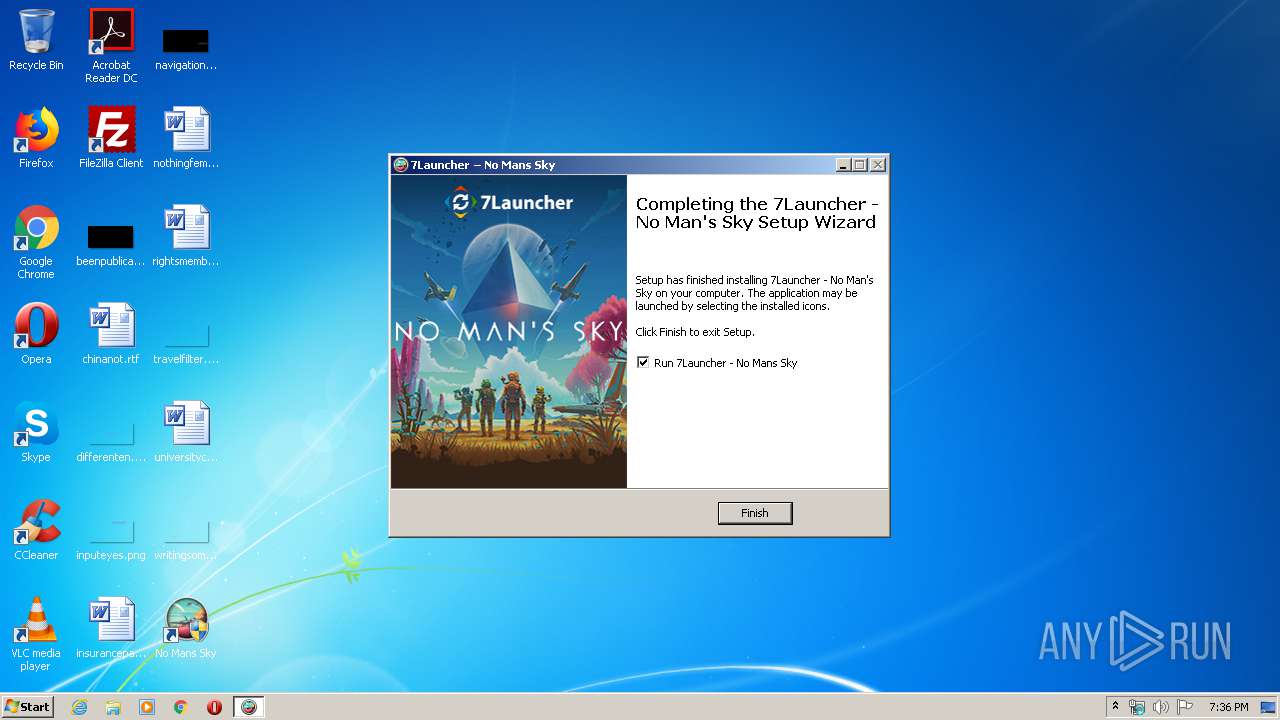
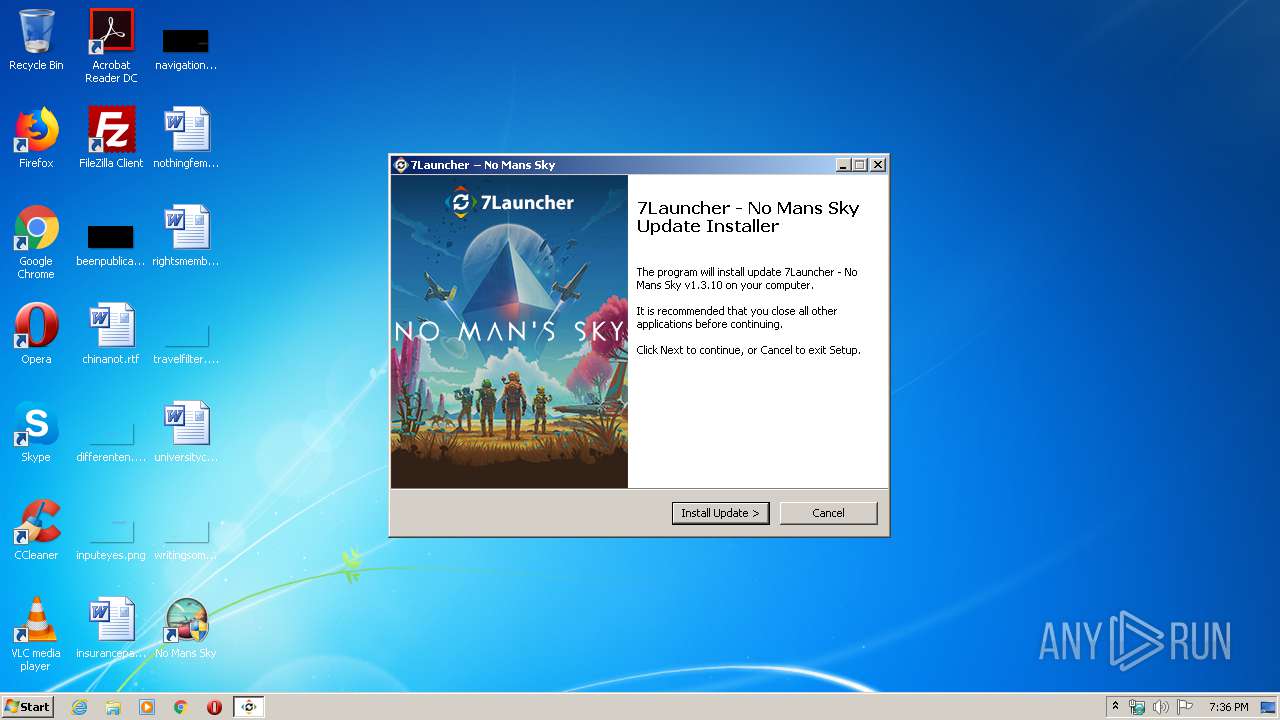
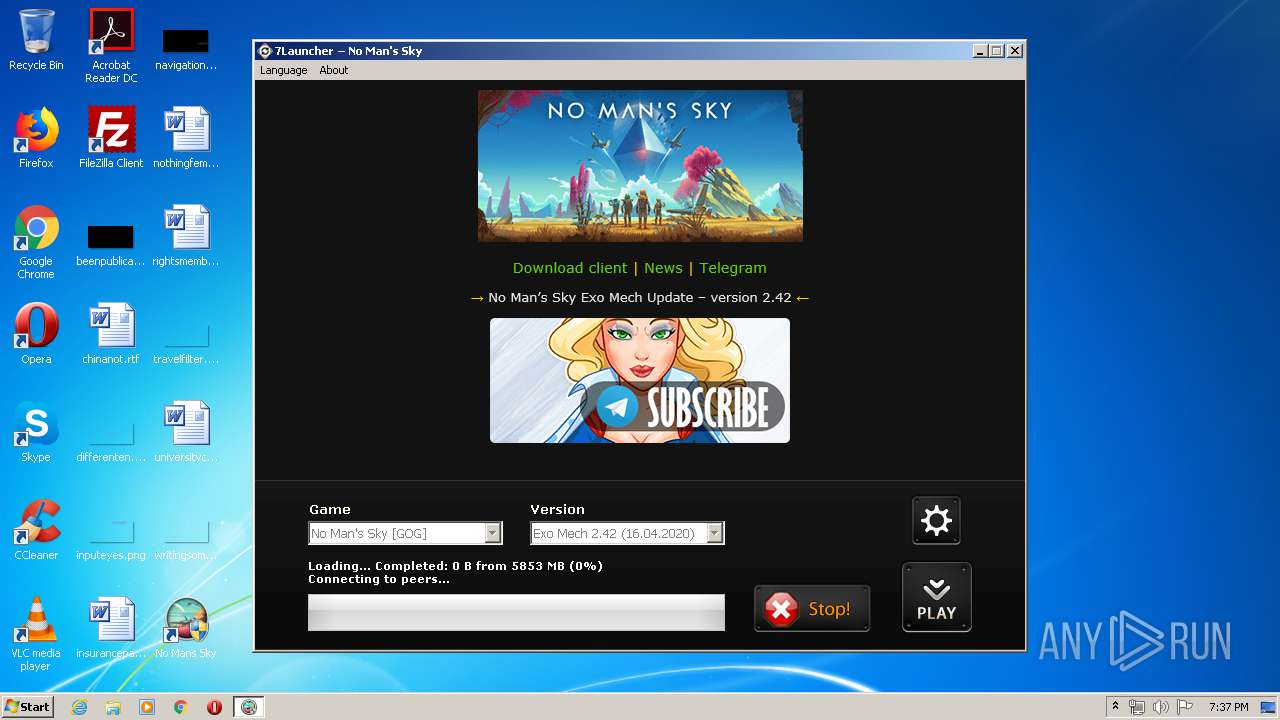
| File name: | 7l_nomanssky_setup.exe |
| Full analysis: | https://app.any.run/tasks/b583ed7b-fb8f-415c-9be3-1462b9f8304e |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2020, 18:35:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B07E683C89380D00EDD69F7191825C56 |
| SHA1: | 4E5BC209EE04494E574E1247AD929E88DCD89C20 |
| SHA256: | 500B90349757197B80E9CDA2B0DA1C15371C3CB708CA9C0C9600D90F7F714B65 |
| SSDEEP: | 49152:dOTrRf8o1OIYHWPf5GE5kvc63vd3RJHlyK8enDd3T8:kl8o1OI+WPc0k/3vhHlybep3Q |
MALICIOUS
Adds new firewall rule via NETSH.EXE
- 7l_nomanssky_setup.tmp (PID: 2732)
Application was dropped or rewritten from another process
- Run_NMS.exe (PID: 3188)
- Run_NMS.exe (PID: 2536)
- Run_NMS.exe (PID: 2052)
- aria2c.exe (PID: 3956)
- Run_NMS.exe (PID: 180)
- upt.exe (PID: 2372)
Changes settings of System certificates
- Run_NMS.exe (PID: 2536)
SUSPICIOUS
Executable content was dropped or overwritten
- 7l_nomanssky_setup.exe (PID: 2740)
- 7l_nomanssky_setup.exe (PID: 2364)
- 7l_nomanssky_setup.tmp (PID: 2732)
- upt.exe (PID: 2372)
- upt.tmp (PID: 1536)
- Run_NMS.exe (PID: 3188)
- Run_NMS.exe (PID: 2536)
Reads the Windows organization settings
- 7l_nomanssky_setup.tmp (PID: 2732)
- upt.tmp (PID: 1536)
Reads Windows owner or organization settings
- 7l_nomanssky_setup.tmp (PID: 2732)
- upt.tmp (PID: 1536)
Uses TASKKILL.EXE to kill process
- 7l_nomanssky_setup.tmp (PID: 2732)
- upt.tmp (PID: 1536)
Uses NETSH.EXE for network configuration
- 7l_nomanssky_setup.tmp (PID: 2732)
Changes IE settings (feature browser emulation)
- Run_NMS.exe (PID: 3188)
- Run_NMS.exe (PID: 2536)
Modifies the open verb of a shell class
- Run_NMS.exe (PID: 3188)
- Run_NMS.exe (PID: 2536)
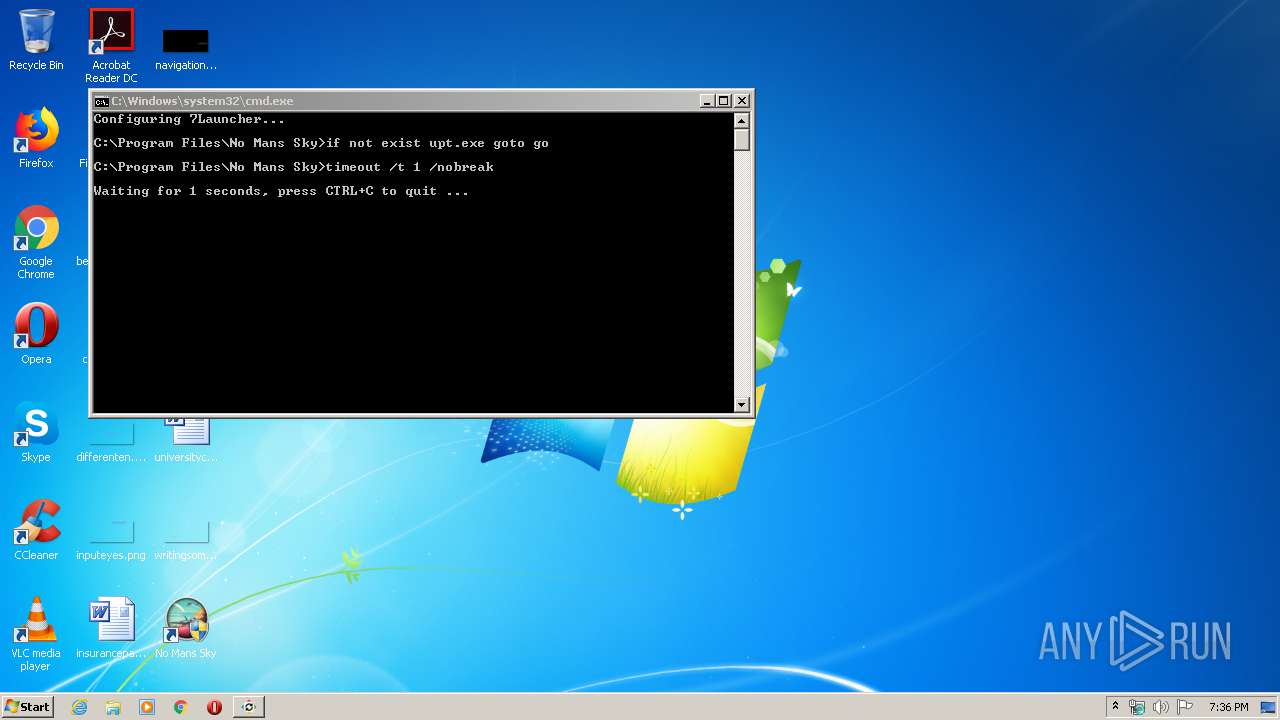
Starts CMD.EXE for commands execution
- upt.tmp (PID: 1536)
Reads Internet Cache Settings
- Run_NMS.exe (PID: 2536)
- Run_NMS.exe (PID: 3188)
Creates files in the user directory
- Run_NMS.exe (PID: 3188)
- Run_NMS.exe (PID: 2536)
Creates files in the program directory
- Run_NMS.exe (PID: 3188)
- Run_NMS.exe (PID: 2536)
- aria2c.exe (PID: 3956)
Reads internet explorer settings
- Run_NMS.exe (PID: 3188)
- Run_NMS.exe (PID: 2536)
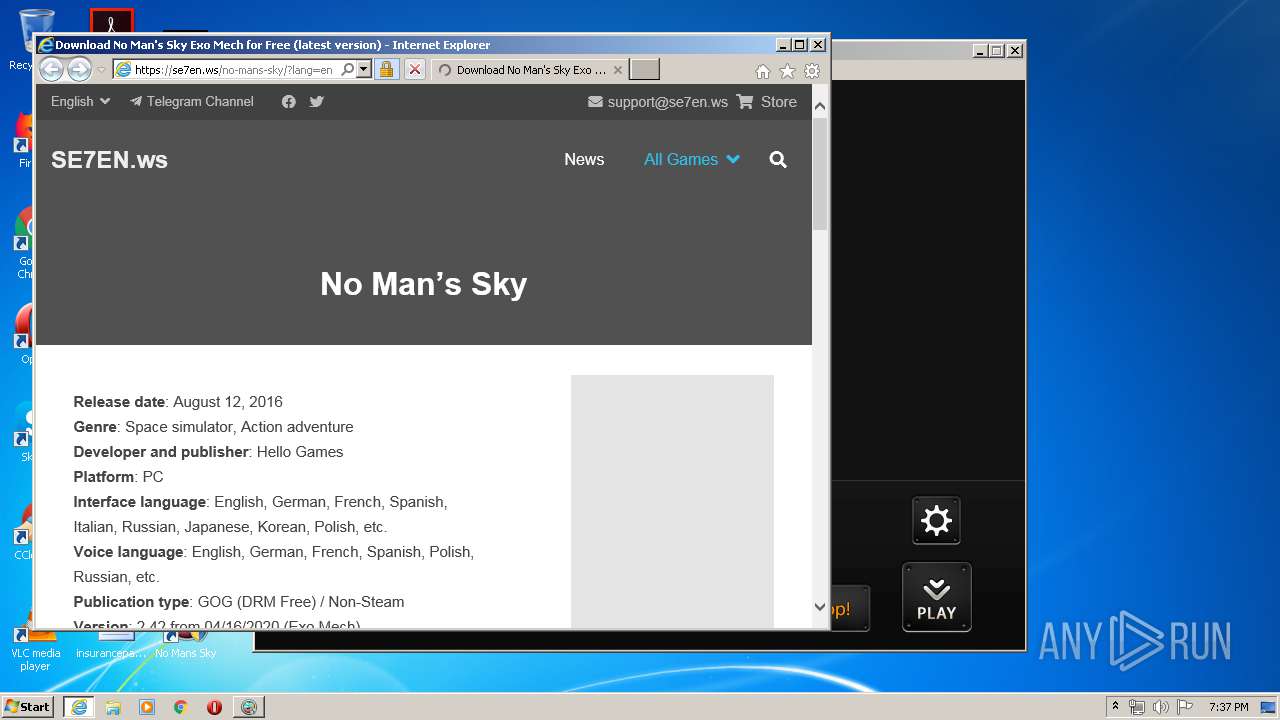
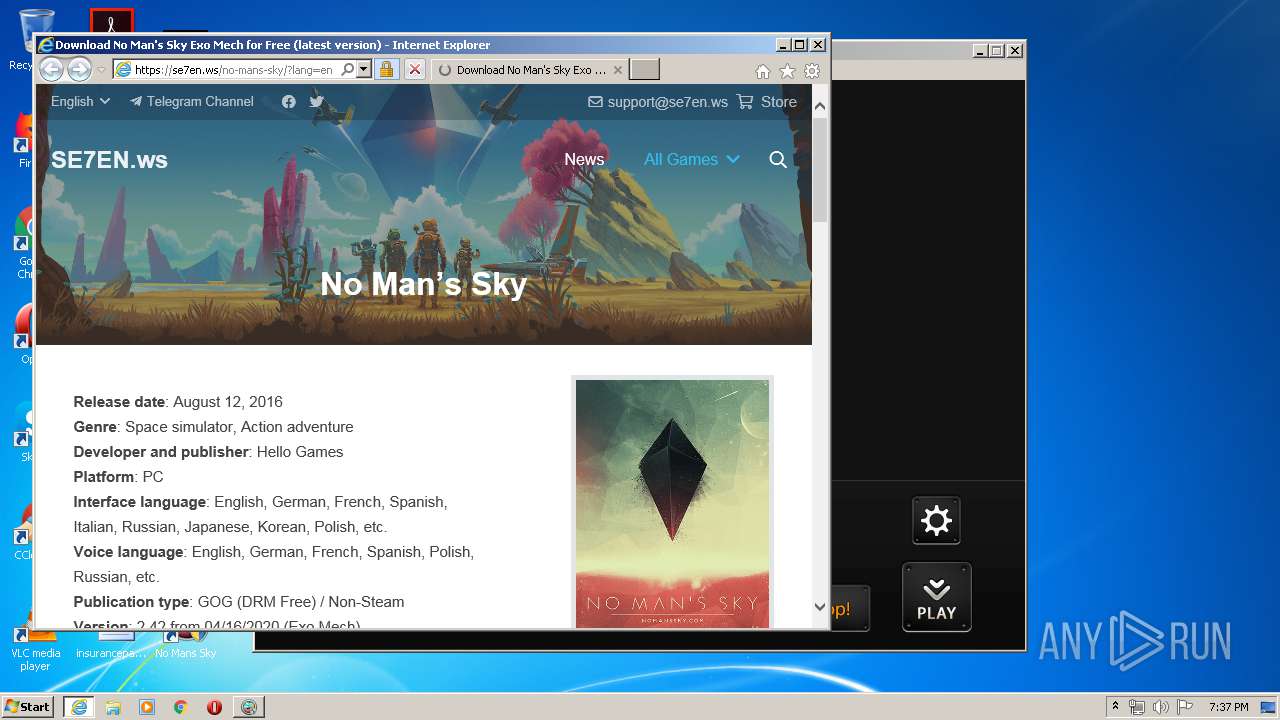
Starts Internet Explorer
- Run_NMS.exe (PID: 2536)
Adds / modifies Windows certificates
- Run_NMS.exe (PID: 2536)
INFO
Application was dropped or rewritten from another process
- 7l_nomanssky_setup.tmp (PID: 2064)
- 7l_nomanssky_setup.tmp (PID: 2732)
- upt.tmp (PID: 1536)
Creates files in the program directory
- 7l_nomanssky_setup.tmp (PID: 2732)
- upt.tmp (PID: 1536)
Creates a software uninstall entry
- 7l_nomanssky_setup.tmp (PID: 2732)
Manual execution by user
- Run_NMS.exe (PID: 180)
- Run_NMS.exe (PID: 2052)
Reads settings of System Certificates
- Run_NMS.exe (PID: 2536)
- iexplore.exe (PID: 2592)
- iexplore.exe (PID: 2212)
Reads the hosts file
- aria2c.exe (PID: 3956)
Reads Internet Cache Settings
- iexplore.exe (PID: 2212)
- iexplore.exe (PID: 2592)
Changes internet zones settings
- iexplore.exe (PID: 2212)
Creates files in the user directory
- iexplore.exe (PID: 2592)
Reads internet explorer settings
- iexplore.exe (PID: 2592)
Changes settings of System certificates
- iexplore.exe (PID: 2592)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:06:14 15:27:46+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 184832 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1181c |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.9.0 |
| ProductVersionNumber: | 1.3.9.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Hello Games |
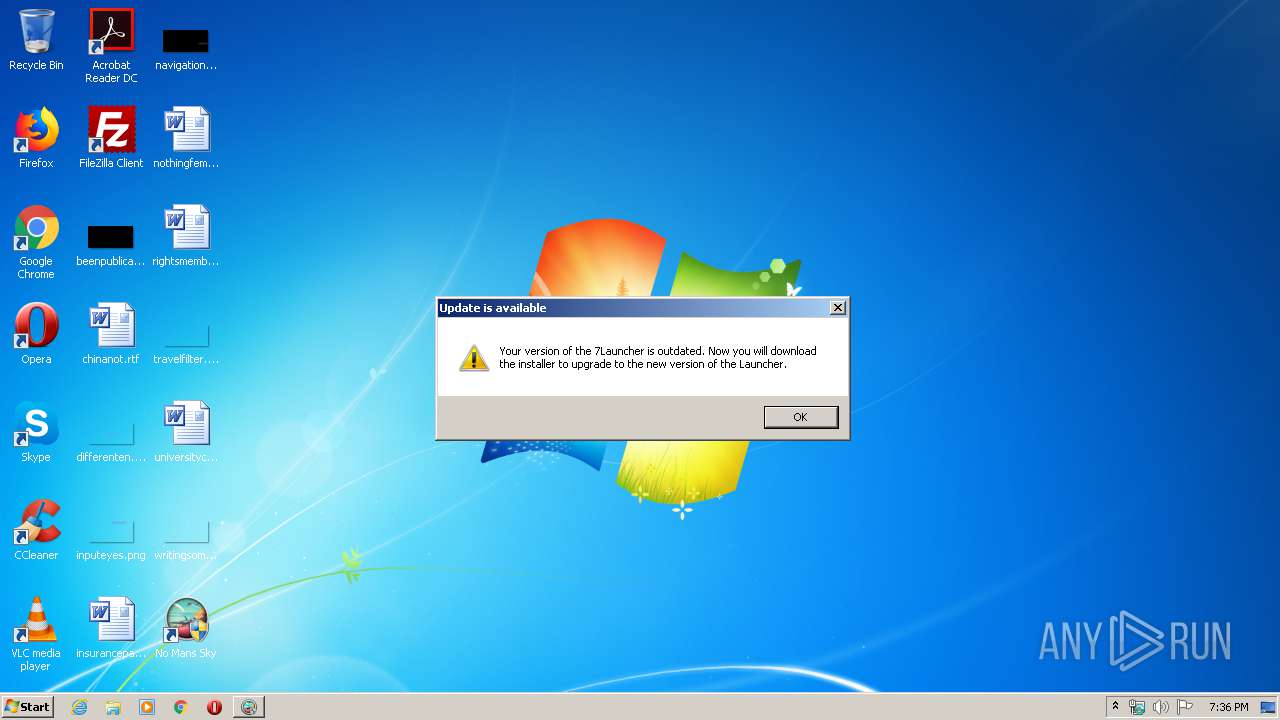
| FileDescription: | 7Launcher - No Man's Sky Setup |
| FileVersion: | 1.3.9 |
| LegalCopyright: | Hello Games |
| ProductName: | 7Launcher - No Man's Sky 1.3.9 |
| ProductVersion: | 1.3.9 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jun-2018 13:27:46 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Hello Games |
| FileDescription: | 7Launcher - No Man's Sky Setup |
| FileVersion: | 1.3.9 |
| LegalCopyright: | Hello Games |
| ProductName: | 7Launcher - No Man's Sky 1.3.9 |
| ProductVersion: | 1.3.9 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 14-Jun-2018 13:27:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F25C | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37588 |
.itext | 0x00011000 | 0x00000FA4 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.77877 |
.data | 0x00012000 | 0x00000C8C | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.30283 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x0002B00C | 0x0002B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.24927 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 7.99184 | 99835 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 6.59192 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.78035 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.90561 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 6.59192 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.78035 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 3.70379 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.79088 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 2.56031 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
79
Monitored processes
21
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
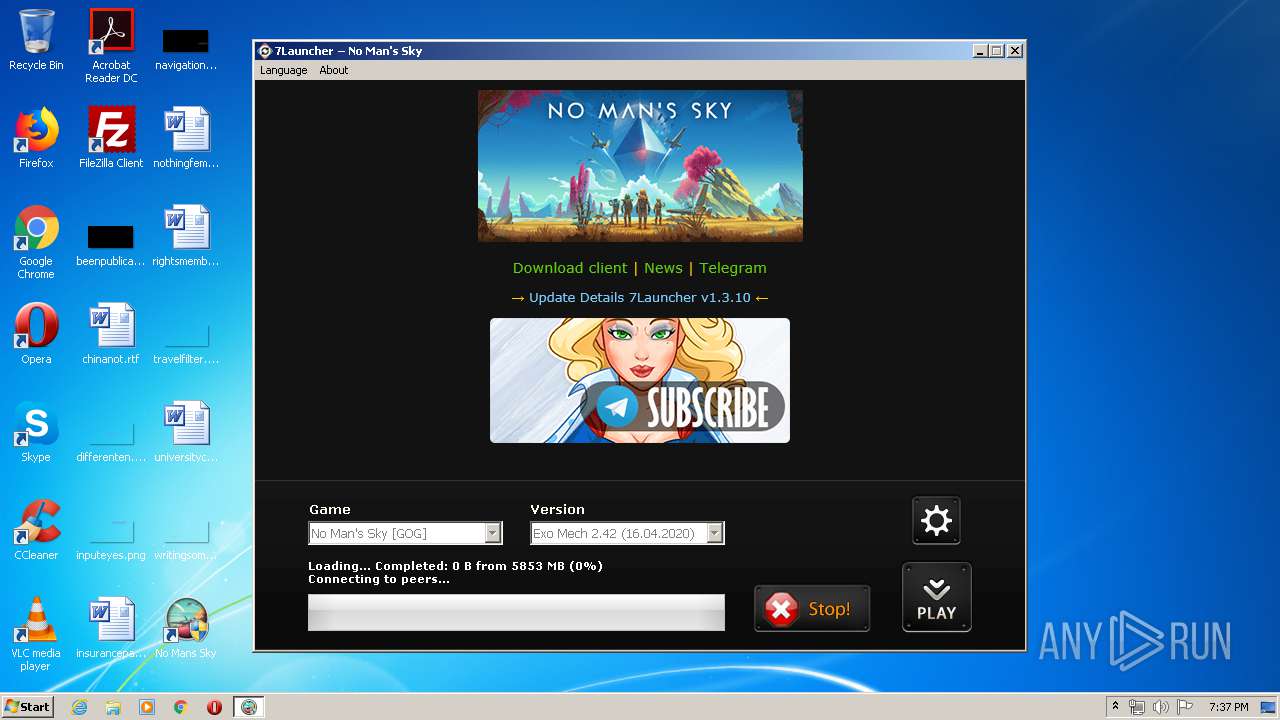
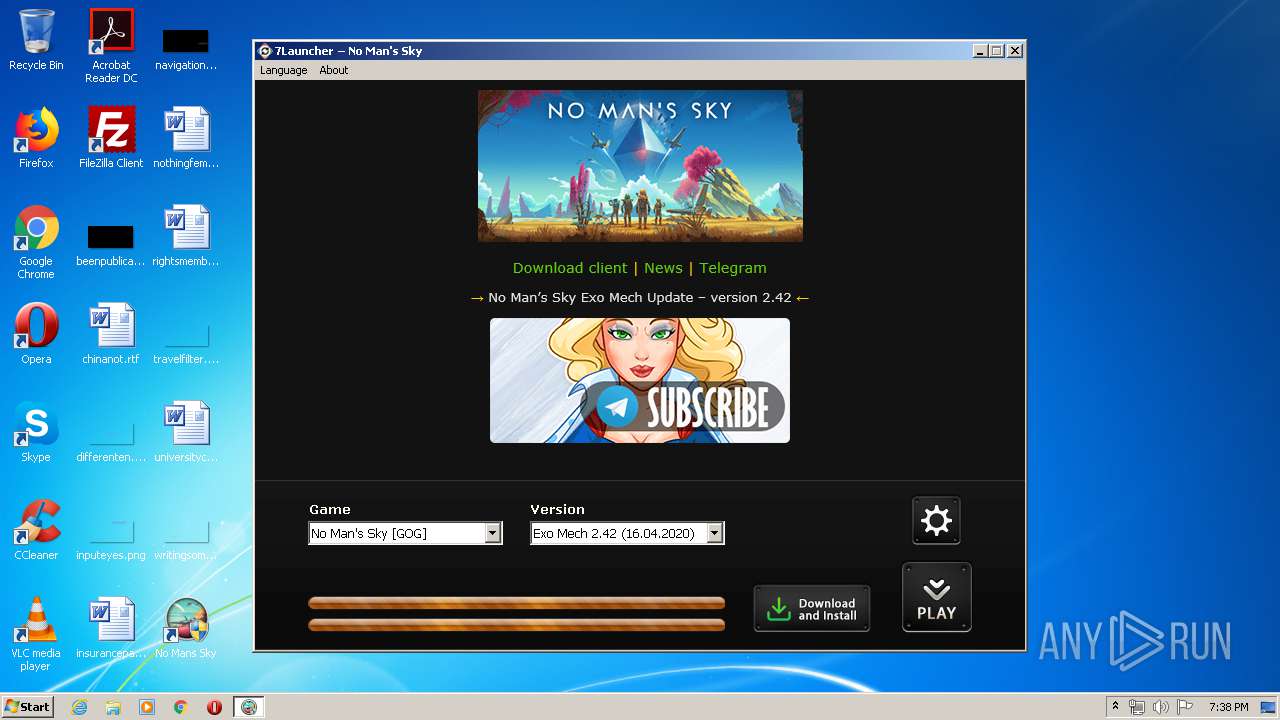
| 180 | "C:\Program Files\No Mans Sky\Run_NMS.exe" | C:\Program Files\No Mans Sky\Run_NMS.exe | — | explorer.exe | |||||||||||
User: admin Company: SE7EN Solutions, Ltd. Integrity Level: MEDIUM Description: 7Launcher - No Man's Sky Exit code: 3221226540 Version: 1.3.10.0 Modules
| |||||||||||||||
| 1452 | "C:\Windows\system32\netsh.exe" advfirewall firewall add rule name="7Launcher - No Man's Sky In" program="C:\Program Files\No Mans Sky\Run_NMS.exe" dir=in action=allow enable=yes | C:\Windows\system32\netsh.exe | — | 7l_nomanssky_setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1536 | "C:\Users\admin\AppData\Local\Temp\is-U8K1K.tmp\upt.tmp" /SL5="$B021C,1618287,308224,C:\Program Files\No Mans Sky\upt.exe" | C:\Users\admin\AppData\Local\Temp\is-U8K1K.tmp\upt.tmp | upt.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1780 | "C:\Windows\system32\netsh.exe" advfirewall firewall add rule name="P2P In" program="C:\Program Files\No Mans Sky\7launcher\tools\aria2\aria2c.exe" dir=in action=allow enable=yes | C:\Windows\system32\netsh.exe | — | 7l_nomanssky_setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1876 | "taskkill.exe" /f /im "Run_NMS.exe" | C:\Windows\system32\taskkill.exe | — | upt.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2052 | "C:\Program Files\No Mans Sky\Run_NMS.exe" | C:\Program Files\No Mans Sky\Run_NMS.exe | explorer.exe | ||||||||||||
User: admin Company: SE7EN Solutions, Ltd. Integrity Level: HIGH Description: 7Launcher - No Man's Sky Exit code: 0 Version: 1.3.10.0 Modules
| |||||||||||||||
| 2064 | "C:\Users\admin\AppData\Local\Temp\is-E6JU9.tmp\7l_nomanssky_setup.tmp" /SL5="$D01A0,1553882,252416,C:\Users\admin\AppData\Local\Temp\7l_nomanssky_setup.exe" | C:\Users\admin\AppData\Local\Temp\is-E6JU9.tmp\7l_nomanssky_setup.tmp | — | 7l_nomanssky_setup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2144 | cmd /c ""C:\Program Files\No Mans Sky\cleanup.bat" " | C:\Windows\system32\cmd.exe | — | upt.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
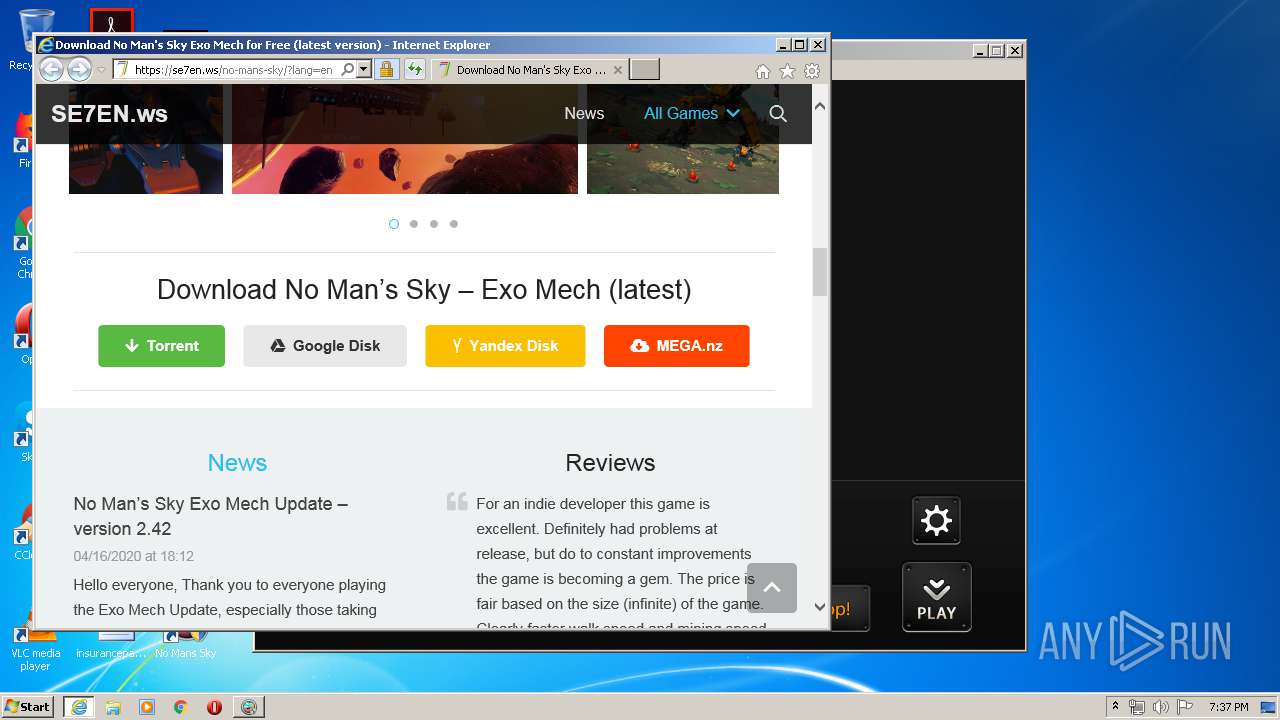
| 2212 | "C:\Program Files\Internet Explorer\iexplore.exe" https://se7en.ws/no-mans-sky/?lang=en | C:\Program Files\Internet Explorer\iexplore.exe | Run_NMS.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2364 | "C:\Users\admin\AppData\Local\Temp\7l_nomanssky_setup.exe" /SPAWNWND=$801C0 /NOTIFYWND=$D01A0 | C:\Users\admin\AppData\Local\Temp\7l_nomanssky_setup.exe | 7l_nomanssky_setup.tmp | ||||||||||||
User: admin Company: Hello Games Integrity Level: HIGH Description: 7Launcher - No Man's Sky Setup Exit code: 0 Version: 1.3.9 Modules
| |||||||||||||||
Total events
3 129
Read events
1 494
Write events
1 618
Delete events
17
Modification events
| (PID) Process: | (2732) 7l_nomanssky_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: AC0A00003C9E15620C2ED601 | |||
| (PID) Process: | (2732) 7l_nomanssky_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 1A623394F413DEB3D9606071A11DD686697767F8FE2E0B0D59A0BD5D7E84A5F2 | |||
| (PID) Process: | (2732) 7l_nomanssky_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2732) 7l_nomanssky_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: \\?\C:\Program Files\No Mans Sky\Run_NMS.exe | |||
| (PID) Process: | (2732) 7l_nomanssky_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 8353C65B8D894030683557E3A3D82045C70F353D0DB63A3E728A151C87C0F660 | |||
| (PID) Process: | (2732) 7l_nomanssky_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\SE7EN\7Launcher - No Man's Sky |
| Operation: | write | Name: | InstallDir |
Value: C:\Program Files\No Mans Sky | |||
| (PID) Process: | (2732) 7l_nomanssky_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\SE7EN\7Launcher - No Man's Sky |
| Operation: | write | Name: | GameEXE |
Value: C:\Program Files\No Mans Sky\NMS.exe | |||
| (PID) Process: | (2732) 7l_nomanssky_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\SE7EN\7Launcher - No Man's Sky |
| Operation: | write | Name: | LauncherEXE |
Value: C:\Program Files\No Mans Sky\Run_NMS.exe | |||
| (PID) Process: | (2732) 7l_nomanssky_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\7l_nms_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.6.1 (u) | |||
| (PID) Process: | (2732) 7l_nomanssky_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\7l_nms_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\No Mans Sky | |||
Executable files
8
Suspicious files
91
Text files
107
Unknown types
58
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2732 | 7l_nomanssky_setup.tmp | C:\Program Files\No Mans Sky\7luninstall\is-AR9C8.tmp | — | |
MD5:— | SHA256:— | |||
| 2732 | 7l_nomanssky_setup.tmp | C:\Program Files\No Mans Sky\7launcher\is-UHU0T.tmp | — | |
MD5:— | SHA256:— | |||
| 2732 | 7l_nomanssky_setup.tmp | C:\Program Files\No Mans Sky\is-I4TVH.tmp | — | |
MD5:— | SHA256:— | |||
| 3188 | Run_NMS.exe | C:\Program Files\No Mans Sky\upt.exe.lzma | — | |
MD5:— | SHA256:— | |||
| 1536 | upt.tmp | C:\Program Files\No Mans Sky\7launcher\is-8EBV1.tmp | — | |
MD5:— | SHA256:— | |||
| 1536 | upt.tmp | C:\Program Files\No Mans Sky\is-9BL42.tmp | — | |
MD5:— | SHA256:— | |||
| 1536 | upt.tmp | C:\Program Files\No Mans Sky\is-TMC9G.tmp | — | |
MD5:— | SHA256:— | |||
| 2740 | 7l_nomanssky_setup.exe | C:\Users\admin\AppData\Local\Temp\is-E6JU9.tmp\7l_nomanssky_setup.tmp | executable | |
MD5:— | SHA256:— | |||
| 2364 | 7l_nomanssky_setup.exe | C:\Users\admin\AppData\Local\Temp\is-3RPA5.tmp\7l_nomanssky_setup.tmp | executable | |
MD5:— | SHA256:— | |||
| 2732 | 7l_nomanssky_setup.tmp | C:\Users\admin\Desktop\No Mans Sky.lnk | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
64
TCP/UDP connections
147
DNS requests
42
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
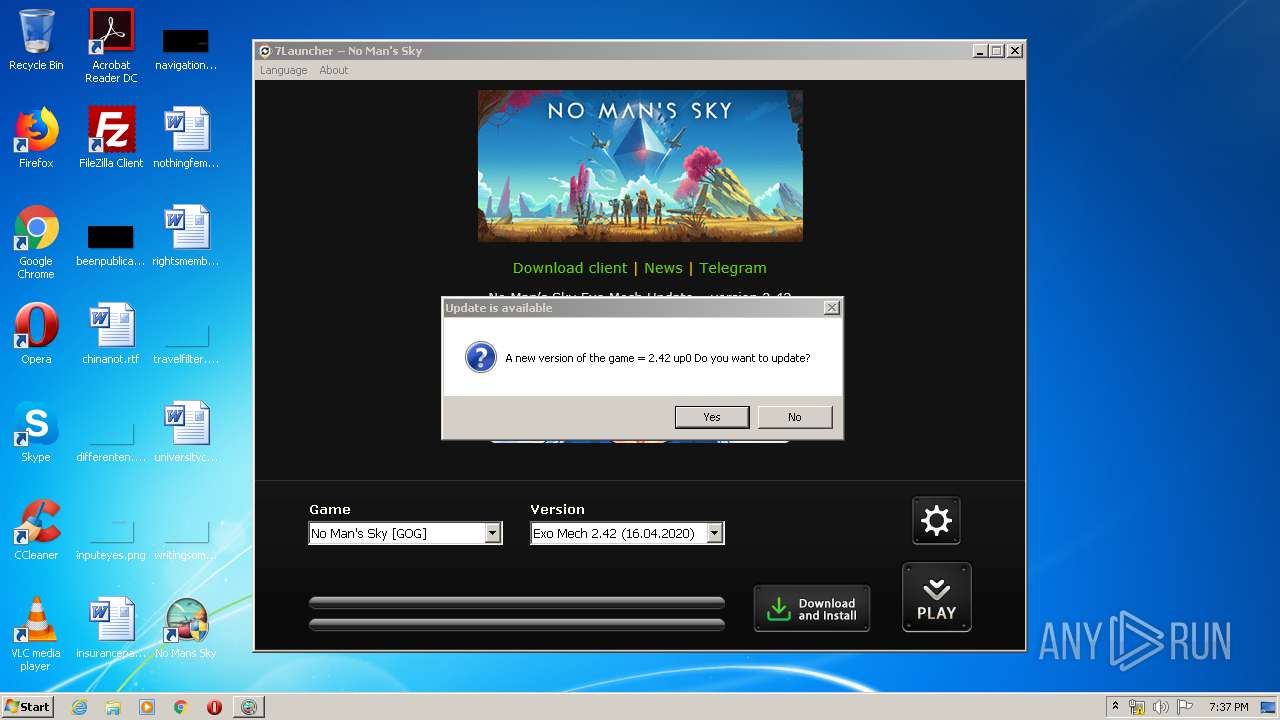
3188 | Run_NMS.exe | GET | 200 | 104.31.79.206:80 | http://updater.se7enkills.net/nms/inf.ini | US | text | 1.04 Kb | whitelisted |
2536 | Run_NMS.exe | GET | 200 | 104.31.78.206:80 | http://updater.se7enkills.net/nms/inf.ini | US | text | 1.04 Kb | whitelisted |
3188 | Run_NMS.exe | GET | 200 | 104.31.79.206:80 | http://updater.se7enkills.net/nms/inf.ini | US | text | 1.05 Kb | whitelisted |
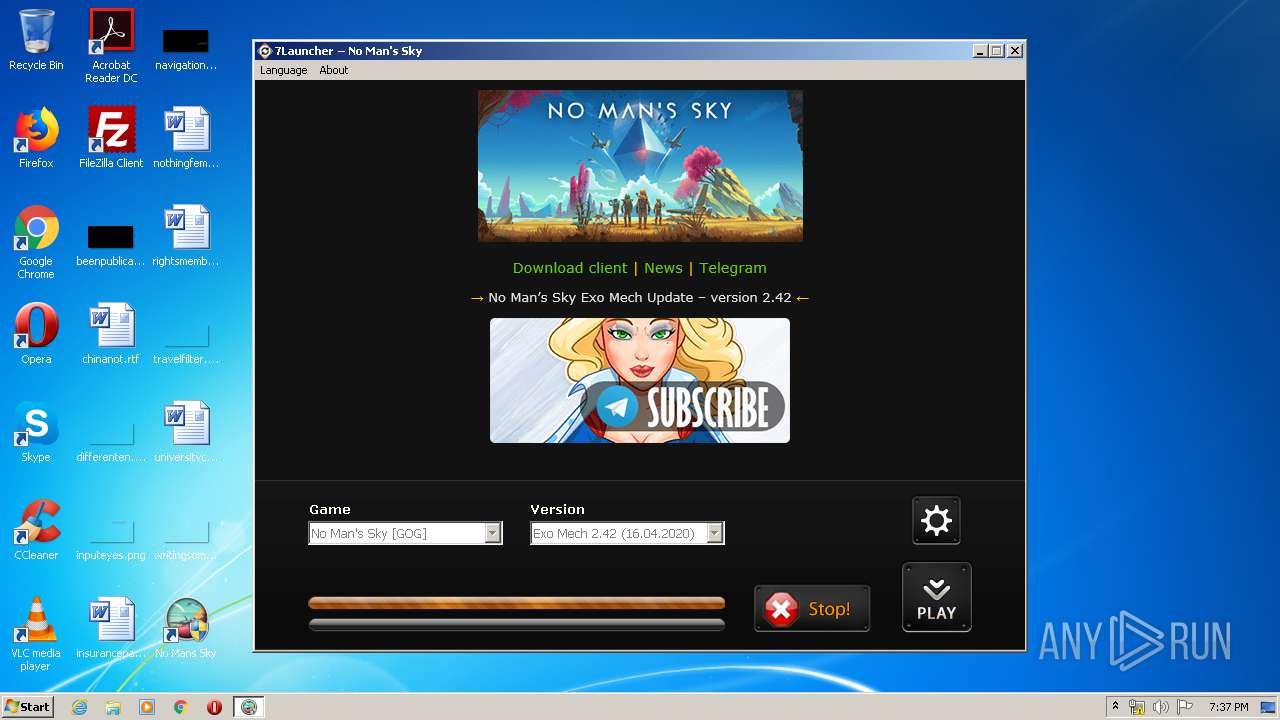
3188 | Run_NMS.exe | GET | 200 | 104.31.79.206:80 | http://updater.se7enkills.net/nms/upt.exe.lzma | US | lzma | 1.97 Mb | whitelisted |
2536 | Run_NMS.exe | GET | 200 | 104.31.78.206:80 | http://updater.se7enkills.net/images/7l-nms-header.png | US | image | 24.6 Kb | whitelisted |
2536 | Run_NMS.exe | GET | 200 | 104.31.78.206:80 | http://updater.se7enkills.net/nms/en/ | US | html | 1.16 Kb | whitelisted |
2536 | Run_NMS.exe | GET | 200 | 104.31.78.206:80 | http://updater.se7enkills.net/images/telega-banner.png | US | image | 20.6 Kb | whitelisted |
2536 | Run_NMS.exe | GET | 200 | 104.31.78.206:80 | http://updater.se7enkills.net/nms/inf.ini | US | text | 1.04 Kb | whitelisted |
2536 | Run_NMS.exe | GET | 200 | 216.58.208.35:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3956 | aria2c.exe | GET | 200 | 159.69.65.157:6969 | http://tracker.files.fm:6969/announce?info_hash=%F5%808%7F3%26%F6%F0G%8FlK%21%8D%06%28%C1%8C%AC%A8&peer_id=A2-1-34-0-%7C8%9B%F0Q%DD%8B%F6%ED%1D&uploaded=0&downloaded=0&left=6138070947&compact=1&key=%9B%F0Q%DD%8B%F6%ED%1D&numwant=50&no_peer_id=1&port=6998&event=started&supportcrypto=1 | US | binary | 398 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2536 | Run_NMS.exe | 104.31.78.206:80 | — | Cloudflare Inc | US | shared |
3956 | aria2c.exe | 104.26.2.87:443 | se7en.ws | Cloudflare Inc | US | suspicious |
2536 | Run_NMS.exe | 216.58.208.35:80 | updater.se7enkills.net | Google Inc. | US | whitelisted |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2536 | Run_NMS.exe | 172.217.16.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3956 | aria2c.exe | 159.69.65.157:6969 | tracker.files.fm | — | US | suspicious |
3956 | aria2c.exe | 159.69.65.157:6885 | tracker.files.fm | — | US | suspicious |
3956 | aria2c.exe | 159.69.65.157:6895 | tracker.files.fm | — | US | suspicious |
3956 | aria2c.exe | 159.69.65.157:6898 | tracker.files.fm | — | US | suspicious |
3956 | aria2c.exe | 159.69.65.157:6897 | tracker.files.fm | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
updater.se7enkills.net |
| whitelisted |
dns.msftncsi.com |
| shared |
www.googletagmanager.com |
| whitelisted |
se7en.ws |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
tracker.files.fm |
| malicious |
cdn.onesignal.com |
| whitelisted |
www.youtube.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2536 | Run_NMS.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
2536 | Run_NMS.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
2536 | Run_NMS.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
3956 | aria2c.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent Announce |
3956 | aria2c.exe | A Network Trojan was detected | ET USER_AGENTS Aria2 User-Agent |
3956 | aria2c.exe | Potential Corporate Privacy Violation | GPL P2P BitTorrent announce request |
2536 | Run_NMS.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
2536 | Run_NMS.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
2536 | Run_NMS.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
2536 | Run_NMS.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |